FreeLibre Open Source Software and When Disclosure Helps
Free/Libre & Open Source Software and When Disclosure Helps Security Peter P. Swire Ohio State University Western Ontario: “Free/Libre and Open Source Software as Democratic Principle” April 7, 2007
Dueling Slogans Open Source mantra: “No Security Through Obscurity” l Secrecy does not work (or at least we shouldn’t depend on it) l Disclosure is good (“virtuous”) Military motto: “Loose Lips Sink Ships” l Secrecy is essential l Disclosure is bad (“treason”) Both can’t be true at the same time
Overview Three papers complete, at www. ssrn. com, search “Swire” 1. A model for when each approach is correct -- assumptions for the Open Source & military approaches l Key reasons computer & network security often differ from earlier security problems and favor disclosure 2. “A Theory of Disclosure for Security & Competitive Reasons: Open Source, Proprietary Software, and Government Agencies” l Incentives for secrecy & openness to be used, even in Open Source, for both security and competitive reasons 3. “Privacy & Information Sharing in the War Against Terrorism” All concern when disclosure helps security We can identify where openness most likely to succeed
I. Model for When Disclosure Helps Security Ø Identify chief costs and benefits of disclosure l l Effect on attackers Effect on defenders Ø Describe scenarios where disclosure of a defense likely to have net benefits or costs Ø Utilitarian in approach l Economics & computer security, not law
Open Source Perspective & Disclosure Helps Defenders Ø Attackers learn little or nothing from public disclosure Ø Disclosures prompts designers to improve the defense -- learn of flaws and fix Ø Disclosure prompts other defenders/users of software to patch and fix l Net: Costs of disclosure low. Bens high. Ø [This is not a discussion of proprietary v. FLOSS – focus is on when disclosure improves security]
Military Base & Disclosure Helps Attackers Ø It is hard for attackers to get close enough to learn the physical defenses Ø Disclosure teaches the designers little about how to improve the defenses Ø Disclosure prompts little improvement by other defenders. l Net: Costs from disclosure high but few benefits.
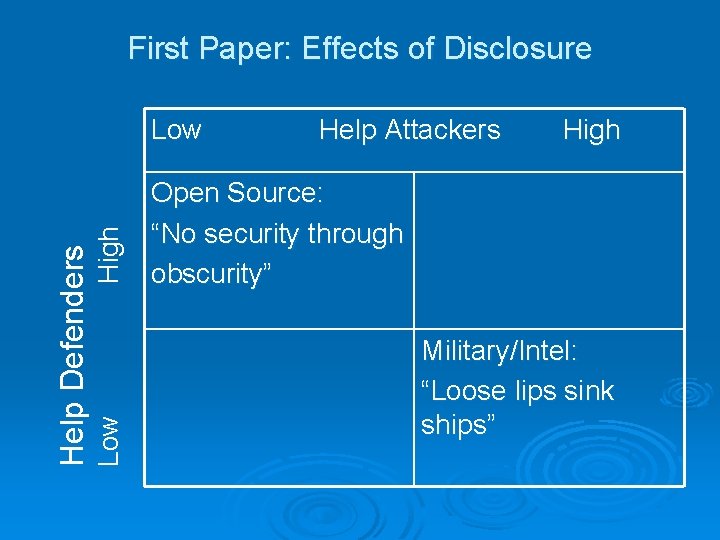
First Paper: Effects of Disclosure High Low Help Defenders Low Help Attackers High Open Source: “No security through obscurity” Military/Intel: “Loose lips sink ships”
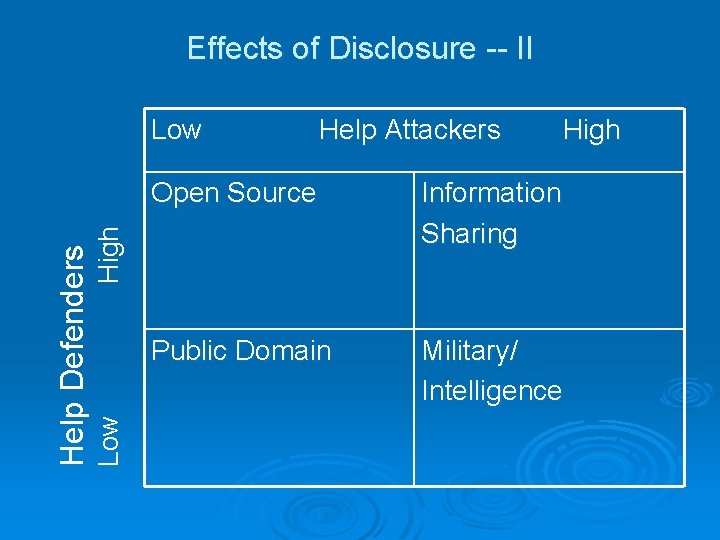
Effects of Disclosure -- II Help Attackers High Open Source Information Sharing Public Domain Military/ Intelligence High Low Help Defenders Low
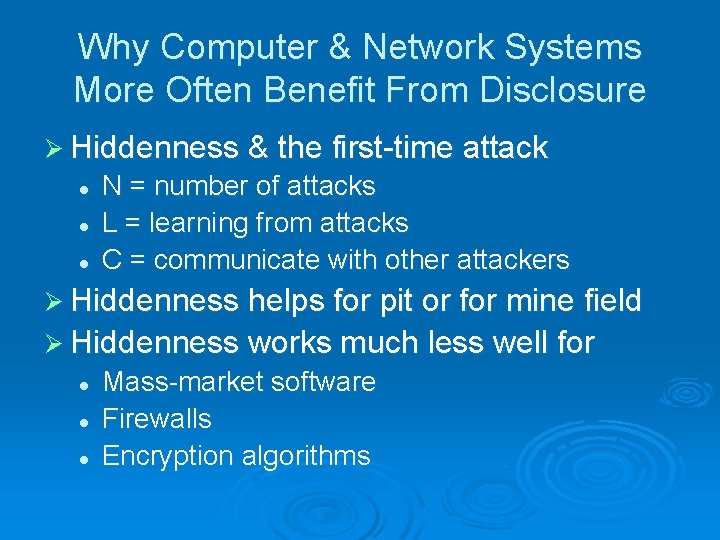
Why Computer & Network Systems More Often Benefit From Disclosure Ø Hiddenness & the first-time attack l l l N = number of attacks L = learning from attacks C = communicate with other attackers Ø Hiddenness helps for pit or for mine field Ø Hiddenness works much less well for l l l Mass-market software Firewalls Encryption algorithms
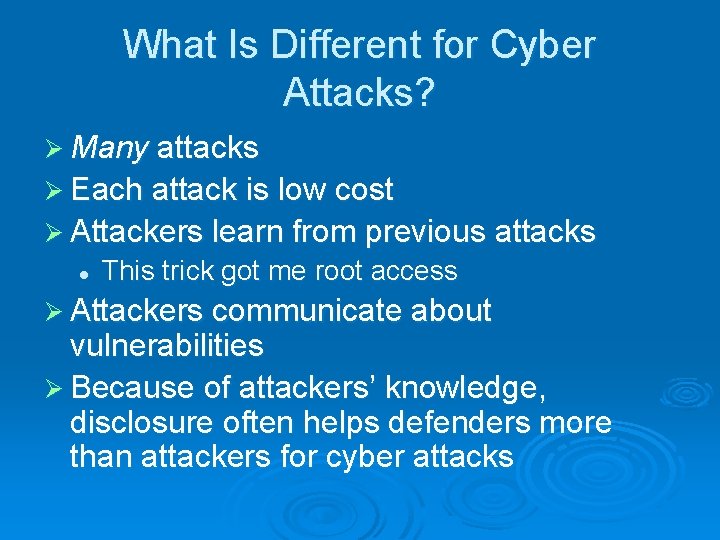
What Is Different for Cyber Attacks? Ø Many attacks Ø Each attack is low cost Ø Attackers learn from previous attacks l This trick got me root access Ø Attackers communicate about vulnerabilities Ø Because of attackers’ knowledge, disclosure often helps defenders more than attackers for cyber attacks
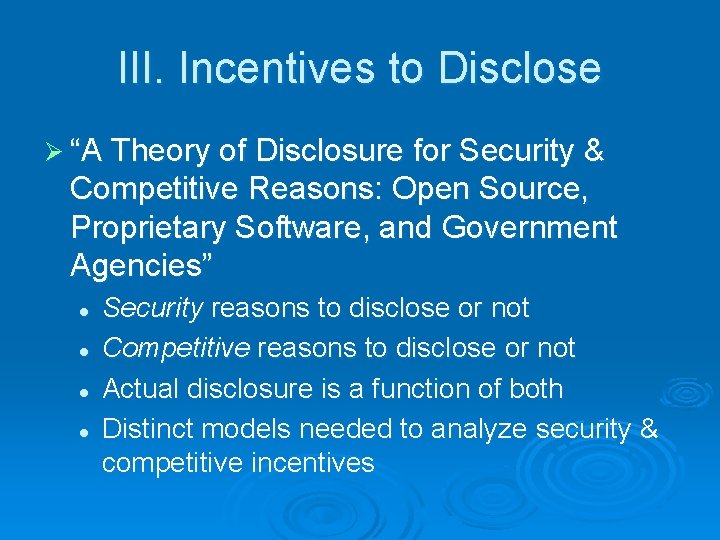
III. Incentives to Disclose Ø “A Theory of Disclosure for Security & Competitive Reasons: Open Source, Proprietary Software, and Government Agencies” l l Security reasons to disclose or not Competitive reasons to disclose or not Actual disclosure is a function of both Distinct models needed to analyze security & competitive incentives
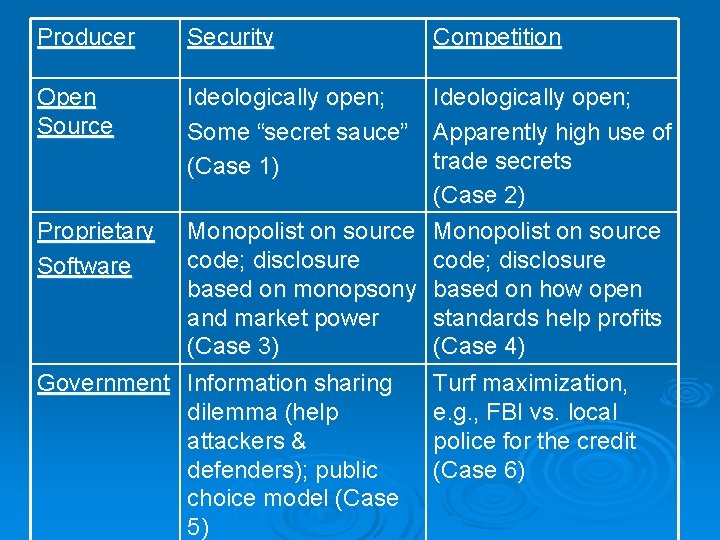
Producer Open Source Security Competition Ideologically open; Some “secret sauce” Apparently high use of trade secrets (Case 1) (Case 2) Proprietary Monopolist on source code; disclosure Software based on monopsony based on how open and market power standards help profits (Case 3) (Case 4) Government Information sharing Turf maximization, dilemma (help e. g. , FBI vs. local attackers & police for the credit defenders); public (Case 6) choice model (Case 5)
Case 1: Open Source/Security By ideology, by definition, & under licenses, open source code is viewable by all Ø Based on interviews, secrecy still used: l For passwords and keys l “Stealth firewalls” and other hidden features that are not observable from the outside l “Secret sauce” such as unusual settings and configurations, to defeat script kiddies Ø In short, rational secrecy is used to foil first-time and unsophisticated attacks Ø
Case 2: Open Source/Competition Interviews with O. S. devotees, they smile and admit that they don’t publish their best stuff – what’s going on? Ø Stay six months ahead of the curve – a form of trade secrets Ø Users and widgit manufacturers won’t want to disclose their internal software activities Ø
Open Source/Competition Ø Ø Services dominate over products in many Open Source business models Systems integrators: “We take very valuable OS software, and build it into a suite of services that is event more valuable” GPL 2. 0 applies to any work “distributed or published”, but not to services provided by one company Conclusion: trade secrets used in services have become a key competitive tool l Consistent with IBM and other major players’ services activities
Case 2: Open Source/Competition Ø Debate on GPL 3. 0 l Apparent defeat of earlier proposal to require publishing of code used internally l Services companies (including large commercial players) sticking with secrecy of their “non-distributed” GPL 2. 0 software to protect their trade secrets and business models
Case 3: Proprietary/Security Initially, the owner of closed-source software is in a monopoly position about flaws in the software it wrote Ø An externality leads to under-disclosure: software company loses reputation and risks liability with disclosure but harm on the 3 rd party user l This description was likely more true several years ago, before computer security was so important l Size of externality depends on the degree to which the seller’s reputation suffers due to security flaws l Over time, outside programmers gain expertise, the 1 st party loses its monopoly position in knowledge about vulnerabilities, & reputation effect is greater Ø
Case 3: Proprietary/Security What pressures force disclosure of vulnerabilities? l Large buyers, who have a taste to know the code in their system l Especially governments, who can (and do) require disclosure of vulnerabilities (Air Force) l To the extent there is competition based on software security, then disclosure may be profit-maximizing Ø Over time, have seen substantially greater openness about vulnerabilities in proprietary software Ø
Case 4: Proprietary/Competitive Hidden source code as a trade secret and possible competitive edge Ø Countervailing incentive to have at least partly “open standards” in order to get broad adoption, network effects, & first-mover advantage l At least share with developers & joint ventures l Complex game theory on when to be open Ø
Open Source & Proprietary Greater secrecy in Open Source than usually recognized l Secret sauce for security l Trade secrets in services Ø Greater openness in proprietary than usually recognized l Large buyers, governments, reputation l Financial gains from at least partly open standards Ø Convergence of the two approaches when it comes to disclosure? Ø
Case 5: Government/Security Summary – incentives for government to disclosure often weak Ø Unclear when to do information sharing: l Disclosure helps both attackers & defenders st party wants to share only with trusted third l 1 parties rd parties may want/need information to l Other 3 protect their own systems/jurisdictions Ø Examples such as terrorist watch lists, terrorist modes of attack, alerts based on intelligence Ø
Case 5: Government/Security Not good market mechanisms for disclosure Ø Thus a rationale for legal rules l FOIA to create transparency, including risks to communities l Executive Orders & congressional mandates to encourage information sharing Ø
Case 6: Government/Competitive Widespread view that law enforcement & intelligence agencies hoard data l Most famously, the FBI has not shared with locals l Hoarding can protect turf – others can’t use it against the 1 st party (the agency) l Hoarding can garner credit with stakeholders – the arrest, the correct intelligence analysis Ø Again, FOIA and Information Sharing mandates can seek to counter-act excessive secrecy Ø
Implications for FOSS & Government Ø Descriptive project – large zone where have a credible claim for security in Open Source approach to software l Ø Openness much more likely to help security for software than for physical security Areas where claim for Open Source security are less strong l l l Nuclear launch codes – few coders First-time attacks – secrecy helps Vulnerabilities that can’t be fixed – obscurity may be the best among imperfect strategies
Conclusions Ø Goal of describing when disclosure is societally optimal – does it help or hurt security Ø Goal of describing incentives, for OS, proprietary, and government Ø I hope you can apply this to your setting, to see when each approach is most likely to achieve security
- Slides: 25