Forensic Analysis of a Windows 2000 Server Operating

- Slides: 63
Forensic Analysis of a Windows 2000 Server Operating System Joshua Young CS 585 F – Fall 2002
Scenario • Computer is still in its original environment • Computer is on • Computer appears connected to the internet. • Computer and room have not yet been touched • Evidence handling procedures are already in place
Take Pictures… (Video if possible)
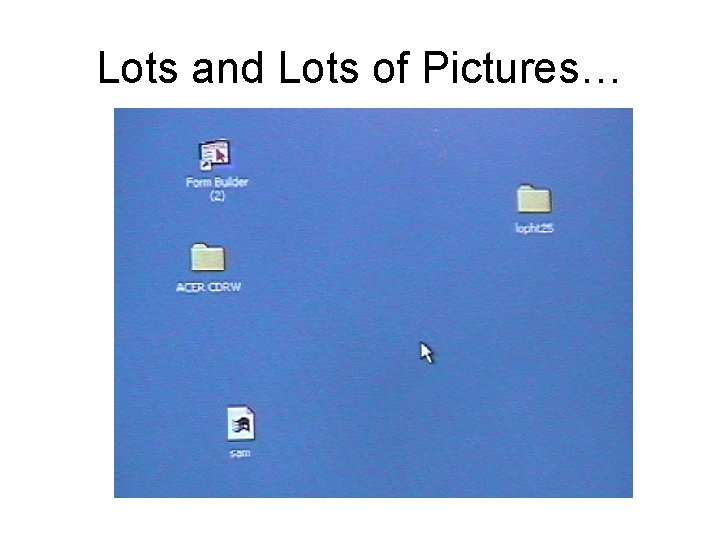
Lots and Lots of Pictures…
Intro to Win. Hex • Hex Editor Plus • Many Forensic Uses, especially for the novice – Disk Cloning, Ram Capture, Hex Searches, Spanned Files • Small (can fit on a floppy) • Inexpensive – Free limited trial Version – $100 for full version (with variations in between) • http: //www. winhex. com
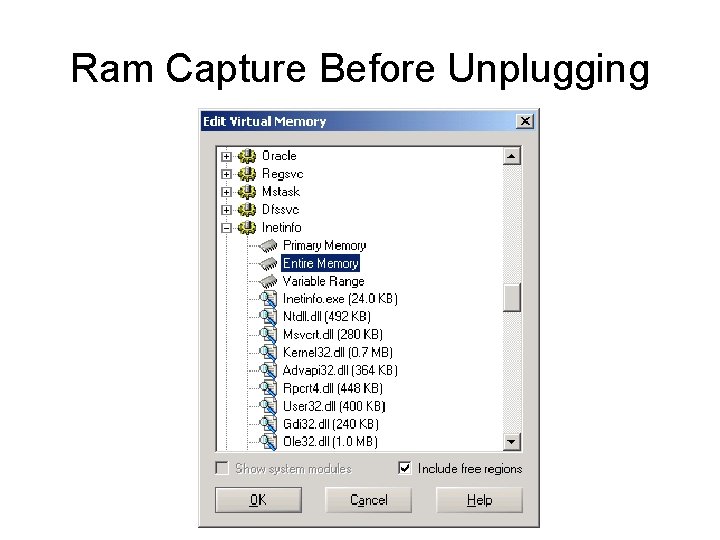
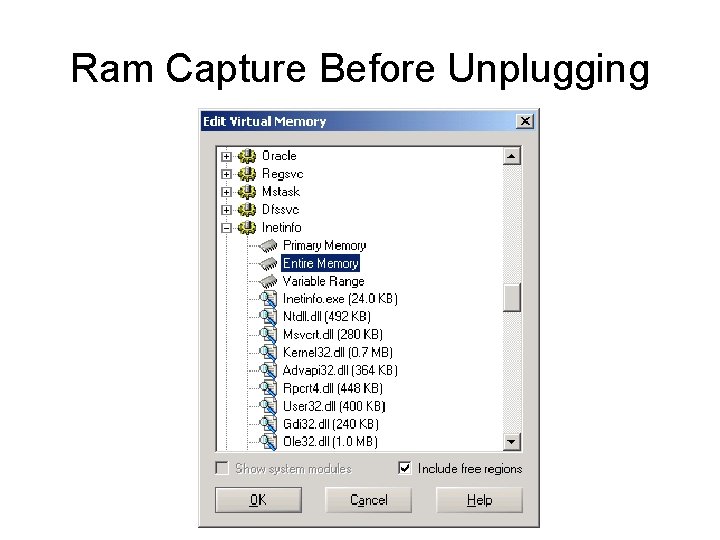
Ram Capture Before Unplugging
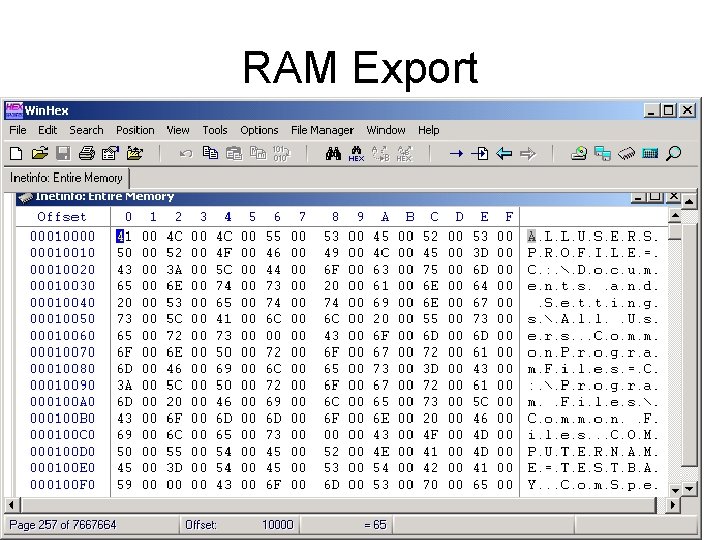
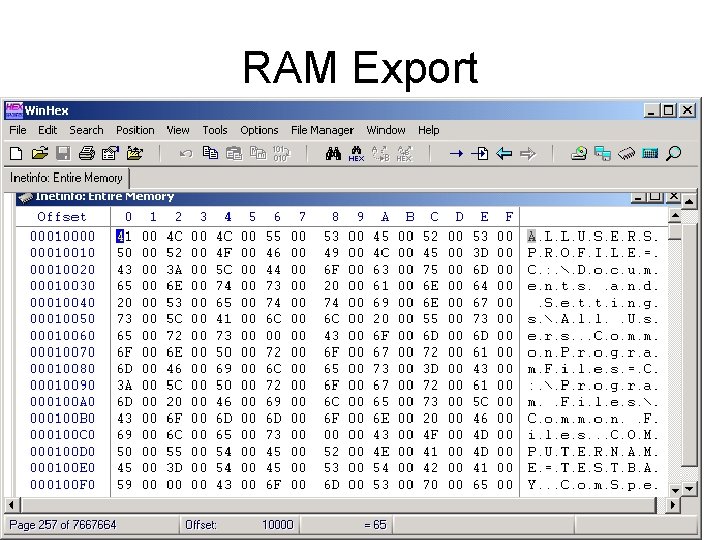
RAM Export
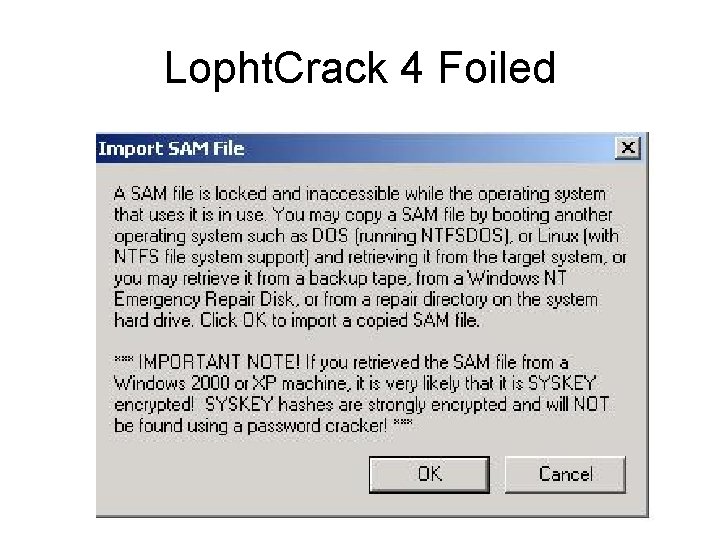
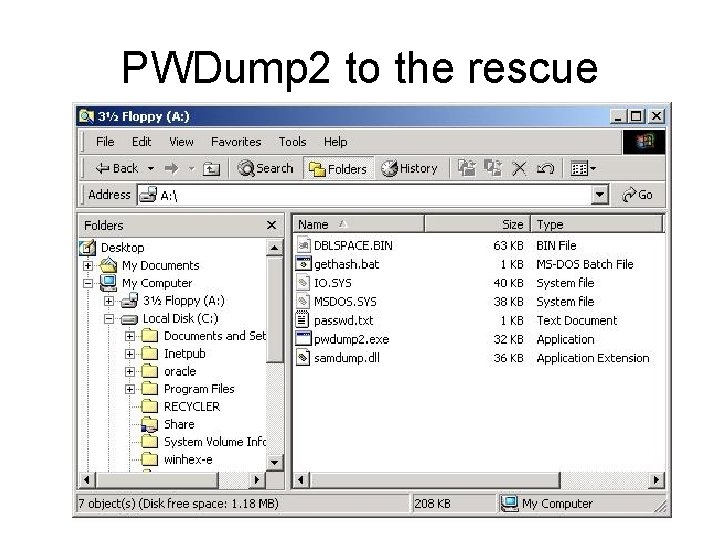
Get Password Hashes • Use PWDUMP from floppy to floppy • While this causes a small change to the disk, the hashes are not easily recovered once the machine is off – Win 2000 encrypts the hashes. Even if you use a boot disk to access the NTFS partition and recover the SAM file, password crackers will not be able to break it.
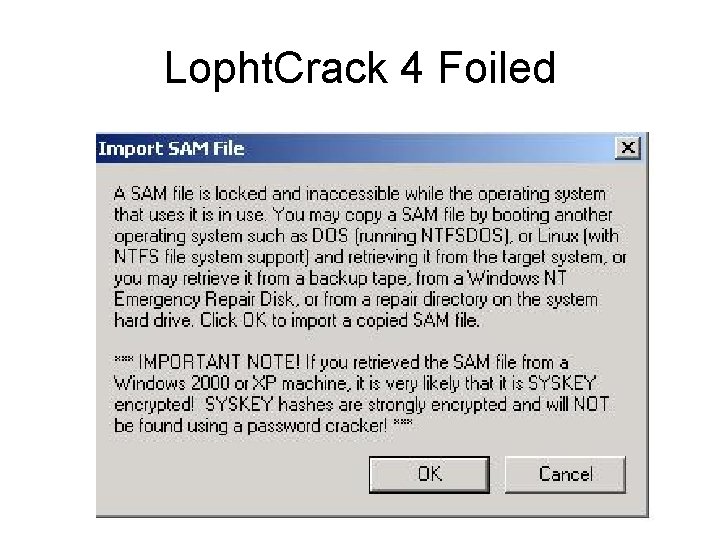
Lopht. Crack 4 Foiled
PWDump 2 • Any changes to the Hard Disk would be minor. • Source Code is available, so the impact could be independently verified • Only works if the person logged on has administrative rights
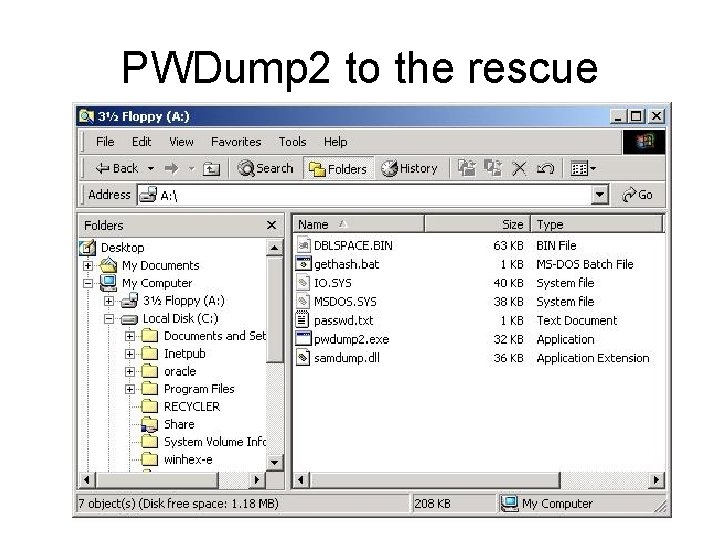
PWDump 2 to the rescue
Freeze the System • Once we have the RAM…. • And the Password Hashes…. . • Pull the plug
Don’t Forget Other Media • Collect all other media for analysis (similar analysis to Hard Disk) – – Floppies CDRoms Zip Disks Smart Cards / Memory Sticks • If media has software on it, record name, serial number, and whether it was original media or not. • If possible, check serial numbers with vendors to see if any of it violates copyright law.
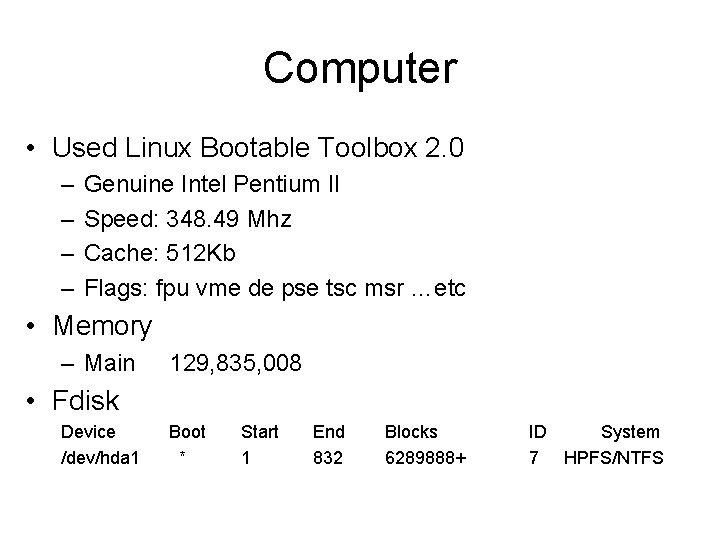
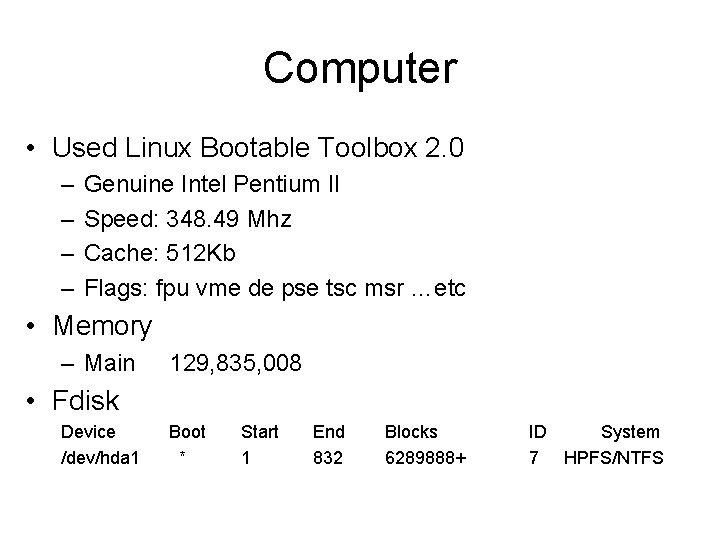
Computer • Used Linux Bootable Toolbox 2. 0 – – Genuine Intel Pentium II Speed: 348. 49 Mhz Cache: 512 Kb Flags: fpu vme de pse tsc msr …etc • Memory – Main 129, 835, 008 • Fdisk Device /dev/hda 1 Boot * Start 1 End 832 Blocks 6289888+ ID System 7 HPFS/NTFS
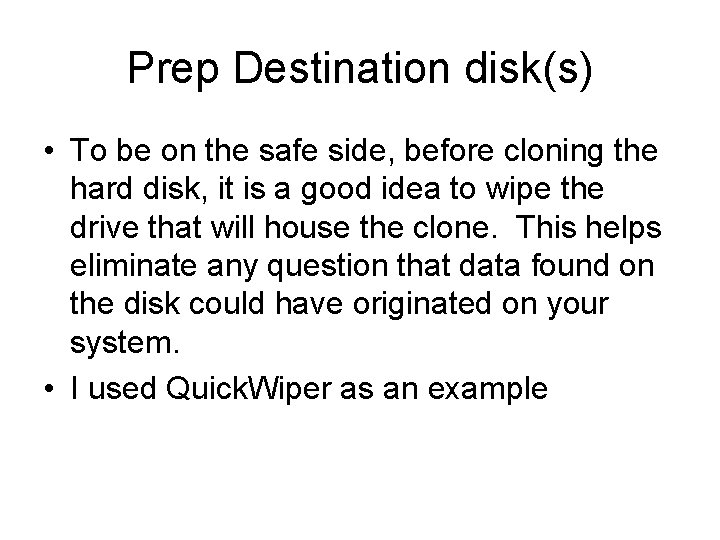
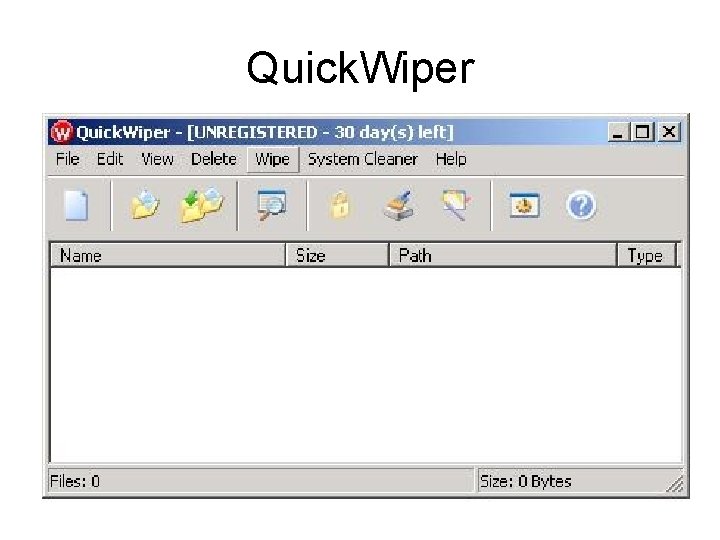
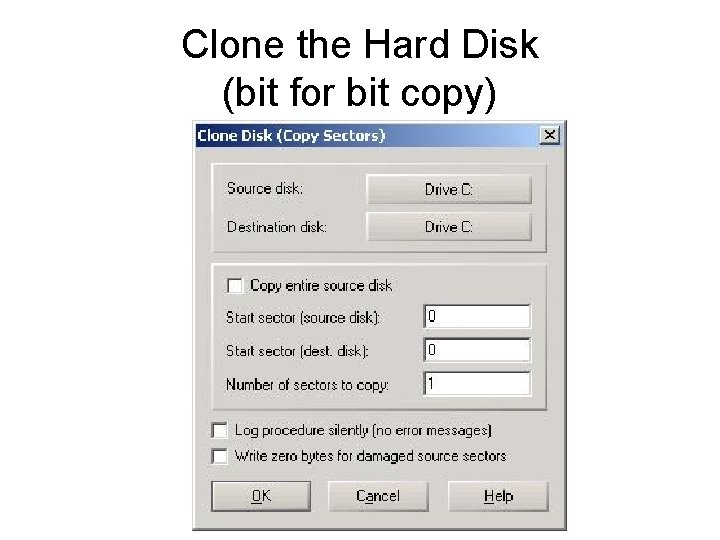
Prep Destination disk(s) • To be on the safe side, before cloning the hard disk, it is a good idea to wipe the drive that will house the clone. This helps eliminate any question that data found on the disk could have originated on your system. • I used Quick. Wiper as an example
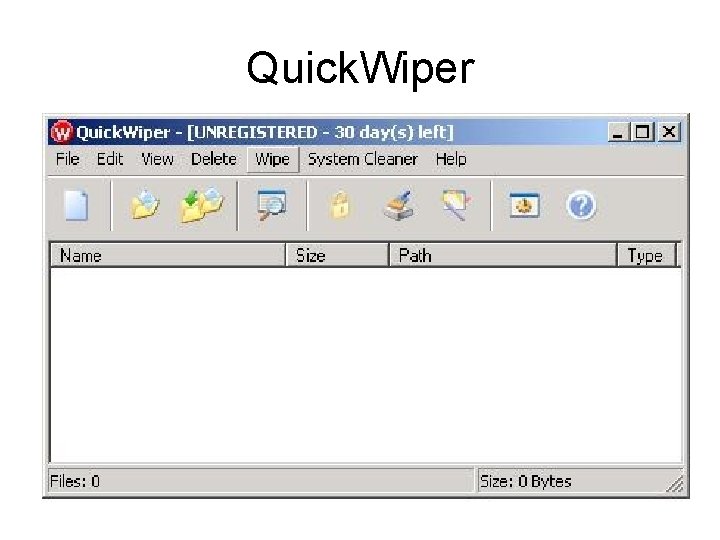
Quick. Wiper
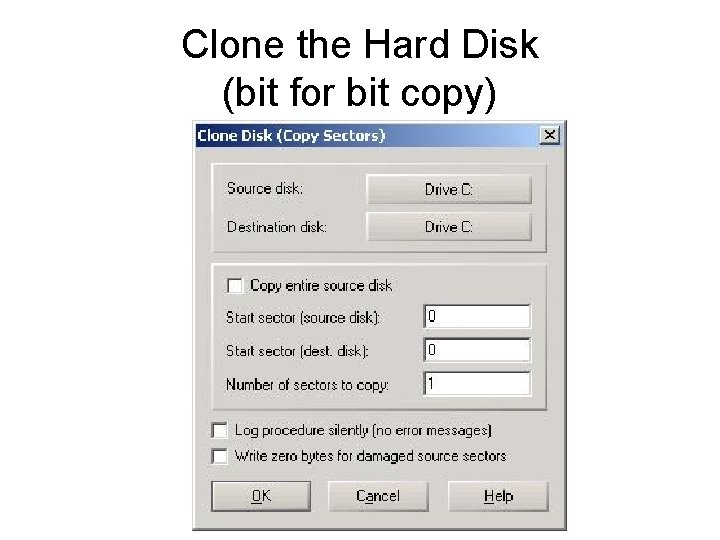
Clone the Hard Disk (bit for bit copy)
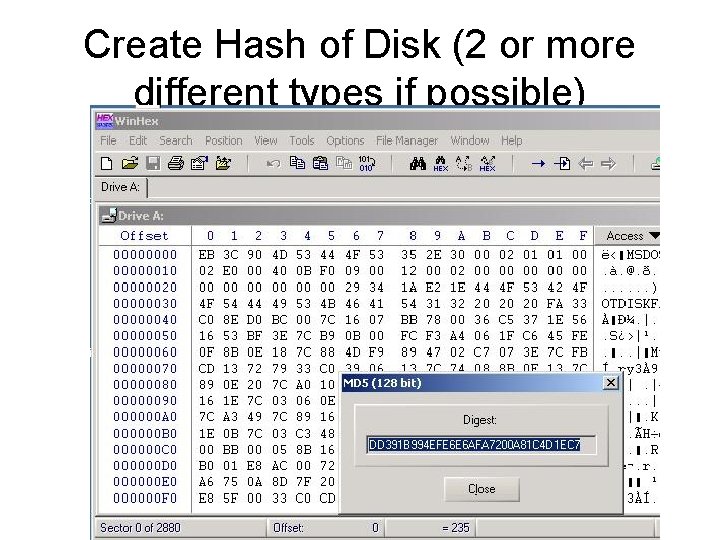
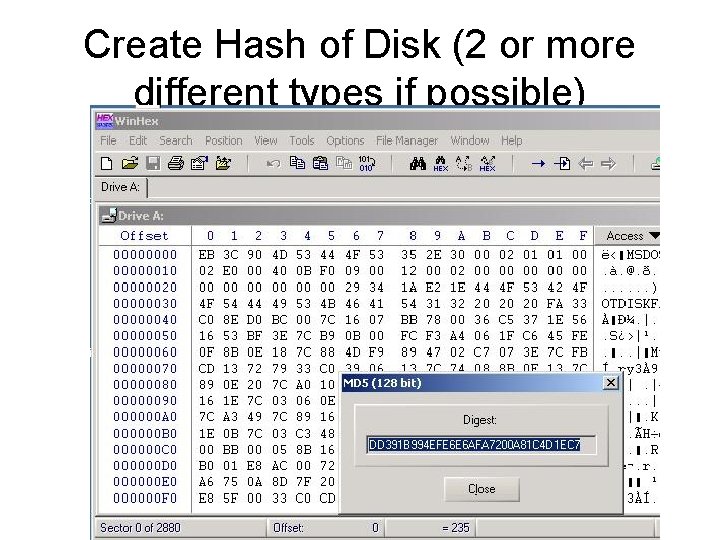
Create Hash of Disk (2 or more different types if possible)
Time Stamp the Evidence • Using a service such as digistamp, it is a good idea to timestamp the evidence to help prove that you made no additional changes to the media.
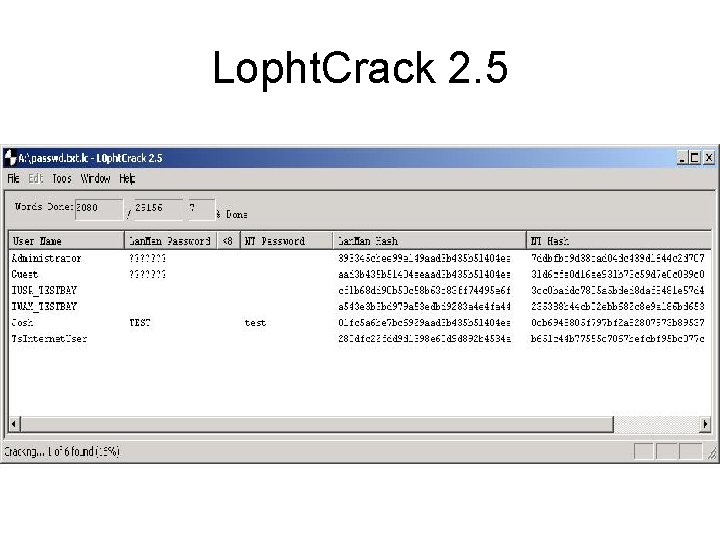
Begin the Analysis • Never work on the original media. Always use the copy. • I conducted my analysis within windows itself. • First I cracked the passwords so I could log in.
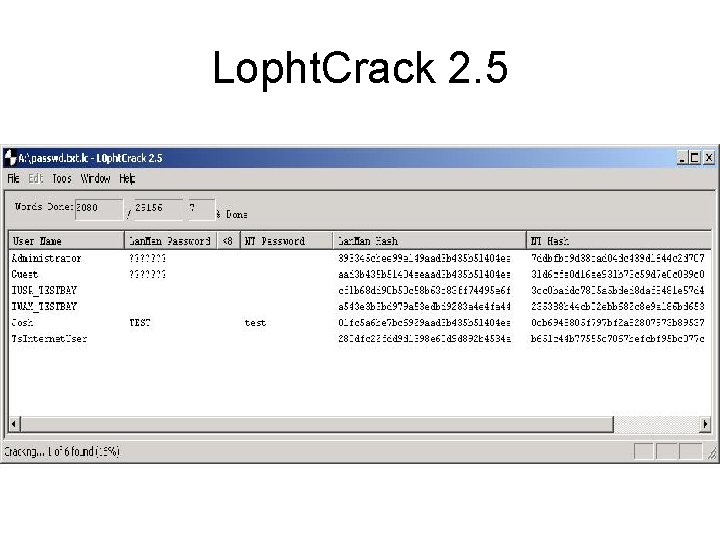
Lopht. Crack 2. 5
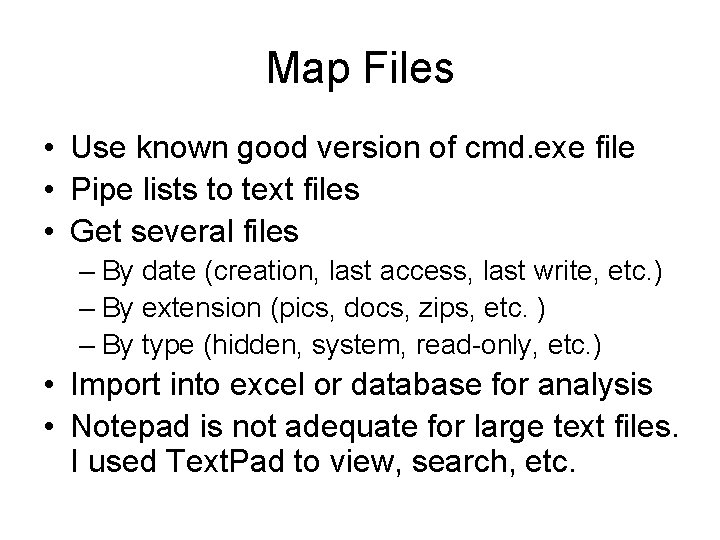
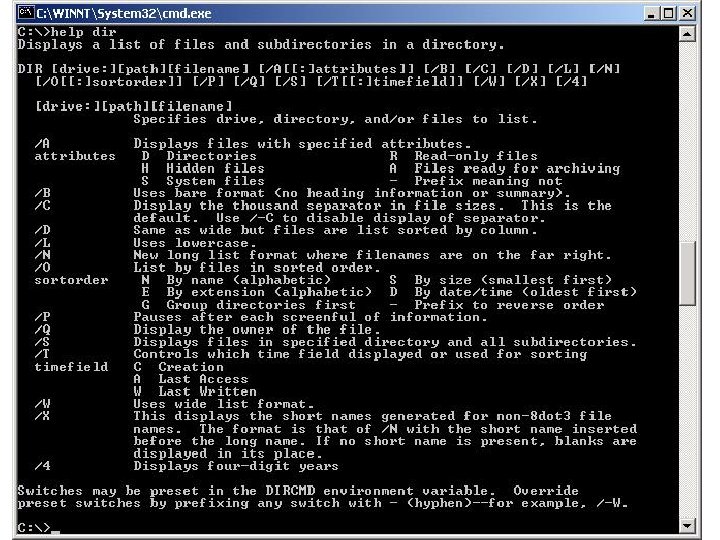
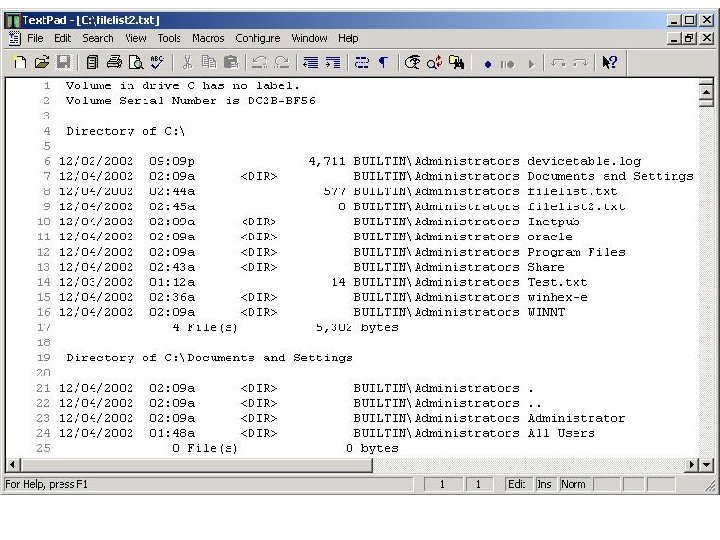
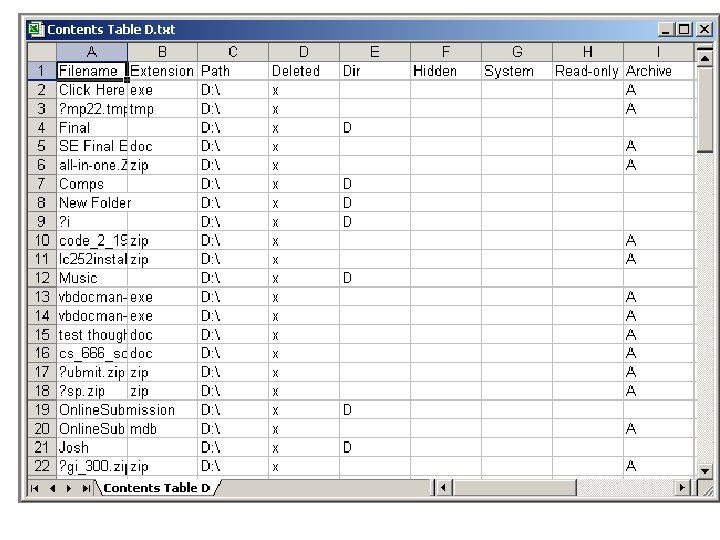
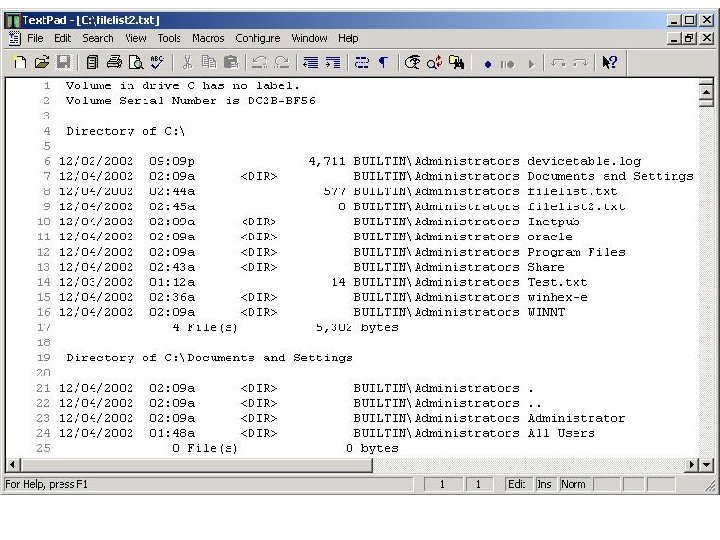
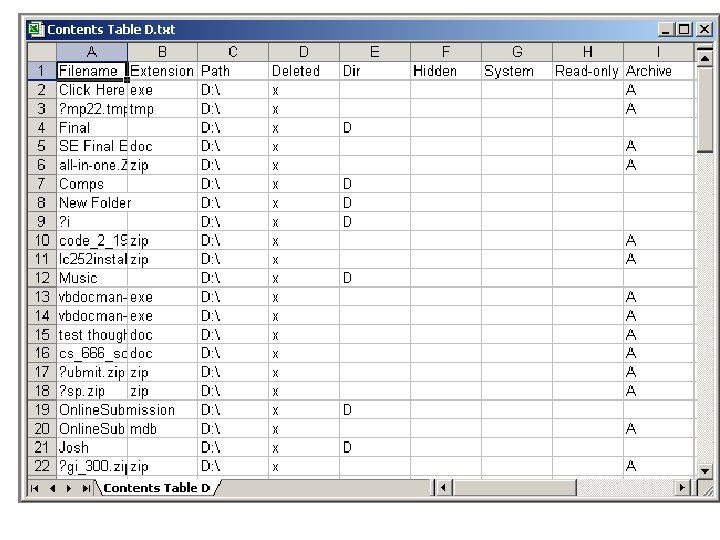
Map Files • Use known good version of cmd. exe file • Pipe lists to text files • Get several files – By date (creation, last access, last write, etc. ) – By extension (pics, docs, zips, etc. ) – By type (hidden, system, read-only, etc. ) • Import into excel or database for analysis • Notepad is not adequate for large text files. I used Text. Pad to view, search, etc.
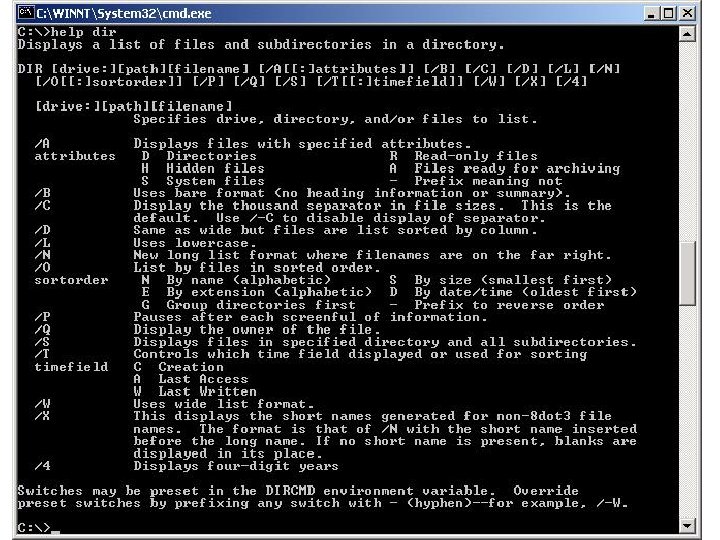
Dir Command • • • Dir c: /Q /S /TA >d: File. List 1. txt Q displays owner S causes recursive list TA displays last access time Took about 5 minutes to run Produced a 4. 5 Meg File
Objective • Focus on typical use of the computer • Focus on possible illegal activities – Illegal Material (Piracy and/or outlawed content) – Hacking – Unauthorized Data • Focus on Information Collection – Contacts – Account Numbers – Passwords
I searched for 4 types of data • Configuration – System Information – Networking Parameters – Installed Programs • Regular – documents, email, keyword, zipped, etc. • Deleted – Recycle Bin – Marked for deletion but still recoverable – Left Over Registry Entries • Hidden – – – Slack/Free Space Steganalysis Encrypted Altered File Types Streams
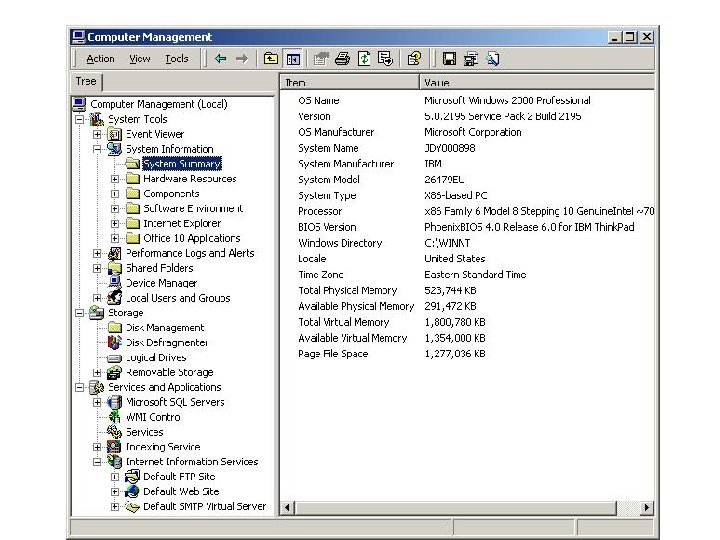
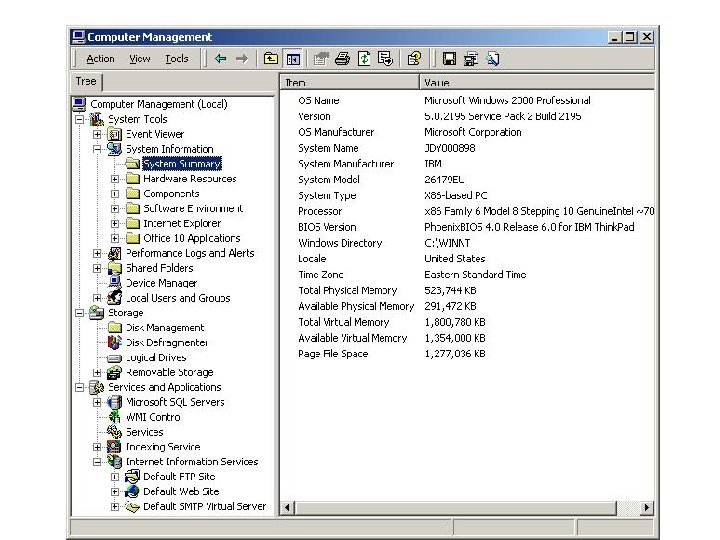
System Info • On top of data obtained by the Linux Bootable Toolkit (shown before), the information contained under the start menu/settings/control panel details the system – All Administrative tools are there – Date/Time, System, Hardware Settings – Disk Tools – Computer Management Application
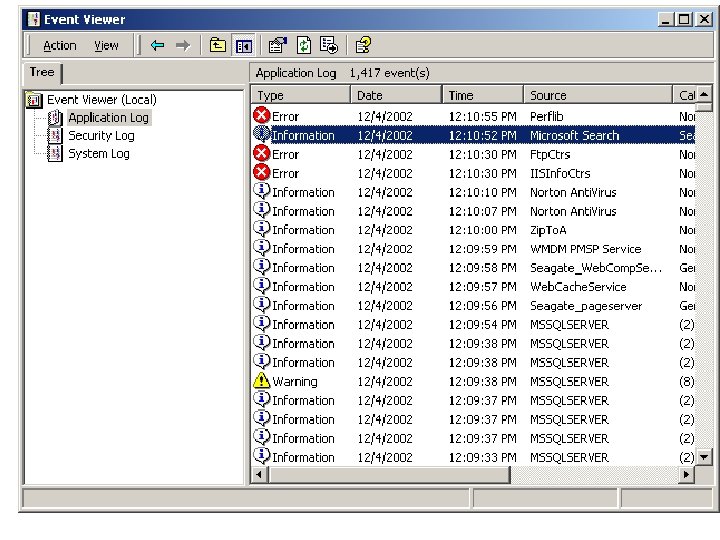
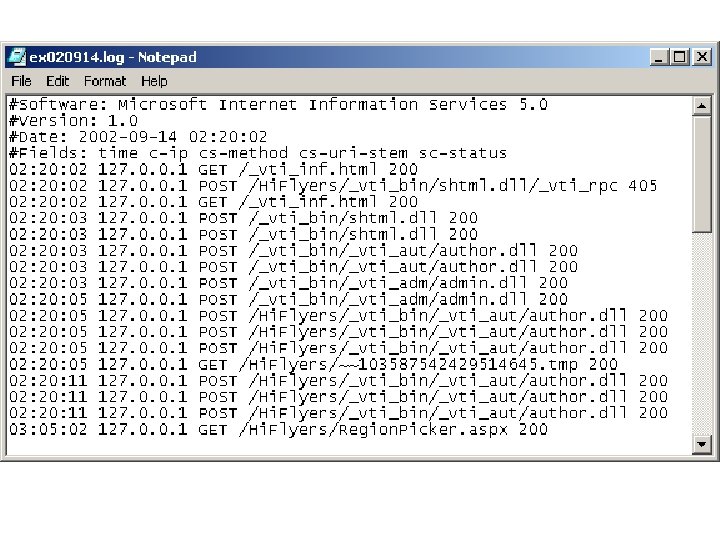
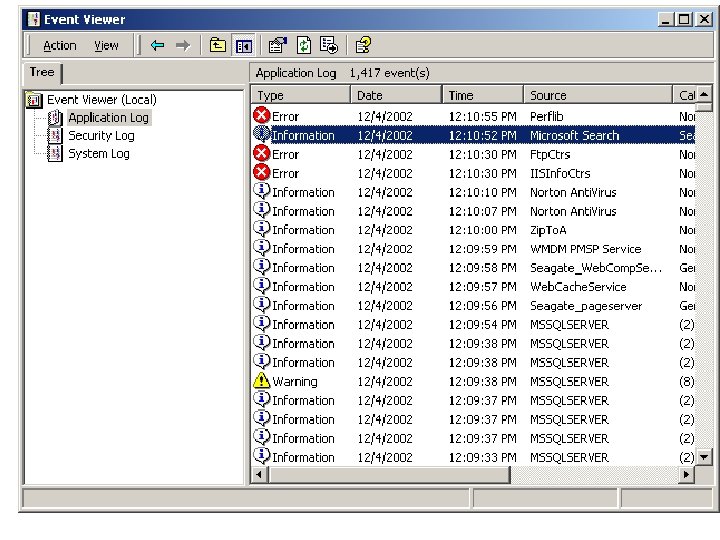
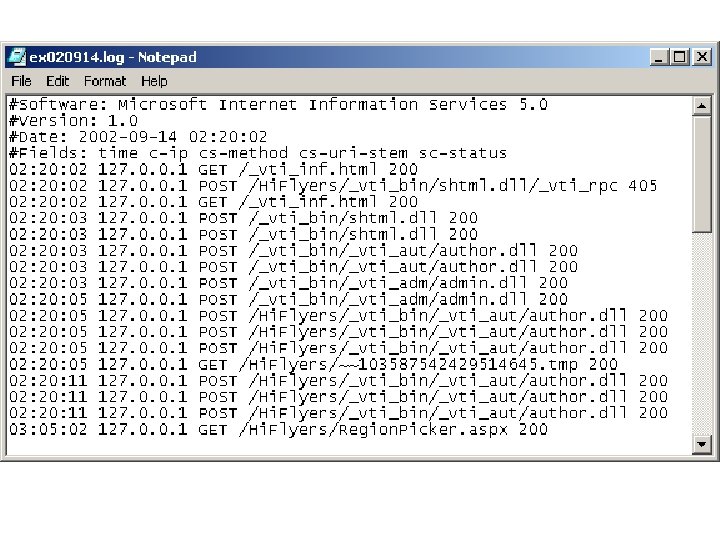
Specific things to look for in configuration • • • Web Site(s) FTP Site(s) Terminal Services DNS or Mail Services Running Log Files – Event. Viewer – C: WINNTsystem 32Log. Files
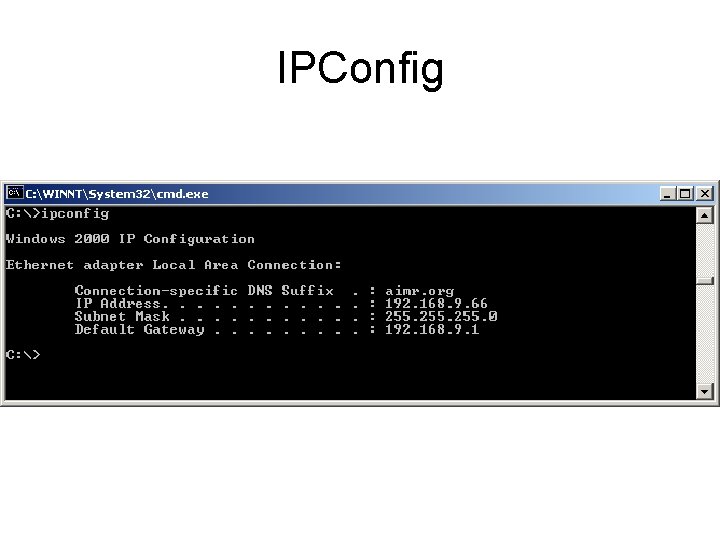
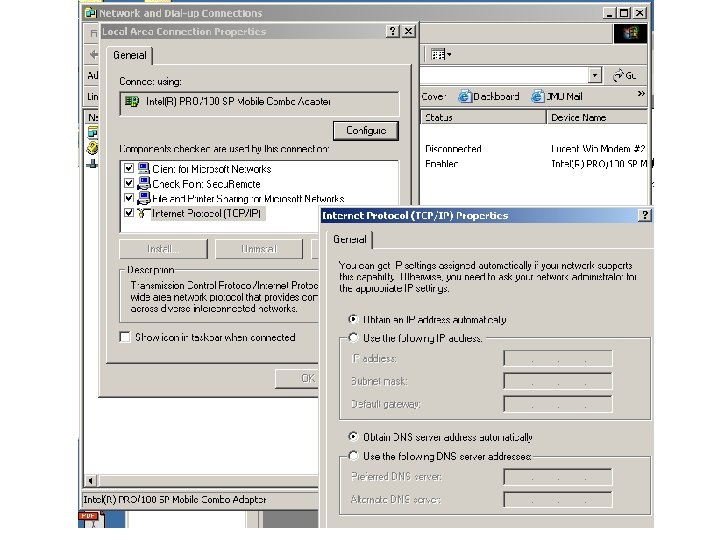
Network Parameters • Simple IPConfig command • Windows Network Dialog – Start Menu/Settings/Network and Dialup Connections
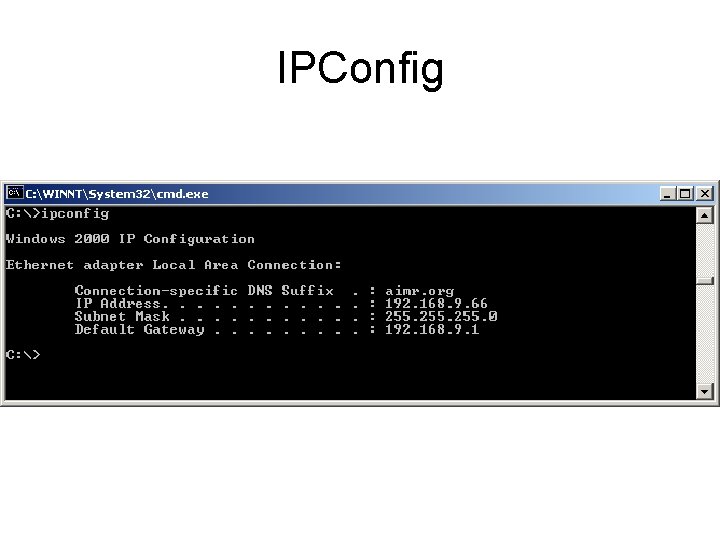
IPConfig
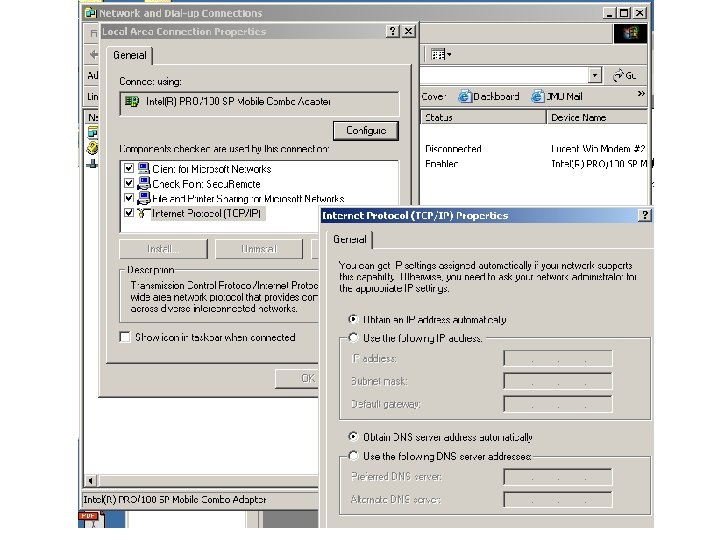
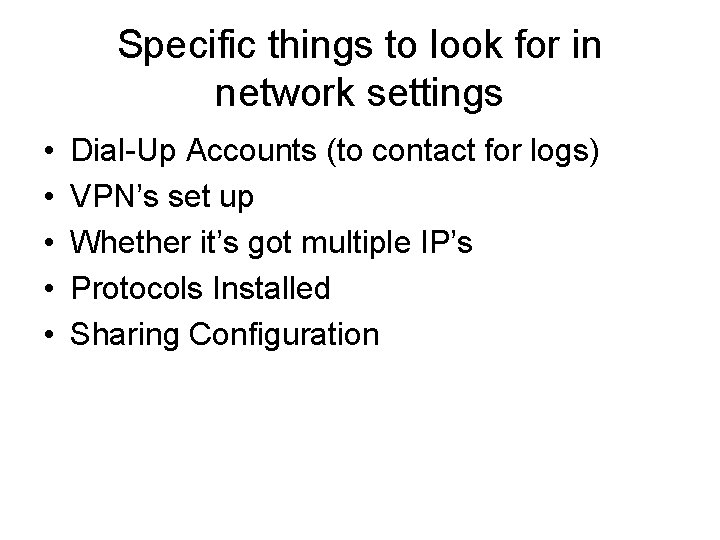
Specific things to look for in network settings • • • Dial-Up Accounts (to contact for logs) VPN’s set up Whether it’s got multiple IP’s Protocols Installed Sharing Configuration
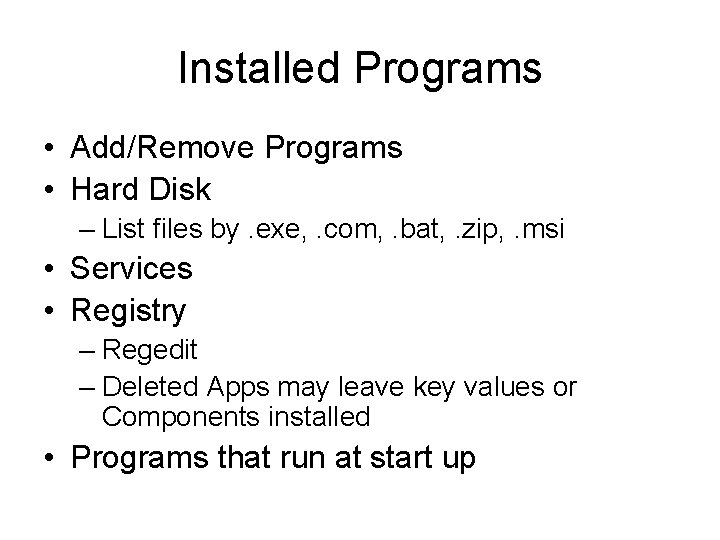
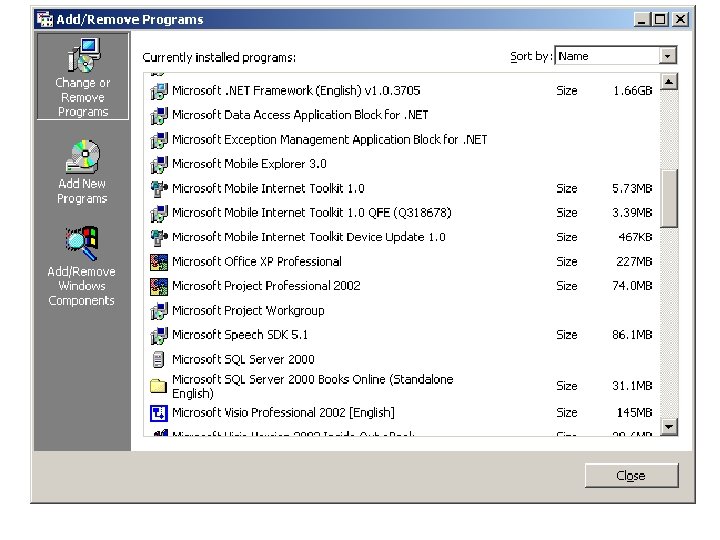
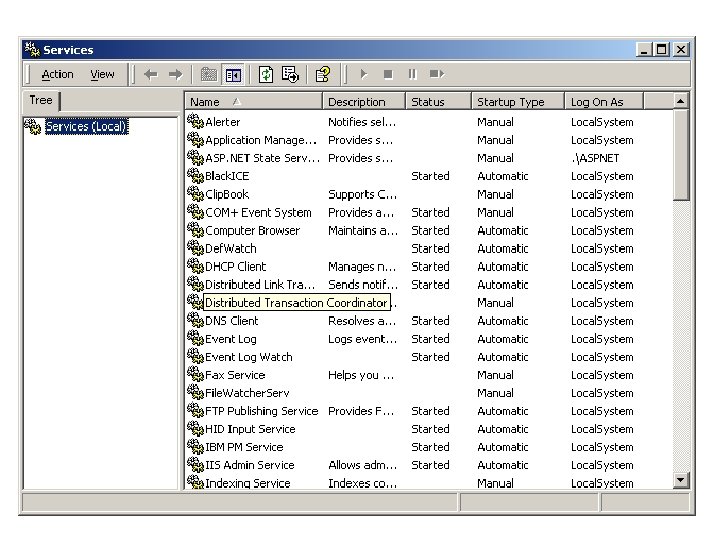
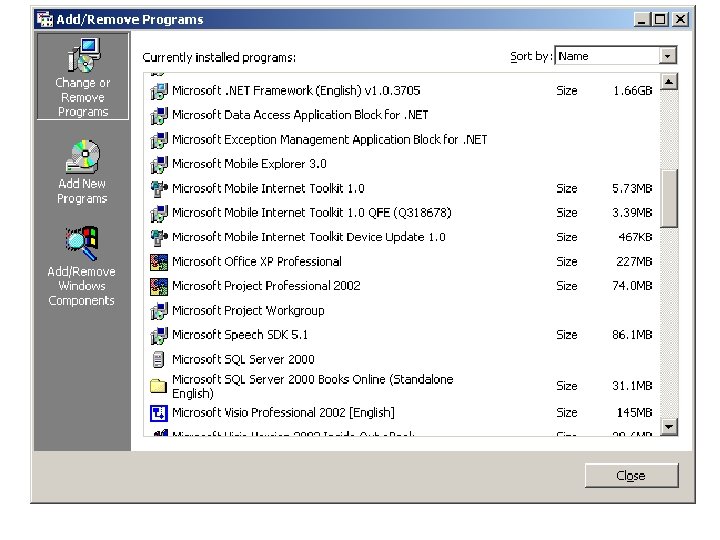
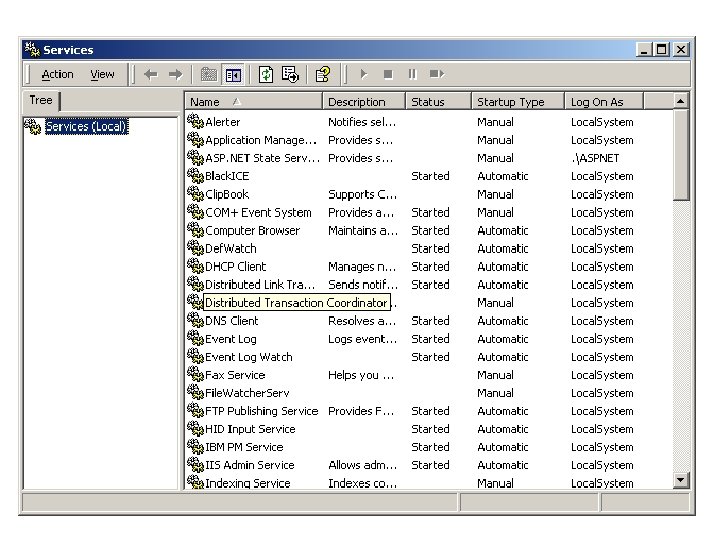
Installed Programs • Add/Remove Programs • Hard Disk – List files by. exe, . com, . bat, . zip, . msi • Services • Registry – Regedit – Deleted Apps may leave key values or Components installed • Programs that run at start up
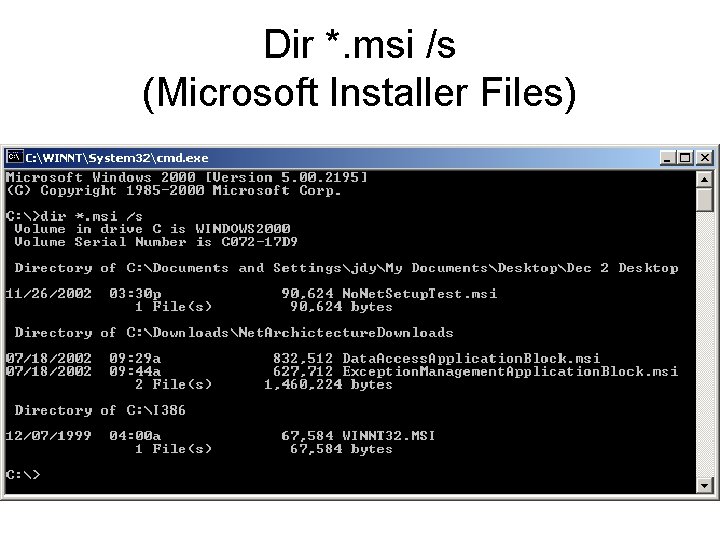
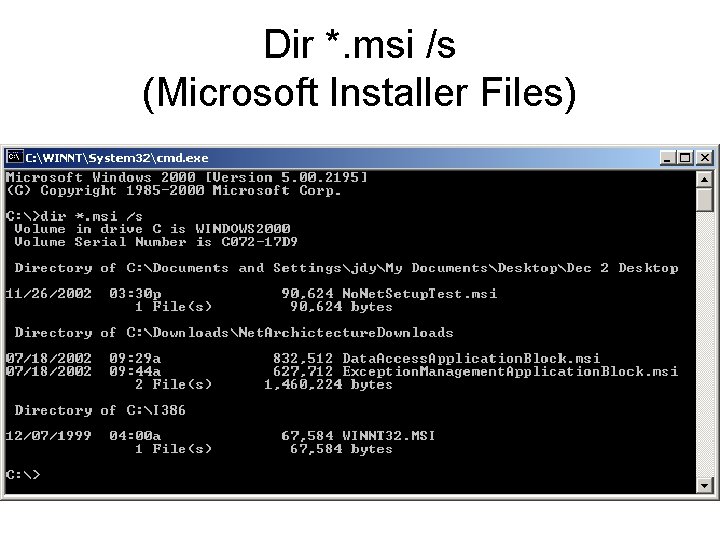
Dir *. msi /s (Microsoft Installer Files)
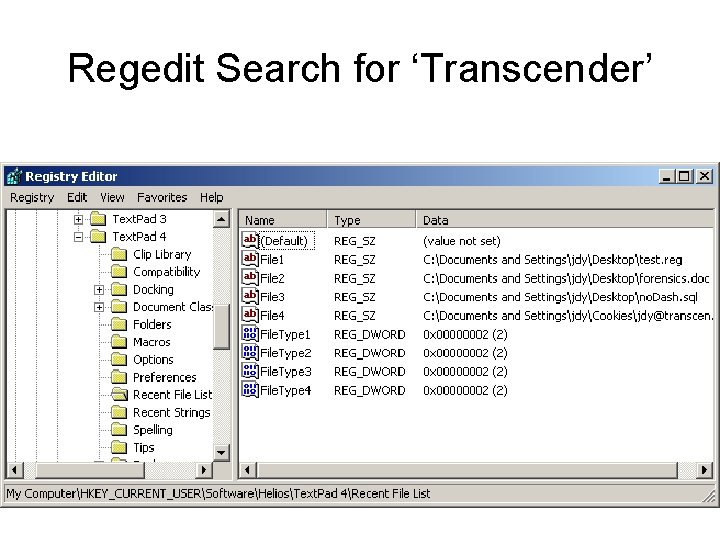
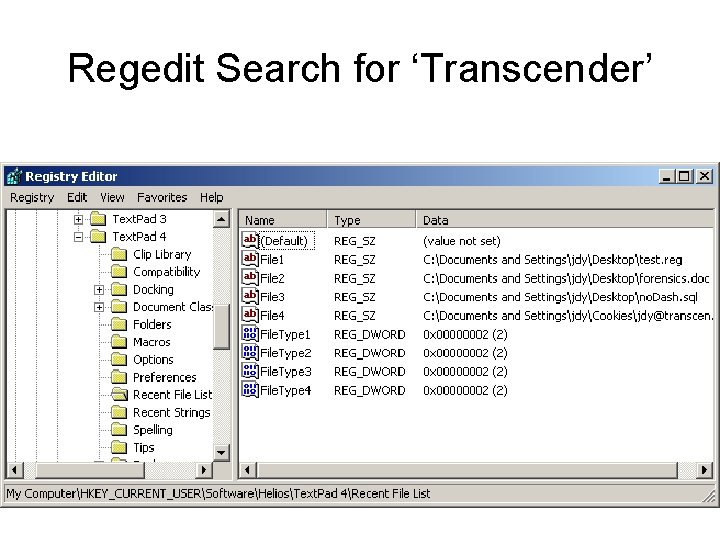
Regedit Search for ‘Transcender’
Start Up Programs • Start Menu For each user • Regkey: – HKEY_LOCAL_MACHINE – HKEY_CURRENT_USER • Software/microsoft/windows/currentversion – Runonceex

Specific things to look for in Installed Programs • Hacking/Cracking Tools – – Encryption Data Hiding Sniffers Password Crackers • Illegal Software – Bootleg Software • Registered Software • Development Tools • Financial Software
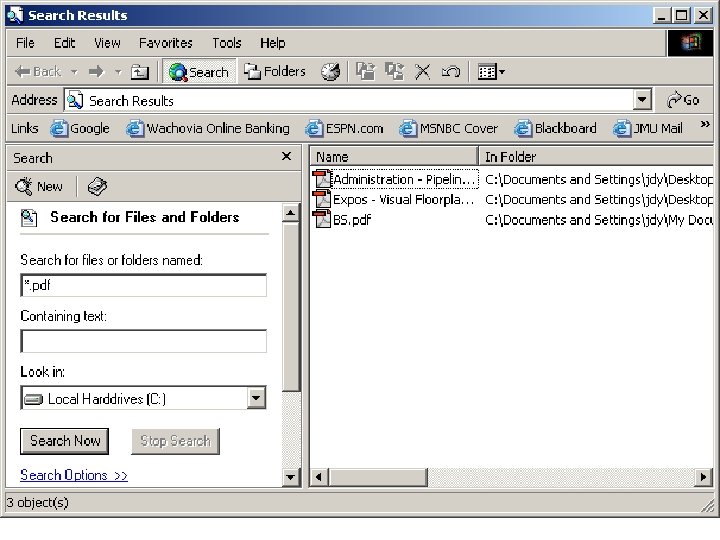
Regular Data • • Pictures Office Docs (Word, Wordperfect, Excel, etc. ) Emails Wav Files Movie Files PDF Files Search for ‘Common File Types’ on www. google. com returns many sites that list common extensions and their viewers.
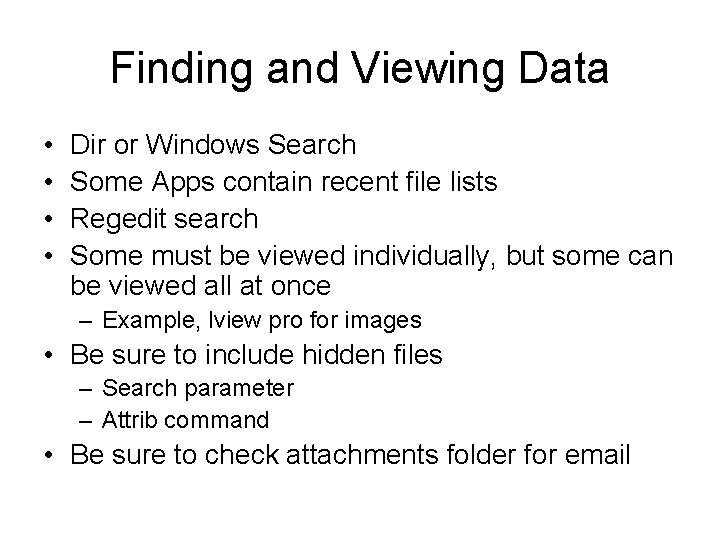
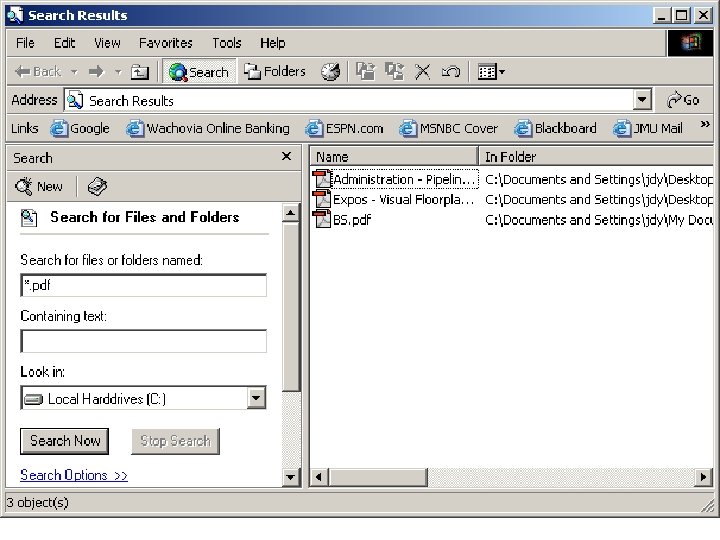
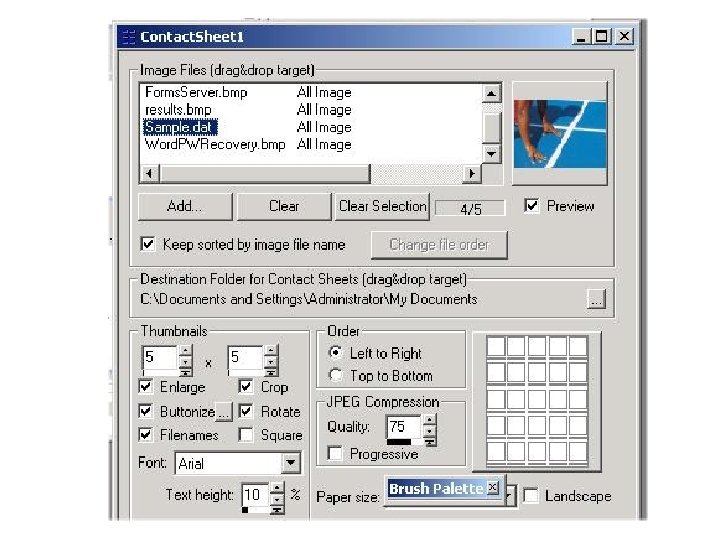
Finding and Viewing Data • • Dir or Windows Search Some Apps contain recent file lists Regedit search Some must be viewed individually, but some can be viewed all at once – Example, lview pro for images • Be sure to include hidden files – Search parameter – Attrib command • Be sure to check attachments folder for email
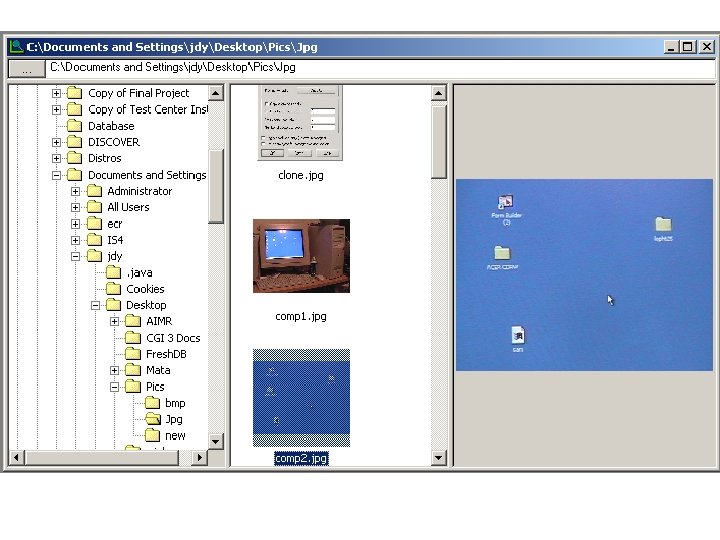
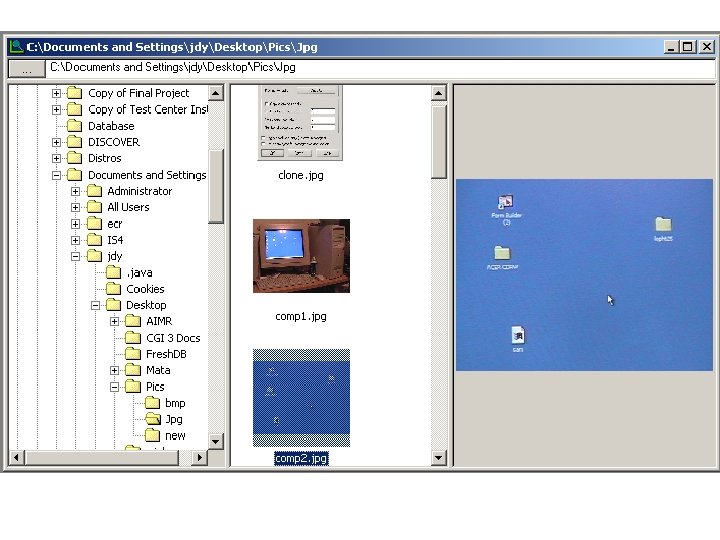
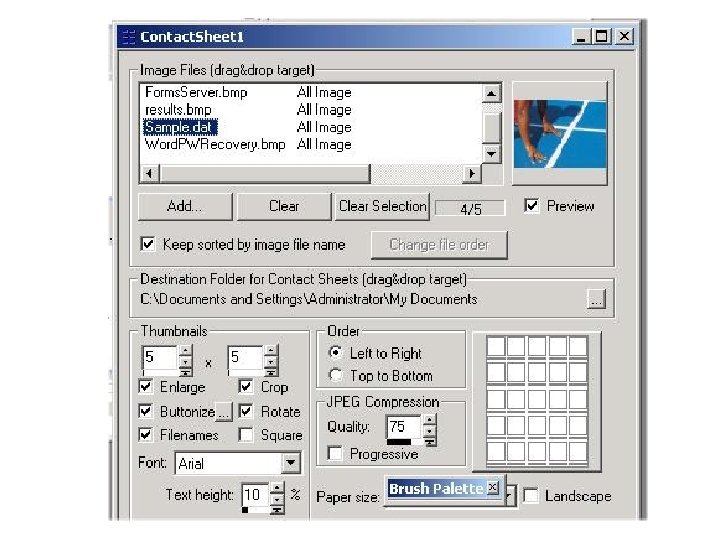
Advantages to Lview • Opens all common image files • Presents in many formats (slideshow, contact sheet, etc. ) • Preview pane • Can pass a file list from command line (obtained by something like the Dir command) • Does not rely on extension – Will open. jpg file even if extension is wrong
If Docs are encrypted… • Several Inexpensive utilities can break passwords on many common files. – Access. Data – Cain • Keys may be found written down or stored electronically in plaintext (via textfiles)
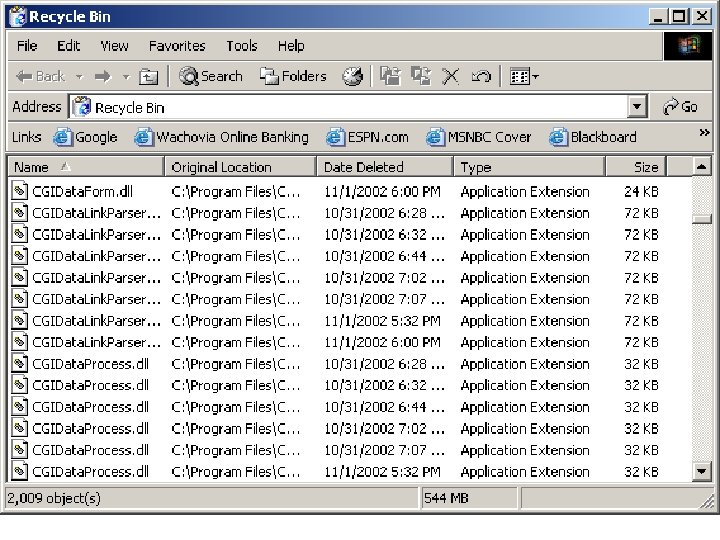
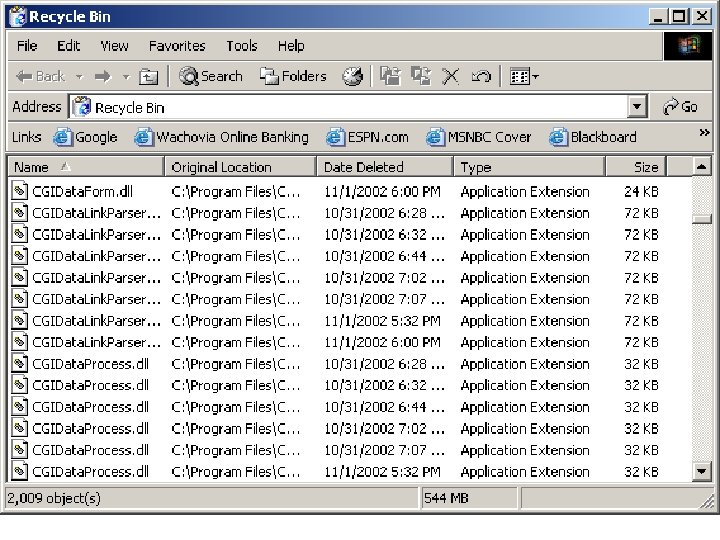
Deleted Data • Recycle Bin • Marked For Delete but recoverable – Trial Version of Norton doesn’t work on NT – Win. Hex will list deleted files, but has limited recovery capability (fragmentation hinders it). • Registry Search – Keys are often left over • Important to do on an unaltered copy of the drive
Web Info • • History Cache Cookies Tools I tried didn’t work
Hidden Data • Important to do these tests on an unaltered copy of the drive • Free/Slack/Swap Space • Staganalysis • Encryption • Altered File Types • Streams
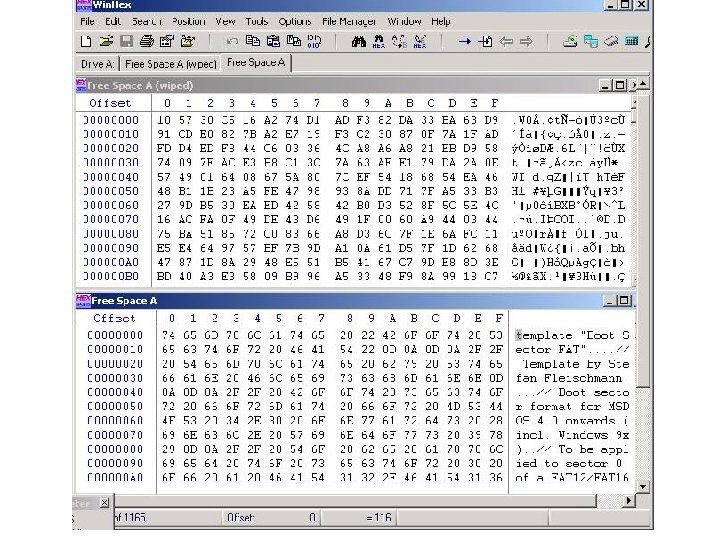
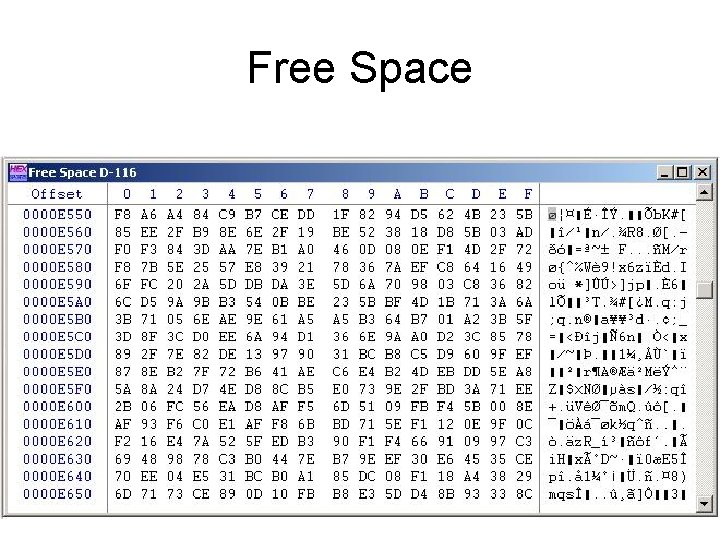
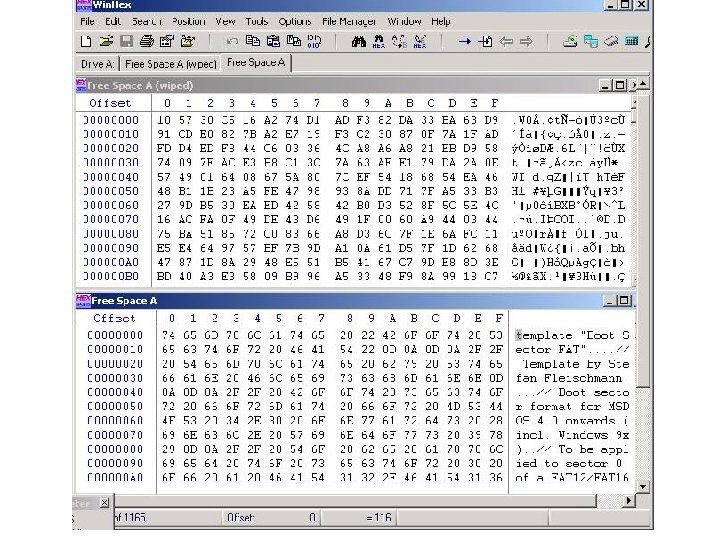
Free/Slack/Swap Space • Swap Space is a file on Windows • Free Space is space marked available to write to in Windows • Slack Space is unused space at the end of a file • Used Win. Hex
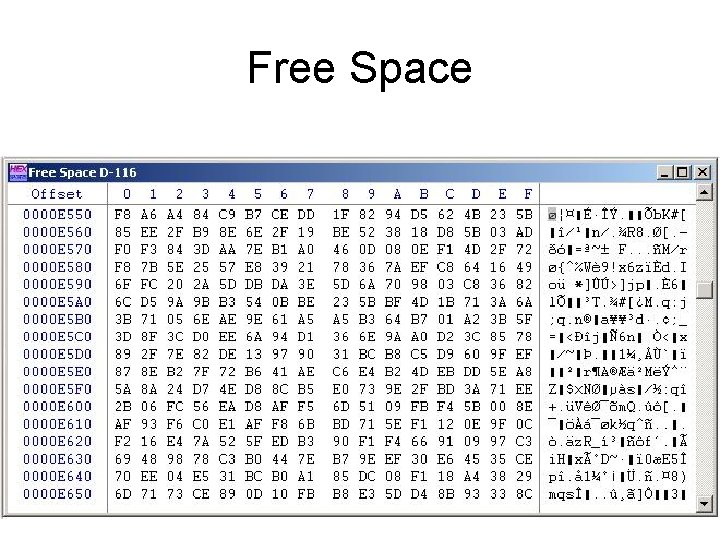
Free Space
Altered File Types • Software can detect files via their headers • Most apps will open their own files correctly if pointed to them directly • Some applications serve as multipurpose. For example, word opens most document types. LView. Pro opens most image types.
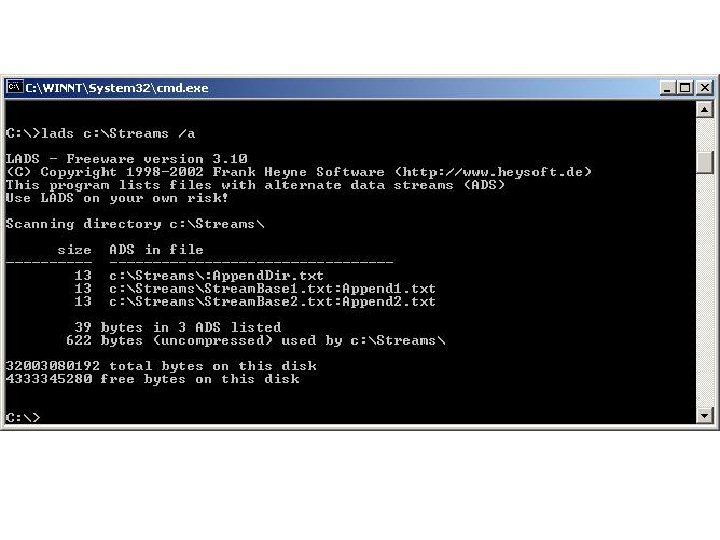
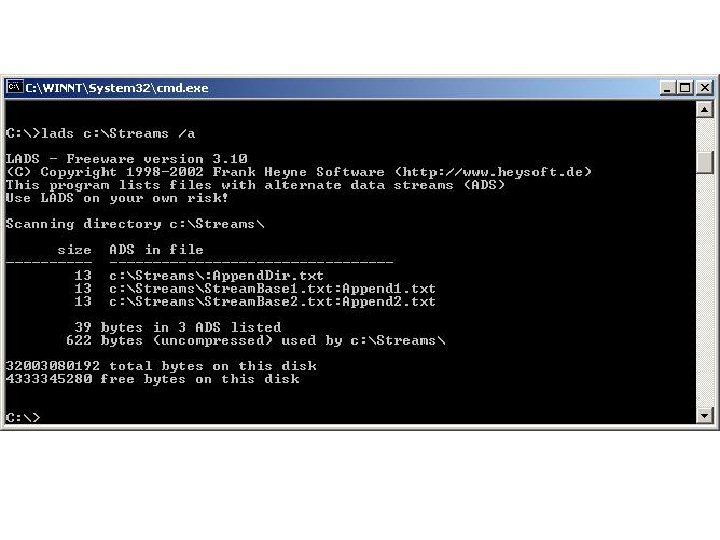
Alternate Data Streams • Originated to provide compatibility with Macintosh Hierarchical File System (HFS) • Invisible using standard windows browsing utilities. • Free program Lads will display all streams
Steganalysis and Encryption • Both very effective at hiding data, especially when used together. • Detection is difficult, but actually recovering the data can be unfeasible for most analysts. • Most common means of detection is the presence of software utilities used for Steganography or Encryption • Most common means of recovery is poor password security. Either passwords are found via other applications or written down.
Conclusion • Was able to accumulate a considerable amount of information from a default Windows 2000 Server machine • Several tools and techniques didn’t work as described in research. Windows is getting better. • If secured correctly, I don’t know that I would have been able to recover much information at all.