Firewalls CS 158 B Don Tran What is
Firewalls CS 158 B Don Tran
What is a Firewall? • A firewall can be a program or a device that controls access to a network.
Why do I need a Firewall? • The Internet is a very dangerous place. • Need to have a way of controlling what gets into and out of your network. • Firewalls also give you detailed information of the kind of traffic passing through your network.
How do Firewalls work? • • There are different types of Firewalls. Some operate at the network layer. Others operate at the application layer. The higher the level the more security the firewall offers.
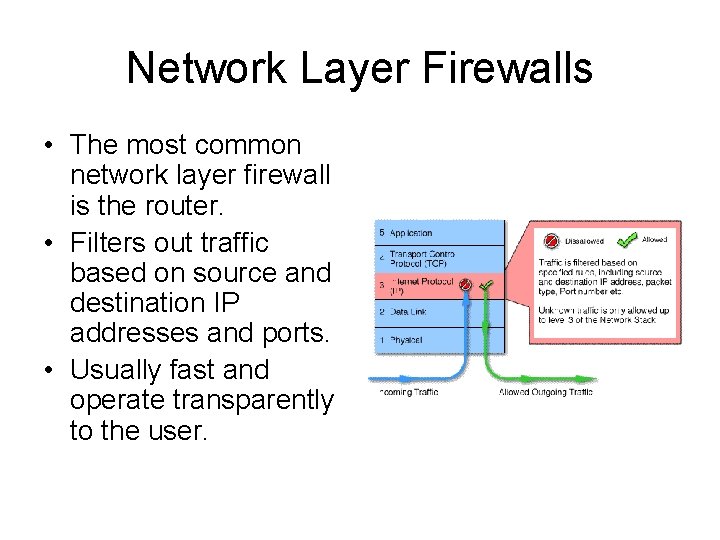
Network Layer Firewalls • The most common network layer firewall is the router. • Filters out traffic based on source and destination IP addresses and ports. • Usually fast and operate transparently to the user.
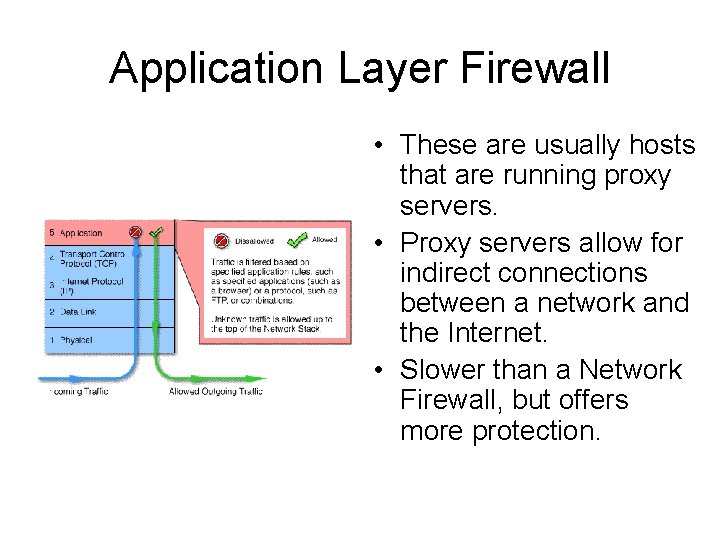
Application Layer Firewall • These are usually hosts that are running proxy servers. • Proxy servers allow for indirect connections between a network and the Internet. • Slower than a Network Firewall, but offers more protection.
Windows Firewall • Windows XP comes with its own firewall service known as Windows Firewall. • Protects your network by blocking unsolicited requests to connect to your network. • Makes managing a firewall easy.
How to configure Windows Firewall • Although blocking unsolicited requests is good… • Sometimes you may want to allow access to your computer. • Examples are Instant Messengers, and some video games may require that other computers connect to your computer.
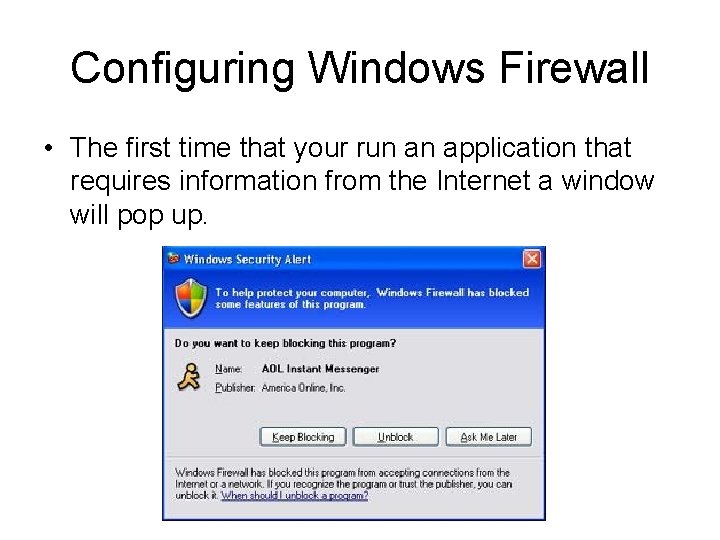
Configuring Windows Firewall • The first time that your run an application that requires information from the Internet a window will pop up.
Configuring Windows Firewall • To access Windows Firewall’s settings: • 1) Click on the “Start” menu button. • 2) Navigate to “Control Panel”. • 3) Click on “Windows Firewall”.
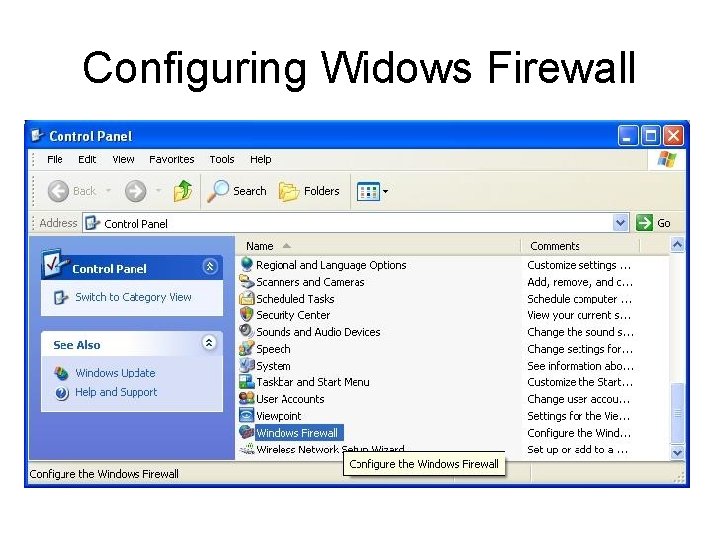
Configuring Widows Firewall
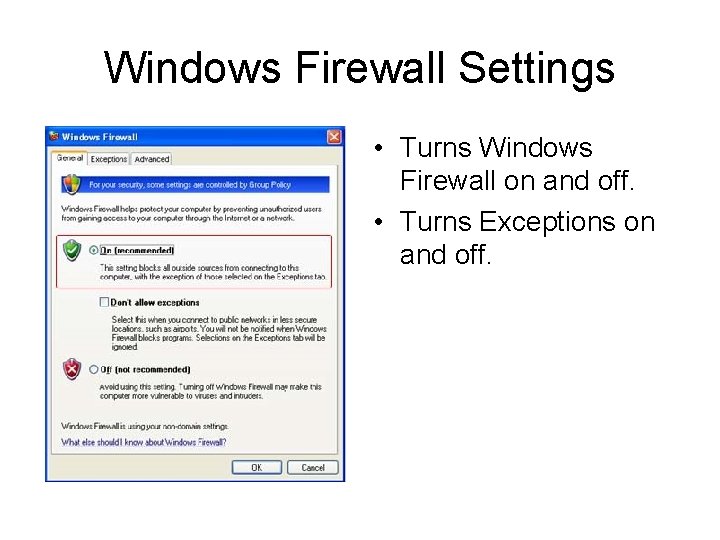
Windows Firewall Settings • Turns Windows Firewall on and off. • Turns Exceptions on and off.
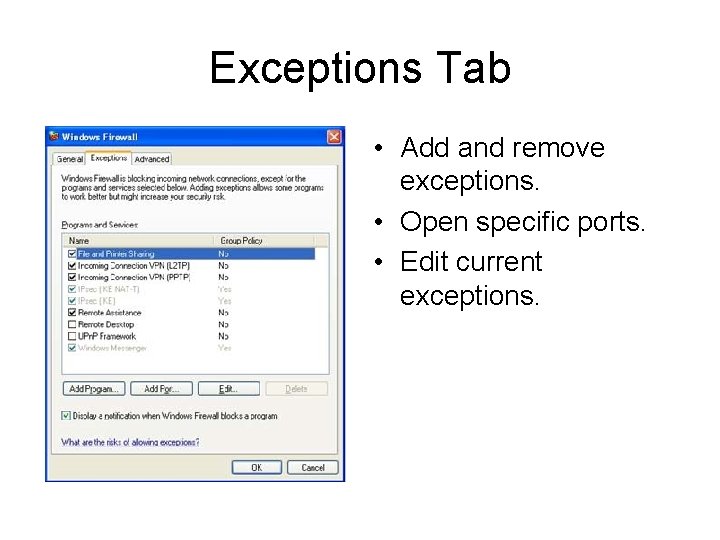
Exceptions Tab • Add and remove exceptions. • Open specific ports. • Edit current exceptions.

Edit Options
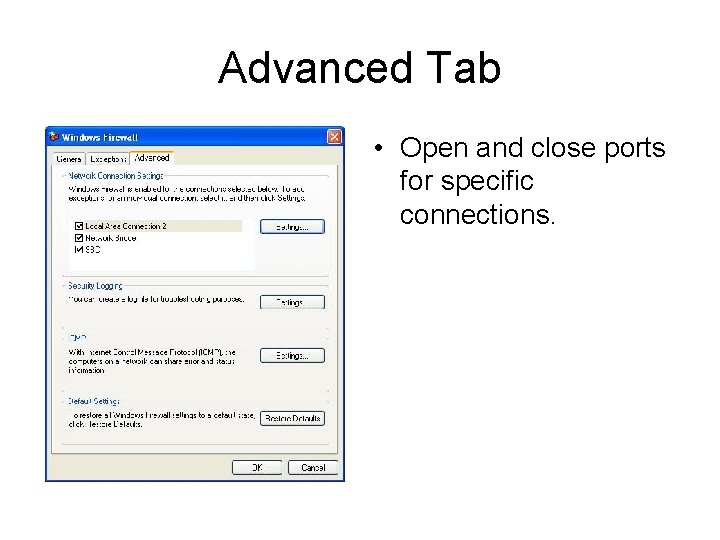
Advanced Tab • Open and close ports for specific connections.
Important Notes • There always security risks involved with allowing exceptions. • Following these rules will help minimize those risks: • 1) Only allow exceptions if you need it. • 2) Don’t allow an exception for a program that you do not recognize. • 3) Remove exceptions when you’re done with them.
- Slides: 16