Finding Information But first some humor BLAMESTORMING Sitting
Finding Information
But first some humor • • • BLAMESTORMING: Sitting around in a group, discussing why a server went down, and who was responsible. SEAGULL MANAGER: A manager who flies in, makes a lot of noise, craps on everything, and then leaves. CUBE FARM: An office filled with cubicles. MOUSE POTATO: The on-line, wired generation's answer to the couch potato. STRESS PUPPY: An admin who seems to thrive on being stressed out, whiney, and complains about stupid users all day. SWIPEOUT: An access card that has been rendered useless because the magnetic strip is worn away from extensive use. PERCUSSIVE MAINTENANCE: The fine art of whacking the crap out of an electronic device to get it to work again. 404: A completely clueless end-user. OHNOSECOND: That fraction of time after hitting Enter, in which you realize that you've just permanently erased a big database. Inoculatte: Taking coffee intravenously when you are pulling an all-nighter getting that database online from the backup tapes.
Go from • We are going to go from a URL – www. juniata. edu • To knowing available ports, addresses, and Operating system
Basic information • For www. juniata. edu find the following – TCP/IP address – OS • Not fair to: – call Joel – ask Matt or Ned – rely on what you already know • Who did it and how?
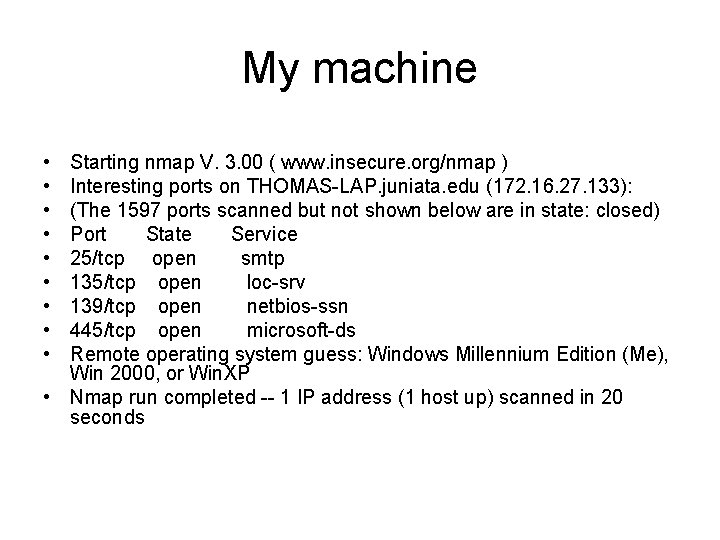
My machine • • • Starting nmap V. 3. 00 ( www. insecure. org/nmap ) Interesting ports on THOMAS-LAP. juniata. edu (172. 16. 27. 133): (The 1597 ports scanned but not shown below are in state: closed) Port State Service 25/tcp open smtp 135/tcp open loc-srv 139/tcp open netbios-ssn 445/tcp open microsoft-ds Remote operating system guess: Windows Millennium Edition (Me), Win 2000, or Win. XP • Nmap run completed -- 1 IP address (1 host up) scanned in 20 seconds
Step one • Basic information about www. juniata. edu – ping – whois – nslookup
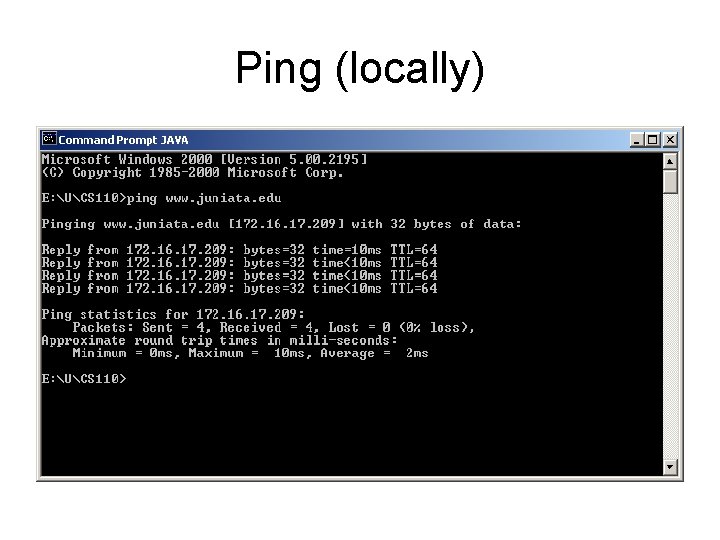
Ping (locally)
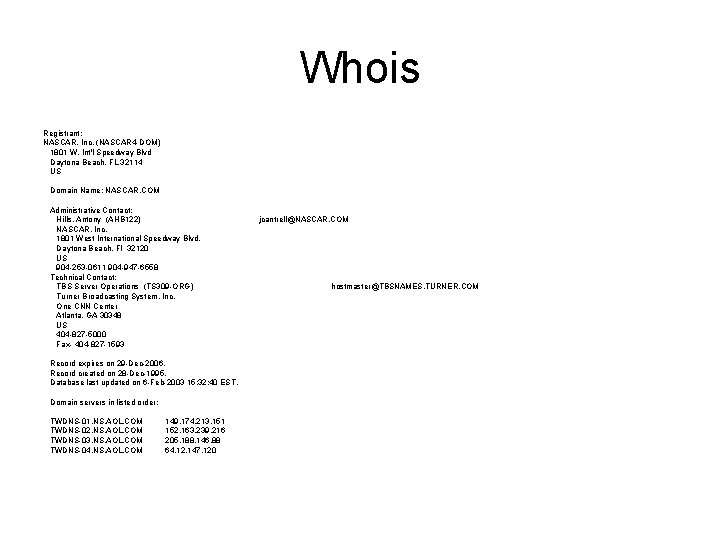
Whois Registrant: NASCAR, Inc. (NASCAR 4 -DOM) 1801 W. Int'l Speedway Blvd Daytona Beach, FL 32114 US Domain Name: NASCAR. COM Administrative Contact: Hills, Antony (AHB 122) NASCAR, Inc. 1801 West International Speedway Blvd. Daytona Beach, Fl 32120 US 904 -253 -0611 904 -947 -6558 Technical Contact: TBS Server Operations (TS 309 -ORG) Turner Broadcasting System, Inc. One CNN Center Atlanta, GA 30348 US 404 -827 -5000 Fax- 404 -827 -1593 Record expires on 29 -Dec-2006. Record created on 28 -Dec-1995. Database last updated on 6 -Feb-2003 15: 32: 40 EST. Domain servers in listed order: TWDNS-01. NS. AOL. COM TWDNS-02. NS. AOL. COM TWDNS-03. NS. AOL. COM TWDNS-04. NS. AOL. COM 149. 174. 213. 151 152. 163. 239. 216 205. 188. 146. 88 64. 12. 147. 120 jcantrell@NASCAR. COM hostmaster@TBSNAMES. TURNER. COM
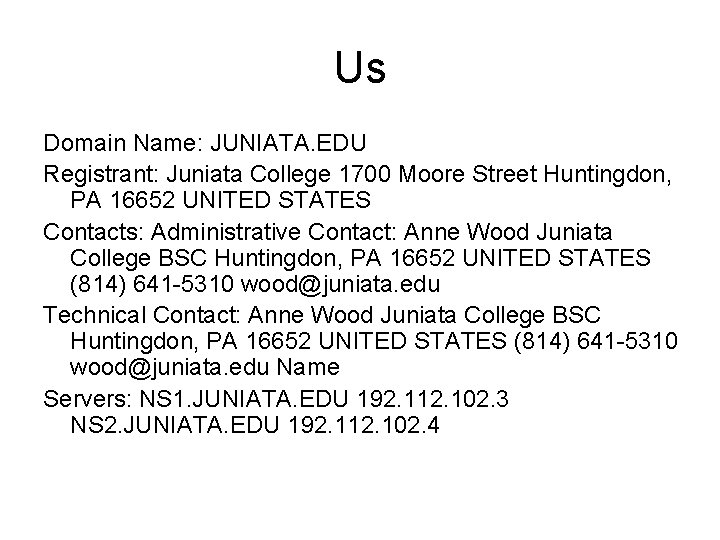
Us Domain Name: JUNIATA. EDU Registrant: Juniata College 1700 Moore Street Huntingdon, PA 16652 UNITED STATES Contacts: Administrative Contact: Anne Wood Juniata College BSC Huntingdon, PA 16652 UNITED STATES (814) 641 -5310 wood@juniata. edu Technical Contact: Anne Wood Juniata College BSC Huntingdon, PA 16652 UNITED STATES (814) 641 -5310 wood@juniata. edu Name Servers: NS 1. JUNIATA. EDU 192. 112. 102. 3 NS 2. JUNIATA. EDU 192. 112. 102. 4
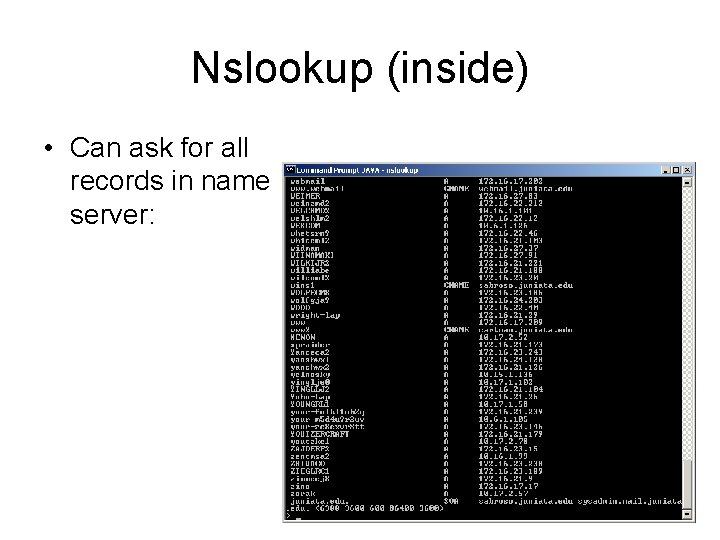
Nslookup (inside) • Can ask for all records in name server:
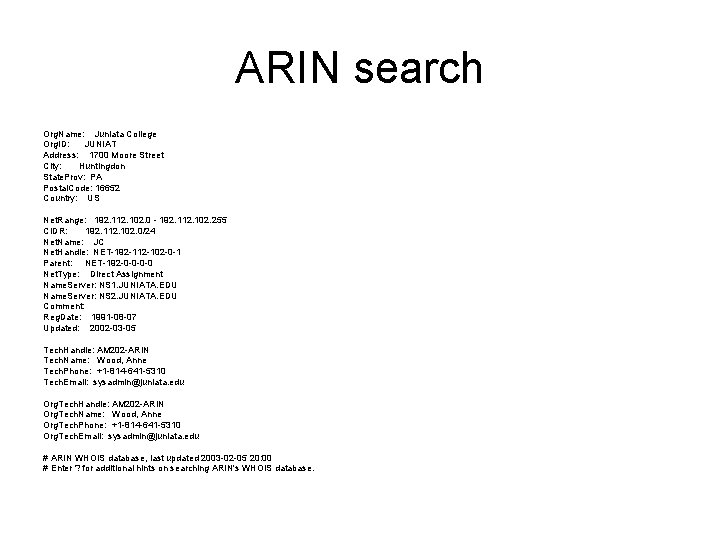
ARIN search Org. Name: Juniata College Org. ID: JUNIAT Address: 1700 Moore Street City: Huntingdon State. Prov: PA Postal. Code: 16652 Country: US Net. Range: 192. 112. 102. 0 - 192. 112. 102. 255 CIDR: 192. 112. 102. 0/24 Net. Name: JC Net. Handle: NET-192 -112 -102 -0 -1 Parent: NET-192 -0 -0 Net. Type: Direct Assignment Name. Server: NS 1. JUNIATA. EDU Name. Server: NS 2. JUNIATA. EDU Comment: Reg. Date: 1991 -08 -07 Updated: 2002 -03 -05 Tech. Handle: AM 202 -ARIN Tech. Name: Wood, Anne Tech. Phone: +1 -814 -641 -5310 Tech. Email: sysadmin@juniata. edu Org. Tech. Handle: AM 202 -ARIN Org. Tech. Name: Wood, Anne Org. Tech. Phone: +1 -814 -641 -5310 Org. Tech. Email: sysadmin@juniata. edu # ARIN WHOIS database, last updated 2003 -02 -05 20: 00 # Enter ? for additional hints on searching ARIN's WHOIS database.
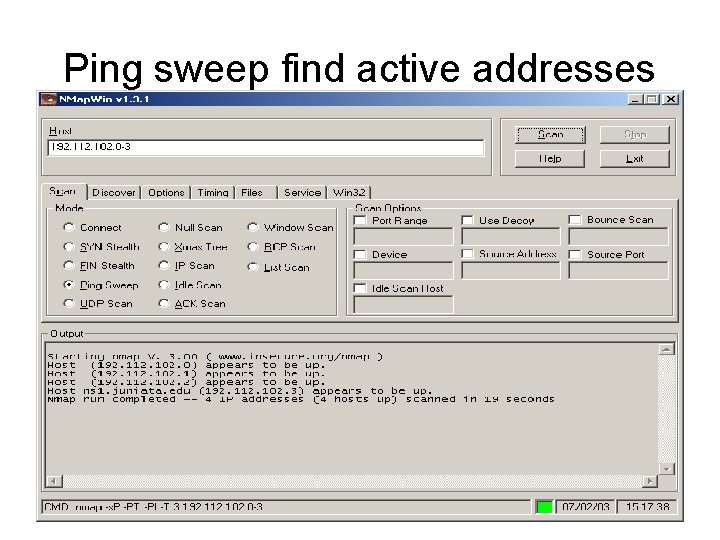
Ping sweep find active addresses
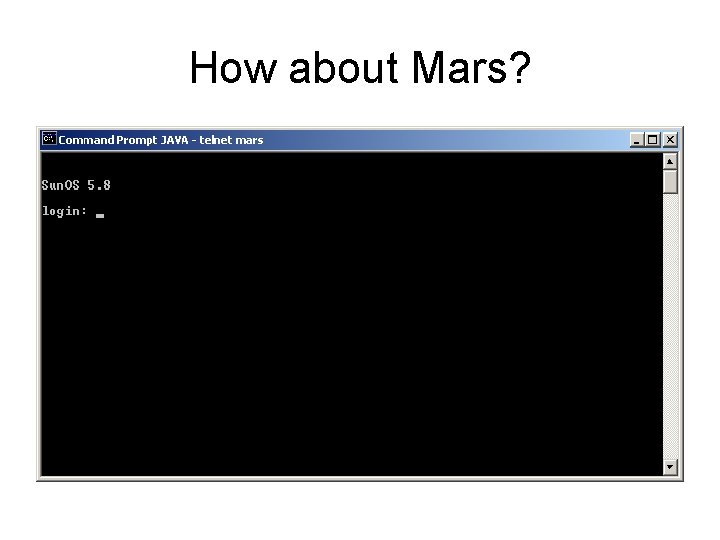
How about Mars?
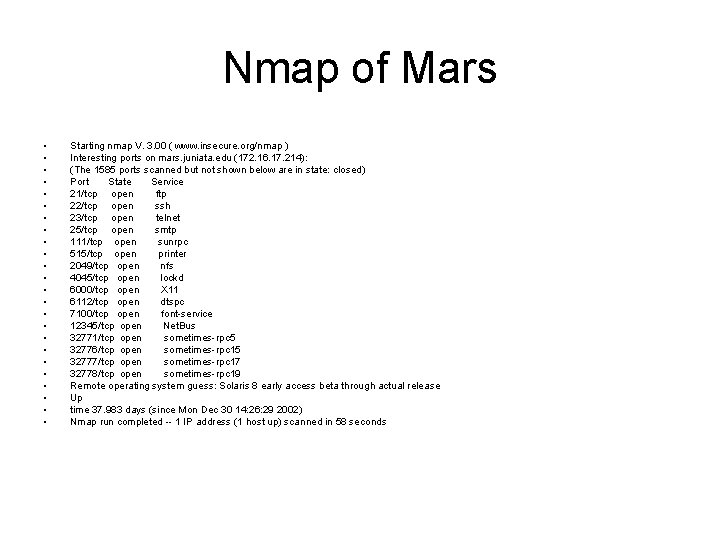
Nmap of Mars • • • • • • Starting nmap V. 3. 00 ( www. insecure. org/nmap ) Interesting ports on mars. juniata. edu (172. 16. 17. 214): (The 1585 ports scanned but not shown below are in state: closed) Port State Service 21/tcp open ftp 22/tcp open ssh 23/tcp open telnet 25/tcp open smtp 111/tcp open sunrpc 515/tcp open printer 2049/tcp open nfs 4045/tcp open lockd 6000/tcp open X 11 6112/tcp open dtspc 7100/tcp open font-service 12345/tcp open Net. Bus 32771/tcp open sometimes-rpc 5 32776/tcp open sometimes-rpc 15 32777/tcp open sometimes-rpc 17 32778/tcp open sometimes-rpc 19 Remote operating system guess: Solaris 8 early access beta through actual release Up time 37. 983 days (since Mon Dec 30 14: 26: 29 2002) Nmap run completed -- 1 IP address (1 host up) scanned in 58 seconds
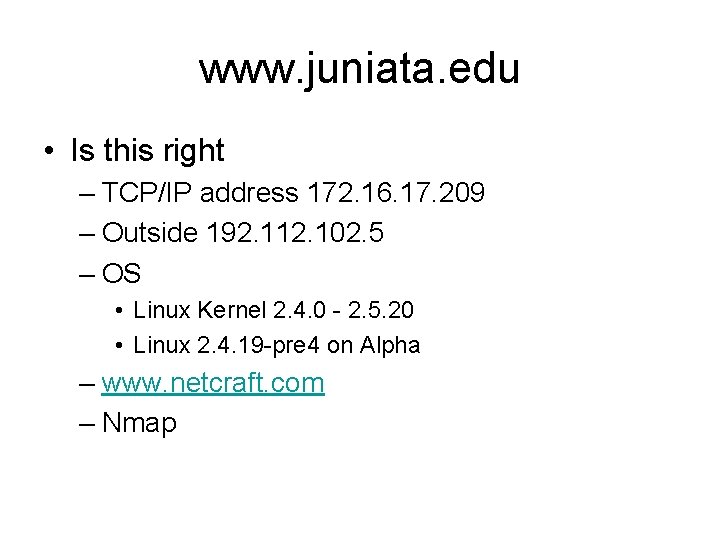
www. juniata. edu • Is this right – TCP/IP address 172. 16. 17. 209 – Outside 192. 112. 102. 5 – OS • Linux Kernel 2. 4. 0 - 2. 5. 20 • Linux 2. 4. 19 -pre 4 on Alpha – www. netcraft. com – Nmap
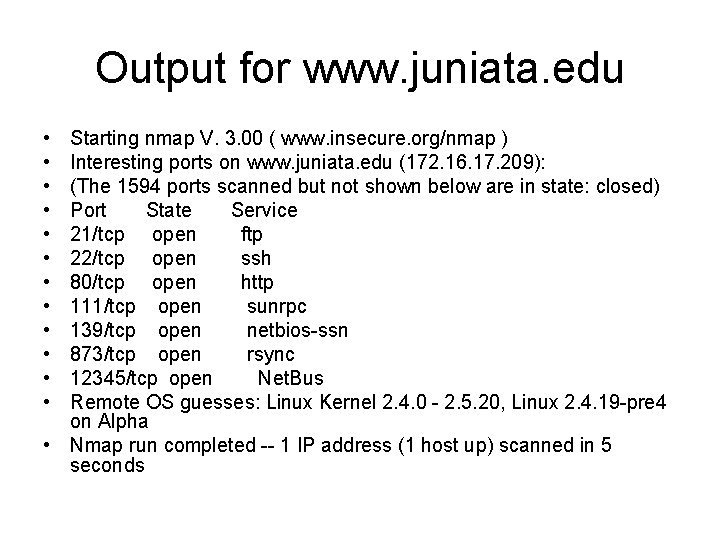
Output for www. juniata. edu • • • Starting nmap V. 3. 00 ( www. insecure. org/nmap ) Interesting ports on www. juniata. edu (172. 16. 17. 209): (The 1594 ports scanned but not shown below are in state: closed) Port State Service 21/tcp open ftp 22/tcp open ssh 80/tcp open http 111/tcp open sunrpc 139/tcp open netbios-ssn 873/tcp open rsync 12345/tcp open Net. Bus Remote OS guesses: Linux Kernel 2. 4. 0 - 2. 5. 20, Linux 2. 4. 19 -pre 4 on Alpha • Nmap run completed -- 1 IP address (1 host up) scanned in 5 seconds
What else • Ping sweep looking for other active machines • Do tracert to understand network – from outside in, typically have router then firewall just before destination. – Nmap router and firewall to get OS • War dailing for open modems
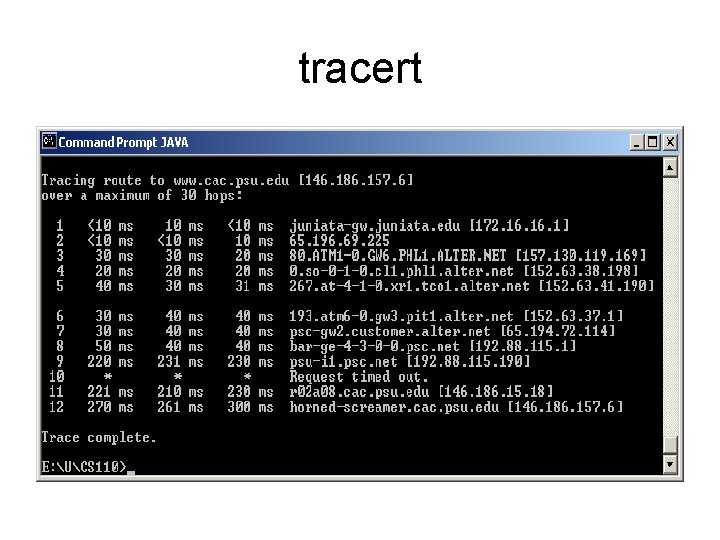
tracert
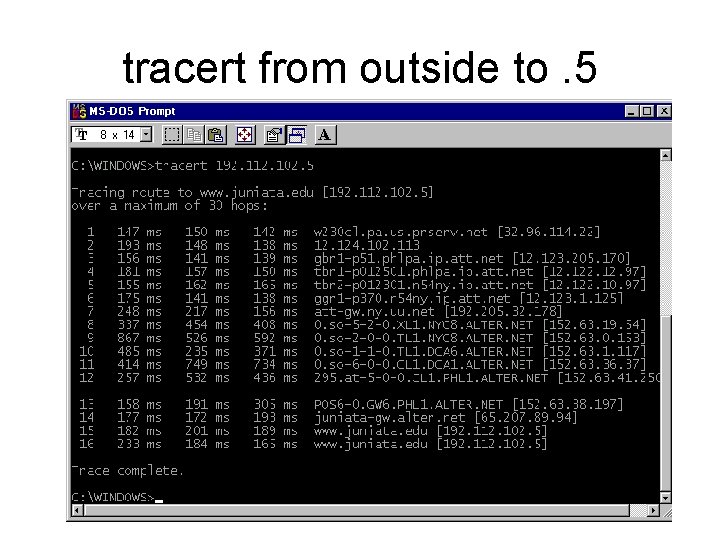
tracert from outside to. 5
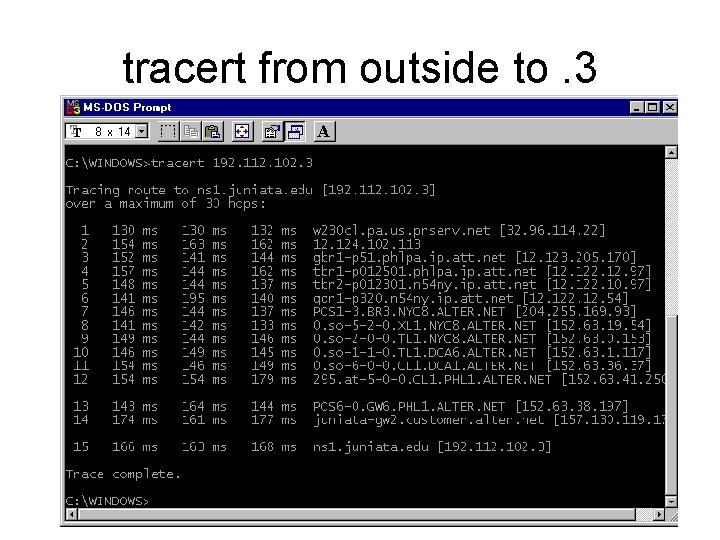
tracert from outside to. 3
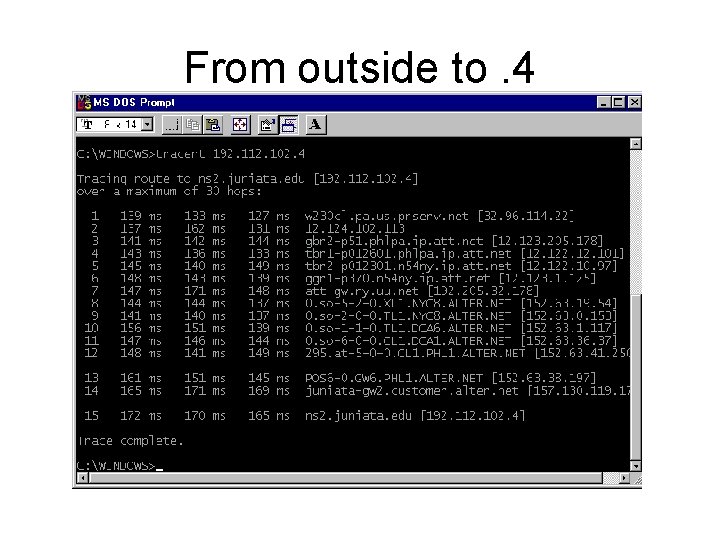
From outside to. 4
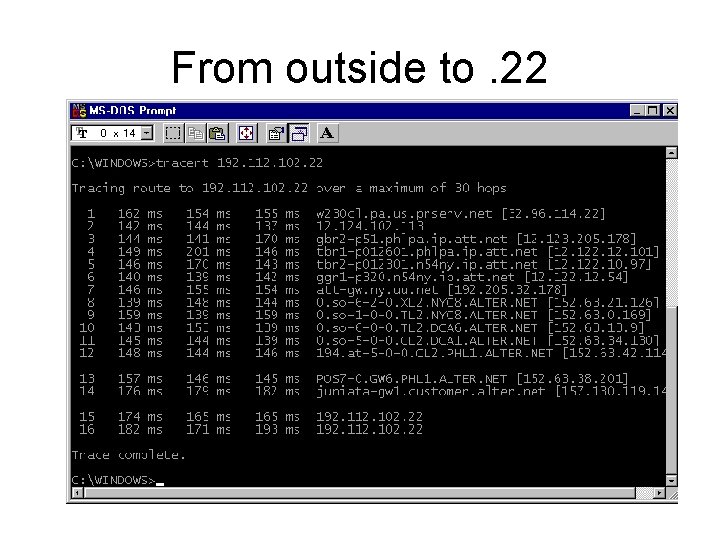
From outside to. 22
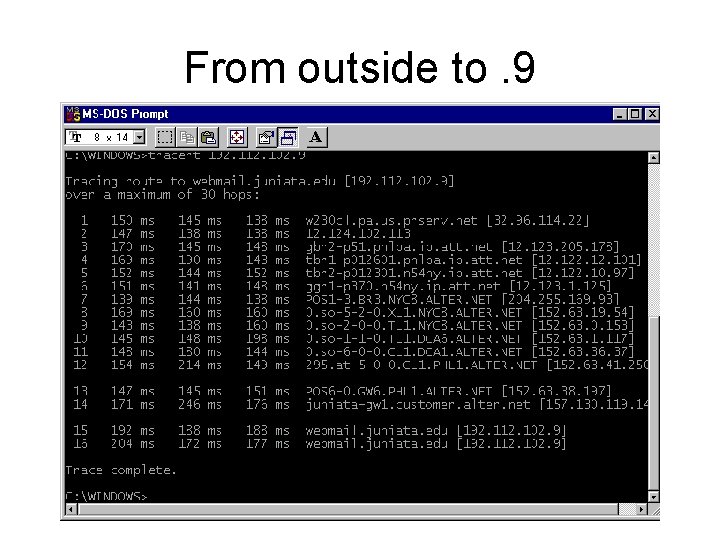
From outside to. 9
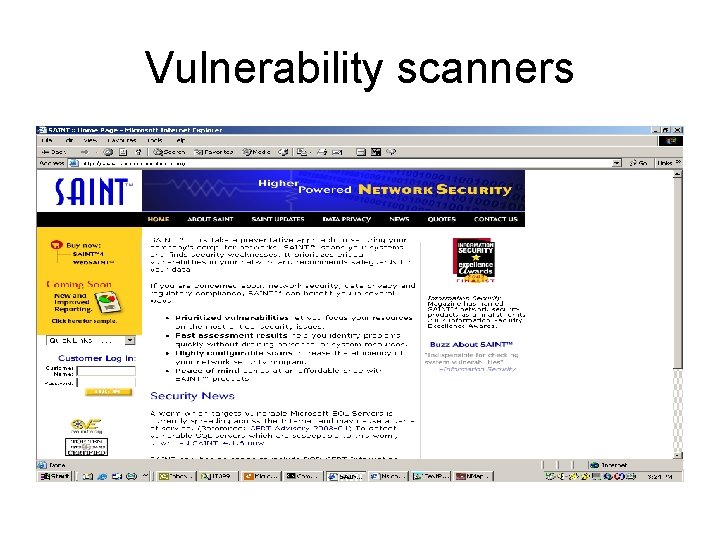
Vulnerability scanners
Red teaming page 90 • Who is page 91 – Protection page 92 – Name risk for social engineering • Can use Special name to catch or initials A. Wood • Although this info can be found other ways remember the easiest is what most people use – Split DNS servers one for external, minimum required information for the outside world – Inside DNS with other name resolution not required by the outside world.
Nslookup • Used to get IP address of servers • Get range of IPs to explore address spaces • Protection – Must provide DNS data to be “seen” – The least you provide the better.
ARIN • Gets address range and subnet • Protection – NAT with private addresses behind the firewall except for external resources help minimize damage
Tracert • Used to explore and “map” system • routes in (necessary to know for Denail of service) • Protection – only way to stop is to disable ICMP traffic (which tracert uses) – disables a lot of “features/functionality” – again security versus features/functionality
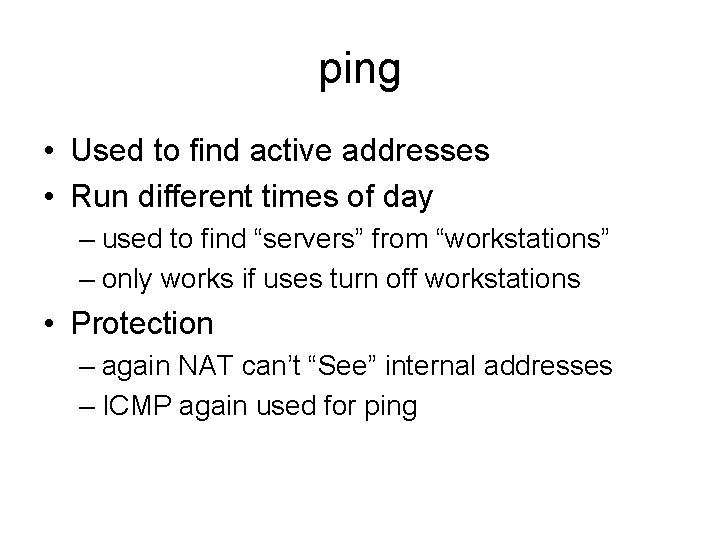
ping • Used to find active addresses • Run different times of day – used to find “servers” from “workstations” – only works if uses turn off workstations • Protection – again NAT can’t “See” internal addresses – ICMP again used for ping
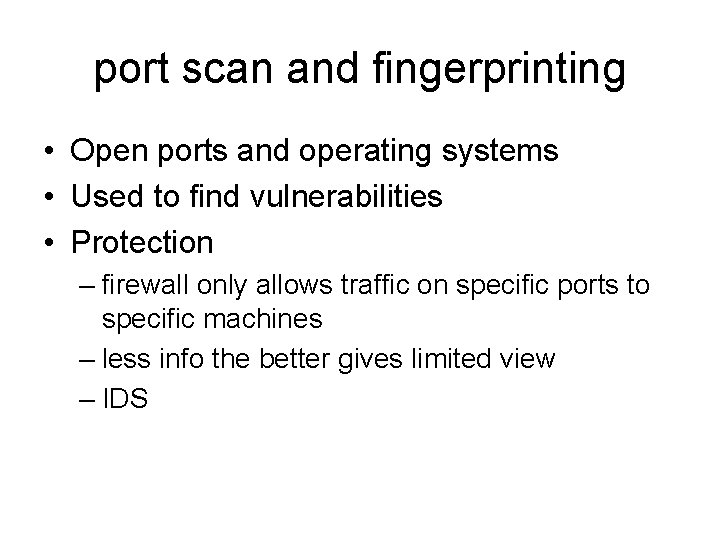
port scan and fingerprinting • Open ports and operating systems • Used to find vulnerabilities • Protection – firewall only allows traffic on specific ports to specific machines – less info the better gives limited view – IDS
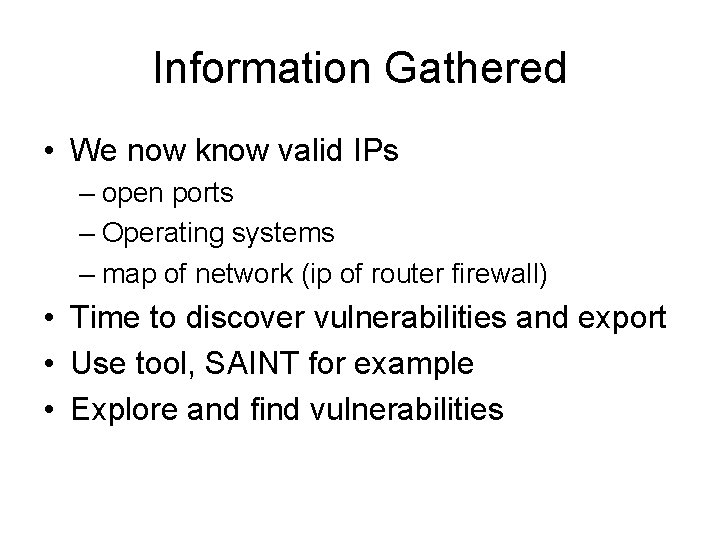
Information Gathered • We now know valid IPs – open ports – Operating systems – map of network (ip of router firewall) • Time to discover vulnerabilities and export • Use tool, SAINT for example • Explore and find vulnerabilities
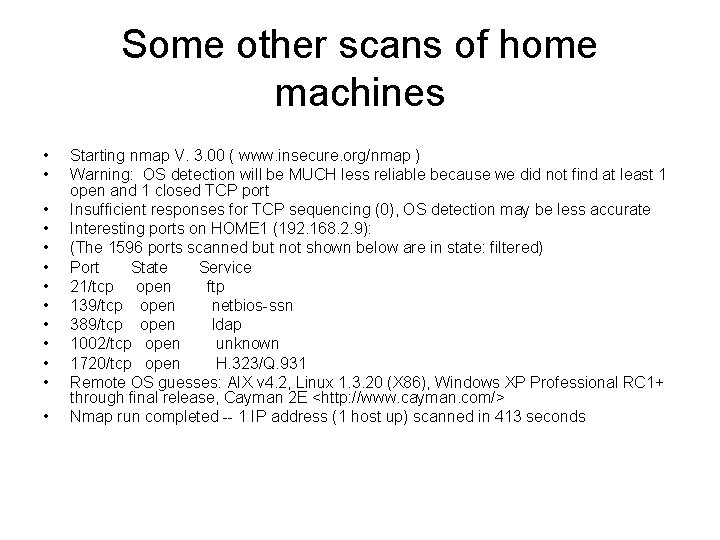
Some other scans of home machines • • • • Starting nmap V. 3. 00 ( www. insecure. org/nmap ) Warning: OS detection will be MUCH less reliable because we did not find at least 1 open and 1 closed TCP port Insufficient responses for TCP sequencing (0), OS detection may be less accurate Interesting ports on HOME 1 (192. 168. 2. 9): (The 1596 ports scanned but not shown below are in state: filtered) Port State Service 21/tcp open ftp 139/tcp open netbios-ssn 389/tcp open ldap 1002/tcp open unknown 1720/tcp open H. 323/Q. 931 Remote OS guesses: AIX v 4. 2, Linux 1. 3. 20 (X 86), Windows XP Professional RC 1+ through final release, Cayman 2 E <http: //www. cayman. com/> Nmap run completed -- 1 IP address (1 host up) scanned in 413 seconds
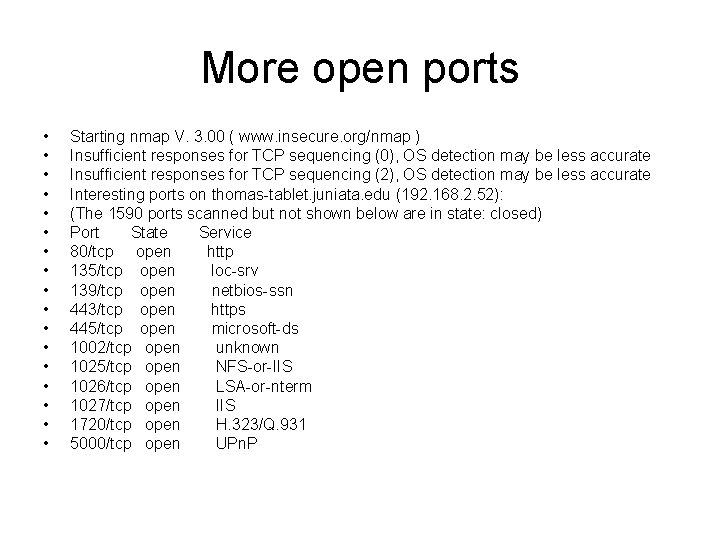
More open ports • • • • • Starting nmap V. 3. 00 ( www. insecure. org/nmap ) Insufficient responses for TCP sequencing (0), OS detection may be less accurate Insufficient responses for TCP sequencing (2), OS detection may be less accurate Interesting ports on thomas-tablet. juniata. edu (192. 168. 2. 52): (The 1590 ports scanned but not shown below are in state: closed) Port State Service 80/tcp open http 135/tcp open loc-srv 139/tcp open netbios-ssn 443/tcp open https 445/tcp open microsoft-ds 1002/tcp open unknown 1025/tcp open NFS-or-IIS 1026/tcp open LSA-or-nterm 1027/tcp open IIS 1720/tcp open H. 323/Q. 931 5000/tcp open UPn. P
Of course todays footprinting must include wireless • http: //www. wellenreiter. net/index. html
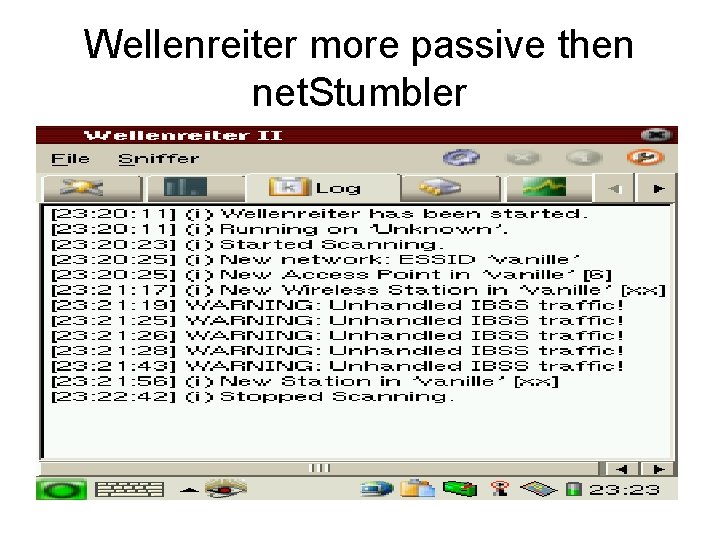
Wellenreiter more passive then net. Stumbler
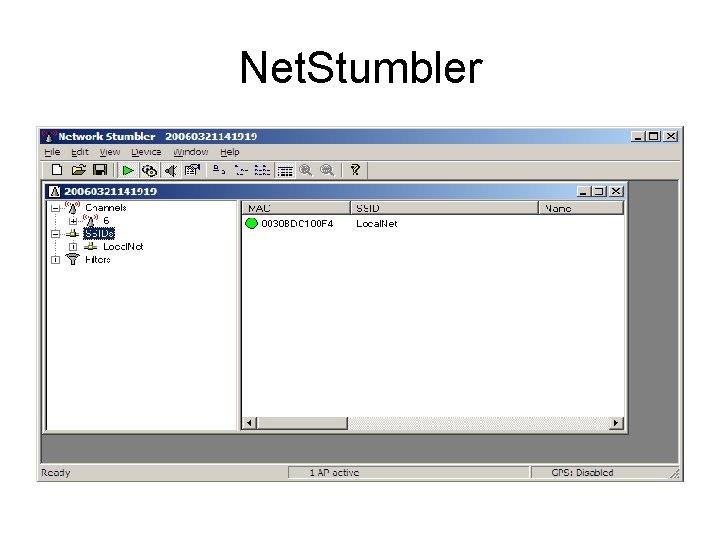
Net. Stumbler
Want to boost your Antenna? • http: //mali. geekcorps. org/article. php 3? id_a rticle=39 • Look at Home. To. Jc in netstumbler
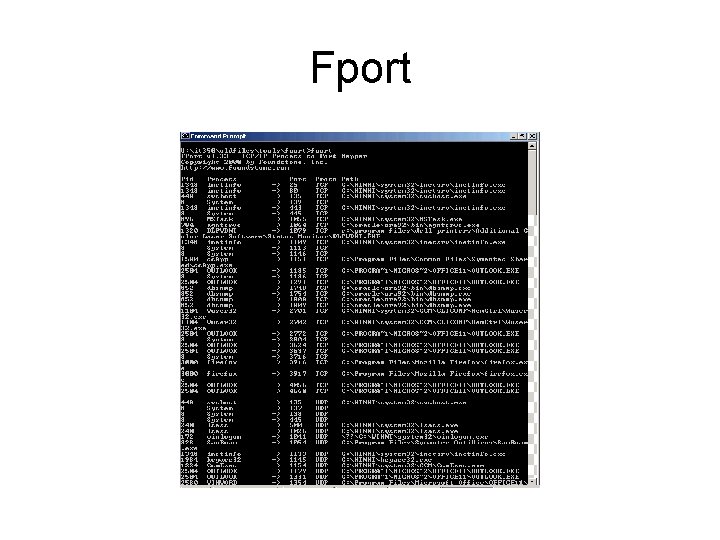
Fport
- Slides: 38