Federal Approach to Electronic Credentials For services to


- Slides: 28
Federal Approach to Electronic Credentials For services to citizens, businesses, other governments, and employees AFCEA January 23, 2002 1/24/2022 Mary J. Mitchell Office of Electronic Government mary. mitchell@gsa. gov 202 501 -7092 web: egov. gov
E-Government Management Initiative Vision: Deliver an order of magnitude improvement in the government’s value to the citizen Integral Part of President’s Management Agenda Definition: Using digital technologies to transform government operations in order to improve effectiveness, efficiency, and service delivery. The Principles: r Citizen-centric, Market-based, Results-oriented r Simplify and Unify 1/24/2022
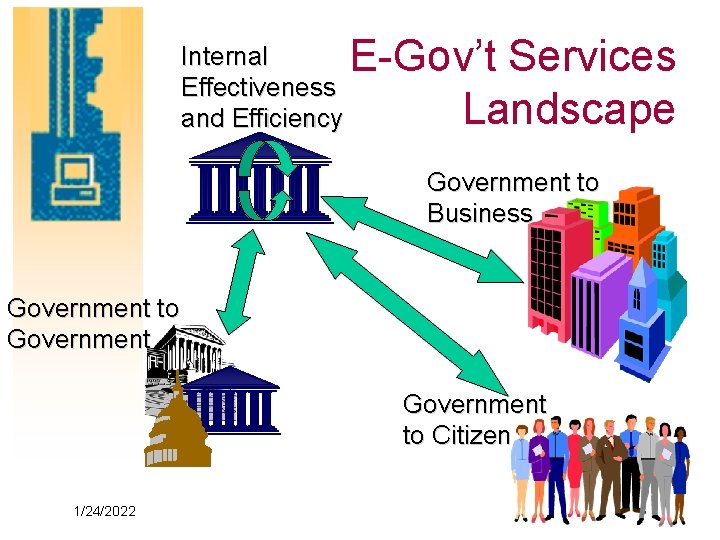
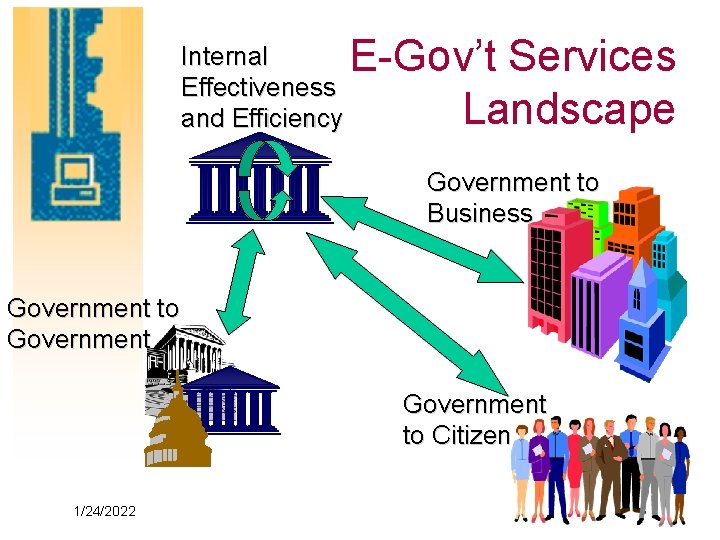
Internal Effectiveness and Efficiency E-Gov’t Services Landscape Government to Business Government to Citizen 1/24/2022
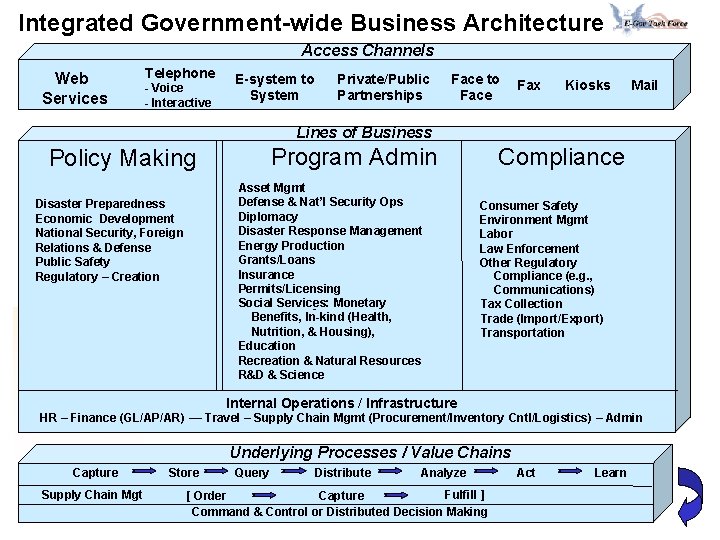
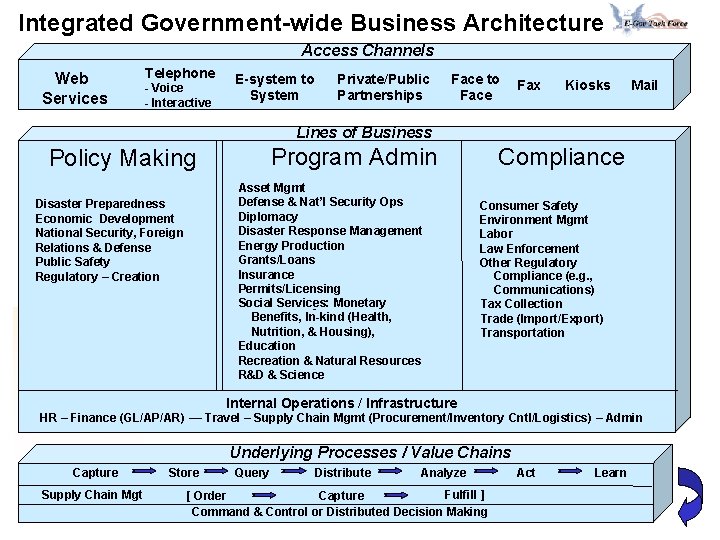
Integrated Government-wide Business Architecture Access Channels Web Services Telephone - Voice - Interactive E-system to System Private/Public Partnerships Face to Face Fax Kiosks Mail Lines of Business Program Admin Policy Making Asset Mgmt Defense & Nat’l Security Ops Diplomacy Disaster Response Management Energy Production Grants/Loans Insurance Permits/Licensing Social Services: - Monetary Benefits, In-kind (Health, Nutrition, & Housing), Education Recreation & Natural Resources R&D & Science Disaster Preparedness Economic Development National Security, Foreign Relations & Defense Public Safety Regulatory – Creation Compliance Consumer Safety Environment Mgmt Labor Law Enforcement Other Regulatory Compliance (e. g. , Communications) Tax Collection Trade (Import/Export) Transportation Internal Operations / Infrastructure HR – Finance (GL/AP/AR) –– Travel – Supply Chain Mgmt (Procurement/Inventory Cntl/Logistics) – Admin Underlying Processes / Value Chains Capture Supply Chain Mgt 1/24/2022 Store Query Distribute Analyze Fulfill ] [ Order Capture Command & Control or Distributed Decision Making Act Learn
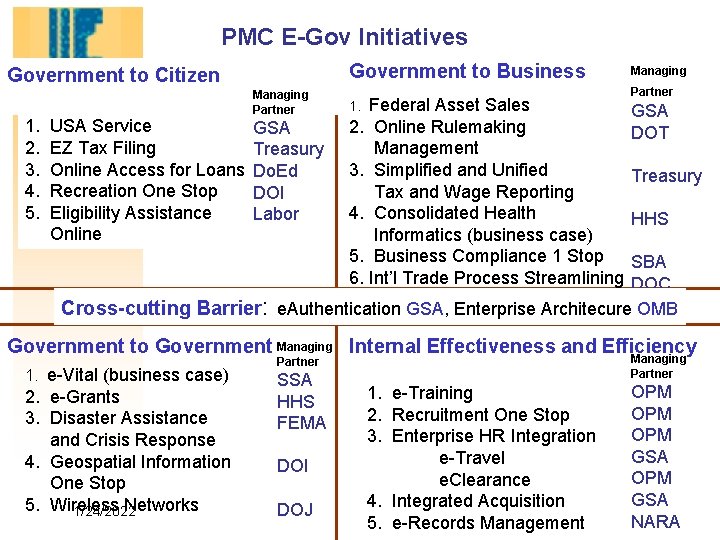
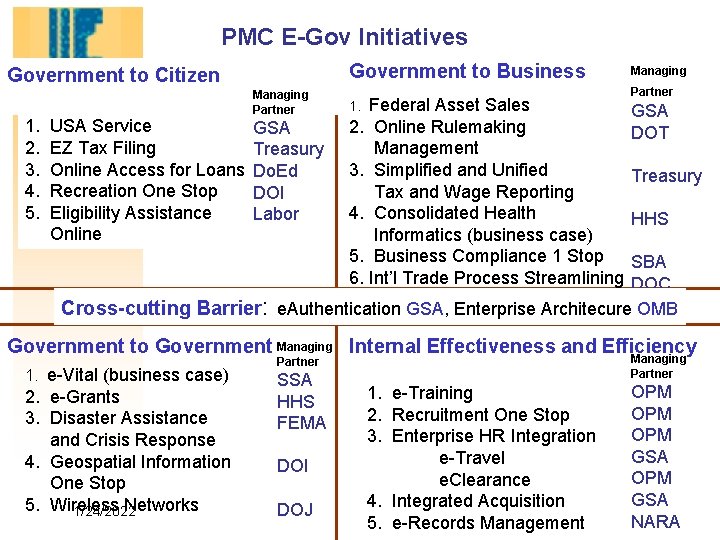
PMC E-Gov Initiatives Government to Business Government to Citizen 1. 2. 3. 4. 5. USA Service EZ Tax Filing Online Access for Loans Recreation One Stop Eligibility Assistance Online Managing Partner GSA Treasury Do. Ed DOI Labor Federal Asset Sales 2. Online Rulemaking Management 3. Simplified and Unified Tax and Wage Reporting 4. Consolidated Health Informatics (business case) 5. Business Compliance 1 Stop 6. Int’l Trade Process Streamlining 1. Managing Partner GSA DOT Treasury HHS SBA DOC Cross-cutting Barrier: e. Authentication GSA, Enterprise Architecure OMB Government to Government Managing Internal Effectiveness and Efficiency 1. e-Vital (business case) 2. e-Grants 3. Disaster Assistance and Crisis Response 4. Geospatial Information One Stop 5. Wireless Networks 1/24/2022 Managing Partner SSA HHS FEMA DOI DOJ 1. e-Training 2. Recruitment One Stop 3. Enterprise HR Integration e-Travel e. Clearance 4. Integrated Acquisition 5. e-Records Management OPM OPM GSA NARA
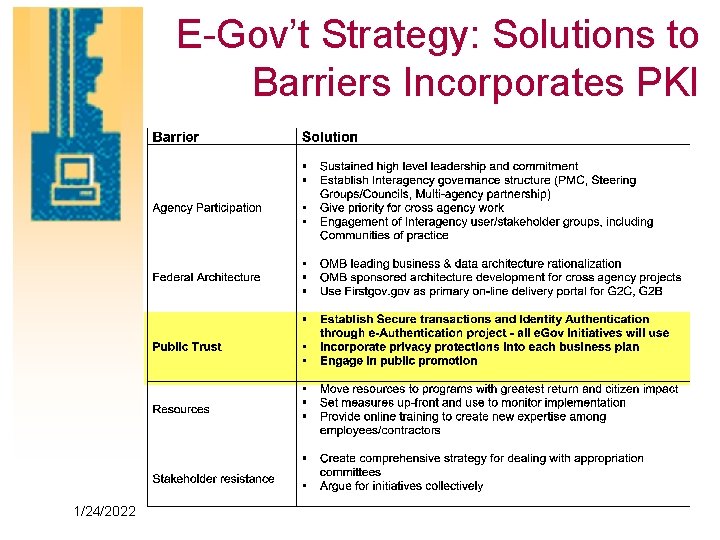
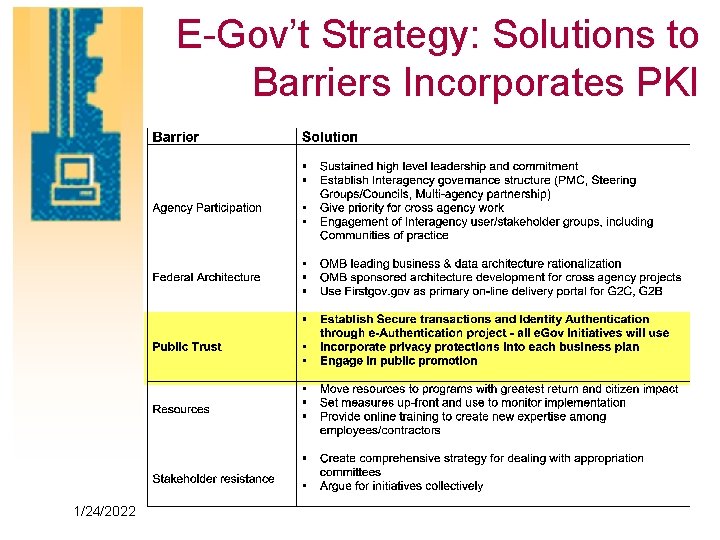
E-Gov’t Strategy: Solutions to Barriers Incorporates PKI 1/24/2022
Trust Online Is Critical • Trust is the belief that Privacy and Security are being provided • Demand that Recourse be available if something goes wrong • Trust is aligned with Brand or Name Recognition • Consumers want Accountability, Ease of Use, and Responsiveness • Businesses want clearly assigned 1/24/2022 Responsibility and Liability
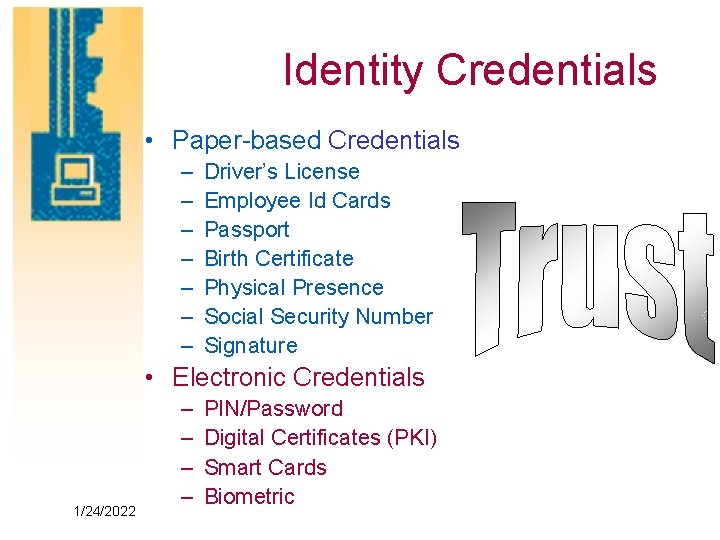
Identity Credentials • Paper-based Credentials – – – – Driver’s License Employee Id Cards Passport Birth Certificate Physical Presence Social Security Number Signature • Electronic Credentials 1/24/2022 – – PIN/Password Digital Certificates (PKI) Smart Cards Biometric
When Do Web Interactions Need Authentication Whenever Operations Exceed Risk Threshold • Privacy protection - Knowing whom you are dealing prior to disclosing “sensitive” data • User Authentication – Knowing who your correspondent is • Transaction Integrity - Ensuring the message sent is the message received • Non-Repudiation – Correspondent cannot deny conducting transaction • Confidentiality 1/24/2022 – Only authorized persons can read the message
Managing Risk • Agencies must assess security risk • Three primary risks: – Improper disclosure – Program fraud – Image of the Agency • Determining transaction risk 1/24/2022 – Recommend an “appropriate” authentication mechanism for a given transaction – Examine transaction flow and vulnerabilities – Provide rough cost estimates
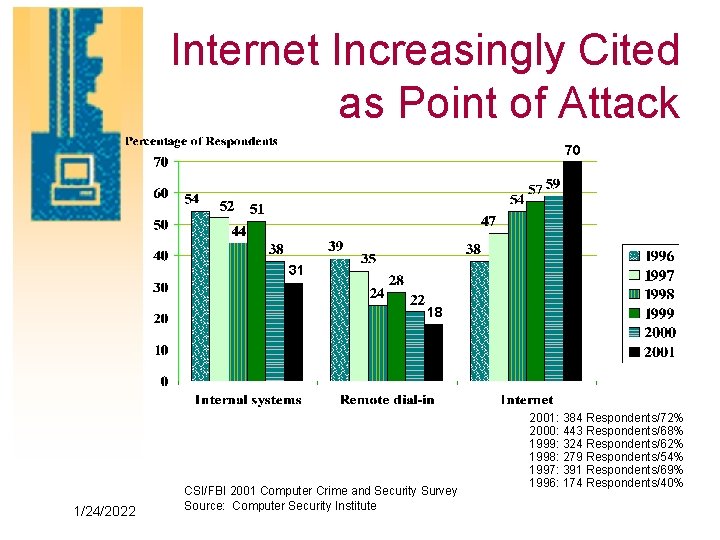
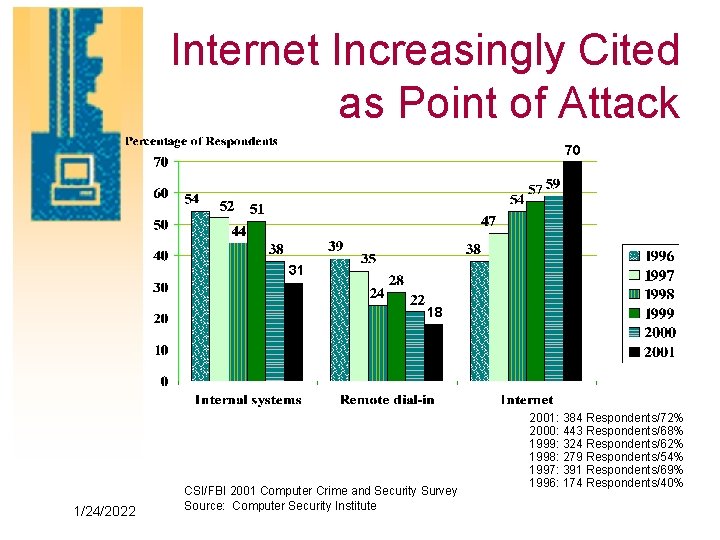
Internet Increasingly Cited as Point of Attack 70 31 18 1/24/2022 CSI/FBI 2001 Computer Crime and Security Survey Source: Computer Security Institute 2001: 384 Respondents/72% 2000: 443 Respondents/68% 1999: 324 Respondents/62% 1998: 279 Respondents/54% 1997: 391 Respondents/69% 1996: 174 Respondents/40%
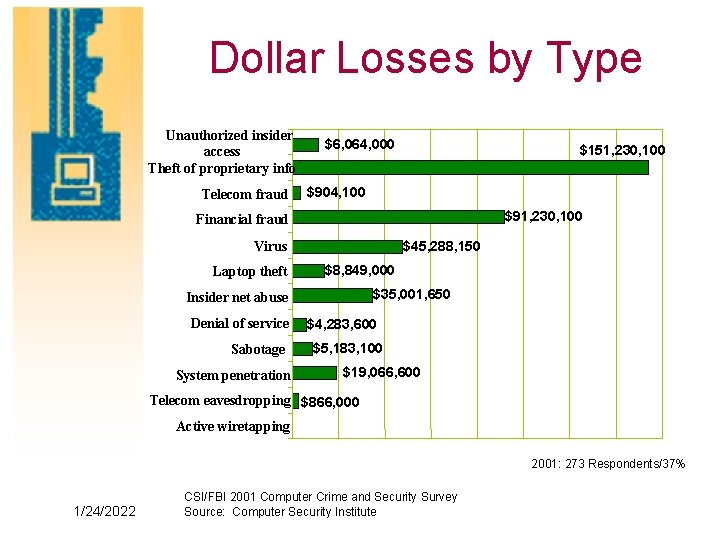
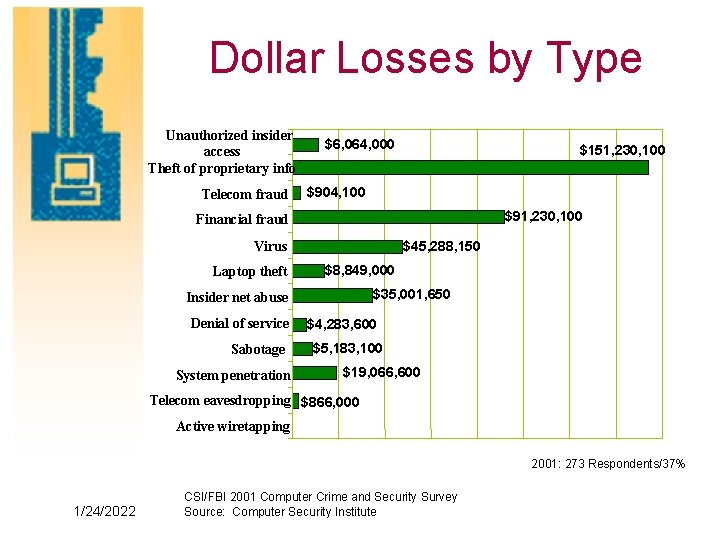
Dollar Losses by Type Unauthorized insider access Theft of proprietary info Telecom fraud $6, 064, 000 $151, 230, 100 $904, 100 $91, 230, 100 Financial fraud Virus Laptop theft $45, 288, 150 $8, 849, 000 $35, 001, 650 Insider net abuse Denial of service Sabotage System penetration $4, 283, 600 $5, 183, 100 $19, 066, 600 Telecom eavesdropping $866, 000 Active wiretapping 2001: 273 Respondents/37% 1/24/2022 CSI/FBI 2001 Computer Crime and Security Survey Source: Computer Security Institute
PMC e. Authentication Initiative • • • 1/24/2022 Simplify and Unify Will serve all of the PMC approved E-Gov Initiatives and eventually business lines Assist other E-Gov initiatives in defining their identity proofing and authentication needs e-Authentication will tie into Firstgov Develop applications and reusable toolkits for cross-governmental use Coordinate aggregated buy of authentication products and services Promote interoperability with other entities like the Federal Bridge Certificate Authority
Authentication ROI Study • Standard methodology for agencies to use in projecting ROI when deploying strong authentication • Synthesize findings from a comprehensive analysis of government and industry business cases and (ROI) studies • Implications of the different cost models • Delivery April 2002 1/24/2022
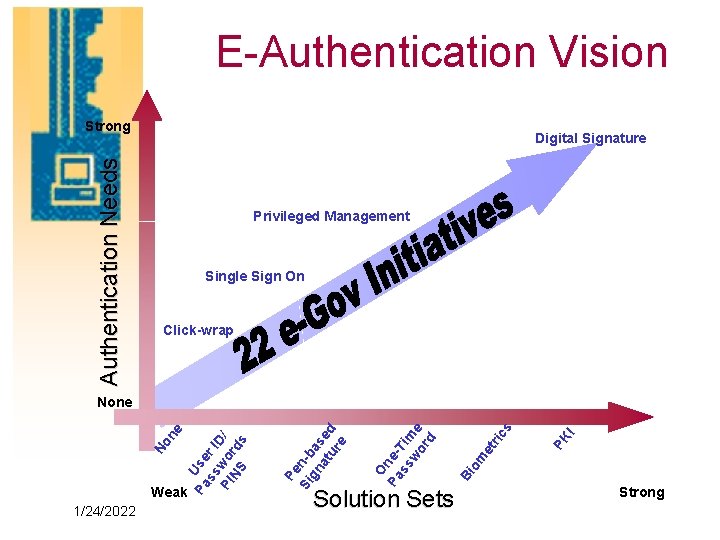
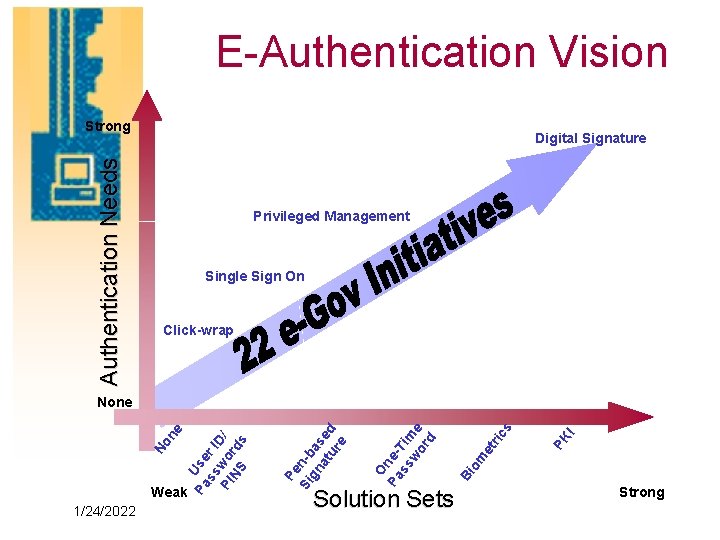
E-Authentication Vision Authentication Needs Strong Digital Signature Privileged Management Single Sign On Click-wrap 1/24/2022 PK I s ric et om Bi O Pa ness Tim wo e rd Weak Pe Si n-b gn as at ed ur e Pa Use ss r I D PI wo / NS rd s No ne None Solution Sets Strong
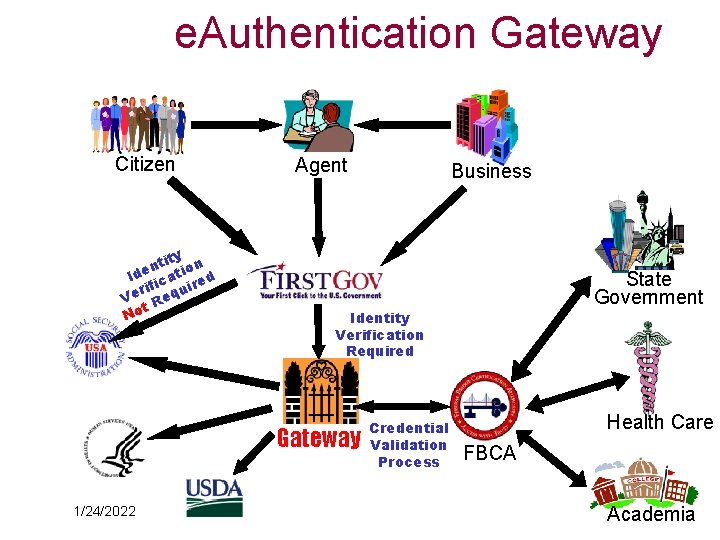
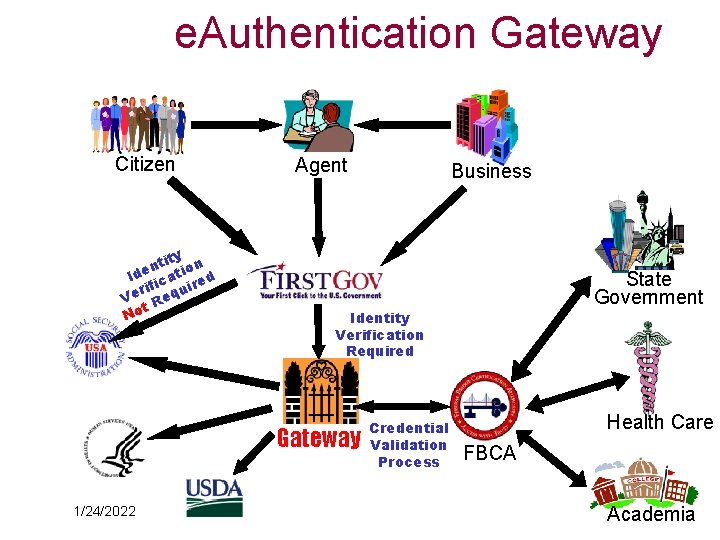
e. Authentication Gateway Citizen y tit on n Ide icati ed rif uir Ve Req t No Agent State Government Identity Verification Required Gateway 1/24/2022 Business Credential Validation Process Health Care FBCA Academia
Citizens Authentication is Particularly Challenging • Some populations (students, lowincome) lack sufficient means for identity proofing credit history, permanent address, etc. • Certain individuals object to divulging personal information (lack of trust in who and if adequately safeguarded) • Cost and administrative complexity of the certificate issuance 1/24/2022

Leverage Investments in Risk and Authentication • Social Security Administration – Risk Methodology and Privacy Board • Access Certificates for Electronic Services • Federal Bridge Certificate Authority – Other PKI efforts: www. cio. gov/fpkisc • Smart Common ID for employees • Other Agency and Alliance Partner 1/24/2022 – National Finance Center
ACES Concept • Common PKI solution encourages agencies to work together • Allows equitable cost sharing among agencies • Efficient, effective, economical due to aggregation of Federal needs • One digital identity credential can be used by multiple Agency processes • “Anonymous” certificate numbering for identification • Public pays nothing for digital ID. 1/24/2022
Nat’l Institute of Standards and Technology (NIST) 1/24/2022 • ACES used for the electronic submission and review of proposals for the Advanced Technology Program (ATP) • Uses digitally signed documents to send proprietary information over the Internet, digitally signs and encrypts forms, captures data and populates ATP database • Uses a web server for downloads/ submission of forms and documents, then pulls them behind NIST and ATP firewall • Pilot with 12 proposal submissions completed in Sept 2001 • Goes “live” for ATP’s FY 2002 competition
Social Security Administration (SSA) 1/24/2022 • Piloting ACES Digital Signature Certificates for on-line annual wage reporting • Following pilot, SSA had a 90 percent approval by the 100 businesses participating • Automating W-2 submissions critical to agency where nearly 6. 5 million employers submit over 240 million W-2 forms for their employees • Continuing to expand pilot capabilities and implementing digitally signed forms
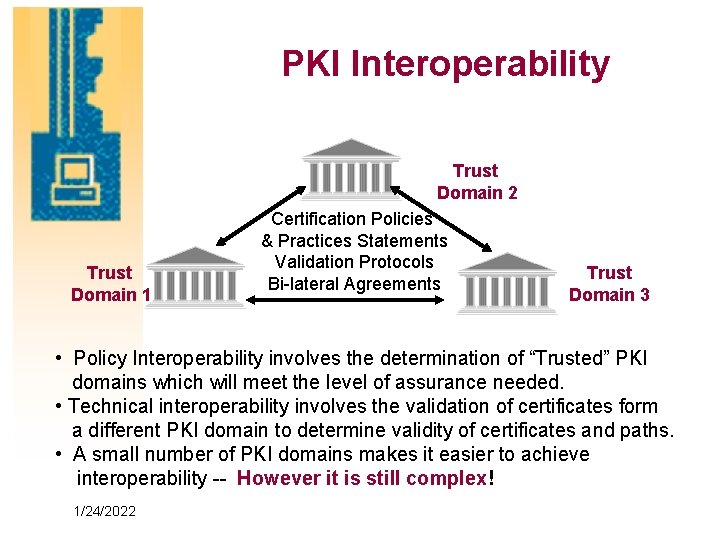
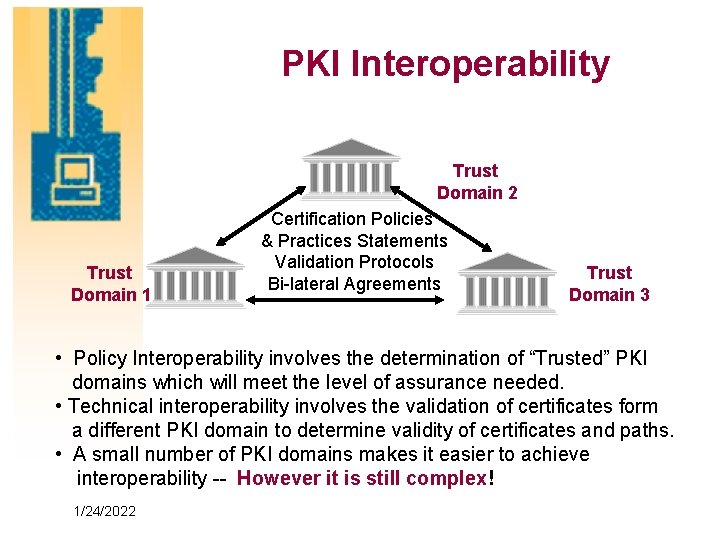
PKI Interoperability Trust Domain 2 Trust Domain 1 Certification Policies & Practices Statements Validation Protocols Bi-lateral Agreements Trust Domain 3 • Policy Interoperability involves the determination of “Trusted” PKI domains which will meet the level of assurance needed. • Technical interoperability involves the validation of certificates form a different PKI domain to determine validity of certificates and paths. • A small number of PKI domains makes it easier to achieve interoperability -- However it is still complex! 1/24/2022
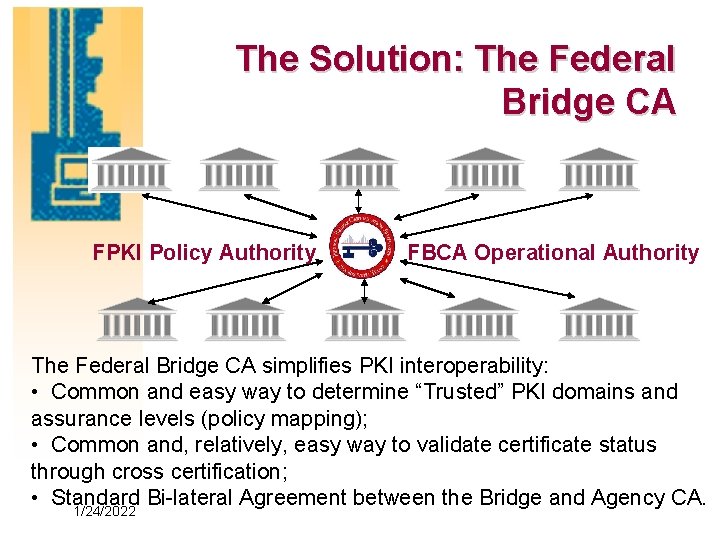
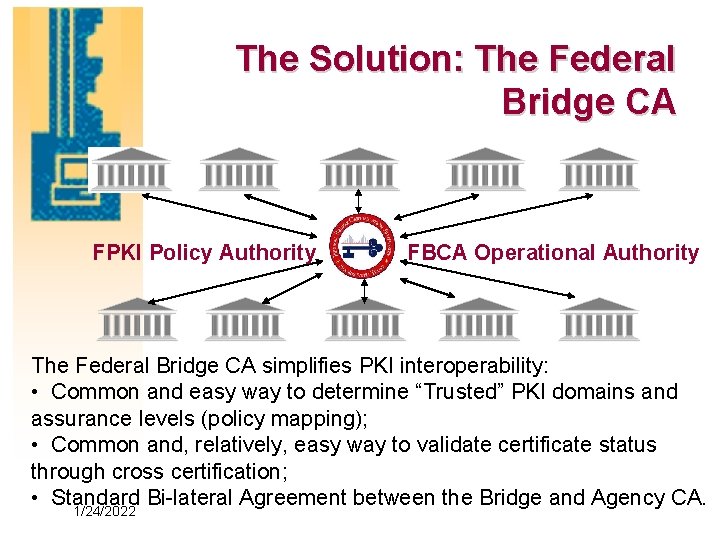
The Solution: The Federal Bridge CA FPKI Policy Authority FBCA Operational Authority The Federal Bridge CA simplifies PKI interoperability: • Common and easy way to determine “Trusted” PKI domains and assurance levels (policy mapping); • Common and, relatively, easy way to validate certificate status through cross certification; • Standard Bi-lateral Agreement between the Bridge and Agency CA. 1/24/2022
In the future, what role does PKI play? • e-Authentication initiative will organize authentication needs for critical government business lines • PKI is not the answer for all the needs • Cross-agency policy and support for interoperability exists for PKI but not for other authentication protocols • PKI for strong authentication addresses mandates such as HIPPA and e. Sign • Federal bridge CA facilitates unifying 1/24/2022 islands of automation
Smart Common ID Card Regional GSA Program • Issue Smart Cards to all Regional GSA Associates and Tenant Agencies –Uses Smart ID Card Specification –Phased approach w/program options –Central card management system • Federal Civic Center, Manhattan – Javits Federal Building (26 Federal Plaza) – 290 Broadway Federal Building – 209 Centre Street Garage • Future Phases: Other GSA Managed 1/24/2022 Buildings
Features/Services • Identification • Physical access • Logical access • Biometrics • Property control • Analysis, integration • Maintenance • Training • Testing Optional value-added services • Cryptographic services • Transit program • Electronic forms and digital signatures • Medical information • Electronic purse 1/24/2022

Smart Turnstiles • Open in ½ second • Anti-tailgating feature • Detect, deter and report unauthorized entry • High security glass panels • Hands-free open • Fail safe -- automatic open in case of emergency 1/24/2022
Closing Words • The Vision: Enable e-Government through – A cross-governmental, ubiquitous, interoperable Authentication Infrastructure – Develop and reuse of applications which employ common multi-protocol authentication solutions in support of Agency business processes • Leverage existing government-wide initiatives: – Federal PKI Policy Authority – Federal Bridge Certification Authority • Recognize Do. D, NFC, other credentials – Access Certificates for Electronic Services – Other authentication investments as appropriate 1/24/2022