GERMWARFARE The Problem of Germ Warfare in NYC

GERM-WARFARE
The Problem of Germ Warfare in NYC n n n n n Germ Warfare – the use of a biological weapon a disease – causing microbe or a toxin intended to injure people, animals, etc. Anthrax is a deadly bacterium produced by the bacteria Bacillus anthracites, stemming from the Greek word for coal. Anthrax is the easiest biological agent to manufacture. Anthrax is easy to develop as a weapon and is easily stored and preserved for long periods of time. The three types of anthrax infections are Cutaneous Anthrax, Gastrointestinal Anthrax, and Inhalation Anthrax. Cutaneous Anthrax is caused by contact with infected animals or contaminated animal products. Gastrointestinal Anthrax occurs when one eats contaminated animal products. Inhalation Anthrax is caused by inhaling anthrax spores which are the most lethal and poses the biggest threat to our country. Symptoms of anthrax in people include fever, malaise, fatigue, coughing, and mild chest discomfort followed by difficulty breathing. www. artdecoworld. com/ gallerychrysler. htm www. stanford. edu/~grass/ page 4. html www. visit-new-york-city. com/
Causes of Germ Warfare in NYC § Terrorism in an attempt to promote national, religious, or political ideals. § Biological agents are inexpensive, easy to obtain, produce, and store, and able to affect masses. § § § Revengeful country. § Insects spread the disease. Mental patient escapes and releases biological agent. Governmental test gone wrong. US Army experiment on civilians. A European country experiment on Americans. Department of Defense Chemical and Biological Warfare research program gone wrong. www. solutions-site. org/kids/ stories/KScat 4_sol 78. htm www. cwru. edu/. . . /finadmin/does/ web/Biosafety. htm emc. ornl. gov/EMC/ Product. Med. Mgmt. Bio. html www. uos. harvard. edu/ehs/ bio_shi. shtml
Probable Reactions Encountering Germ Warfare n Mass hysteria. n Riots looting of the city. n Intensive care units and isolation beds across the city are at maximum capacity. n Shortage of antibiotics. n Triage plan enforced. n Stock piling of food. n People refuse to return to their homes, businesses are abandoned and the city commerce suffers tremendous losses. n The tourism industry collapses. n Train, bus, and plane traffic to and from the city is sharply disrupted.
Safety Procedures § All procedures shall be performed carefully to minimize the www. alumni. utah. edu/continuum/winter 98/gene. html www. fisheredu. com/cgi-bin/catalog. cgi? item =q 0419 www. pp. okstate. edu/ehs/ modules/bbpppe. htm creation of aerosols. § Laboratory windows and doors should be kept closed when experiments are in progress. § No eating, drinking, or smoking should be allowed in laboratory at any time. § Investigators must always wear protective clothing such as coverings on their shoes and latex gloves. § Investigators should Avoid touching mucosal surfaces with their hands (gloved or ungloved). § Physical containment provides means of containment of recombinants within the equipment in order to prevent propagation and dissemination to the laboratory staff or other objects. § All contaminants originated from the experimental organisms shall be sterilized before disposal, and other contaminated apparatus should be re-used after cleansing or decontaminated or sterilized before disposal. § If an infectious agent is suspected in the air, labs should turn off fans or ventilate units in the immediate area. § Decontaminate laboratory after each use and dispose of supplies and equipment in proper receptacles. § Remove and reverse gloves before leaving laboratory and dispose of them in a biohazard container.
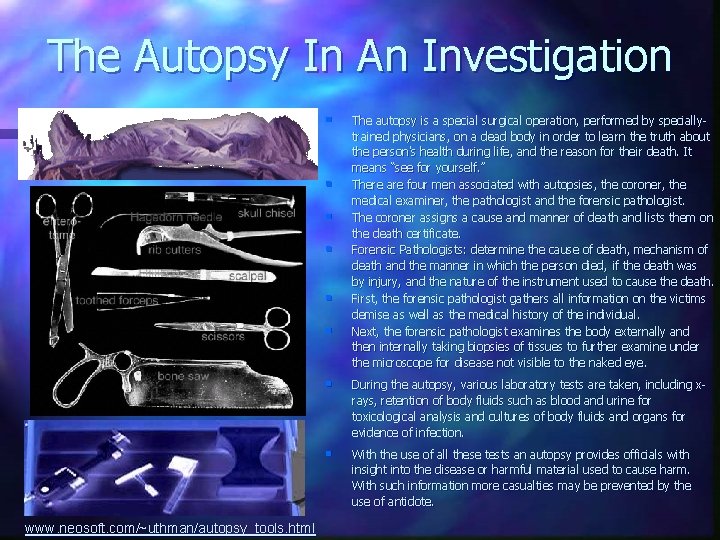
The Autopsy In An Investigation § § § www. neosoft. com/~uthman/autopsy_tools. html The autopsy is a special surgical operation, performed by speciallytrained physicians, on a dead body in order to learn the truth about the person's health during life, and the reason for their death. It means “see for yourself. ” There are four men associated with autopsies, the coroner, the medical examiner, the pathologist and the forensic pathologist. The coroner assigns a cause and manner of death and lists them on the death certificate. Forensic Pathologists: determine the cause of death, mechanism of death and the manner in which the person died, if the death was by injury, and the nature of the instrument used to cause the death. First, the forensic pathologist gathers all information on the victims demise as well as the medical history of the individual. Next, the forensic pathologist examines the body externally and then internally taking biopsies of tissues to further examine under the microscope for disease not visible to the naked eye. § During the autopsy, various laboratory tests are taken, including xrays, retention of body fluids such as blood and urine for toxicological analysis and cultures of body fluids and organs for evidence of infection. § With the use of all these tests an autopsy provides officials with insight into the disease or harmful material used to cause harm. With such information more casualties may be prevented by the use of antidote.
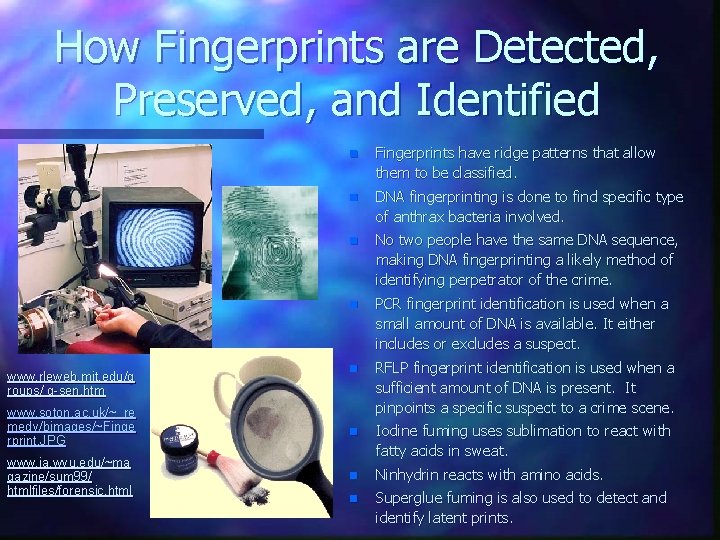
How Fingerprints are Detected, Preserved, and Identified n Fingerprints have ridge patterns that allow them to be classified. n DNA fingerprinting is done to find specific type of anthrax bacteria involved. n No two people have the same DNA sequence, making DNA fingerprinting a likely method of identifying perpetrator of the crime. n PCR fingerprint identification is used when a small amount of DNA is available. It either includes or excludes a suspect. n www. soton. ac. uk/~_re medy/bimages/~Finge rprint. JPG RFLP fingerprint identification is used when a sufficient amount of DNA is present. It pinpoints a specific suspect to a crime scene. n www. ia. wvu. edu/~ma gazine/sum 99/ htmlfiles/forensic. html Iodine fuming uses sublimation to react with fatty acids in sweat. n Ninhydrin reacts with amino acids. n Superglue fuming is also used to detect and identify latent prints. www. rleweb. mit. edu/g roups/ g-sen. htm
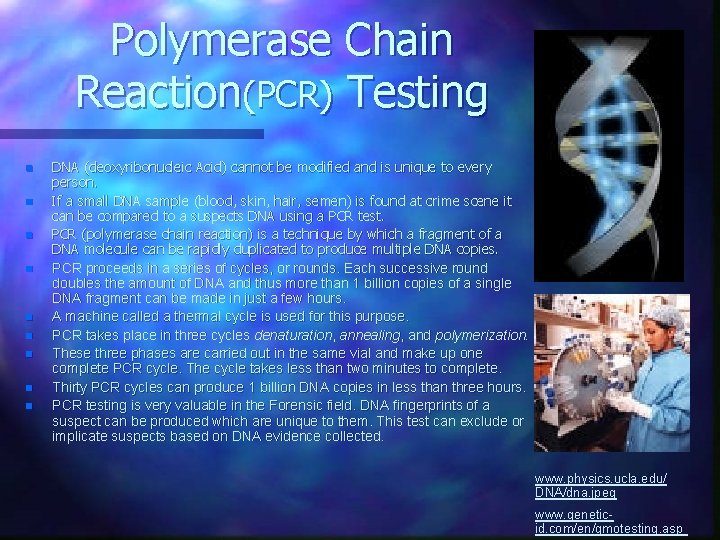
Polymerase Chain Reaction(PCR) Testing n n n n n DNA (deoxyribonucleic Acid) cannot be modified and is unique to every person. If a small DNA sample (blood, skin, hair, semen) is found at crime scene it can be compared to a suspects DNA using a PCR test. PCR (polymerase chain reaction) is a technique by which a fragment of a DNA molecule can be rapidly duplicated to produce multiple DNA copies. PCR proceeds in a series of cycles, or rounds. Each successive round doubles the amount of DNA and thus more than 1 billion copies of a single DNA fragment can be made in just a few hours. A machine called a thermal cycle is used for this purpose. PCR takes place in three cycles denaturation, annealing, and polymerization. These three phases are carried out in the same vial and make up one complete PCR cycle. The cycle takes less than two minutes to complete. Thirty PCR cycles can produce 1 billion DNA copies in less than three hours. PCR testing is very valuable in the Forensic field. DNA fingerprints of a suspect can be produced which are unique to them. This test can exclude or implicate suspects based on DNA evidence collected. www. physics. ucla. edu/ DNA/dna. jpeg www. geneticid. com/en/gmotesting. asp
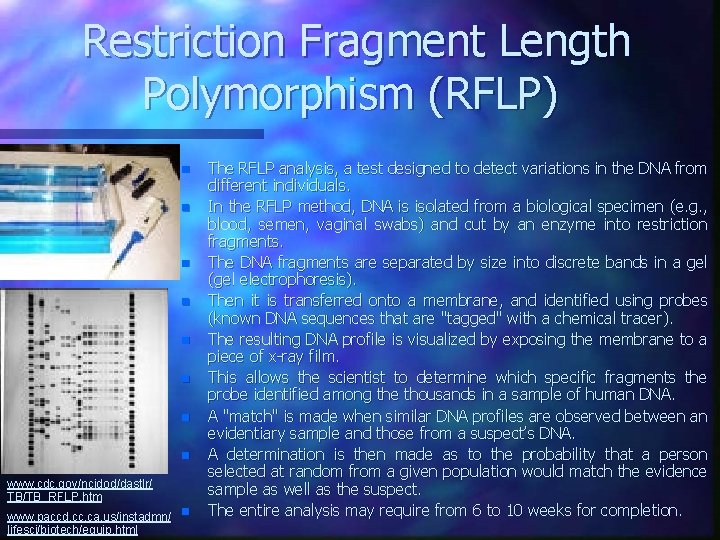
Restriction Fragment Length Polymorphism (RFLP) n n n n www. cdc. gov/ncidod/dastlr/ TB/TB_RFLP. htm www. paccd. cc. ca. us/instadmn/ n lifesci/biotech/equip. html The RFLP analysis, a test designed to detect variations in the DNA from different individuals. In the RFLP method, DNA is isolated from a biological specimen (e. g. , blood, semen, vaginal swabs) and cut by an enzyme into restriction fragments. The DNA fragments are separated by size into discrete bands in a gel (gel electrophoresis). Then it is transferred onto a membrane, and identified using probes (known DNA sequences that are "tagged" with a chemical tracer). The resulting DNA profile is visualized by exposing the membrane to a piece of x-ray film. This allows the scientist to determine which specific fragments the probe identified among the thousands in a sample of human DNA. A "match" is made when similar DNA profiles are observed between an evidentiary sample and those from a suspect’s DNA. A determination is then made as to the probability that a person selected at random from a given population would match the evidence sample as well as the suspect. The entire analysis may require from 6 to 10 weeks for completion.
Documentation Examination Document examination consists of three processes: n Letter Examination n Handwriting Analysis n Ink Analysis www. bellevuesquare. com/ aboutus/feedback. cfm www. writersmanual. com/ article 1093. html www. exn. ca/forensics/ documents. cfm
Letter Examination n Establishing the location at which a letter was postmarked can be determined by examining the post office stamp placed on the envelope. n The person responsible for mailing the letter can be identified by: – trace evidence, such as DNA taken from saliva, – hair samples, – fingerprints. www. co. san-diego. ca. us/. . . /sheriff/ patrol/lab 1. html
Handwriting Analysis Must be done by a trained and licensed examiner. n www. michigansipsig. match. org/ abouthub 4. htm n An analysis of the graphics of print and cursive writing must be conducted. n A person’s handwriting depends on his/her habits and mannerisms. n No two genuine handwritten words or signatures made by one person are identical. This is because we do not have machine-like precisions in the human body. n Handwriting changes dependent upon a person’s mood, physical condition, muscular co-ordination and external influences.
Ink Analysis n Chemical tests are applied to samples of ink removed from a document. n The analysis is conducted by method called Thin Layer Chromatography (TLC). n This process involves examining small “plugs” of ink, adding a solvent to dissolve the ink, and placing it on a performance plate. n In a developing chamber, a solvent system migrates www. co. san-diego. ca. us/. . . /sheriff/ up the plate and components of the ink separate it into patrol/lab 1. html distinct bands of colors. n The procedure can help establish if a letter has been contaminated with or altered after a particular signature.
Laboratory Policy Collection and Processing of Physical Evidence n n n n n Processing a biological crime scene Specialists responding to a suspected bioterrorist attack gather evidence to conduct a simultaneous medical and criminal investigation. FBI agents trained in the science of germ warfare lead the investigation. Safety in containment Lab scientists and investigators follow safety procedures. Cleaning up Evacuees are decontaminated, then washed with detergent or bleach and water. Most clothing is collected for evidence. (rest is destroyed). Hunting for clues Field tests, including a quick look at a microbe’s DNA can yield preliminary results within hours. All evidence is bagged and tagged, following a strict “chain of custody” procedure that connects evidence to its origins. Hand-held devices suck up ambient air and test it for floating microbes. Air systems that could circulate microbes are shut down and scrapings taken from filters. Examination under the microscope A lab network is set up for various levels of testing – hospitals can grow and analyze bacteria cultures while at the most specialized level, labs at the Centers for Disease Control and Prevention can identify unusual or exotic germ.
US Current Counterterrorism Policy n Make no concessions to terrorists and strike no deals with terrorists. n Bring terrorists to justice for their crimes. n Isolate and apply pressure on states that sponsor terrorism to force them to change their behavior. n Bolster the counter terrorism capabilities of those countries that work with the US and require assistance. www. americasunknownchild. net/summary. htm
Overt Response to Potential Bioterrorist Attacks § Law enforcement makes the necessary notification to public health: the public is made aware of the release of an agent. § There is immediate local law enforcement response, including local police, fire and emergency response medical service(EMS). § The FBI Weapons of Mass Destruction (WMD) Coordinator is notified and dispatched to the scene, where with the first responders in the community, he helps coordinate the assessment of the threat. § The FBI investigates threats - response protocol includes securing crime scene, initiating the FBI’s interagency threat assessment process. § The FBI’s Counterterrorism Division at FBI headquarters coordinates threat assessment to assess the credibility of the threat received, immediate concerns involving health and safety of responding personal, and the requisite level of response warranted by the federal government. § Centers for Disease Control and Prevention (CDC), Department of Health and Human Services(DHHS) , Unites States Department of Agriculture(USDA) and the Food and Drug Administration(FDA) are key agencies the FBI calls upon to assist in assessing the threat. § Threat assessment can range from full federal response if threat is credible to collection of material in an effort to rule out the presence to rule out any biological material if threat deemed not credible. § Suspect materials are collected, screened, and packaged by state and local Hazmut teams according to the method established by FBI’s Hazardous Material Response Unit (HMRU).
Covert Response to Potential Bioterrorist Attacks § Notification to law enforcement is made by the public health sector encouraging sharing of information between criminal and epidemiological investigators. § The FBI assumes primary authority in conducting investigation and analyzing evidence collected, while Public Health maintains responsibility for health and welfare of citizens. § At the local level, involving the FBI WMD Coordinator, the sate or local public health department and at the national level between FBI headquarters and the CDC coordinator, effective coordination is accomplished to address requisite roles and responsibilities of each agency. § The response to actual threat or one that is later determined to be not credible or a hoax, is the same.
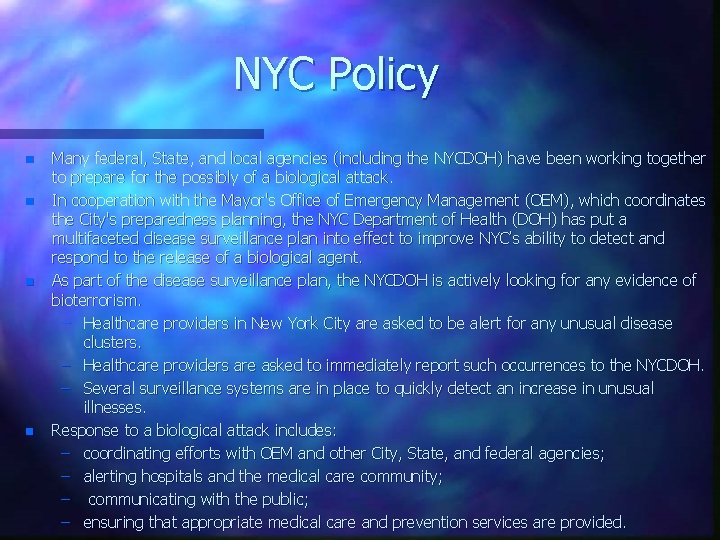
NYC Policy n n Many federal, State, and local agencies (including the NYCDOH) have been working together to prepare for the possibly of a biological attack. In cooperation with the Mayor's Office of Emergency Management (OEM), which coordinates the City's preparedness planning, the NYC Department of Health (DOH) has put a multifaceted disease surveillance plan into effect to improve NYC’s ability to detect and respond to the release of a biological agent. As part of the disease surveillance plan, the NYCDOH is actively looking for any evidence of bioterrorism. – Healthcare providers in New York City are asked to be alert for any unusual disease clusters. – Healthcare providers are asked to immediately report such occurrences to the NYCDOH. – Several surveillance systems are in place to quickly detect an increase in unusual illnesses. Response to a biological attack includes: – coordinating efforts with OEM and other City, State, and federal agencies; – alerting hospitals and the medical care community; – communicating with the public; – ensuring that appropriate medical care and prevention services are provided.
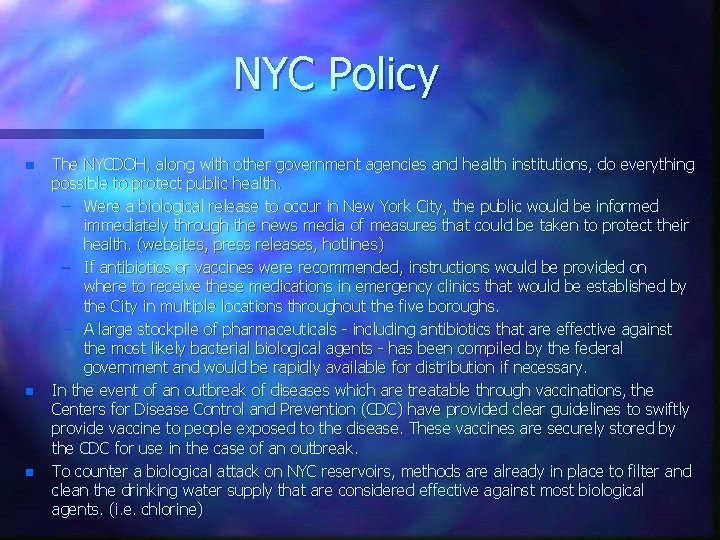
NYC Policy n n n The NYCDOH, along with other government agencies and health institutions, do everything possible to protect public health. – Were a biological release to occur in New York City, the public would be informed immediately through the news media of measures that could be taken to protect their health. (websites, press releases, hotlines) – If antibiotics or vaccines were recommended, instructions would be provided on where to receive these medications in emergency clinics that would be established by the City in multiple locations throughout the five boroughs. – A large stockpile of pharmaceuticals - including antibiotics that are effective against the most likely bacterial biological agents - has been compiled by the federal government and would be rapidly available for distribution if necessary. In the event of an outbreak of diseases which are treatable through vaccinations, the Centers for Disease Control and Prevention (CDC) have provided clear guidelines to swiftly provide vaccine to people exposed to the disease. These vaccines are securely stored by the CDC for use in the case of an outbreak. To counter a biological attack on NYC reservoirs, methods are already in place to filter and clean the drinking water supply that are considered effective against most biological agents. (i. e. chlorine)
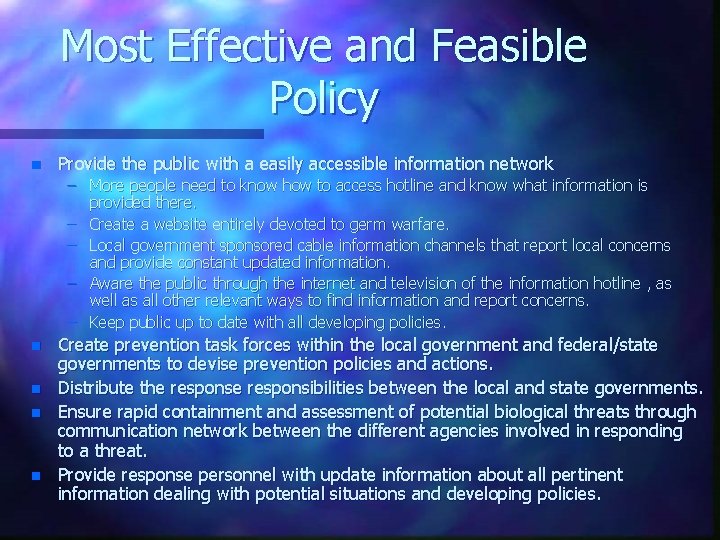
Most Effective and Feasible Policy n Provide the public with a easily accessible information network – More people need to know how to access hotline and know what information is provided there. – Create a website entirely devoted to germ warfare. – Local government sponsored cable information channels that report local concerns and provide constant updated information. – Aware the public through the internet and television of the information hotline , as well as all other relevant ways to find information and report concerns. – Keep public up to date with all developing policies. n n Create prevention task forces within the local government and federal/state governments to devise prevention policies and actions. Distribute the responsibilities between the local and state governments. Ensure rapid containment and assessment of potential biological threats through communication network between the different agencies involved in responding to a threat. Provide response personnel with update information about all pertinent information dealing with potential situations and developing policies.
References n n Cover References http: //www. stg. srs. com/ CBW/threat. htm http: // www. cnn. com/2000/US/01/ 07/anthrax. indictment/ http: // www. cnn. com/US/9804/14/ infectious. threats/ http: // www. vetmed. ucdavis. edu/whc/ Necropsy/General. html http: // www. nasca. org. uk/Strange_Maps/ germwarfare/germwarfare. html http: //www. russiajournal. com/news/ rj_news. shtml? nd=1070 Slide 2 http: //home. earthlink. net/~bkonop/Germ. Incidents 2. html http: //www. emergency. com/1999/alibek 99. html Slides 3 - 4 http: //www. cdn-friends-cej. ca/medigest/mar 97/backgrnd. html http: //www. poynter. org http: //www. bt. cdc. gov Slide 5 http: //www. llnl. gpv/str/pdfs/05 00. 1. pdf http: //www. asmusa. org/pcsrc/cmr 364. pdf
References n n n Slide 5 cont http: //www. bt. cdc. gov/Documents. App/Anthrax/10122001 Handle /1012001. asp Slide 6 http: //www. bt. cdc. gov/Documents. App/Facts. About/asp http: //www. thename. org/career/htm Slide 7 http: //www. ph. ucla. edu/epi. bioter/anthapha_id_a. html http: //www. biology. washington. edu/fingerprint/dnaintro. html http: //www. psu. edu/dept/police/technology/html Slide 8 [1]"Polymerase Chain Reaction, " Microsoft® Encarta® Encyclopedia 99. © 1993 -1998 Microsoft Corporation. All rights reserved. http: //www. scientific. org/tutorials/articles/riley. html Slides 9 – 10 http: //www. ndsu. nodak. edu/instruct/mcclean/plsc 731/mapping/ mapping 1. html http: //science. kennesaw. edu/~rrascati/biol 4415/rflp. htm Slides 11 - 13 http: // www. fdeservices. com http: // www. cxp. ca/forensic/ink. exp
References n n n Slide 14 http: //CDC Update: investigtionof bioterrorism-related anthrax and interimguidelinesfor exposure management and antimicrobial therapy, October 20001. MMWR 2001; 50: 909 http: //inceftionconrtol. uscfmedicalcenter. org/What_s_New/Anthrax_ Exposure_Guidelines/anthrax+exposure_guidelines. html http: //medicine. uscf. edu/EM/Other. Dept. Policy/DHSAnthrax. html Slides 15 -17 http: //www. nyc. gov/html/doh/html/cd/abio 5. html http: //www. nyc. gov/html/doh/html/cd/abio 4. html htto: //www. usamriid. army. mil/education/bluebook. html http: // www. hopkins-biodefense. org Slides 18 - 19 http: //www. nyc. gov/html/doh/html/cd/wtc 8. html
Credits The Bronx High School of Science Teacher: Ms. Mary Villani Class Code: SBF 6 -05 2001 - 2002 Student Leaders: Francis, Kwesi Marra, John Papakostas, Sofia Shpolyansky, Evelina Skiba, Carolyn Production Staff: Abreu, Juana Lau, Joanna Chow, Ming Chieh Mc. Elfresh, Paul Chu, Michael Merritt, Busisiwe Connor, David Ochakovskaya, Yulia Conrad, Stephanie Picicci, Amanda Dawkins, Eivori Reynolds, Matthew Dubensky, Lyssa Rhee, Amy Furst, Cassandra Saafir, Bilal Greene, Sasha Theiroff, Amanda Heyman, Rachel Ting, Rosalind Jaime, Celmali Tisi, Lisa Karlya, Joseph Topol, Jacqueline Khan, Brandi Trainer, Cydney Koldayev, Vladimir Zaltsman, Inna Korolkoff, Lily
- Slides: 24