Forensic Investigation Methodology ABDULAZIZ A HAMEDA Forensic Investigation
Forensic Investigation Methodology ABDULAZIZ A. HAMEDA
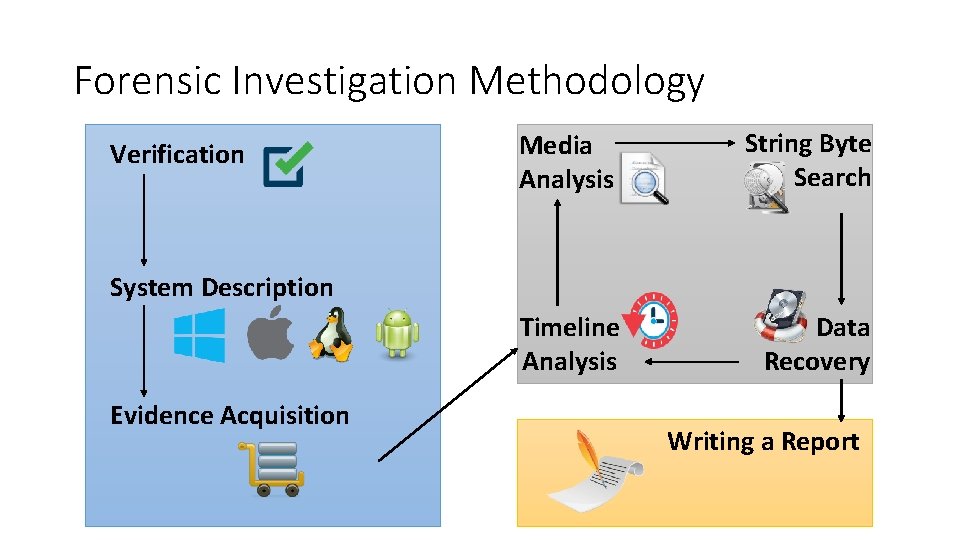
Forensic Investigation Methodology Verification Media Analysis String Byte Search Timeline Analysis Data Recovery System Description Evidence Acquisition Writing a Report
Step 1: Verification • The first step in the forensic investigation is to verify that an incident has occurred. The investigator needs to talk to any personnel associated with the system such as, the system's admin. • Check any logs they may have. • Note: you need to secure the scene and start the investigation.
Step 2: System Description • Take notes, document and label all evidence (Photography or video is a good way of doing this). • Describe the system that is being analysed. • Document what has been acquired such as, Laptop, Desktop PC and Server. • What is its configuration such as, Operating System and Network.
Step 3: Evidence Acquisition • Obtain volatile data from the processes, memory and network connections. • Obtain pertinent data. • Obtain a forensic image. • Build a “dirty word” list. • Shutting down the computer(s).
Step 4: Timeline Analysis • Perform a file timeline analysis for the time in which the incident occurred, which gives the following: • • Modified, accessed, created/changed time. Highlight when the operating system was installed. When were major updates performed? When was it used last? • Note: Timeline is usually the bedrock of your investigation.
Step 5: Media Analysis • Examine the resulting image using forensic tools of your choice. • Describe the analysis system in detail. • Describe each tool used to examine the system and why you used it. • Show your tools did not modify the evidence when performing your examination.
Step 6: String or Byte Searches • Conduct a string search on the media. • What keywords would you look for? Why would you look for those keywords? • Using your dirty word list, examine your evidence at a low level (bitby-bit).
Step 7: Data Recovery • Recover files or data deleted or in slack from the system. • Identify when the files were deleted and recover the pertinent files. • Describe methods in detail in your report.
Step 8: Reporting • Based on your analysis, what information could be gathered as to the habits of the subject? • Evidence that supports the claim? • Evidence that rejects the claim? • Findings and conclusions written. • Could be used in a court. • Scrutinised by opposing counsel.
- Slides: 10