Format String Vulnerability Yeongjin Jang 030118 Attack Primitives
Format String Vulnerability Yeongjin Jang 03/01/18
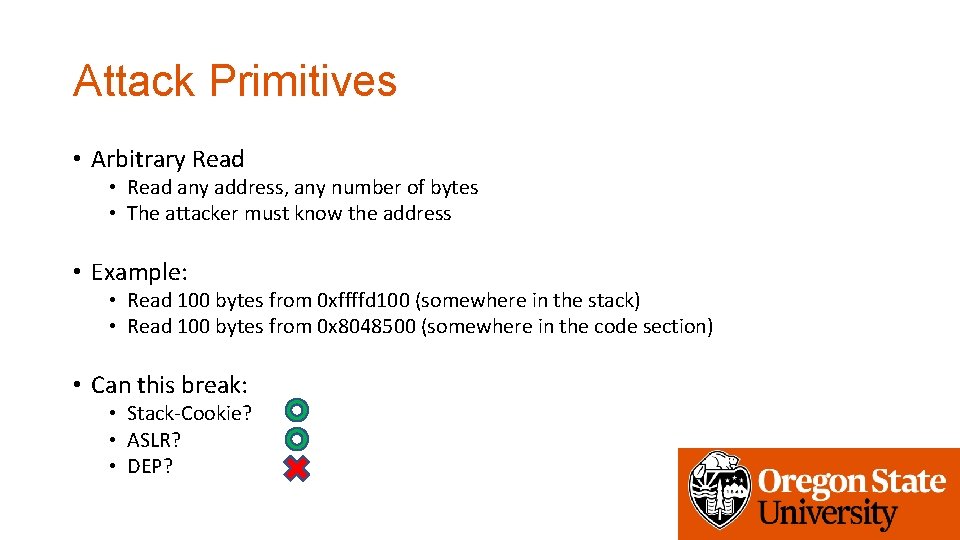
Attack Primitives • Arbitrary Read • Read any address, any number of bytes • The attacker must know the address • Example: • Read 100 bytes from 0 xffffd 100 (somewhere in the stack) • Read 100 bytes from 0 x 8048500 (somewhere in the code section) • Can this break: • Stack-Cookie? • ASLR? • DEP?
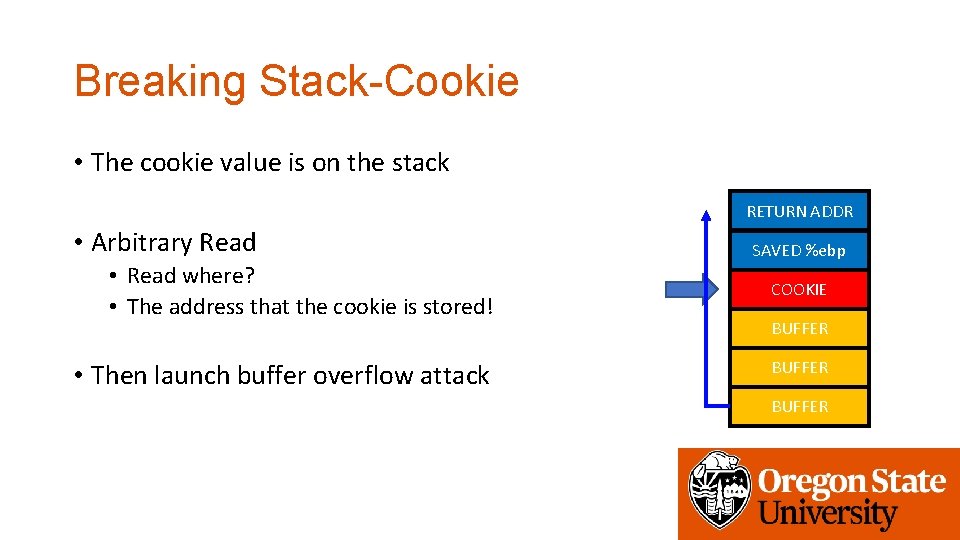
Breaking Stack-Cookie • The cookie value is on the stack RETURN ADDR • Arbitrary Read • Read where? • The address that the cookie is stored! • Then launch buffer overflow attack SAVED %ebp COOKIE BUFFER
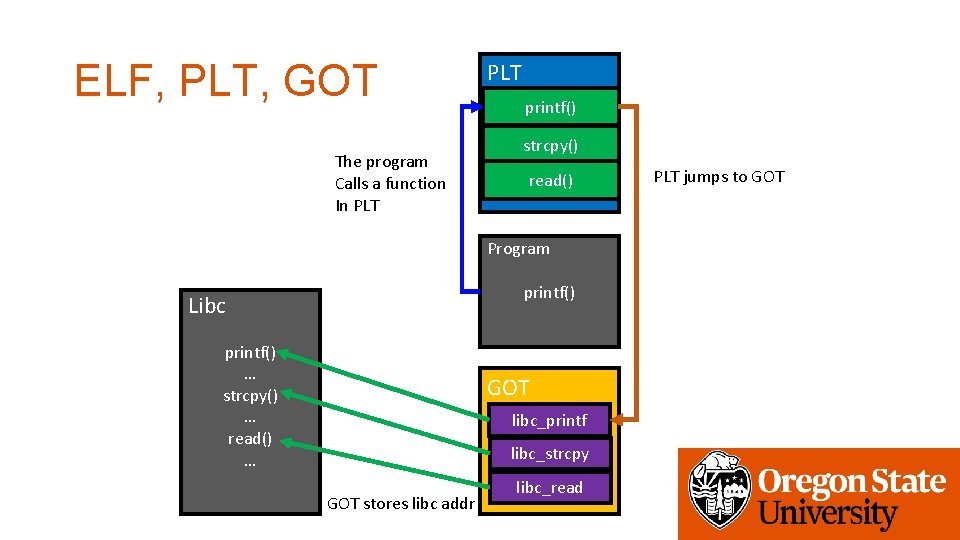
ELF, PLT, GOT The program Calls a function In PLT printf() strcpy() read() Program printf() Libc printf() … strcpy() … read() … GOT libc_printf libc_strcpy GOT stores libc addr libc_read PLT jumps to GOT
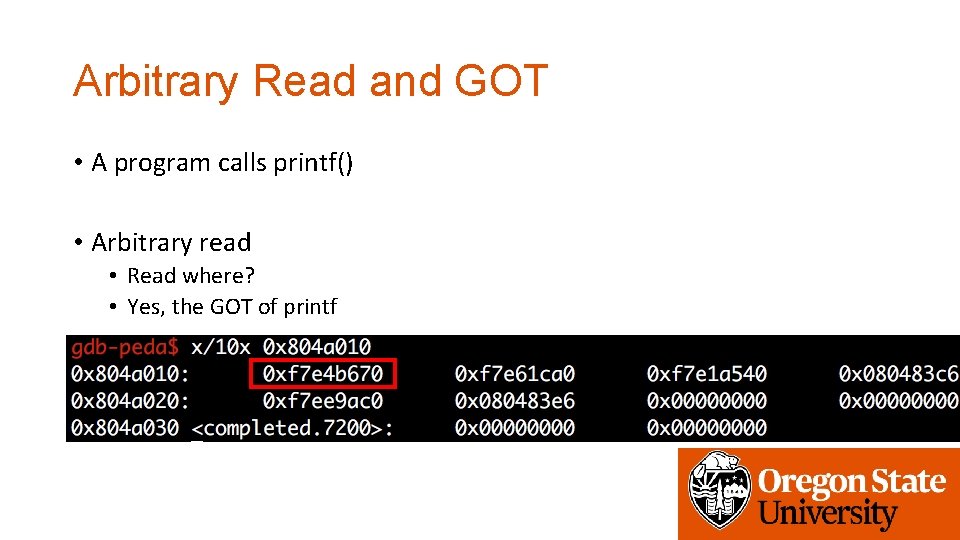
Arbitrary Read and GOT • A program calls printf() • Arbitrary read • Read where? • Yes, the GOT of printf
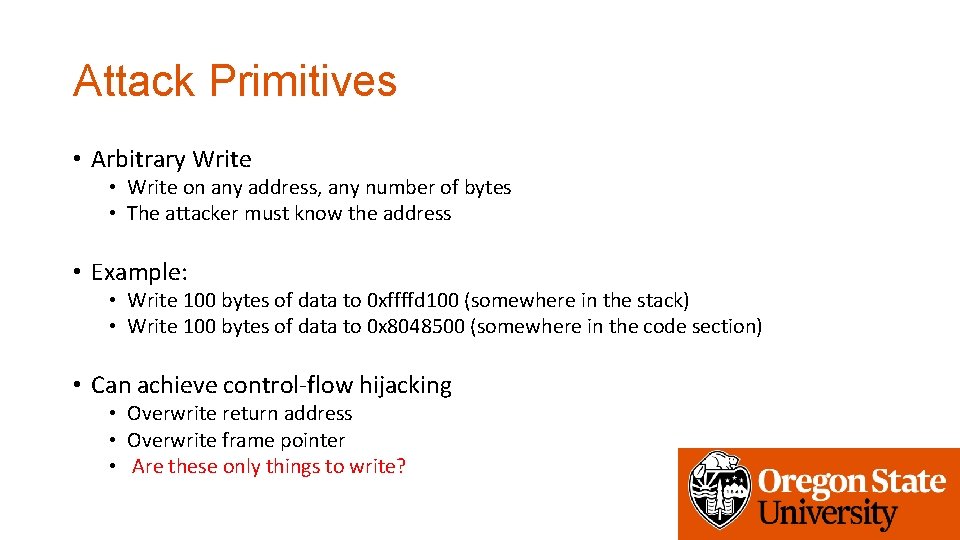
Attack Primitives • Arbitrary Write • Write on any address, any number of bytes • The attacker must know the address • Example: • Write 100 bytes of data to 0 xffffd 100 (somewhere in the stack) • Write 100 bytes of data to 0 x 8048500 (somewhere in the code section) • Can achieve control-flow hijacking • Overwrite return address • Overwrite frame pointer • Are these only things to write?
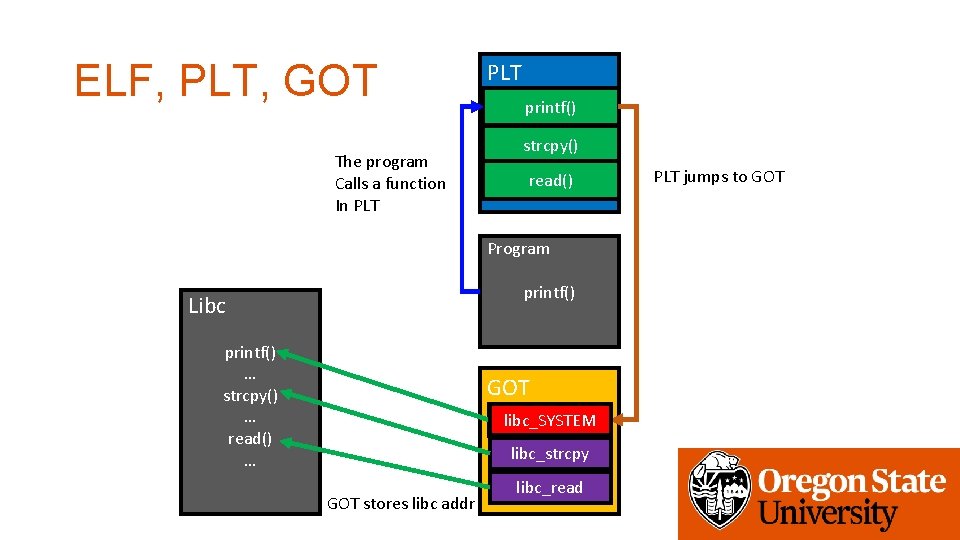
ELF, PLT, GOT The program Calls a function In PLT printf() strcpy() read() Program printf() Libc printf() … strcpy() … read() … GOT libc_SYSTEM libc_printf libc_strcpy GOT stores libc addr libc_read PLT jumps to GOT
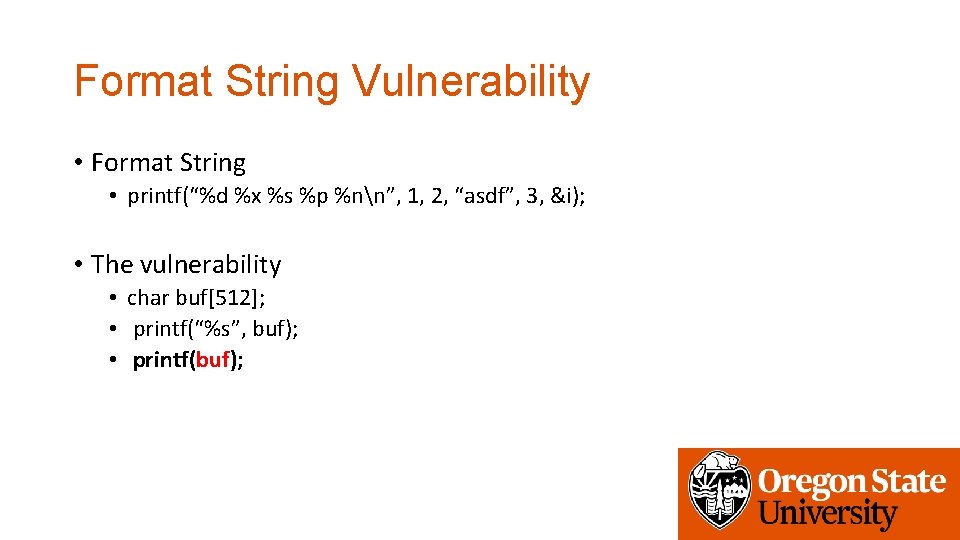
Format String Vulnerability • Format String • printf(“%d %x %s %p %nn”, 1, 2, “asdf”, 3, &i); • The vulnerability • char buf[512]; • printf(“%s”, buf); • printf(buf);
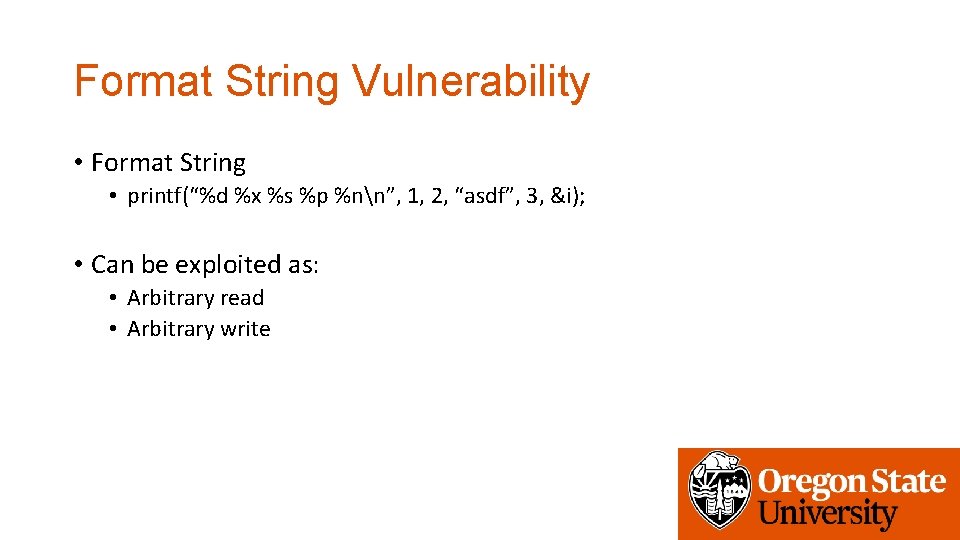
Format String Vulnerability • Format String • printf(“%d %x %s %p %nn”, 1, 2, “asdf”, 3, &i); • Can be exploited as: • Arbitrary read • Arbitrary write
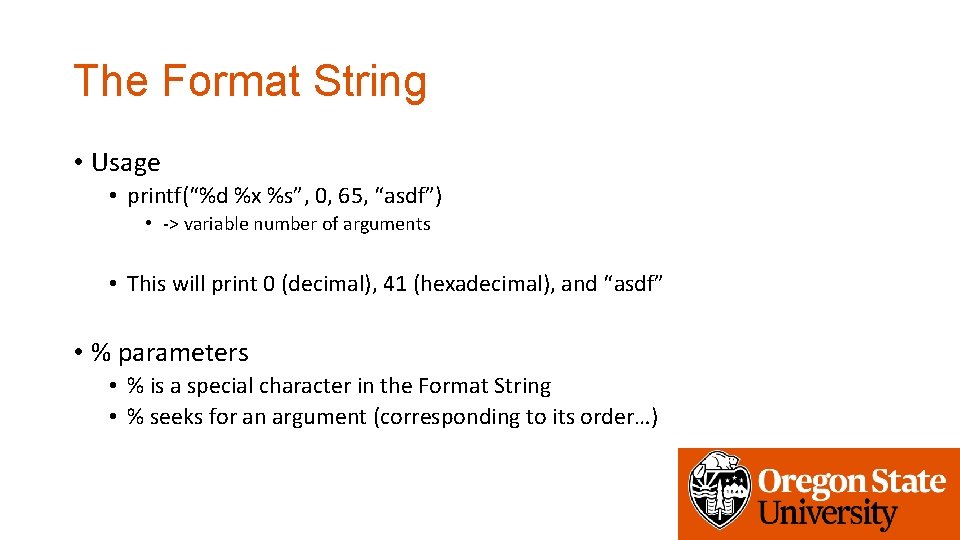
The Format String • Usage • printf(“%d %x %s”, 0, 65, “asdf”) • -> variable number of arguments • This will print 0 (decimal), 41 (hexadecimal), and “asdf” • % parameters • % is a special character in the Format String • % seeks for an argument (corresponding to its order…)
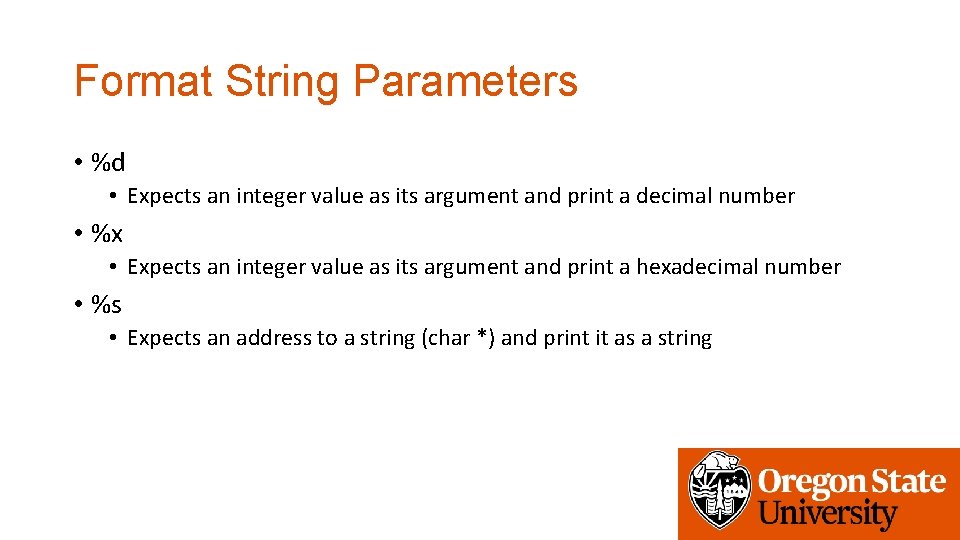
Format String Parameters • %d • Expects an integer value as its argument and print a decimal number • %x • Expects an integer value as its argument and print a hexadecimal number • %s • Expects an address to a string (char *) and print it as a string
![Format String Syntax • %1$08 d • %[argument_position]$[length][parameter] • Meaning • Print an integer Format String Syntax • %1$08 d • %[argument_position]$[length][parameter] • Meaning • Print an integer](http://slidetodoc.com/presentation_image/8a5fa66b9dcd94ced1aac5d896b09331/image-12.jpg)
Format String Syntax • %1$08 d • %[argument_position]$[length][parameter] • Meaning • Print an integer as a decimal value • Justify its length to length • Get the value from n-th argument • Print 8 -length decimal integer, with the value at the 1 st argument (padded with 0)
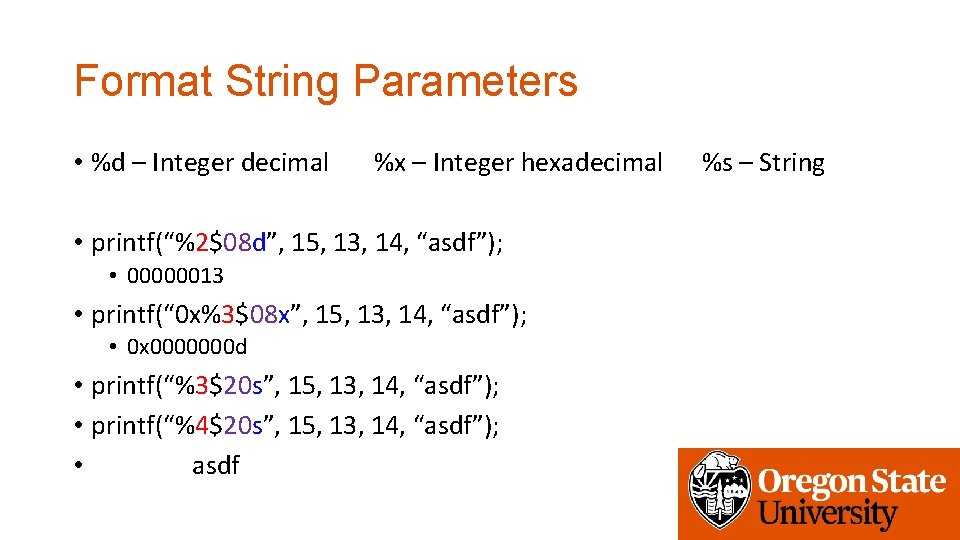
Format String Parameters • %d – Integer decimal %x – Integer hexadecimal • printf(“%2$08 d”, 15, 13, 14, “asdf”); • 00000013 • printf(“ 0 x%3$08 x”, 15, 13, 14, “asdf”); • 0 x 0000000 d • printf(“%3$20 s”, 15, 13, 14, “asdf”); • printf(“%4$20 s”, 15, 13, 14, “asdf”); • asdf %s – String
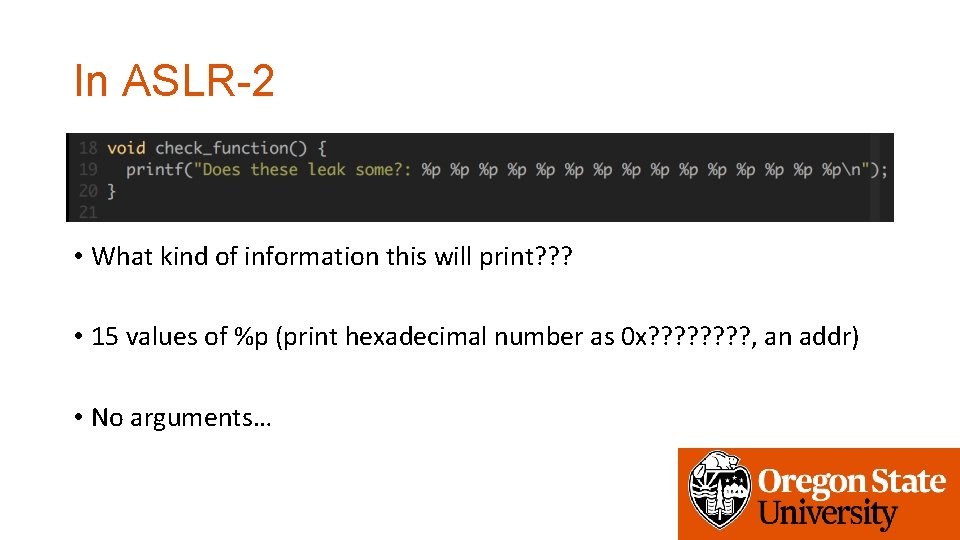
In ASLR-2 • What kind of information this will print? ? ? • 15 values of %p (print hexadecimal number as 0 x? ? ? ? , an addr) • No arguments…
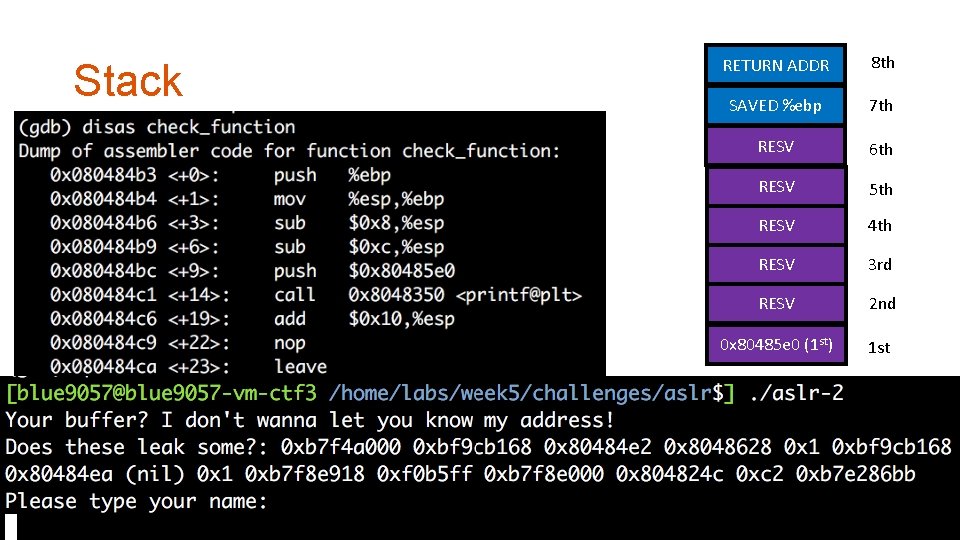
Stack RETURN ADDR 8 th SAVED %ebp 7 th RESV 6 th RESV 5 th RESV 4 th RESV 3 rd RESV 2 nd 0 x 80485 e 0 (1 st) 1 st
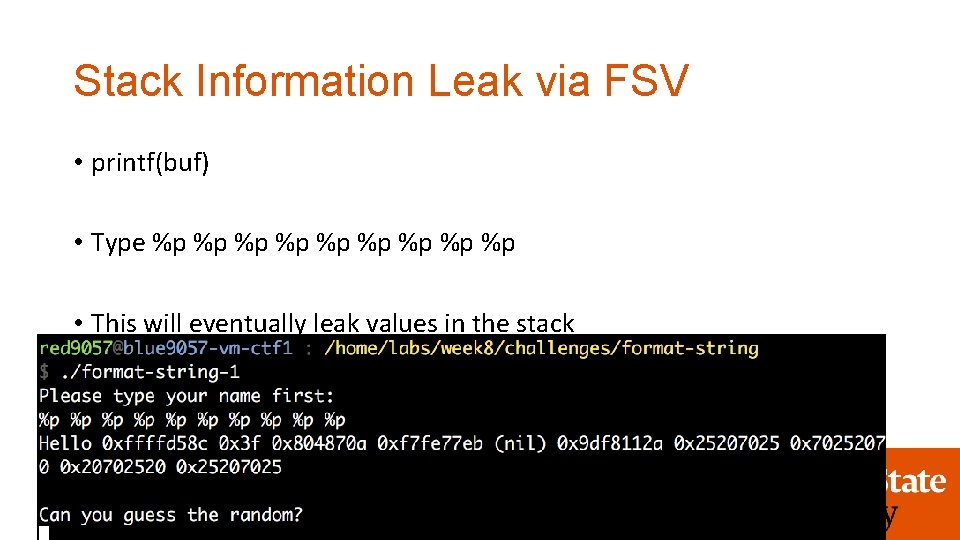
Stack Information Leak via FSV • printf(buf) • Type %p %p %p • This will eventually leak values in the stack
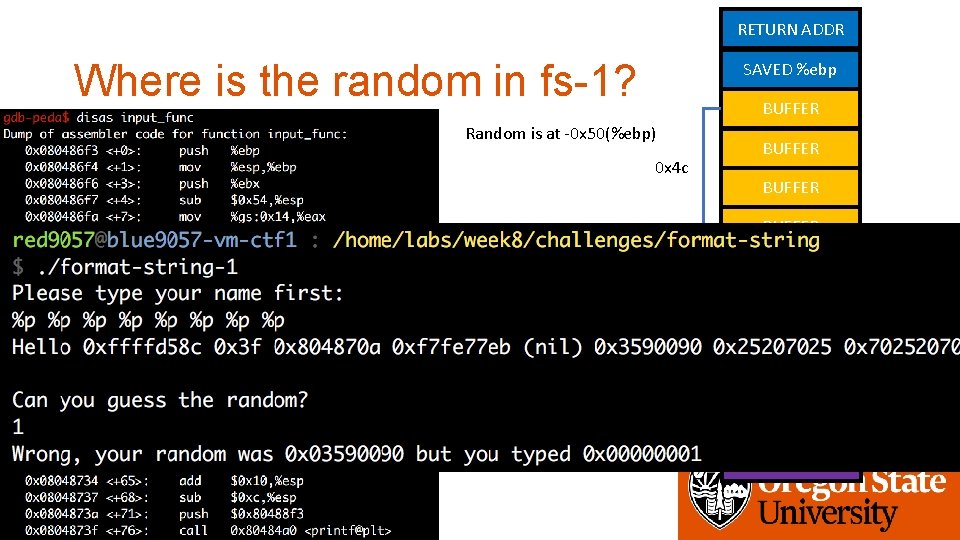
RETURN ADDR Where is the random in fs-1? SAVED %ebp BUFFER Random is at -0 x 50(%ebp) 0 x 4 c BUFFER random 6 th variable 5 th RESV 4 th RESV 3 rd RESV 2 nd Arg 1 of printf
Assignment: Week-8 • Please solve challenges in the /home/labs/week 8 directory • Some are in VM-CTF 1 and some are in VM-CTF 3 (ASLR-enabled) • Get flags from programs in the challeges directory • You can attach gdb to these programs, but your exploit must work without attaching gdb. • Due: 3/13 4: 00 pm
- Slides: 18