Exploring Security Vulnerabilities by Exploiting Buffer Overflow using
Exploring Security Vulnerabilities by Exploiting Buffer Overflow using the MIPS ISA Andrew T. Phillips Jack S. E. Tan Department of Computer Science University of Wisconsin – Eau Claire
Smashing the stack § Limitations of C permit security exploits § Library routines: § strcpy, strcat, sprintf, etc. § no automatic bounds checking. § Shortcomings: § allow writing past end of array. §Major source of security exploits
The Original Exploit § The trade magazine "Phrack" published: § "Smashing the Stack for Fun and Profit" by Aleph One §http: //www. phrack. com/phrack/49/P 49 -14 §Original exploit done on the Intel architecture
Overall Strategy § Write a small program that starts a shell window: use something like system("/bin/sh") §Translate the program into HEX, modifying individual bytes as needed (explained later) §Put the HEX code into a buffer, followed by the address of the start of that buffer, repeated many times §Will overwrite the return address (on the stack) of the servers buffer handler routine
Basic Steps § Get a copy of the OS to be attacked § Analyze the system stack layout for that OS § Put the "shell window" HEX code into a buffer § Send your buffer to a program on the target OS (maybe one that runs as "root") that takes a buffer as input, makes a copy of that buffer, and doesn't check its bounds
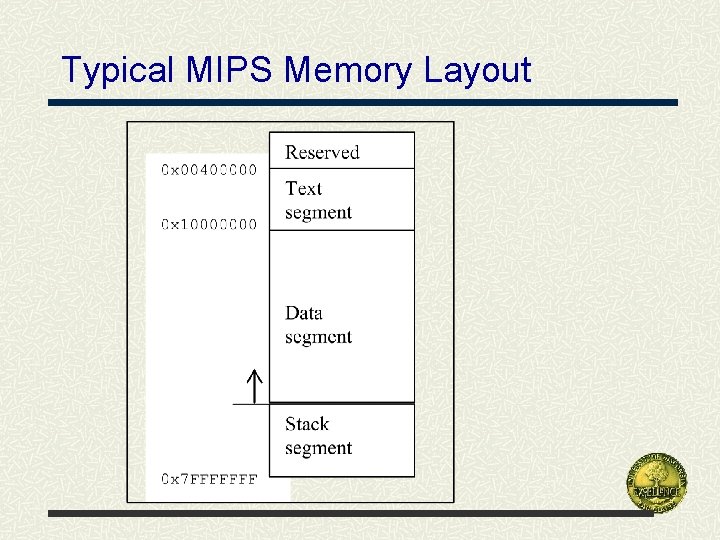
Typical MIPS Memory Layout
Stack Frame On a function call: q Preserve state of calling function q Allocate additional memory for calling function q Stack frame (activation record) created q Pushed onto execution stack
Stack Frame – cont’d Stack frame (activation record) contains: q Function arguments q Local variables q Return address ($ra) q Global pointer ($gp) Note: Not all local variables may be stacked: Optimizing compiler may put them in registers.
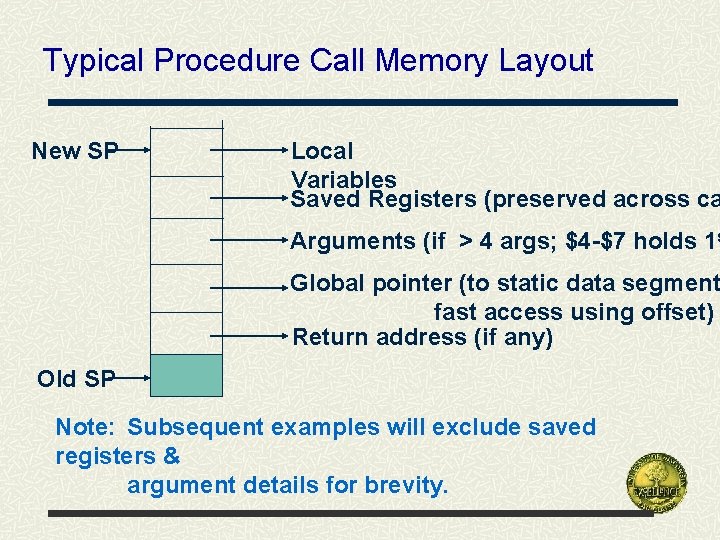
Typical Procedure Call Memory Layout New SP Local Variables Saved Registers (preserved across ca Arguments (if > 4 args; $4 -$7 holds 1 s Global pointer (to static data segment fast access using offset) Return address (if any) Old SP Note: Subsequent examples will exclude saved registers & argument details for brevity.
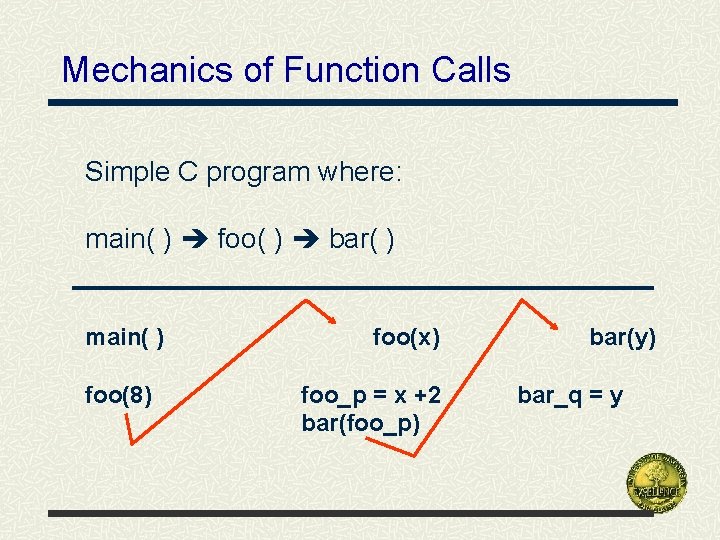
Mechanics of Function Calls Simple C program where: main( ) foo( ) bar( ) main( ) foo(8) foo(x) foo_p = x +2 bar(foo_p) bar(y) bar_q = y
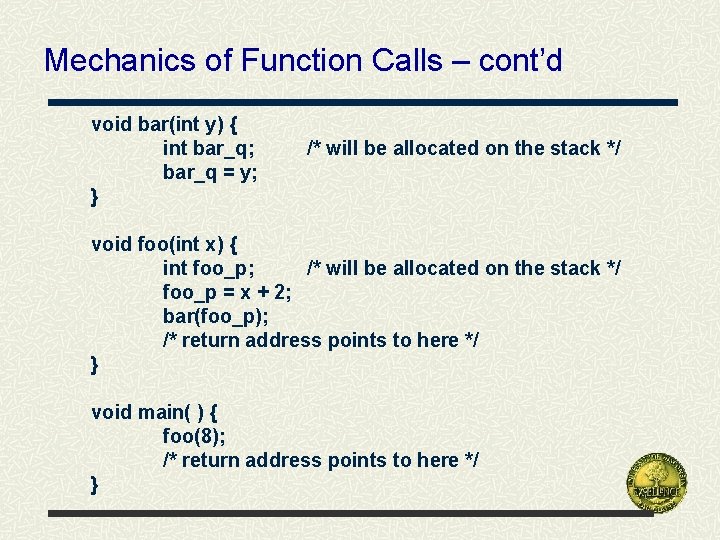
Mechanics of Function Calls – cont’d void bar(int y) { int bar_q; bar_q = y; } /* will be allocated on the stack */ void foo(int x) { int foo_p; /* will be allocated on the stack */ foo_p = x + 2; bar(foo_p); /* return address points to here */ } void main( ) { foo(8); /* return address points to here */ }
Memory Layout for foo( )
![Overview of an Overflow void foo(char *buf) { char local_buf[10]; strcpy(local_buf, buf); } void Overview of an Overflow void foo(char *buf) { char local_buf[10]; strcpy(local_buf, buf); } void](http://slidetodoc.com/presentation_image_h2/51d8342a3f7a7df2756a91ea5aab74d1/image-13.jpg)
Overview of an Overflow void foo(char *buf) { char local_buf[10]; strcpy(local_buf, buf); } void main() { char *large_buf = “a……a”; // lots of a’s foo(large_buf); /* location of return from foo() */ }
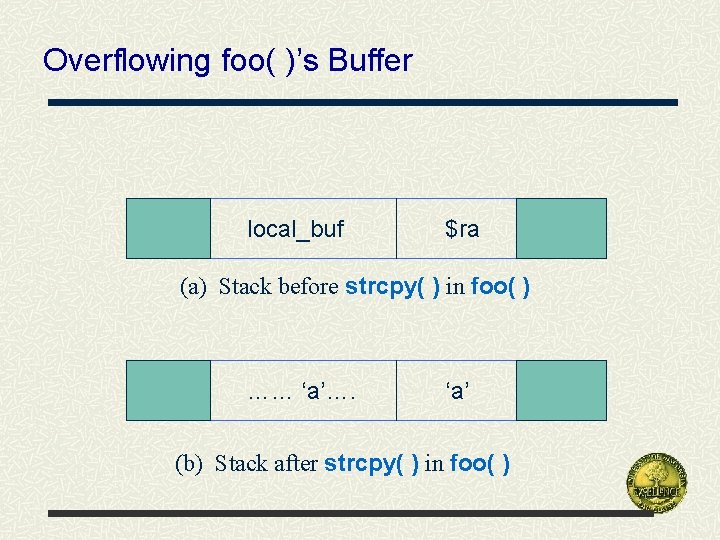
Overflowing foo( )’s Buffer local_buf $ra (a) Stack before strcpy( ) in foo( ) …… ‘a’…. ‘a’ (b) Stack after strcpy( ) in foo( )
![Implementing Overflow in the MIPS ISA void foo(char *buf) { char local_buf[10]; int i Implementing Overflow in the MIPS ISA void foo(char *buf) { char local_buf[10]; int i](http://slidetodoc.com/presentation_image_h2/51d8342a3f7a7df2756a91ea5aab74d1/image-15.jpg)
Implementing Overflow in the MIPS ISA void foo(char *buf) { char local_buf[10]; int i = 0; while (buf[i] != 0) { local_buf[i] = buf[i]; i++; } bar(); /* code for bar() not shown */ /* bar( )’s RA in $31 reg. ; foo( )’s RA on stack */ } void main() { char *large_buf = “a……a”; // lots of a’s foo(large_buf); /* location of return from foo() */ }
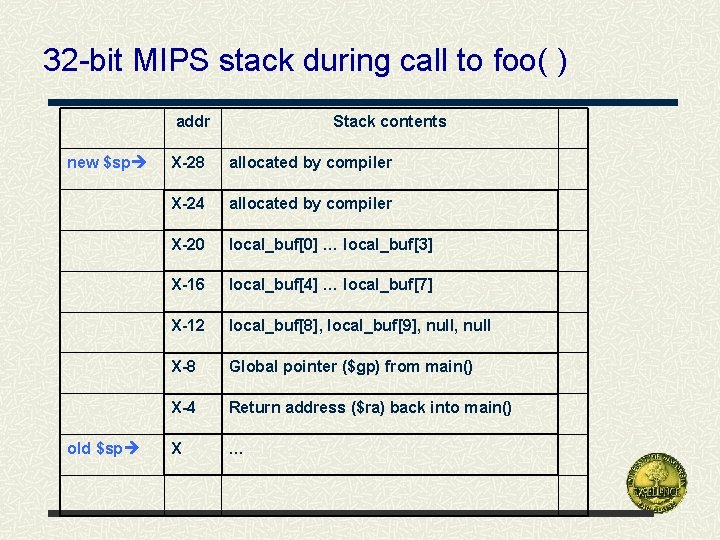
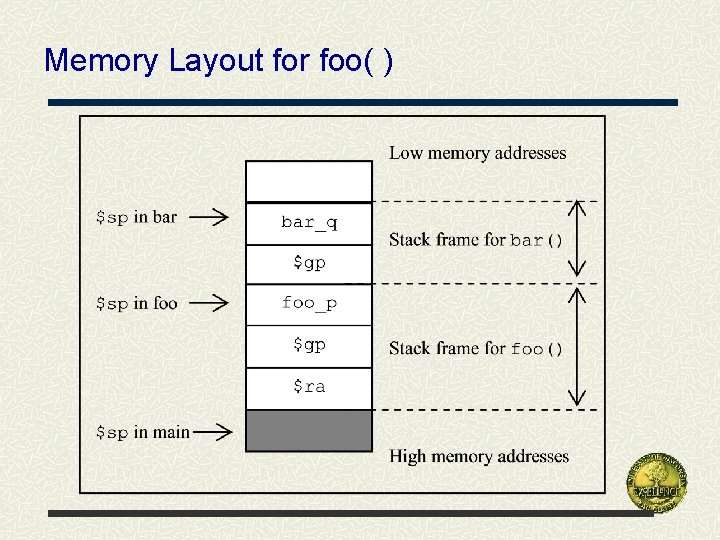
32 -bit MIPS stack during call to foo( ) addr new $sp old $sp Stack contents X-28 allocated by compiler X-24 allocated by compiler X-20 local_buf[0] … local_buf[3] X-16 local_buf[4] … local_buf[7] X-12 local_buf[8], local_buf[9], null X-8 Global pointer ($gp) from main() X-4 Return address ($ra) back into main() X …
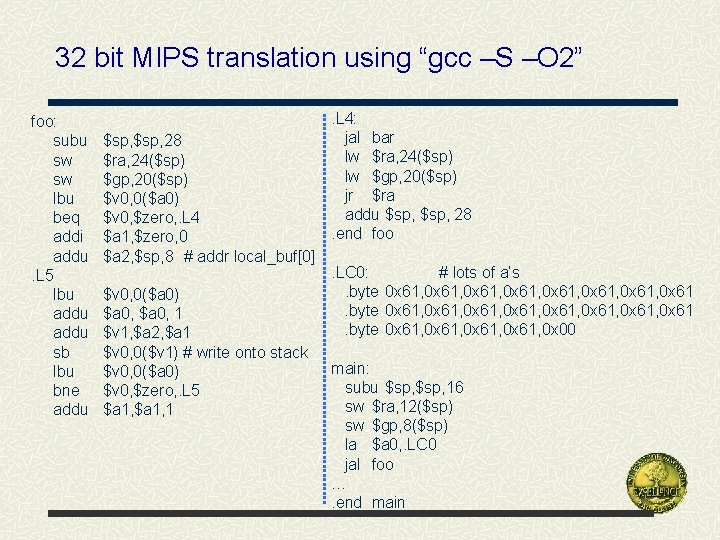
32 bit MIPS translation using “gcc –S –O 2” foo: subu sw sw lbu beq addi addu. L 5 lbu addu sb lbu bne addu $sp, 28 $ra, 24($sp) $gp, 20($sp) $v 0, 0($a 0) $v 0, $zero, . L 4 $a 1, $zero, 0 $a 2, $sp, 8 # addr local_buf[0] $v 0, 0($a 0) $a 0, 1 $v 1, $a 2, $a 1 $v 0, 0($v 1) # write onto stack $v 0, 0($a 0) $v 0, $zero, . L 5 $a 1, 1 . L 4: jal bar lw $ra, 24($sp) lw $gp, 20($sp) jr $ra addu $sp, 28. end foo. LC 0: # lots of a’s. byte 0 x 61, 0 x 61, 0 x 61, 0 x 61, 0 x 61. byte 0 x 61, 0 x 00 main: subu $sp, 16 sw $ra, 12($sp) sw $gp, 8($sp) la $a 0, . LC 0 jal foo …. end main
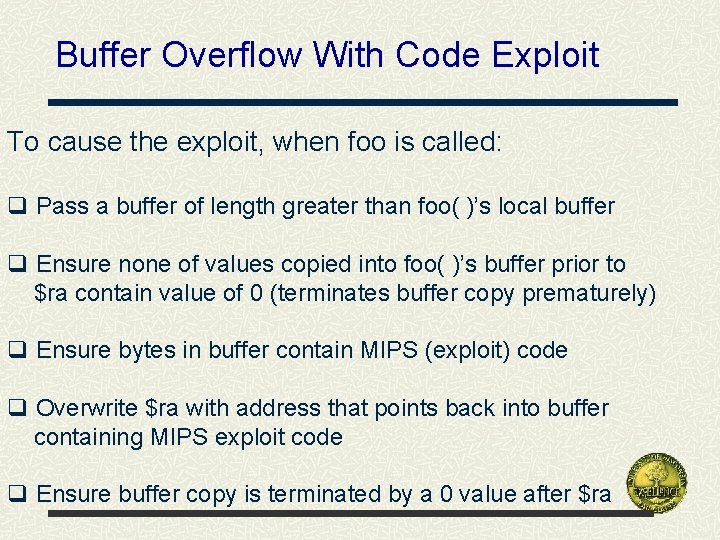
Buffer Overflow With Code Exploit To cause the exploit, when foo is called: q Pass a buffer of length greater than foo( )’s local buffer q Ensure none of values copied into foo( )’s buffer prior to $ra contain value of 0 (terminates buffer copy prematurely) q Ensure bytes in buffer contain MIPS (exploit) code q Overwrite $ra with address that points back into buffer containing MIPS exploit code q Ensure buffer copy is terminated by a 0 value after $ra
![Buffer Overflow With Code Exploit void foo(char *buf) { char local_buf[256]; strcpy(local_buf, buf); } Buffer Overflow With Code Exploit void foo(char *buf) { char local_buf[256]; strcpy(local_buf, buf); }](http://slidetodoc.com/presentation_image_h2/51d8342a3f7a7df2756a91ea5aab74d1/image-19.jpg)
Buffer Overflow With Code Exploit void foo(char *buf) { char local_buf[256]; strcpy(local_buf, buf); } void main() { char *large_buf = “x 01x 20x 48x 20” /* add $t 1, $zero */ “x 01x 20x 48x 20” … “x 20x 84x. FF” /* addi $a 0, -1 */ “x 12x 34x 56x 78” /* guess address of exploit */ “x 00”; foo(large_buf); /* location of return from foo() */ }
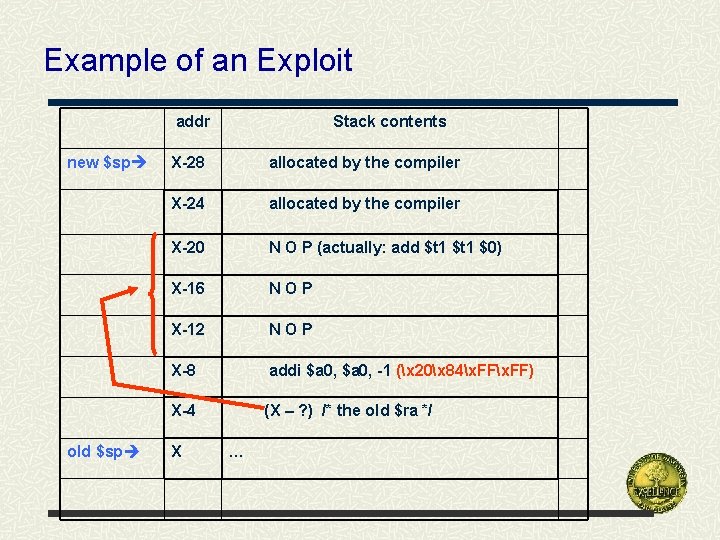
Example of an Exploit addr new $sp old $sp Stack contents X-28 allocated by the compiler X-24 allocated by the compiler X-20 N O P (actually: add $t 1 $0) X-16 NOP X-12 NOP X-8 addi $a 0, -1 (x 20x 84x. FF) X-4 (X – ? ) /* the old $ra */ X …
Detailed Paper Explaining the Exploit http: //www. cs. uwec. edu/~tan/priv/wwwdocs/cs 362/buff_overflow. pdf
- Slides: 21