Firewalls n Types of Firewalls n Inspection Methods
- Slides: 12
Firewalls n Types of Firewalls n Inspection Methods ¡ ¡ Static Packet Inspection Stateful Packet Inspection NAT Application Firewalls n Firewall Architecture n Configuring, Testing, and Maintenance 1
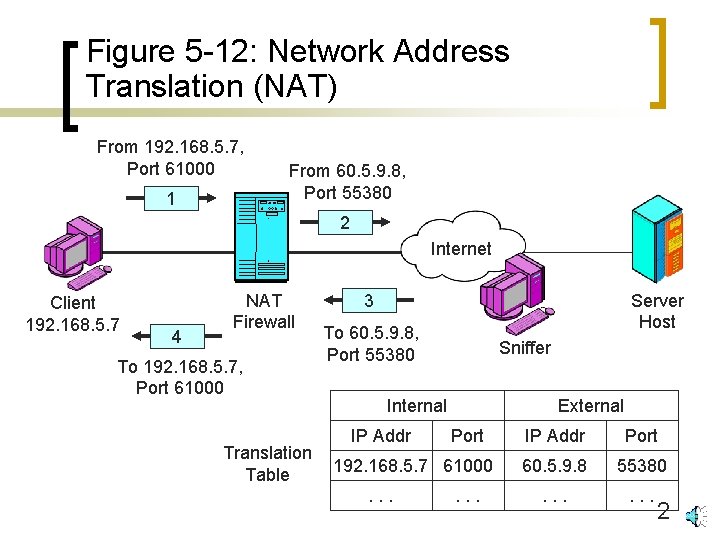
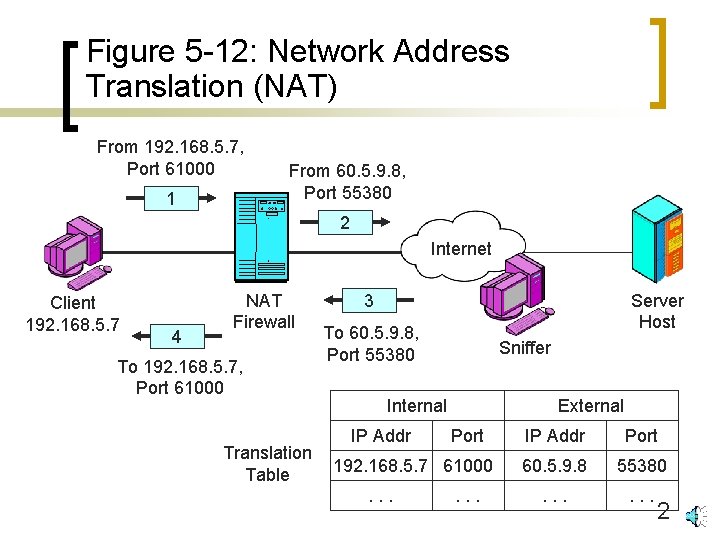
Figure 5 -12: Network Address Translation (NAT) From 192. 168. 5. 7, Port 61000 1 From 60. 5. 9. 8, Port 55380 2 Internet Client 192. 168. 5. 7 4 NAT Firewall To 192. 168. 5. 7, Port 61000 Translation Table Server Host 3 To 60. 5. 9. 8, Port 55380 Sniffer Internal IP Addr External Port 192. 168. 5. 7 61000. . . IP Addr Port 60. 5. 9. 8 55380 . . . 2
Firewalls n Types of Firewalls n Inspection Methods ¡ ¡ Static Packet Inspection Stateful Packet Inspection NAT Application Firewalls n Firewall Architecture n Configuring, Testing, and Maintenance 3
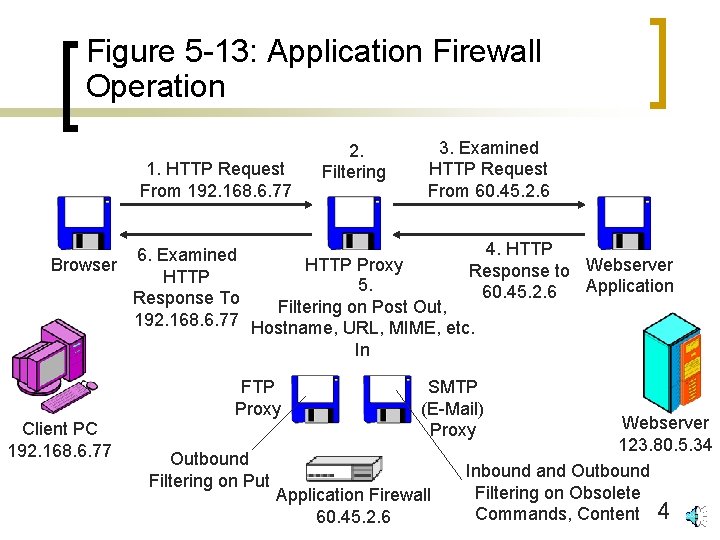
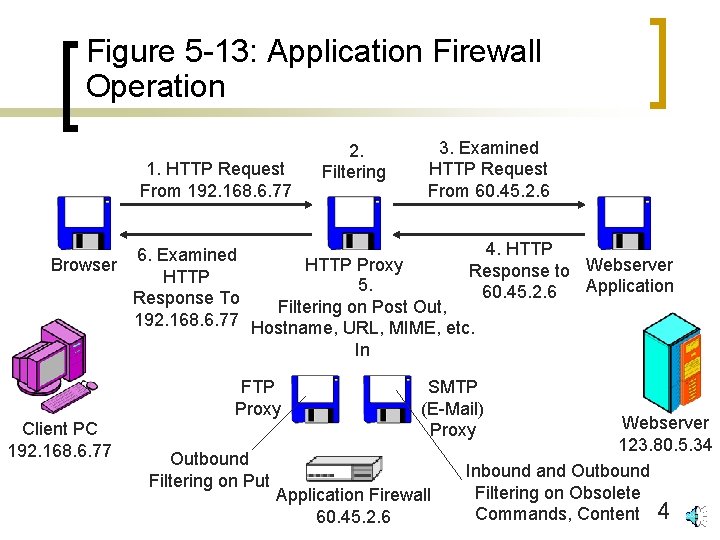
Figure 5 -13: Application Firewall Operation 1. HTTP Request From 192. 168. 6. 77 2. Filtering 3. Examined HTTP Request From 60. 45. 2. 6 4. HTTP 6. Examined Browser HTTP Proxy Response to Webserver HTTP 5. Application 60. 45. 2. 6 Response To Filtering on Post Out, 192. 168. 6. 77 Hostname, URL, MIME, etc. In FTP Proxy Client PC 192. 168. 6. 77 Outbound Filtering on Put SMTP (E-Mail) Proxy Application Firewall 60. 45. 2. 6 Webserver 123. 80. 5. 34 Inbound and Outbound Filtering on Obsolete Commands, Content 4
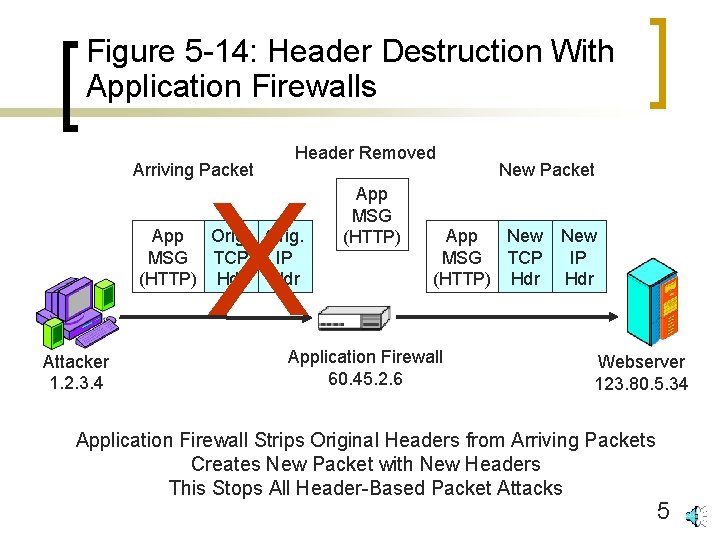
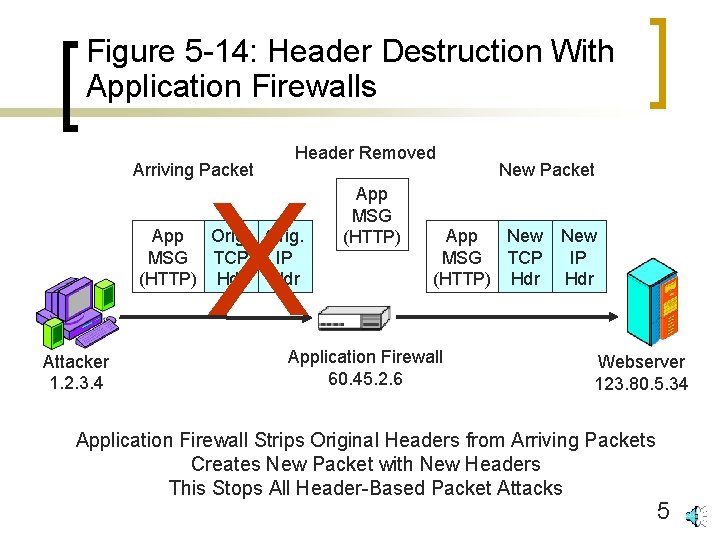
Figure 5 -14: Header Destruction With Application Firewalls Arriving Packet Header Removed X App Orig. MSG TCP IP (HTTP) Hdr Attacker 1. 2. 3. 4 App MSG (HTTP) New Packet App New MSG TCP (HTTP) Hdr Application Firewall 60. 45. 2. 6 New IP Hdr Webserver 123. 80. 5. 34 Application Firewall Strips Original Headers from Arriving Packets Creates New Packet with New Headers This Stops All Header-Based Packet Attacks 5
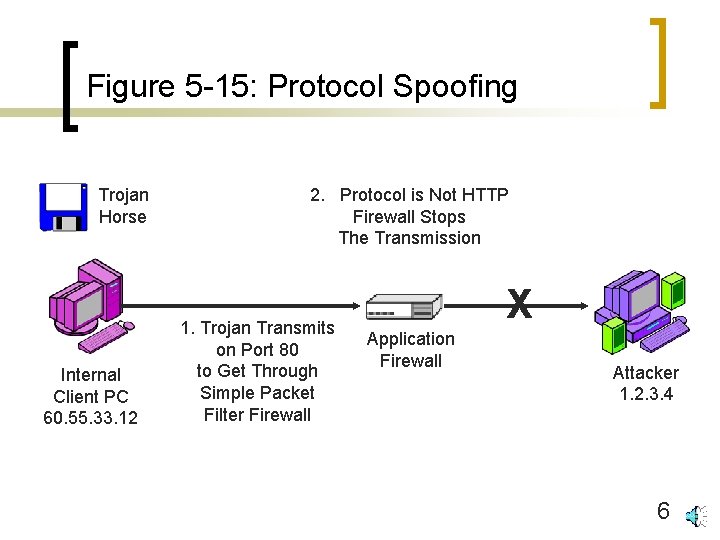
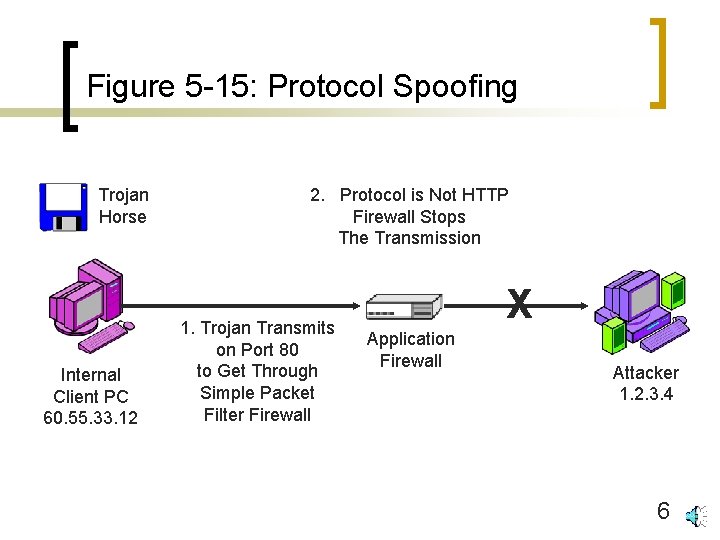
Figure 5 -15: Protocol Spoofing Trojan Horse Internal Client PC 60. 55. 33. 12 2. Protocol is Not HTTP Firewall Stops The Transmission 1. Trojan Transmits on Port 80 to Get Through Simple Packet Filter Firewall X Application Firewall Attacker 1. 2. 3. 4 6
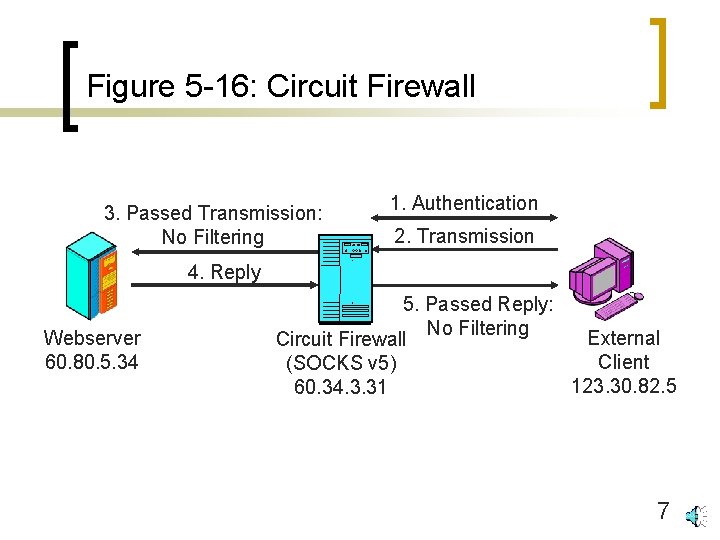
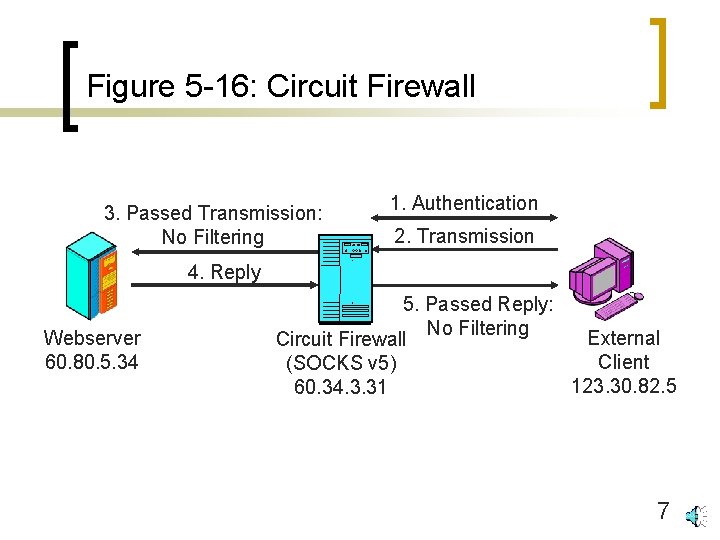
Figure 5 -16: Circuit Firewall 3. Passed Transmission: No Filtering 1. Authentication 2. Transmission 4. Reply Webserver 60. 80. 5. 34 5. Passed Reply: No Filtering External Circuit Firewall Client (SOCKS v 5) 123. 30. 82. 5 60. 34. 3. 31 7
Firewalls n Types of Firewalls n Inspection Methods n Firewall Architecture ¡ ¡ n Single site in large organization Home firewall SOHO firewall router Distributed firewall architecture Configuring, Testing, and Maintenance 8
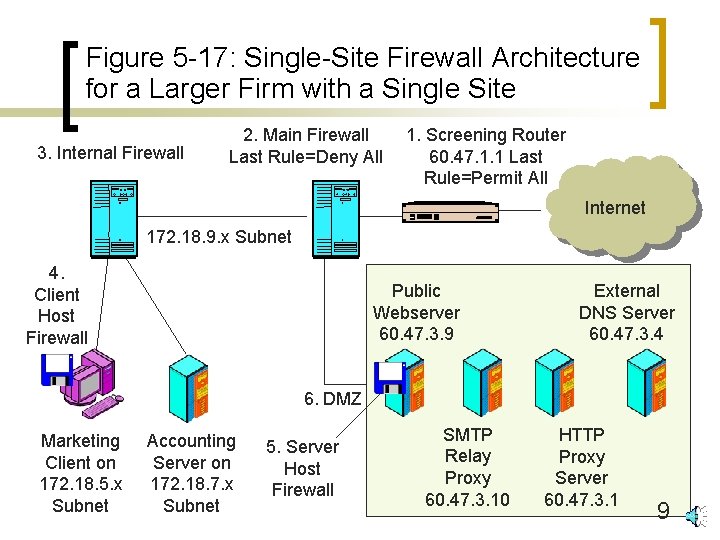
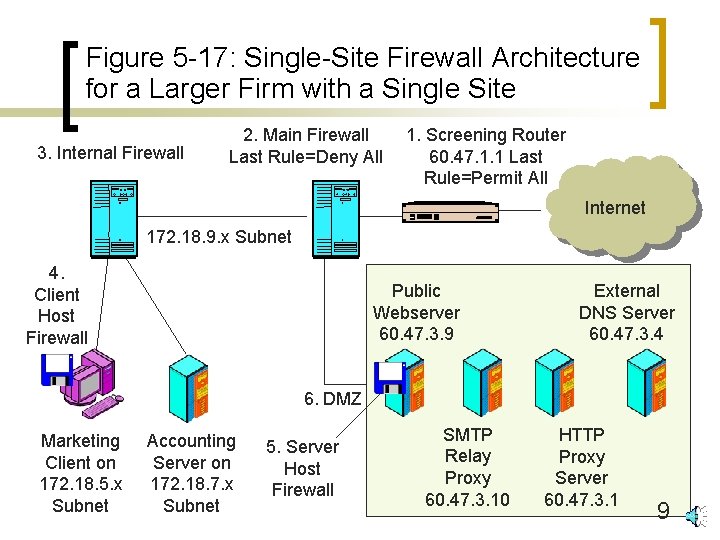
Figure 5 -17: Single-Site Firewall Architecture for a Larger Firm with a Single Site 3. Internal Firewall 2. Main Firewall Last Rule=Deny All 1. Screening Router 60. 47. 1. 1 Last Rule=Permit All Internet 172. 18. 9. x Subnet 4. Client Host Firewall Public Webserver 60. 47. 3. 9 External DNS Server 60. 47. 3. 4 6. DMZ Marketing Client on 172. 18. 5. x Subnet Accounting Server on 172. 18. 7. x Subnet 5. Server Host Firewall SMTP Relay Proxy 60. 47. 3. 10 HTTP Proxy Server 60. 47. 3. 1 9
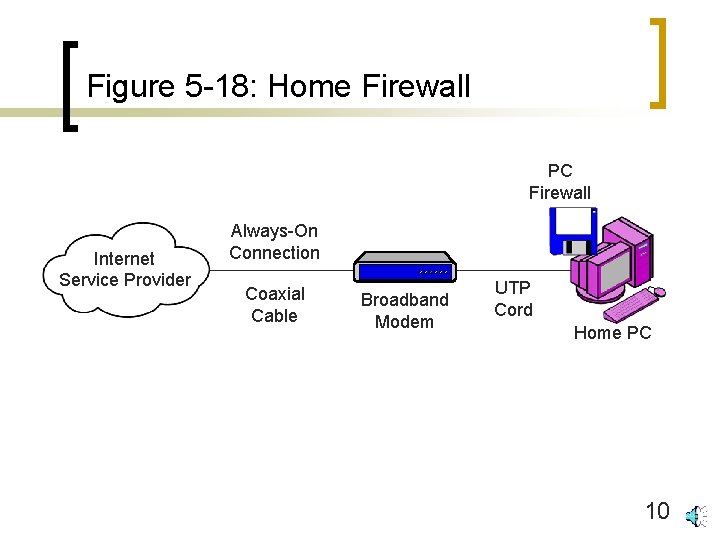
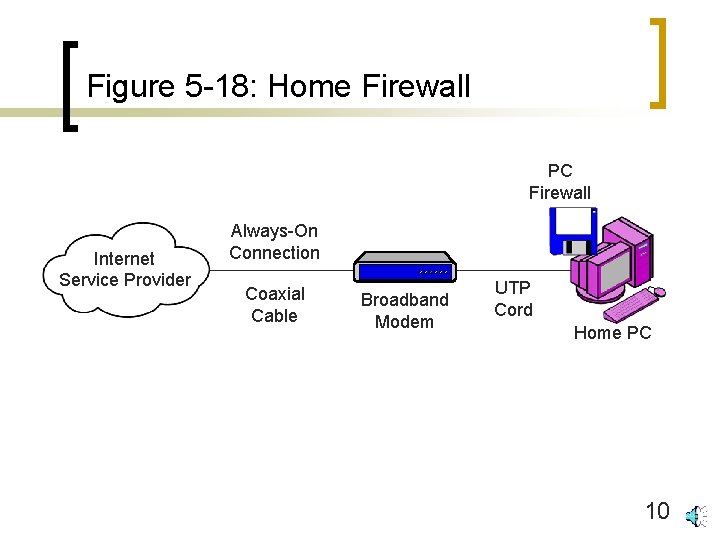
Figure 5 -18: Home Firewall PC Firewall Internet Service Provider Always-On Connection Coaxial Cable Broadband Modem UTP Cord Home PC 10
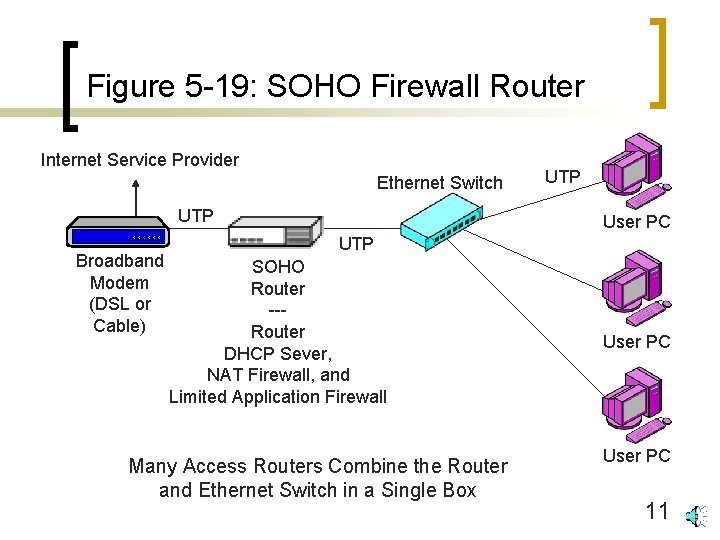
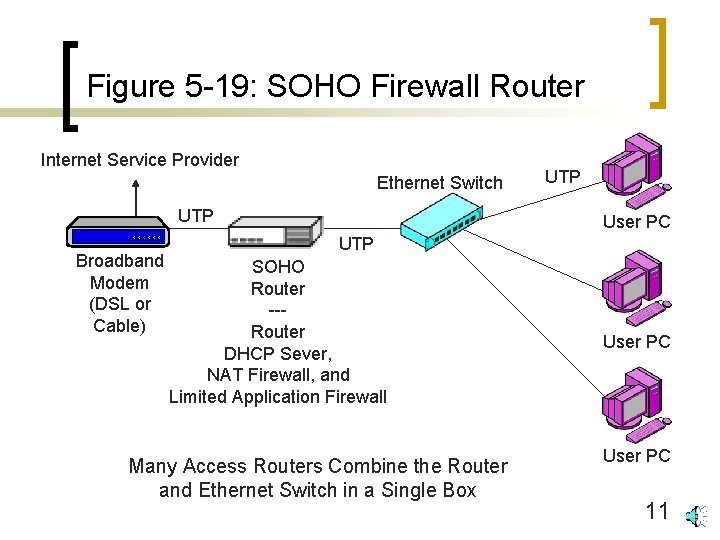
Figure 5 -19: SOHO Firewall Router Internet Service Provider Ethernet Switch UTP Broadband Modem (DSL or Cable) UTP User PC UTP SOHO Router --Router DHCP Sever, NAT Firewall, and Limited Application Firewall Many Access Routers Combine the Router and Ethernet Switch in a Single Box User PC 11
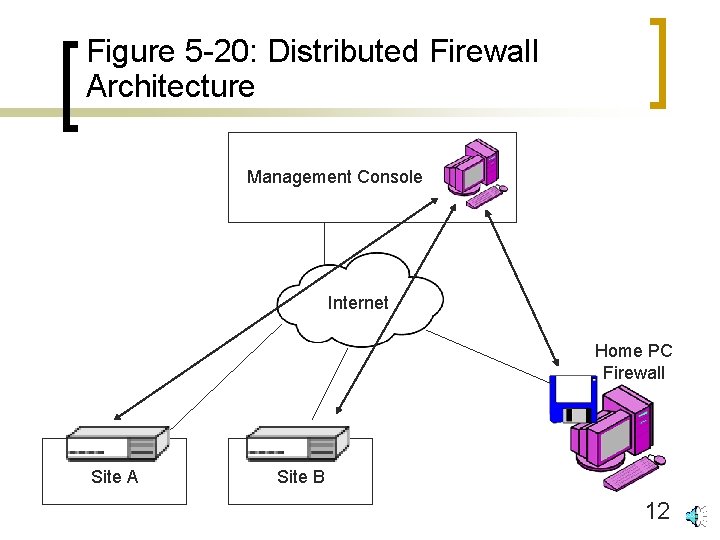
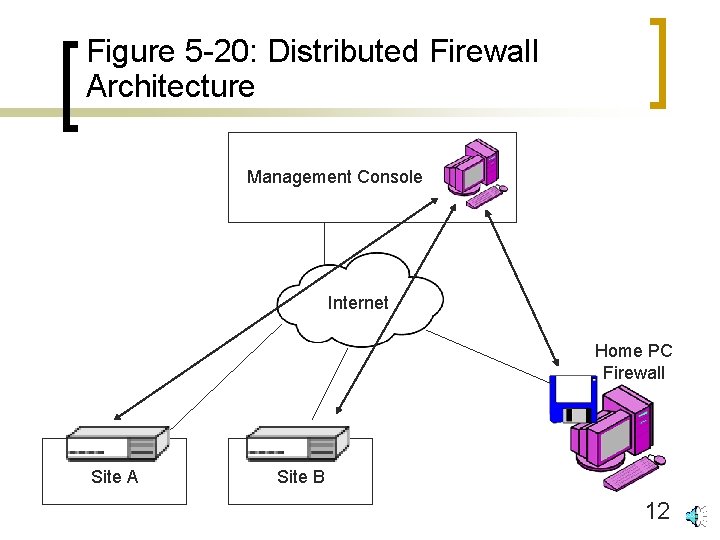
Figure 5 -20: Distributed Firewall Architecture Management Console Internet Home PC Firewall Site A Site B 12