Fences Make Good Neighbors Monitoring Academic Networks at
Fences Make Good Neighbors Monitoring Academic Networks at the Port Level Educause Security Conference April 4, 5 2005 Washington DC David La. Porte / Kevin Amorin Harvard University Angelo Bravos Judson College
Topics ¨ Overview of the problems/needs ¨ Solutions – Bradford Campus. Manager – Packet. Fence ¨ Questions 1
Network (In)security ¨ Perimeter security – Firewalls, IDS, IPS, Router ACLs – “Hard on the outside soft on the inside” – Leads to complacency ¨ 60 -80% of attacks originate from systems on the internal network (behind the firewall) – VPN – Wireless – Dial-up 2
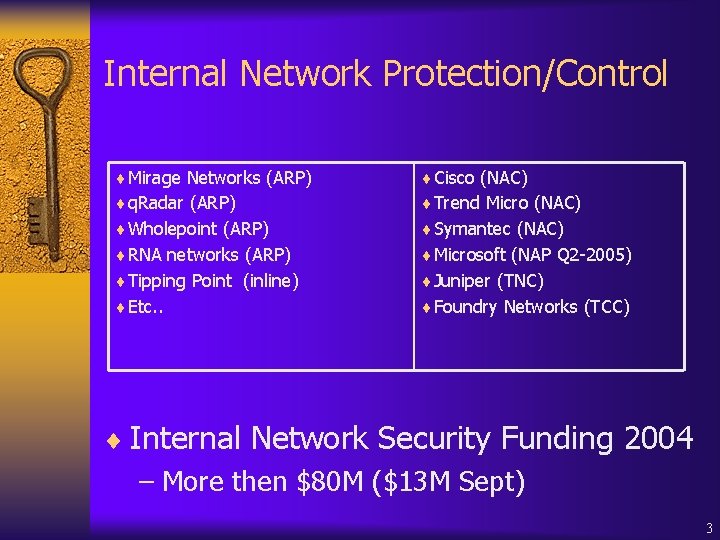
Internal Network Protection/Control ¨Mirage Networks (ARP) ¨Cisco (NAC) ¨q. Radar (ARP) ¨Trend Micro (NAC) ¨Wholepoint (ARP) ¨Symantec (NAC) ¨RNA networks (ARP) ¨Microsoft (NAP Q 2 -2005) ¨Tipping Point (inline) ¨Juniper (TNC) ¨Etc. . ¨Foundry Networks (TCC) ¨ Internal Network Security Funding 2004 – More then $80 M ($13 M Sept) 3
Academic Issues ¨ Network Environment – Worms – Bot nets – DMCA – Policy violations • NATs • p 2 p applications ¨ Identity – Who owns an infected/offending system? ¨ Support – Do you want to be manning the helpdesk on move -in day? 4
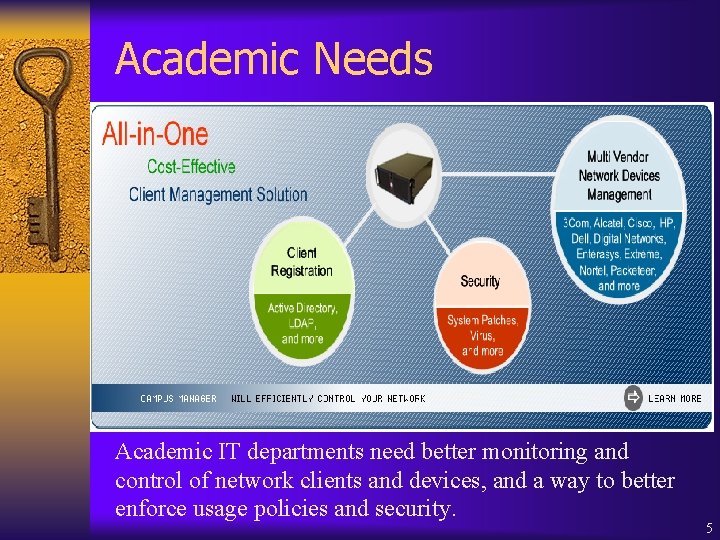
Academic Needs Academic IT departments need better monitoring and control of network clients and devices, and a way to better enforce usage policies and security. 5
Academic Needs - Clients ¨ Dealing with Hosts with no antivirus ¨ Better Client Management for all users accessing the network (Direct & Wireless) ¨ Better client management for Dorms and open labs ¨ Enforcing acceptable usage policy ¨ Identifying roamers ¨ Denying/restricting service to certain groups ¨ Restricting certain applications, chat, p 2 p, gaming 6
Academic Needs – Network management ¨ Better management of different equipment: Cisco, HP, 3 Com, Enterasys, Packeteer, Nortel, Alcatel ¨ Better Internet and Intranet bandwidth management ¨ Enable and disable ports ¨ Port-based VLAN switching ¨ Discover network devices and connectivity ¨ Alarm and notify on network events ¨ Detection of Multi-Access Points ¨ DHCP Application Server Management 7
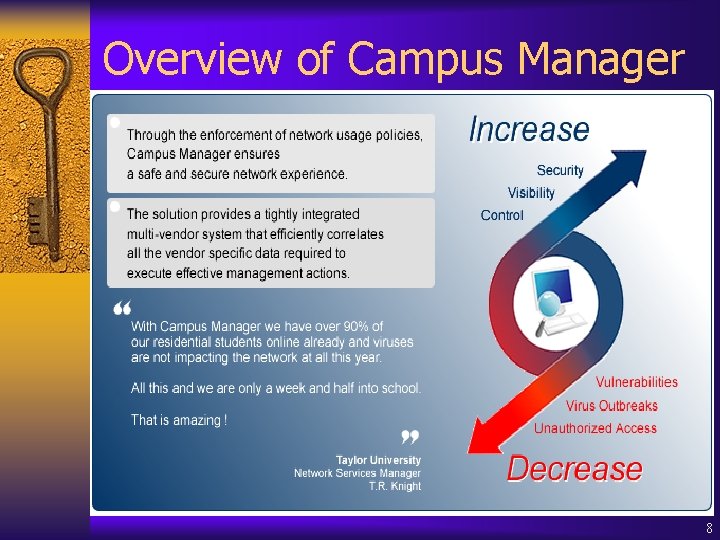
Overview of Campus Manager 8
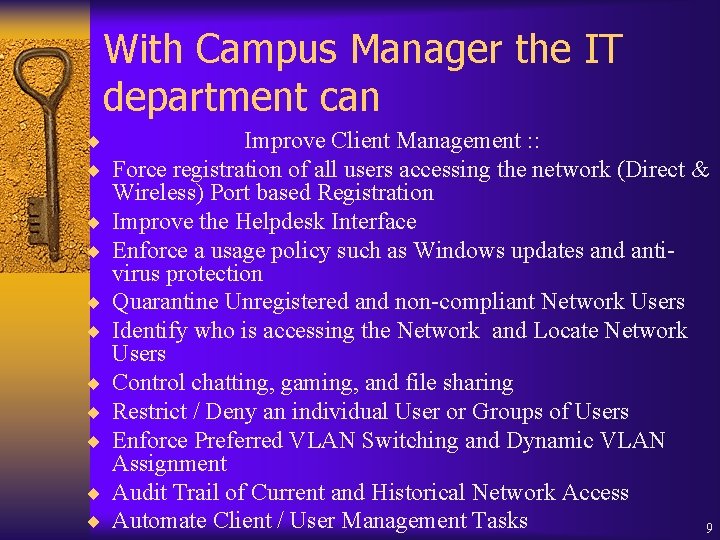
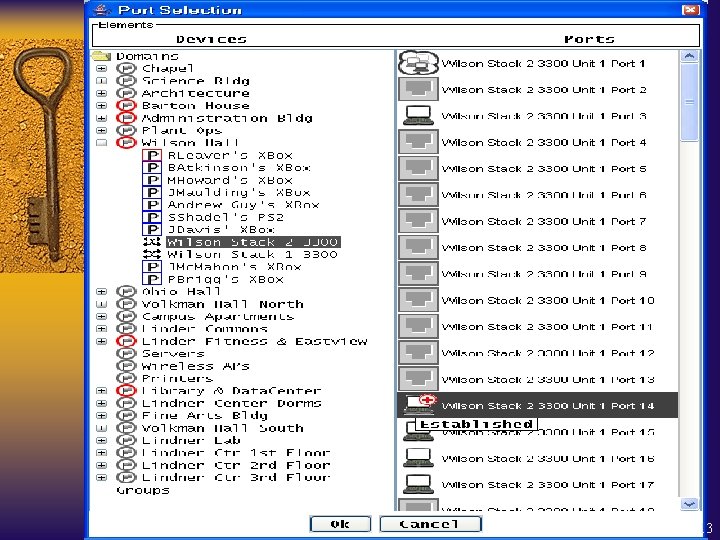
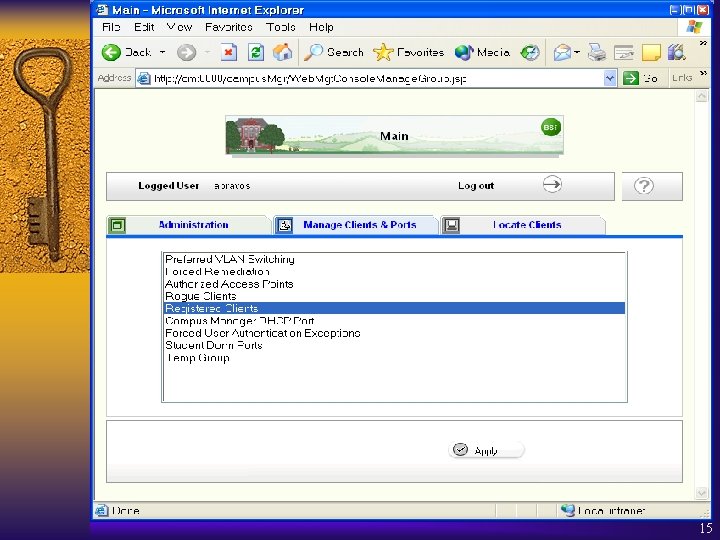
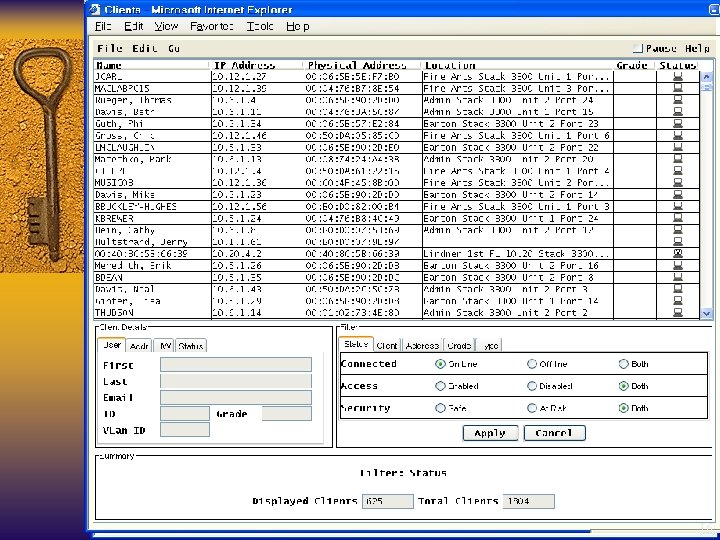
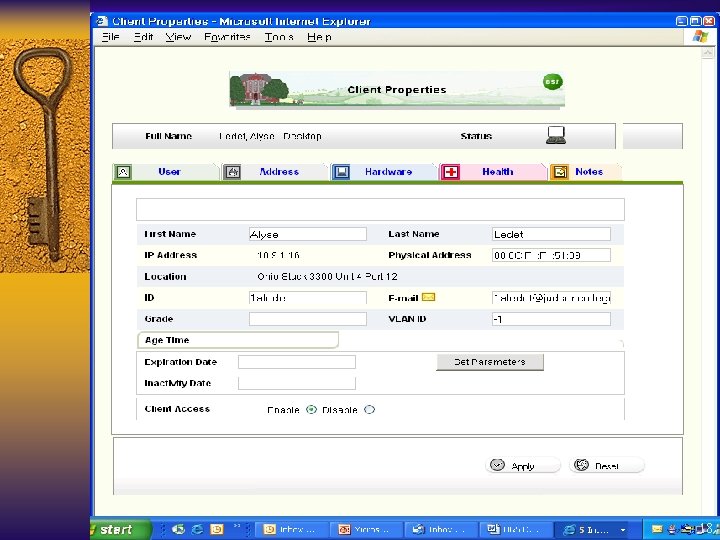
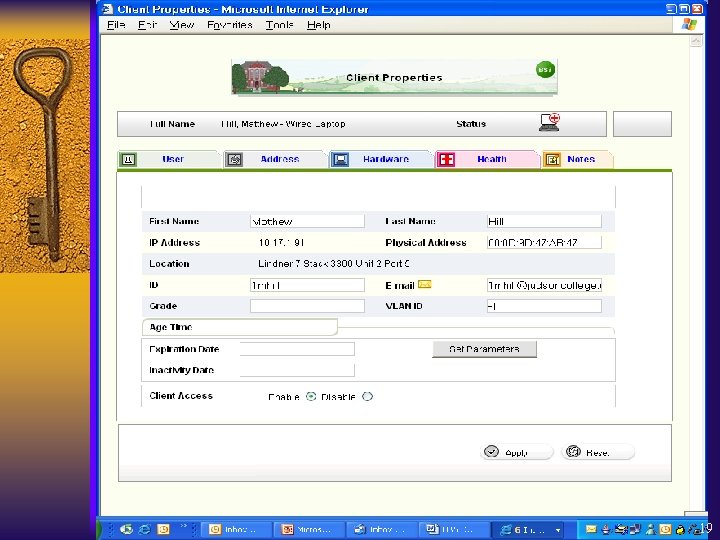
With Campus Manager the IT department can ¨ Improve Client Management : : ¨ Force registration of all users accessing the network (Direct & ¨ ¨ ¨ ¨ ¨ Wireless) Port based Registration Improve the Helpdesk Interface Enforce a usage policy such as Windows updates and antivirus protection Quarantine Unregistered and non-compliant Network Users Identify who is accessing the Network and Locate Network Users Control chatting, gaming, and file sharing Restrict / Deny an individual User or Groups of Users Enforce Preferred VLAN Switching and Dynamic VLAN Assignment Audit Trail of Current and Historical Network Access Automate Client / User Management Tasks 9
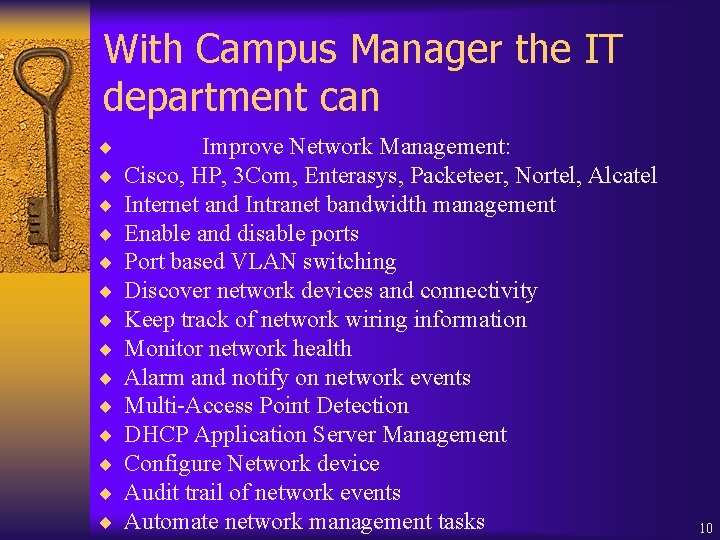
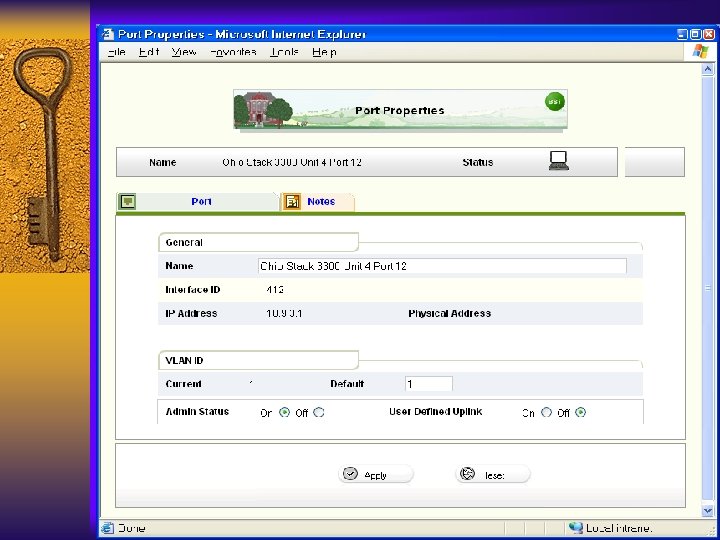
With Campus Manager the IT department can ¨ ¨ ¨ ¨ Improve Network Management: Cisco, HP, 3 Com, Enterasys, Packeteer, Nortel, Alcatel Internet and Intranet bandwidth management Enable and disable ports Port based VLAN switching Discover network devices and connectivity Keep track of network wiring information Monitor network health Alarm and notify on network events Multi-Access Point Detection DHCP Application Server Management Configure Network device Audit trail of network events Automate network management tasks 10
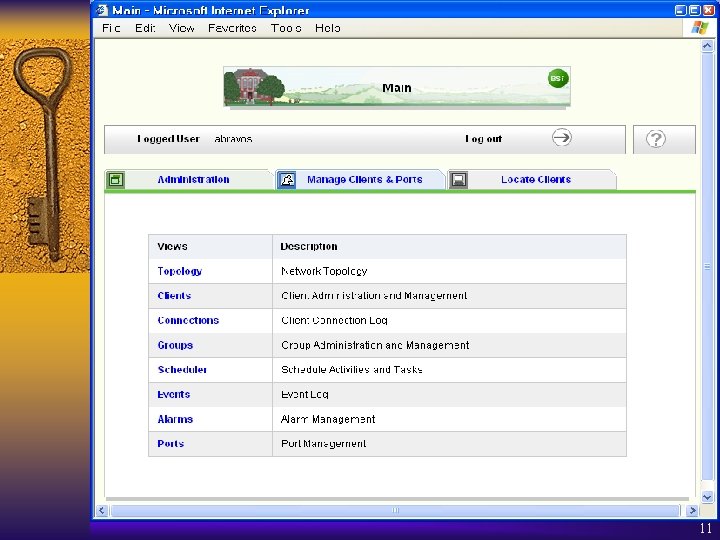
11
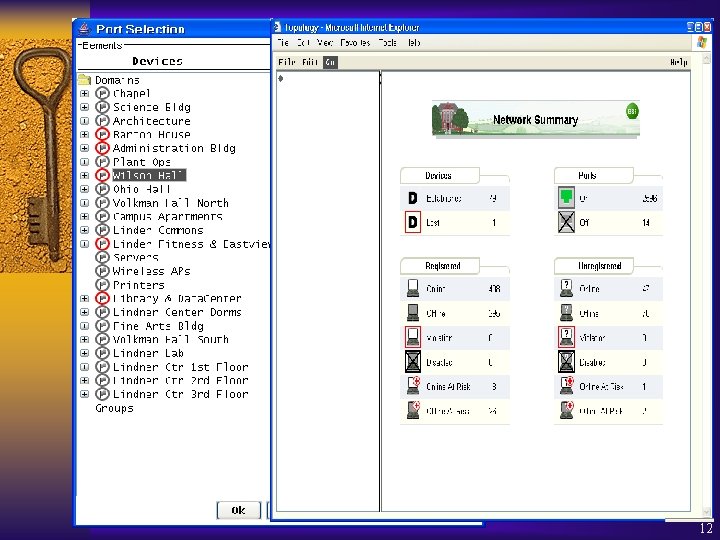
12
13

14
15
16
17
18
19

20
21
22
What is Packet. Fence ¨ Open-source network registration and worm mitigation solution – Co-developed by Kevin Amorin and David La. Porte • GUI developed by Randy Heins, UIS NOC – Captive portal • Intercepts HTTP sessions and forces client to view content • Similar to Bluesocket – Based on un-modified open-source components 23
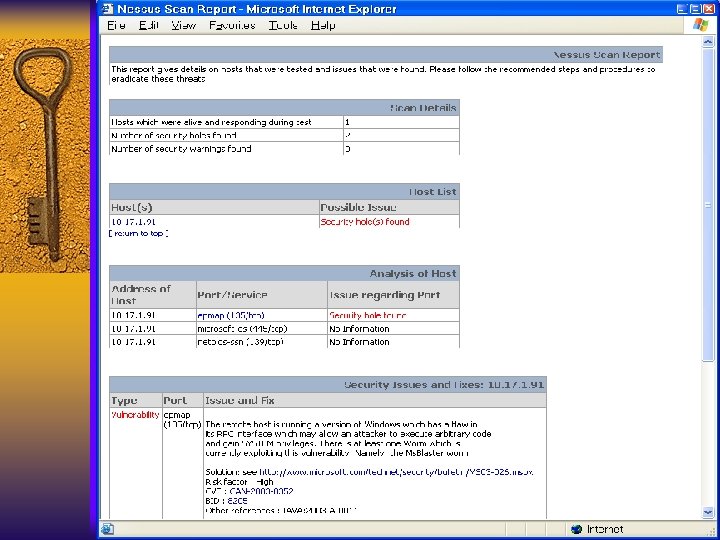
Features ¨ Network registration – Register systems to an authenticated user • LDAP, RADIUS, POP, IMAP…anything Apache supports – Force AUP acceptance – Stores assorted system information • Net. BIOS computer name & Web browser user-agent string • Presence of some NAT device – Stores no personal information • ID->MAC mapping only – Above data can provide a rough system inventory – Vulnerability scans • at registration • scheduled/ad hoc 24
Features ¨ Worm mitigation – Behavioral and signature-based detection – Optional isolation of infected nodes • Implemented but not deployed – Self-remediation • Empower users • Provides remediation instruction specific to infection ¨ Network “inoculation” – Preemptively detect and trap vulnerable hosts 25
Features ¨ Remediation – Requires signature-based detect – Provides user context-specific remediation instructions – Redirection to the captive portal • via Proxy • via Firewall pass-through – Helpdesk support number if all else fails 26
Inline ¨ Security bottleneck – immune to subversion ¨ Fail-closed ¨ Performance bottleneck ¨ Single point of failure ¨ May not be necessary/preferable – academia 27
Passive ¨ Fail-open solution – Preferable in academic environment ¨ No bandwidth bottlenecks ¨ Network visibility – Hub, monitor port, tap ¨ Easy integrating – no changes to infrastructure – plug and play (pray? ) ¨ Manipulates client ARP cache – “Virtually” in-line 28
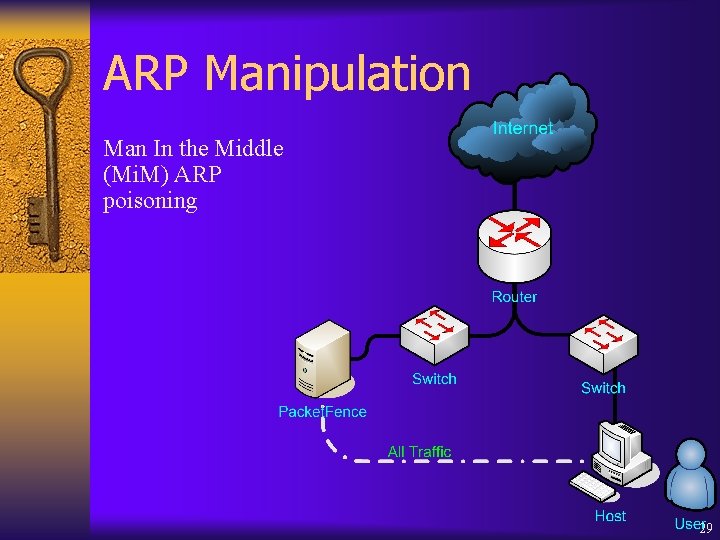
ARP Manipulation Man In the Middle (Mi. M) ARP poisoning 29
Detection (optional) ¨ Traffic analysis – Anomaly based – Signature based – Time based ¨ Snort with small signature set & portscan ¨ Any signature and/or anomaly based detection tool can be used (“glue” will be necessary) 30
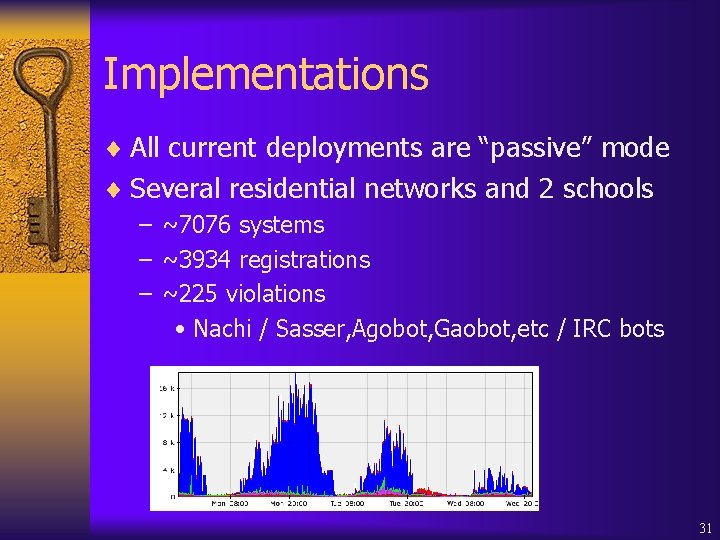
Implementations ¨ All current deployments are “passive” mode ¨ Several residential networks and 2 schools – ~7076 systems – ~3934 registrations – ~225 violations • Nachi / Sasser, Agobot, Gaobot, etc / IRC bots 31
Coming Soon… ¨ Static IP/ARP Detection ¨ DHCP Combat ¨ Queue-based Violation/Registration ¨ Independent components ¨ Isolation mechanisms – DHCP • Change DHCP scope (reserved IP with enforcer gateway) • Change DNS server to resolve all IP’s to Enforcer – Switch port manipulation • Change VLAN to isolation network • Disable port 32
In Closing ¨ Packet. Fence – Open-source – Passive deployment • “plug and play” • no infrastructure changes needed – Proactive and reactive remediation – Extremely configurable 33
In Closing – Campus Manager ¨ ¨ ¨ ¨ ¨ An all-in-one management solution Provides managed network access to all clients Manages and controls wireless network access Enforces a campus wide network usage policy Reduces the time to - Locate users - Take action on network access violations - Detect network problems Troubleshoot network problems - Configure network devices Delegates client management to network operators and helpdesk personnel Vendor independent solution Passive management system on the network Comprehensive integrations with vendor solutions Reallocate IT staff from building management solutions to managing the network services 34
35
- Slides: 36