General Data Protection Regulations GDPR Effective 25 05

- Slides: 15

General Data Protection Regulations (GDPR) Effective 25. 05. 2018 Ian Gibbs Head of ICT Governance & Security one. Source Just Seven Things Framework 1. 2. 3. 4. 5. 6. 7. Governance & Accountability Risk Management Security Evidence Based Rights Records Management Penalties
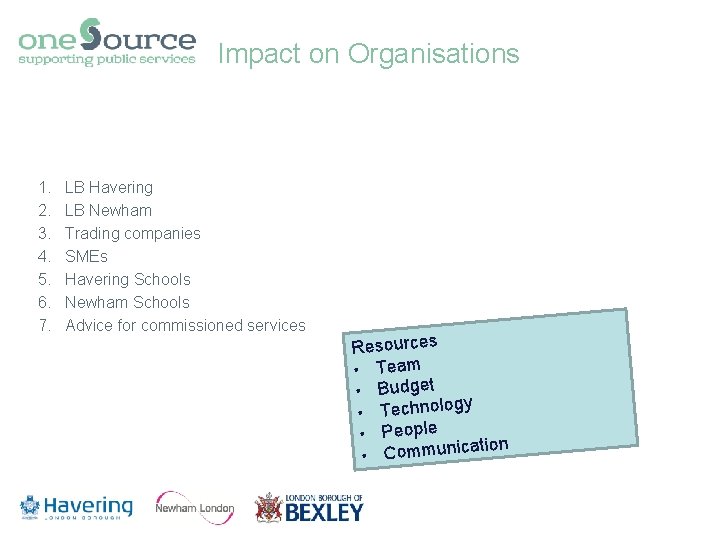
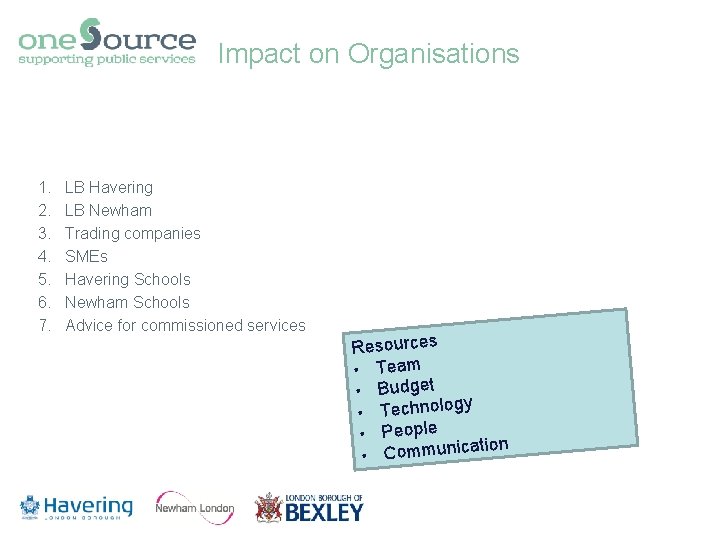
Impact on Organisations 1. 2. 3. 4. 5. 6. 7. LB Havering LB Newham Trading companies SMEs Havering Schools Newham Schools Advice for commissioned services Resources • Team • Budget y • Technolog • People ation • Communic
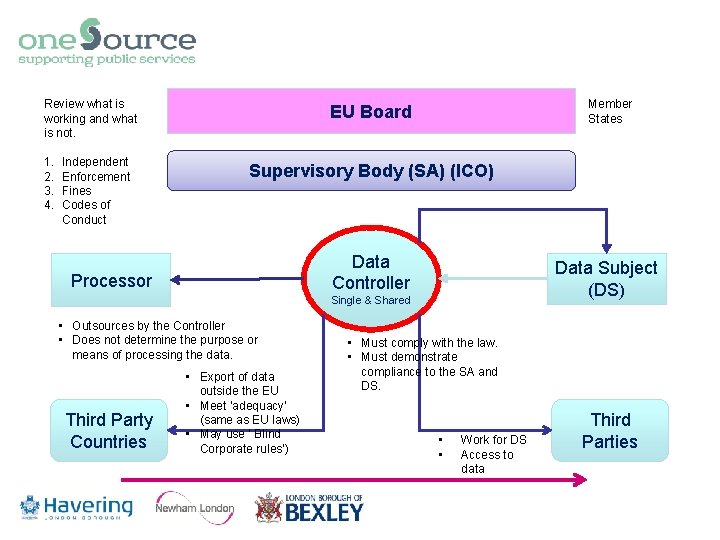
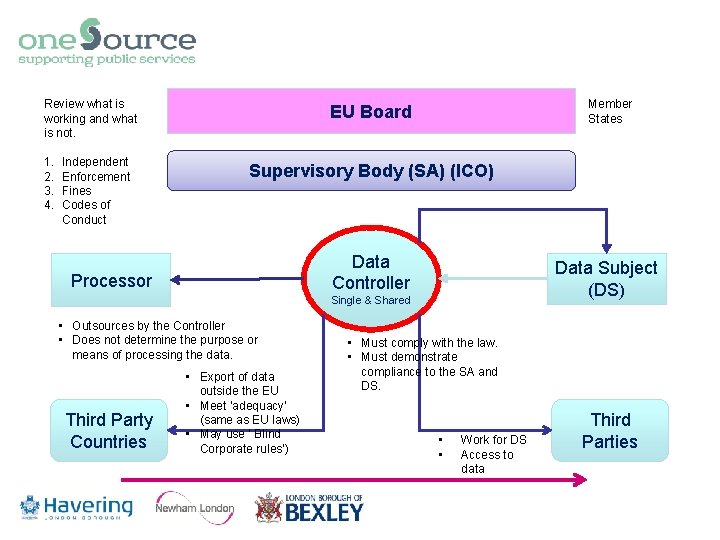
Review what is working and what is not. 1. 2. 3. 4. Independent Enforcement Fines Codes of Conduct Member States EU Board Supervisory Body (SA) (ICO) Data Controller Processor Data Subject (DS) Single & Shared • Outsources by the Controller • Does not determine the purpose or means of processing the data. Third Party Countries • Export of data outside the EU • Meet ‘adequacy’ (same as EU laws) • May use ‘ Blind Corporate rules’) • Must comply with the law. • Must demonstrate compliance to the SA and DS. • • Work for DS Access to data Third Parties
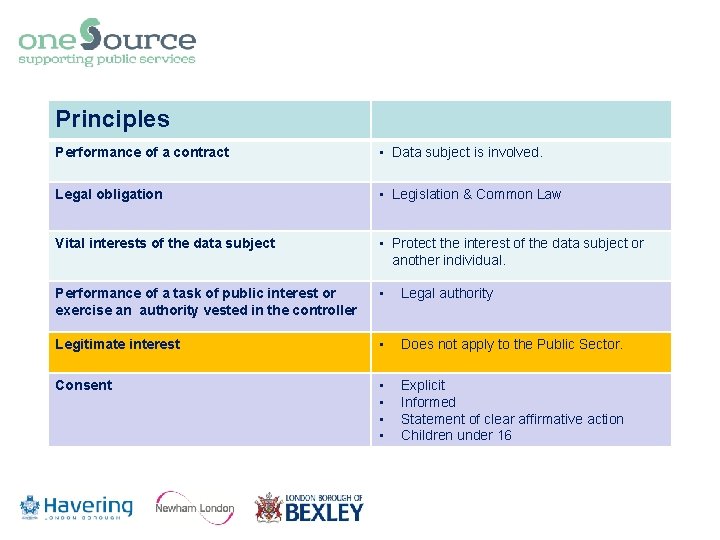
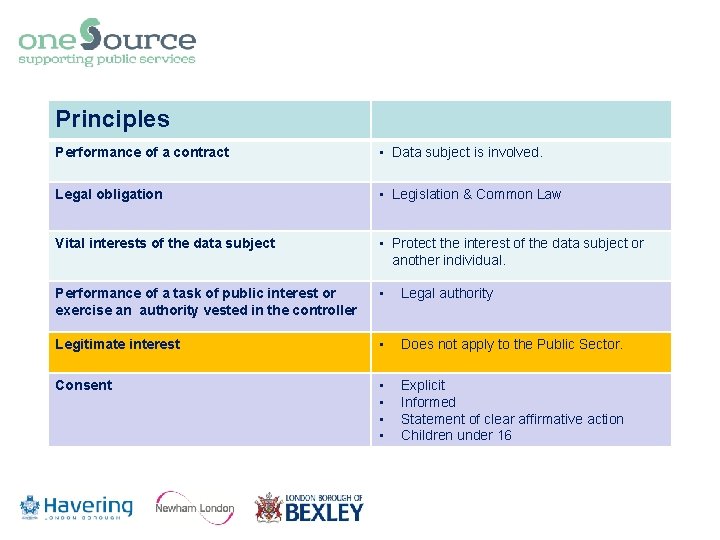
Principles Performance of a contract • Data subject is involved. Legal obligation • Legislation & Common Law Vital interests of the data subject • Protect the interest of the data subject or another individual. Performance of a task of public interest or exercise an authority vested in the controller • Legal authority Legitimate interest • Does not apply to the Public Sector. Consent • • Explicit Informed Statement of clear affirmative action Children under 16
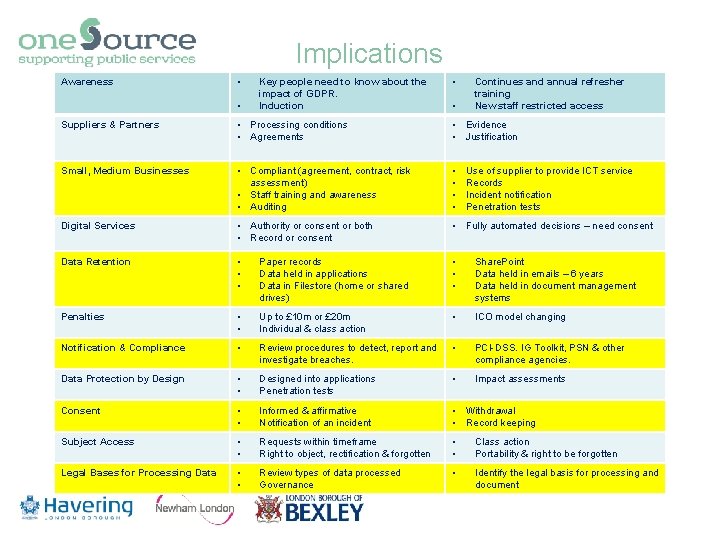
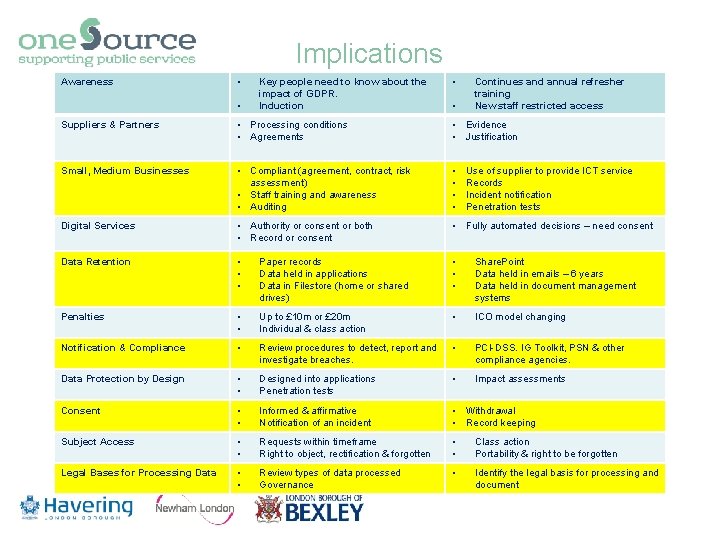
Implications Awareness • • Key people need to know about the impact of GDPR. Induction • • Continues and annual refresher training New staff restricted access Suppliers & Partners • Processing conditions • Agreements • Evidence • Justification Small, Medium Businesses • Compliant (agreement, contract, risk assessment) • Staff training and awareness • Auditing • • Digital Services • Authority or consent or both • Record or consent • Fully automated decisions – need consent Data Retention • • • Paper records Data held in applications Data in Filestore (home or shared drives) • • • Share. Point Data held in emails – 6 years Data held in document management systems Penalties • • Up to £ 10 m or £ 20 m Individual & class action • ICO model changing Notification & Compliance • Review procedures to detect, report and investigate breaches. • PCI-DSS. IG Toolkit, PSN & other compliance agencies. Data Protection by Design • • Designed into applications Penetration tests • Impact assessments Consent • • Informed & affirmative Notification of an incident • Withdrawal • Record keeping Subject Access • • Requests within timeframe Right to object, rectification & forgotten • • Class action Portability & right to be forgotten Legal Bases for Processing Data • • Review types of data processed Governance • Identify the legal basis for processing and document Use of supplier to provide ICT service Records Incident notification Penetration tests
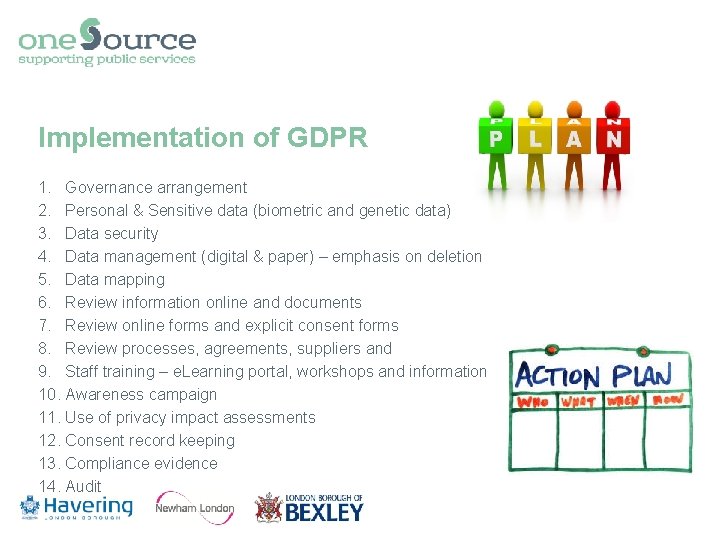
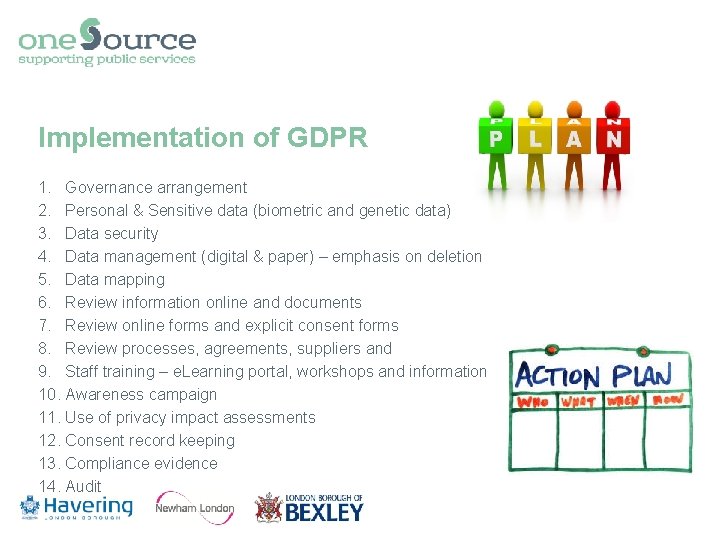
Implementation of GDPR 1. Governance arrangement 2. Personal & Sensitive data (biometric and genetic data) 3. Data security 4. Data management (digital & paper) – emphasis on deletion 5. Data mapping 6. Review information online and documents 7. Review online forms and explicit consent forms 8. Review processes, agreements, suppliers and 9. Staff training – e. Learning portal, workshops and information 10. Awareness campaign 11. Use of privacy impact assessments 12. Consent record keeping 13. Compliance evidence 14. Audit
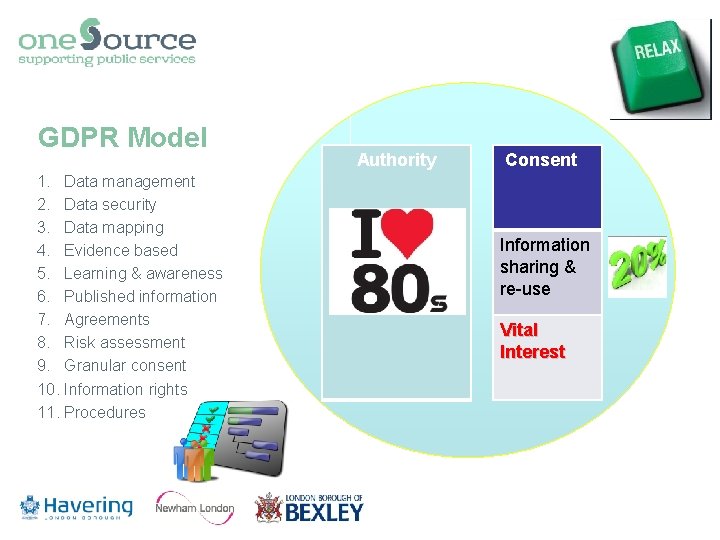
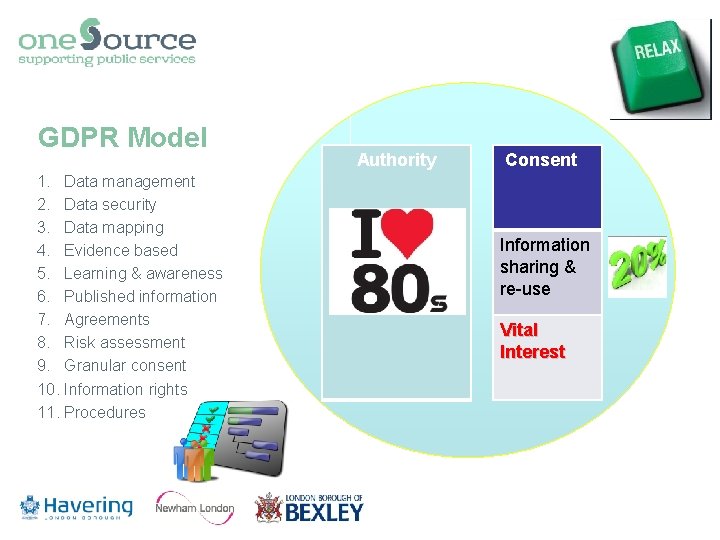
GDPR Model 1. Data management 2. Data security 3. Data mapping 4. Evidence based 5. Learning & awareness 6. Published information 7. Agreements 8. Risk assessment 9. Granular consent 10. Information rights 11. Procedures Authority Consent Information sharing & re-use Vital Interest
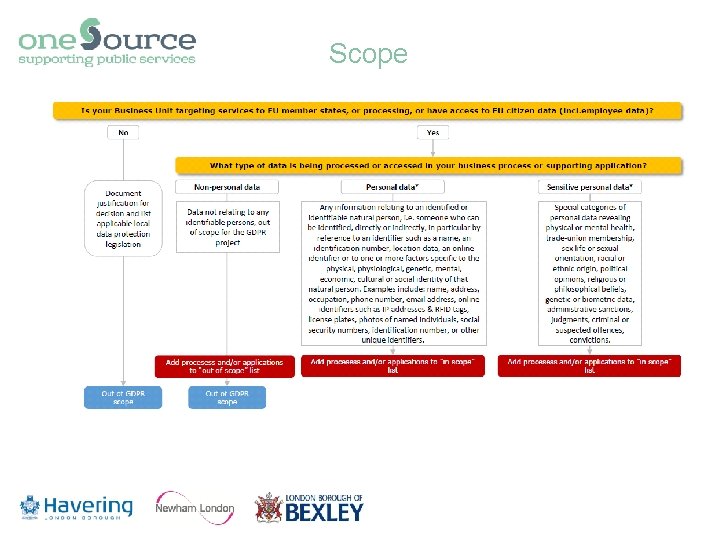
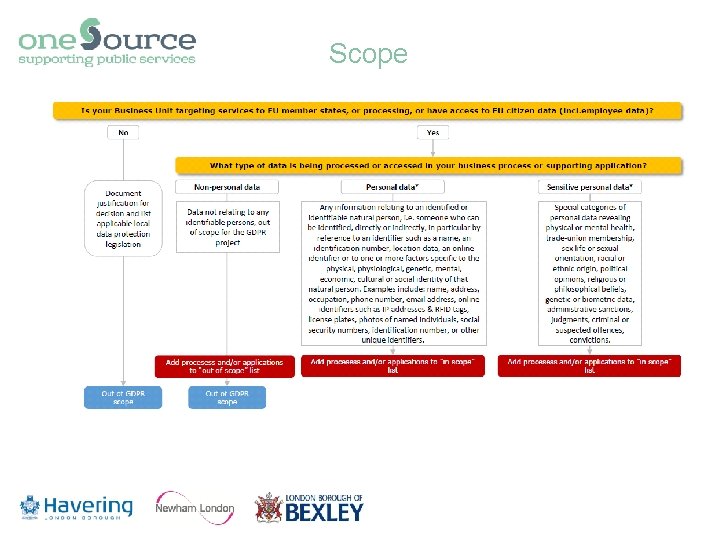
Scope
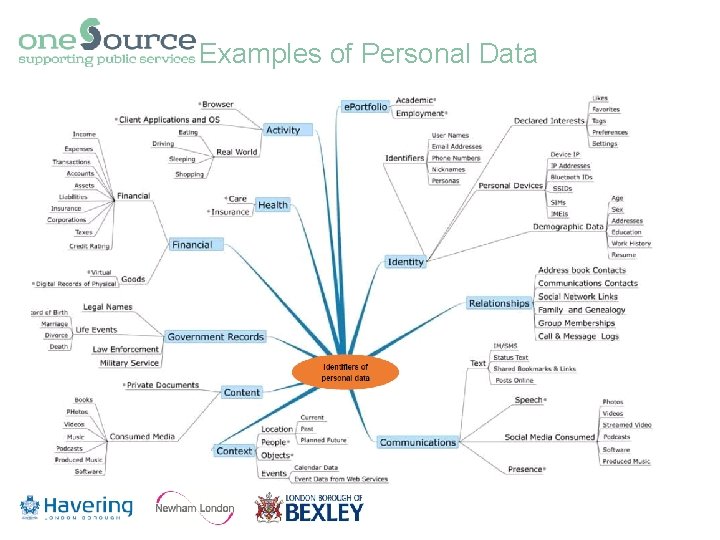
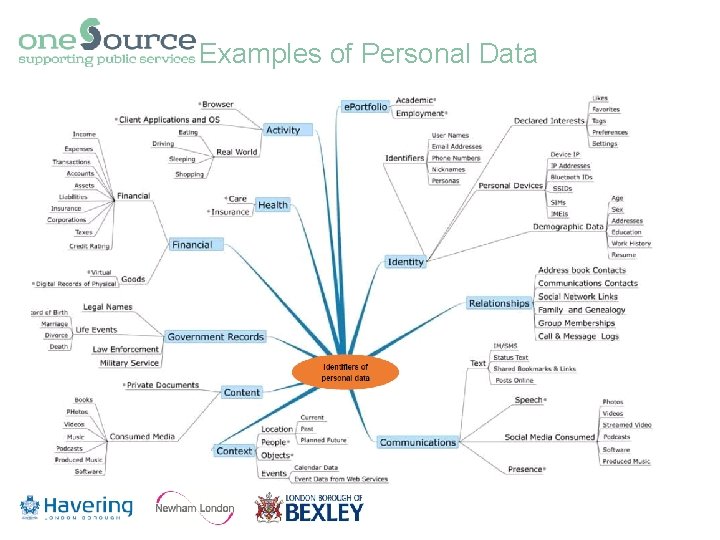
Examples of Personal Data
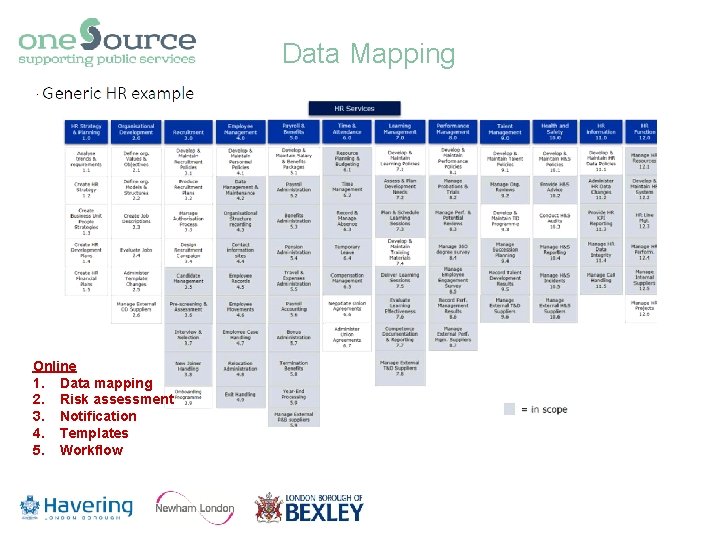
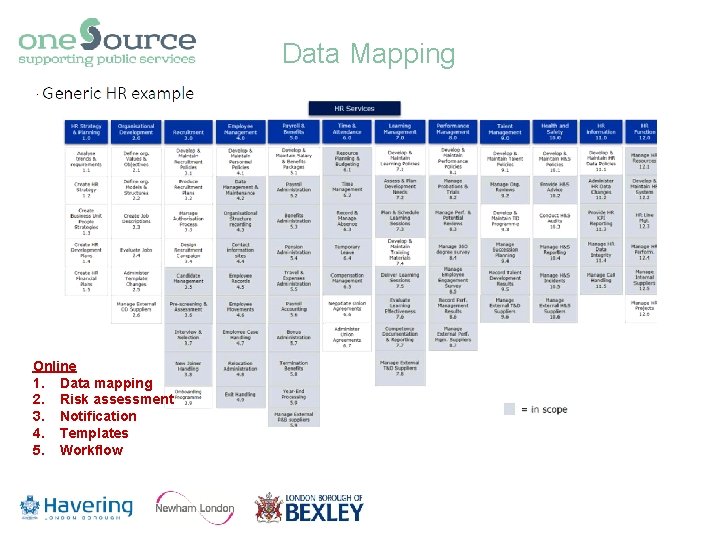
Data Mapping Online 1. Data mapping 2. Risk assessment 3. Notification 4. Templates 5. Workflow
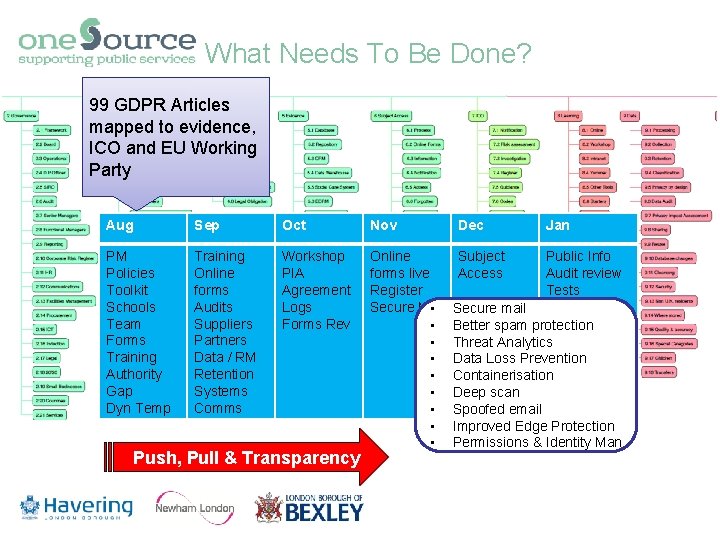
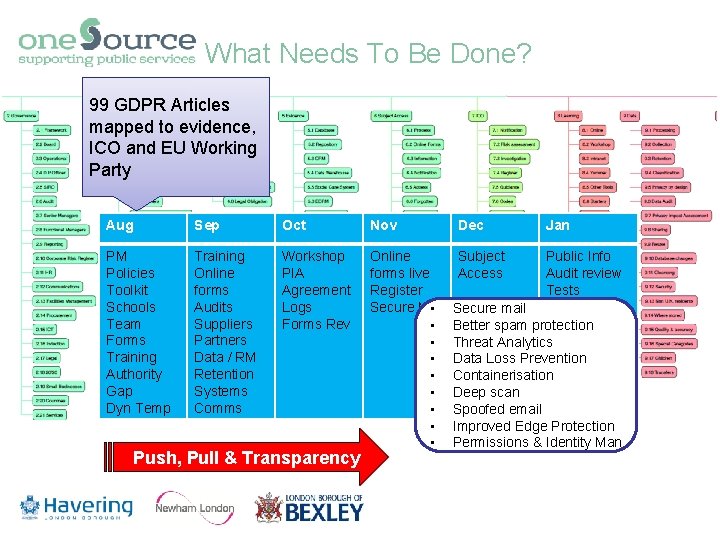
What Needs To Be Done? 99 GDPR Articles mapped to evidence, ICO and EU Working Party Aug Sep Oct Nov Dec Jan PM Policies Toolkit Schools Team Forms Training Authority Gap Dyn Temp Training Online forms Audits Suppliers Partners Data / RM Retention Systems Comms Workshop PIA Agreement Logs Forms Rev Online forms live Register Secure Mail • • • Subject Access Public Info Audit review Tests Push, Pull & Transparency Secure mail Better spam protection Threat Analytics Data Loss Prevention Containerisation Deep scan Spoofed email Improved Edge Protection Permissions & Identity Man
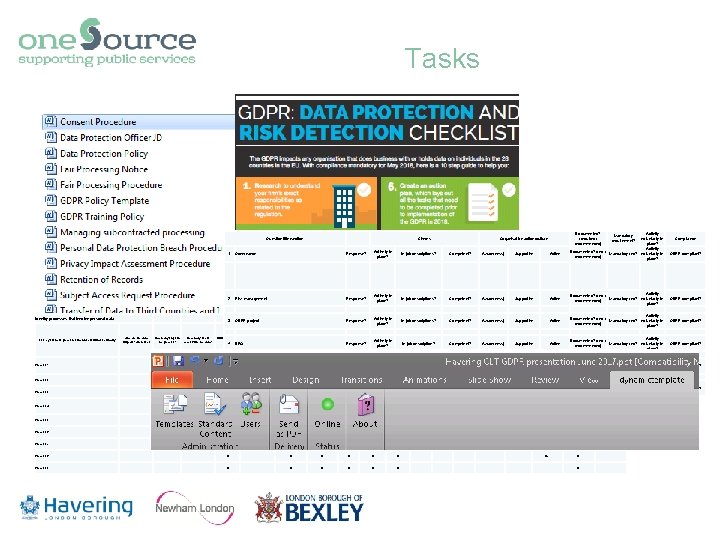
Tasks Question title/section Identify processes that involve personal data Who are the data subjects? (Describe) List key business processes in order of business criticality Process 1 How many steps in the process? How many users access/use the data? 1 Governance Response? 2 Risk management Response? 3 GDPR project Current process map? 4 DPO N 5 6 Scope of compliance Process 2 N Process 3 N Process 4 Process 5 Process 6 Process 7 Process 8 Process 9 Response? ID numbers N N N N N N N In job descriptions? N Response? NActively in N Response? place? Data formats N Recorded? Aware(ness) Competent? Data volume Are GDPR responsibilities N PDF Existing data Very high Competent? in job descriptions? N N N N N One entity Group entity N N N N N N N Supportive Uncontrolled Aware(ness) Shared? Aware(ness) Active No Supportive Third Party Yes - contract Supportive Active GDPR compliant? Activity Documented? (req. / Mandatory req? voluntarily in recommended) place? GDPR compliant? Activity Mandatory req? voluntarily in place? Transborder Automated processing? Documented? (req. / processing? recommended) No Active Compliance Activity Documented? (req. / Mandatory req? voluntarily in recommended) place? Outsourced processing? Mandatory requirement? Supportive Access control Active Activity voluntarily in place? Activity Documented? (req. / Mandatory req? voluntarily in recommended) place? Supportive Aware(ness) Competent? Active Data source In job description? Supportive place? Competent? In job descriptions? Financial data Special categories Actively in Children's Aware(ness) Response? Competent? Actively in place? Data categories Personal data In job descriptions? Actively in place? Documented? (required / recommended) Organisation action/culture Joint controller Roles and responsibilities Actively in place? Organisation's status Checks GDPR compliant? Activity Documented? (req. / N Y - EEA Mandatory req? voluntarily in recommended) place? N Activity Documented? (req. / Mandatory req? voluntarily in recommended) N place? No Yes, contract unknown N No N N GDPR compliant?
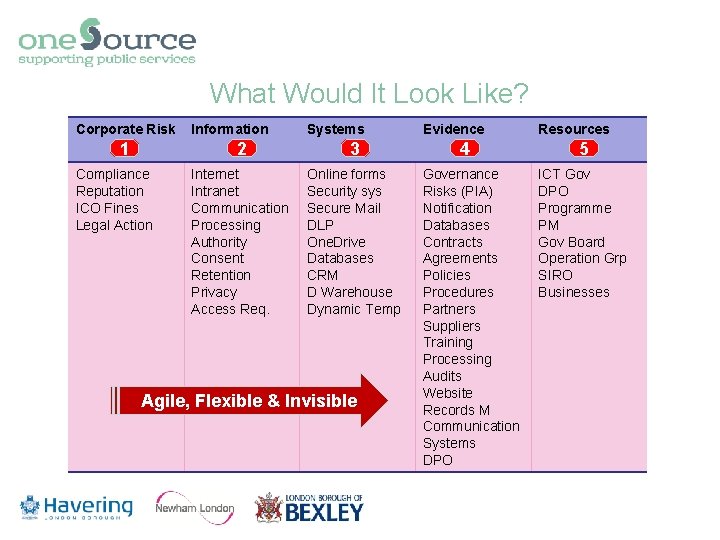
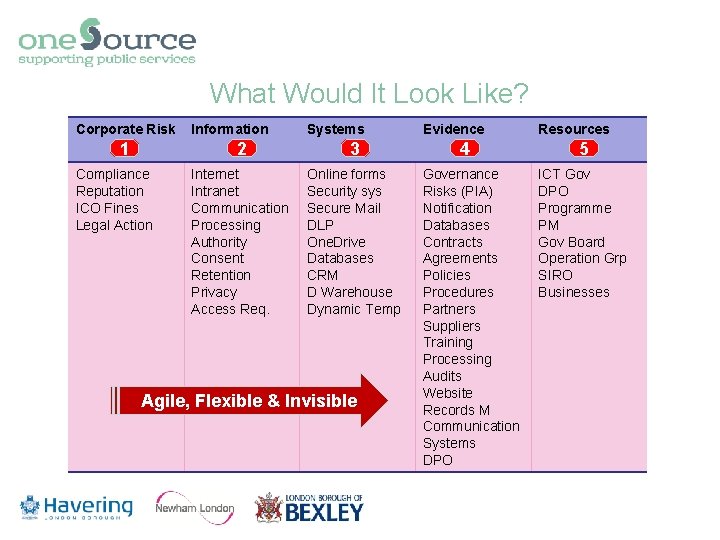
What Would It Look Like? Corporate Risk 1 Compliance Reputation ICO Fines Legal Action Information Systems 2 3 Internet Intranet Communication Processing Authority Consent Retention Privacy Access Req. Online forms Security sys Secure Mail DLP One. Drive Databases CRM D Warehouse Dynamic Temp Agile, Flexible & Invisible Evidence 4 Governance Risks (PIA) Notification Databases Contracts Agreements Policies Procedures Partners Suppliers Training Processing Audits Website Records M Communication Systems DPO Resources 5 ICT Gov DPO Programme PM Gov Board Operation Grp SIRO Businesses
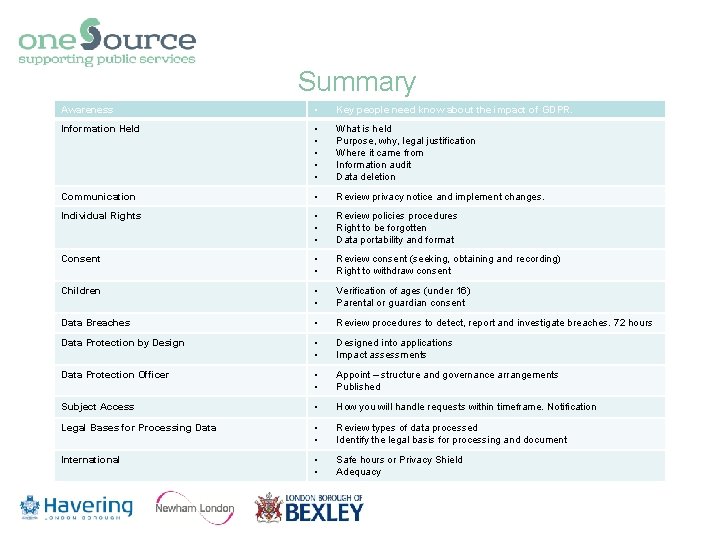
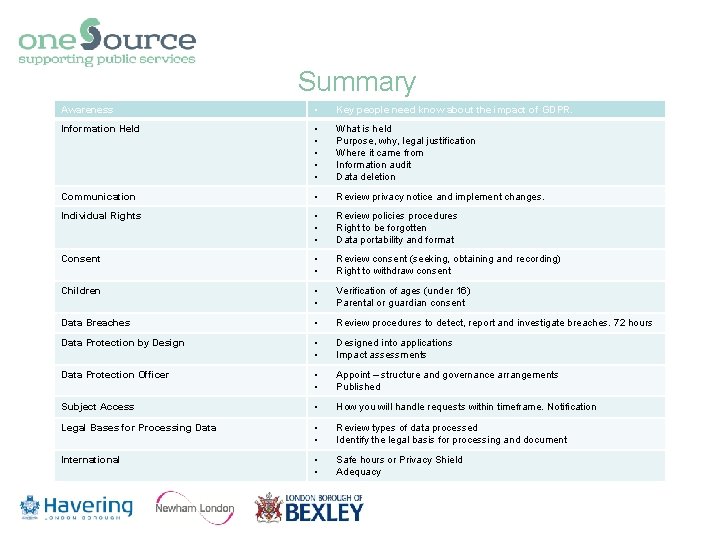
Summary Awareness • Key people need know about the impact of GDPR. Information Held • • • What is held Purpose, why, legal justification Where it came from Information audit Data deletion Communication • Review privacy notice and implement changes. Individual Rights • • • Review policies procedures Right to be forgotten Data portability and format Consent • • Review consent (seeking, obtaining and recording) Right to withdraw consent Children • • Verification of ages (under 16) Parental or guardian consent Data Breaches • Review procedures to detect, report and investigate breaches. 72 hours Data Protection by Design • • Designed into applications Impact assessments Data Protection Officer • • Appoint – structure and governance arrangements Published Subject Access • How you will handle requests within timeframe. Notification Legal Bases for Processing Data • • Review types of data processed Identify the legal basis for processing and document International • • Safe hours or Privacy Shield Adequacy
GDPR Questions Just Seven Things Framework Governance & Accountability Risk Management Security Evidence Based Rights Records Management Penalties