Final Lab Spam Group 10 Scott Durr Stephen

Final Lab - Spam Group 10: Scott Durr Stephen Thompson
Outline • Introduction • Set up • Obtaining Email Addresses • Sending Mass Emails • Filtering & Stopping Spam
Introduction Almost 90% of email is now considered Spam! – Messaging Anti-Abuse Working Group Report #6, Oct 2007 • Huge drain on resources • Strains the infrastructure • Distracts/Annoys us all • Major delivery mechanism for Malware!
The Costs • The State of California estimates Spam cost the state’s economy $1. 2 billion in 2003. The estimate the entire US suffered a $10 billion loss in that same year. – http: //www. spamlaws. com/state/ca. shtml • That was in 2003…
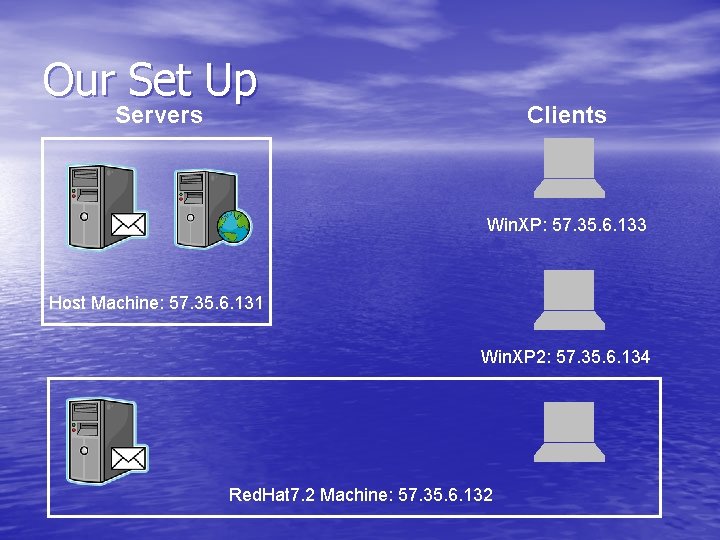
Our Set Up Servers Clients Win. XP: 57. 35. 6. 133 Host Machine: 57. 35. 6. 131 Win. XP 2: 57. 35. 6. 134 Red. Hat 7. 2 Machine: 57. 35. 6. 132
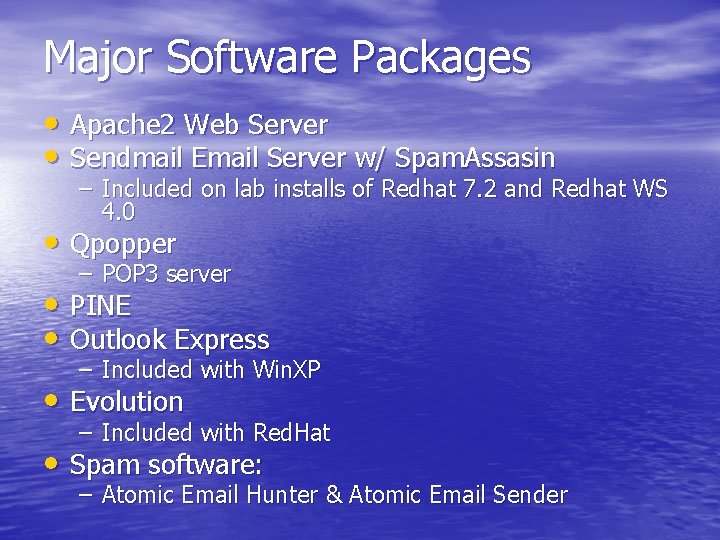
Major Software Packages • Apache 2 Web Server • Sendmail Email Server w/ Spam. Assasin – Included on lab installs of Redhat 7. 2 and Redhat WS 4. 0 • Qpopper – POP 3 server • PINE • Outlook Express – Included with Win. XP • Evolution – Included with Red. Hat • Spam software: – Atomic Email Hunter & Atomic Email Sender
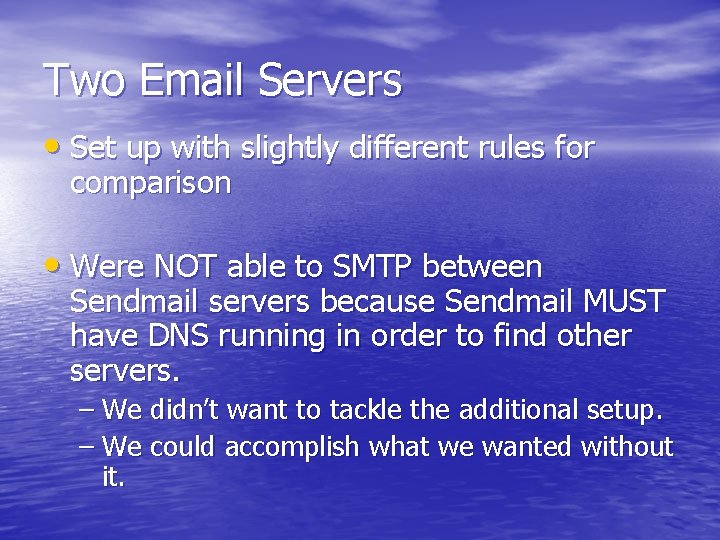
Two Email Servers • Set up with slightly different rules for comparison • Were NOT able to SMTP between Sendmail servers because Sendmail MUST have DNS running in order to find other servers. – We didn’t want to tackle the additional setup. – We could accomplish what we wanted without it.
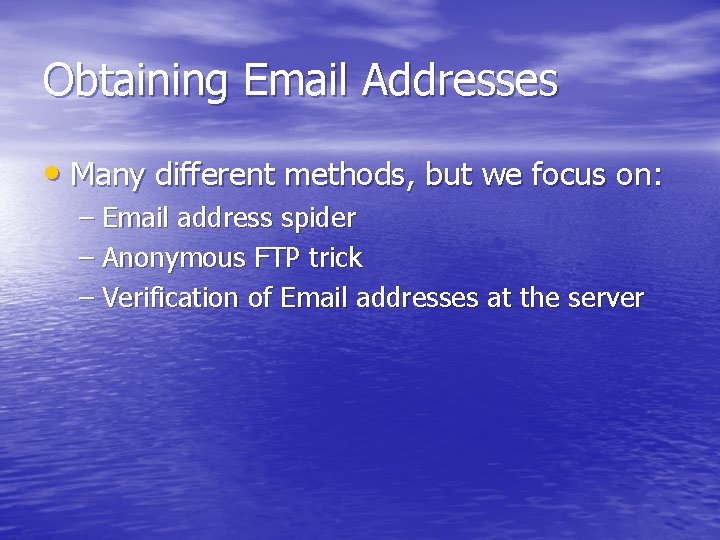
Obtaining Email Addresses • Many different methods, but we focus on: – Email address spider – Anonymous FTP trick – Verification of Email addresses at the server
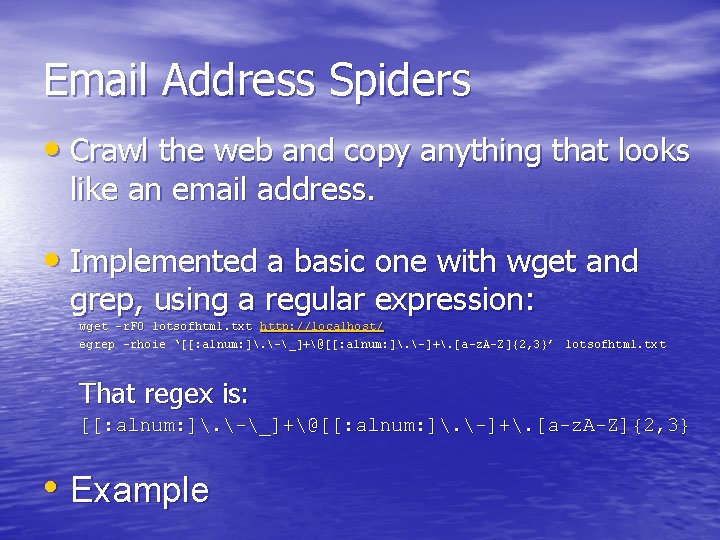
Email Address Spiders • Crawl the web and copy anything that looks like an email address. • Implemented a basic one with wget and grep, using a regular expression: wget –r. FO / –r. FO lotsofhtml. txt http: //localhost/ egrep –rhoie ‘[[: alnum: ]. -_]+@[[: alnum: ]. -]+. [a-z. A-Z]{2, 3}’ lotsofhtml. txt That regex is: [[: alnum: ]. -_]+@[[: alnum: ]. -]+. [a-z. A-Z]{2, 3} • Example
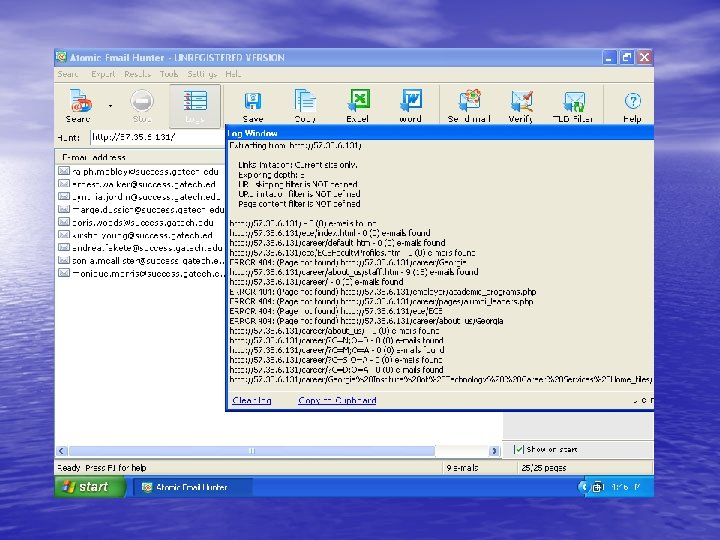
“Atomic Email Hunter” • Commercial Windows program that implements an email address spider. • Tested on the same dummy websites as our homemade one. • Has a lot more features.
Anonymous FTP • A throwback from the days of old: Anonymous • FTP logins require an email address as a password! Set up your web page to grab images via FTP vice HTML and some browsers will cough up an email address. • Tested on Mozilla and IE: they give dummy addresses.
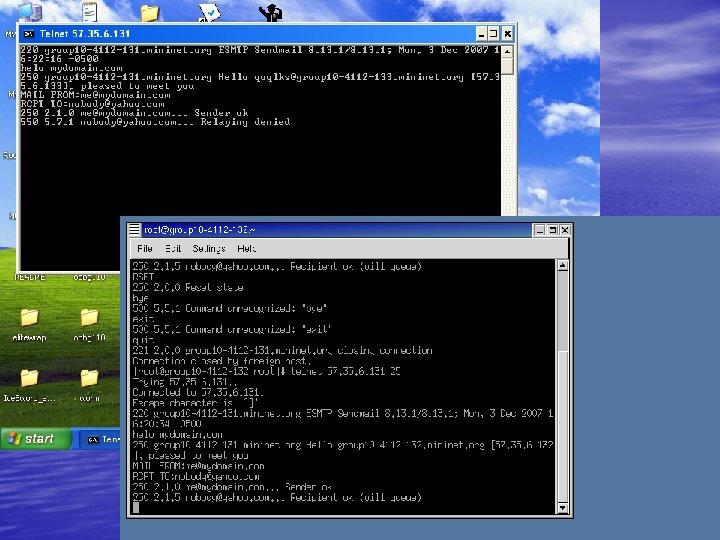
Verifying Email Addresses • Why is this important? – A “good” email list will minimize alerts that might catch the spammer. – Allows for a ‘guess and test’ method of email address discovery. • VRFY and EXPN – Ask the server if an address is good (VRFY) – Ask the server about an alias/list (EXPN) – Disable these!
Verifying Email Addresses • During the SMTP exchange, you pass a “TO” address to the server. It will come back and tell you if it is good! • Email header implemented by many clients: Return-Receipt-To: <email-address> X-Confirm-Reading-To: <email-address> Make sure you disable these as defaults in Outlook and others!
Defeating those Email Spiders • Two choices – Hide your email address – Actively counter spiders
Hide your email address • Use script to return an email address instead of putting the address in code. • ECE does this for their faculty! • Great example, courtesy of Mr. Tim Williams at U. Arizona: http: //www. u. arizona. edu/~trw/spam 4. htm
WPoison • Available at http: //www. monkeys. com/wpoison/ • Actively thwarts spiders by generating random pages with more links and email addresses. • Each link leads right back to WPoison! – Run the spider in a circle, filling it with garbage. – We have a video
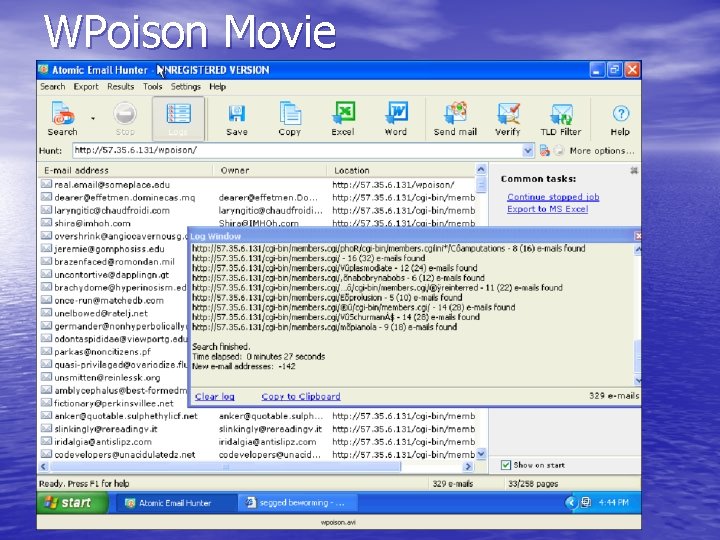
WPoison Movie
Sending Mass Emails • Methods 1. Use your own (school/isp) SMTP server • You will probably get caught and shut down! 2. Use another, third party SMTP server • You will probably be blocked from Relaying 3. Connect directly to the recipient’s server • This takes some work, and you might get blacklisted 4. Do any of the above via a Bot Net • Even if you get caught, you don’t get blocked!
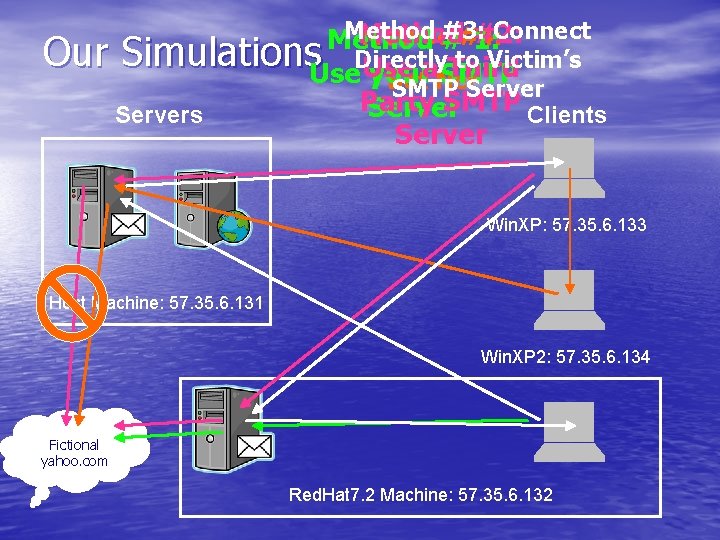
Method #3: Connect Method #2: Method# #4: Method 1: Our Simulations. Use. Directly to Victim’s Use a Third your SMTP Bot Net. Server SMTP Party SMTP Clients Servers Server Win. XP: 57. 35. 6. 133 Host Machine: 57. 35. 6. 131 Win. XP 2: 57. 35. 6. 134 Fictional yahoo. com Red. Hat 7. 2 Machine: 57. 35. 6. 132
Mass Email Countermeasures • Limit who can send on your server – Only users on the domain can “RELAY” – Use a blacklist to prevent connections from known spammers • Filter messages as they come in
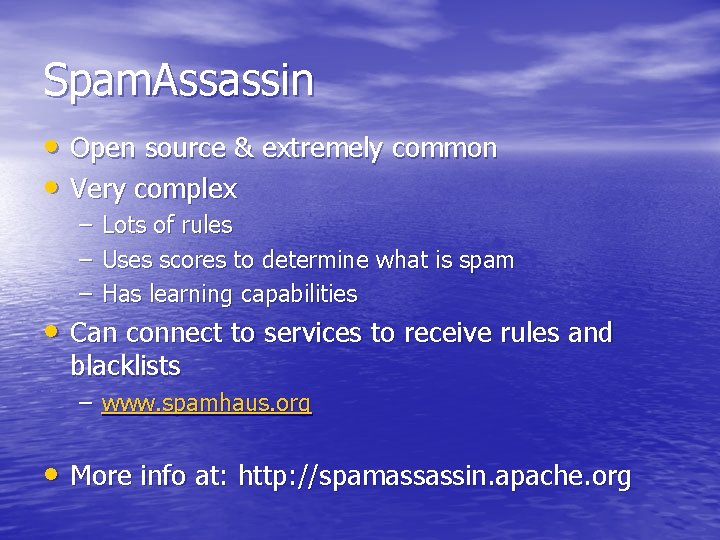
Spam. Assassin • Open source & extremely common • Very complex – – – Lots of rules Uses scores to determine what is spam Has learning capabilities • Can connect to services to receive rules and blacklists – www. spamhaus. org • More info at: http: //spamassassin. apache. org
Spam. Assassin in the Lab • We walk through the setup of some basic rules.
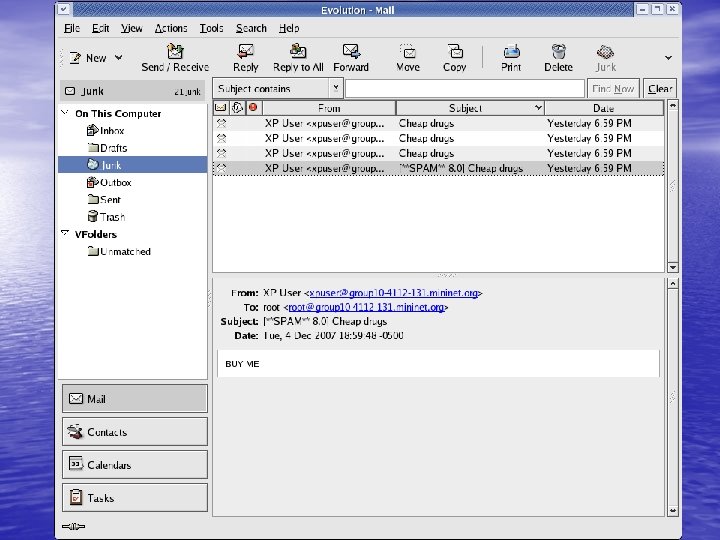
Your Last Line of Defense… • The email client • Web-based email clients can rapidly aggregate feedback and build more responsive filters. • Gmail, Yahoo, Hotmail, etc.
In the Lab Summary • Set up Servers • Harvest emails – Email Address Spiders: wget/grep & Atomic – FTP method • Experiment with address verification • Send mass emails through each scenario – Use manual connection and Atomic Email Sender • Implement some countermeasures – RELAY limitations – WPoison – Hide Email Addresses • Install, setup, and test Spam. Assassin
Questions?
- Slides: 28