Force Information Security Brief Information Security is YOUR
Force Information Security Brief Information Security is YOUR Responsibility Page 1 Lincolnshire Police 2008. All rights reserved.
Contents • • • Page 2 What is information? What is Information Security? Physical Access Government Protective Marking Scheme Computer Access Intranet/Internet & E-Mail Access Clear Desk Policy Security Incident Reporting Your Responsibility Lincolnshire Police 2008. All rights reserved.
What Is Information? • • • Page 3 The spoken word Computer systems Mobile computing/mobile communications Voice mail, telephone & voice communications Multimedia Fax Machines Voice or other recording Postal services/facilities Paper-based mail • • • Pocket books Police diary Output reports One-time-use printer ribbons Magnetic tapes Removable disks or cassettes User Manuals Video Recordings Photographs Confidential waste Paper-based documents/files Lincolnshire Police 2008. All rights reserved.
What is Information Security? Information security is protecting information and information systems from unauthorised access, use, disclosure, disruption, modification, perusal, inspection, recording or destruction Page 4 C Confidentiality – Preventing the disclosure of information to unauthorised individuals or systems. I Integrity – Safeguarding the accuracy and completeness of the information. A Availability – Information being accessible and usable upon demand by an authorised user or body Lincolnshire Police 2008. All rights reserved.
Physical Access Controls • Door Controls • Locked Drawers & Cabinets • Visitors • Challenge • Don’t Tailgate! • Passes • Contractors Page 5 Lincolnshire Police 2008. All rights reserved.
Government Protective Marking Scheme (GPMS) • Information is graded on its value in terms of the damage that is likely to result from that information being compromised • • • NOT PROTECTIVELY MARKED PROTECT (with descriptor) RESTRICTED CONFIDENTIAL SECRET TOP SECRET It is the originators decision on which protective marking is assigned to an asset Page 6 Lincolnshire Police 2008. All rights reserved.
RESTRICTED Accidental or deliberate compromise would be likely to cause: • A risk to an individual’s personal safety or liberty • Disruption to emergency service activities that requires reprioritisation at the County or Organisational level to meet expected levels of service • Hinder the detection, impede the investigation of, or facilitate the commission of low level crime, or hinder the detection of serious crime • A low-level criminal prosecution to collapse, declared unsafe or referred for appeal • A breach of statutory restrictions on disclosure of material • An undermining of confidence in public services Page 7 Lincolnshire Police 2008. All rights reserved.
CONFIDENTIAL Impact level 4 Accidental or deliberate compromise would be likely to cause: • A risk to a group of individuals safety or liberty • Disruption to emergency service activities that requires reprioritisation at national level to meet expected levels of service • Impeding of the investigation of, or facilitate the commission of serious crime • A serious crime prosecution to collapse, declared unsafe or referred to appeal Page 8 Lincolnshire Police 2008. All rights reserved.
Government Security Classification (GSC) Learn more through NCALT e. Learning, Security Bulletins and the Intranet Page 9 Lincolnshire Police 2008. All rights reserved.
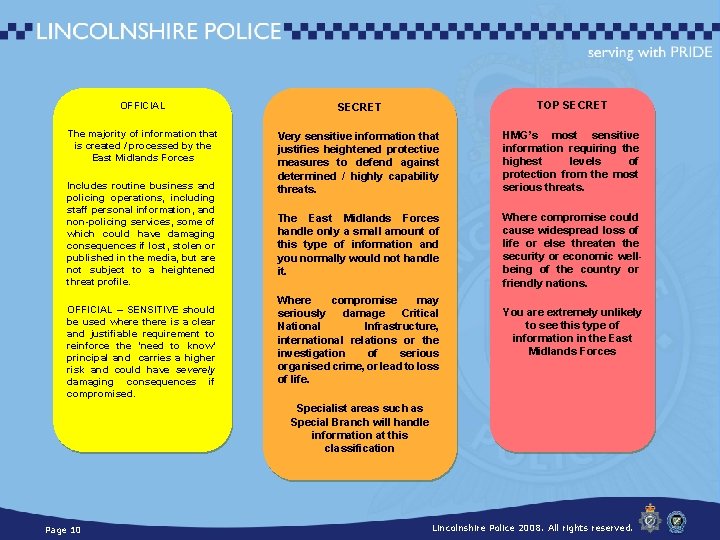
OFFICIAL SECRET TOP SECRET The majority of information that is created / processed by the East Midlands Forces Very sensitive information that justifies heightened protective measures to defend against determined / highly capability threats. HMG’s most sensitive information requiring the highest levels of protection from the most serious threats. The East Midlands Forces handle only a small amount of this type of information and you normally would not handle it. Where compromise could cause widespread loss of life or else threaten the security or economic wellbeing of the country or friendly nations. Includes routine business and policing operations, including staff personal information, and non-policing services, some of which could have damaging consequences if lost, stolen or published in the media, but are not subject to a heightened threat profile. OFFICIAL – SENSITIVE should be used where there is a clear and justifiable requirement to reinforce the ‘need to know’ principal and carries a higher risk and could have severely damaging consequences if compromised. Where compromise may seriously damage Critical National Infrastructure, international relations or the investigation of serious organised crime, or lead to loss of life. You are extremely unlikely to see this type of information in the East Midlands Forces Specialist areas such as Special Branch will handle information at this classification Page 10 Lincolnshire Police 2008. All rights reserved.
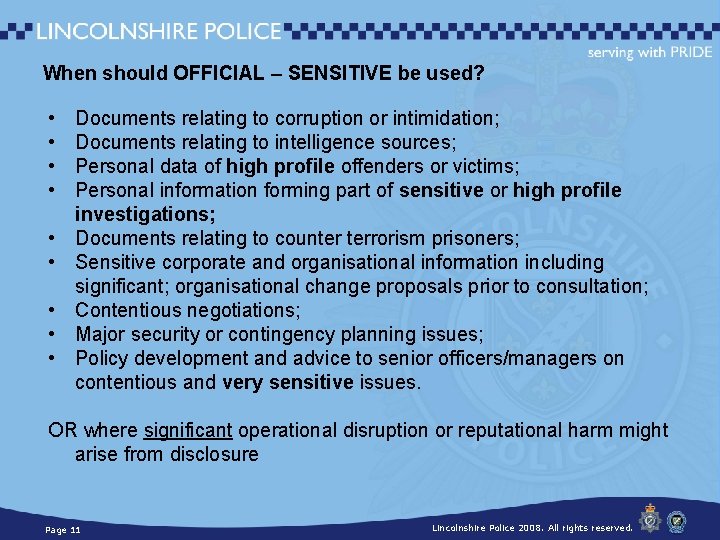
When should OFFICIAL – SENSITIVE be used? • • • Documents relating to corruption or intimidation; Documents relating to intelligence sources; Personal data of high profile offenders or victims; Personal information forming part of sensitive or high profile investigations; Documents relating to counter terrorism prisoners; Sensitive corporate and organisational information including significant; organisational change proposals prior to consultation; Contentious negotiations; Major security or contingency planning issues; Policy development and advice to senior officers/managers on contentious and very sensitive issues. OR where significant operational disruption or reputational harm might arise from disclosure Page 11 Lincolnshire Police 2008. All rights reserved.
Applying Handling Instructions should be written on the front page of any document, and at the top of each page. These instructions should identify: Why special handling is required; Who is to be allowed access to the information; How that information or data is allowed (or not) to be circulated or forwarded and How it is to be stored. Page 12 Lincolnshire Police 2008. All rights reserved.
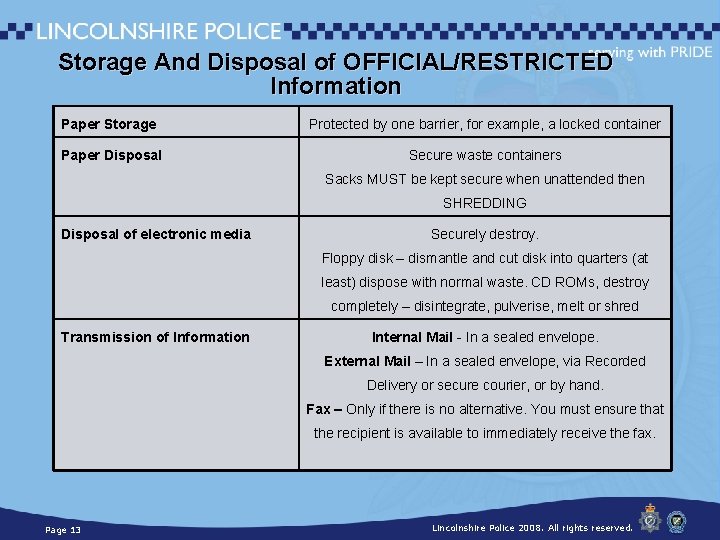
Storage And Disposal of OFFICIAL/RESTRICTED Information Paper Storage Protected by one barrier, for example, a locked container Paper Disposal Secure waste containers Sacks MUST be kept secure when unattended then SHREDDING Disposal of electronic media Securely destroy. Floppy disk – dismantle and cut disk into quarters (at least) dispose with normal waste. CD ROMs, destroy completely – disintegrate, pulverise, melt or shred Transmission of Information Internal Mail - In a sealed envelope. External Mail – In a sealed envelope, via Recorded Delivery or secure courier, or by hand. Fax – Only if there is no alternative. You must ensure that the recipient is available to immediately receive the fax. Page 13 Lincolnshire Police 2008. All rights reserved.
Computer Access • Access systems necessary to do your job only • Search systems for a policing purpose only • Password control • Log off or lock your screen when it is unattended • Only use force supplied encrypted USB sticks • Do not e-mail or upload force information onto personal computers Page 14 Lincolnshire Police 2008. All rights reserved.
Intranet/Internet & E-Mail Access Page 15 • Personal use of Internet is permitted during recognised breaks only • Sites such as gambling, violence, hatred, sexual content …are not to be accessed unless for a Policing purpose • Secure addresses only e. g. pnn, gsi Lincolnshire Police 2008. All rights reserved.
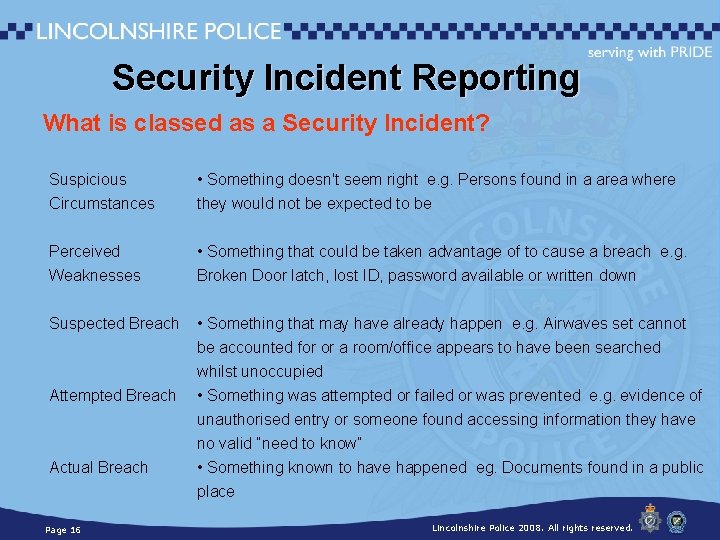
Security Incident Reporting What is classed as a Security Incident? Suspicious Circumstances • Something doesn't seem right e. g. Persons found in a area where they would not be expected to be Perceived Weaknesses • Something that could be taken advantage of to cause a breach e. g. Broken Door latch, lost ID, password available or written down Suspected Breach • Something that may have already happen e. g. Airwaves set cannot be accounted for or a room/office appears to have been searched whilst unoccupied • Something was attempted or failed or was prevented e. g. evidence of unauthorised entry or someone found accessing information they have no valid “need to know” • Something known to have happened eg. Documents found in a public place Attempted Breach Actual Breach Page 16 Lincolnshire Police 2008. All rights reserved.
Security Incident Reporting Common & recent incidents Lost warrant cards Anti Virus incidents Physical Security - Insecure doors Unauthorised documents released Fax’s sent to wrong numbers Page 17 Lincolnshire Police 2008. All rights reserved.
NCALT Mandatory Training Page 18 • Managing Information • An Introduction to Government Security Classification (GSC) Lincolnshire Police 2008. All rights reserved.
Information Security is YOUR Responsibility! • Passwords • Challenge staff not displaying their Force badge • Follow GPMS guidelines • Report Security incidents • Adhere to the Force Clear Desk Policy Page 19 • Do not use Force IT systems for personal use • Do not disclose information to those without a valid NEED TO KNOW Lincolnshire Police 2008. All rights reserved.
Questions? Information Security is YOUR Responsibility Page 20 Lincolnshire Police 2008. All rights reserved.
- Slides: 20