Fall GSHRM Conference The RitzCarlton Lake Oconee Greensboro
Fall GSHRM Conference The Ritz-Carlton, Lake Oconee Greensboro, GA September 9, 2019 Beyond HIPAA: Cyber Threats, Hackers and Risks … and How to Protect PHI Richard Sheinis, FIP, CIPP-US, CIPT Hall Booth Smith, P. C. 11215 North Community House Road, Suite 750 Charlotte, NC 28277 (980) 859 -0381 rsheinis@hallboothsmith. com @Sheinis. Cyber. Law
Talk About 3 Things 1. Ransomware 2. Other Cyber Risks to PHI and Patient Safety 3. What Can You Do About It?
What Is Ransomware? Ransomware is malware (malicious software) that infects a computer system and encrypts data so it is not accessible by the owner of the data. The hacker then demands that a ransom be paid (always in bitcoin) in exchange for the key to decrypt the data. Ransomware is almost always delivered via a phishing e-mail, although it can also be spread through websites or drive-by downloads.
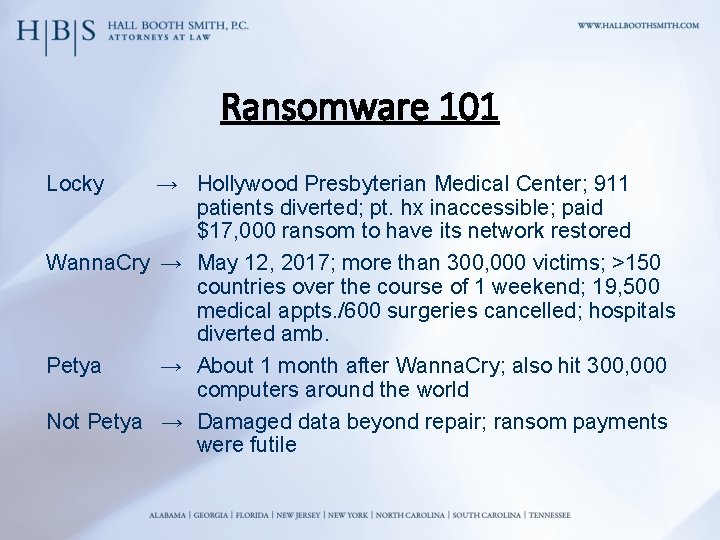
Ransomware 101 Locky → Hollywood Presbyterian Medical Center; 911 patients diverted; pt. hx inaccessible; paid $17, 000 ransom to have its network restored Wanna. Cry → May 12, 2017; more than 300, 000 victims; >150 countries over the course of 1 weekend; 19, 500 medical appts. /600 surgeries cancelled; hospitals diverted amb. Petya → About 1 month after Wanna. Cry; also hit 300, 000 computers around the world Not Petya → Damaged data beyond repair; ransom payments were futile
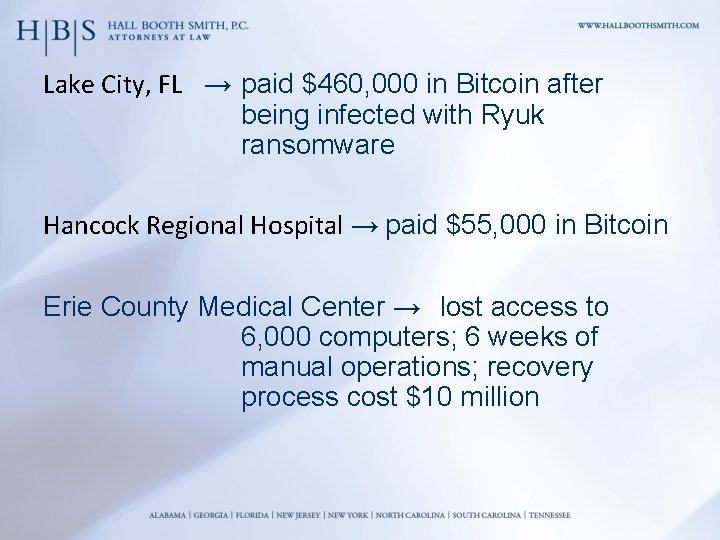
Lake City, FL → paid $460, 000 in Bitcoin after being infected with Ryuk ransomware Hancock Regional Hospital → paid $55, 000 in Bitcoin Erie County Medical Center → lost access to 6, 000 computers; 6 weeks of manual operations; recovery process cost $10 million
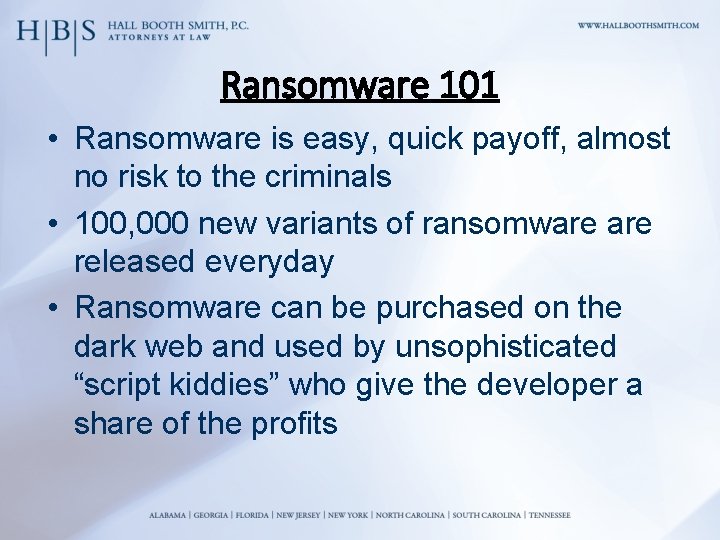
Ransomware 101 • Ransomware is easy, quick payoff, almost no risk to the criminals • 100, 000 new variants of ransomware released everyday • Ransomware can be purchased on the dark web and used by unsophisticated “script kiddies” who give the developer a share of the profits
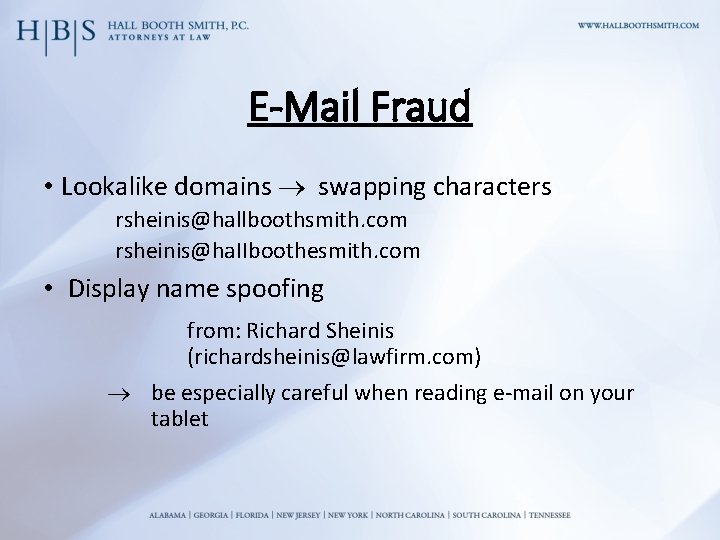
E-Mail Fraud • Lookalike domains swapping characters rsheinis@hallboothsmith. com rsheinis@ha. IIboothesmith. com • Display name spoofing from: Richard Sheinis (richardsheinis@lawfirm. com) be especially careful when reading e-mail on your tablet
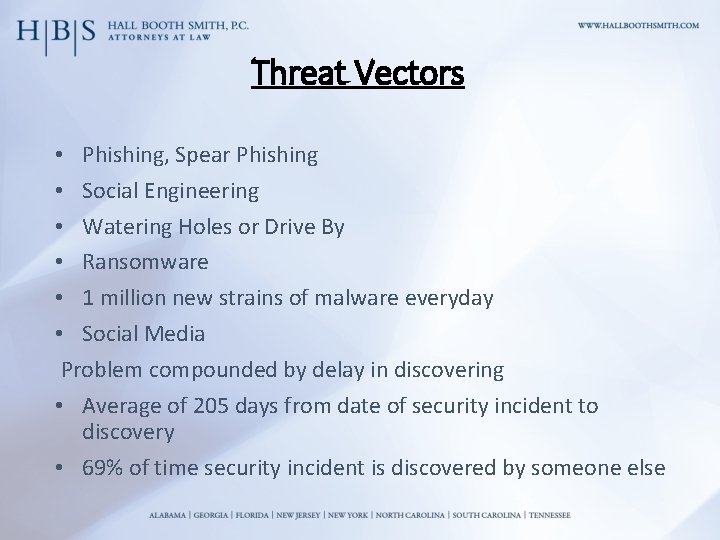
Threat Vectors • Phishing, Spear Phishing • Social Engineering • Watering Holes or Drive By • Ransomware • 1 million new strains of malware everyday • Social Media Problem compounded by delay in discovering • Average of 205 days from date of security incident to discovery • 69% of time security incident is discovered by someone else
What Is The Weakest Link In Our Cyber Security A) B) C) D) E) Firewalls Old Equipment Software vulnerabilities The internet Employees
We are the weakest link! 93% of data breaches have an element of employee lack of awareness
INTERNET AND BROWSER VULNERABILITIES • Distribution of malicious code via corrupted web pages • An infected file and a script program are placed on a web page. When a user visits the page, the infected file is downloaded onto the user’s computer. • The hacker may then send spam e-mails to get as many users as possible to visit the infected page. • But how does the web page get infected in the first place? – The cybercriminal uses a vulnerability within an operating system or an application, such as Java. Script.
Social Media Concerns • Facebook reported in 2015 that 31 million (2%) accounts are false; now it is 60 million • Estimated 20 million fake Twitter accounts • Instagram may have 95 million fake accounts
BONUS!! Top Ten Cybersecurity Tips 10. 9. 8. 7. 6. Back-up, Back-up and Test the Back-up Two-factor authentication Passwords Auditing Access Control
5. 4. 3. 2. 1. RDP Stop using private e-mail accounts Vendor due diligence Risk Analysis Training
- Slides: 15