Federated RBAC Fortress OAuth 2 JWT Java EE
Federated RBAC: Fortress, OAuth 2, JWT, Java EE, & JASPIC Federated Role-Based Access Control Security
“WE ARE” - Software Engineering Chris Harm (Manager of Software Infrastructure) Steve Moyer (Enterprise Software Architect) Shawn Smith (Director of Software Engineering) Shawn Mc. Kinney (Symas - Software Architect) Federated Role-Based Access Control Security
Problem Statement • Our team is responsible for almost 100 applications (and growing) • Many hand coded specialized RBAC systems • Penn State is a large decentralized organization • Historically systems had considered Authentication == Authorization • Existing IAM evolved over many years • Legacy authorization is based primarily on LDAP groups Federated Role-Based Access Control Security

Scope • Students 96 k • Employees 26 k • Campuses 24 • Locations > 100 • Departments 100 s • Titles 1 1000 s 1. (Job descriptions, positions, etc) Federated Role-Based Access Control Security
Implications • Centralized role and permission granting and revoking is impossible • Mapping “titles” to roles is impossible • Those who know how to map employees (and sometimes students) into roles are commonly not in an IT organization • We need a clear migration path from custom IAM to a common security system Federated Role-Based Access Control Security
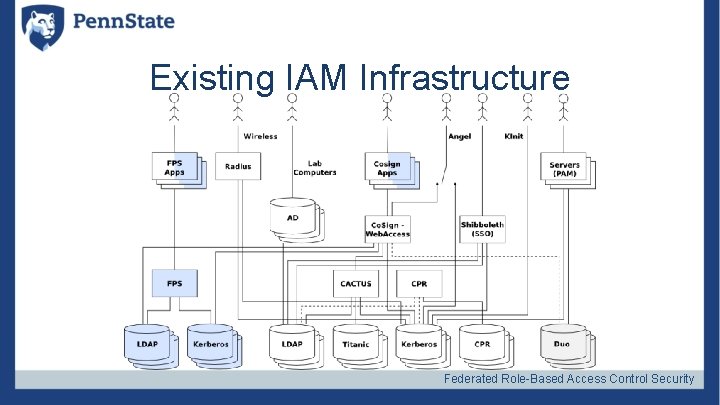
Existing IAM Infrastructure Federated Role-Based Access Control Security

Goals • Functional Goals • End to end security chaining • Delegated role creation, granting and revoking • Course grained access control (method access) • Fine grained access control (data slicing) • Implementation Goals • Performant and Scaleable • Pluggable • Standards compliant Federated Role-Based Access Control Security
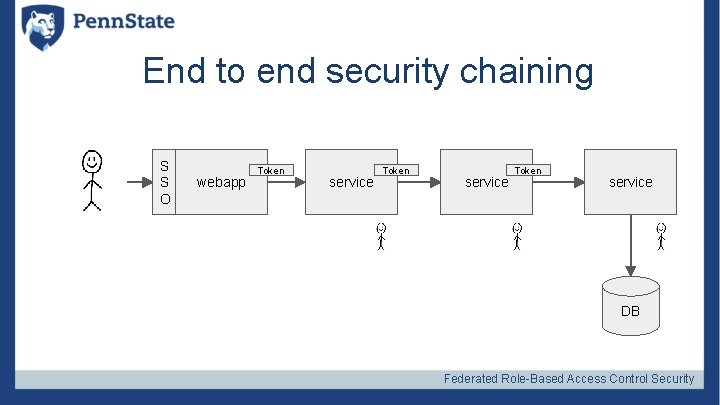
End to end security chaining S S O webapp Token service DB Federated Role-Based Access Control Security
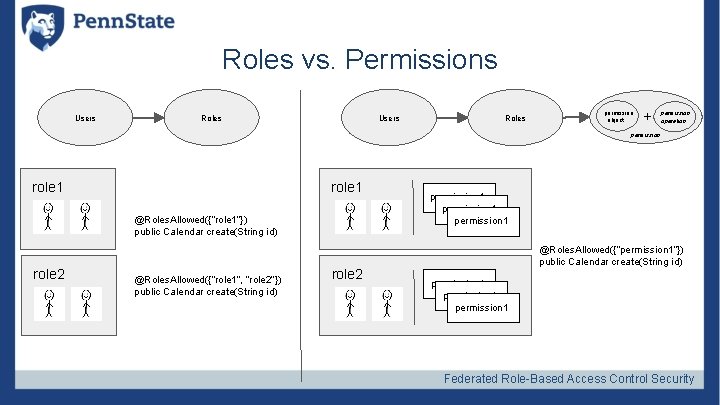
Roles vs. Permissions Users Roles permission object + permission operation permission role 1 @Roles. Allowed({“role 1”}) public Calendar create(String id) role 2 @Roles. Allowed({“role 1”, “role 2”}) public Calendar create(String id) role 2 permission 1 @Roles. Allowed({“permission 1”}) public Calendar create(String id) permission 1 Federated Role-Based Access Control Security
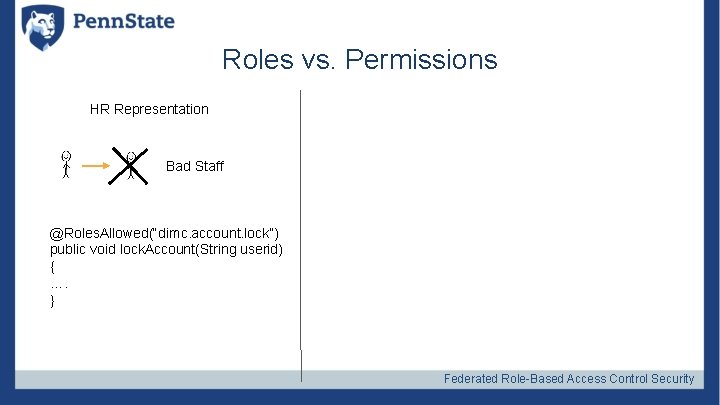
Roles vs. Permissions HR Representation Bad Staff @Roles. Allowed(“dimc. account. lock”) public void lock. Account(String userid) { …. } Federated Role-Based Access Control Security
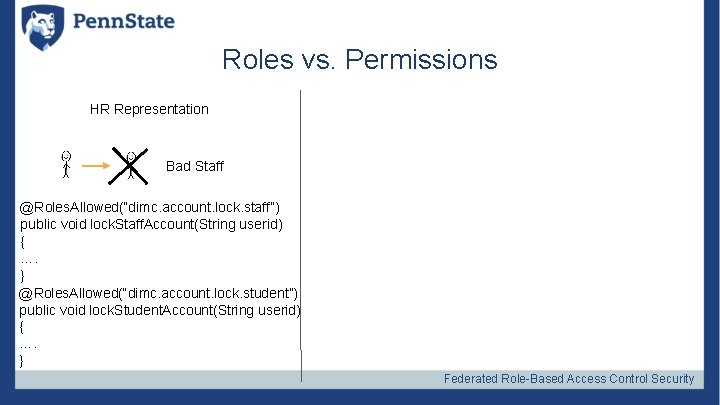
Roles vs. Permissions HR Representation Bad Staff @Roles. Allowed(“dimc. account. lock. staff”) public void lock. Staff. Account(String userid) { …. } @Roles. Allowed(“dimc. account. lock. student”) public void lock. Student. Account(String userid) { …. } Federated Role-Based Access Control Security
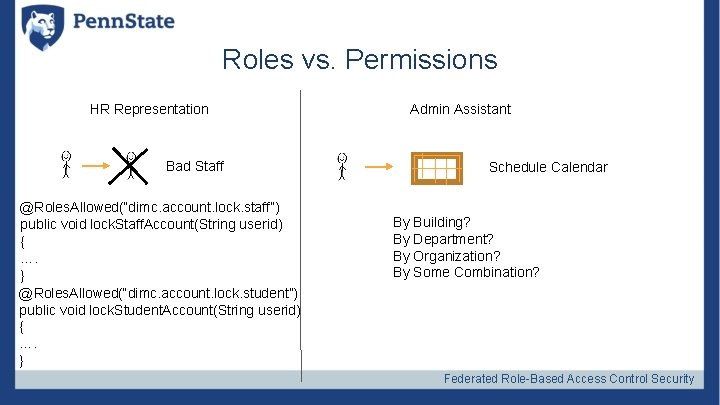
Roles vs. Permissions HR Representation Bad Staff @Roles. Allowed(“dimc. account. lock. staff”) public void lock. Staff. Account(String userid) { …. } @Roles. Allowed(“dimc. account. lock. student”) public void lock. Student. Account(String userid) { …. } Admin Assistant Schedule Calendar By Building? By Department? By Organization? By Some Combination? Federated Role-Based Access Control Security
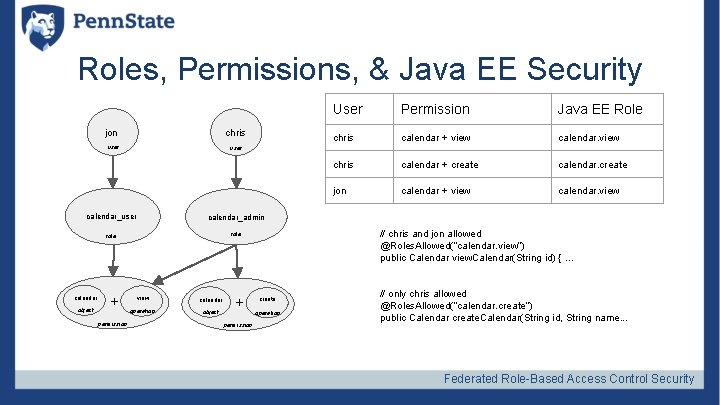
Roles, Permissions, & Java EE Security jon chris user calendar_admin role object + permission Permission Java EE Role chris calendar + view calendar. view chris calendar + create calendar. create jon calendar + view calendar. view user calendar_user calendar User view calendar operation object + permission // chris and jon allowed @Roles. Allowed(“calendar. view”) public Calendar view. Calendar(String id) { … create operation // only chris allowed @Roles. Allowed(“calendar. create”) public Calendar create. Calendar(String id, String name. . . Federated Role-Based Access Control Security
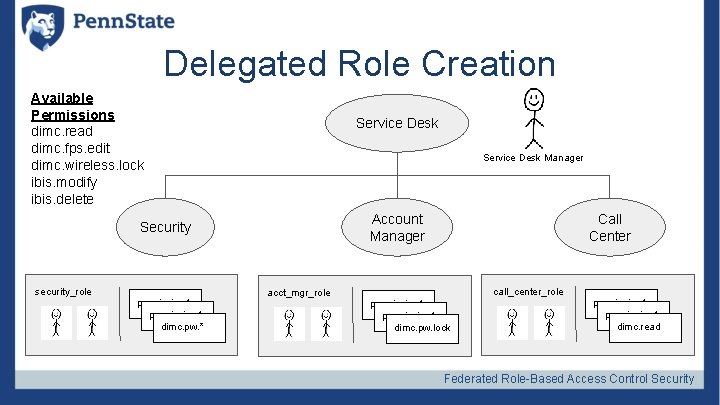
Delegated Role Creation Available Permissions dimc. read dimc. fps. edit dimc. wireless. lock ibis. modify ibis. delete Service Desk Manager Account Manager Security security_role permission 1 dimc. pw. * Call Center call_center_role acct_mgr_role permission 1 dimc. pw. lock permission 1 dimc. read Federated Role-Based Access Control Security
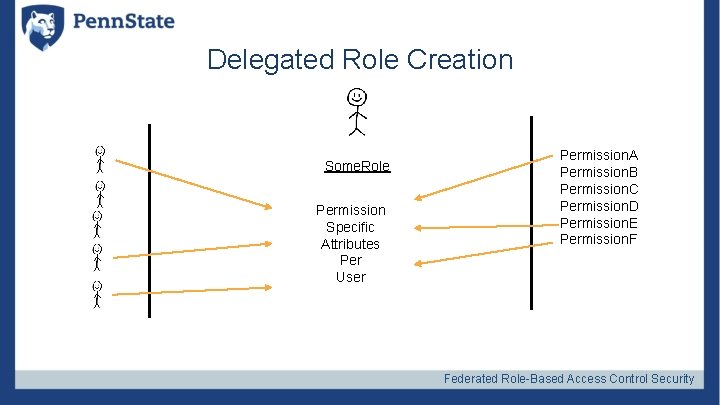
Delegated Role Creation Some. Role Permission Specific Attributes Per User Permission. A Permission. B Permission. C Permission. D Permission. E Permission. F Federated Role-Based Access Control Security

What we’ve done. . . Federated Role-Based Access Control Security
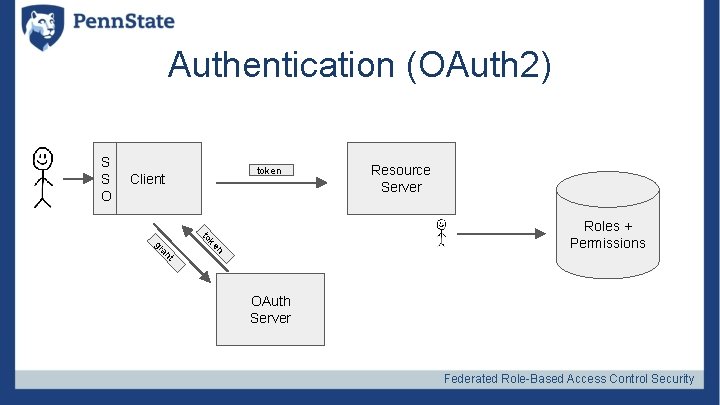
Authentication (OAuth 2) S S O token Client Resource Server t an n gr ke to Roles + Permissions OAuth Server Federated Role-Based Access Control Security
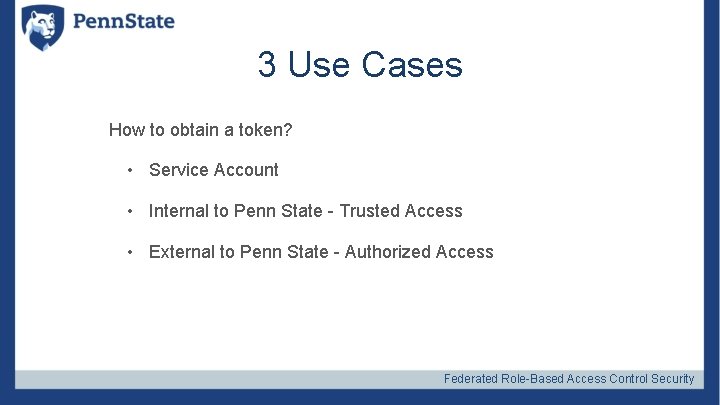
3 Use Cases How to obtain a token? • Service Account • Internal to Penn State - Trusted Access • External to Penn State - Authorized Access Federated Role-Based Access Control Security
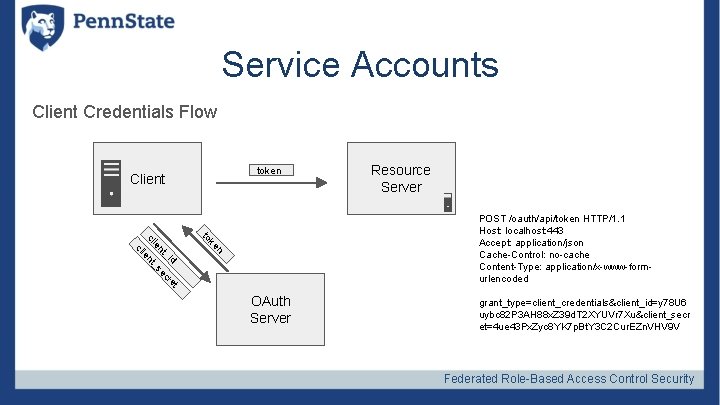
Service Accounts Client Credentials Flow token Client Resource Server n ke to id t re ec _s nt ie _ nt ie cl cl POST /oauth/api/token HTTP/1. 1 Host: localhost: 443 Accept: application/json Cache-Control: no-cache Content-Type: application/x-www-formurlencoded OAuth Server grant_type=client_credentials&client_id=y 78 U 6 uybc 82 P 3 AH 88 x. Z 39 d. T 2 XYUVr 7 Xu&client_secr et=4 ue 43 Px. Zyc 8 YK 7 p. Bt. Y 3 C 2 Cur. EZn. VHV 9 V Federated Role-Based Access Control Security
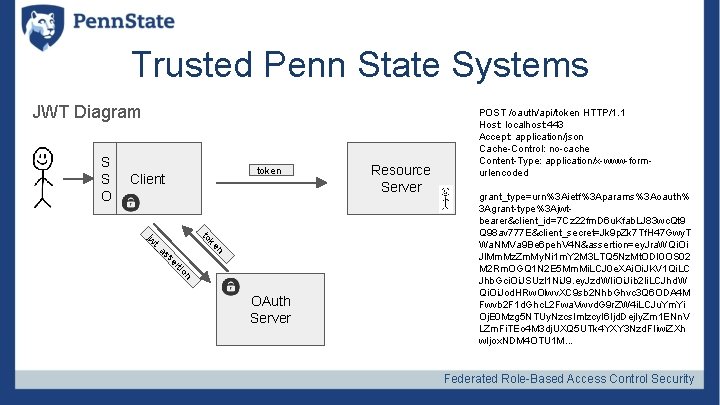
Trusted Penn State Systems JWT Diagram S S O token Client to n a t_ ke jw n tio er ss OAuth Server Resource Server POST /oauth/api/token HTTP/1. 1 Host: localhost: 443 Accept: application/json Cache-Control: no-cache Content-Type: application/x-www-formurlencoded grant_type=urn%3 Aietf%3 Aparams%3 Aoauth% 3 Agrant-type%3 Ajwtbearer&client_id=7 Cz 22 fm. D 6 u. Kfab. LJ 83 wc. Qt 9 Q 98 av 777 E&client_secret=Jk 9 p. Zk 7 Tf. H 47 Gwy. T Wa. NMVa 9 Be 6 peh. V 4 N&assertion=ey. Jra. WQi. Oi Jl. Mm. Mz. Zm. My. Ni 1 m. Y 2 M 3 LTQ 5 Nz. Mt. ODI 0 OS 02 M 2 Rm. OGQ 1 N 2 E 5 Mm. Mi. LCJ 0 e. XAi. Oi. JKV 1 Qi. LC Jhb. Gci. Oi. JSUz. I 1 Ni. J 9. ey. Jzd. WIi. Oi. Jib 2 Ii. LCJhd. W Qi. Oi. Jod. HRw. Olwv. XC 9 sb 2 Nhb. Ghvc 3 Q 6 ODA 4 M Fwvb 2 F 1 d. Ghc. L 2 Fwa. Vwvd. G 9 r. ZW 4 i. LCJu. Ym. Yi Oj. E 0 Mzg 5 NTUy. Nzcs. Imlzcy. I 6 Ijd. Dej. Iy. Zm 1 ENn. V LZm. Fi. TEo 4 M 3 dj. UXQ 5 UTk 4 YXY 3 Nzd. FIiwi. ZXh w. Ijox. NDM 4 OTU 1 M. . . Federated Role-Based Access Control Security
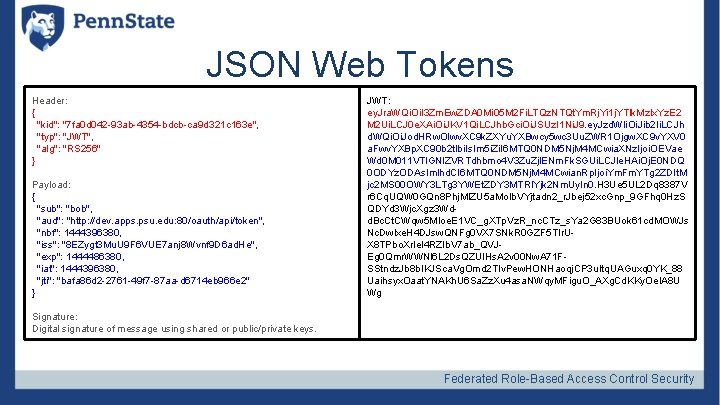
JSON Web Tokens Header: { "kid": "7 fa 0 d 042 -93 ab-4354 -bdcb-ca 9 d 321 c 163 e", "typ": "JWT", "alg": "RS 256" } Payload: { "sub": "bob", "aud": "http: //dev. apps. psu. edu: 80/oauth/api/token", "nbf": 1444396380, "iss": "8 EZygt 3 Mu. U 9 F 6 VUE 7 anj 8 Wvnf 9 D 6 ad. He", "exp": 1444486380, "iat": 1444396380, "jti": "bafa 86 d 2 -2761 -49 f 7 -87 aa-d 6714 eb 966 e 2" } JWT: ey. Jra. WQi. Oi. I 3 Zm. Ew. ZDA 0 Mi 05 M 2 Fi. LTQz. NTQt. Ym. Rj. Yi 1 j. YTlk. Mz. Ix. Yz. E 2 M 2 Ui. LCJ 0 e. XAi. Oi. JKV 1 Qi. LCJhb. Gci. Oi. JSUz. I 1 Ni. J 9. ey. Jzd. WIi. Oi. Jib 2 Ii. LCJh d. WQi. Oi. Jod. HRw. Olwv. XC 9 k. ZXYu. YXBwcy 5 wc 3 Uu. ZWR 1 Ojgw. XC 9 v. YXV 0 a. Fwv. YXBp. XC 90 b 2 tlbi. Is. Im 5 i. Zi. I 6 MTQ 0 NDM 5 Nj. M 4 MCwia. XNz. Ijoi. OEVae Wd 0 M 011 VTl. GNl. ZVRTdhbmo 4 V 3 Zu. Zjl. ENm. Fk. SGUi. LCJle. HAi. Oj. E 0 NDQ 0 ODYz. ODAs. Imlhd. CI 6 MTQ 0 NDM 5 Nj. M 4 MCwian. Rp. Ijoi. Ym. Fm. YTg 2 ZDIt. M jc 2 MS 00 OWY 3 LTg 3 YWEt. ZDY 3 MTRl. Yjk 2 Nm. Uy. In 0. H 3 Ue 5 UL 2 Dq 8387 V r 6 Cq. UQW 0 GQn 8 Phj. Ml. ZU 5 a. Mo. Ib. VYjtadn 2_r. Jbej 52 xc. Gnp_9 GFhq 0 Hz. S QDYd 3 Wjc. Xgz 3 Wdd. Bc. Ct. CWqw 5 MIoe. E 1 VC_g. XTp. Vz. R_nc. CTz_s. Ya 2 G 83 BUok 61 cd. MOWJs Nc. Dwlxe. H 4 DJsw. QNFg 0 VX 7 SNk. R 0 GZF 5 TIr. UX 8 TPbo. Xr. Iel 4 RZIb. V 7 ab_QVJEg 0 Qmr. WWNl 6 L 2 Ds. QZUl. Hs. A 2 v 00 Nw. A 71 FSStndz. Jb 8 b. IKJSca. Vg. Omd 2 TIv. Pew. HONHaoqj. CP 3 u. Itq. UAGuxq 0 YK_88 Uaihsyx. Oaat. YNAKh. U 6 Sa. Zz. Xu 4 asa. NWqy. MFigu. O_AXg. Cd. KKy. Oe. IA 8 U Wg Signature: Digital signature of message using shared or public/private keys. Federated Role-Based Access Control Security
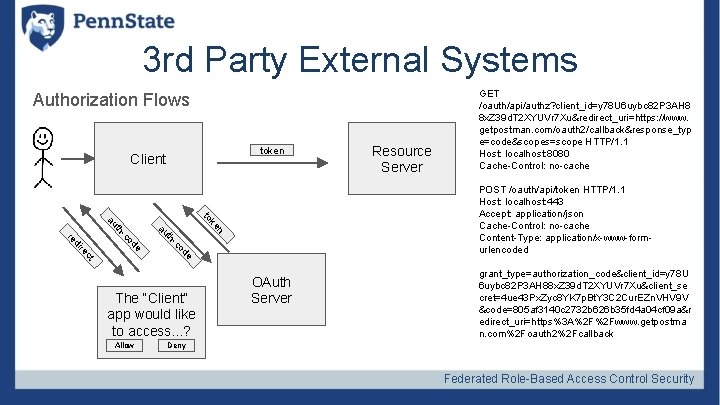
3 rd Party External Systems Authorization Flows token Client POST /oauth/api/token HTTP/1. 1 Host: localhost: 443 Accept: application/json Cache-Control: no-cache Content-Type: application/x-www-formurlencoded ke to n au o -c th de t c re e od -c th au di re The “Client” app would like to access. . . ? Allow Resource Server GET /oauth/api/authz? client_id=y 78 U 6 uybc 82 P 3 AH 8 8 x. Z 39 d. T 2 XYUVr 7 Xu&redirect_uri=https: //www. getpostman. com/oauth 2/callback&response_typ e=code&scopes=scope HTTP/1. 1 Host: localhost: 8080 Cache-Control: no-cache OAuth Server grant_type=authorization_code&client_id=y 78 U 6 uybc 82 P 3 AH 88 x. Z 39 d. T 2 XYUVr 7 Xu&client_se cret=4 ue 43 Px. Zyc 8 YK 7 p. Bt. Y 3 C 2 Cur. EZn. VHV 9 V &code=805 af 3140 c 2732 b 626 b 35 fd 4 a 04 cf 09 a&r edirect_uri=https%3 A%2 F%2 Fwww. getpostma n. com%2 Foauth 2%2 Fcallback Deny Federated Role-Based Access Control Security

How to Validate Access Tokens are opaque to the client, but the Resource Server and OAuth Server need to understand how to create and validate the tokens Options • Shared DB Resource Server Client • REST Callback to OAuth Service • JWT encoded Access Tokens OAuth Server Federated Role-Based Access Control Security
Java. EE Integration with JASPI Java Authentication Service Provider Interface for Containers - JASPI(C) Implementation based off Java. EE 7 Samples Project (https: //github. com/javaeesamples/javaee 7 -samples/tree/master/jaspic) Integrated with Wildfly Security Context propagates throughout entire container (Web tier to EJB tier) Federated Role-Based Access Control Security
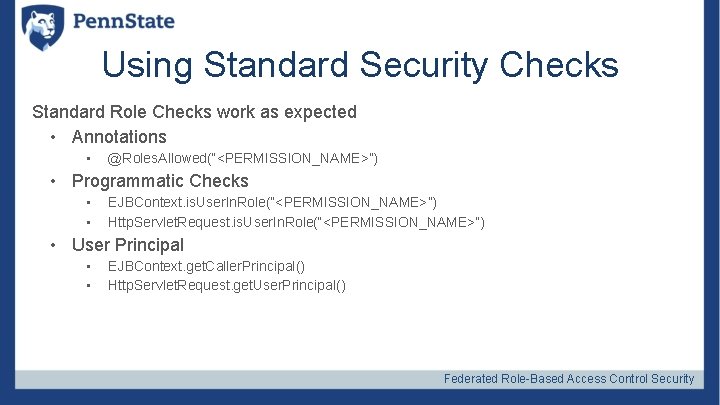
Using Standard Security Checks Standard Role Checks work as expected • Annotations • @Roles. Allowed(“<PERMISSION_NAME>”) • Programmatic Checks • • EJBContext. is. User. In. Role(“<PERMISSION_NAME>”) Http. Servlet. Request. is. User. In. Role(“<PERMISSION_NAME>”) • User Principal • • EJBContext. get. Caller. Principal() Http. Servlet. Request. get. User. Principal() Federated Role-Based Access Control Security
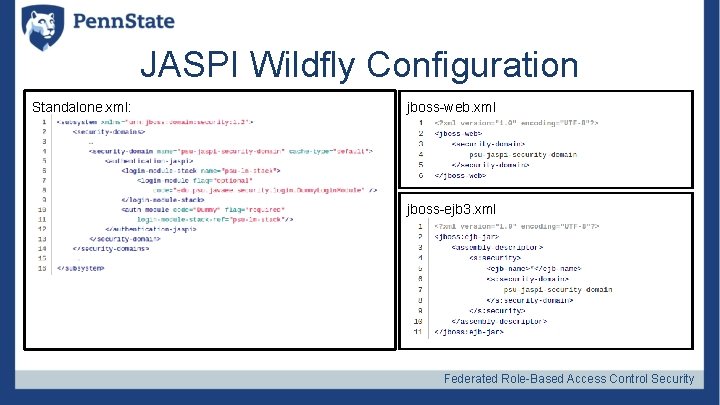
JASPI Wildfly Configuration Standalone. xml: jboss-web. xml jboss-ejb 3. xml Federated Role-Based Access Control Security
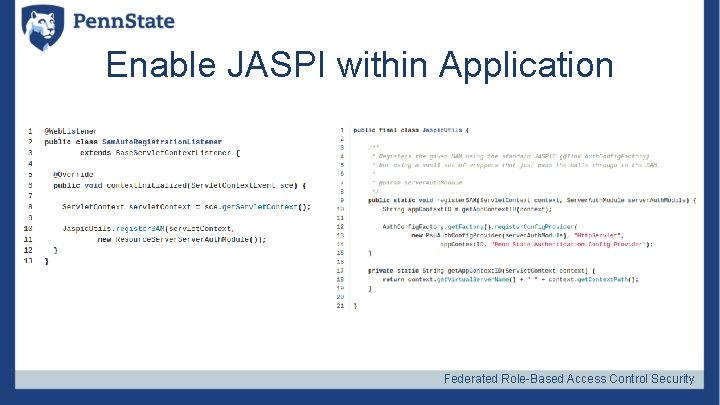
Enable JASPI within Application Federated Role-Based Access Control Security
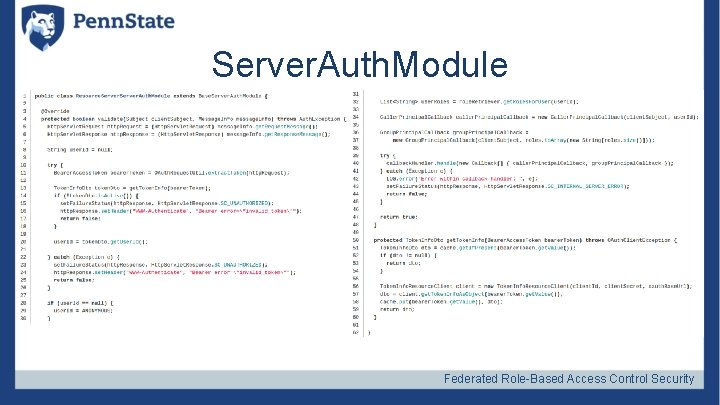
Server. Auth. Module Federated Role-Based Access Control Security
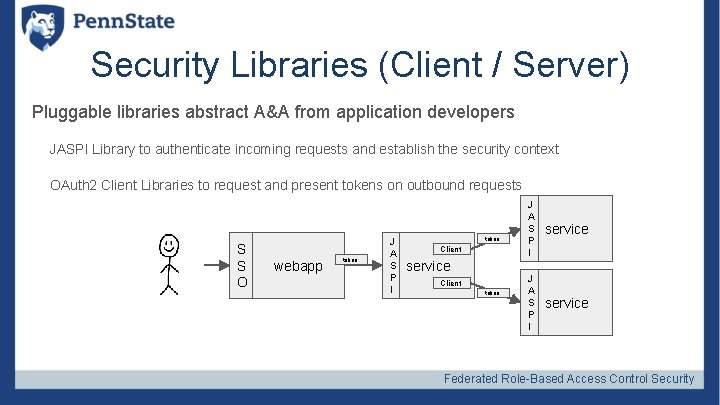
Security Libraries (Client / Server) Pluggable libraries abstract A&A from application developers JASPI Library to authenticate incoming requests and establish the security context OAuth 2 Client Libraries to request and present tokens on outbound requests S S O webapp token J A S P I token Client service Client token J A S P I service Federated Role-Based Access Control Security
Audit As services proliferate it becomes more important to be able to audit the entire chain of authority through a single transaction. Federated Role-Based Access Control Security
Authorization (Apache Fortress) Apache Fortress Overview * Apache 2. 0 License * Sub-project of Apache Directory * Java Based Identity and Access Management * Permission-based Access Control Model (RBAC) Federated Role-Based Access Control Security
Authorization (Apache Fortress) Four. Components: * Core – Java APIs + utilities * Realm – Java EE policy enforcement – Web – Administrative UI * Rest – APIs over HTTP interface LDAPv 3 Compliant: * Works with Open. LDAP and Apache Directory Server by default. * Other possible Federated Role-Based Access Control Security
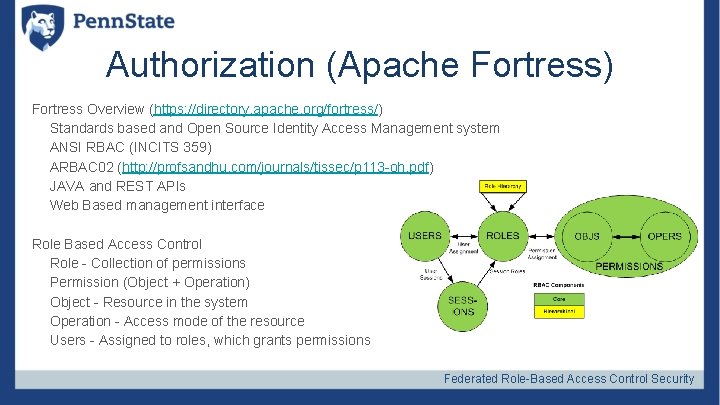
Authorization (Apache Fortress) Fortress Overview (https: //directory. apache. org/fortress/) Standards based and Open Source Identity Access Management system ANSI RBAC (INCITS 359) ARBAC 02 (http: //profsandhu. com/journals/tissec/p 113 -oh. pdf) JAVA and REST APIs Web Based management interface Role Based Access Control Role - Collection of permissions Permission (Object + Operation) Object - Resource in the system Operation - Access mode of the resource Users - Assigned to roles, which grants permissions Federated Role-Based Access Control Security
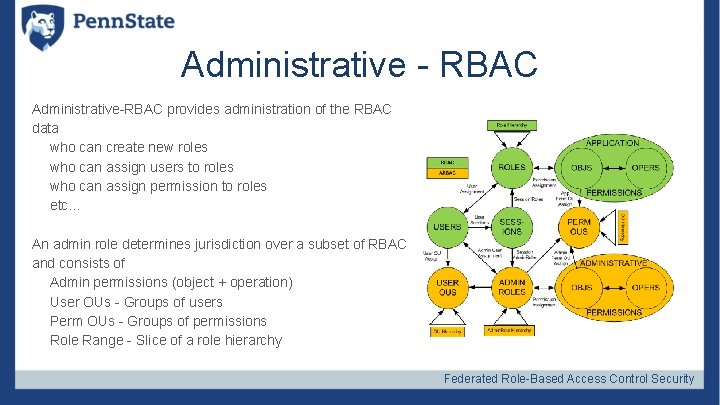
Administrative - RBAC Administrative-RBAC provides administration of the RBAC data who can create new roles who can assign users to roles who can assign permission to roles etc… An admin role determines jurisdiction over a subset of RBAC and consists of Admin permissions (object + operation) User OUs - Groups of users Perm OUs - Groups of permissions Role Range - Slice of a role hierarchy Federated Role-Based Access Control Security
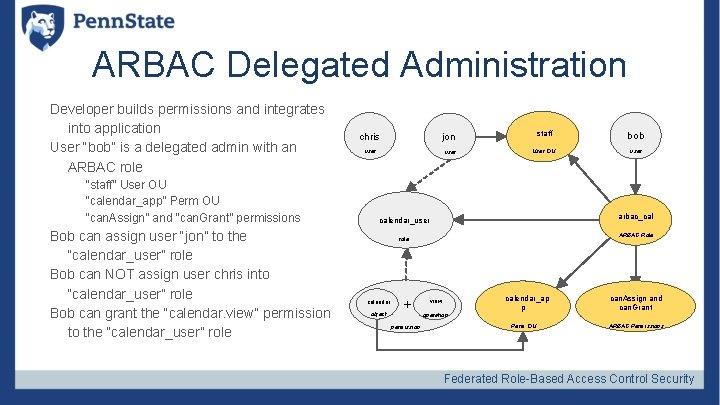
ARBAC Delegated Administration Developer builds permissions and integrates into application User “bob” is a delegated admin with an ARBAC role “staff” User OU “calendar_app” Perm OU “can. Assign” and “can. Grant” permissions Bob can assign user “jon” to the “calendar_user” role Bob can NOT assign user chris into “calendar_user” role Bob can grant the “calendar. view” permission to the “calendar_user” role chris staff bob User OU user jon user arbac_cal calendar_user ARBAC Role role calendar object + permission view operation calendar_ap p Perm OU can. Assign and can. Grant ARBAC Permissions Federated Role-Based Access Control Security
We hit a wall Federated Role-Based Access Control Security
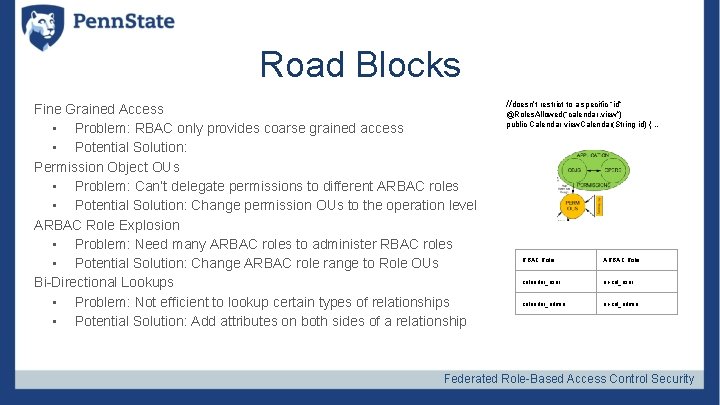
Road Blocks Fine Grained Access • Problem: RBAC only provides coarse grained access • Potential Solution: Permission Object OUs • Problem: Can’t delegate permissions to different ARBAC roles • Potential Solution: Change permission OUs to the operation level ARBAC Role Explosion • Problem: Need many ARBAC roles to administer RBAC roles • Potential Solution: Change ARBAC role range to Role OUs Bi-Directional Lookups • Problem: Not efficient to lookup certain types of relationships • Potential Solution: Add attributes on both sides of a relationship //doesn’t restrict to a specific “id” @Roles. Allowed(“calendar. view”) public Calendar view. Calendar(String id) { … RBAC Role ARBAC Role calendar_user ar-cal_user calendar_admin ar-cal_admin Federated Role-Based Access Control Security
Road Blocks How do we draw the picture? Federated Role-Based Access Control Security
Lessons Learned Doing fine grained security in a simple generic way is really hard!!! Federated Role-Based Access Control Security
(Almost) The End Federated Role-Based Access Control Security
We’re Hiring! Software Engineering - UI/UX https: //psu. jobs/job/59211 System and Network Security Analyst https: //psu. jobs/job/59541 Hardware Configuration Manager https: //psu. jobs/job/59543 Software Configuration Manager https: //psu. jobs/job/59542 Software Test Engineer https: //psu. jobs/job/59670 Other jobs at Penn State https: //psu. jobs/jobs Federated Role-Based Access Control Security
Thank You Shawn Smith – ses 44@psu. edu Steve Moyer – swm 16@psu. edu Chris Harm – crh 5255@psu. edu Shawn Mc. Kinney - smckinney@symas. com Federated Role-Based Access Control Security
Questions? Federated Role-Based Access Control Security
- Slides: 43