FRAC Implementing RoleBased Access Control for Network File
FRAC: Implementing Role-Based Access Control for Network File Systems Aniruddha Bohra, Stephen Smaldone, and Liviu Iftode Department of Computer Science Rutgers University {bohra, smaldone, iftode}@cs. rutgers. edu
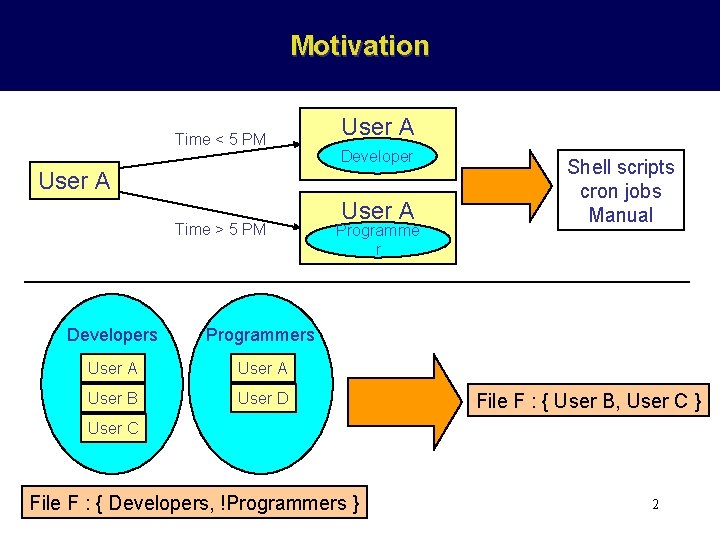
Motivation Time < 5 PM User A Developer User A Time > 5 PM Developers Programmers User A User B User D User A Programme r Shell scripts cron jobs Manual File F : { User B, User C } User C File F : { Developers, !Programmers } 2
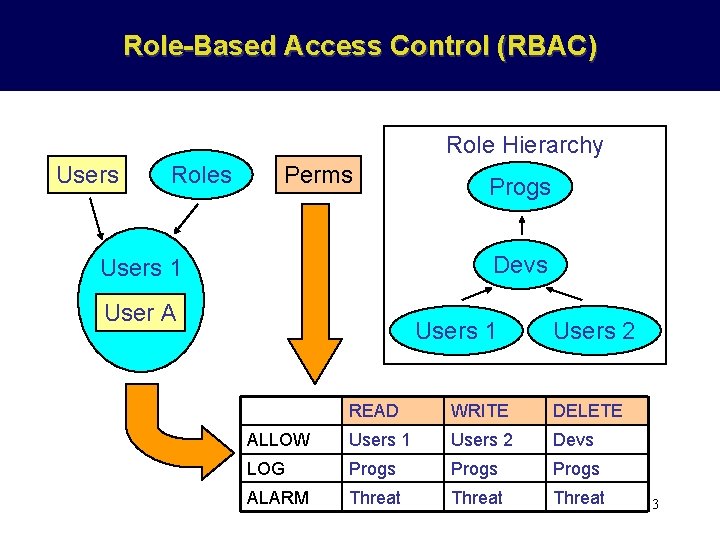
Role-Based Access Control (RBAC) Role Hierarchy Users Roles Perms Progs Devs Users 1 User A Users 1 Users 2 READ WRITE DELETE ALLOW Users 1 Users 2 Devs LOG Progs ALARM Threat 3
Benefits of RBAC • Policy Specification – Administrators define system-wide access control policies – Users may query and update portions of the access control system state – Simplified sharing and protection • Role Management – Role Hierarchy: Inheritance – Static Separation of Duties (SSD) • Session Management – Dynamic User to Role Mapping – Dynamic Separation of Duties (DSD) • Centralized Access Control Policy Enforcement – Enforcement of Principle of Least Privilege (POLP) – Verifiability of policy enforcement: auditing 4
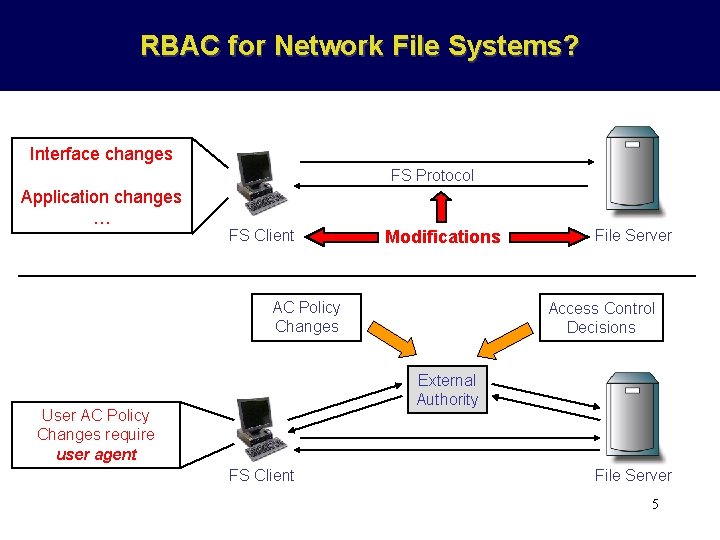
RBAC for Network File Systems? Interface changes FS Protocol Application changes … FS Client Modifications AC Policy Changes File Server Access Control Decisions External Authority User AC Policy Changes require user agent FS Client File Server 5
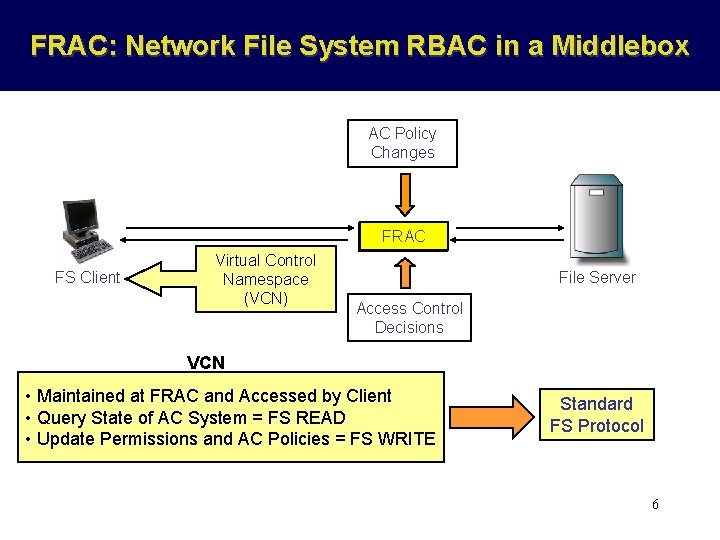
FRAC: Network File System RBAC in a Middlebox AC Policy Changes FRAC Middlebox FS Client Virtual Control Namespace (VCN) File Server Access Control Decisions VCN • Maintained at FRAC and Accessed by Client • Query State of AC System = FS READ • Update Permissions and AC Policies = FS WRITE Standard FS Protocol 6
Outline • Introduction • Design and Implementation – – Background Permission Evaluation in FRAC Enforcing Principle of Least Privilege Virtual Control Namespace (VCN) • Evaluation • Related Work • Conclusions 7
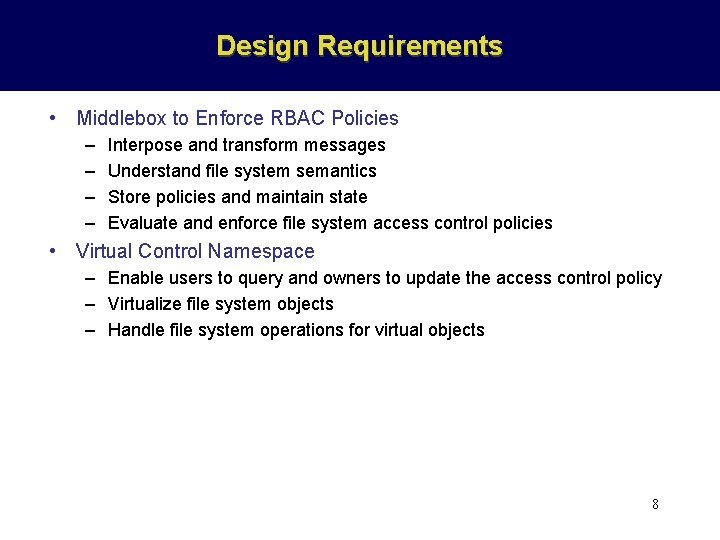
Design Requirements • Middlebox to Enforce RBAC Policies – – Interpose and transform messages Understand file system semantics Store policies and maintain state Evaluate and enforce file system access control policies • Virtual Control Namespace – Enable users to query and owners to update the access control policy – Virtualize file system objects – Handle file system operations for virtual objects 8
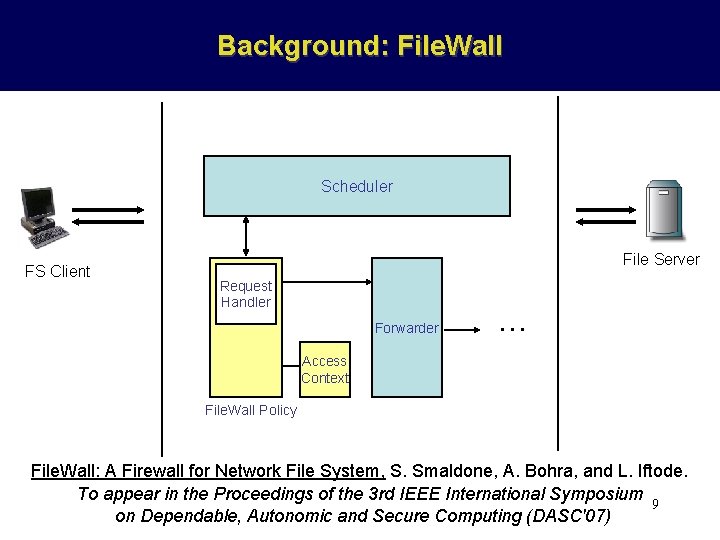
Background: File. Wall Scheduler FS Client File Server Request Handler Forwarder … Access Context File. Wall Policy File. Wall: A Firewall for Network File System, S. Smaldone, A. Bohra, and L. Iftode. To appear in the Proceedings of the 3 rd IEEE International Symposium 9 on Dependable, Autonomic and Secure Computing (DASC'07)
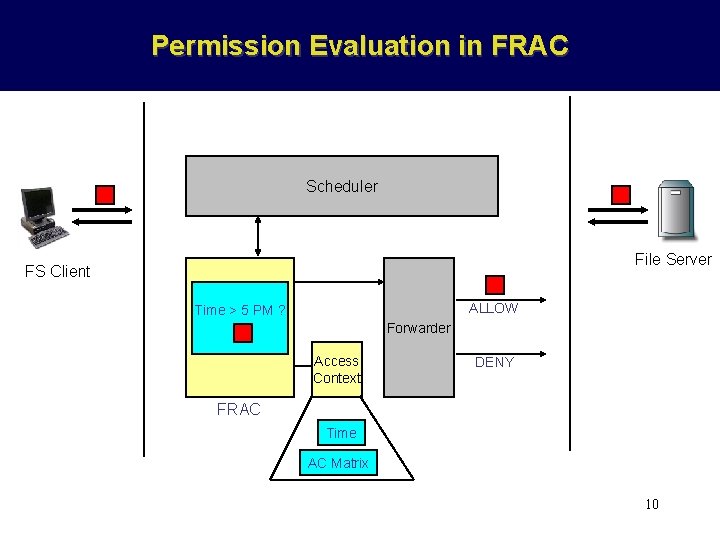
Permission Evaluation in FRAC Scheduler File Server FS Client ALLOW Time > 5 PM ? Forwarder Access Context DENY FRAC Time AC Matrix 10
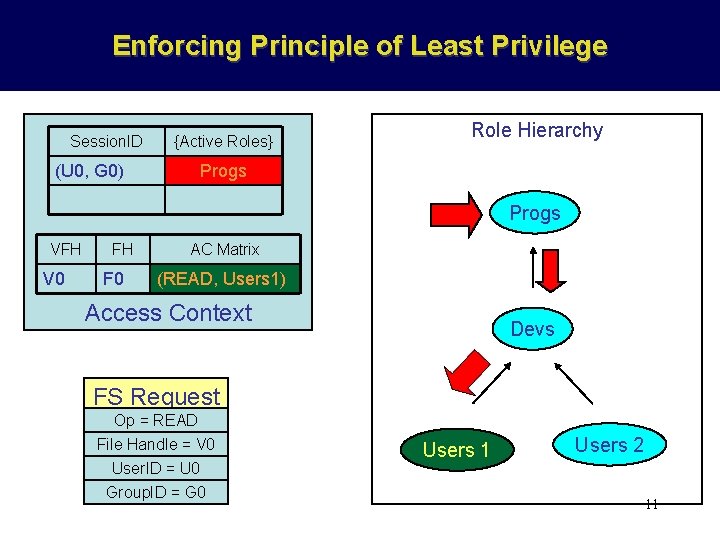
Enforcing Principle of Least Privilege Session. ID (U 0, G 0) {Active Roles} Role Hierarchy Progs VFH V 0 FH F 0 AC Matrix (READ, Users 1) Access Context Devs FS Request Op = READ File Handle = V 0 User. ID = U 0 Group. ID = G 0 Users 1 Users 2 11
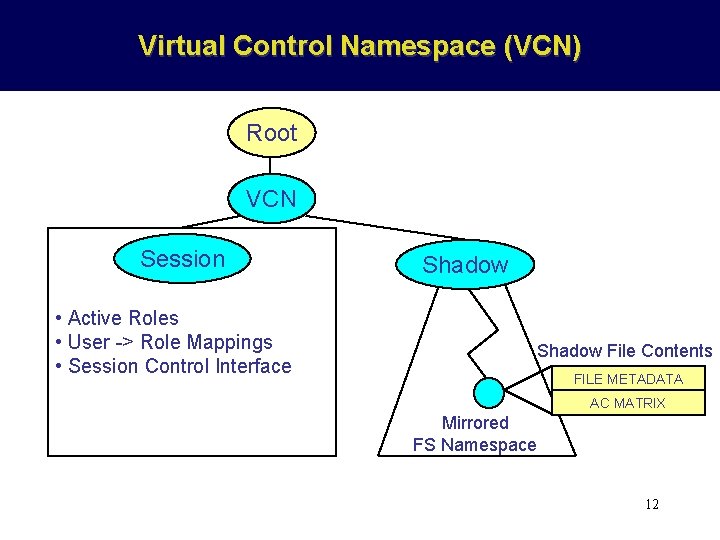
Virtual Control Namespace (VCN) Root VCN Session • Active Roles • User -> Role Mappings • Session Control Interface Shadow File Contents FILE METADATA AC MATRIX Mirrored FS Namespace 12
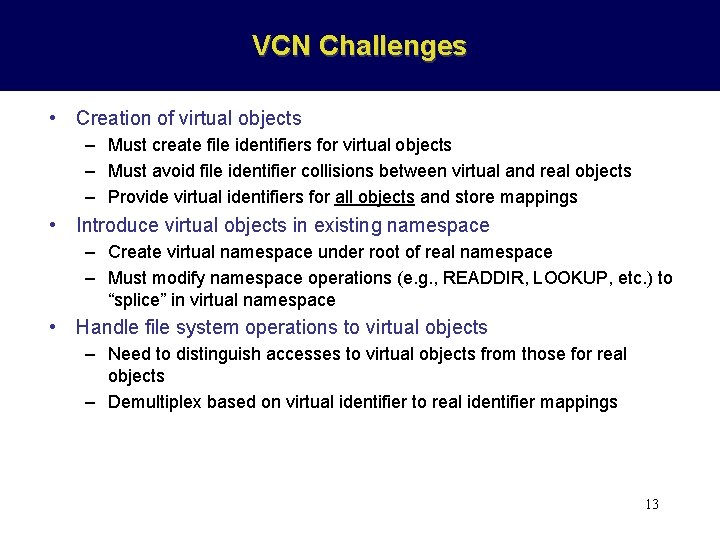
VCN Challenges • Creation of virtual objects – Must create file identifiers for virtual objects – Must avoid file identifier collisions between virtual and real objects – Provide virtual identifiers for all objects and store mappings • Introduce virtual objects in existing namespace – Create virtual namespace under root of real namespace – Must modify namespace operations (e. g. , READDIR, LOOKUP, etc. ) to “splice” in virtual namespace • Handle file system operations to virtual objects – Need to distinguish accesses to virtual objects from those for real objects – Demultiplex based on virtual identifier to real identifier mappings 13
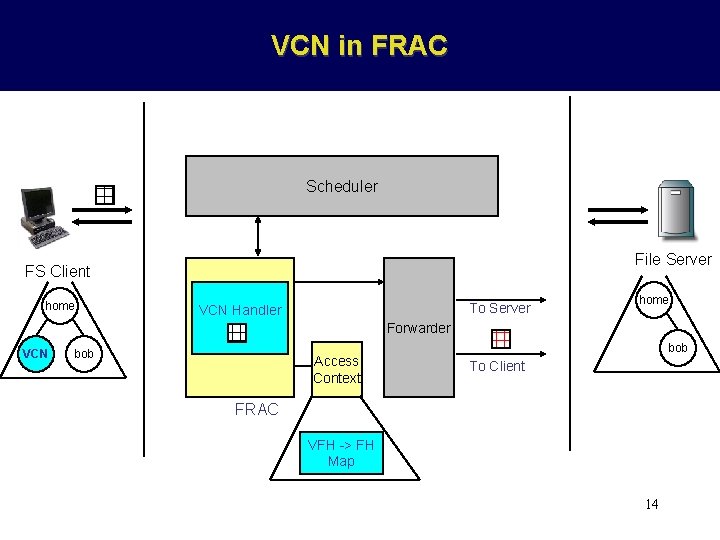
VCN in FRAC Scheduler File Server FS Client home To Server VCN Handler home Forwarder VCN bob Access Context bob To Client FRAC VFH -> FH Map 14
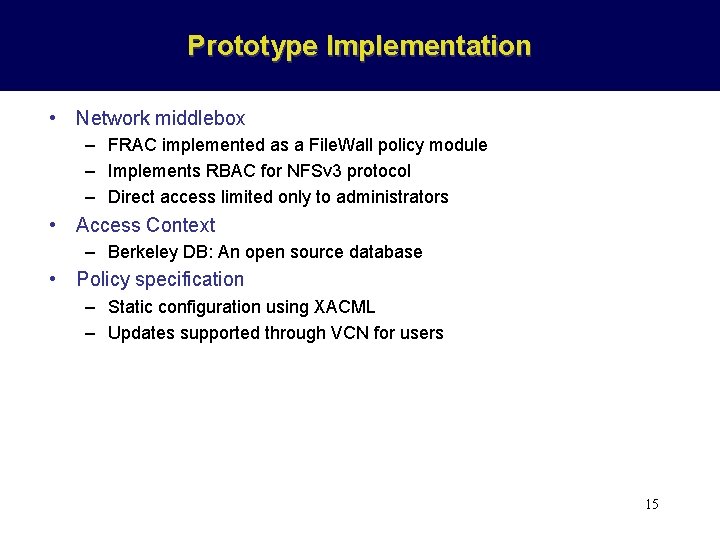
Prototype Implementation • Network middlebox – FRAC implemented as a File. Wall policy module – Implements RBAC for NFSv 3 protocol – Direct access limited only to administrators • Access Context – Berkeley DB: An open source database • Policy specification – Static configuration using XACML – Updates supported through VCN for users 15
Outline • • • Introduction Design and Implementation Evaluation Related Work Conclusions 16
Evaluation • Roles – Arranged as linear chain: highest to lowest privilege level – Session starts with a role at head of chain (worst case) • Setup – Systems: Dell Poweredge 2600 SMP systems, 2. 4 GHz Xeon II CPU, 2 GB RAM, running Linux 2. 6 – Microbenchmark: User-level RPC client – Application Benchmark: Open. SSH compilation 17
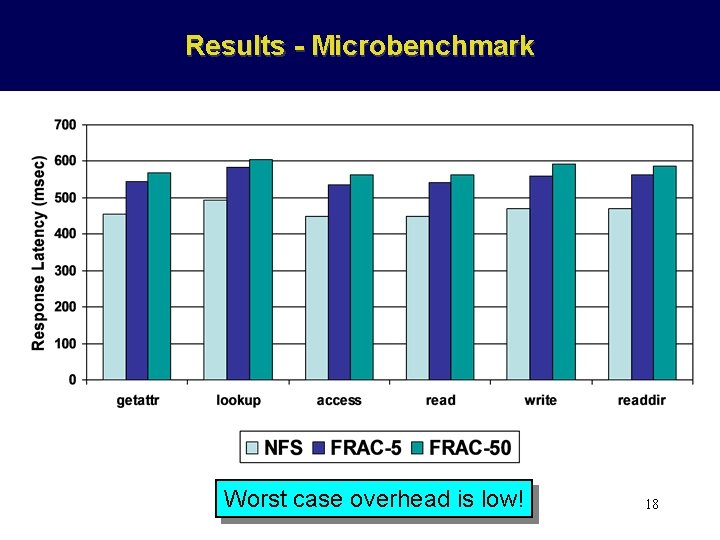
Results - Microbenchmark Worst case overhead is low! 18
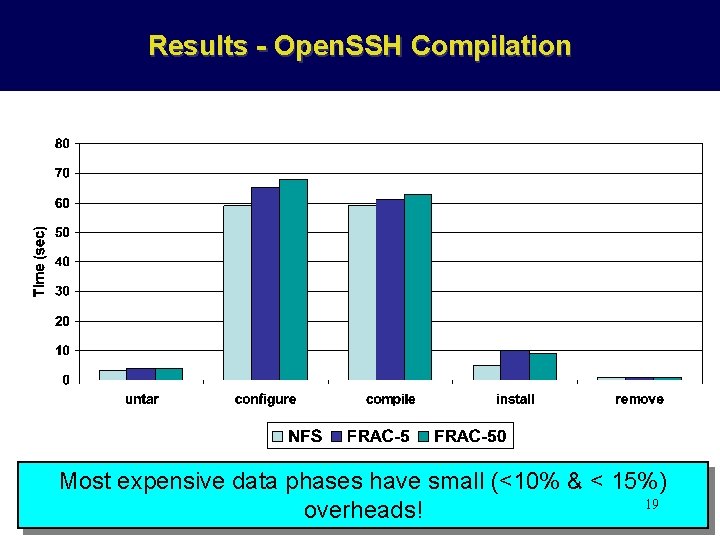
Results - Open. SSH Compilation Most expensive data phases have small (<10% & < 15%) 19 overheads!
![Related Work • RBAC Model – RBAC Standards [Ferraiolo’ 01, ANSI/INCITS’ 04] • RBAC Related Work • RBAC Model – RBAC Standards [Ferraiolo’ 01, ANSI/INCITS’ 04] • RBAC](http://slidetodoc.com/presentation_image/3871be88be6c9ef6bec1b89268c89784/image-20.jpg)
Related Work • RBAC Model – RBAC Standards [Ferraiolo’ 01, ANSI/INCITS’ 04] • RBAC for Network File Systems – Protocol Modifications [Gustaffson’ 97] – Agent-Based Systems [He’ 05] • Virtual and Programmable Namespaces – Plan 9 [Pike’ 93] – Semantic File Systems [Sheldon’ 91] 20
Conclusions and Future Work • FRAC: RBAC for network file systems using a middlebox (File. Wall) – Requires no client or server modifications – Virtual Control Namespace eliminates use of specialized agents – Low overheads: < 15% overhead for up to 50 roles • Future Work: – Language for Specification and Verification of policies – Continuous Monitoring of network file system accesses 21
Thank You! Questions?
- Slides: 22