Federal Aviation Administration NAS Enterprise Information System Security
- Slides: 33
Federal Aviation Administration NAS Enterprise Information System Security (NEISS) Vic Patel, FAA ICAP, ACP WG-I May 28 th – 30 th
Agenda • Why do we need NEISS • NEISS described • Current status/activities • Future plans ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 2
Introduction • The NAS Enterprise Information Systems Security (NEISS) Program – Seeks to implement a NAS Security Architecture that is based on Enterprise or “Common” Controls rather than the current system-by-system controls – All NAS and Next. Gen Programs interface to and use the Common Controls to gain the mitigation benefits – The five Common Controls that comprise NEISS ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 3
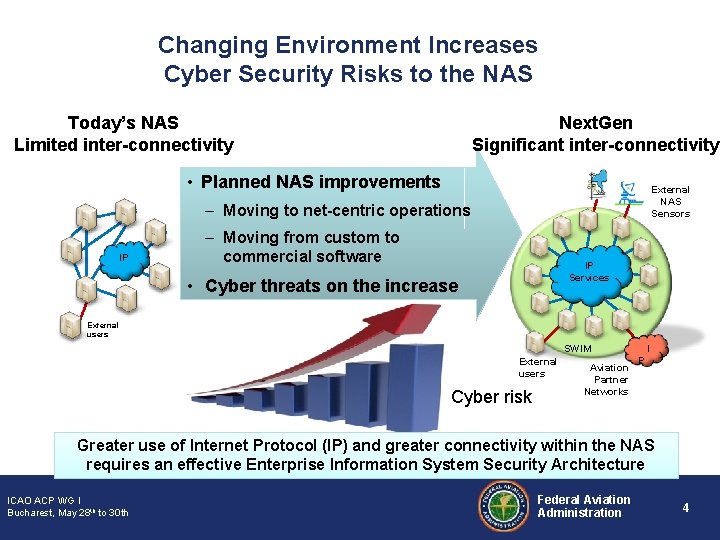
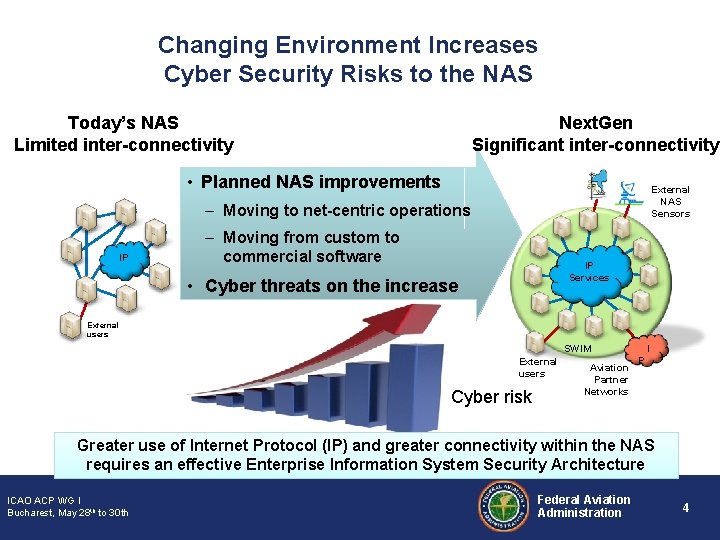
Changing Environment Increases Cyber Security Risks to the NAS Today’s NAS Limited inter-connectivity Next. Gen Significant inter-connectivity • Planned NAS improvements External NAS Sensors – Moving to net-centric operations IP – Moving from custom to commercial software IP Services • Cyber threats on the increase External users SWIM External users Cyber risk Aviation Partner Networks I P Greater use of Internet Protocol (IP) and greater connectivity within the NAS requires an effective Enterprise Information System Security Architecture ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 4
Potential Impacts to NAS Are Serious • Major disruption of NAS services possible – Malware can enter the NAS accidently – The NAS can be targeted • Disruption cause substantial economic loss • Loss of public confidence in the NAS • NAS disruption can interfere with logistical support of military missions ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 5
The Threat • Cyber exploitation activity has – Grown more sophisticated – More targeted – And more serious • The intelligence community has concluded that nation states – Have the technical capabilities to • • • Target and disrupt elements of the US information infrastructure Collect intelligence information for future use against the US Stux. Net – Specifically targeted an Industrial Control System similar to NAS ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 6
The Challenge It’s hard to keep them out When they get in, it’s hard to find them When we find them, it’s hard to get them out ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 7
What Can We Do? • Understand the threat – Characterize the NAS cyber threat environment – Identify tools, techniques, and procedures used by adversaries • Lay a solid foundation – Develop core Enterprise Solutions that position the NAS to deal with an ever increasing problem • Be agile – Develop techniques and approaches useful for defending and countering cyber attacks – Developing and enforcing Enterprise Solutions that can quickly adapt to the changing threat environment and apply to all NAS systems • Be resilient – Adopt approaches for continued operations during cyber attacks ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 8
The Plan: NAS Enterprise Information System Security • NAS ISS architecture was developed to provide a foundational cyber infrastructure for NAS enterprise security beginning now and continuing through Next. Gen • Doable in five years - Enterprise-wide solutions - Minimal end-system changes - Expand existing program solutions where applicable • Flexible and Scalable - Security solutions can vary over time. • NAS ISS architecture will allow: - Improvements in security technology ICAO ACP WG I - New to 30 th security features Bucharest, May 28 th Federal Aviation Administration 9
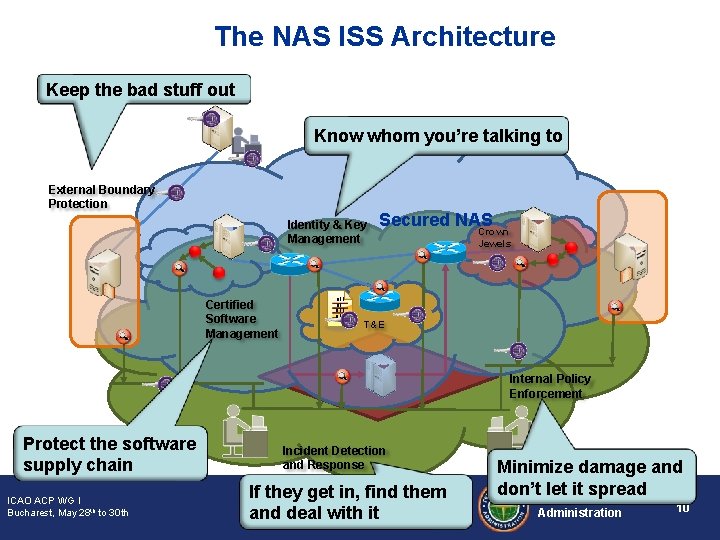
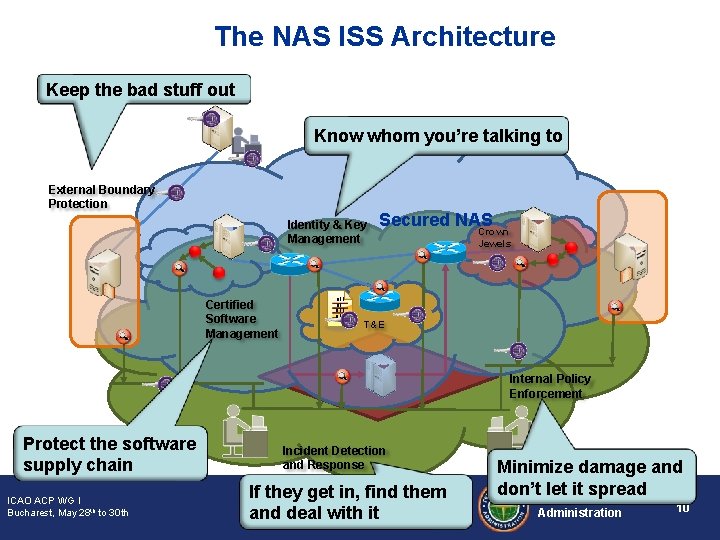
The NAS ISS Architecture Keep the bad stuff out Know whom you’re talking to External Boundary Protection Identity & Key Management Certified Software Management 011 01 Secured NAS Crown Jewels T&E Internal Policy Enforcement Protect the software supply chain ICAO ACP WG I Bucharest, May 28 th to 30 th Incident Detection and Response If they get in, find them and deal with it Minimize damage and don’t let it spread Federal Aviation Administration 10
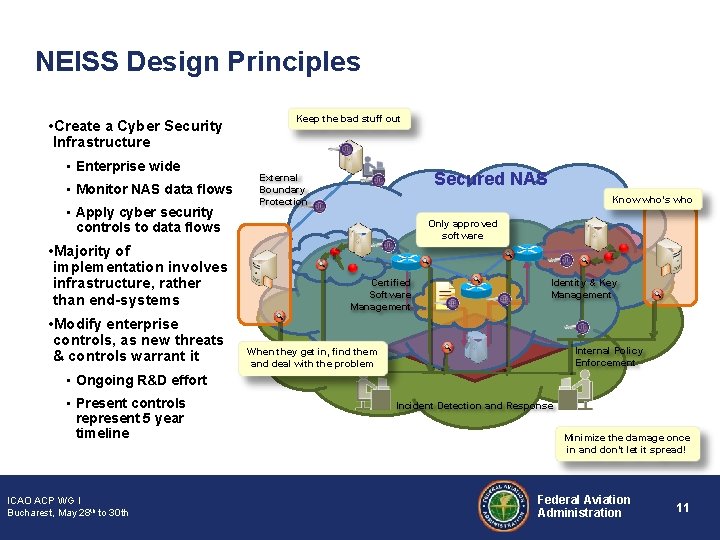
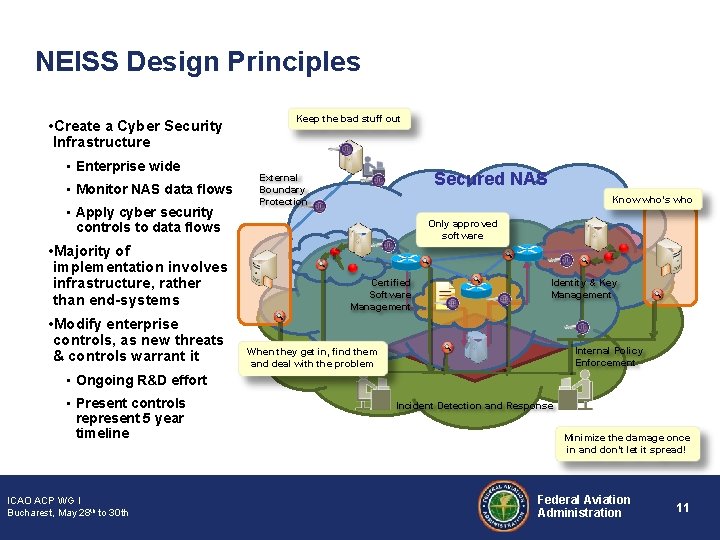
NEISS Design Principles • Create a Cyber Security Infrastructure • Enterprise wide • Monitor NAS data flows • Apply cyber security controls to data flows • Majority of implementation involves infrastructure, rather than end-systems • Modify enterprise controls, as new threats & controls warrant it Keep the bad stuff out Secured NAS External Boundary Protection Know who’s who Only approved software Certified Software Management Identity & Key Management Internal Policy Enforcement When they get in, find them and deal with the problem • Ongoing R&D effort • Present controls represent 5 year timeline ICAO ACP WG I Bucharest, May 28 th to 30 th Incident Detection and Response Minimize the damage once in and don’t let it spread! Federal Aviation Administration 11
Under the Hood: What’s Happening in NEISS ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 12
Why a NAS Enterprise Information System Security (ISS) Architecture Is Needed (I) • Growing and evolving cyber security threats – Cyber terrorism, cyber crime, cyber vandalism, cyber espionage, cyber war • Evolution to support and enable Next. Gen – Increased levels of network connectivity (from point-to-point to net-centricity) – Newer technologies (satellite-based surveillance and navigation) – Increased complexity from interoperability needs (legacy systems and Next. Gen implementation) • Security is based around individual systems – Non-uniform security, the weakest link paradigm applies – Costly to implement – Individual system security never intended to mitigate the advanced threats ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 13
Why a NAS Enterprise Information System Security (ISS) Architecture Is Needed (II) • Architecture Provides – Uniform and enterprise cyber security capabilities – Layered cyber security capabilities (defense-in-depth) – Robust, resilient, agile and scalable cyber security capabilities – Incremental approach ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 14
Why a NAS Enterprise Information System Security (ISS) Architecture Is Needed (III) • Benefits – Protect the NAS from malware and advance cyber threats Organized crime, terrorist organizations, foreign governments – Provide better opportunities to leverage net-centric services for security – Greater network connectivity, newer technologies, greater complexity – Provide uniform enterprise cyber security capabilities • Reduce complexity, weakest link paradigm – Reduce implementation costs • One enterprise implementation vs. each system’s implementation NEISS will be responsible for the implementation of the NAS EA ISS roadmap ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 15
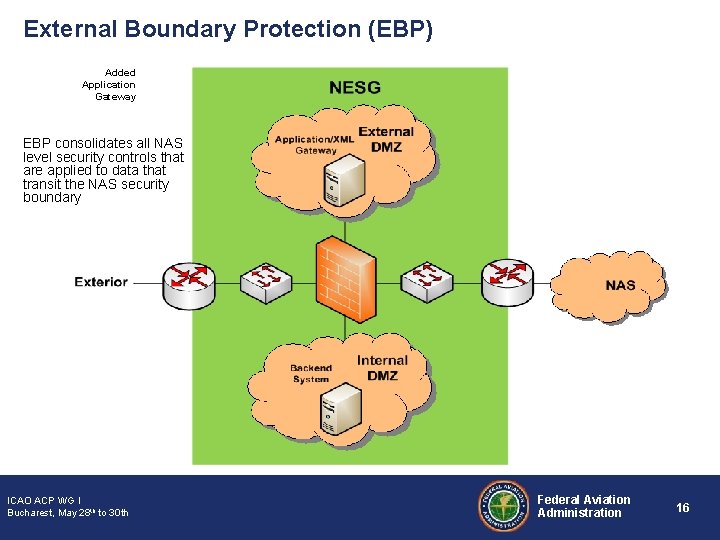
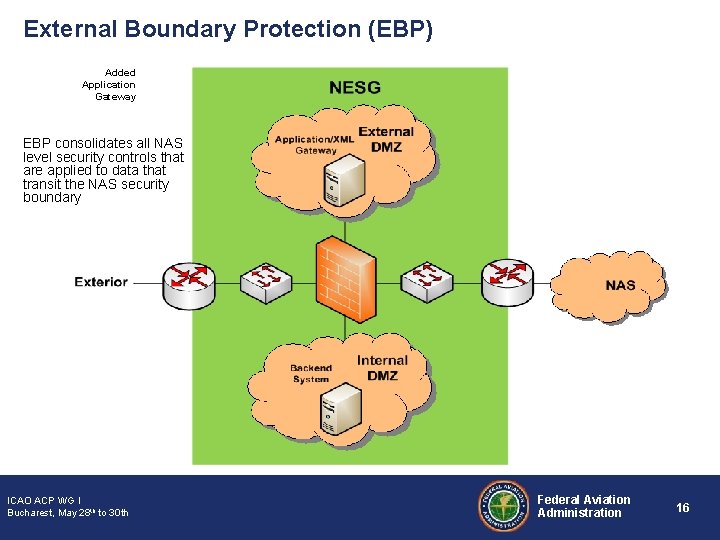
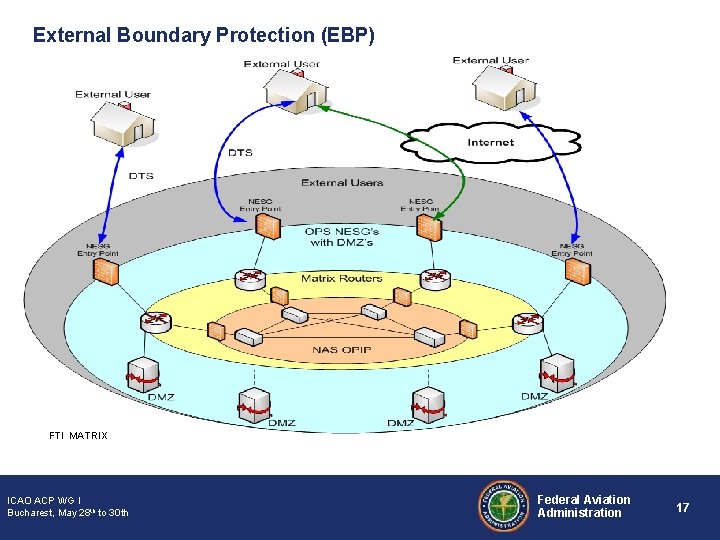
External Boundary Protection (EBP) Added Application Gateway EBP consolidates all NAS level security controls that are applied to data that transit the NAS security boundary ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 16
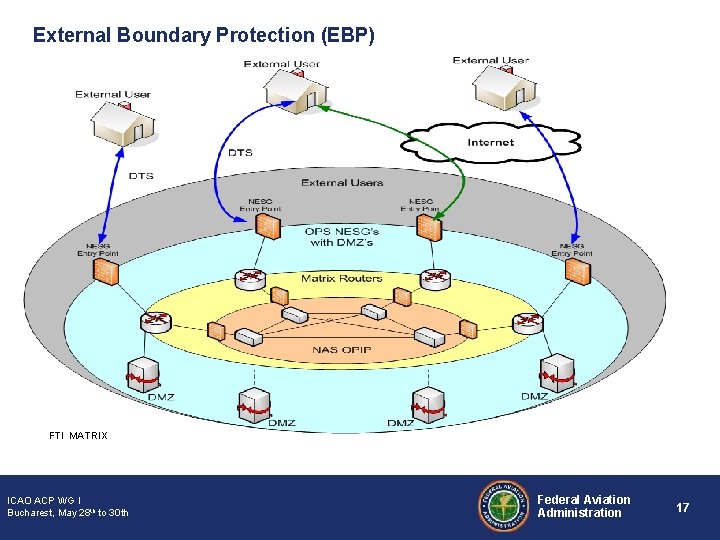
External Boundary Protection (EBP) FTI MATRIX ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 17
External Boundary Protection (EBP) Status • Developing AMS artifacts supporting EBP • Working with SWIM and FTI to implement early capability centered around the NAS Enterprise Security Gateway (NESG) • Conducting the Operational Safety Assessment • Future Activities: – – Transition strategy Governance Guidance FY 13 Legacy NAS transition candidates ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 18
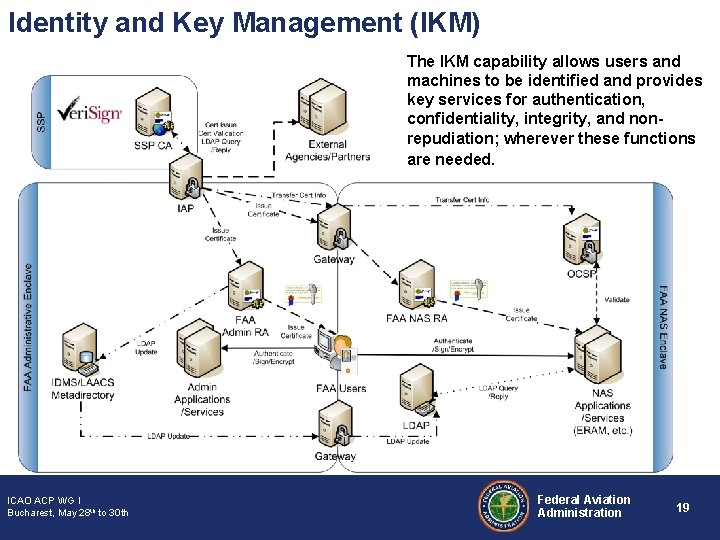
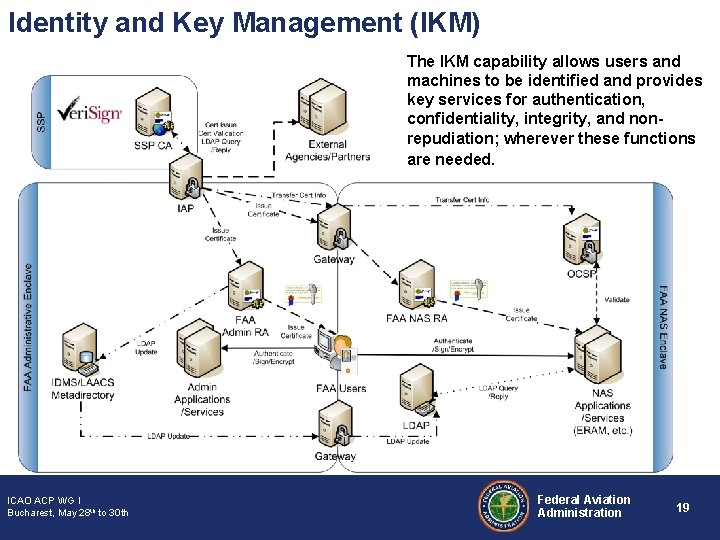
Identity and Key Management (IKM) The IKM capability allows users and machines to be identified and provides key services for authentication, confidentiality, integrity, and nonrepudiation; wherever these functions are needed. ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 19
Identity and Key Management (IKM) - cont • • • Status: Actively Developing Requirements Implementer: SWIM Accomplishments: – Defined IKM requirements in SWIM S 2 FPR, – OSA data collection complete, – Leading implementation of IKM in SWIM Segment 1+ • • Future Activities: Implement in test bed the four phase approach regarding integration with legacy systems. Issues: – Need clarity on allocation of some IKM functions, including Security Token Service – Selection of early adopters – Policy/Standards needed ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 20
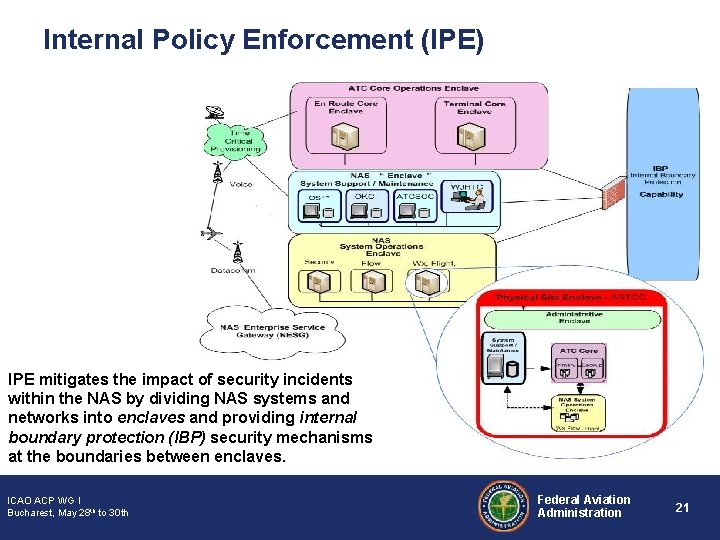
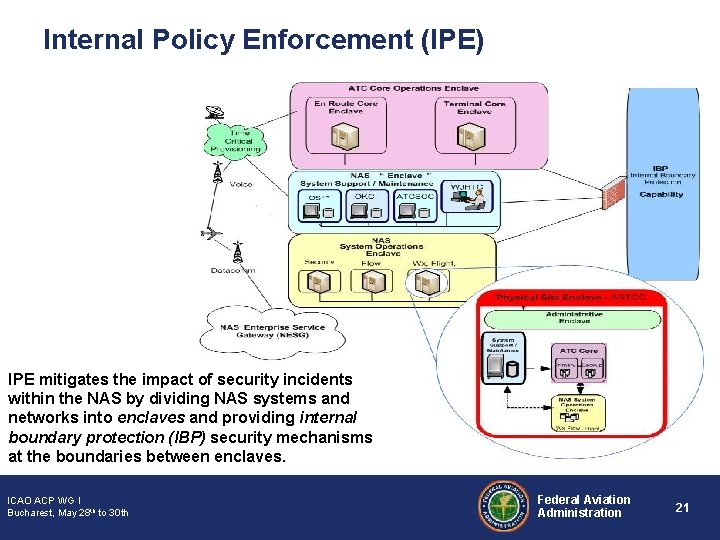
Internal Policy Enforcement (IPE) IPE mitigates the impact of security incidents within the NAS by dividing NAS systems and networks into enclaves and providing internal boundary protection (IBP) security mechanisms at the boundaries between enclaves. ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 21
Internal Policy Enforcement (IPE) - cont • • Status: Engineering new environment Implementer: NEISS Accomplishments: Defined Enclave Environment Future Activities: – Prototype IPE in test bed. – Implement IPE in legacy environment utilizing a four step approach. – Solicit support from different lines of business to test IPE design in and design secondary network for data transmission if enclave is compromised. • Issues: Concern with cost for possible secondary form of data transmission. ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 22
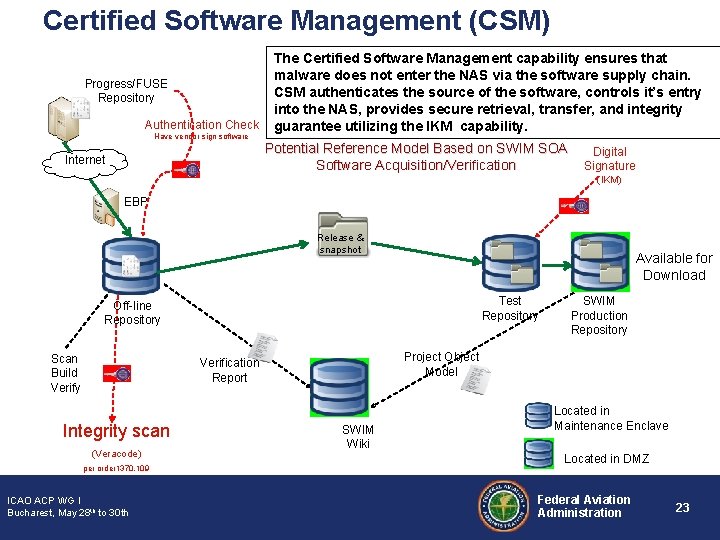
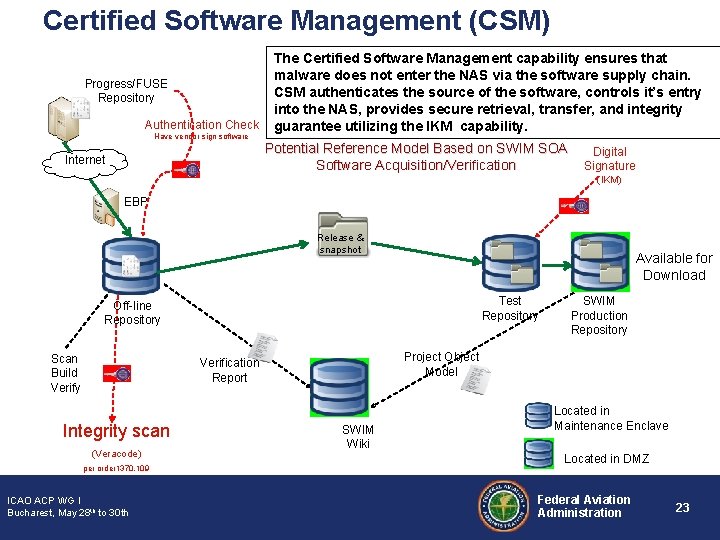
Certified Software Management (CSM) Progress/FUSE Repository Authentication Check Have vendor sign software Internet The Certified Software Management capability ensures that malware does not enter the NAS via the software supply chain. CSM authenticates the source of the software, controls it’s entry into the NAS, provides secure retrieval, transfer, and integrity guarantee utilizing the IKM capability. Potential Reference Model Based on SWIM SOA Digital Software Acquisition/Verification Signature (IKM) EBP Release & snapshot Available for Download Test Repository Off-line Repository Scan Build Verify Project Object Model Verification Report Integrity scan (Veracode) per order 1370. 109 ICAO ACP WG I Bucharest, May 28 th to 30 th SWIM Production Repository SWIM Wiki Located in Maintenance Enclave Located in DMZ Federal Aviation Administration 23
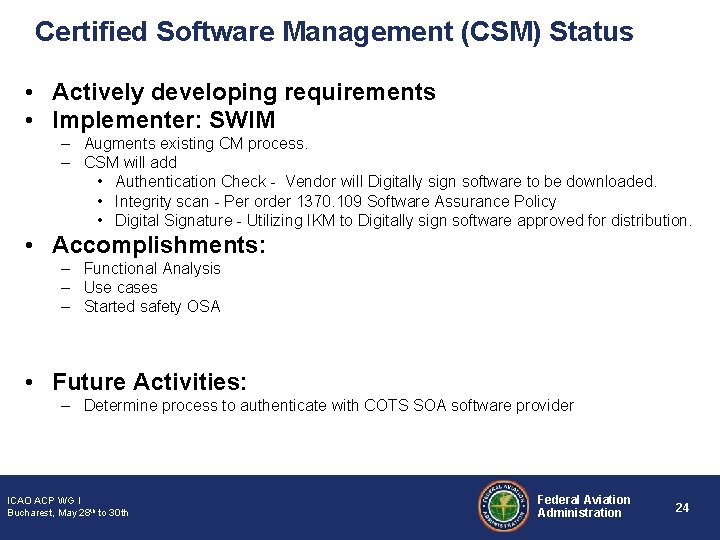
Certified Software Management (CSM) Status • Actively developing requirements • Implementer: SWIM – Augments existing CM process. – CSM will add • Authentication Check - Vendor will Digitally sign software to be downloaded. • Integrity scan - Per order 1370. 109 Software Assurance Policy • Digital Signature - Utilizing IKM to Digitally sign software approved for distribution. • Accomplishments: – Functional Analysis – Use cases – Started safety OSA • Future Activities: – Determine process to authenticate with COTS SOA software provider ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 24
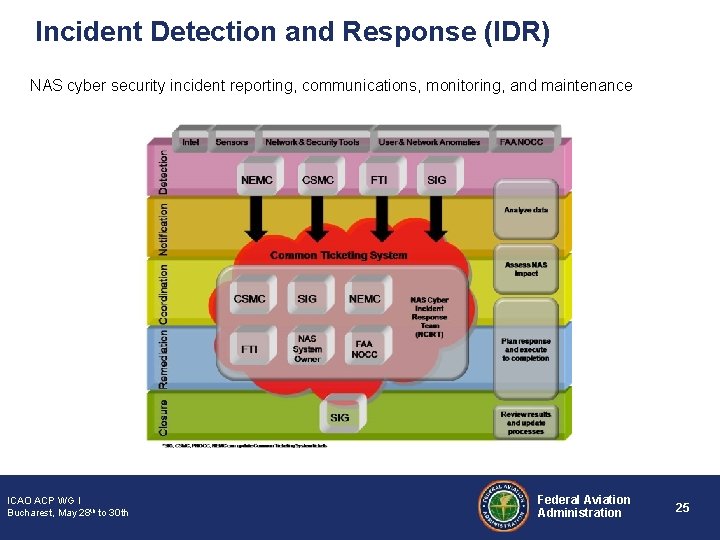
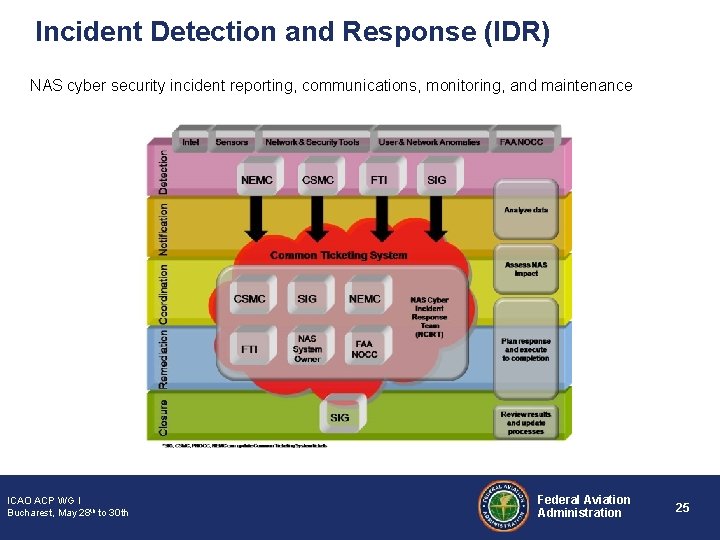
Incident Detection and Response (IDR) NAS cyber security incident reporting, communications, monitoring, and maintenance ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 25
Incident Detection and Response (IDR) • Status: Policy Development • Update of CONUSE and Functional Analysis Documents • Implementer: NEISS IDR • Accomplishments: • CEMWG was established to formalize/combine process of handling NAS cyber events • Drafted IDR Policy and SOP • OSA draft complete ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 26
Incident Detection and Response (IDR) Future Activities: • Completion of Policy and SOP • Continuous update of the supporting documents as we evolve • Validation of SOPs • Issues: • AMS process time – Training and resources needed • Technology – Tech changes and advancements • Use of automated tools for data and traffic flows to detect anomalies ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 27
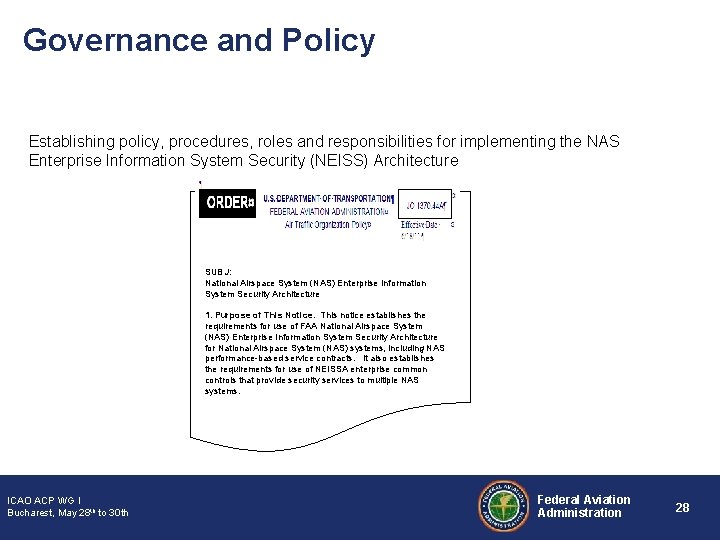
Governance and Policy Establishing policy, procedures, roles and responsibilities for implementing the NAS Enterprise Information System Security (NEISS) Architecture SUBJ: National Airspace System (NAS) Enterprise Information System Security Architecture 1. Purpose of This Notice. This notice establishes the requirements for use of FAA National Airspace System (NAS) Enterprise Information System Security Architecture for National Airspace System (NAS) systems, including NAS performance-based service contracts. It also establishes the requirements for use of NEISSA enterprise common controls that provide security services to multiple NAS systems. ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 28
Governance and Policy - cont • Status: Actively Drafting Policy – – Extending Notice JO 1370. 44 to include enterprise ISS and current NIST guidance Working with FAA’s CIO Offices on incorporating ISS in AMS life cycle • Accomplishments: Annotated outline • Future Activities: – First full draft expected early January 2011 – Identify and integrate Enterprise ISS in JRC checklist • Issues: Balancing specificity and clarity against length ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 29
NEISS Challenges • Disposition of the NAS Enterprise ISS requirements – Need a way to resolve and approve changes (particularly deletion) and implementation of NEISS requirements • Conveying an understanding of the NEISS – Threat/risk motivation – Understanding capabilities – Programs need to be clear on when and how to adapt to NEISS • Schedule, Funding, Requirements • ISS architecture governance – What are the Rules (Policy)? – Who are the Gatekeepers? • Establishing NEISS priority and importance – Urgency – Early funding • Coordinating across the many stakeholders – Nearly everyone in the NAS/Next. Gen is a stakeholder – All need attention ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 30
ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 31
Backup Slides ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 32
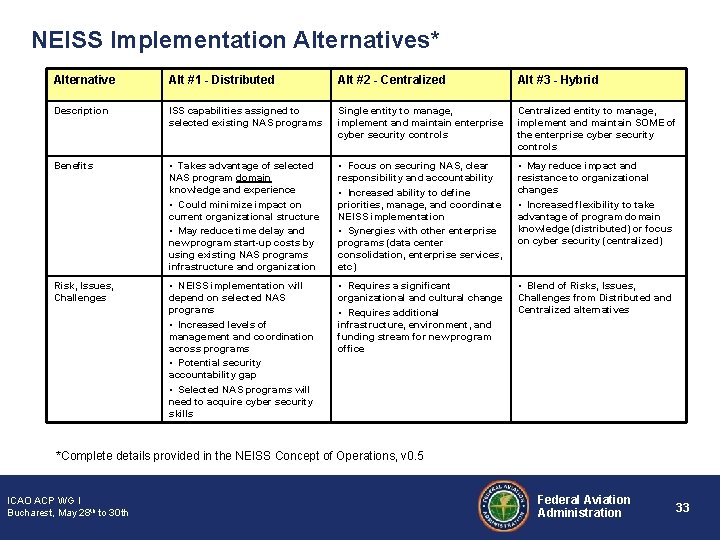
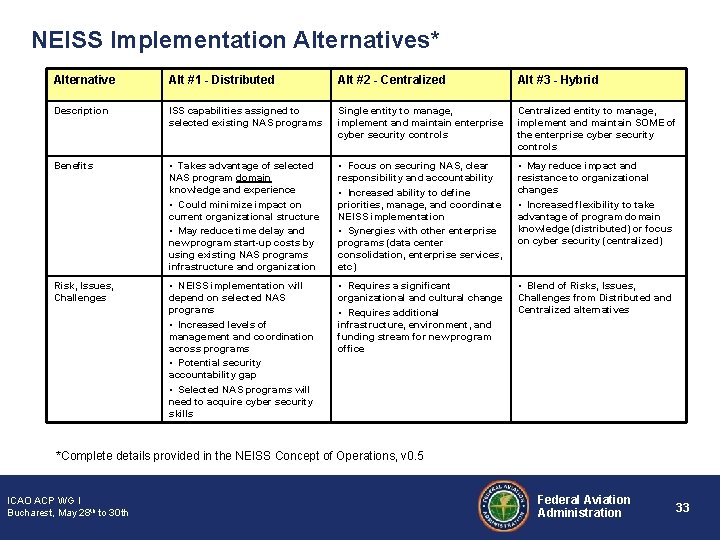
NEISS Implementation Alternatives* Alternative Alt #1 - Distributed Alt #2 - Centralized Alt #3 - Hybrid Description ISS capabilities assigned to selected existing NAS programs Single entity to manage, implement and maintain enterprise cyber security controls Centralized entity to manage, implement and maintain SOME of the enterprise cyber security controls Benefits • Takes advantage of selected NAS program domain knowledge and experience • Could minimize impact on current organizational structure • May reduce time delay and new program start-up costs by using existing NAS programs infrastructure and organization • Focus on securing NAS, clear responsibility and accountability • Increased ability to define priorities, manage, and coordinate NEISS implementation • Synergies with other enterprise programs (data center consolidation, enterprise services, etc) • May reduce impact and resistance to organizational changes • Increased flexibility to take advantage of program domain knowledge (distributed) or focus on cyber security (centralized) Risk, Issues, Challenges • NEISS implementation will depend on selected NAS programs • Increased levels of management and coordination across programs • Potential security accountability gap • Selected NAS programs will need to acquire cyber security skills • Requires a significant organizational and cultural change • Requires additional infrastructure, environment, and funding stream for new program office • Blend of Risks, Issues, Challenges from Distributed and Centralized alternatives *Complete details provided in the NEISS Concept of Operations, v 0. 5 ICAO ACP WG I Bucharest, May 28 th to 30 th Federal Aviation Administration 33