Federal Identity Management and Homeland Security Presidential Directive

- Slides: 17
Federal Identity Management and Homeland Security Presidential Directive 12 David Temoshok Director, Identity Policy and Management GSA Office of Governmentwide Educause Conference 2007 October 24, 2007

President’s Domestic Agenda • President’s Management Agenda: 1. Strategic Management of Human Capital 2. Competitive Sourcing 3. Improved Financial performance 4. Expanded Electronic Government 5. Budget and Performance Integration • E-Government Act of 2002 • OMB Office of E-Government and Technology 2
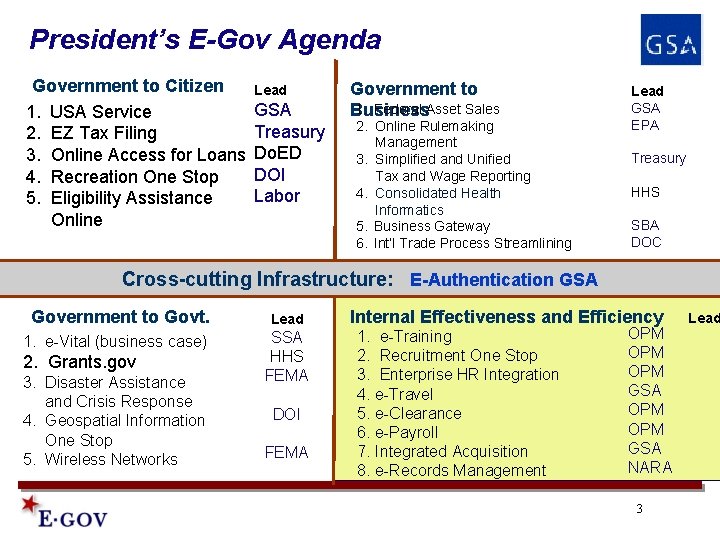
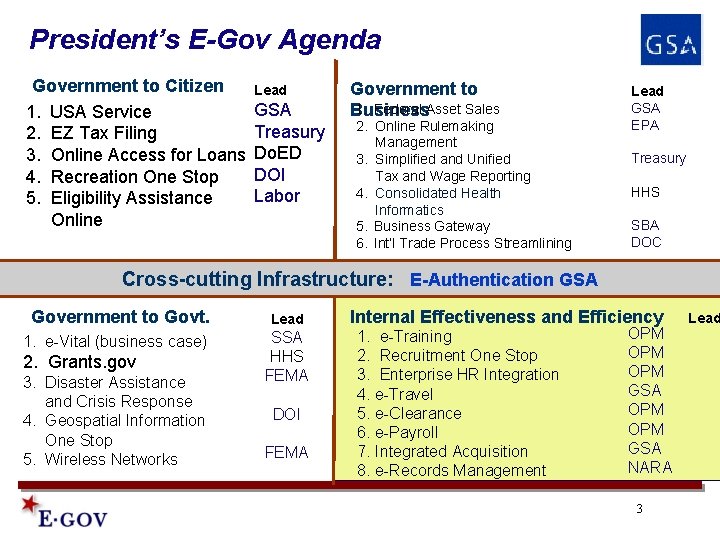
President’s E-Gov Agenda Government to Citizen 1. USA Service 2. EZ Tax Filing 3. Online Access for Loans 4. Recreation One Stop 5. Eligibility Assistance Online Lead GSA Treasury Do. ED DOI Labor Government to 1. Federal Asset Sales Business 2. Online Rulemaking Management 3. Simplified and Unified Tax and Wage Reporting 4. Consolidated Health Informatics 5. Business Gateway 6. Int’l Trade Process Streamlining Lead GSA EPA Treasury HHS SBA DOC Cross-cutting Infrastructure: E-Authentication GSA Government to Govt. 1. e-Vital (business case) 2. Grants. gov 3. Disaster Assistance and Crisis Response 4. Geospatial Information One Stop 5. Wireless Networks Lead SSA HHS FEMA DOI FEMA Internal Effectiveness and Efficiency 1. e-Training 2. Recruitment One Stop 3. Enterprise HR Integration 4. e-Travel 5. e-Clearance 6. e-Payroll 7. Integrated Acquisition 8. e-Records Management OPM OPM GSA NARA 3 Lead
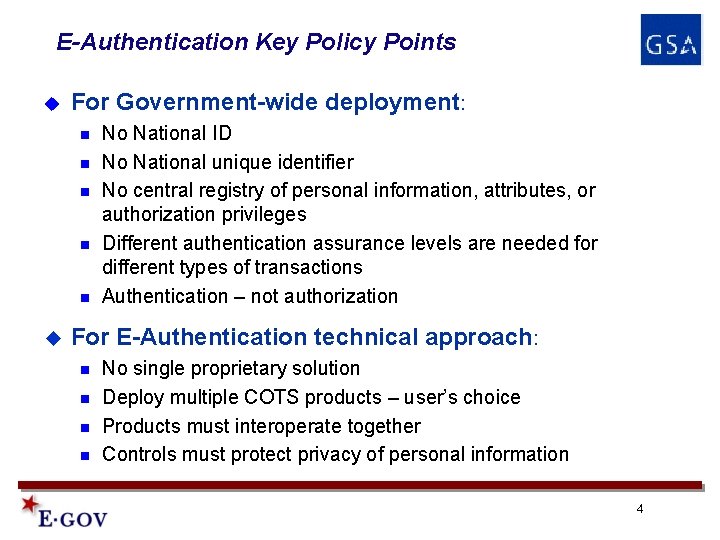
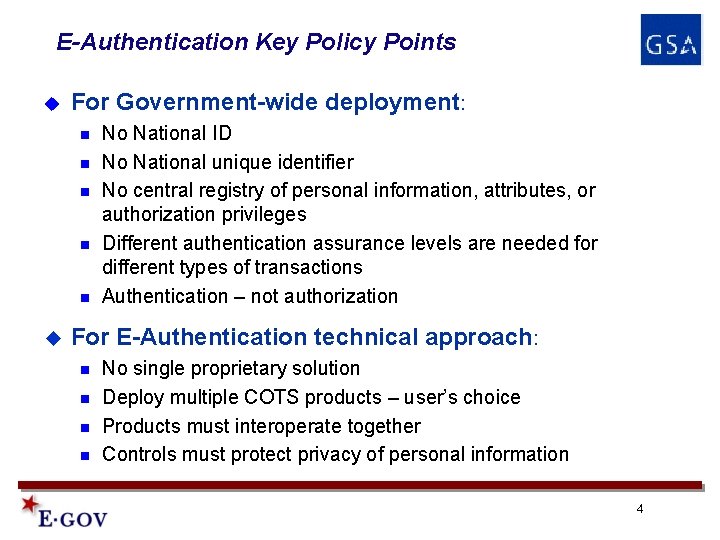
E-Authentication Key Policy Points u For Government-wide deployment: n n n u No National ID No National unique identifier No central registry of personal information, attributes, or authorization privileges Different authentication assurance levels are needed for different types of transactions Authentication – not authorization For E-Authentication technical approach: n n No single proprietary solution Deploy multiple COTS products – user’s choice Products must interoperate together Controls must protect privacy of personal information 4
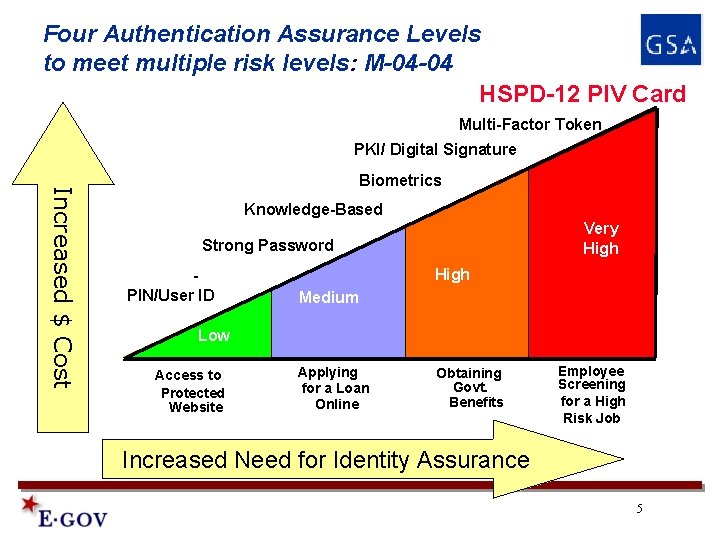
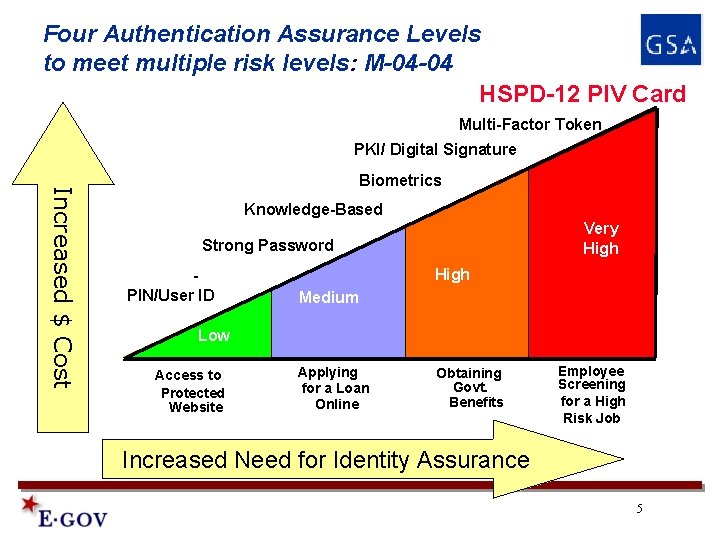
Four Authentication Assurance Levels to meet multiple risk levels: M-04 -04 HSPD-12 PIV Card Multi-Factor Token PKI/ Digital Signature Increased $ Cost Biometrics Knowledge-Based Very High Strong Password PIN/User ID High Medium Low Access to Protected Website Applying for a Loan Online Obtaining Govt. Benefits Employee Screening for a High Risk Job Increased Need for Identity Assurance 5
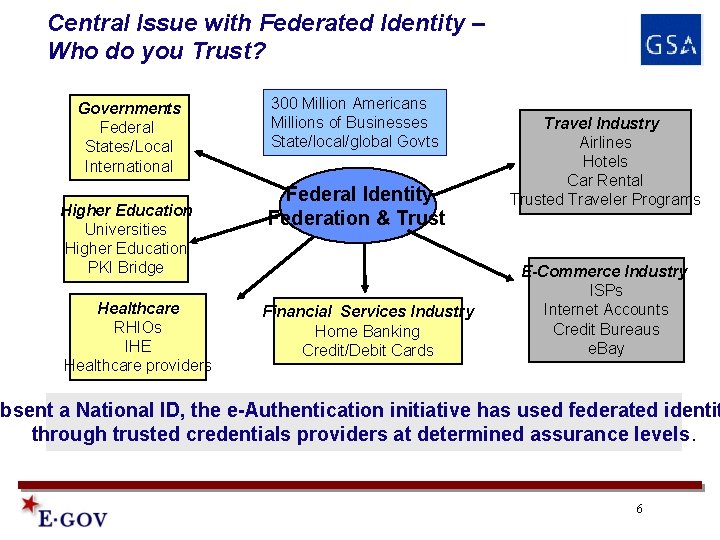
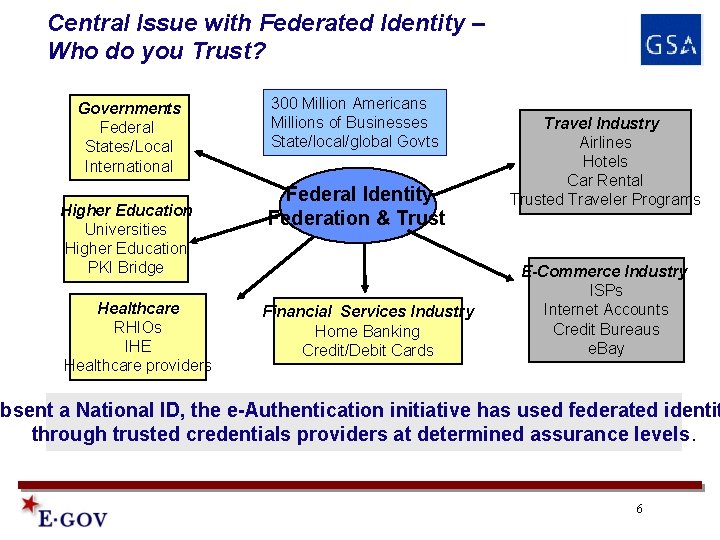
Central Issue with Federated Identity – Who do you Trust? Governments Federal States/Local International Higher Education Universities Higher Education PKI Bridge Healthcare RHIOs IHE Healthcare providers 300 Million Americans Millions of Businesses State/local/global Govts Federal Identity Federation & Trust Financial Services Industry Home Banking Credit/Debit Cards Travel Industry Airlines Hotels Car Rental Trusted Traveler Programs E-Commerce Industry ISPs Internet Accounts Credit Bureaus e. Bay Absent a National ID, the e-Authentication initiative has used federated identit through trusted credentials providers at determined assurance levels. 6
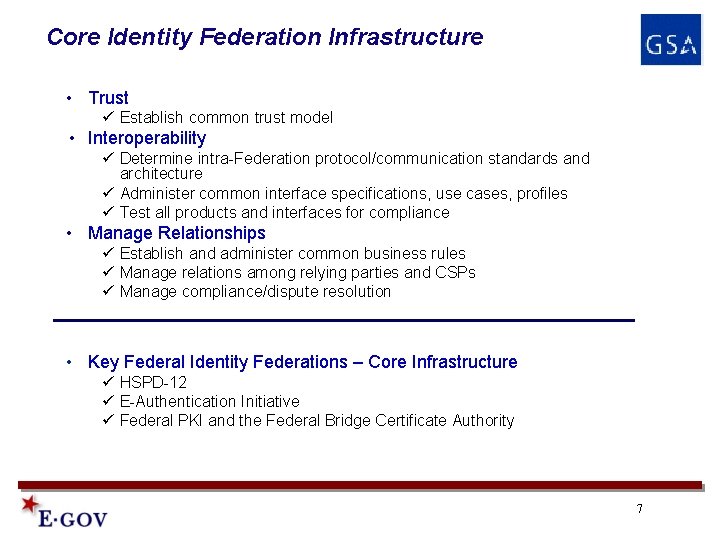
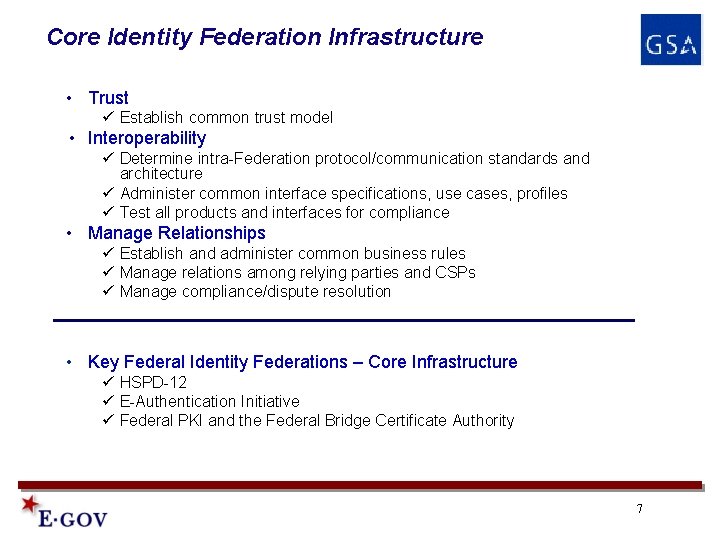
Core Identity Federation Infrastructure • Trust ü Establish common trust model • Interoperability ü Determine intra-Federation protocol/communication standards and architecture ü Administer common interface specifications, use cases, profiles ü Test all products and interfaces for compliance • Manage Relationships ü Establish and administer common business rules ü Manage relations among relying parties and CSPs ü Manage compliance/dispute resolution • Key Federal Identity Federations – Core Infrastructure ü HSPD-12 ü E-Authentication Initiative ü Federal PKI and the Federal Bridge Certificate Authority 7
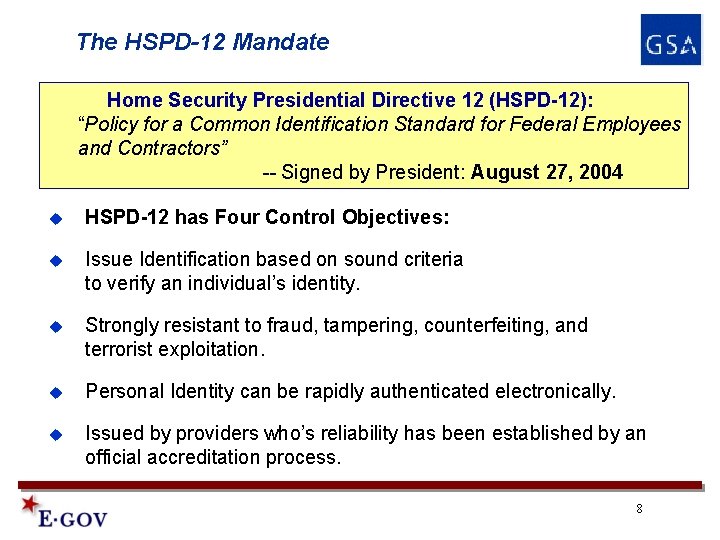
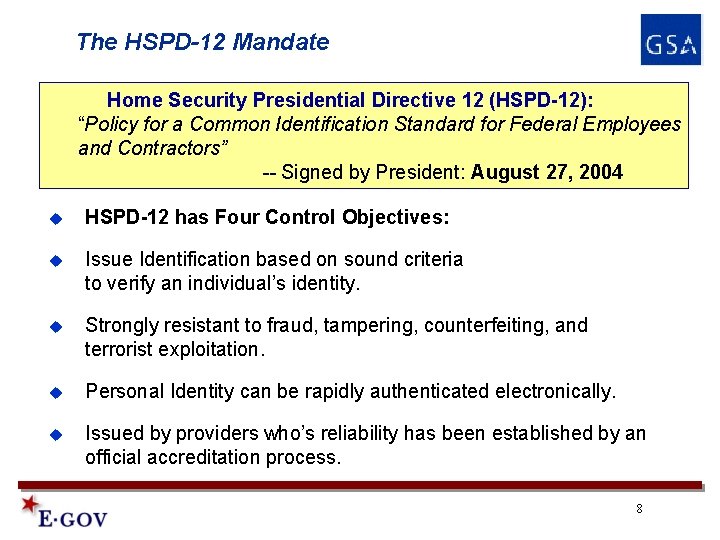
The HSPD-12 Mandate Home Security Presidential Directive 12 (HSPD-12): “Policy for a Common Identification Standard for Federal Employees and Contractors” -- Signed by President: August 27, 2004 u HSPD-12 has Four Control Objectives: u Issue Identification based on sound criteria to verify an individual’s identity. u Strongly resistant to fraud, tampering, counterfeiting, and terrorist exploitation. u Personal Identity can be rapidly authenticated electronically. u Issued by providers who’s reliability has been established by an official accreditation process. 8
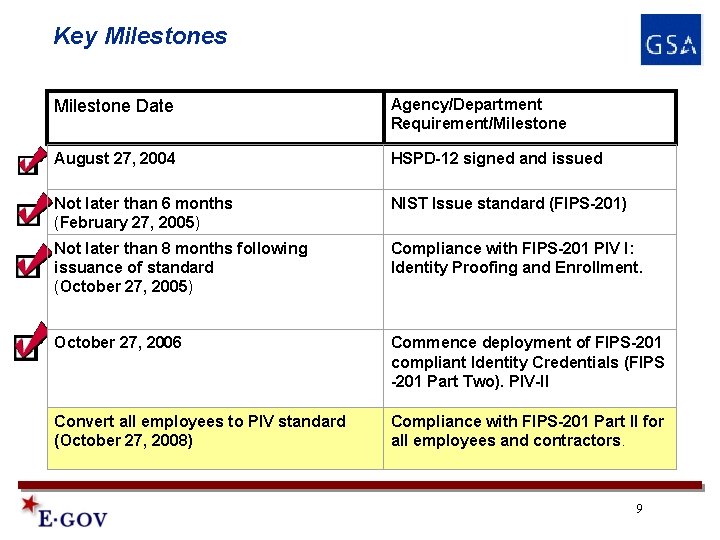
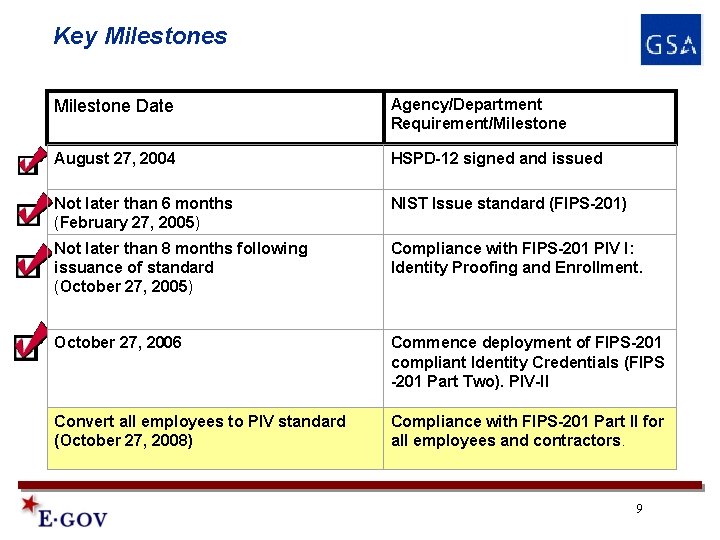
Key Milestones Milestone Date Agency/Department Requirement/Milestone August 27, 2004 HSPD-12 signed and issued Not later than 6 months (February 27, 2005) NIST Issue standard (FIPS-201) Not later than 8 months following issuance of standard (October 27, 2005) Compliance with FIPS-201 PIV I: Identity Proofing and Enrollment. October 27, 2006 October 2005 Not later 27, than 20 months following issuance of standard (October 27, 2006) Commence deployment of FIPS-201 compliant Identity Credentials (FIPS -201 Part Two). PIV-II Convert all employees to PIV standard (October 27, 2008) Compliance with FIPS-201 Part II for all employees and contractors. 9
Government-wide Implementation Strategy • OMB provides policy and implementation guidance. • NIST provides HSPD-12 process and technical requirements (FIPS 201 and associated Special Publications). • GSA (OGP and FAS) provides government-wide implementation and acquisition assistance, coordinates agency implementation through the Federal Identity Credentialing Committee, develops and tests interface specifications for interoperability, and serves as “Executive Agent for Acquisition” for approval of products and services for the implementation of HSPD-12. • Interoperability of HSPD-12 systems across government is required. Agency implementation is controlled through Approved Product List, acquisition controls, and Standard Interface Specifications. • GSA is designated to provide shared services and infrastructure for government-wide implementation (MSO). • Extremely aggressive milestones are needed to maintain focus and momentum. 10
Multiple PIV Authentication Technologies To provide multiple authentication assurance levels, FIPS 201 requires multiple authentication technologies: • Authentication using PIV Visual Credentials – Facial Image • Authentication using the Cardholder Unique Identifier (CHUID) – contact or contact-less • Authentication using PIN • Authentication using Biometric (match on/off card) – fingerprint template • Authentication using PIV asymmetric Cryptography (PKI) – authentication digital certificate • Optional biometric(s) and cryptographic keys (3) Something I have – PIV Card, Keys Something I know - PIN Something I am – Biometric 11
Key Architecture Design Considerations • Architecture must support multiple authentication technologies – PIN, biometric template, CHUID, authentication keys. • Architecture must support multiple protocols – for credential validation and “electronic authentication”. • Federal Government will not mandate a single proprietary solution, therefore, Architecture must support multiple COTS products. • All architecture components must interoperate with ALL other components (see www. idmanagement. gov) – requires product and systems testing. • Interface specifications are necessary for inter-system data exchange. • Controls must protect privacy of personal information. 12
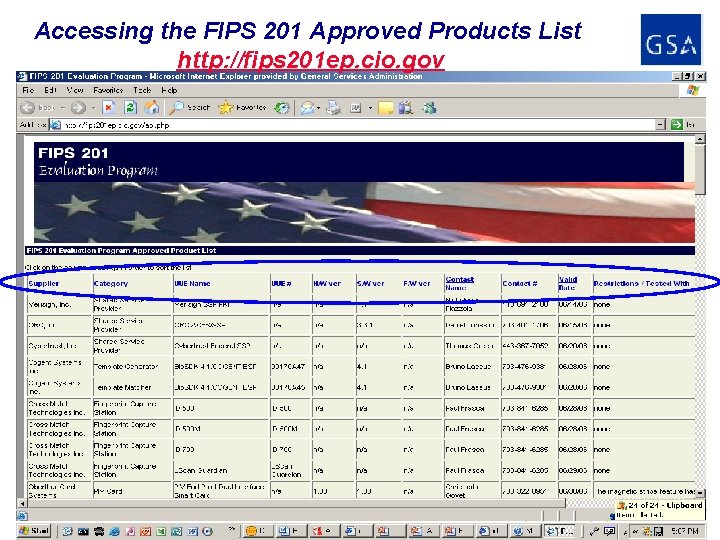
Status of GSA FIPS 201 Evaluation Program • OGP administers the FIPS-201 Evaluation Program to determine conformance to FIPS-201 normative requirements. ü Certified laboratories perform all FIPS 201 compliance evaluations ü OGP approves all evaluations and posts to Approved Product List ü Approved Product List posted at http: //fips 201 ep. cio. gov/ • GSA/NIST identified 24 categories of products/services which must comply with specific normative requirements contained in FIPS 201 ü e. g. , PIV smart cards, smart card readers, fingerprint scanners, fingerprint capture stations, facial image capture stations, card printing stations, etc. • Current product and services approvals: ü 300+ products on FIPS 201 Approved Product List • Current certified labs: ü Atlan Laboratories, Info. Gard Laboratories ü Several more lab certifications in progress 13
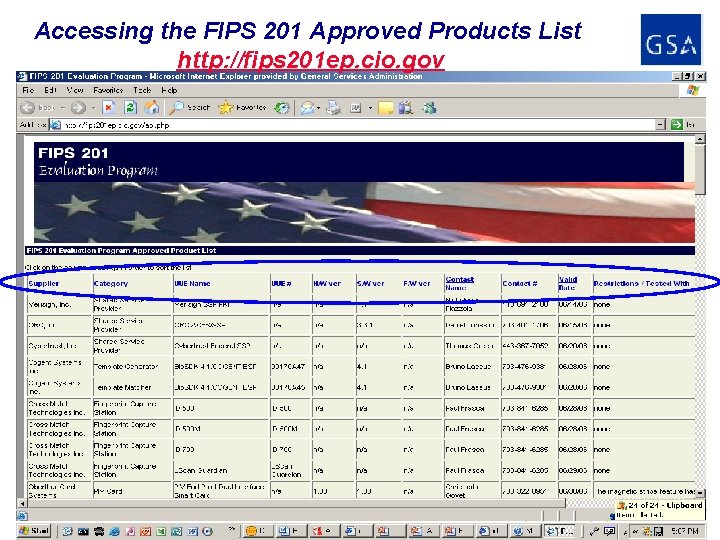
Accessing the FIPS 201 Approved Products List http: //fips 201 ep. cio. gov 14
Where are we today? • 12+ agencies committed to their own infrastructure: ü DHS, Do. D, NASA, SSA, EPA, FTC, Dept. of State, VA, HHS, ED, DOL, NSF, • 100+ Agencies want to share infrastructure ü All small agencies ü DOC, HUD, USDA, DOJ, DOI, GSA, DOE, DOT, Treasury, OPM, Federal Reserve, USPS, NARA, FCC committed • Shared Service Providers ü Do. D/DMDC – for branches of military ü Dept. of State -- 8 agencies serviced by State Dept. ü GSA for government-wide services – 70+ agencies • GSA Roll-out ü Shared Service pricing released 6/8/07 -- $49/seat for enrollment, $36/year for maintenance ü GSA implemented enrollment station roll-out for national deployment starting in Washington DC in August 2007. ü Goal is to deploy 225 shared enrollment stations nationwide and enroll all MSO customers (800, 000 +) by October 2008. 15
Conclusion • • This is the THE START … surface is only scratched There is much work … • • • Roll-out hundreds of enrollment stations nationwide Issue to all users by October 2008 Test and Certify systems Build common applications for access control and e-Government Stabilize operations … • Commitment to continue issuance • Protect and promote interoperability • Government procurement rules provide discipline • Extend to other communities – Leverage infrastructure • First responders, Health Care, State and local governments. • Transportation workers (TWIC), trusted traveler programs 16
For More Information ● Visit our Websites: http: //www. idmanagement. gov http: //www. Fed. IDCard. gov http: //www. cio. gov/ficc http: //www. csrc. nist. gov/piv-project ● Or contact: David Temoshok Director, Identity Policy and Management 202 -208 -7655 david. temoshok@gsa. gov 17