Federal Security Privacy Update FISMA OMB NIST Larry
Federal Security & Privacy Update: FISMA, OMB, NIST Larry G. Wlosinski, CISSP, CAP, CCSP, CISM, CISA, CRISC, CBCP, CDP, ITIL v 3 L_Wlosinski@Hotmail. com March 2016 1
Larry G. Wlosinski CISM, CISA, CRISC, CISSP, CAP, CCSP, CBCP, CDP, ITIL v 3 � Federal Government Experience (25+ yrs) ◦ � Commercial Industry Experience (14 yrs) ◦ � Insurance, International & Interstate Banking, Collections, Small Business Consulting Experience ◦ ◦ ◦ � EPA, NIH, CMS, DOJ, DHS, DOE, DIA, NOAA, SSA Veris Group, LLC – Senior Associate Computer Sciences Corp. (CSC) – Section Manager Lockheed Martin – IT Security Manager Booz Allen Hamilton (BAH) – Associate And others – Sr. IT Security Engineer, Project Manager, etc. IT Security Expertise (16+ yrs) ◦ ◦ ◦ Cybersecurity IT Security Assessments (C&A/A&A, Risk, Audit) Continuity Planning (OEP, BIA, ISCP, COOP, DRP, Devolution, etc. ) Cloud Security Policy, Procedures, Guidance, Standards, Templates, Checklists Incident Response & Planning 2 2
Agenda FISMA 2014 OMB Circular A-130 OMB Circular A-108 OMB Memoranda NIST Privacy Controls 3
FEDERAL INFORMATION SECURITY MODERNIZATION ACT (FISMA) 2014 (PUBLIC LAW 113 -283) 4
FISMA Amendment Amends the Federal Information Security Management Act of 2002 (FISMA) to: 1. Reestablish the oversight authority of the Director of the Office of Management and Budget (OMB) with respect to agency information security policies and practices, and 2. Set forth authority for the Secretary of Homeland Security (DHS) to administer the implementation of such policies and practices for information systems. 5
Requirements of the Secretary Requires the Secretary to develop and oversee implementation of operational directives requiring agencies to implement the Director's standards and guidelines for safeguarding federal information and systems from a known or reasonably suspected information security threat, vulnerability, or risk. Authorizes the Director to revise or repeal operational directives that are not in accordance with the Director's policies. Requires the Secretary (currently, the Director) to ensure the operation of the federal information security incident center (FISIC). Directs the Secretary to administer procedures to deploy technology, upon request by an agency, to assist the agency to continuously diagnose and mitigate against cyber threats and vulnerabilities. Directs the Secretary to consult with and consider guidance developed by the National Institute of Standards and Technology (NIST) to ensure that operational directives do not conflict with NIST information security standards. 6
Agency Requirements Directs agency heads to ensure that: 1. information security management processes are integrated with budgetary planning; 2. senior agency officials, including chief information officers, carry out their information security responsibilities; and 3. all personnel are held accountable for complying with the agency-wide information security program. Provides for the use of automated tools in agencies' information security programs, including for periodic risk assessments, testing of security procedures, and detecting, reporting, and responding to security incidents. Requires agencies to include offices of general counsel as recipients of security incident notices. Requires agencies to notify Congress of major security incidents within seven days after there is a reasonable basis to conclude that a major incident has occurred. 7
Agency Requirements – Cont. Directs agencies to submit an annual report regarding major incidents to OMB, DHS, Congress, and the Comptroller General (GAO). Requires such reports to include: 1. threats and threat actors, vulnerabilities, and impacts; 2. risk assessments of affected systems before, and the status of compliance of the systems at the time of, major incidents; 3. detection, response, and remediation actions; 4. the total number of incidents; and 5. a description of the number of individuals affected by, and the information exposed by, major incidents involving a breach of personally identifiable information. 8
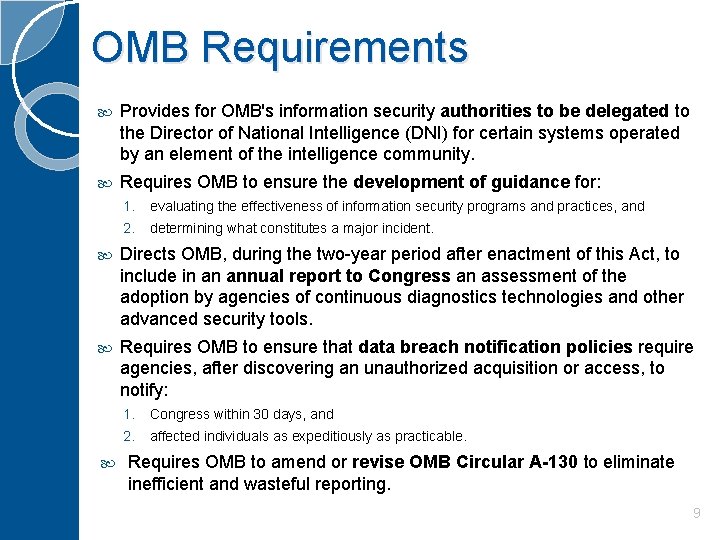
OMB Requirements Provides for OMB's information security authorities to be delegated to the Director of National Intelligence (DNI) for certain systems operated by an element of the intelligence community. Requires OMB to ensure the development of guidance for: 1. evaluating the effectiveness of information security programs and practices, and 2. determining what constitutes a major incident. Directs OMB, during the two-year period after enactment of this Act, to include in an annual report to Congress an assessment of the adoption by agencies of continuous diagnostics technologies and other advanced security tools. Requires OMB to ensure that data breach notification policies require agencies, after discovering an unauthorized acquisition or access, to notify: 1. Congress within 30 days, and 2. affected individuals as expeditiously as practicable. Requires OMB to amend or revise OMB Circular A-130 to eliminate inefficient and wasteful reporting. 9
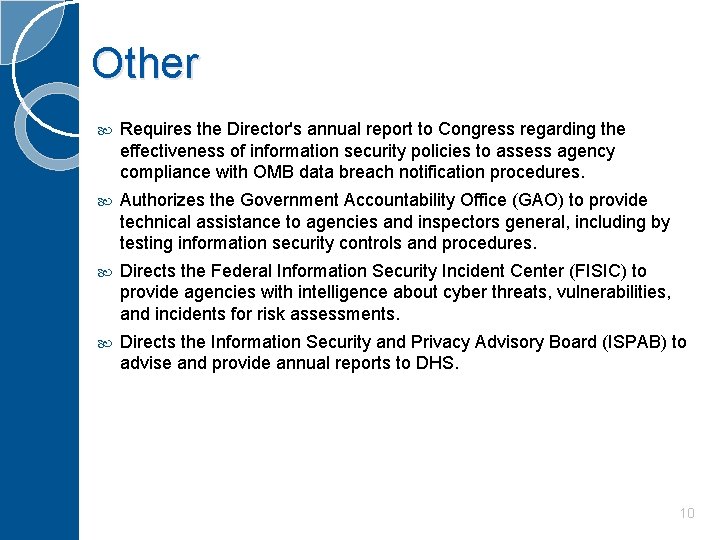
Other Requires the Director's annual report to Congress regarding the effectiveness of information security policies to assess agency compliance with OMB data breach notification procedures. Authorizes the Government Accountability Office (GAO) to provide technical assistance to agencies and inspectors general, including by testing information security controls and procedures. Directs the Federal Information Security Incident Center (FISIC) to provide agencies with intelligence about cyber threats, vulnerabilities, and incidents for risk assessments. Directs the Information Security and Privacy Advisory Board (ISPAB) to advise and provide annual reports to DHS. 10
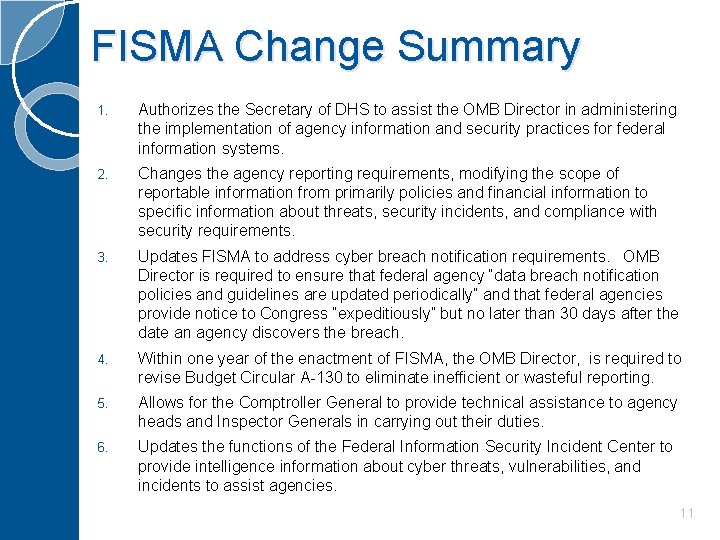
FISMA Change Summary 1. Authorizes the Secretary of DHS to assist the OMB Director in administering the implementation of agency information and security practices for federal information systems. 2. Changes the agency reporting requirements, modifying the scope of reportable information from primarily policies and financial information to specific information about threats, security incidents, and compliance with security requirements. 3. Updates FISMA to address cyber breach notification requirements. OMB Director is required to ensure that federal agency “data breach notification policies and guidelines are updated periodically” and that federal agencies provide notice to Congress “expeditiously” but no later than 30 days after the date an agency discovers the breach. 4. Within one year of the enactment of FISMA, the OMB Director, is required to revise Budget Circular A-130 to eliminate inefficient or wasteful reporting. 5. Allows for the Comptroller General to provide technical assistance to agency heads and Inspector Generals in carrying out their duties. 6. Updates the functions of the Federal Information Security Incident Center to provide intelligence information about cyber threats, vulnerabilities, and incidents to assist agencies. 11
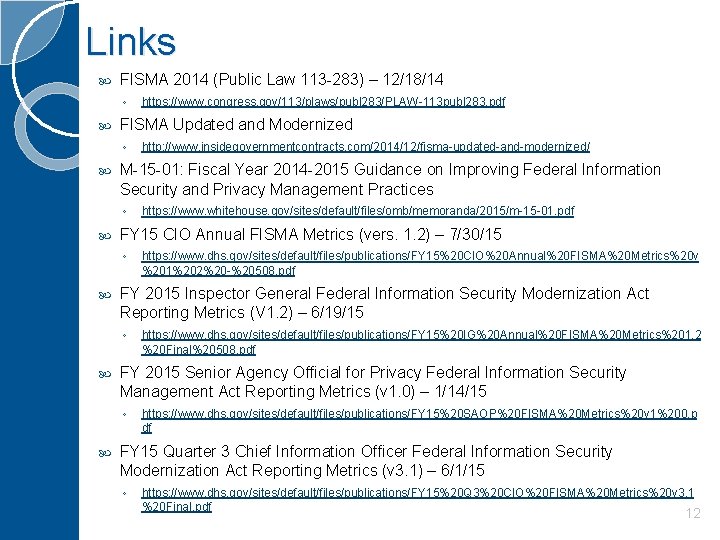
Links FISMA 2014 (Public Law 113 -283) – 12/18/14 ◦ FISMA Updated and Modernized ◦ https: //www. dhs. gov/sites/default/files/publications/FY 15%20 IG%20 Annual%20 FISMA%20 Metrics%201. 2 %20 Final%20508. pdf FY 2015 Senior Agency Official for Privacy Federal Information Security Management Act Reporting Metrics (v 1. 0) – 1/14/15 ◦ https: //www. dhs. gov/sites/default/files/publications/FY 15%20 CIO%20 Annual%20 FISMA%20 Metrics%20 v %201%202%20 -%20508. pdf FY 2015 Inspector General Federal Information Security Modernization Act Reporting Metrics (V 1. 2) – 6/19/15 ◦ https: //www. whitehouse. gov/sites/default/files/omb/memoranda/2015/m-15 -01. pdf FY 15 CIO Annual FISMA Metrics (vers. 1. 2) – 7/30/15 ◦ http: //www. insidegovernmentcontracts. com/2014/12/fisma-updated-and-modernized/ M-15 -01: Fiscal Year 2014 -2015 Guidance on Improving Federal Information Security and Privacy Management Practices ◦ https: //www. congress. gov/113/plaws/publ 283/PLAW-113 publ 283. pdf https: //www. dhs. gov/sites/default/files/publications/FY 15%20 SAOP%20 FISMA%20 Metrics%20 v 1%200. p df FY 15 Quarter 3 Chief Information Officer Federal Information Security Modernization Act Reporting Metrics (v 3. 1) – 6/1/15 ◦ https: //www. dhs. gov/sites/default/files/publications/FY 15%20 Q 3%20 CIO%20 FISMA%20 Metrics%20 v 3. 1 %20 Final. pdf 12
OMB CIRCULAR A-130* Management of Federal Information Resources Appendix I, Federal Agency Responsibilities for Maintaining Records About Individuals Appendix II, Implementation of the Government Paperwork Elimination Act Appendix III, Security of Federal Automated Information Resources Appendix IV, Analysis of Key Sections *https: //www. whitehouse. gov/omb/circulars_a 130 13
Background �Overarching policy for Federal Information Resources Management to include security and privacy. �Last revision was November 2000. �FISMA 2014 requires OMB to amend or revise A-130 to eliminate inefficient and wasteful reporting. �Existing content does not reflect current statute, Executive Orders, Presidential Directives, government-wide policies, standards and practices. 14
Authorities � Requires that oversight of Federal computer security activities be more closely linked to the oversight established pursuant to the Federal Manager's Financial Integrity Act (FMFIA), P. L. 97 -255. If computer security does not meet established thresholds, it will be identified as a material weakness in the FMFIA report. � Incorporates CIO authorities recently established with the passage of the Federal IT Acquisition Reform Act (FITARA). � Requires Federal agencies to identify and provide security protection consistent with the Computer Security Act of 1987 (40 U. S. C. 759 note). � Government-wide security responsibilities are to be consistent with the Paperwork Reduction Act of 1995. 15
Common Baseline � Each agency shall take the following actions to implement the Common Baseline: ◦ ◦ Complete agency self-assessment and plan Submit to OMB for acceptance of plan Support ongoing oversight of plan and common baseline Conduct annual review and update to self-assessment � Additional actions to be taken to support implementation of the common baseline: ◦ Federal CIO Council shall develop and share on-going support and tools ◦ Support President’s Management Council (PMC) followup 16
Policy � Provides general policy for the planning, budgeting, governance, acquisition, and management of federal information resources, taking into account the new statutory requirements and enhanced technological capabilities that have developed over the past 15 years. � Centralizes a wide range of policy updates that have come down on acquisitions, cybersecurity, information governance, records management, open data and privacy -- either administratively or in recent legislation. � The new policy replaces a federated procurement approach, which supported the "timely acquisition" of IT, with more-directed guidance to award contracts within 180 days after a solicitation goes out, and a declaration that IT should be delivered within 18 months. � Establishes general policy for the acquisition and management of information technology personnel, equipment, funds, and other resources. � Discusses policy on protecting Federal information resources. 17
Overview (1) Intended to guide agencies in securing government information resources as they increasingly rely on an open and interconnected National Information Infrastructure. � A-130 goes into detail on how IT should be managed, budgeted and bought, and contains provisions on how to protect and safeguard the privacy associated with personally identifiable information. � It stresses management controls: � ◦ Individual responsibility ◦ Awareness and training ◦ Accountability Explains how management controls can be supported by technical controls. � Requires agencies to assure that: � ◦ Risk-based rules of behavior are established ◦ Employees are trained in them ◦ Rules are enforced. 18
Overview (2) � Data. Covers the new focus on data, mandating that government data that is public facing be accessible, discoverable and of usable quality. � System authorization. ◦ States that systems will need to be reauthorized if changes occur in a number of different areas, including new threats and vulnerabilities, new business functions or new statutes from NIST or OMB, among others. ◦ Pushes for moving security checks from a static, pointin-time authorization process to a dynamic, near realtime ongoing process. � Electronic transactions. Provides guidance on use of electronic transactions and related electronic documentation statutes. 19
Overview (3) � Goals. Integrates security into program and mission goals. � System Security Plan (SSP). Reduces the centralized reporting of security plans. � Risk. Emphasizes the management of risk rather than its measurement. � Strategic Planning. Requires an information security plan to be part of each agency's strategic information technology (IT) plan. � Awareness and training. Requires that awareness and training of employees and contractors � Contingency Planning. Requires agencies improve planning for contingencies. � Emergency Response. Requires that agencies establish computer emergency response teams and employ formal emergency response capabilities. 20
Privacy � Fed. RAMP. Gives agency privacy offices separate and independent authority over the Federal Risk and Authorization Management Program, or Fed. RAMP, the government's standard approach to cloud security assessment and authorization. � Authorization authority. Creates a parallel authorization authority and gives privacy officers the ability to deny authorizations. Privacy officer approval would be separate from the current security assessment process and could force the final authorization request to be taken to the agency head. � Allows for the separation of security and privacy control plans. [The plans can be contained in the same plan or in separate plans. ] � SAOP. Agencies are instructed to designate a “Senior Agency Official for Privacy" (SAOP) to make sure that the laws and policies governing personally identifiable information stored on federal systems are maintained. 21
Responsibilities Delineates the responsibilities of OMB, the Department of Homeland Security (DHS) and National Institute of Standards and Technology (NIST) when it comes to securing federal systems, and requires continuous diagnostics and mitigation to be part of the government's defensive arsenal. OMB is tasked to develop and oversee the implementation of policies, principles, standards and guidelines on security. Includes a discussion of agency responsibilities for managing Personally Identifiable Information (PII). 22
SAOP Responsibilities � The SAOP has overall responsibility and accountability for implementing privacy protections and ensuring that all privacy requirements are met. � Accordingly, the SAOP is responsible for: ◦ Developing and implementing a privacy continuous monitoring strategy ◦ Reviewing and approving the categorization of information systems ◦ Designating privacy controls ◦ Reviewing and approving the privacy plan ◦ Conducting privacy control assessments ◦ Reviewing authorization packages for information systems. 23
CIO Responsibilities � IT Portfolio. It requires CIOs to present an "IT Portfolio" with "appropriate estimates of all IT resources included in the budget request, " in lieu of the Exhibit 53 format CIOs had previously used to sync IT projects with budget dollars. � Acquisitions. The proposal nudges CIOs to speed acquisition, with guidance to award contracts within 180 days of solicitation and a delivery date no later than 18 months. � Old technology. Tells CIOs to revisit old technology that it can no longer protect or secure and prioritize those systems for "upgrade, replacement or retirement. " It also puts CIOs on notice that the buck stops with them when it comes to obsolete technology. Under the new policy, CIOs must be "made aware of information systems and components that cannot be appropriately protected or secured and that such systems are given a high priority for upgrade, replacement, or retirement. " 24
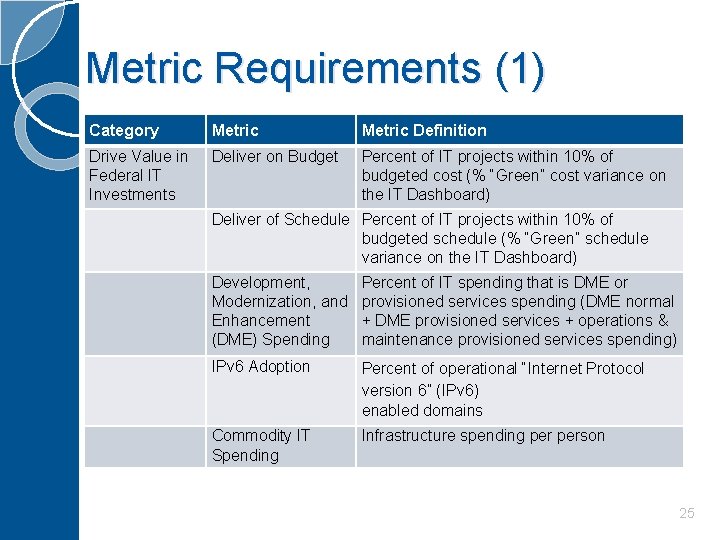
Metric Requirements (1) Category Metric Definition Drive Value in Federal IT Investments Deliver on Budget Percent of IT projects within 10% of budgeted cost (% “Green” cost variance on the IT Dashboard) Deliver of Schedule Percent of IT projects within 10% of budgeted schedule (% “Green” schedule variance on the IT Dashboard) Development, Modernization, and Enhancement (DME) Spending Percent of IT spending that is DME or provisioned services spending (DME normal + DME provisioned services + operations & maintenance provisioned services spending) IPv 6 Adoption Percent of operational “Internet Protocol version 6” (IPv 6) enabled domains Commodity IT Spending Infrastructure spending person 25
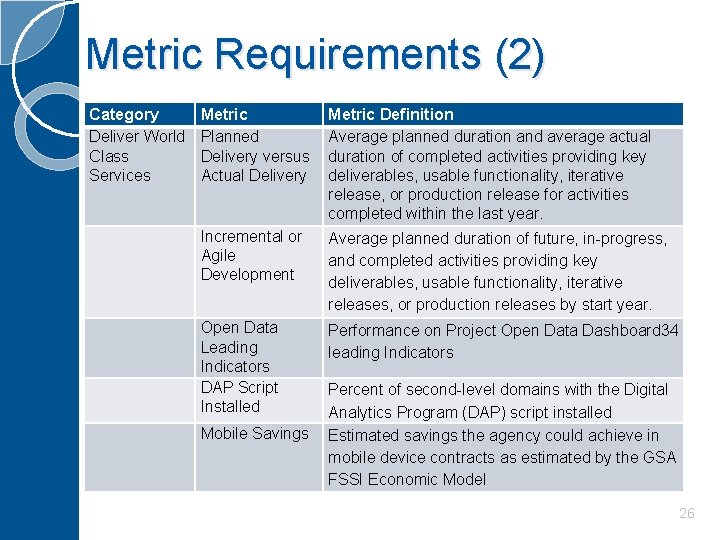
Metric Requirements (2) Category Deliver World Class Services Metric Planned Delivery versus Actual Delivery Metric Definition Average planned duration and average actual duration of completed activities providing key deliverables, usable functionality, iterative release, or production release for activities completed within the last year. Incremental or Agile Development Average planned duration of future, in-progress, and completed activities providing key deliverables, usable functionality, iterative releases, or production releases by start year. Open Data Leading Indicators DAP Script Installed Performance on Project Open Data Dashboard 34 leading Indicators Mobile Savings Percent of second-level domains with the Digital Analytics Program (DAP) script installed Estimated savings the agency could achieve in mobile device contracts as estimated by the GSA FSSI Economic Model 26
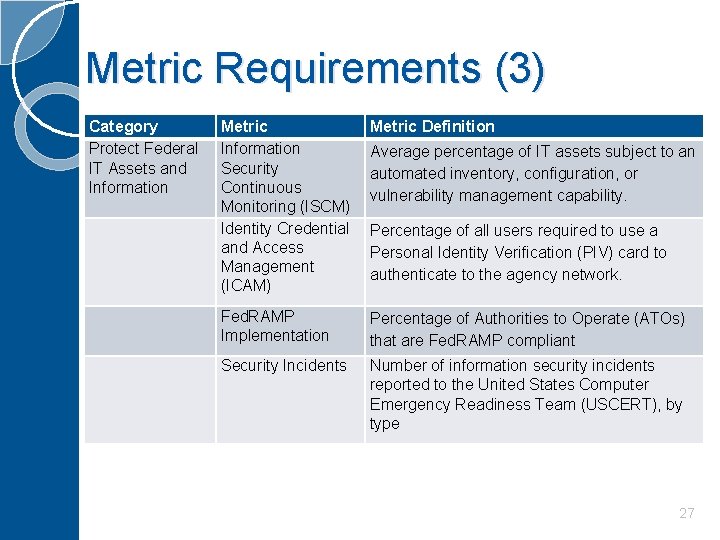
Metric Requirements (3) Category Protect Federal IT Assets and Information Metric Information Security Continuous Monitoring (ISCM) Identity Credential and Access Management (ICAM) Metric Definition Fed. RAMP Implementation Percentage of Authorities to Operate (ATOs) that are Fed. RAMP compliant Security Incidents Number of information security incidents reported to the United States Computer Emergency Readiness Team (USCERT), by type Average percentage of IT assets subject to an automated inventory, configuration, or vulnerability management capability. Percentage of all users required to use a Personal Identity Verification (PIV) card to authenticate to the agency network. 27
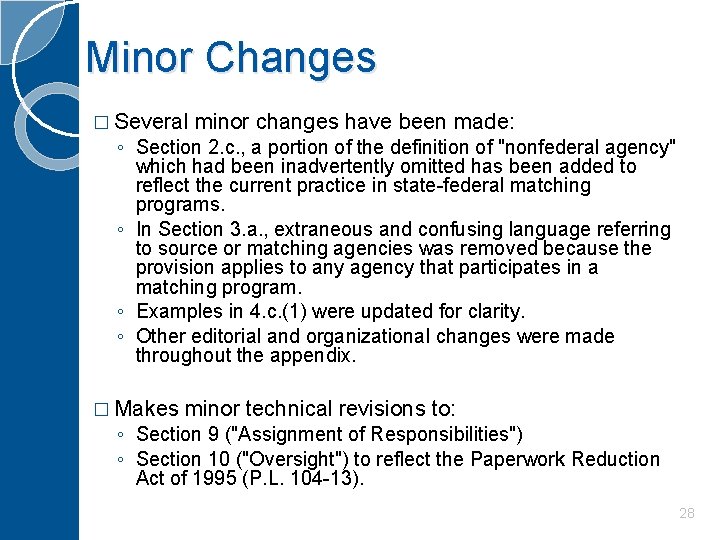
Minor Changes � Several minor changes have been made: ◦ Section 2. c. , a portion of the definition of "nonfederal agency" which had been inadvertently omitted has been added to reflect the current practice in state-federal matching programs. ◦ In Section 3. a. , extraneous and confusing language referring to source or matching agencies was removed because the provision applies to any agency that participates in a matching program. ◦ Examples in 4. c. (1) were updated for clarity. ◦ Other editorial and organizational changes were made throughout the appendix. � Makes minor technical revisions to: ◦ Section 9 ("Assignment of Responsibilities") ◦ Section 10 ("Oversight") to reflect the Paperwork Reduction Act of 1995 (P. L. 104 -13). 28
OMB A-130 Appendices Federal Agency Responsibilities for Maintaining Records About Individuals II. Implementation of the Government Paperwork Elimination Act* III. Security of Federal Automated Information Resources IV. Analysis of Key Sections I. *No Changes 29
Appendices I & IV � Appendix I (Federal Agency Responsibilities for Maintaining Records About Individuals) ◦ In Section 3. a. changes the annual requirement to review recordkeeping practices, training, violations, and notices to a biennial review, in accordance with other regular agency reviews not required by statute. � Appendix IV (Analysis of Key Sections) ◦ Includes material from OMB Memorandum M-95 -22, "Implementing the Information Dissemination Provisions of the Paperwork Reduction Act of 1995" (September 29, 1995) ◦ Deletes some outdated or otherwise already implemented guidance from the discussion of Sections 9 and 10. 30
Appendix I Responsibilities for Management of Personally Identifiable Information (PII) � Provides guidance on Federal agencies’ responsibilities for protecting PII – including PII collected for statistical purposes under a pledge of confidentiality. � Describes a set of Fair Information Practice Principles (FIPPs) that Federal agencies should consult when managing information resources that involve PII. � Requires Federal agencies to implement the privacy controls in NIST Special Publication 80053, Security and Privacy Controls for Federal Information Systems and Organizations. 31
Appendix III Security of Federal Automated Information Resources � Examples of additional requirements included in the revised Appendix III focus on: ◦ Incident response, encryption ◦ Inclusion of security requirements in contracts ◦ Oversight of contractors ◦ Protecting against insider threats ◦ Protecting against supply chain risks ◦ Prohibiting unsupported software and system components ◦ Holding personnel accountable. 32
Appendix III Security of Federal Automated Information Resources � Reflects requirements from FISMA 2014, more recent OMB policies, and NIST standards and guidelines. For example: ◦ Introduces the DHS responsibilities and other requirements from new FISMA statute ◦ Incorporates requirements of the NIST Risk Management Framework (800 -37) and related publications, to include the transition from the 3 year system re-authorization requirement to a more dynamic continuous monitoring and ongoing authorization process for information systems ◦ Addresses specific safeguarding measures to reinforce the protection of Federal information and Federal information systems � Provides guidance on how agencies should take a coordinated approach to information security and privacy 33
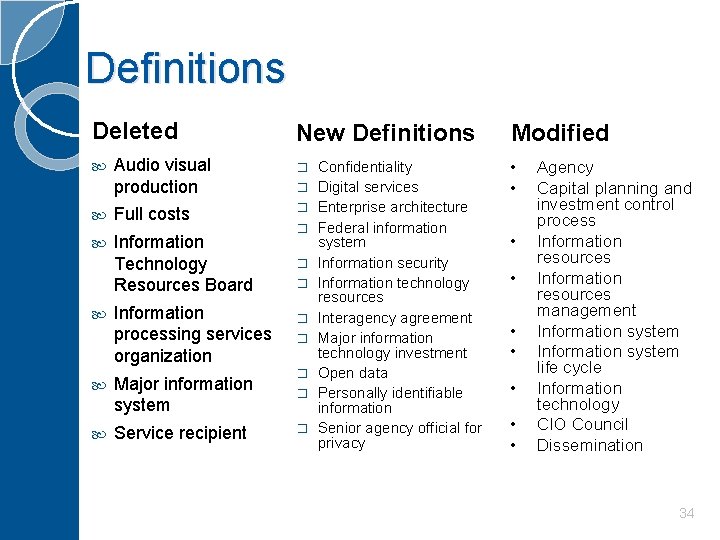
Definitions Deleted New Definitions Audio visual production � Full costs � Information Technology Resources Board Information processing services organization � � � Major information system � Service recipient � � Confidentiality Digital services Enterprise architecture Federal information system Information security Information technology resources Interagency agreement Major information technology investment Open data Personally identifiable information Senior agency official for privacy Modified • • • Agency Capital planning and investment control process Information resources management Information system life cycle Information technology CIO Council Dissemination 34
OMB CIRCULAR A-108 FEDERAL AGENCY RESPONSIBILITIES FOR REVIEW, REPORTING, AND PUBLICATION UNDER THE PRIVACY ACT 35
Federal Agency Responsibilities for Review, Reporting, and Publication under the Privacy Act Purpose: Supplement and clarify existing guidance including: ◦ OMB Circular No. A-130, Managing Information as a Strategic Resource ◦ Privacy Act Implementation: Guidelines and Responsibilities ◦ Implementation of the Privacy Act of 1974: Supplementary Guidance ◦ Final Guidance Interpreting the Provisions of Public Law 100 -503 ◦ The Computer Matching and Privacy Protection Act of 1988. Resurrects A-108 Establishes general requirements 36
Background 9/27/1975 – Privacy Act of 1974 7/1/1975 – OMB Circular A-108 9/30/1975 – OMB issued a supplement to A-108 12/12/1985 – OMB Circular A-130 issued (rescinded A-108) 2016 – OMB A-108 is resurrected 37
Table of Contents 1. 2. 3. 4. 5. 6. 7. 8. 9. Purpose Authorities Applicability Background Definitions Publishing System of Records Notices (SORNs) Reporting Systems of Records to OMB and Congress Publishing Matching Notices Reporting Matching Programs to OMB and Congress 38
Table of Contents – Cont. 10. 11. 12. 13. 14. 15. 16. 17. 18. Privacy Act Implementation Rules Privacy Act Exemption Rules Privacy Act Reviews Annual FISMA Privacy Review and Report Annual Matching Activity Review and Report Agency Website Posting Government-wide Responsibilities Effectiveness Inquiries 39
Appendices I: Summary of Key Requirements ◦ Federal Register Publication Requirements ◦ Reporting Requirements ◦ Agency Website Posting Requirements ◦ Agency Review Requirements II: Office of the Federal Register SORN Template III: Office of the Federal Register Matching Notice Template 40
6. Publishing System of Records Notices (SORNs) What to publish - template Who publishes the SORN When to publish a SORN Effective date of the SORN Rescinding a SORN Format and Style of SORN Scope of a SORN Government-wide SORNs operated by Contractors Routine uses Information collections and Privacy Act statements 41
7. Reporting Systems of Records to OMB and Congress Advance notice of a new or altered System of Records Changes to a system or records that require a report Instructions for Reporting a New or Altered System of Records Request for Expedited Review of a New or Altered System of Records Content of the Report of a New or Altered System of Records Reporting General Changes to Multiple Systems of Records 42
8. Publishing Matching Notices What to publish – template Who publishes a Matching Notice When to publish a Matching Notice Format and Style of a Matching Notice 43
9. Reporting Matching Programs to OMB and Congress Advance Notice of an Established, Re-Established, or Significantly Altered Matching Program Changes to a Matching Program that Require a Report Instructions for Reporting an Established, Re-Established, or Significantly Altered Matching Program Request for Expedited Review of an Established, Re. Established, or Significantly Altered Matching Program Content of the Report of an Established, Re-Established, or Significantly Altered Matching Program – Transmittal letter, Narrative statement, Supporting documentation 44
12. Privacy Act Reviews Systems of Records Notices Routine uses Privacy Act exemptions Contracts Social Security Numbers Recordkeeping Privacy training Violations 45
15. Agency Website Posting System of records notices Privacy impact assessments Matching notices and agreements Exemptions to the Privacy Act implementation rules Publicly available agency policies on privacy Publicly available agency reports on privacy Instructions for submitting a Privacy Act request Contact information for submitting a privacy question or complaint Identity of Senior Agency Official for Privacy 46
16. Government-wide Responsibilities Office of Management and Budget (OMB) Department of Commerce (DOC) Federal Acquisition Regulations Council (FARC) Office of Personnel Management (OPM) National Archives and Records Administration (NARA) 47
OMB MEMORANDA M-14 -03 M-14 -04 M-15 -01 M-15 -13 M-16 -04 48
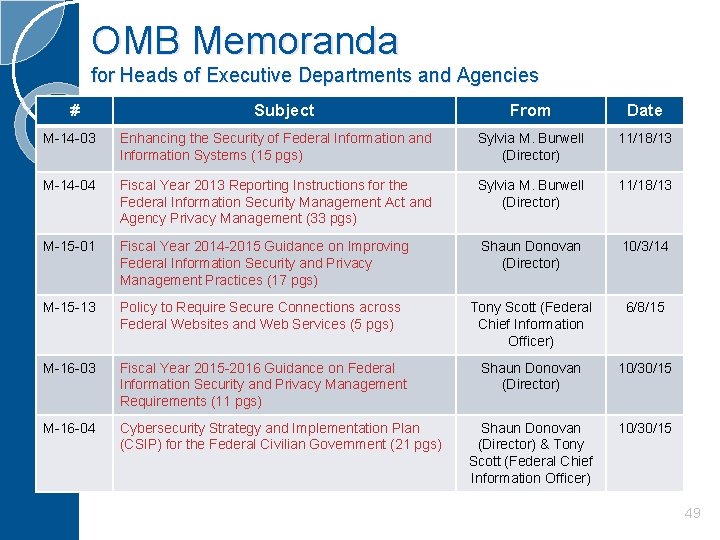
OMB Memoranda for Heads of Executive Departments and Agencies # Subject From Date M-14 -03 Enhancing the Security of Federal Information and Information Systems (15 pgs) Sylvia M. Burwell (Director) 11/18/13 M-14 -04 Fiscal Year 2013 Reporting Instructions for the Federal Information Security Management Act and Agency Privacy Management (33 pgs) Sylvia M. Burwell (Director) 11/18/13 M-15 -01 Fiscal Year 2014 -2015 Guidance on Improving Federal Information Security and Privacy Management Practices (17 pgs) Shaun Donovan (Director) 10/3/14 M-15 -13 Policy to Require Secure Connections across Federal Websites and Web Services (5 pgs) Tony Scott (Federal Chief Information Officer) 6/8/15 M-16 -03 Fiscal Year 2015 -2016 Guidance on Federal Information Security and Privacy Management Requirements (11 pgs) Shaun Donovan (Director) 10/30/15 M-16 -04 Cybersecurity Strategy and Implementation Plan (CSIP) for the Federal Civilian Government (21 pgs) Shaun Donovan (Director) & Tony Scott (Federal Chief Information Officer) 10/30/15 49
Enhancing the Security of Federal Information and Information Systems M-14 -03 To fully implement ISCM across the Government, agencies shall: 1. Develop and maintain, consistent with existing statutes, OMB policy, NIST guidelines and the CONOPS, an ISCM strategy, and establish an ISCM program that: a. b. 2. 3. Provides a clear understanding of organizational risk and helps officials set priorities and manage such risk consistently throughout the agency; and Addresses how the agency will conduct ongoing authorizations of information systems and the environments in which those systems operate, including the agency's use of common controls. Establish plans, in coordination with DHS, to implement an agency ISCM program; Standardize, to the extent practicable, the requirement to establish ISCM as an agency-wide solution, deploying enterprise ISCM products and services instead of developing multiple, disparate services across agency bureaus and components; 50
Enhancing the Security of Federal Information and Information Systems 4. 5. 6. 7. M-14 -03 Establish plans, to the extent practicable, to migrate to the GSA BPA as contract terms expire for acquisition vehicles currently used to acquire ISCM products and services. Submit specified security-related information to the Federal ISCM dashboard maintained by DHS; Evaluate and upgrade information systems and deploy new products, as needed, including agency and component ISCM dashboards, to support ISCM and the need to submit security-related information; Require that external service providers hosting Federal information meet Federal information security requirements for ISCM (i. e. , FISMA). This includes Fed. RAMP requirements for cloud computing; and Ensure adequate staff and training to meet the objectives of the ISCM program. 51
Enhancing the Security of Federal Information and Information Systems M-14 -03 In addition to the general agency responsibilities: 1. 2. 3. 4. 5. 6. OMB will continue to oversee agency information security practices, in accordance with FISMA of 2002; DHS shall work with each agency to establish an ISCM implementation program that capitalizes on the processes established in the CONOPS and leverages, to the extent practicable, the BPA; DHS, in consultation with OMB, shall establish a Federal dashboard for ISCM, which will provide a government-wide view of ISCM, as well as the technical specifications and guidance for agencies on the requirements for submitting information to this Federal dashboard; DHS, in coordination with OMB, shall monitor the implementation of agencies ISCM strategies and programs in conjunction with Portfolio. Stat (i. e. , M-12 -10, M-13 -09)* and through Cyber. Stat (i. e. , M-12 -20**); The Joint Continuous Monitoring Working Group (JCMWG), in coordination with stakeholders, shall update the CONOPS at least annually; and NIST shall issue additional guidance on conducting ongoing authorizations. *M-12 -10: Implementing Portfolio. Stat (March 30, 2012) *M-13 -09: Fiscal Year 2013 Portfolio. Stat Guidance: Strengthening Federal IT Portfolio Management (3/27/2013) **M-12 -20: FY 2012 Reporting Instructions for the Federal Information Security Management Act and Agency Privacy Management (9/27/2012) 52
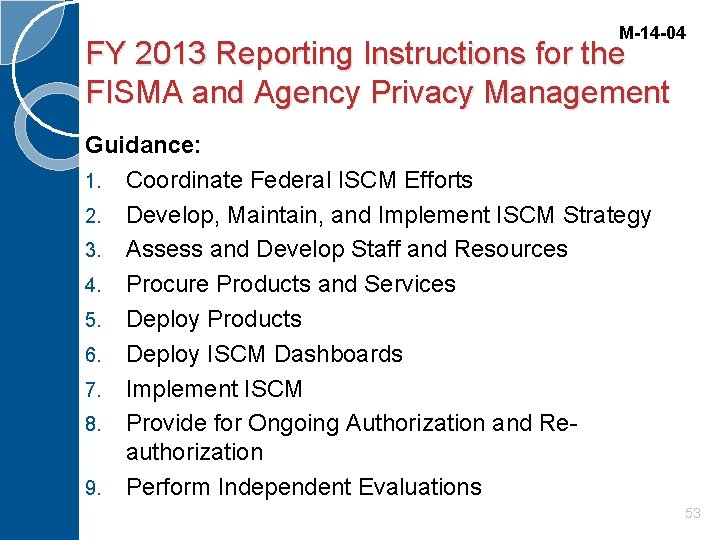
M-14 -04 FY 2013 Reporting Instructions for the FISMA and Agency Privacy Management Guidance: 1. Coordinate Federal ISCM Efforts 2. Develop, Maintain, and Implement ISCM Strategy 3. Assess and Develop Staff and Resources 4. Procure Products and Services 5. Deploy Products 6. Deploy ISCM Dashboards 7. Implement ISCM 8. Provide for Ongoing Authorization and Reauthorization 9. Perform Independent Evaluations 53
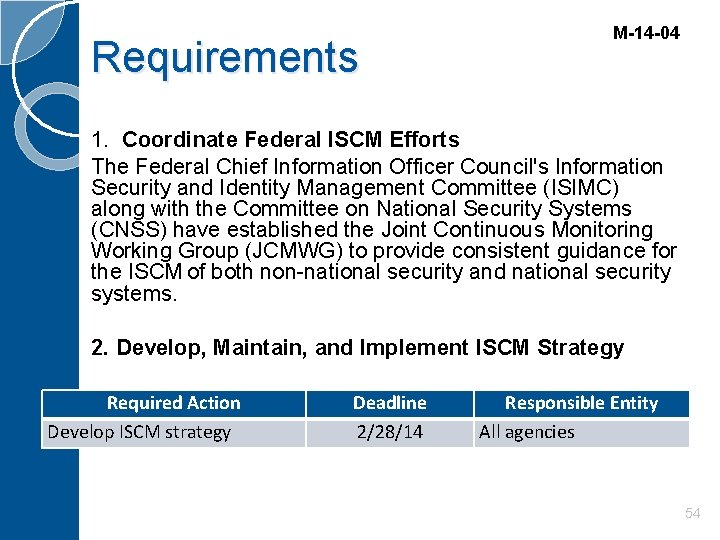
Requirements M-14 -04 1. Coordinate Federal ISCM Efforts The Federal Chief Information Officer Council's Information Security and Identity Management Committee (ISIMC) along with the Committee on National Security Systems (CNSS) have established the Joint Continuous Monitoring Working Group (JCMWG) to provide consistent guidance for the ISCM of both non-national security and national security systems. 2. Develop, Maintain, and Implement ISCM Strategy Required Action Develop ISCM strategy Deadline 2/28/14 Responsible Entity All agencies 54
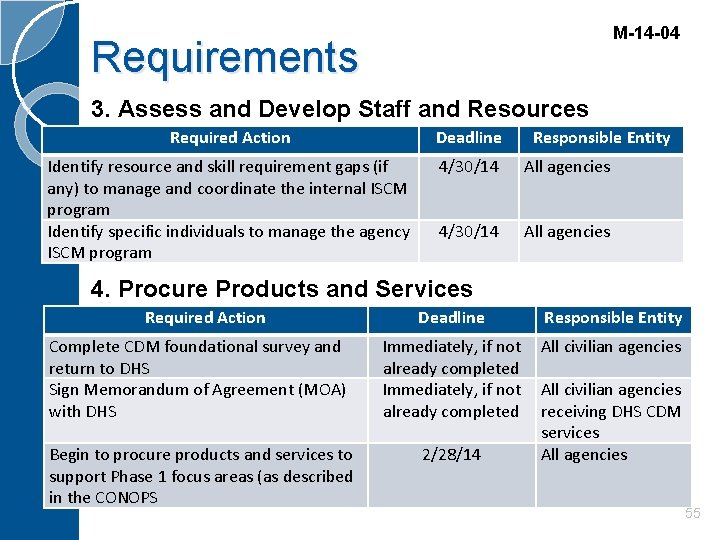
M-14 -04 Requirements 3. Assess and Develop Staff and Resources Required Action Deadline Responsible Entity Identify resource and skill requirement gaps (if any) to manage and coordinate the internal ISCM program Identify specific individuals to manage the agency ISCM program 4/30/14 All agencies 4. Procure Products and Services Required Action Deadline Responsible Entity Complete CDM foundational survey and return to DHS Sign Memorandum of Agreement (MOA) with DHS Immediately, if not already completed All civilian agencies Begin to procure products and services to support Phase 1 focus areas (as described in the CONOPS 2/28/14 All civilian agencies receiving DHS CDM services All agencies 55
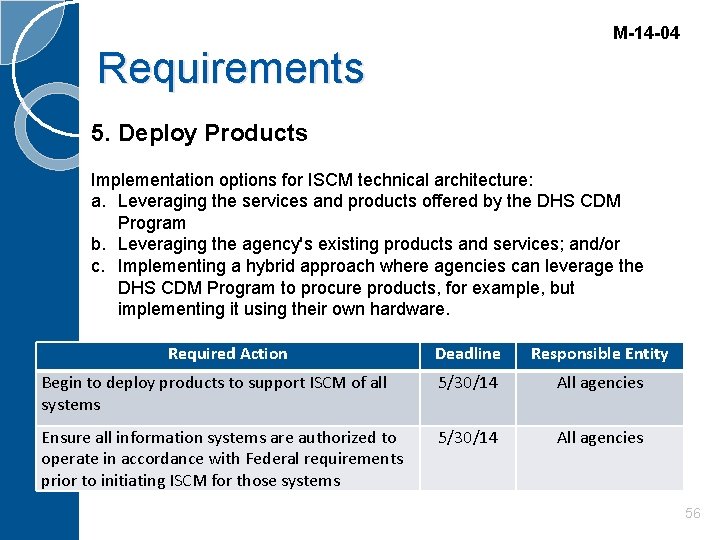
M-14 -04 Requirements 5. Deploy Products Implementation options for ISCM technical architecture: a. Leveraging the services and products offered by the DHS CDM Program b. Leveraging the agency's existing products and services; and/or c. Implementing a hybrid approach where agencies can leverage the DHS CDM Program to procure products, for example, but implementing it using their own hardware. Required Action Deadline Responsible Entity Begin to deploy products to support ISCM of all systems 5/30/14 All agencies Ensure all information systems are authorized to operate in accordance with Federal requirements prior to initiating ISCM for those systems 5/30/14 All agencies 56
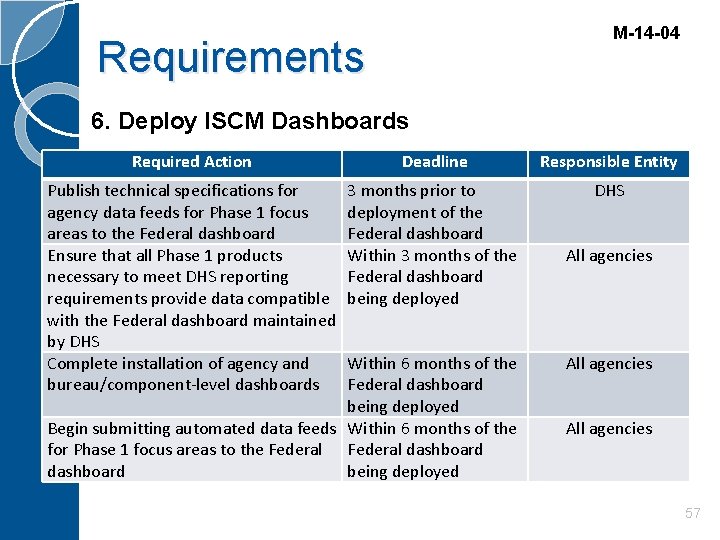
M-14 -04 Requirements 6. Deploy ISCM Dashboards Required Action Deadline Responsible Entity Publish technical specifications for agency data feeds for Phase 1 focus areas to the Federal dashboard Ensure that all Phase 1 products necessary to meet DHS reporting requirements provide data compatible with the Federal dashboard maintained by DHS Complete installation of agency and bureau/component-level dashboards 3 months prior to deployment of the Federal dashboard Within 3 months of the Federal dashboard being deployed DHS Within 6 months of the Federal dashboard being deployed Begin submitting automated data feeds Within 6 months of the for Phase 1 focus areas to the Federal dashboard being deployed All agencies 57
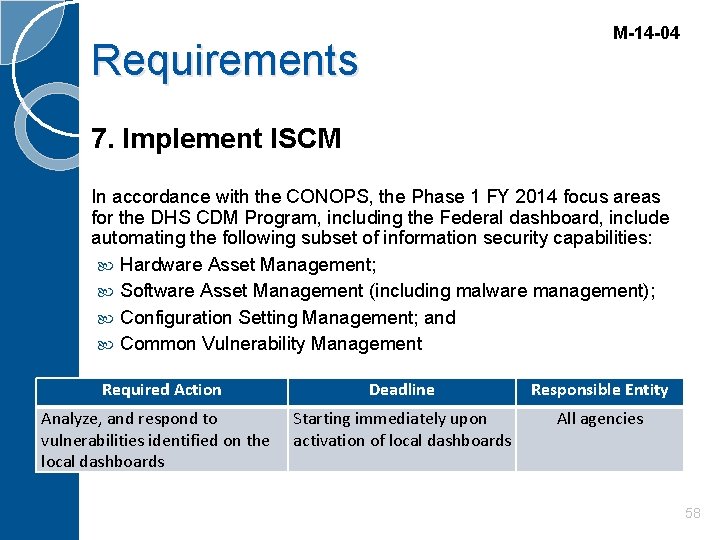
M-14 -04 Requirements 7. Implement ISCM In accordance with the CONOPS, the Phase 1 FY 2014 focus areas for the DHS CDM Program, including the Federal dashboard, include automating the following subset of information security capabilities: Hardware Asset Management; Software Asset Management (including malware management); Configuration Setting Management; and Common Vulnerability Management Required Action Analyze, and respond to vulnerabilities identified on the local dashboards Deadline Responsible Entity Starting immediately upon activation of local dashboards All agencies 58
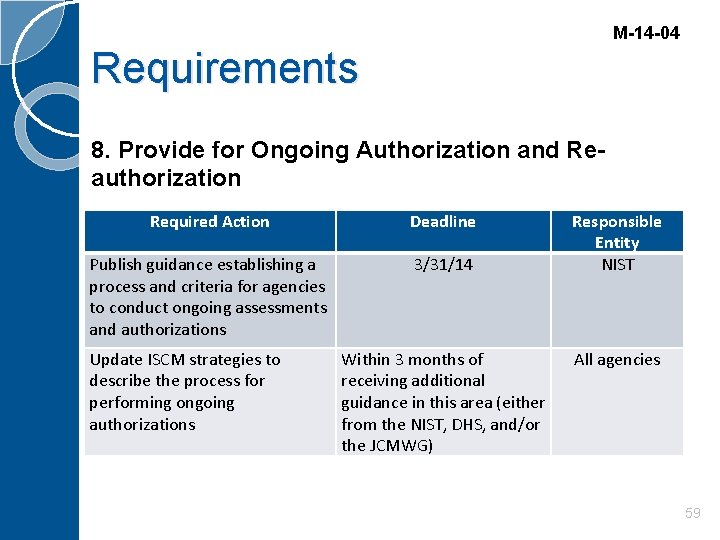
M-14 -04 Requirements 8. Provide for Ongoing Authorization and Reauthorization Required Action Deadline Publish guidance establishing a process and criteria for agencies to conduct ongoing assessments and authorizations 3/31/14 Update ISCM strategies to describe the process for performing ongoing authorizations Within 3 months of receiving additional guidance in this area (either from the NIST, DHS, and/or the JCMWG) Responsible Entity NIST All agencies 59
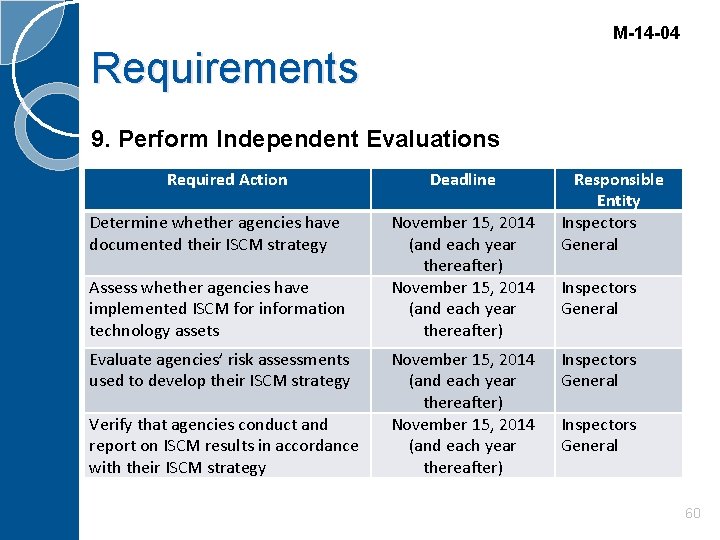
M-14 -04 Requirements 9. Perform Independent Evaluations Required Action Determine whether agencies have documented their ISCM strategy Assess whether agencies have implemented ISCM for information technology assets Evaluate agencies’ risk assessments used to develop their ISCM strategy Verify that agencies conduct and report on ISCM results in accordance with their ISCM strategy Deadline November 15, 2014 (and each year thereafter) Responsible Entity Inspectors General 60
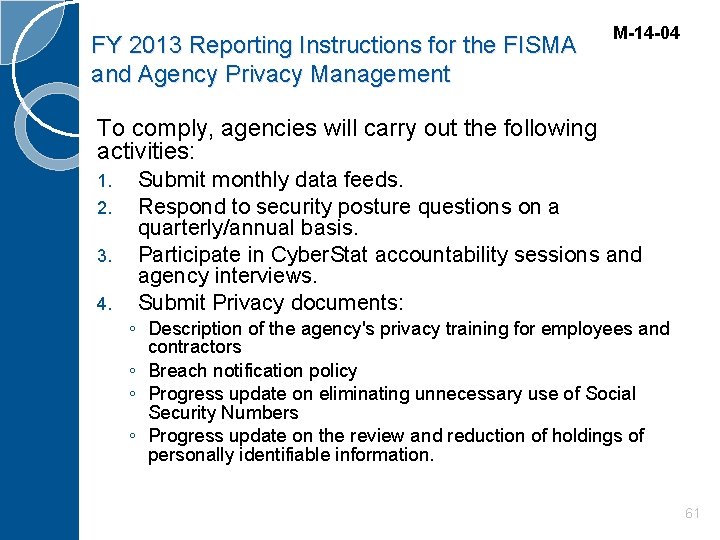
FY 2013 Reporting Instructions for the FISMA and Agency Privacy Management M-14 -04 To comply, agencies will carry out the following activities: 1. 2. 3. 4. Submit monthly data feeds. Respond to security posture questions on a quarterly/annual basis. Participate in Cyber. Stat accountability sessions and agency interviews. Submit Privacy documents: ◦ Description of the agency's privacy training for employees and contractors ◦ Breach notification policy ◦ Progress update on eliminating unnecessary use of Social Security Numbers ◦ Progress update on the review and reduction of holdings of personally identifiable information. 61
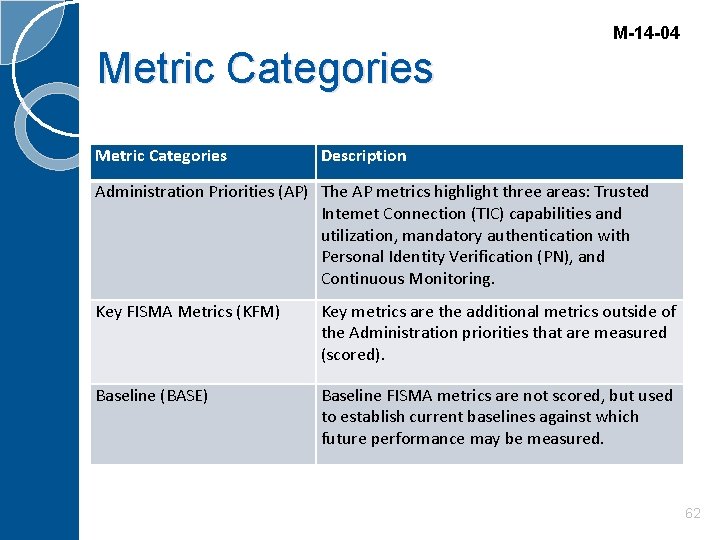
M-14 -04 Metric Categories Description Administration Priorities (AP) The AP metrics highlight three areas: Trusted Intemet Connection (TIC) capabilities and utilization, mandatory authentication with Personal Identity Verification (PN), and Continuous Monitoring. Key FISMA Metrics (KFM) Key metrics are the additional metrics outside of the Administration priorities that are measured (scored). Baseline (BASE) Baseline FISMA metrics are not scored, but used to establish current baselines against which future performance may be measured. 62
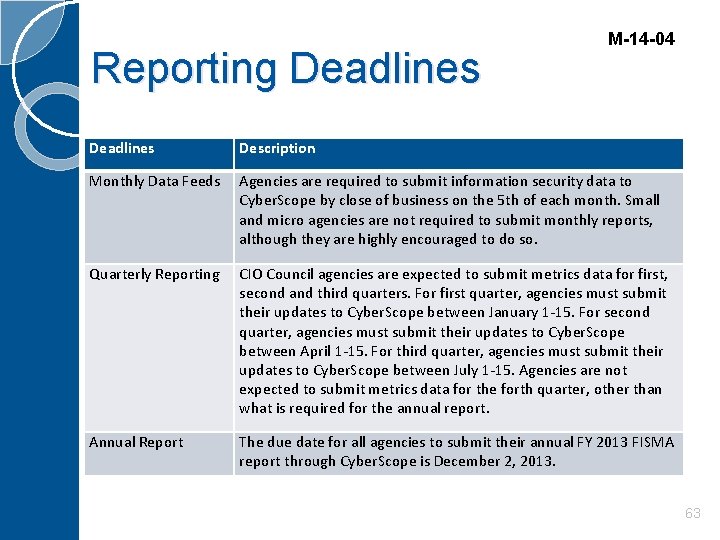
Reporting Deadlines M-14 -04 Deadlines Description Monthly Data Feeds Agencies are required to submit information security data to Cyber. Scope by close of business on the 5 th of each month. Small and micro agencies are not required to submit monthly reports, although they are highly encouraged to do so. Quarterly Reporting CIO Council agencies are expected to submit metrics data for first, second and third quarters. For first quarter, agencies must submit their updates to Cyber. Scope between January 1 -15. For second quarter, agencies must submit their updates to Cyber. Scope between April 1 -15. For third quarter, agencies must submit their updates to Cyber. Scope between July 1 -15. Agencies are not expected to submit metrics data for the forth quarter, other than what is required for the annual report. Annual Report The due date for all agencies to submit their annual FY 2013 FISMA report through Cyber. Scope is December 2, 2013. 63
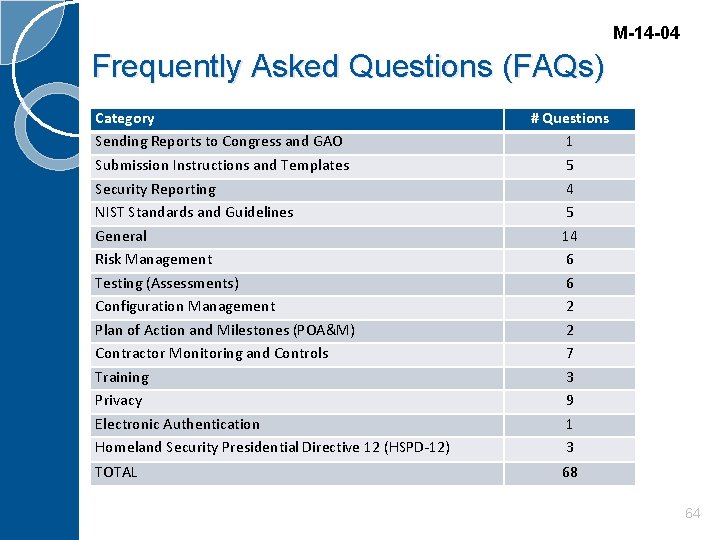
M-14 -04 Frequently Asked Questions (FAQs) Category Sending Reports to Congress and GAO Submission Instructions and Templates Security Reporting NIST Standards and Guidelines General Risk Management Testing (Assessments) Configuration Management Plan of Action and Milestones (POA&M) Contractor Monitoring and Controls Training Privacy Electronic Authentication Homeland Security Presidential Directive 12 (HSPD-12) TOTAL # Questions 1 5 4 5 14 6 6 2 2 7 3 9 1 3 68 64
M-15 -01 Fiscal Year 2014 -2015 Guidance on Improving Federal Information Security and Privacy Management Practices Key Initiatives and Policy Updates: OMB Memorandum M-14 -03 and the Continuous Diagnostics and Mitigation (CDM) Program FY 2015 FISMA Metrics FY 2015 Cybersecurity CAP Goal Formalized Process for Proactive Scans of Public Facing Agency Networks Updated DHS US-CERT Incident Notification Guidelines Section: I. Information Security Program Oversight Requirements II. Formalized Process for Proactive Scans of Public Facing Agency Networks III. FY 2014 -2015 FISMA Reporting and Privacy Management Guidance IV. Updates to FAQs on Reporting for FISMA and Agency Privacy Management 65
M-15 -01 Section I: Agency Oversight Purpose: Participate in Cyber. Stat accountability sessions and agency interviews. DHS Interview Goals: 1. Assess progress towards the Administration's cybersecurity priorities and other governance, information security risk management, and FISMA compliance issues and challenges. 2. Identify security best practices and raising awareness of FISMA reporting requirements. 3. Identify any agency-specific challenges with meeting cyber mandates and/or operational security requirements. 4. Establish meaningful dialogue with the agency 's senior leadership. 66
M-15 -01 Section II: Agency Scanning DHS Shall: 1. 2. 3. Scan internet accessible addresses and public facing segments of Federal civilian agency systems for vulnerabilities on an ongoing basis as well as in response to newly discovered vulnerabilities on an urgent basis, to include without prior agency authorization on an emergency basis where not prohibited by law; Maintain a mechanism for the reporting of Federal department and agency website and system vulnerabilities. Contracted third parties and cloud service providers, in accordance with agency and provider incident response plans (IRP) and Fed. RAMP requirements, should report vulnerabilities to the relevant agencies who should in turn report to DHS; Continue to deploy consolidated intrusion detection and prevention capabilities to protect Federal department and agency information and information systems; 67
M-15 -01 Section II: Agency Scanning DHS Shall: 4. 5. 6. 7. Develop and periodically update guidance for the reporting of cybersecurity incidents involving Federal department and agency information systems to DHS US-CERT, which serves as the Federal Information Security Incident Center as established in 44 U. S. C. § 3546; Report to OMB on the identification and mitigation of risks and vulnerabilities across Federal agency information systems; Provide Federal agencies with the agency-specific results of DHS scanning and reports on the identification risks and vulnerabilities across the department or agency's internet accessible addresses, systems and external access points; and, Offer additional risk and vulnerability assessment services upon the request of individual Federal agencies. 68
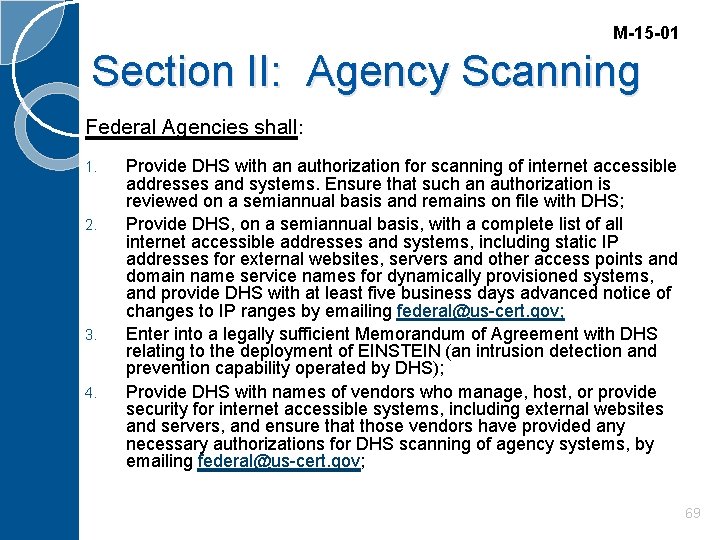
M-15 -01 Section II: Agency Scanning Federal Agencies shall: 1. 2. 3. 4. Provide DHS with an authorization for scanning of internet accessible addresses and systems. Ensure that such an authorization is reviewed on a semiannual basis and remains on file with DHS; Provide DHS, on a semiannual basis, with a complete list of all internet accessible addresses and systems, including static IP addresses for external websites, servers and other access points and domain name service names for dynamically provisioned systems, and provide DHS with at least five business days advanced notice of changes to IP ranges by emailing federal@us-cert. gov; Enter into a legally sufficient Memorandum of Agreement with DHS relating to the deployment of EINSTEIN (an intrusion detection and prevention capability operated by DHS); Provide DHS with names of vendors who manage, host, or provide security for internet accessible systems, including external websites and servers, and ensure that those vendors have provided any necessary authorizations for DHS scanning of agency systems, by emailing federal@us-cert. gov; 69
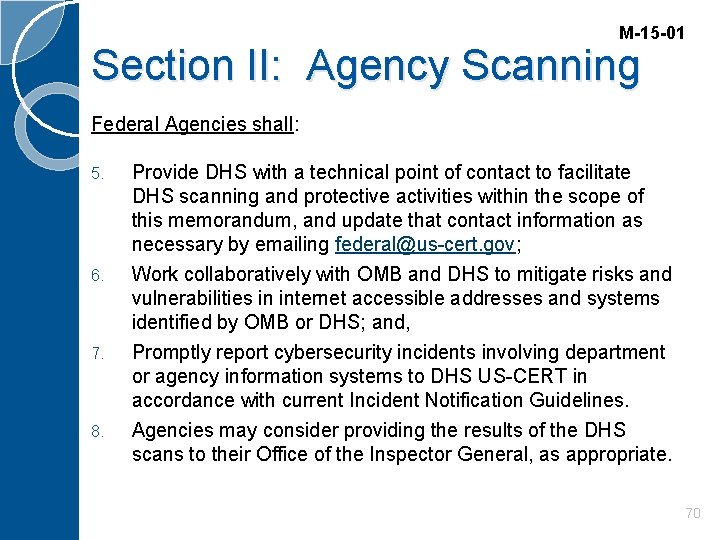
M-15 -01 Section II: Agency Scanning Federal Agencies shall: 5. 6. 7. 8. Provide DHS with a technical point of contact to facilitate DHS scanning and protective activities within the scope of this memorandum, and update that contact information as necessary by emailing federal@us-cert. gov; Work collaboratively with OMB and DHS to mitigate risks and vulnerabilities in internet accessible addresses and systems identified by OMB or DHS; and, Promptly report cybersecurity incidents involving department or agency information systems to DHS US-CERT in accordance with current Incident Notification Guidelines. Agencies may consider providing the results of the DHS scans to their Office of the Inspector General, as appropriate. 70
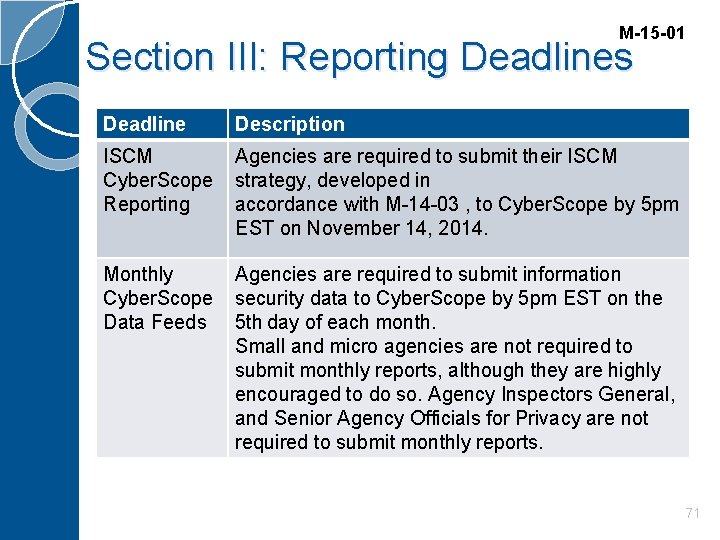
M-15 -01 Section III: Reporting Deadlines Deadline Description ISCM Agencies are required to submit their ISCM Cyber. Scope strategy, developed in Reporting accordance with M-14 -03 , to Cyber. Scope by 5 pm EST on November 14, 2014. Monthly Agencies are required to submit information Cyber. Scope security data to Cyber. Scope by 5 pm EST on the Data Feeds 5 th day of each month. Small and micro agencies are not required to submit monthly reports, although they are highly encouraged to do so. Agency Inspectors General, and Senior Agency Officials for Privacy are not required to submit monthly reports. 71
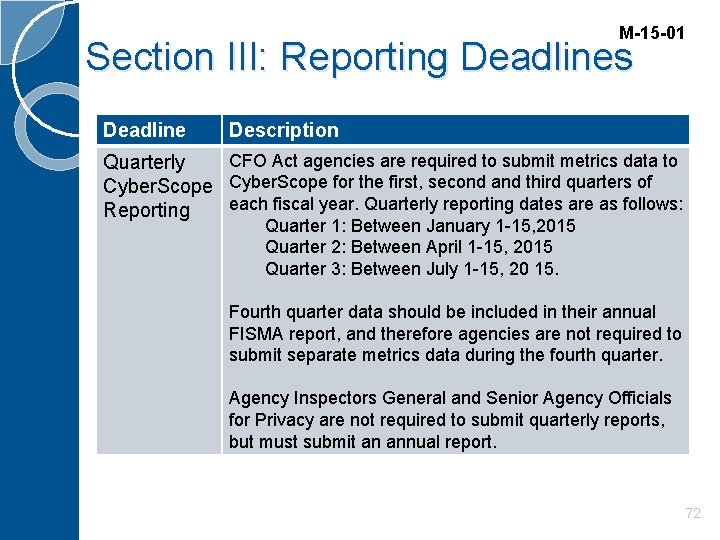
M-15 -01 Section III: Reporting Deadlines Deadline Description CFO Act agencies are required to submit metrics data to Quarterly Cyber. Scope for the first, second and third quarters of each fiscal year. Quarterly reporting dates are as follows: Reporting Quarter 1: Between January 1 -15, 2015 Quarter 2: Between April 1 -15, 2015 Quarter 3: Between July 1 -15, 20 15. Fourth quarter data should be included in their annual FISMA report, and therefore agencies are not required to submit separate metrics data during the fourth quarter. Agency Inspectors General and Senior Agency Officials for Privacy are not required to submit quarterly reports, but must submit an annual report. 72
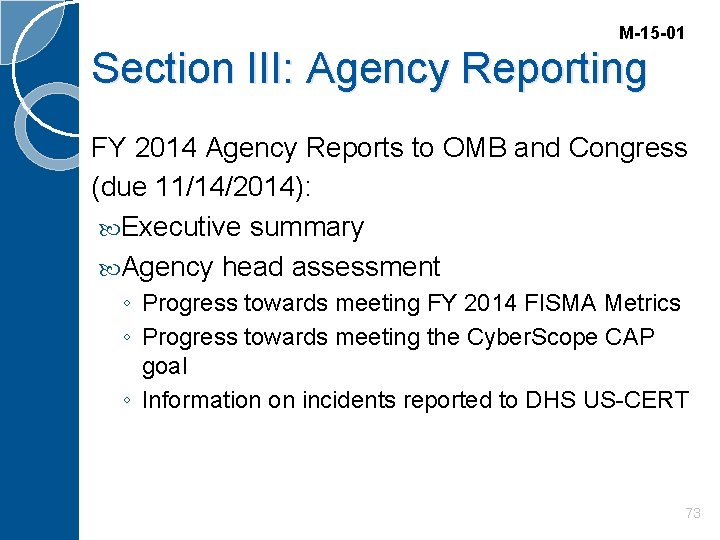
M-15 -01 Section III: Agency Reporting FY 2014 Agency Reports to OMB and Congress (due 11/14/2014): Executive summary Agency head assessment ◦ Progress towards meeting FY 2014 FISMA Metrics ◦ Progress towards meeting the Cyber. Scope CAP goal ◦ Information on incidents reported to DHS US-CERT 73
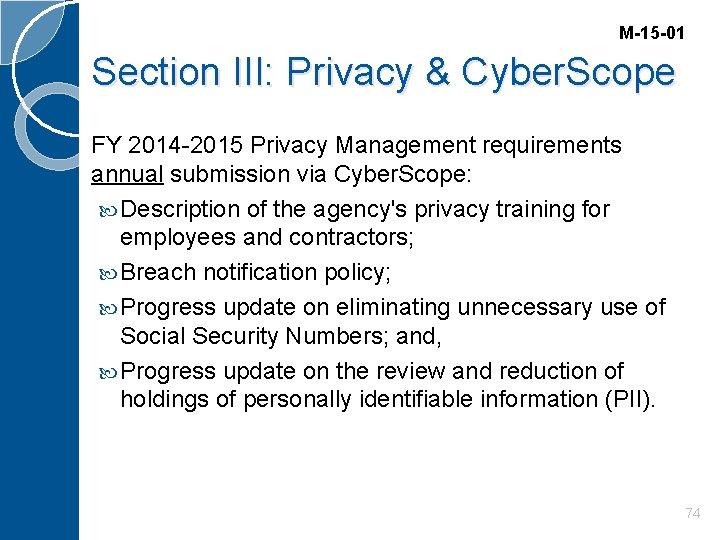
M-15 -01 Section III: Privacy & Cyber. Scope FY 2014 -2015 Privacy Management requirements annual submission via Cyber. Scope: Description of the agency's privacy training for employees and contractors; Breach notification policy; Progress update on eliminating unnecessary use of Social Security Numbers; and, Progress update on the review and reduction of holdings of personally identifiable information (PII). 74
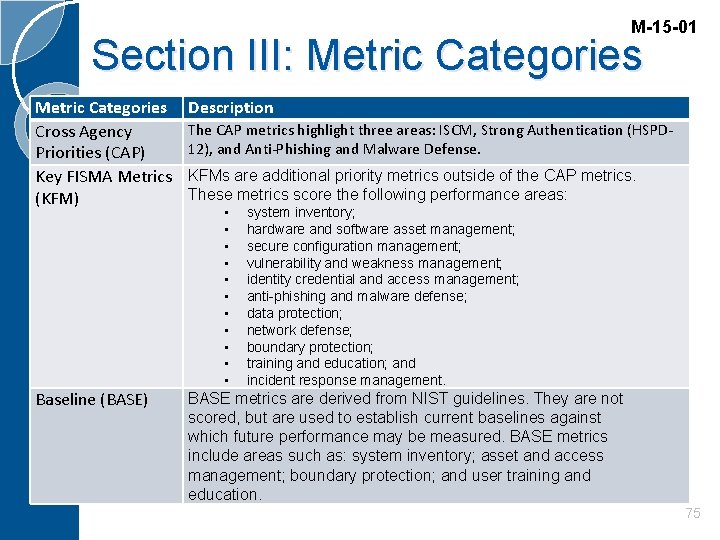
M-15 -01 Section III: Metric Categories Cross Agency Priorities (CAP) Key FISMA Metrics (KFM) Description Baseline (BASE) BASE metrics are derived from NIST guidelines. They are not scored, but are used to establish current baselines against which future performance may be measured. BASE metrics include areas such as: system inventory; asset and access management; boundary protection; and user training and education. The CAP metrics highlight three areas: ISCM, Strong Authentication (HSPD 12), and Anti-Phishing and Malware Defense. KFMs are additional priority metrics outside of the CAP metrics. These metrics score the following performance areas: • • • system inventory; hardware and software asset management; secure configuration management; vulnerability and weakness management; identity credential and access management; anti-phishing and malware defense; data protection; network defense; boundary protection; training and education; and incident response management. 75
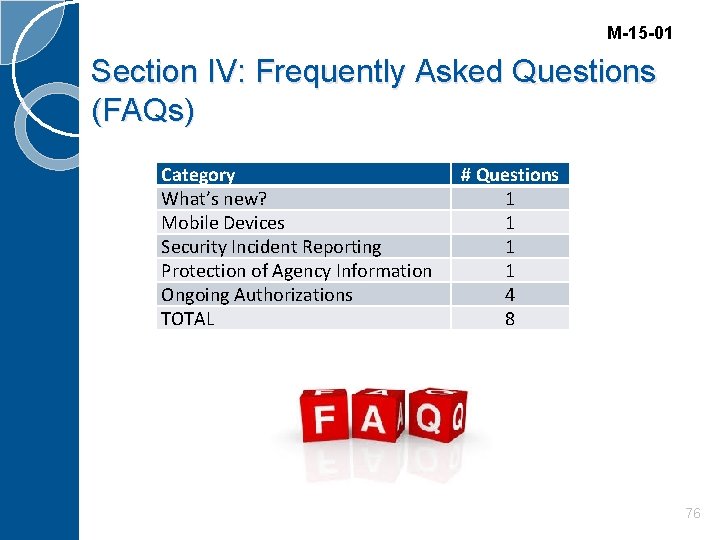
M-15 -01 Section IV: Frequently Asked Questions (FAQs) Category What’s new? Mobile Devices Security Incident Reporting Protection of Agency Information Ongoing Authorizations TOTAL # Questions 1 1 4 8 76
M-15 -13 Policy to Require Secure Connections across Federal Websites and Web Services Requires that all publicly accessible Federal websites and web services only provide service through a secure connection Expands on M-05 -04* and relates to M-08 -23** Explains what HTTPS Does and Doesn’t Do Discusses Challenges and Considerations Contains HTTPS Guidelines *M-05 -04: Policies for Federal Agency Websites - https: //www. whitehouse. gov/sites/default/files/omb/memoranda/fv 2005/m 05 -04. pdf **M-08 -23: Securing the Federal Government's Domain Name System Infrastructure - https: //www. whitehouse. gov/sites/default/files/omb/assets/omb/memoranda/fy 2008/m 08 -23. pdf 77
M-15 -13 Challenges and Considerations Site Performance – May improve in some major browsers Server Name Indication - Some legacy clients may not support new technology Mixed Content - Ensure that all external resources (images, scripts, fonts, iframes, etc. ) are also loaded over a secure connection. APIs and Services – Non-browser clients (e. g. , web APIs) may not be able to configure to HTTPS Planning for Change (e. g. , Updates to certificates, cipher choices, protocol versions, and other configuration elements) Strict Transport Security – Enable HTTP Strict Transport Security (HSTS) Domain Name System Security (DNSEC) – Does not rescind M-08 -23* *M-08 -23: Securing the Federal Government's Domain Name System Infrastructure 78
HTTPS Guidelines M-15 -13 Newly developed websites and services at all Federal agency domains or subdomains must adhere to this policy upon launch. For existing websites and services, agencies should prioritize deployment using a risk-based analysis. Web services that involve an exchange of personally identifiable information (PII), where the content is unambiguously sensitive in nature, or where the content receives a high-level of traffic should receive priority and migrate as soon as possible. Agencies must make all existing websites and services accessible through a secure connection (HTTPS-only, with HSTS) by December 31, 2016. The use of HTTPS is encouraged on intranets, but not explicitly required. 79
Fiscal Year 2015 -2016 Guidance on Federal Information Security and Privacy Management Requirements M-16 -03 Section I: Information Security and Privacy Program Oversight and Reporting Requirements Provides Federal agencies with timelines and requirements for quarterly and annual reporting; Establishes detailed instructions for preparing the annual agency FISMA reports, which must be submitted to DHS through Cyber. Scope no later than November 13, 2015; and Provides the definition of a "Major Incident”. Section II: Improved Cybersecurity Preparedness and Coordination Updates procedures to ensure greater consistency in agency response practices, by: ◦ Requiring that agencies formally address the need for sensitive positions; ◦ Formalizing the process by which agencies can request and receive on-site, technical assistance from DHS; ◦ Providing agencies with best practices based upon lessons learned from major cybersecurity incidents 80
M-16 -03 Implementation of the Cybersecurity Sprint Immediately deploy indicators provided by DHS regarding priority threat-actor Techniques, Tactics, and Procedures (TTPs) to scan systems and check logs; Patch critical vulnerabilities without delay; Tighten policies and practices for privileged users; Dramatically accelerate implementation of strong authentication, especially for privileged users; and Immediately identify agency specific High Value Assets (HVAs) and assess the security protections around those HVAs. 81
M-16 -03 Agency Letter to OMB & Congress A description of each major incident including: 1. 2. 3. 4. Threats and threat actors, vulnerabilities, and impacts; Risk assessments conducted on the system before the incident; The status of compliance of the affected information system with security requirements at the time of the incident; and The detection, response, and remediation actions the agency has completed. For each major incident that involved a breach of PII, the description must also include: 1. 2. The number of individuals whose information was affected by the major incident; and A description of the information that was breached or exposed. The total number of cyber incidents, including a description of system impact levels, types of incident, and locations of affected systems. Progress towards meeting FY 2015 FISMA Metrics Progress toward meeting the Cybersecurity Cross Agency Priority (CAP) goal 82
M-16 -03 Reporting Requirements and Deadlines FY 2015 Annual FISMA Reporting Deadline All agencies will update the Annual FY 2015 FISMA metrics by November 13, 2015. Agency reports are due to Congress by March 1, 2016 FY 2016 FISMA Reporting Timelines Quarter 1: no later than January 15, 2016 Quarter 2: no later than April 15, 2016 Quarter 3: no later than July 15, 2016 Quarter 4 / FY 2016 Annual: TBD 83
FY 2015 -2016 Privacy Management Requirements (Annual Submission) M-16 -03 Description of the agency’s privacy training for employees and contractors; Copy of the agency’s breach notification policy; Progress update on reducing the holdings of personally identifiable information (PII), including eliminating unnecessary use of Social Security numbers; and A memorandum describing the agency’s privacy program, including: ◦ A description of the structure of the agency’s privacy program, including the role of the Senior Agency Official for Privacy and the resources that the agency has dedicated to privacy-related functions; ◦ An assessment of whether the Senior Agency Official for Privacy has the necessary authority, independence, access to agency leadership, subject matter expertise, and resources to effectively manage and oversee all privacy-related functions across the agency; and ◦ Any other information OMB should know about how privacy-related functions are performed at the agency. 84
M-16 -03 Definition of Major Incident Involves information that is Classified, Controlled Unclassified Information (CUI) proprietary, CUI Privacy, or CUI Other; Is not recoverable, not recoverable within a specified amount of time, or is recoverable only with supplemental resources; and Has a high or medium functional impact to the mission of an agency; Or Involves the exfiltration, modification, deletion or unauthorized access or lack of availability to information or systems within certain parameters to include either: ◦ A specific threshold of number of records or users affected; or ◦ Any record of special importance. 85
Agencies to provide DHS by November 13, 2015 M-16 -03 A standing Federal Network Authorization. Ensure that such an authorization is reviewed on a semiannual basis and remains on file with DHS and will be activated by an email from the victim agency to DHS at the time of an incident; A technical point of contact, to be updated as necessary, to facilitate DHS scanning and protective activities within the scope of this memorandum 86
Agencies to Improve Coordination with DHS M-16 -03 Designate a principal Security Operations Center (SOC) and reporting this to DHS US-CERT by emailing soc@us-cert. gov by November 13, 2015. Begin reporting their high value assets as first identified in the Cybersecurity Sprint to DHS for ongoing assessment. Continue to provide all public facing IP addresses to the DHS National Cybersecurity Assessment and Technical Services (NCATS) team at ncats@hq. dhs. gov for scanning as directed in OMB M-15 -01*. *M-15 -01: Fiscal Year 2014 -2015 Guidance on Improving Federal Information Security and Privacy Management Practices 87
M-16 -04 Cybersecurity Strategy and Implementation Plan (CSIP) for the Federal Civilian Government Contains five (5) key objectives Outlines key actions, responsibilities, and timeframes for implementation. Progress will be tracked through several mechanisms, to include comprehensive reviews of agency-specific cybersecurity posture (Cyber. Stats), the CIO Council, and the Information Security and Identity Management Committee (ISIMC). The PMC will serve as the Executive Steering Committee and will oversee quarterly performance reviews to identify major performance gaps. 88
M-16 -04 OMB Cyber* The OMB Cyber and National Security Unit (OMB Cyber) will strengthen Federal cybersecurity through: 1. Data-driven, risk-based oversight of agency and government-wide cybersecurity programs; 2. Issuance and implementation of Federal policies to address emerging IT security risks; and 3. Oversight of the government-wide response to major incidents and vulnerabilities to reduce their impact on the Federal Government. *OMB Cyber was created at the beginning of FY 2015. 89
M-16 -04 New OMB Services* Identity, Authentication, and Authorization Services Mobile Security Services Network Segmentation Services Digital Rights Management (DRM) Encryption Services *OMB is providing new services for agencies without existing capabilities 90
M-16 -04 Cybersecurity Strategy and Implementation Plan (CSIP) The CSIP is organized in the following manner: Objectives: “What we need to achieve” Actions: “How and where we focus our efforts to achieve those objectives” 91
Objectives M-16 -04 1. Prioritized Identification and Protection of high value information and assets; 2. Timely Detection of and Rapid Response to cyber incidents; Rapid Recovery from incidents when they occur and Accelerated Adoption of lessons learned from the Sprint assessment; Recruitment and Retention of the most highly-qualified Cybersecurity Workforce talent the Federal Government can bring to bear; and Efficient and Effective Acquisition and Deployment of Existing and Emerging Technology. 3. 4. 5. 92
Actions M-16 -04 1. All agencies will continue to identify their high value assets (HVAs) and critical system architecture in order to understand the potential impact to those assets from a cyber incident, and ensure robust physical and cybersecurity protections are in place. 2. DHS will accelerate the deployment of Continuous Diagnostics and Mitigation (CDM) and E (EINSTEIN) capabilities to all participating Federal agencies to enhance detection of cyber vulnerabilities and protection from cyber threats. 3. All agencies will improve the identity and access management of user accounts on Federal information systems to drastically reduce vulnerabilities and successful intrusions. 4. OMB, in coordination with NSC and DHS, will issue incident response best practices for use by Federal agencies, incorporating lessons learned from past cyber incidents to ensure future incidents are mitigated in a consistent and timely manner. 93
Actions M-16 -04 5. The National Institute of Standards and Technology (NIST) will provide updated guidance to agencies on how to recover from cyber events. 6. The Office of Personnel Management (OPM) and OMB will initiate several new efforts to improve Federal cybersecurity workforce recruitment, hiring, and training and ensure a pipeline for future talent is put in place. 7. The Chief Information Officer (CIO) Council will create an Emerging Technology Sub-Committee to facilitate efforts to rapidly deploy emerging technologies at Federal agencies. 8. The President’s Management Council (PMC) will oversee the implementation of the CSIP in recognition of the key role Deputy Secretaries play in managing cybersecurity within their agencies. 9. CIOs and Chief Information Security Officers (CISOs) will also have direct responsibility and accountability for implementation of the CSIP, consistent with their role of ensuring the identification and protection of their agency’s critical systems and information. 94
OMB References � Circular A-130 - https: //www. whitehouse. gov/omb/circulars_a 130 � Memoranda ◦ ◦ ◦ ◦ � 03 -22: OMB Guidance for Implementing the Privacy Provisions of the E-Government Act of 2002 - https: //www. whitehouse. gov/omb/memoranda_m 03 -22 05 -08: Designation of Senior Agency Officials for Privacy - https: //www. whitehouse. gov/sites/default/files/omb/memoranda/fy 2005/m 05 -08. pdf 06 -08: 2006 Inventories of Commercial and Inherently Governmental Activities - http: //georgewbush-whitehouse. archives. gov/omb/memoranda/fy 2006/m-06 -08. pdf 06 -16: Protection of Sensitive Agency Information - https: //www. whitehouse. gov/sites/default/files/omb/memoranda/fy 2006/m 06 -16. pdf 07 -16: Safeguarding Against and Responding to the Breach of Personally Identifiable Information - https: //www. whitehouse. gov/sites/default/files/omb/memoranda/fy 2007/m 0716. pdf 08 -09: New FISMA Privacy Reporting Requirements for FY 2008 - https: //www. whitehouse. gov/sites/default/files/omb/memoranda/fy 2008/m 08 -09. pdf 10 -22: Guidance for Online Use of Web Measurement and Customization Technologies - https: //www. whitehouse. gov/sites/default/files/omb/assets/memoranda_2010/m 10 -22. pdf 10 -23: Guidance for Agency Use of Third-Party Websites and Applications - https: //www. whitehouse. gov/sites/default/files/omb/assets/memoranda_2010/m 10 -23. pdf Guidelines for Ensuring and Maximizing the Quality, Objectivity, Utility, and Integrity of Information Disseminated by Federal Agencies (February 2002) - https: //www. whitehouse. gov/sites/default/files/omb/fedreg/reproducible 2. pdf 95
Special Publications (SPs) 500 – Computer Technology Systems 800 – Computer Security 1800 – Cybersecurity Practice Guides Interagency Reports (IRs) 96
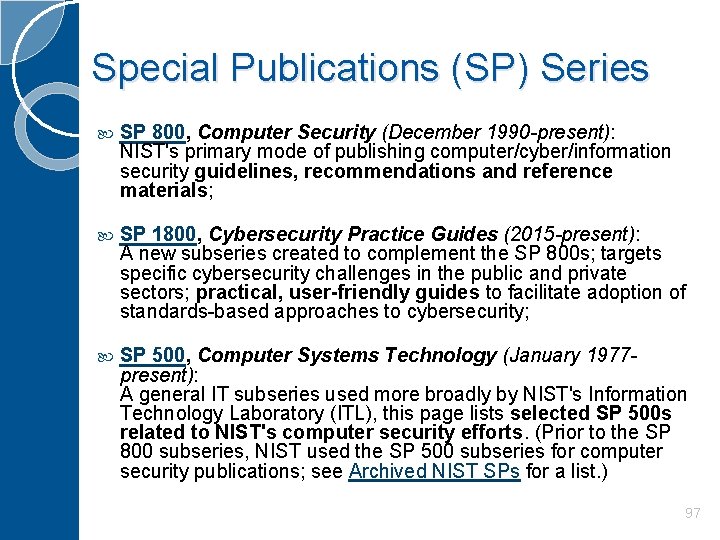
Special Publications (SP) Series SP 800, Computer Security (December 1990 -present): NIST's primary mode of publishing computer/cyber/information security guidelines, recommendations and reference materials; SP 1800, Cybersecurity Practice Guides (2015 -present): A new subseries created to complement the SP 800 s; targets specific cybersecurity challenges in the public and private sectors; practical, user-friendly guides to facilitate adoption of standards-based approaches to cybersecurity; SP 500, Computer Systems Technology (January 1977 present): A general IT subseries used more broadly by NIST's Information Technology Laboratory (ITL), this page lists selected SP 500 s related to NIST's computer security efforts. (Prior to the SP 800 subseries, NIST used the SP 500 subseries for computer security publications; see Archived NIST SPs for a list. ) 97
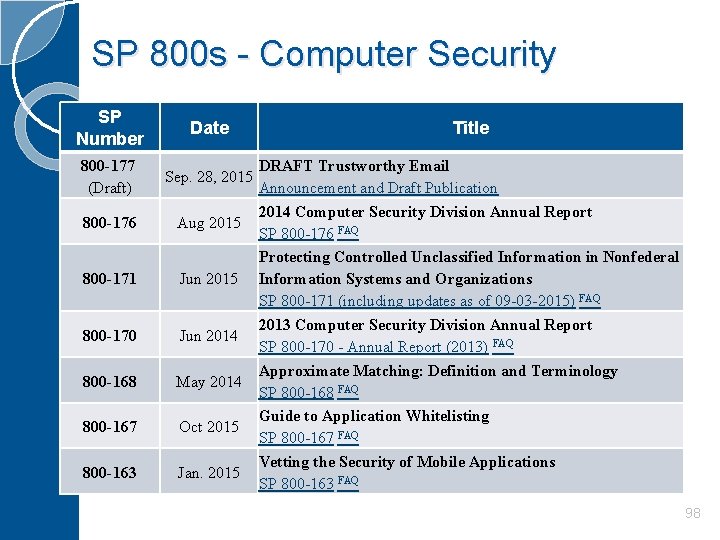
SP 800 s - Computer Security SP Number Date 800 -177 (Draft) Sep. 28, 2015 800 -176 Aug 2015 800 -171 Jun 2015 800 -170 Jun 2014 800 -168 May 2014 800 -167 Oct 2015 800 -163 Jan. 2015 Title DRAFT Trustworthy Email Announcement and Draft Publication 2014 Computer Security Division Annual Report SP 800 -176 FAQ Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations SP 800 -171 (including updates as of 09 -03 -2015) FAQ 2013 Computer Security Division Annual Report SP 800 -170 - Annual Report (2013) FAQ Approximate Matching: Definition and Terminology SP 800 -168 FAQ Guide to Application Whitelisting SP 800 -167 FAQ Vetting the Security of Mobile Applications SP 800 -163 FAQ 98
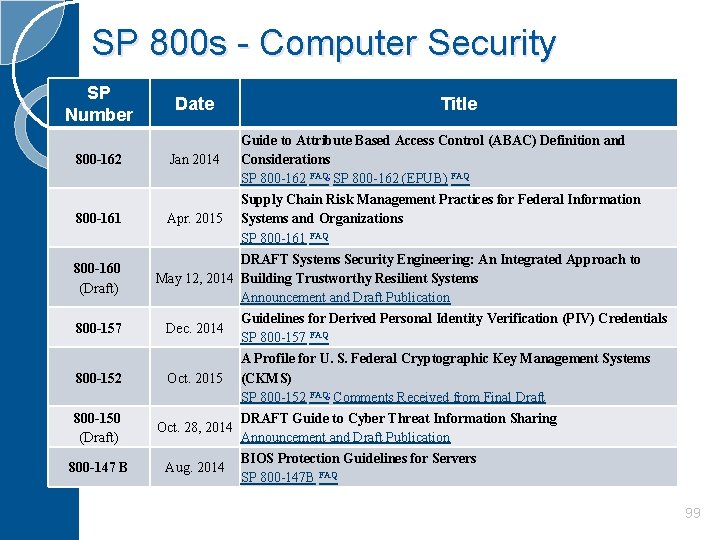
SP 800 s - Computer Security SP Number 800 -162 800 -161 800 -160 (Draft) 800 -157 800 -152 800 -150 (Draft) 800 -147 B Date Title Guide to Attribute Based Access Control (ABAC) Definition and Jan 2014 Considerations SP 800 -162 FAQ; SP 800 -162 (EPUB) FAQ Supply Chain Risk Management Practices for Federal Information Apr. 2015 Systems and Organizations SP 800 -161 FAQ DRAFT Systems Security Engineering: An Integrated Approach to May 12, 2014 Building Trustworthy Resilient Systems Announcement and Draft Publication Guidelines for Derived Personal Identity Verification (PIV) Credentials Dec. 2014 SP 800 -157 FAQ A Profile for U. S. Federal Cryptographic Key Management Systems Oct. 2015 (CKMS) SP 800 -152 FAQ; Comments Received from Final Draft DRAFT Guide to Cyber Threat Information Sharing Oct. 28, 2014 Announcement and Draft Publication BIOS Protection Guidelines for Servers Aug. 2014 SP 800 -147 B FAQ 99
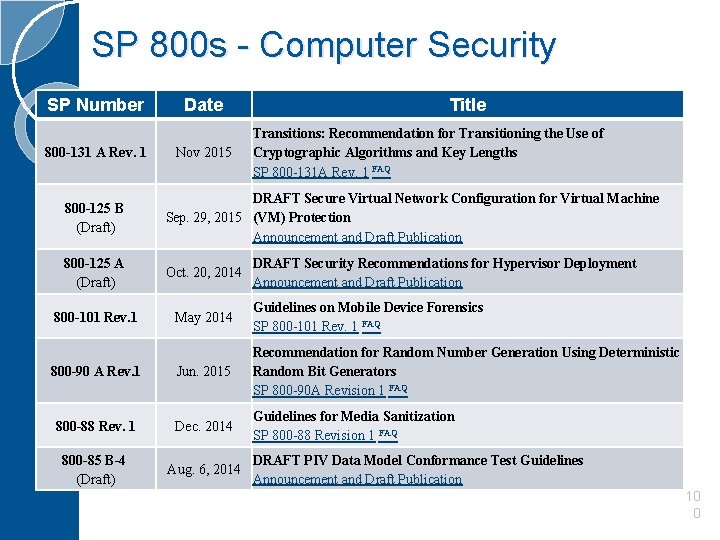
SP 800 s - Computer Security SP Number 800 -131 A Rev. 1 Date Nov 2015 Title Transitions: Recommendation for Transitioning the Use of Cryptographic Algorithms and Key Lengths SP 800 -131 A Rev. 1 FAQ 800 -125 B (Draft) DRAFT Secure Virtual Network Configuration for Virtual Machine Sep. 29, 2015 (VM) Protection Announcement and Draft Publication 800 -125 A (Draft) Oct. 20, 2014 800 -101 Rev. 1 May 2014 Guidelines on Mobile Device Forensics SP 800 -101 Rev. 1 FAQ 800 -90 A Rev. 1 Jun. 2015 Recommendation for Random Number Generation Using Deterministic Random Bit Generators SP 800 -90 A Revision 1 FAQ 800 -88 Rev. 1 Dec. 2014 Guidelines for Media Sanitization SP 800 -88 Revision 1 FAQ 800 -85 B-4 (Draft) Aug. 6, 2014 DRAFT Security Recommendations for Hypervisor Deployment Announcement and Draft Publication DRAFT PIV Data Model Conformance Test Guidelines Announcement and Draft Publication 10 0
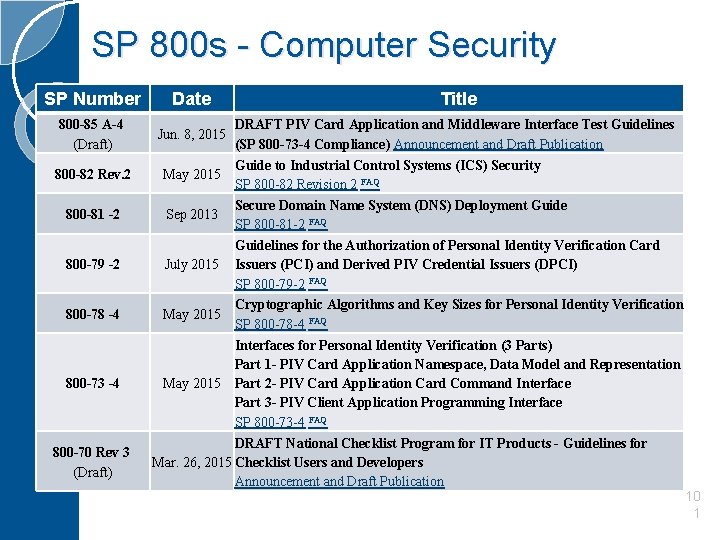
SP 800 s - Computer Security SP Number 800 -85 A-4 (Draft) 800 -82 Rev. 2 800 -81 -2 800 -79 -2 800 -78 -4 800 -73 -4 800 -70 Rev 3 (Draft) Date Title DRAFT PIV Card Application and Middleware Interface Test Guidelines (SP 800 -73 -4 Compliance) Announcement and Draft Publication Guide to Industrial Control Systems (ICS) Security May 2015 SP 800 -82 Revision 2 FAQ Secure Domain Name System (DNS) Deployment Guide Sep 2013 SP 800 -81 -2 FAQ Guidelines for the Authorization of Personal Identity Verification Card July 2015 Issuers (PCI) and Derived PIV Credential Issuers (DPCI) SP 800 -79 -2 FAQ Cryptographic Algorithms and Key Sizes for Personal Identity Verification May 2015 SP 800 -78 -4 FAQ Interfaces for Personal Identity Verification (3 Parts) Part 1 - PIV Card Application Namespace, Data Model and Representation May 2015 Part 2 - PIV Card Application Card Command Interface Part 3 - PIV Client Application Programming Interface SP 800 -73 -4 FAQ DRAFT National Checklist Program for IT Products - Guidelines for Mar. 26, 2015 Checklist Users and Developers Announcement and Draft Publication Jun. 8, 2015 10 1
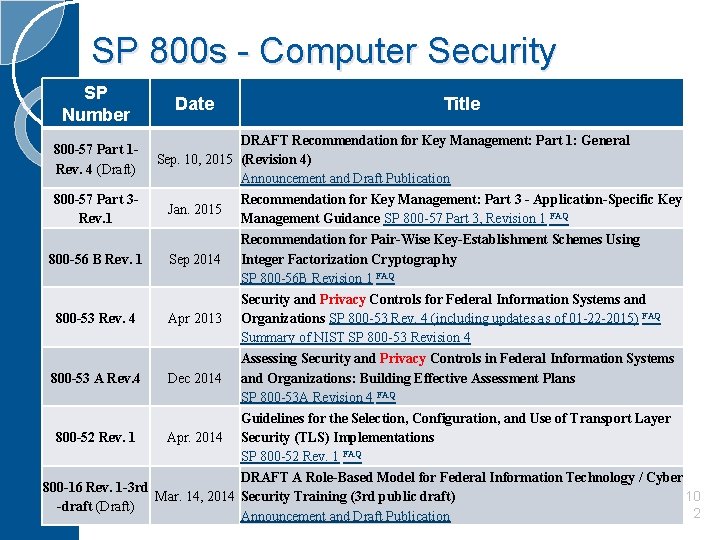
SP 800 s - Computer Security SP Number Date Title DRAFT Recommendation for Key Management: Part 1: General Sep. 10, 2015 (Revision 4) Announcement and Draft Publication 800 -57 Part 3 Recommendation for Key Management: Part 3 - Application-Specific Key Jan. 2015 Rev. 1 Management Guidance SP 800 -57 Part 3, Revision 1 FAQ Recommendation for Pair-Wise Key-Establishment Schemes Using 800 -56 B Rev. 1 Sep 2014 Integer Factorization Cryptography SP 800 -56 B Revision 1 FAQ Security and Privacy Controls for Federal Information Systems and 800 -53 Rev. 4 Apr 2013 Organizations SP 800 -53 Rev. 4 (including updates as of 01 -22 -2015) FAQ Summary of NIST SP 800 -53 Revision 4 Assessing Security and Privacy Controls in Federal Information Systems 800 -53 A Rev. 4 Dec 2014 and Organizations: Building Effective Assessment Plans SP 800 -53 A Revision 4 FAQ Guidelines for the Selection, Configuration, and Use of Transport Layer 800 -52 Rev. 1 Apr. 2014 Security (TLS) Implementations SP 800 -52 Rev. 1 FAQ DRAFT A Role-Based Model for Federal Information Technology / Cyber 800 -16 Rev. 1 -3 rd 10 Mar. 14, 2014 Security Training (3 rd public draft) -draft (Draft) 2 Announcement and Draft Publication 800 -57 Part 1 Rev. 4 (Draft)
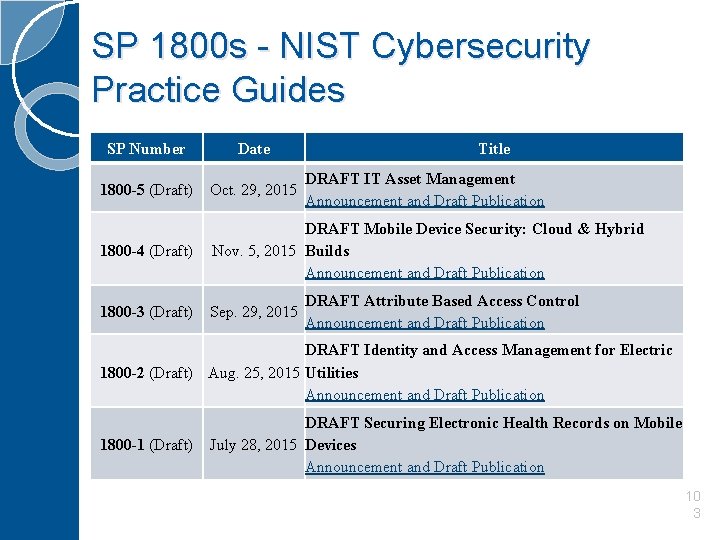
SP 1800 s - NIST Cybersecurity Practice Guides SP Number Date Title 1800 -5 (Draft) Oct. 29, 2015 1800 -4 (Draft) DRAFT Mobile Device Security: Cloud & Hybrid Nov. 5, 2015 Builds Announcement and Draft Publication 1800 -3 (Draft) Sep. 29, 2015 DRAFT IT Asset Management Announcement and Draft Publication DRAFT Attribute Based Access Control Announcement and Draft Publication DRAFT Identity and Access Management for Electric 1800 -2 (Draft) Aug. 25, 2015 Utilities Announcement and Draft Publication 1800 -1 (Draft) DRAFT Securing Electronic Health Records on Mobile July 28, 2015 Devices Announcement and Draft Publication 10 3
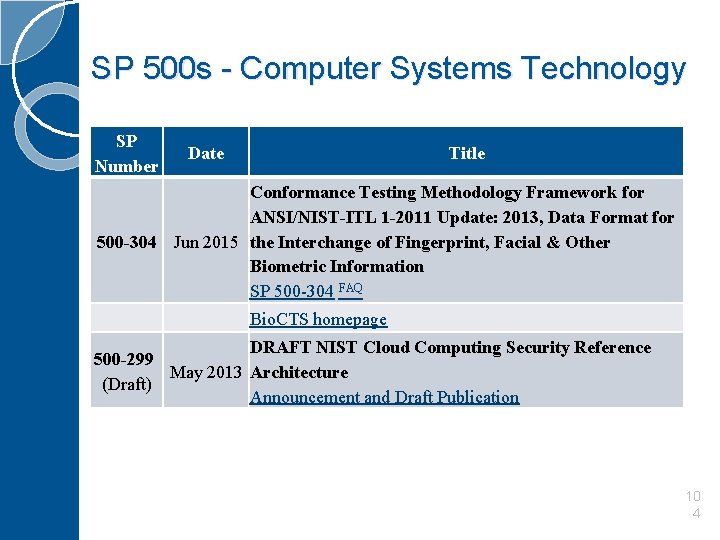
SP 500 s - Computer Systems Technology SP Number Date Title Conformance Testing Methodology Framework for ANSI/NIST-ITL 1 -2011 Update: 2013, Data Format for 500 -304 Jun 2015 the Interchange of Fingerprint, Facial & Other Biometric Information SP 500 -304 FAQ Bio. CTS homepage DRAFT NIST Cloud Computing Security Reference 500 -299 May 2013 Architecture (Draft) Announcement and Draft Publication 10 4
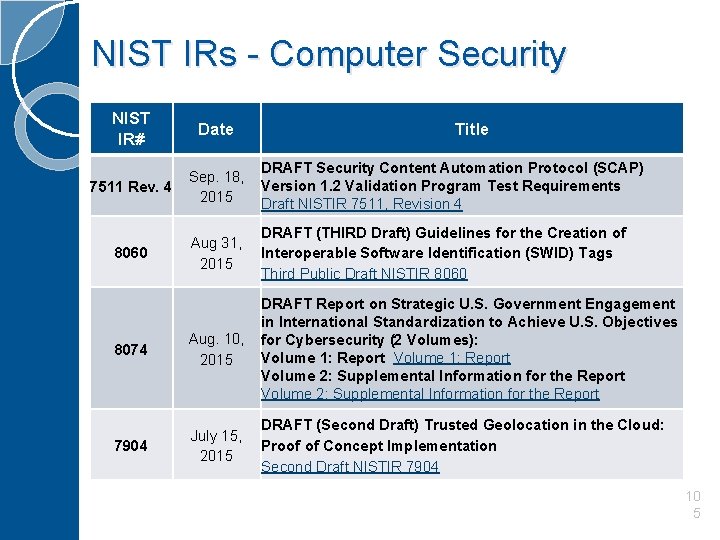
NIST IRs - Computer Security NIST IR# 7511 Rev. 4 Date Title DRAFT Security Content Automation Protocol (SCAP) Sep. 18, Version 1. 2 Validation Program Test Requirements 2015 Draft NISTIR 7511, Revision 4 8060 DRAFT (THIRD Draft) Guidelines for the Creation of Aug 31, Interoperable Software Identification (SWID) Tags 2015 Third Public Draft NISTIR 8060 8074 DRAFT Report on Strategic U. S. Government Engagement in International Standardization to Achieve U. S. Objectives Aug. 10, for Cybersecurity (2 Volumes): Volume 1: Report 2015 Volume 2: Supplemental Information for the Report 7904 DRAFT (Second Draft) Trusted Geolocation in the Cloud: July 15, Proof of Concept Implementation 2015 Second Draft NISTIR 7904 10 5
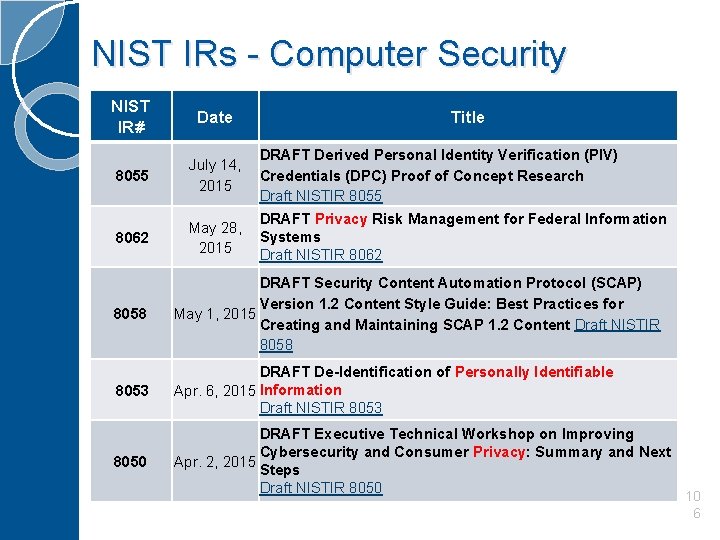
NIST IRs - Computer Security NIST IR# Date Title 8055 DRAFT Derived Personal Identity Verification (PIV) July 14, Credentials (DPC) Proof of Concept Research 2015 Draft NISTIR 8055 8062 DRAFT Privacy Risk Management for Federal Information May 28, Systems 2015 Draft NISTIR 8062 8058 DRAFT Security Content Automation Protocol (SCAP) Version 1. 2 Content Style Guide: Best Practices for May 1, 2015 Creating and Maintaining SCAP 1. 2 Content Draft NISTIR 8058 8053 DRAFT De-Identification of Personally Identifiable Apr. 6, 2015 Information Draft NISTIR 8053 8050 DRAFT Executive Technical Workshop on Improving Cybersecurity and Consumer Privacy: Summary and Next Apr. 2, 2015 Steps Draft NISTIR 8050 10 6
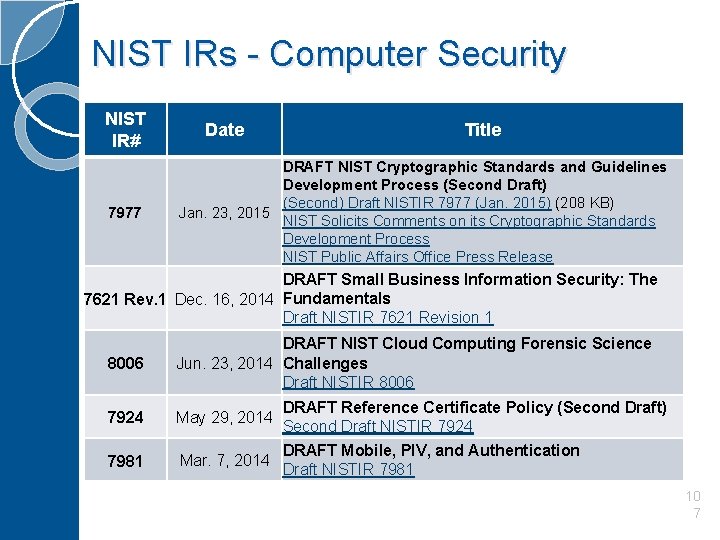
NIST IRs - Computer Security NIST IR# 7977 Date Title DRAFT NIST Cryptographic Standards and Guidelines Development Process (Second Draft) (Second) Draft NISTIR 7977 (Jan. 2015) (208 KB) Jan. 23, 2015 NIST Solicits Comments on its Cryptographic Standards Development Process NIST Public Affairs Office Press Release DRAFT Small Business Information Security: The 7621 Rev. 1 Dec. 16, 2014 Fundamentals Draft NISTIR 7621 Revision 1 8006 DRAFT NIST Cloud Computing Forensic Science Jun. 23, 2014 Challenges Draft NISTIR 8006 7924 May 29, 2014 DRAFT Reference Certificate Policy (Second Draft) Second Draft NISTIR 7924 7981 Mar. 7, 2014 DRAFT Mobile, PIV, and Authentication Draft NISTIR 7981 10 7

Privacy Controls NIST SP 800 -53 REV. 4 10 8
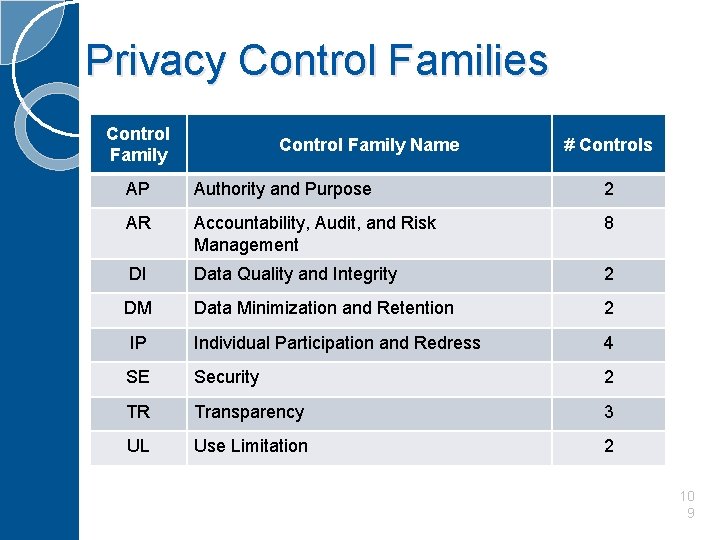
Privacy Control Families Control Family Name # Controls AP Authority and Purpose 2 AR Accountability, Audit, and Risk Management 8 DI Data Quality and Integrity 2 DM Data Minimization and Retention 2 IP Individual Participation and Redress 4 SE Security 2 TR Transparency 3 UL Use Limitation 2 10 9
Authority and Purpose (AP) AP-1 Authority to Collect ◦ The organization determines and documents the legal authority that permits the collection, use, maintenance, and sharing of personally identifiable information (PII), either generally or in support of a specific program or information system need. AP-2 Purpose Specification ◦ The organization describes the purpose(s) for which PII is collected, used, maintained, and shared in its privacy notices. 11 0
Accountability, Audit, and Risk Management (AR) AR-1 Governance and Privacy Program The organization: a. Appoints a Senior Agency Official for Privacy (SAOP)/Chief Privacy Officer (CPO) accountable for developing, implementing, and maintaining an organization-wide governance and privacy program to ensure compliance with all applicable laws and regulations regarding the collection, use, maintenance, sharing, and disposal of personally identifiable information (PII) by programs and information systems; b. Monitors federal privacy laws and policy for changes that affect the privacy program; c. Allocates [Assignment: organization-defined allocation of budget and staffing] sufficient resources to implement and operate the organization-wide privacy program; d. Develops a strategic organizational privacy plan for implementing applicable privacy controls, policies, and procedures; e. Develops, disseminates, and implements operational privacy policies and procedures that govern the appropriate privacy and security controls for programs, information systems, or technologies involving PII; and f. Updates privacy plan, policies, and procedures [Assignment: organization-defined frequency, at least biennially]. 11 1
Accountability, Audit, and Risk Management (AR) AR-2 Privacy Impact and Risk Assessment The organization: a. Documents and implements a privacy risk management process that assesses privacy risk to individuals resulting from the collection, sharing, storing, transmitting, use, and disposal of PII; and b. Conducts Privacy Impact Assessments (PIAs) for information systems, programs, or other activities that pose a privacy risk in accordance with applicable law, OMB policy, or any existing organizational policies and procedures. AR-3 Privacy Requirements for Contractors and Service Providers The organization: a. Establishes privacy roles, responsibilities, and access requirements for contractors and service providers; and b. Includes privacy requirements in contracts and other acquisition-related documents. AR-4 Privacy Monitoring and Auditing � The organization monitors and audits privacy controls and internal privacy policy [Assignment: organization-defined frequency] to ensure effective implementation. 11 2
Accountability, Audit, and Risk Management (AR) AR-5 Privacy Awareness and Training The organization: a. Develops, implements, and updates a comprehensive training and awareness strategy aimed at ensuring that personnel understand privacy responsibilities and procedures; b. Administers basic privacy training [Assignment: organization-defined frequency, at least annually] and targeted, role-based privacy training for personnel having responsibility for PII or for activities that involve PII [Assignment: organization-defined frequency, at least annually]; and c. Ensures that personnel certify (manually or electronically) acceptance of responsibilities for privacy requirements [Assignment: organization-defined frequency, at least annually]. AR-6 Privacy Reporting � The organization develops, disseminates, and updates reports to the Office of Management and Budget (OMB), Congress, and other oversight bodies, as appropriate, to demonstrate accountability with specific statutory and regulatory privacy program mandates, and to senior management and other personnel with responsibility for monitoring privacy program progress and compliance. 11 3
Accountability, Audit, and Risk Management (AR) AR-7 Privacy- Enhanced System Design and Development � The organization designs information systems to support privacy by automating privacy controls. AR-8 Accounting of Disclosures The organization: a. Keeps an accurate accounting of disclosures of information held in each system of records under its control, including: 1. 2. b. c. Date, nature, and purpose of each disclosure of a record; and Name and address of the person or agency to which the disclosure was made; Retains the accounting of disclosures for the life of the record or five years after the disclosure is made, whichever is longer; and Makes the accounting of disclosures available to the person named in the record upon request. 11 4
Data Quality and Integrity (DI) DI-1 Data Quality The organization: a. b. c. d. Confirms to the greatest extent practicable upon collection or creation of PII, the accuracy, relevance, timeliness, and completeness of that information; Collects PII directly from the individual to the greatest extent practicable; Checks for, and corrects as necessary, any inaccurate or outdated PII used by its programs or systems [Assignment: organization-defined frequency]; and Issues guidelines ensuring and maximizing the quality, utility, objectivity, and integrity of disseminated information. DI-2 Data Integrity and Data Integrity Board The organization: a. b. Documents processes to ensure the integrity of PII through existing security controls; and Establishes a Data Integrity Board when appropriate to oversee organizational Computer Matching Agreements and to ensure that those agreements comply with the computer matching provisions of the Privacy Act. 11 5
Data Minimization and Retention (DM) DM-1 Minimization of Personally Identifiable Information (PII) The organization: a. Identifies the minimum PII elements that are relevant and necessary to accomplish the legally authorized purpose of collection; b. Limits the collection and retention of PII to the minimum elements identified for the purposes described in the notice and for which the individual has provided consent; and c. Conducts an initial evaluation of PII holdings and establishes and follows a schedule for regularly reviewing those holdings [Assignment: organizationdefined frequency, at least annually] to ensure that only PII identified in the notice is collected and retained, and that the PII continues to be necessary to accomplish the legally authorized purpose. 11 6
Data Minimization and Retention (DM) DM-2 Data Retention and Disposal The organization: a. b. c. Retains each collection of PII for [Assignment: organizationdefined time period] to fulfill the purpose(s) identified in the notice or as required by law; Disposes of, destroys, erases, and/or anonymizes the PII, regardless of the method of storage, in accordance with a NARA -approved record retention schedule and in a manner that prevents loss, theft, misuse, or unauthorized access; and Uses [Assignment: organization-defined techniques or methods] to ensure secure deletion or destruction of PII (including originals, copies, and archived records). DM-3 Minimization of PII Used in Testing, Training, and Research The organization: a. b. Develops policies and procedures that minimize the use of PII for testing, training, and research; and Implements controls to protect PII used for testing, training, and research. 11 7
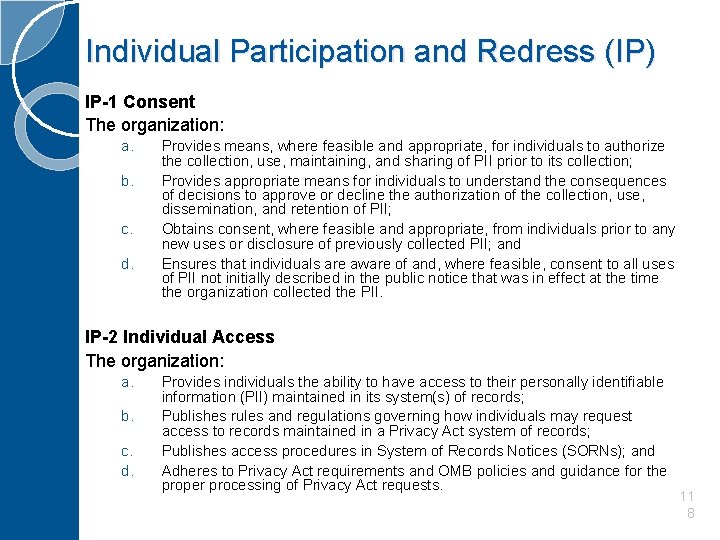
Individual Participation and Redress (IP) IP-1 Consent The organization: a. b. c. d. Provides means, where feasible and appropriate, for individuals to authorize the collection, use, maintaining, and sharing of PII prior to its collection; Provides appropriate means for individuals to understand the consequences of decisions to approve or decline the authorization of the collection, use, dissemination, and retention of PII; Obtains consent, where feasible and appropriate, from individuals prior to any new uses or disclosure of previously collected PII; and Ensures that individuals are aware of and, where feasible, consent to all uses of PII not initially described in the public notice that was in effect at the time the organization collected the PII. IP-2 Individual Access The organization: a. b. c. d. Provides individuals the ability to have access to their personally identifiable information (PII) maintained in its system(s) of records; Publishes rules and regulations governing how individuals may request access to records maintained in a Privacy Act system of records; Publishes access procedures in System of Records Notices (SORNs); and Adheres to Privacy Act requirements and OMB policies and guidance for the proper processing of Privacy Act requests. 11 8
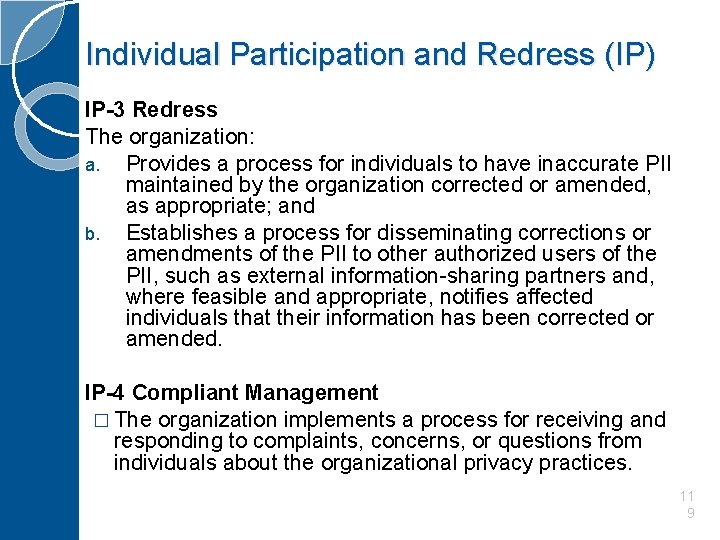
Individual Participation and Redress (IP) IP-3 Redress The organization: a. Provides a process for individuals to have inaccurate PII maintained by the organization corrected or amended, as appropriate; and b. Establishes a process for disseminating corrections or amendments of the PII to other authorized users of the PII, such as external information-sharing partners and, where feasible and appropriate, notifies affected individuals that their information has been corrected or amended. IP-4 Compliant Management � The organization implements a process for receiving and responding to complaints, concerns, or questions from individuals about the organizational privacy practices. 11 9
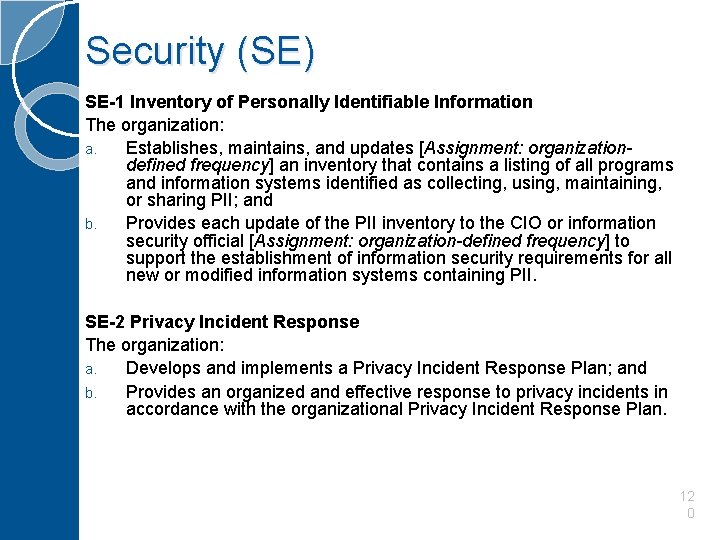
Security (SE) SE-1 Inventory of Personally Identifiable Information The organization: a. Establishes, maintains, and updates [Assignment: organizationdefined frequency] an inventory that contains a listing of all programs and information systems identified as collecting, using, maintaining, or sharing PII; and b. Provides each update of the PII inventory to the CIO or information security official [Assignment: organization-defined frequency] to support the establishment of information security requirements for all new or modified information systems containing PII. SE-2 Privacy Incident Response The organization: a. Develops and implements a Privacy Incident Response Plan; and b. Provides an organized and effective response to privacy incidents in accordance with the organizational Privacy Incident Response Plan. 12 0
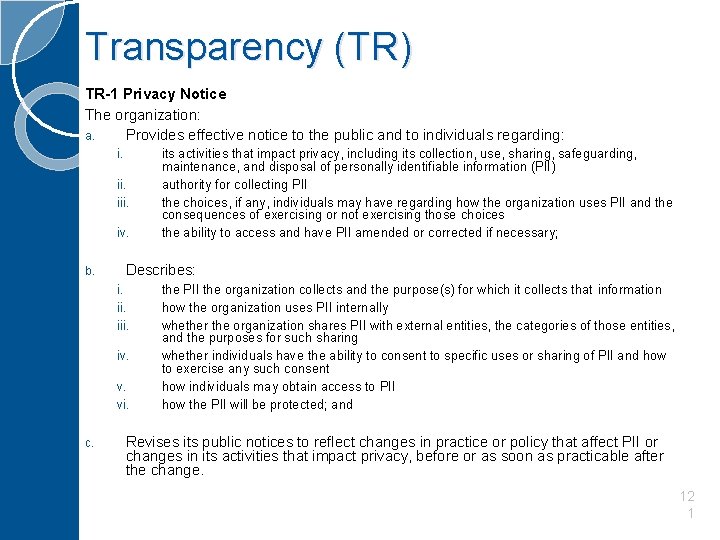
Transparency (TR) TR-1 Privacy Notice The organization: a. Provides effective notice to the public and to individuals regarding: i. iii. iv. b. Describes: i. iii. iv. v. vi. c. its activities that impact privacy, including its collection, use, sharing, safeguarding, maintenance, and disposal of personally identifiable information (PII) authority for collecting PII the choices, if any, individuals may have regarding how the organization uses PII and the consequences of exercising or not exercising those choices the ability to access and have PII amended or corrected if necessary; the PII the organization collects and the purpose(s) for which it collects that information how the organization uses PII internally whether the organization shares PII with external entities, the categories of those entities, and the purposes for such sharing whether individuals have the ability to consent to specific uses or sharing of PII and how to exercise any such consent how individuals may obtain access to PII how the PII will be protected; and Revises its public notices to reflect changes in practice or policy that affect PII or changes in its activities that impact privacy, before or as soon as practicable after the change. 12 1
Transparency (TR) TR-2 System of Records Notices and Privacy Act Statements The organization: a. Publishes System of Records Notices (SORNs) in the Federal Register, subject to required oversight processes, for systems containing personally identifiable information (PII); b. Keeps SORNs current; and c. Includes Privacy Act Statements on its forms that collect PII, or on separate forms that can be retained by individuals, to provide additional formal notice to individuals from whom the information is being collected. TR-3 Dissemination of Privacy Program Information The organization: a. Ensures that the public has access to information about its privacy activities and is able to communicate with its Senior Agency Official for Privacy (SAOP)/Chief Privacy Officer (CPO); and b. Ensures that its privacy practices are publicly available through organizational websites or otherwise. 12 2
Use Limitation (UL) UL-1 Internal Use � The organization uses personally identifiable information (PII) internally only for the authorized purpose(s) identified in the Privacy Act and/or in public notices. UL-2 Information Sharing with Third Parties The organization: a. Shares PII externally, only for the authorized purposes identified in the Privacy Act and/or described in its notice(s) or for a purpose that is compatible with those purposes; b. Where appropriate, enters into Memoranda of Understanding, Memoranda of Agreement, Letters of Intent, Computer Matching Agreements, or similar agreements, with third parties that specifically describe the PII covered and specifically enumerate the purposes for which the PII may be used; c. Monitors, audits, and trains its staff on the authorized sharing of PII with third parties and on the consequences of unauthorized use or sharing of PII; and d. Evaluates any proposed new instances of sharing PII with third parties to assess whether the sharing is authorized and whether additional or new public notice is required. 123
NIST SP 800 -53 Rev. 4 Privacy Law & Regulation References �Privacy Act of 1974 �Federal Information Security Management Act (FISMA) of 2002 �E-Government Act of 2002 �Federal Acquisition Regulation � 9/11 Commission Act �Consolidated Appropriations Act of 2005 �Treasury and General Government Appropriations Act for Fiscal Year 2001 �Paperwork Reduction Act 124
NIST References � Federal Information Processing Standards Publication (FIPS) 199 - http: //csrc. nist. gov/publications/fips 199/FIPS-PUB-199 -final. pdf � Special Publications (SPs): ◦ 800 -37 - Guide for Applying the Risk Management Framework to Federal Information Systems: A Security Life Cycle Approach - http: //nvlpubs. nist. gov/nistpubs/Special. Publications/NIST. SP. 800 -37 r 1. pdf ◦ 800 -88 - Guidelines for Media Sanitization - http: //nvlpubs. nist. gov/nistpubs/Special. Publications/NIST. SP. 800 -88 r 1. pdf ◦ 800 -122 - Guide to Protecting the Confidentiality of Personally Identifiable Information (PII) - http: //csrc. nist. gov/publications/nistpubs/800 -122/sp 800 -122. pdf 125
Other References Federal Enterprise Architecture Security and Privacy Profile - https: //cio. gov/wp-content/uploads/downloads/2012/09/FEA-Security-Privacy. Profile-v 3 -09 -30 -2010. pdf Information Sharing Environment (ISE) Privacy Guidelines - https: //www. ise. gov/sites/default/files/Privacy. Guidelines 20061204_1. pdf 126
- Slides: 126