Forwardinglabel Support in CCN Protocol draftraviforwardinglabel00 txt Ravindran
Forwarding-label Support in CCN Protocol “draft-ravi-forwarding-label-00. txt” Ravindran, Asit Chakraborti (Huawei) Mark Mosko, Ignacio Solis (PARC)

Agenda • • • Motivation Forwarding label Mgmt On the Wire Forwarding-label Processing PIT Implications Cache Implications Multi-Domain Scenario Security Considerations Use Case Scenario – – Producer Mobility Securing forwarding-label Example Simulation Results
Last Meeting • We had proposed several wire format affecting considerations – Forwarding Label – Interest Notification – Elastic Payloads – Conversational Traffic – Context Handling • Plan few drafts combining one or more of these topics– for this meeting we discuss forwardinglabel.
Motivation for Forwarding-label • A name other than the one in the Interest message. • Modifiable in the network – Allows Insert, Swap, Remove operations – Enables dynamism – mobility, caching, service migration etc. – A key difference from the ‘Links’ proposed in NDN [1]. • Useful for Several Scenario – – – Late-binding for Producer mobility [2] Routing Scalability Service Indirection Multi-Protocol Support Fast forwarding Interests [3] • Depending on the use case scenario, the implication on PIT/CS/FIB operation is different. [1] Alexander Afanesyev, Cheng Yi et al, “Map-and-Encap for Scaling NDN Routing”, NDN Technical Report , NDN-004. [2] Aytac Azgin, Ravindran, G. Q. Wang, “Scalable Mobility-Centric Architecture for Named data Networking”, IEEE, CCNC (SCENE Workshop), 2014 [3] Mark Mosko, “CCNx Label Forwarding (CCNLF)”– PARC
Forwarding-Label Management • Forwarding-label can be inserted by applications or by the network. – Routers needn’t trust application inserted labels. – Reasons of cache poisoning. • Registration, Resolution System, Resolution Query process has to be secure. – More secure when it is limited to a single domain. • This draft considers the case where Forwarding-label operation is handled within a single administrative boundary. • Multiple administrative domains can federate, so that labels inserted by one can be trusted by another.

On the Wire +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Fixed Header | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | <Optional TLVs> | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | T_LOCATER_NAME | Length | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Value (Name TLV ) | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Optional Security Attributes | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ Forwarding Label +--------------+---------+---------+ | Forwarding-Label | Meaning | Value | +--------------+---------+---------+ | Locater-Name | Identifies an | Name TLV| | | AS-ID/Gateway| | /Service Point | | +---------------+---------+--------+ • This is considering CCNx 1. 0 proposal. • Proposed as Optional field in the option body of the fixed header • The type is of “Locator-Name”, Optional Security attributes includes information for authentication and integrity check. • Future extension could include different types of forwarding-label

FL Processing: FIB • All forwarders process optional headers, follows the following processing rules. • If FL is present, it should be preferred for FIB lookup instead of the Interest name. • During FIB look-up, check if the locator-name exact matches a service name. – If ‘Yes’, the related service logic re-resolves the Interest name to another locater-name, or decide to remove it and subject FIB processing based on the Interest name. – If ‘No’, use longest prefix match to determine the next hop • Case of using multiple forwarding labels depends on the purpose it is used for. – For e. g. in mobility it may help in multicasting Interests to the old and new Attachement Point (AP) – This draft doesn’t deal with such scenarios, though there is potential usage of such stacking.
FL Processing: PIT Processing • If the network service is such that multiple requests arrives at a router cannot have different forwarding labels then FL needn’t be considered for PIT processing. • If service leads to multiple requests with the same Interest name arriving at the router with different forwarding-labels. – The forwarding-label state is saved along with Interest name and other metadata information. – While Interests can be aggregated, the new Interest should be forwarded to meet the service requirements. • In another situation, the service expresses Interests with a name with specific FL. – In this case FL is matched even in the reverse path with the Interest when it is forwarded back. – In case if the labels are swapped, then the reverse path shall append the right forwarding label in the content object. – One way to mitigate the cache poisoning problem
FL Processing: Cache Processing Implications • Depends on the case considered in the PIT processing discussion. • If Interests with the same name don’t carry different FLs, then CO processing follows the usual process. • Similarly if Interests arrive with different FLs have only forwarding implications – Then the returned CO’s are not returned with the FL hence no additional cache processing is required. • Caching implication exists if forwarding-label is required to be piggybacked along with the content object. – In this case the Content Object is cached with the forwarding-label, and used to match against the Interest’s FL for the future Interests too.
Multi-Domain Scenario • Use of forwarding-label by another domain depends on the trust association between domains. • It is useful, if labels assists with inter-domain routing, avoiding insertion/removal at the ingress/egress of every domain. • If forwarding-label cannot be re-used, forwarding -label is removed at the domain boundaries and, and new label pushed, with appropriate security attributes.
Security Considerations • Generally hop-by-hop fields are subjected to security issues as they are outside the Interest/Content-object security envelop. • Forwarding-label security depends on the service using it. – The threat vector spans registration, mapping system, resolution, and data-plane security. • We provide more details in the context of producer mobility.
![Use Case Scenario: Producer Mobility • The study in [1] uses forwarding-label to support Use Case Scenario: Producer Mobility • The study in [1] uses forwarding-label to support](http://slidetodoc.com/presentation_image_h/d20bca2378662d7a4688ace8ba472b0c/image-12.jpg)
Use Case Scenario: Producer Mobility • The study in [1] uses forwarding-label to support intra-/inter- session/domain producer mobility. • Seamless mobility is enabled by signaling between attachment points, allowing latebinding using forwarding-label. [1] Aytac Azgin, Ravindran, G. Q. Wang, “Scalable Mobility-Centric Architecture for Named data Networking”, IEEE, ICCCN (SCENE Workshop), 2014, http: //arxiv. org/abs/1406. 7049
Differentiating Mobile Flows • Supporting mobility incurs cost, as it requires assistance from resolution service and incurs dataplane overhead. • So differentiating flows which require mobility support is more efficient, alternatives: – Use Consumer Signalling to indicate Interest flow requires mobility service support. – Use name prefix to identify such network service invocation.
Using Forwarding-Label Name Resolution: • At the service edge router, the name resolution service is invoked which maps the Interest name to a locater-name. FIB Operation: • The forwarding-label is inserted, and forwarded to the next hop. • The successive hops checks if the locator-name maps to itself. If yes, the mobility service logic checks if the Interest name is registered locally. – If it is, then FIB processing is based on the Interest name – If it is not, then mobility logic re-resolves the interest name to a new FL and forwards the Interest based on it. • Once the Interest reaches the foreign or home domain, the FL is swapped to its current attachment point. • At the AP, if the mobile prefix is registered, it is forwarded towards the appropriate BS. • If the mobile device has moved, then the AP inserts a new FL, and forwards it to the new AP.
Using Forwarding Label PIT Operation • In the mobility case, Interests with the same name could arrive with different FL, due to device mobility. • Hence the FL should be saved in the PIT with the Interest name and new Interests with different FL should be forwarded. Caching Operation • For mobility, the objective is to use FL to guide the Interest to producer’s new location without considering any binding with the name, hence the FL is not piggybacked with the CO. Inter-domain Operation • Depending on the trust association between domains, the locatername can be used by another domain, especially if the inter-domain routing is enabled.

Name Resolution System • Handling mobility using FLs requires a name resolution system. • Centralized systems are hierarchical, so name registration in the lower domain has to announced to the higher level where it can be resolved. – Requires agreement on names between the hierarchical layers, e. g. DNS. • With CCN/NDN, decentralized systems can be realized. The Interest name can Identify the resolution domain. – E. g. /Enterprise/Alice/Phone/Service can implicitly resolved at /Enterprise/mobility-controller. – This relationship can be used by foreign domains to update the home domain when a mobile device registers in its own domain. – Here the domains can potentially manage their own name space, without a centralized management authority.
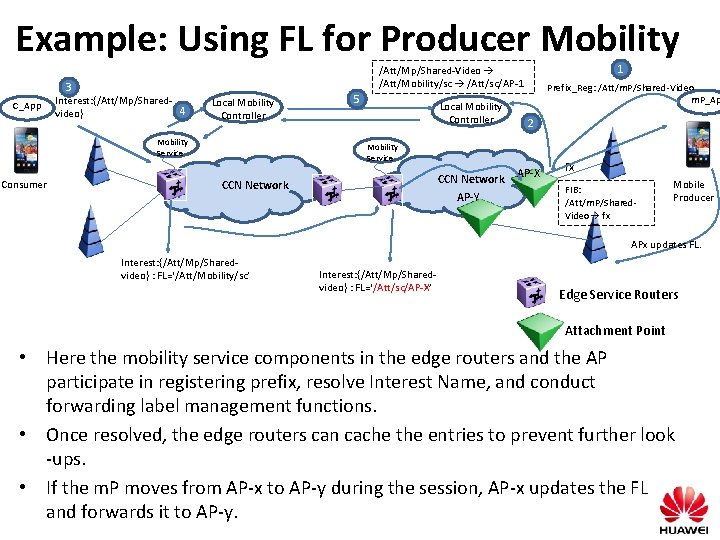
Example: Using FL for Producer Mobility 3 C_App Interest: {/Att/Mp/Shared 4 video} Local Mobility Controller Mobility Service Consumer 1 /Att/Mp/Shared-Video /Att/Mobility/sc /Att/sc/AP-1 5 Local Mobility Controller Prefix_Reg: /Att/m. P/Shared-Video m. P_Ap 2 Mobility Service CCN Network AP-Y CCN Network AP-X fx FIB: /Att/m. P/Shared. Video fx Mobile Producer APx updates FL. Interest: {/Att/Mp/Sharedvideo} : FL=‘/Att/Mobility/sc’ Interest: {/Att/Mp/Sharedvideo} : FL=‘/Att/sc/AP-X’ Edge Service Routers Attachment Point • Here the mobility service components in the edge routers and the AP participate in registering prefix, resolve Interest Name, and conduct forwarding label management functions. • Once resolved, the edge routers can cache the entries to prevent further look -ups. • If the m. P moves from AP-x to AP-y during the session, AP-x updates the FL and forwards it to AP-y.
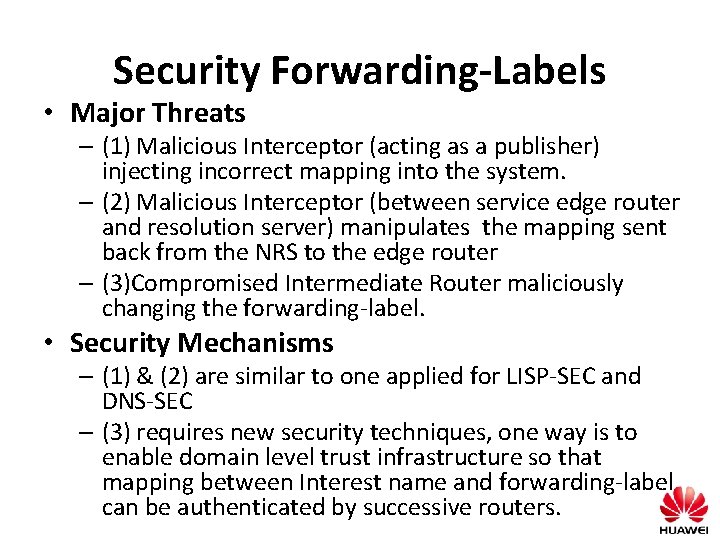
Security Forwarding-Labels • Major Threats – (1) Malicious Interceptor (acting as a publisher) injecting incorrect mapping into the system. – (2) Malicious Interceptor (between service edge router and resolution server) manipulates the mapping sent back from the NRS to the edge router – (3)Compromised Intermediate Router maliciously changing the forwarding-label. • Security Mechanisms – (1) & (2) are similar to one applied for LISP-SEC and DNS-SEC – (3) requires new security techniques, one way is to enable domain level trust infrastructure so that mapping between Interest name and forwarding-label can be authenticated by successive routers.

Performance Analysis • Simulated with ndn. SIM (built on ns 3) • Grid-based topologies (2 x 2, 3 x 3, 4 x 4 AS topologies, each with 1 LC and 8 CRs) • Input parameters: – Handover latency (50 ms), link specs (10 Mbps and 10 ms), CBR traffic (20 pps) – Randomly placed Consumer/Producer pair • Performance comparison to Flooding and Semi-flooding • Performance metrics of interest: – Session throughput (measures transmission efficiency, impact of retransmissions and recovery latency Po. A after handovers) – Recovery overhead (measures number of Interests transmitted per successfully received Data packet) LC LC ER SR ER ER ER LC LC 2 x 2 grid-based AS topology Semi-flooding: Flood after handover, and after convergence use single path
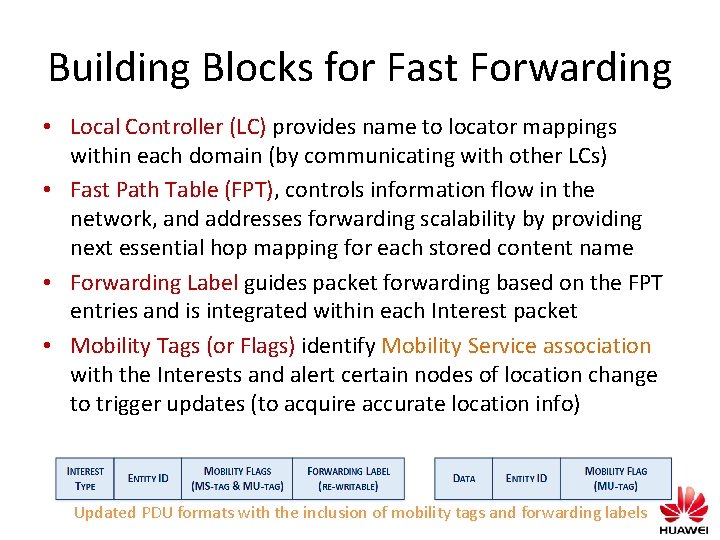
Building Blocks for Fast Forwarding • Local Controller (LC) provides name to locator mappings within each domain (by communicating with other LCs) • Fast Path Table (FPT), controls information flow in the network, and addresses forwarding scalability by providing next essential hop mapping for each stored content name • Forwarding Label guides packet forwarding based on the FPT entries and is integrated within each Interest packet • Mobility Tags (or Flags) identify Mobility Service association with the Interests and alert certain nodes of location change to trigger updates (to acquire accurate location info) Updated PDU formats with the inclusion of mobility tags and forwarding labels
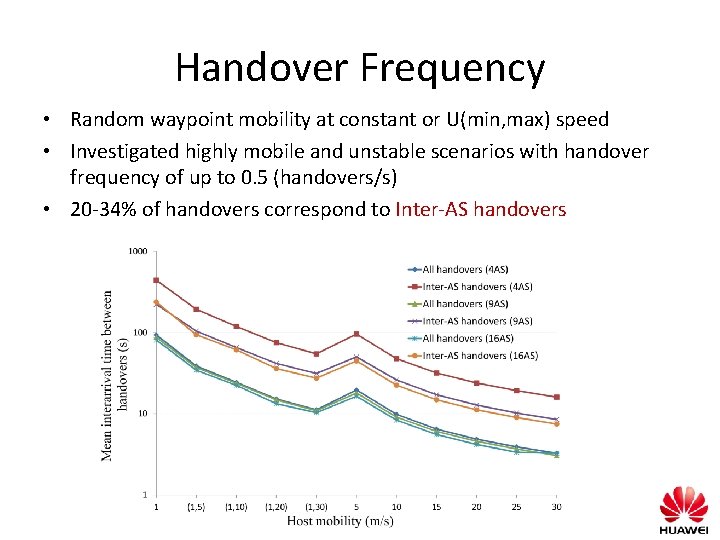
Handover Frequency • Random waypoint mobility at constant or U(min, max) speed • Investigated highly mobile and unstable scenarios with handover frequency of up to 0. 5 (handovers/s) • 20 -34% of handovers correspond to Inter-AS handovers
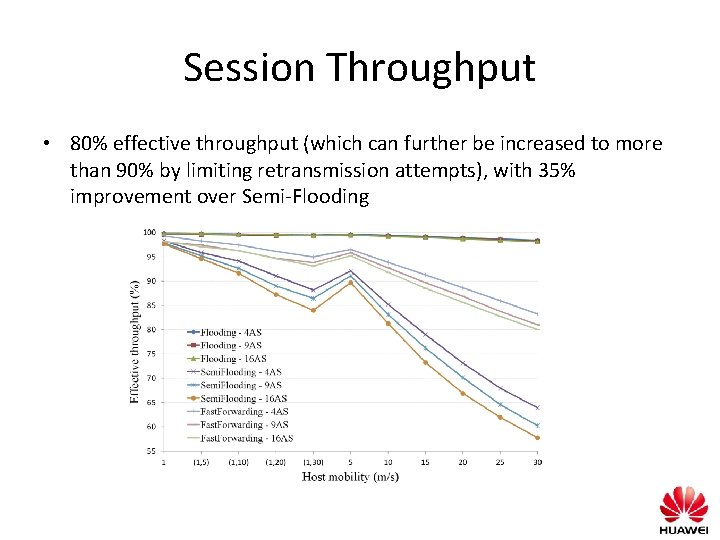
Session Throughput • 80% effective throughput (which can further be increased to more than 90% by limiting retransmission attempts), with 35% improvement over Semi-Flooding
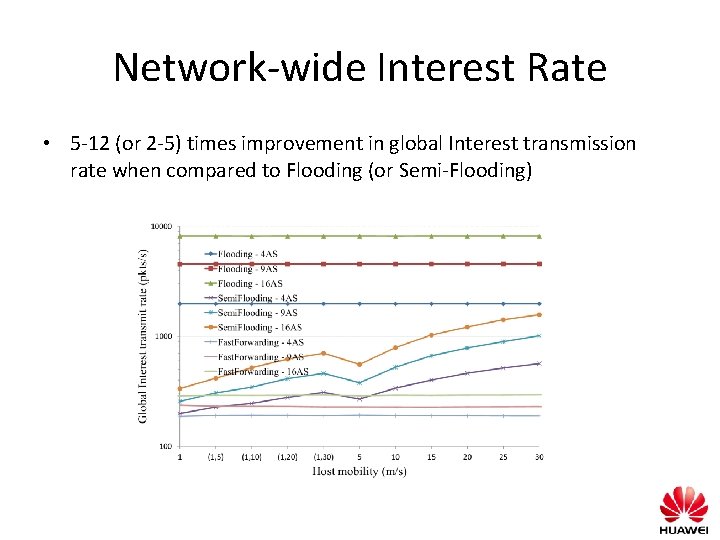
Network-wide Interest Rate • 5 -12 (or 2 -5) times improvement in global Interest transmission rate when compared to Flooding (or Semi-Flooding)
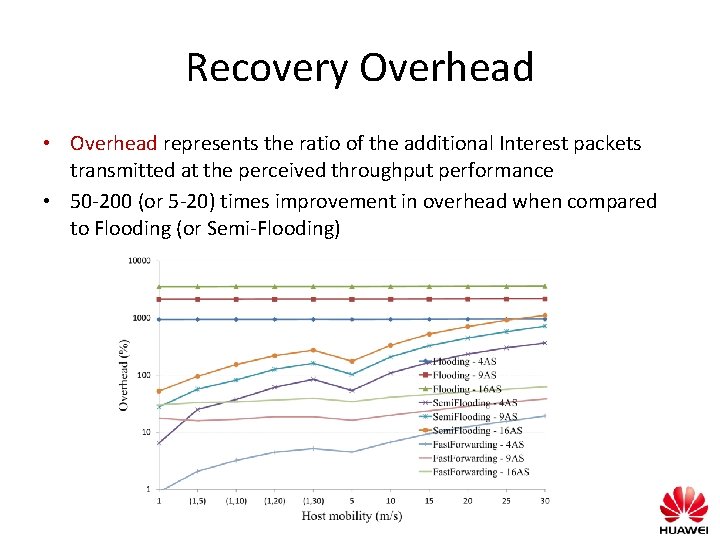
Recovery Overhead • Overhead represents the ratio of the additional Interest packets transmitted at the perceived throughput performance • 50 -200 (or 5 -20) times improvement in overhead when compared to Flooding (or Semi-Flooding)
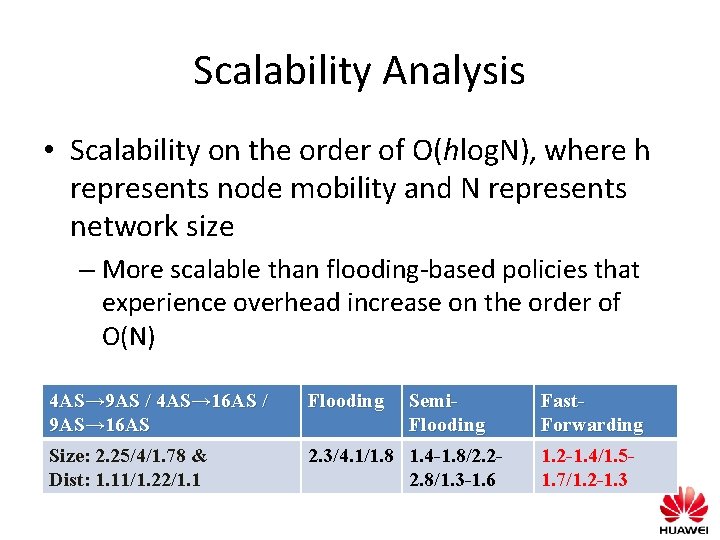
Scalability Analysis • Scalability on the order of O(hlog. N), where h represents node mobility and N represents network size – More scalable than flooding-based policies that experience overhead increase on the order of O(N) 4 AS→ 9 AS / 4 AS→ 16 AS / 9 AS→ 16 AS Flooding Semi. Flooding Size: 2. 25/4/1. 78 & Dist: 1. 11/1. 22/1. 1 2. 3/4. 1/1. 8 1. 4 -1. 8/2. 22. 8/1. 3 -1. 6 Fast. Forwarding 1. 2 -1. 4/1. 51. 7/1. 2 -1. 3
Summary • Forwarding-label can be used for multiple purposes. – The draft proposed a FL of type locater-name. • Security mechanisms depends on its use, and should include registration, name resolution, data plane aspects. • We discuss its usage for producer mobility.
- Slides: 26