From Clubs and Spears to the Invisible Cloak
From Clubs and Spears to the Invisible Cloak, the Role of Technology in Weaponry Looking at the historical development, usage and technology related to weapons from 3. 5 billions years ago till present. ************************* Week 1, Nature, the maestro. . (3. 5 billions years to a few millions years) Week 2, Pre-historic and Ancient (Up to 500 AD) Week 3, Medieval to WW I (500 AD to 1914) Week 4, WW I (1914 to 1918) Week 5, WW II (1939 to 1945) Week 6, Post war, Present, Future. . (1945 to present an future)
Last Week’s Business
Question of the week True or False? The Exploratorium is the creation of Oppenheimer, the same person who was the director of Manhattan project.
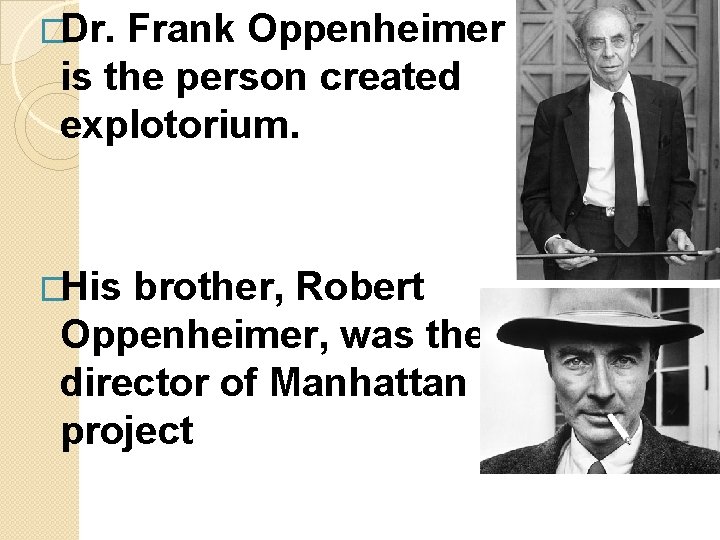
�Dr. Frank Oppenheimer is the person created explotorium. �His brother, Robert Oppenheimer, was the director of Manhattan project
�Like his brother, he was a Physicist. �Worked on Uranium enrichment as well as Manhattan project. �Shortly after WWII, while he was a professor in Colorado, he was forced to resign as a result of actions taken by the House Un-American Activities
�And 10 years as a cattle rancher in Pagosa Springs, Colorado. �He taught in a high school for a while. �In 1959, he was offered an appointment at the University of Colorado.
�Frank was invited to plan a new branch of the Smithsonian, but he declined, preferring instead to work on what he called his “San Francisco project”. �in 1969, the doors opened to Frank’s Exploratorium. Frank nurtured and shaped the growing museum until 1985,
What kind of Gyro was in the chip? �They are MEMS (Micro- Electro-Mechanical Systems).
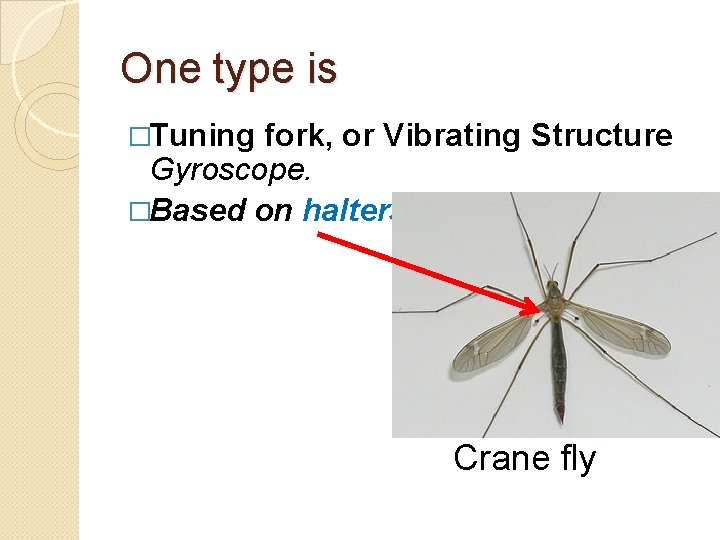
One type is �Tuning fork, or Vibrating Structure Gyroscope. �Based on halters Crane fly
How does it Work?
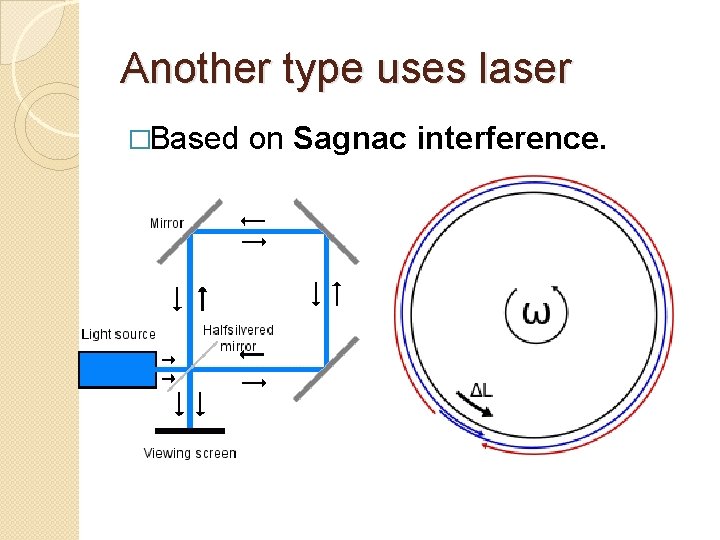
Another type uses laser �Based on Sagnac interference.
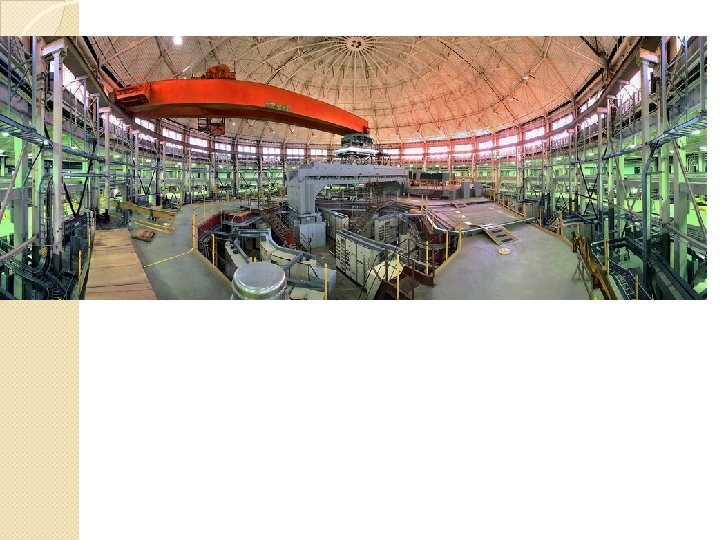
TVA (Tennessee Valley Authority) connection �Advanced Light Source, ALS visit. �Built from 1987 to 1993. �Formerly Lawrence Berkeley Lab, housing 184 inch Cyclotron.
What was the question again? ! �TVA (Tennessee Valley Authority) connection?
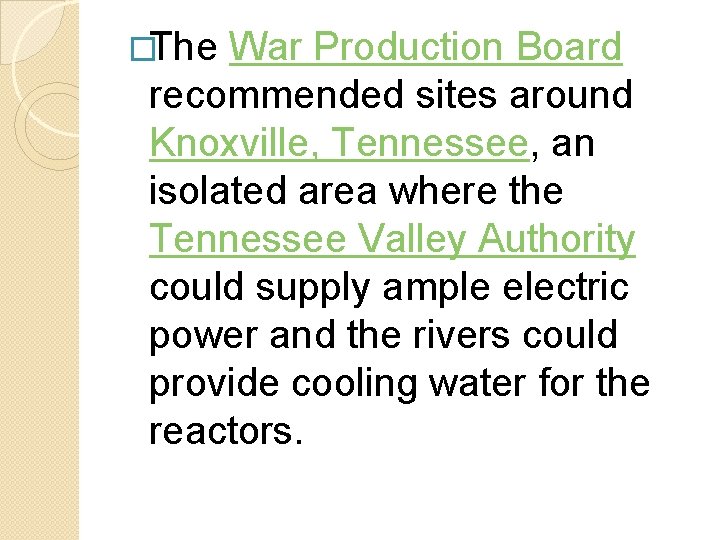
�The War Production Board recommended sites around Knoxville, Tennessee, an isolated area where the Tennessee Valley Authority could supply ample electric power and the rivers could provide cooling water for the reactors.
�Many residents came home to find eviction notices tacked to their doors. �Most were given six weeks to evacuate �Several had as little as two weeks. �Some were even forced out before they received compensation.
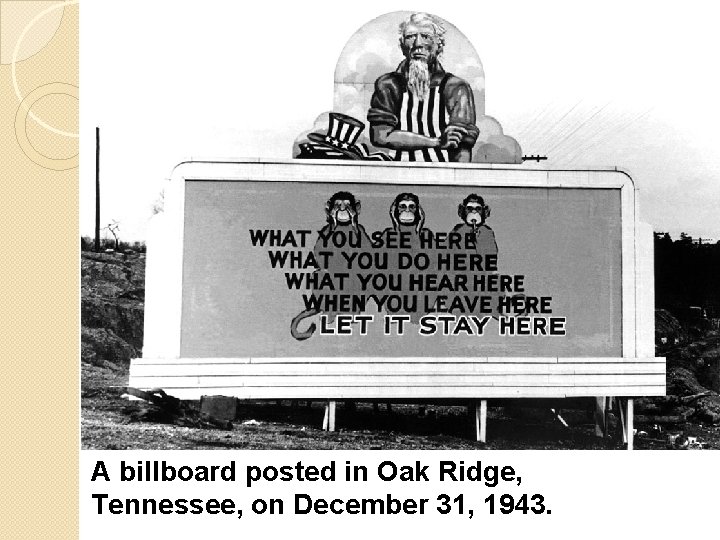
A billboard posted in Oak Ridge, Tennessee, on December 31, 1943.
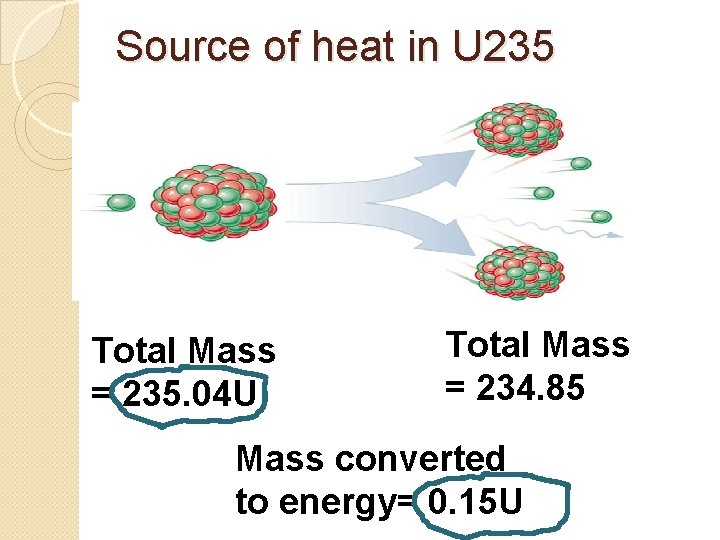
Source of heat in U 235 Total Mass = 235. 04 U Total Mass = 234. 85 Mass converted to energy= 0. 15 U
2 E = m. C 8 m/s C=3 x 10
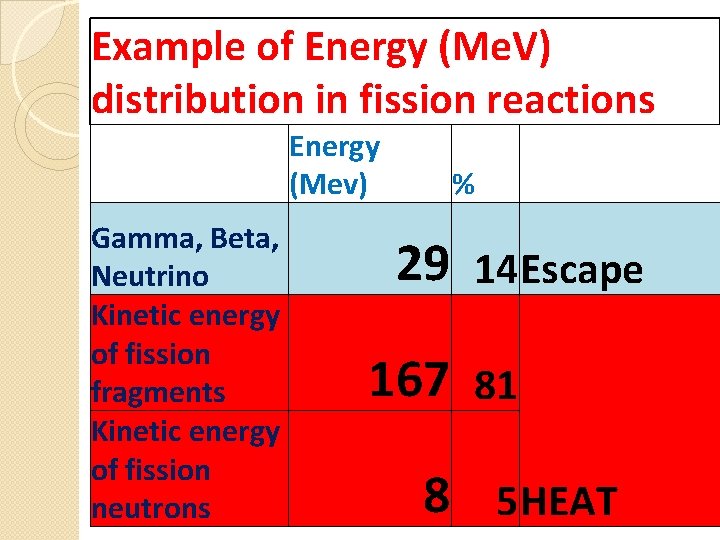
Example of Energy (Me. V) distribution in fission reactions Gamma, Beta, Neutrino Kinetic energy of fission fragments Kinetic energy of fission neutrons Energy (Mev) % 29 14 Escape 167 81 8 5 HEAT
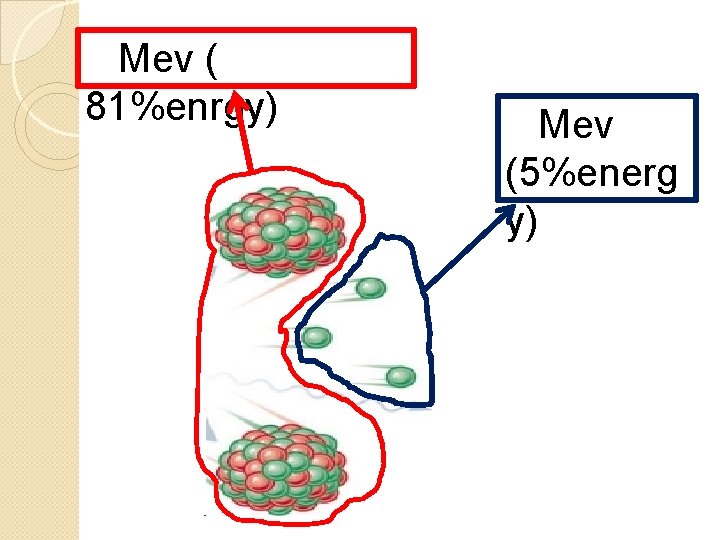
Mev ( 81%enrgy) Mev (5%energ y)
How much is 200 MEV? �Energy required to lift a grain of sand by 1 mm! �Not impressive? That is just one atom.
�When 1 KG U 235 completes the fission, it looses 0. 8 grams of its mass (size of sesame seed). �But energy produced is enough to lift the Empire State Building (365000 tons) by 20 miles!
Nuclear Fission Confirmed as Source of More than Half of Earth’s Heat. By: David Biello | July 18, 2011
Hollywood take on Carrier landing �Sent by Jon Frieseke � http: //www. youtube. com/watch? v=z. CK 0 VQKSfwc
Article from Smithsonian �Feb 2013, “the little bang” �The first rocket was firework made from bamboo tube, early 12 th century in China. �This is earlier than previous date of 1232. �Nicknamed “ground rat”.
�Week 6, Post war, Present, Future. . (1945 to present and future)
Will there be another WW? �I know not with what weapons World War III will be fought, but World War IV will be fought with sticks and stones. Albert Einstein
�Political climate after the war… �Can it be regarded as extended WWIII? �Cold War: 1945 to 1991 � (45 years).
�If we compress 45 years of cold war into 3 to 4 years and specially look at “Proxy Wars” during this period:
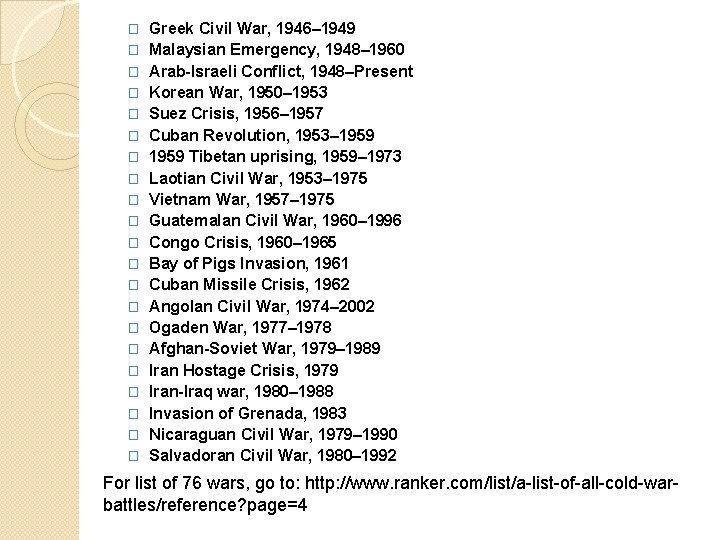
� � � � � � Greek Civil War, 1946– 1949 Malaysian Emergency, 1948– 1960 Arab-Israeli Conflict, 1948–Present Korean War, 1950– 1953 Suez Crisis, 1956– 1957 Cuban Revolution, 1953– 1959 Tibetan uprising, 1959– 1973 Laotian Civil War, 1953– 1975 Vietnam War, 1957– 1975 Guatemalan Civil War, 1960– 1996 Congo Crisis, 1960– 1965 Bay of Pigs Invasion, 1961 Cuban Missile Crisis, 1962 Angolan Civil War, 1974– 2002 Ogaden War, 1977– 1978 Afghan-Soviet War, 1979– 1989 Iran Hostage Crisis, 1979 Iran-Iraq war, 1980– 1988 Invasion of Grenada, 1983 Nicaraguan Civil War, 1979– 1990 Salvadoran Civil War, 1980– 1992 For list of 76 wars, go to: http: //www. ranker. com/list/a-list-of-all-cold-warbattles/reference? page=4
How close did we come to WWIII? �Remember Cuban missile crisis?
How about: � 1983 Soviet nuclear false alarm incident. �On September 26, 1983, the nuclear early warning system of the Soviet Union twice reported the launch of American Minuteman ICBMs from bases in the United States.
�Stanislav Yevgrafovich Petrov, an officer of the USSR, decided to do nothing! �Only three weeks earlier, the Soviet military had shot down a South Korean passenger jet that had strayed into Soviet airspace, killing all 269 people on board. �Many Americans were killed, including U. S. Congressman Larry Mc. Donald.
�It was subsequently determined that the false alarms had been created by a rare alignment of sunlight on high-altitude clouds and the satellites' Molniya orbits (highly elliptical orbits).
� There were other close calls!
Much bigger atomic and new bombs, submarines, tanks, carriers, … � Much �Even using outer space
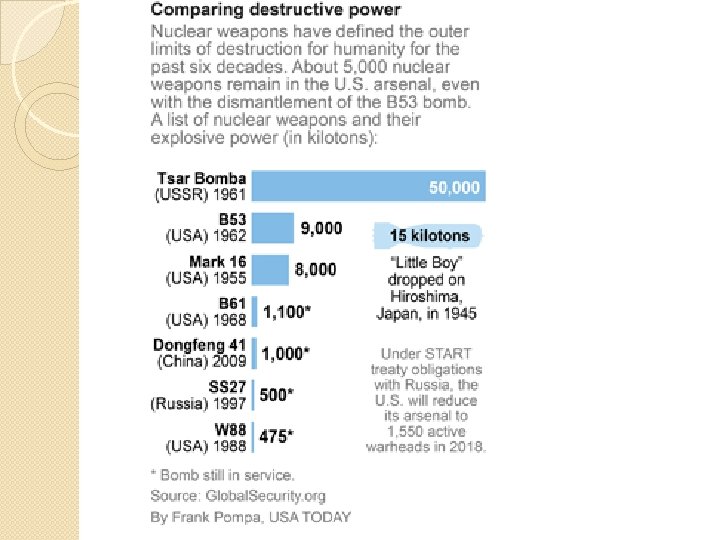
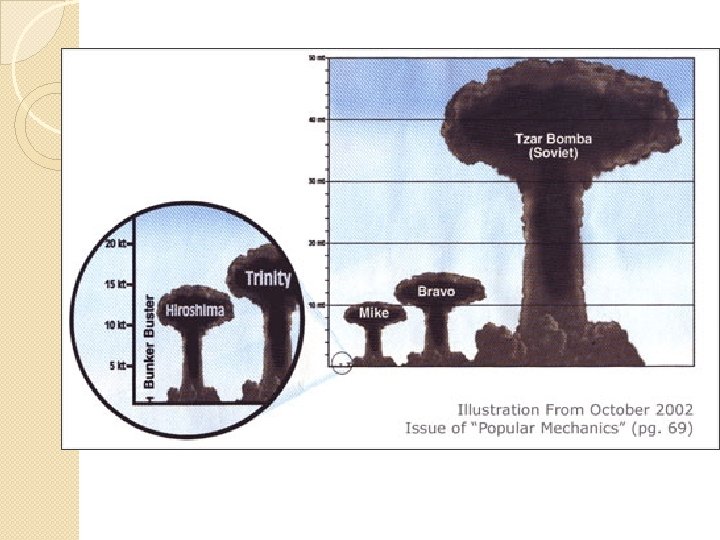
The H bomb �First tested: Nov �USSR: 1, 1952 1953 �By 1970, seven countries had H bomb.

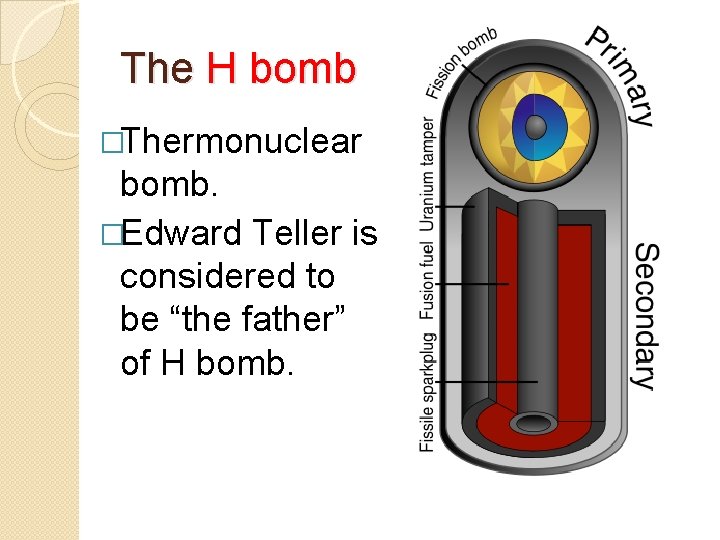
The H bomb �Thermonuclear bomb. �Edward Teller is considered to be “the father” of H bomb.
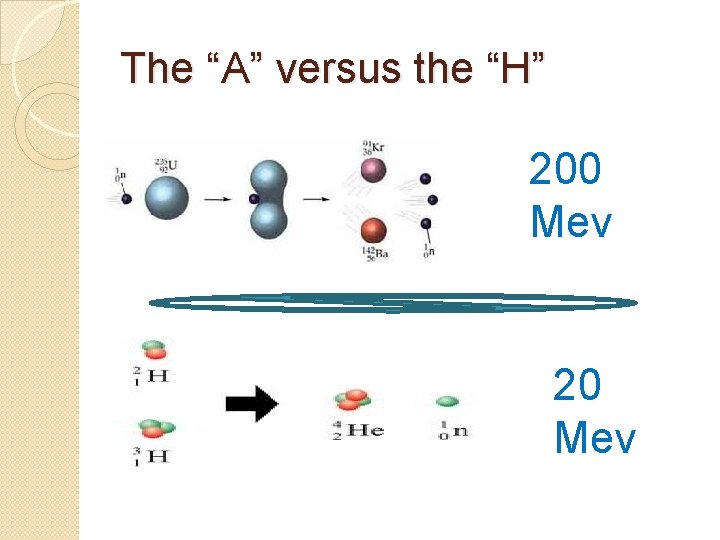
The “A” versus the “H” 200 Mev 20 Mev
Neutron bomb �Also called enhanced radiation weapon (ERW) �Is a type of thermonuclear weapon. �Designed to release a large portion of its energy as fast neutrons rather than explosive energy.
�Theoretically have no destructive advantage over a normal hydrogen bomb. �However, the intense pulse of high-energy neutrons that is generated is intended as the principal killing mechanism, not the fallout, heat or blast.
�Although neutron bombs are commonly believed to "leave the infrastructure intact", current designs have explosive yields in the kiloton range.
Explosion Footages

Advanced Weapons
Stealth Bomber �How can you make the plane invisible?
�It is invisible to RADAR. �When RADAR does not receive the echo, the object becomes invisible.
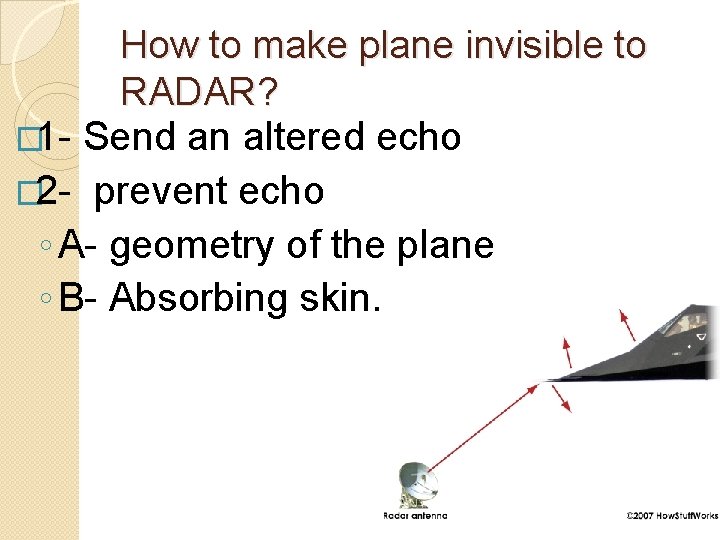
How to make plane invisible to RADAR? � 1 - Send an altered echo � 2 - prevent echo ◦ A- geometry of the plane ◦ B- Absorbing skin.

F 117 - Nighthawk
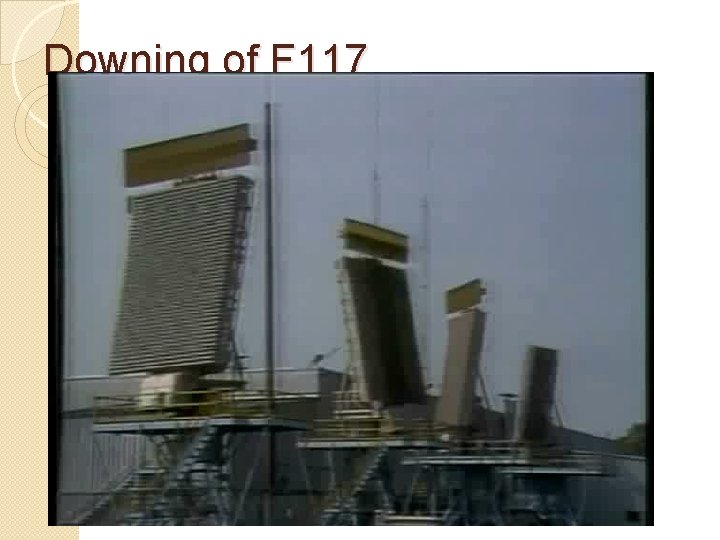
Downing of F 117
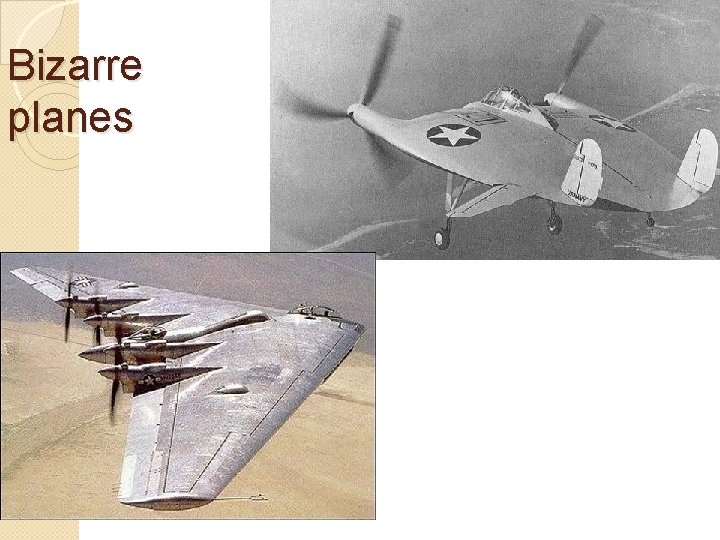
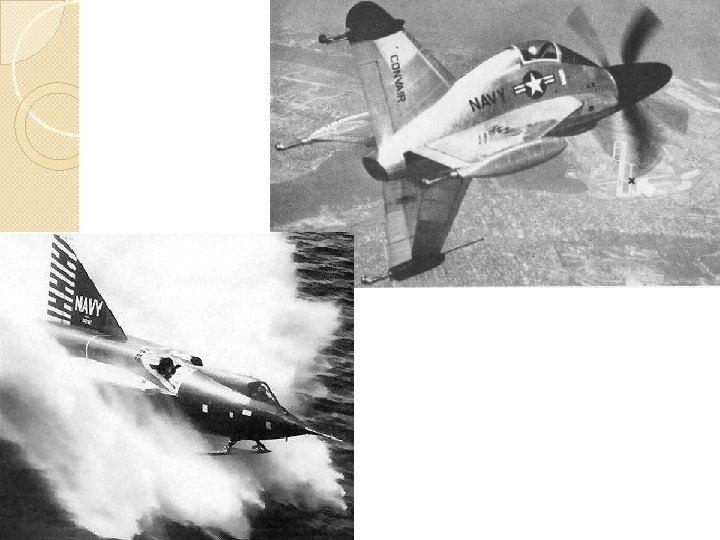
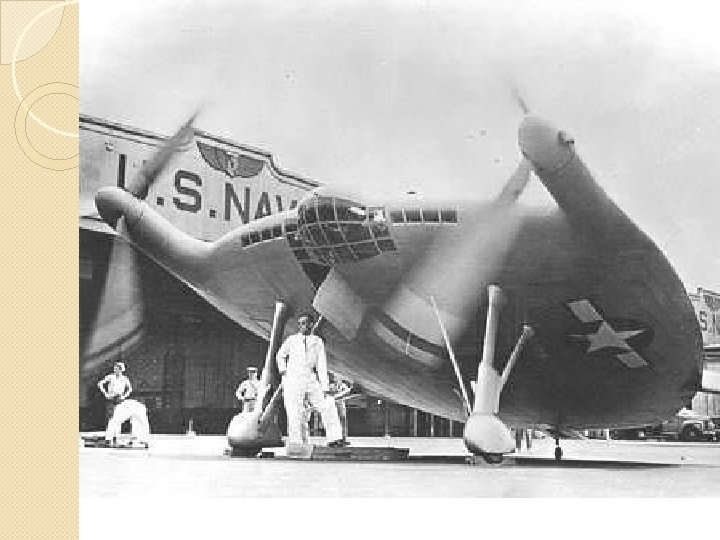
Bizarre planes

Bizarre Weapons �Corkscrew Tank
Operation Plowshare �It was to develop techniques to use nuclear explosives for peaceful construction purposes. �Program was terminated in 1977, due in large part to public opposition, after $770 million had been spent.
Sedan test to prove Plowshare feasibility.
Operation Plumbbob �Consisted of 29 explosions. �Twenty-one laboratories and government agencies were involved. �They included 43 military effects tests on civil and military structures, radiation and biomedical studies, and aircraft structural tests.
�Almost 1, 200 pigs were subjected to bio- medical experiments and blast-effects studies during Operation Plumbbob. �Approximately 18, 000 members of the U. S. Air Force, Army, Navy and Marines participated. �The military was interested in knowing how the average foot-soldier would stand up, physically and psychologically, to the rigors of the tactical nuclear battlefield.
�Plumbbob released 58, 300 kilocuries of radioiodine (I-131) into the atmosphere. �Statistically speaking, this level of exposure would be expected to eventually cause between 11, 000 and 212, 000 excess cases of thyroid cancer, leading to between 1, 000 and 20, 000 deaths
Bizarre Bombs
�(1994) "gay bomb" are informal names for a theoretical non-lethal chemical weapons. �United States Air Force research laboratory speculated about producing, which involved discharging female sex pheromones over enemy forces in order to make them sexually attracted to each other.
�It appears that a 'heavy sweating bomb', 'flatulence bomb' and 'halitosis bomb' were also considered by a committee at the time. �The plan was to make an enemy so smelly they could be quite literally sniffed out of hiding by their opponents. �It was also considered fairly damaging to the enemy's morale.
Spying, Secret Communication As old as humanity
�Greeks use Cryptography as well as Steganography. ◦ Cryptography: hide the meaning of message. ◦ Steganography: hide the message.
�Hid message under wax of wax table. �Tattooed messages into the shaved scalp of slaves. �Also used torches for signaling. �Polybius (Greek historian )used matrix of 5 x 5 to code messages.
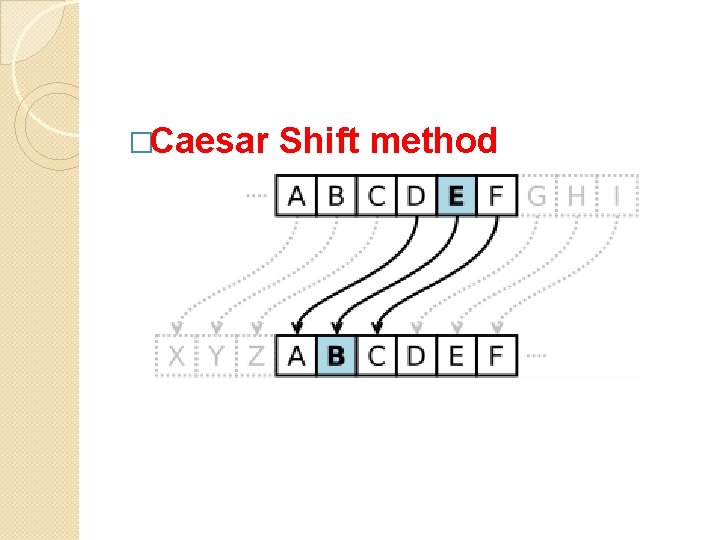
�Caesar Shift method
Phaistos Disk �Disk of fired clay from the Minoan palace of Phaistos on the Greek island of Crete �It is about 5. 9 in in diameter and covered on both sides with a spiral of stamped symbols. �Its purpose and meaning, and even its original geographical place of manufacture, remain disputed. �Is it a hoax?
�The first recorded method of “frequency analysis” of letters points to Islamic scholars in 750 AD. �For example, in English laguage, “e” occurs most often, 12% of the time. Next are t, a, . .
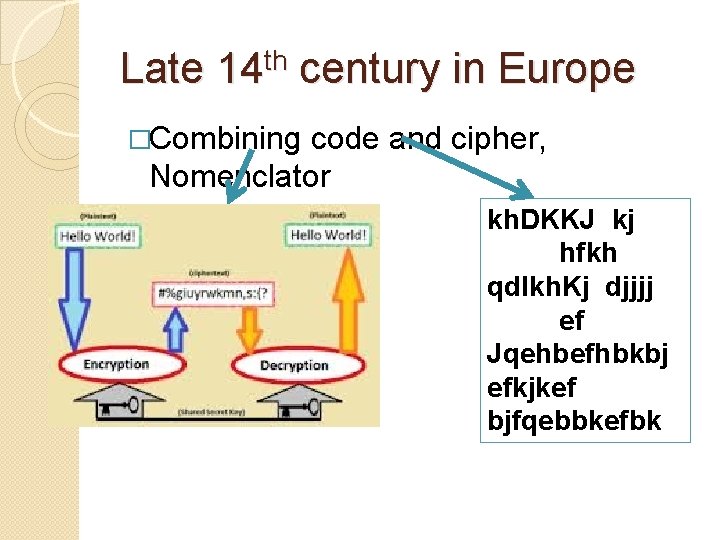
Late 14 th century in Europe �Combining code and cipher, Nomenclator kh. DKKJ kj hfkh qdlkh. Kj djjjj ef Jqehbefhbkbj efkjkef bjfqebbkefbk
�The ancient writings of Chinese and Indian military strategists contain information on deception and subversion (Psychological technique similar to 5 th column), making use of assassinations, spies and secret agents.
Hidden messages �See: � Rosslyn’s secrets � Mozart � Da Vinci
The most mysterious book �The Voynich manuscript. �dates to the early 15 th century (1404– 1438), possibly from northern Italy. �Named after the book dealer Wilfrid Voynich, who purchased it in 1912
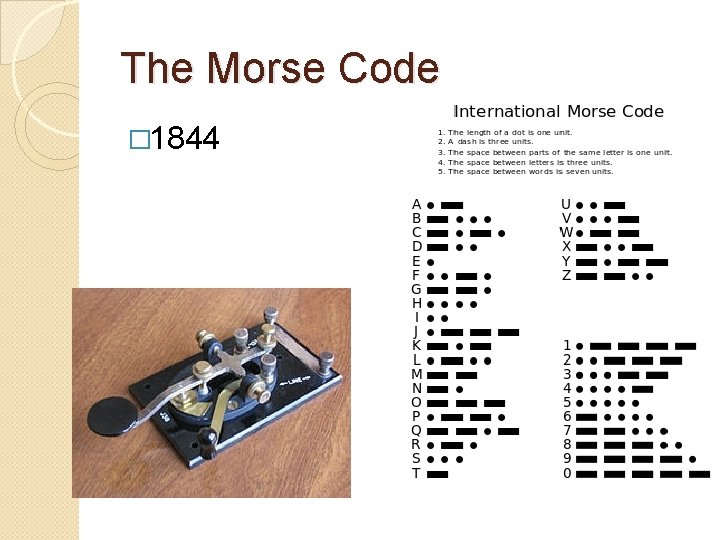
The Morse Code � 1844
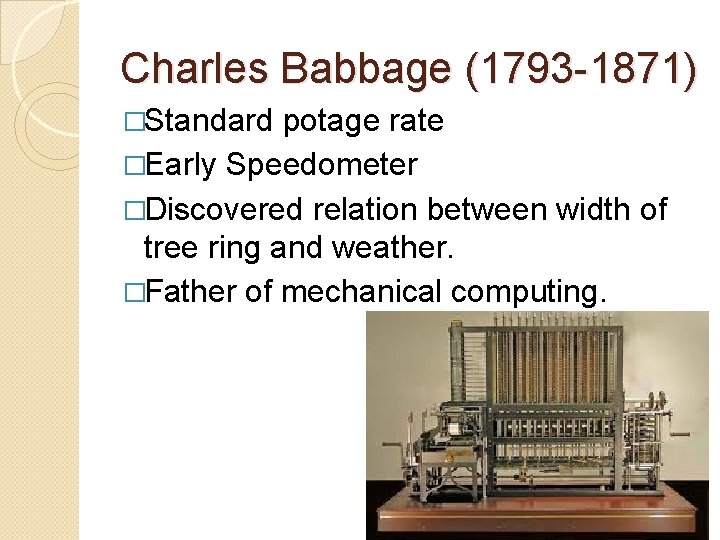
Charles Babbage (1793 -1871) �Standard potage rate �Early Speedometer �Discovered relation between width of tree ring and weather. �Father of mechanical computing.
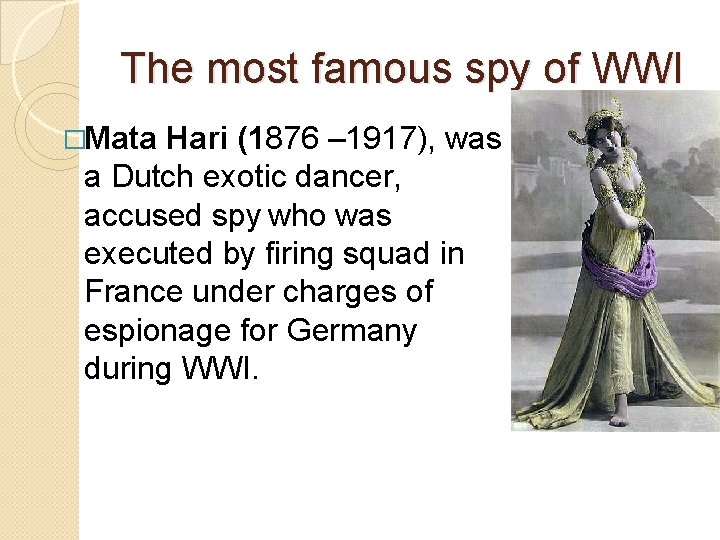
The most famous spy of WWI �Mata Hari (1876 – 1917), was a Dutch exotic dancer, accused spy who was executed by firing squad in France under charges of espionage for Germany during WWI.
Enigma Machine
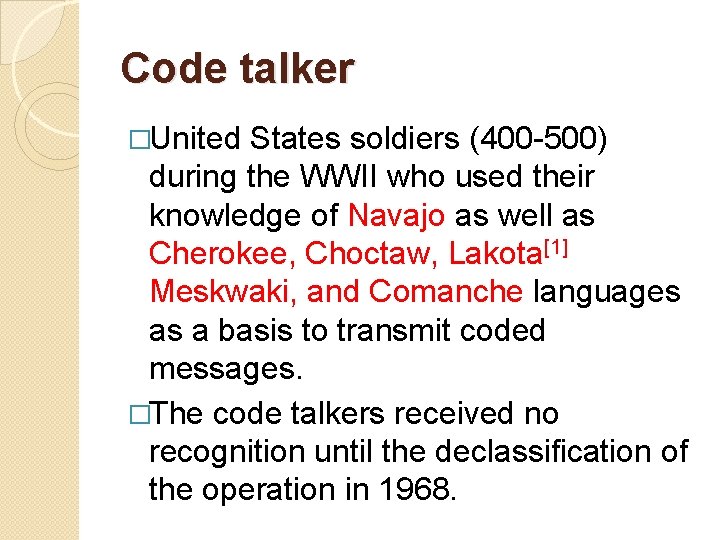
Code talker �United States soldiers (400 -500) during the WWII who used their knowledge of Navajo as well as Cherokee, Choctaw, Lakota[1] Meskwaki, and Comanche languages as a basis to transmit coded messages. �The code talkers received no recognition until the declassification of the operation in 1968.
Post war espionage, gadgets �James Bond movie do an injustice to the level of sophistication!
US embassy in Russia “the Great Transmitter” �Soon after construction began on the embassy in 1979, the State Department discovered that the Russian workers employed for the job were planting listening devices in the structure.
�U. S. officials thought that they would be able to render the bugs ineffective before the building was occupied. �But in 1985, when work on the chancery was nearly complete, they realized that hidden microphones embedded in the bricks and building materials were so numerous and so cleverly designed that there was no way to remove or neutralize them without demolishing the structure.
�The chancery became known as "the Great Transmitter" and sat unoccupied for more than a decade. �As a gesture of friendship after the 1991 breakup of the Soviet Union, Russian security services handed over the bugging plan for the building to the Americans in Moscow.
�The building originally was constructed as part of a deal in which the Soviet Union and the United States built new embassies for each other.
�After the revelation of the bugging, U. S. officials refused to let the Russians occupy their new chancery in Washington until 1994, nine years after it was completed. The remodeling work on the chancery will cost $240 million--nearly twice as much as construction of the original building. � FROM: http: //articles. latimes. com/1997/sep/26/news/mn-36452
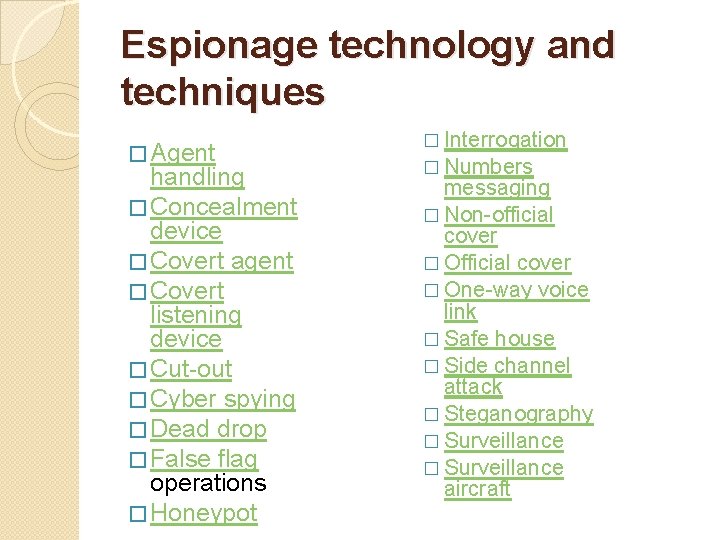
Espionage technology and techniques � Agent handling � Concealment device � Covert agent � Covert listening device � Cut-out � Cyber spying � Dead drop � False flag operations � Honeypot � Interrogation � Numbers messaging � Non-official cover � One-way voice link � Safe house � Side channel attack � Steganography � Surveillance aircraft
Also see �Quantum Cryptography �Cyber espionage (e. g. flame, stuxnet and red October). �“Trade secret” espionage.
Is there a silver Lining? Dual use technology • Missile • Nuclear • Chemical • Electronics • Biological
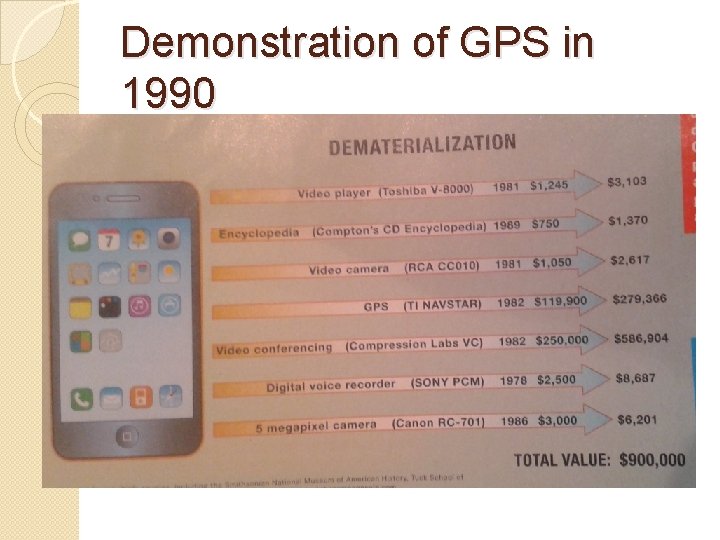
Demonstration of GPS in 1990
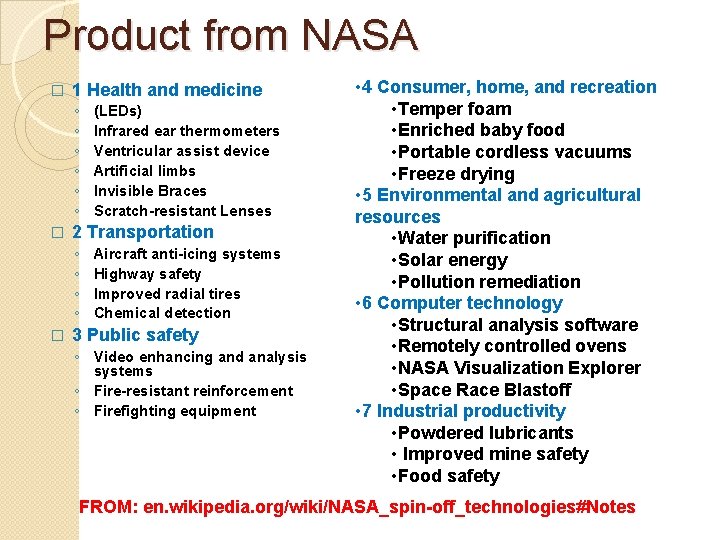
Product from NASA � 1 Health and medicine ◦ ◦ ◦ � 2 Transportation ◦ ◦ � (LEDs) Infrared ear thermometers Ventricular assist device Artificial limbs Invisible Braces Scratch-resistant Lenses Aircraft anti-icing systems Highway safety Improved radial tires Chemical detection 3 Public safety ◦ Video enhancing and analysis systems ◦ Fire-resistant reinforcement ◦ Firefighting equipment • 4 Consumer, home, and recreation • Temper foam • Enriched baby food • Portable cordless vacuums • Freeze drying • 5 Environmental and agricultural resources • Water purification • Solar energy • Pollution remediation • 6 Computer technology • Structural analysis software • Remotely controlled ovens • NASA Visualization Explorer • Space Race Blastoff • 7 Industrial productivity • Powdered lubricants • Improved mine safety • Food safety FROM: en. wikipedia. org/wiki/NASA_spin-off_technologies#Notes
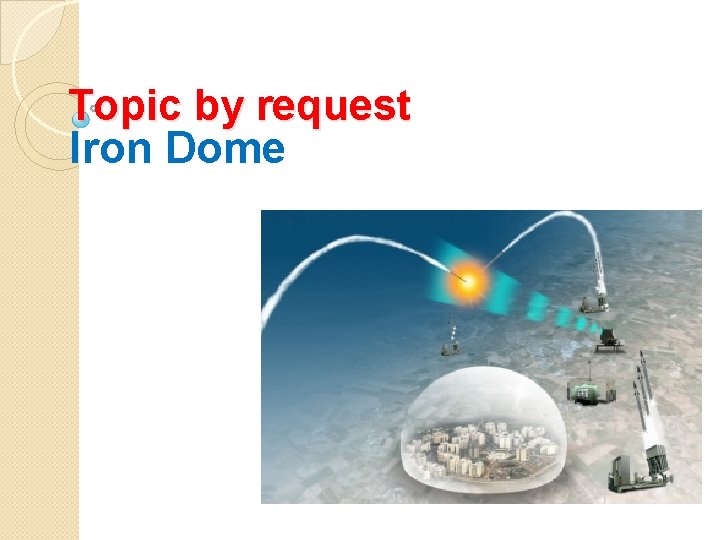
Topic by request Iron Dome

�Also known as “Iron Cap” �It is a mobile all-weather air defense system.
�It is a missile system designed to intercept and destroy shortrange rockets and artillery shells fired from distances of 4 to 70 kilometers away and whose trajectory would take them to a populated area.
�Iron Dome was declared operational and initially deployed on 27 March 2011. �It has been reported that the system shot down 90% of rockets launched from Gaza that would have landed in populated areas. �By November 2012, it had intercepted 400+ rockets. �It is considered to be the most effective and most tested missile shield in existence.
- Slides: 99