FFIEC Customer Authentication Guidance Authentication in an Internet
- Slides: 16
FFIEC Customer Authentication Guidance: Authentication in an Internet Banking Environment
About the Speaker Matthew Clohessy, CPA, CIA, has six and a half years of experience as an internal auditor at midsized commercial banking institutions where he specializes in evaluating internal controls over electronic banking delivery channels, retail and commercial banking operations, loss prevention and consumer banking regulatory compliance. Prior to his career in internal auditing, Mr. Clohessy was a network administrator for a small company in the office design industry for four years, where he was responsible for the operation, security and maintenance of the company’s IT infrastructure.
Discussion Topics • Overview of the FFIEC • Evolution of the guidance • Evolving cybercrime fraud landscape • Objectives of the guidance • Layered security approach • Risk assessments • Recent court cases • New FFIEC working group
Overview of the FFIEC The Federal Financial Institutions Examination Council (FFIEC) is an interagency body which promotes uniformity and consistency in the supervision of financial institutions through establishing uniform principles, standards and report forms for financial institution regulatory agencies. Regulatory Agencies: • Board of Governors of the Federal Reserve System (FRB); • Federal Deposit Insurance Corporation (FDIC); • National Credit Union Administration (NCUA); • Office of the Comptroller of the Currency (OCC); and • Consumer Financial Protection Bureau (CFPB) (Joined July 2011)
Evolution of the Guidance The “Authentication Guidance” issued by the FFIEC continues to evolve as new technologies emerge and as changes occur in the fraud environment that financial institutions are faced with: • August 2001: Authentication in an Electronic Banking Environment • October 2005: Authentication in an Internet Banking Environment (Replaced 2001 Guidance) • June 2011: Supplement to Authentication in an Internet Banking Environment The “ 2001 Guidance” focused on risk management controls necessary to authenticate the identity of retail and commercial customers accessing Internet-based financial services The “ 2005 Guidance” replaced the 2001 Guidance and provided a risk management framework for financial institutions offering Internet based products and services to their customers. The “ 2011 Supplement” reinforced the 2005 Guidance’s risk management framework and updated the Agencies’ expectations regarding customer authentication, layered security, or other controls.
Evolving Cybercrime Landscape • Organized crime rings with significant financial backing • Cyber criminals are utilizing malware designed specifically to collect user ids/passwords from infected devices (eg. Zeus/Zbot, Clampi/llomo, Spy. Eye) • Increased sophistication of attacks • Cross-channel fraud – Utilizing a combination of Web, Telephone and/or other electronic channels to execute fraudulent transactions. • Layered assaults – Utilizing DDo. S immediately after perpetrating fraud to prevent customers from accessing their accounts/identifying fraudulent transactions before they clear.
Objectives of the Guidance The FFIEC’s Authentication Guidance provides a set of guidelines for financial institutions on establishing a risk based control environment to prevent losses as a result of external fraud. The guidance focuses on implementing a layered security approach and executing periodic risk assessments to establish a commercially reasonable control environment for electronic financial services.
Layered Security Approach “Since virtually every authentication technique can be compromised, financial institutions should not rely solely on any single control for authorizing high risk transactions, but rather institute a system of layered security. . ” (2011 Supplemental guidance) A Layered Security approach relies upon different controls at different points of the transaction and consists a combination of the following elements to reduce the risks associated with high risk online activities: • Multi-Factor Authentication • Effective Layered Controls
Multi-Factor Authentication consists of having more than one of the following “Factors”: • Something the user knows (e. g. , password, PIN); • Something the user has(e. g. , ATM card, smart card); and • Something the user is (e. g. , biometric characteristic, such as a fingerprint)
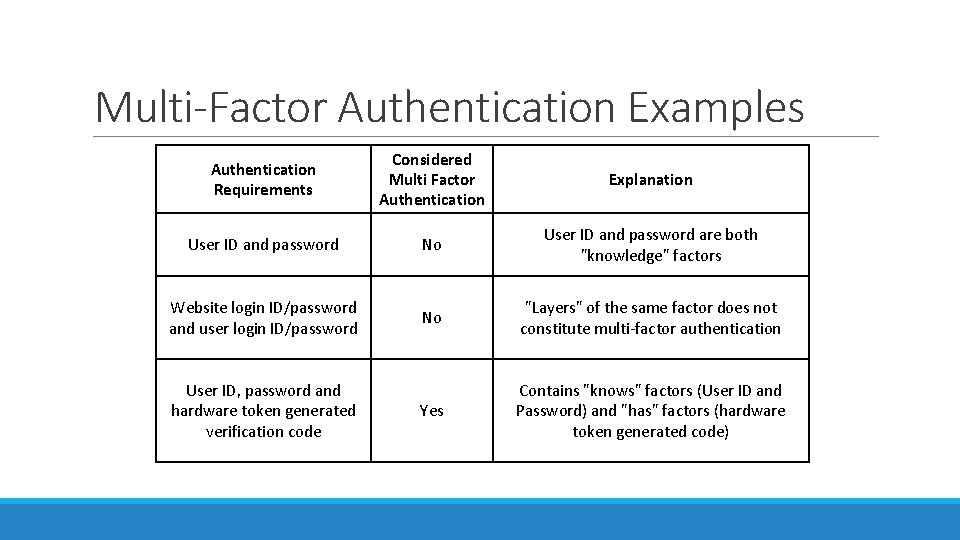
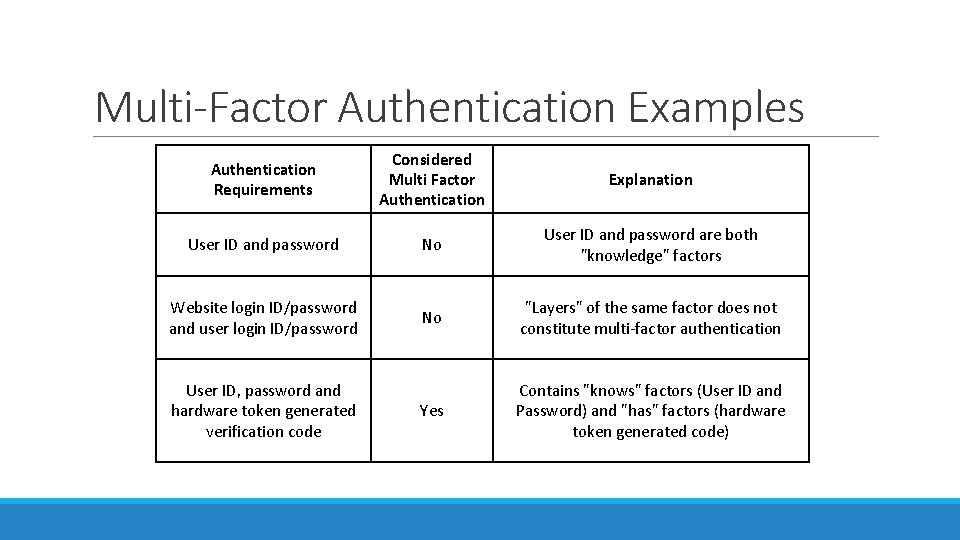
Multi-Factor Authentication Examples Authentication Requirements Considered Multi Factor Authentication Explanation User ID and password No User ID and password are both "knowledge" factors Website login ID/password and user login ID/password No "Layers" of the same factor does not constitute multi-factor authentication Yes Contains "knows" factors (User ID and Password) and "has" factors (hardware token generated code) User ID, password and hardware token generated verification code
Effective Layered Controls Multi-Factor Authentication may not be considered a strong enough control by itself for high risk transactions (eg. high dollar wire transactions) or practical to implement (eg. retail web banking customers). As such, implementing additional controls is critical to establishing an effective layered control environment. Examples of layered controls: • fraud detection and monitoring systems that include consideration of customer history and behavior and enable a timely and effective institution response; • the use of dual customer authorization through different access devices; • the use of out of band verification for transactions; • the use of “positive pay, ” debit blocks, and other techniques to appropriately limit the transactional use of the account • enhanced controls over account activities; such as transaction value thresholds, payment recipients, number of transactions allowed per day, and allowable payment windows (e. g. , days and times); • internet protocol (IP) reputation based tools to block connection to banking servers from IP addresses known or suspected to be associated with fraudulent activities; • policies and practices for addressing customer devices identified as potentially compromised and customers who may be facilitating fraud; • enhanced control over changes to account maintenance activities performed by customers either online or through customer service channels; and • enhanced customer education to increase awareness of the fraud risk and effective techniques customers can use to mitigate the risk.
Establishing Effective Layered Controls A well designed control framework does not always mean that effective controls are in place: Effective authentication should have customer acceptance, reliable performance (with formally established policies and procedures), scalability to accommodate growth, interoperability with existing systems and future plan. Effective Layered controls must have quality substance, not just the form of a control. Challenge questions that are overused, or publically obtainable knowledge are not considered effective (eg. mother’s maiden name, high school the customer graduated from, year of graduation from college, etc). Utilization of sophisticated “out-of-wallet” questions along with “red herring” questions is considered effective. Simple device identification (cookie based) and geolocation can be circumvented through the use of copying cookie files and proxies. Use of “one time” cookies and more complex digital fingerprints are considered to be effective tools.
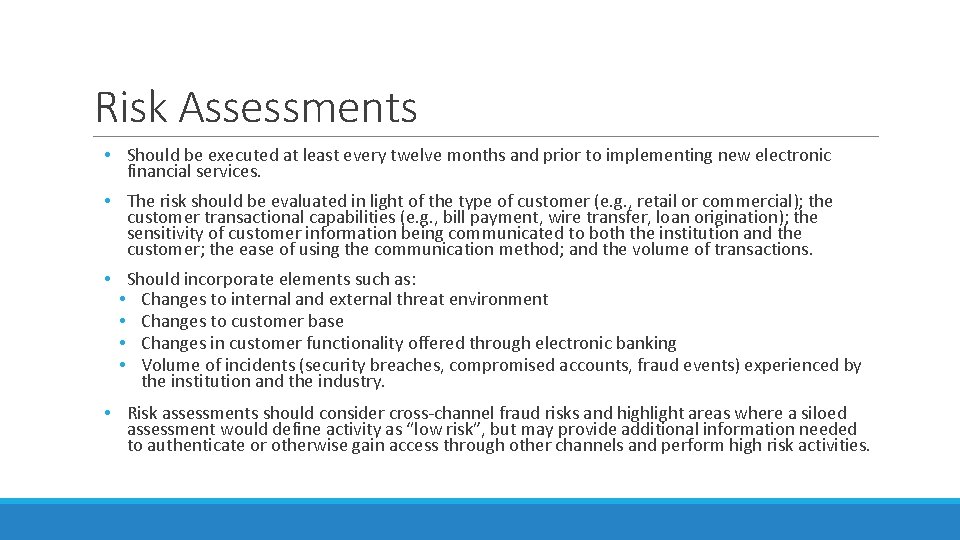
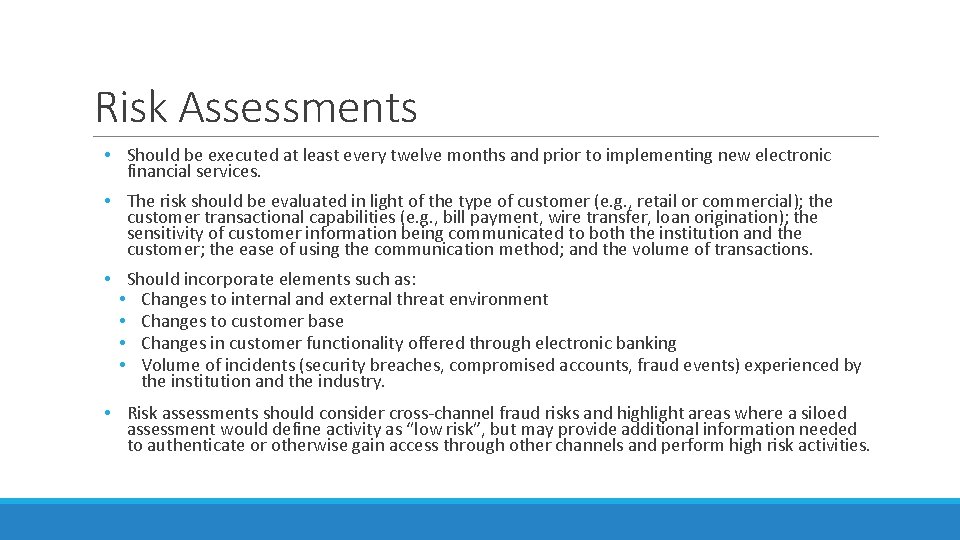
Risk Assessments • Should be executed at least every twelve months and prior to implementing new electronic financial services. • The risk should be evaluated in light of the type of customer (e. g. , retail or commercial); the customer transactional capabilities (e. g. , bill payment, wire transfer, loan origination); the sensitivity of customer information being communicated to both the institution and the customer; the ease of using the communication method; and the volume of transactions. • Should incorporate elements such as: • Changes to internal and external threat environment • Changes to customer base • Changes in customer functionality offered through electronic banking • Volume of incidents (security breaches, compromised accounts, fraud events) experienced by the institution and the industry. • Risk assessments should consider cross-channel fraud risks and highlight areas where a siloed assessment would define activity as “low risk”, but may provide additional information needed to authenticate or otherwise gain access through other channels and perform high risk activities.
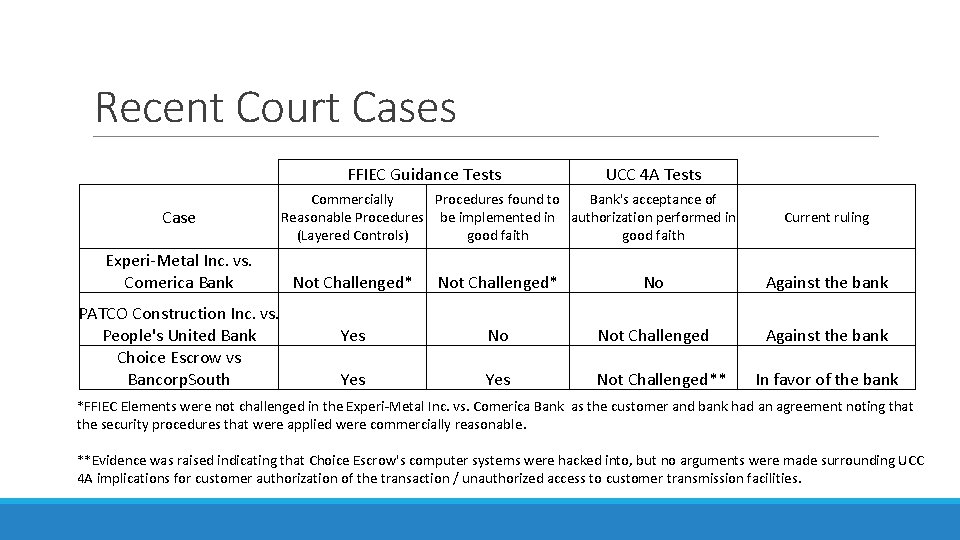
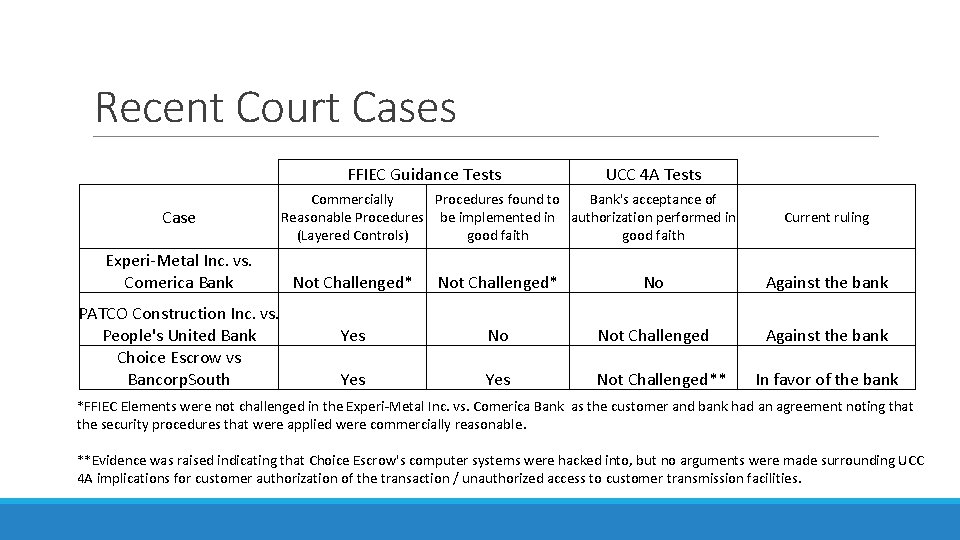
Recent Court Cases FFIEC Guidance Tests Case Experi-Metal Inc. vs. Comerica Bank PATCO Construction Inc. vs. People's United Bank Choice Escrow vs Bancorp. South UCC 4 A Tests Commercially Procedures found to Bank's acceptance of Reasonable Procedures be implemented in authorization performed in (Layered Controls) good faith Current ruling Not Challenged* No Against the bank Yes No Not Challenged Against the bank Yes Not Challenged** In favor of the bank *FFIEC Elements were not challenged in the Experi-Metal Inc. vs. Comerica Bank as the customer and bank had an agreement noting that the security procedures that were applied were commercially reasonable. **Evidence was raised indicating that Choice Escrow's computer systems were hacked into, but no arguments were made surrounding UCC 4 A implications for customer authorization of the transaction / unauthorized access to customer transmission facilities.
New FFIEC Working Group June 6, 2013: FFIEC Forms Cybersecurity and Critical Infrastructure Working Group Objective of the working group is to further promote coordination across the federal and state banking regulatory agencies on critical infrastructure and cybersecurity issues such as the growing sophistication and volume of cyber attacks and the global importance of critical financial infrastructure. - Changes/updates to authentication guidance forthcoming from this committee?
Questions?