Exchange Online Protection overview Eliminate threats with multilayered













- Slides: 30


Exchange Online Protection overview
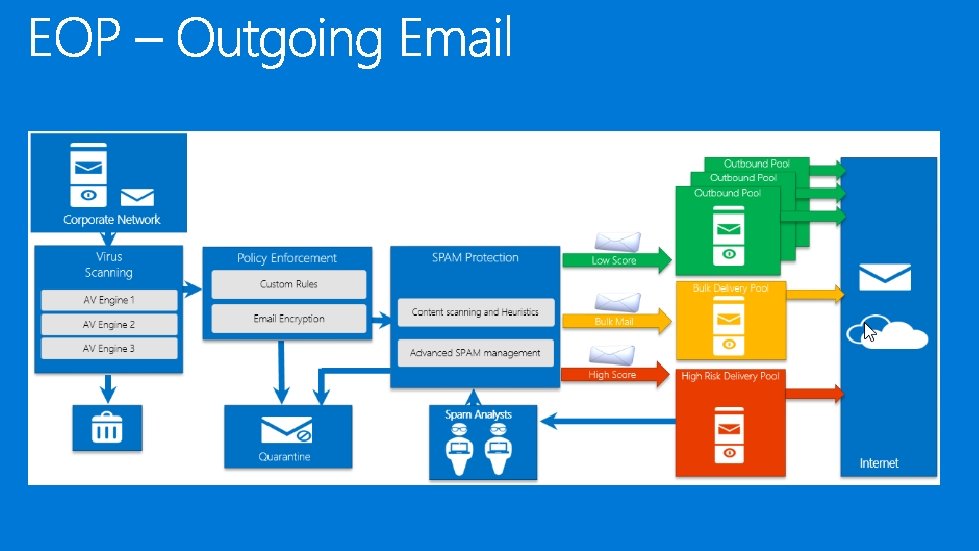
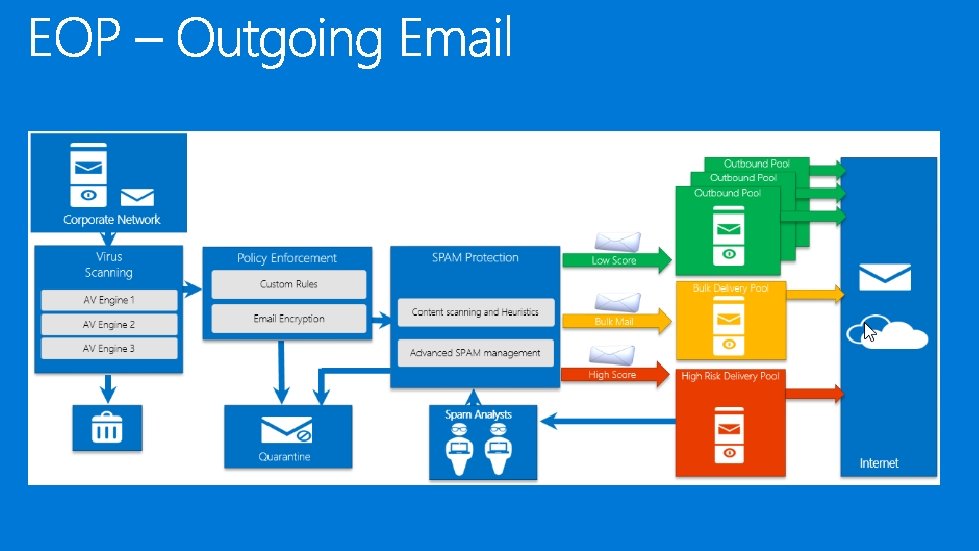
• Eliminate threats with multi-layered, real-time anti-spam and multi-engine antimalware protection. • Protect your company's IP reputation - separate outbound delivery pools for high-risk email. • Five financially backed SLAs including protection from 100% of known viruses and 99% of spam. • Globally load-balanced network of datacenters helps to ensure a 99. 999% network uptime.
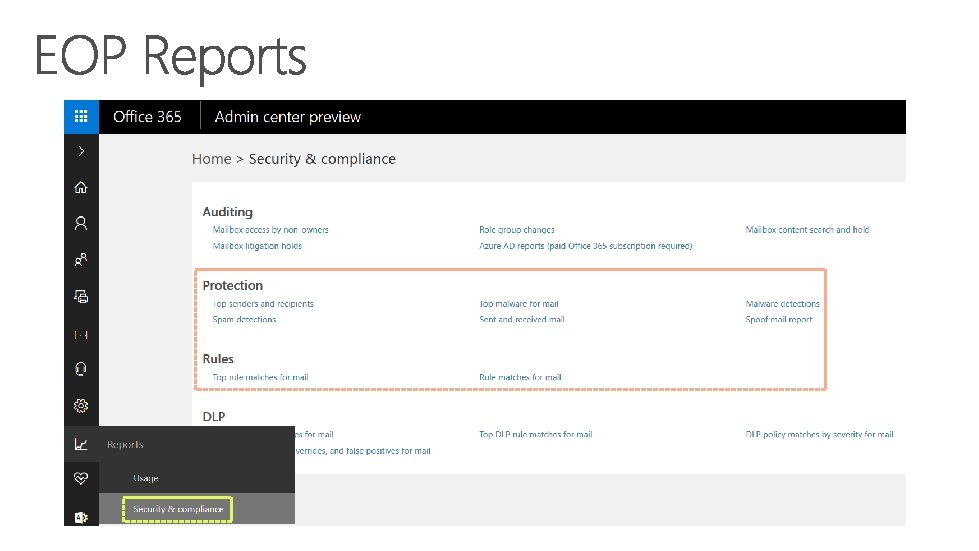
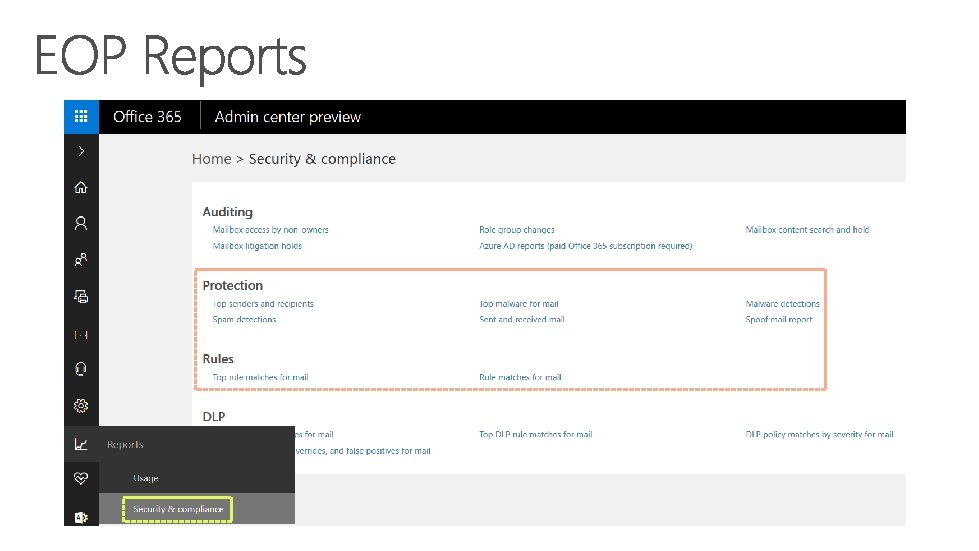
• Manage and administer from the Exchange Administration Center—a single web-based interface. • Near real-time reporting and message traces • Active content, connection, and policy-based filtering enables compliance with corporate policies and government regulations. • IT-level phone support 24 hours a day, 7 days a week, 365 days a year at no additional cost.
• No hardware or software required to install, manage, and maintain. • Predictable payment schedule - subscription-based service. Multiple EOP plans. • Automatic queuing - no email is lost or bounced if the destination email server is unavailable. • Get up and running quickly with a simple MX record change.
Standalone All mailboxes are located on-premises Purchasable on its own or Part of Exchange Enterprise CAL with Services Fully hosted All mailboxes are hosted in the cloud with Microsoft Exchange Online license Hybrid Some mailboxes are hosted in Exchange Online, and some mailboxes on-premises Exchange Online license

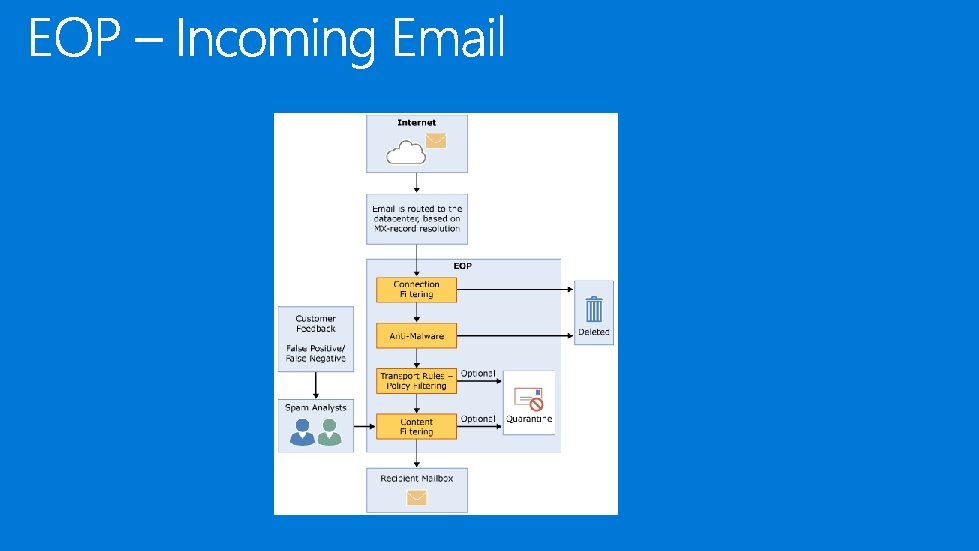
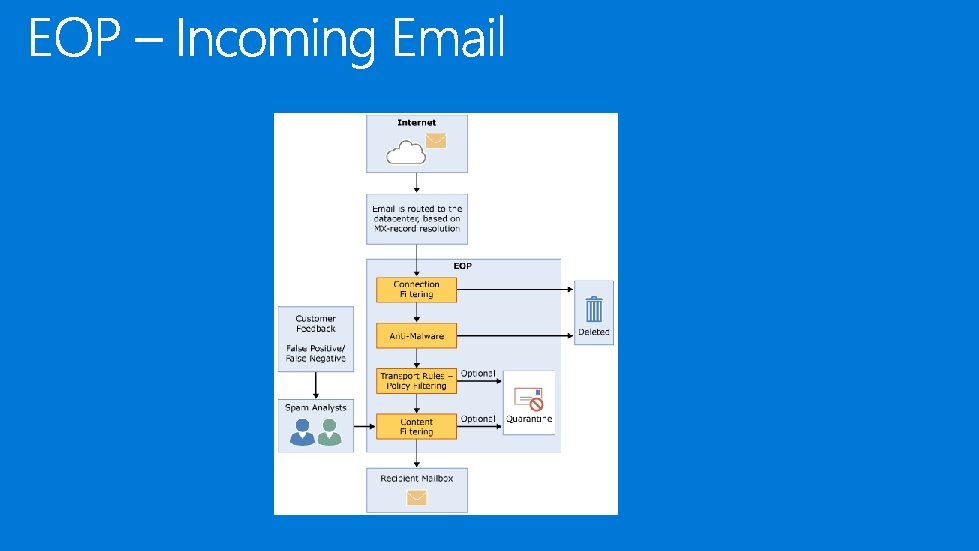
Exchange Online Protection Architecture Overview
Protection Overview
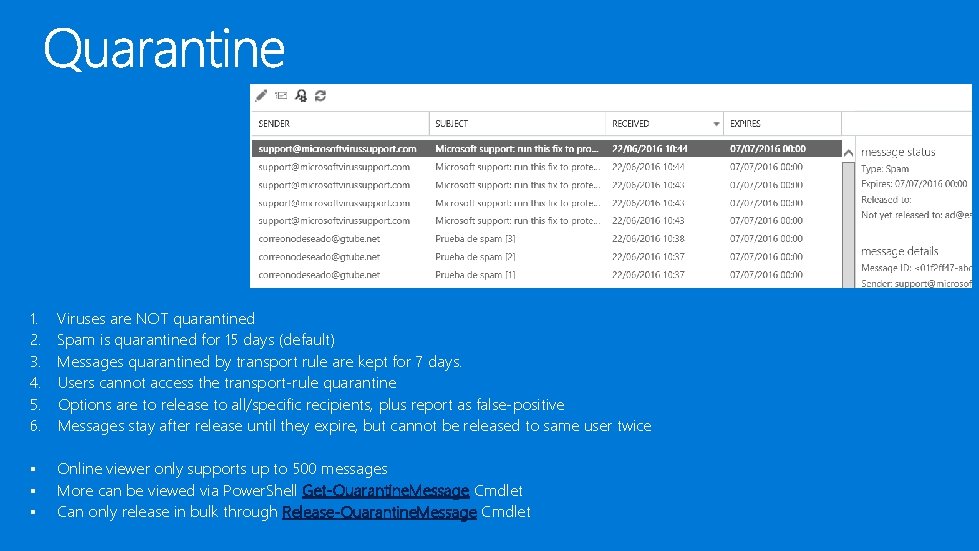
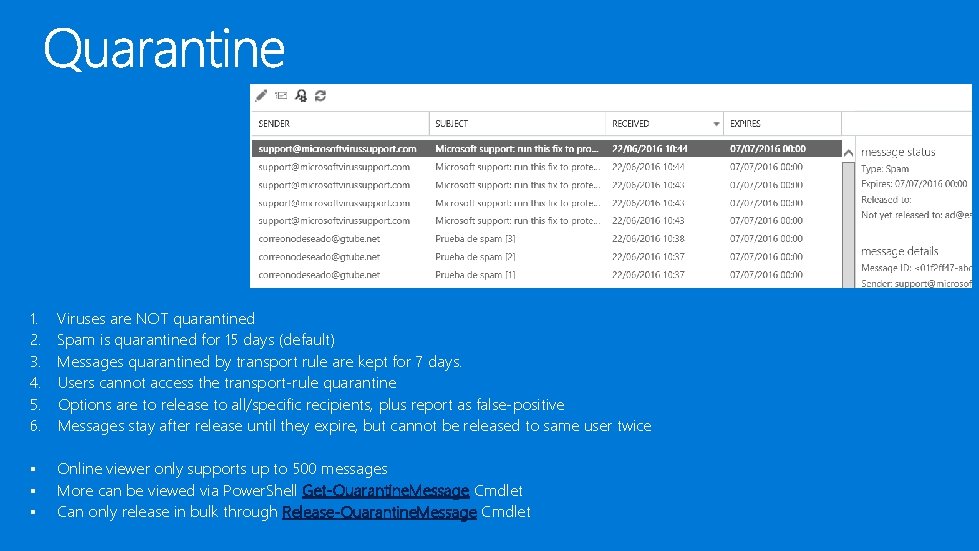
1. 2. 3. 4. 5. 6. Viruses are NOT quarantined Spam is quarantined for 15 days (default) Messages quarantined by transport rule are kept for 7 days. Users cannot access the transport-rule quarantine Options are to release to all/specific recipients, plus report as false-positive Messages stay after release until they expire, but cannot be released to same user twice § § § Online viewer only supports up to 500 messages More can be viewed via Power. Shell Get-Quarantine. Message Cmdlet Can only release in bulk through Release-Quarantine. Message Cmdlet

Mailflow Overview


Message Traces
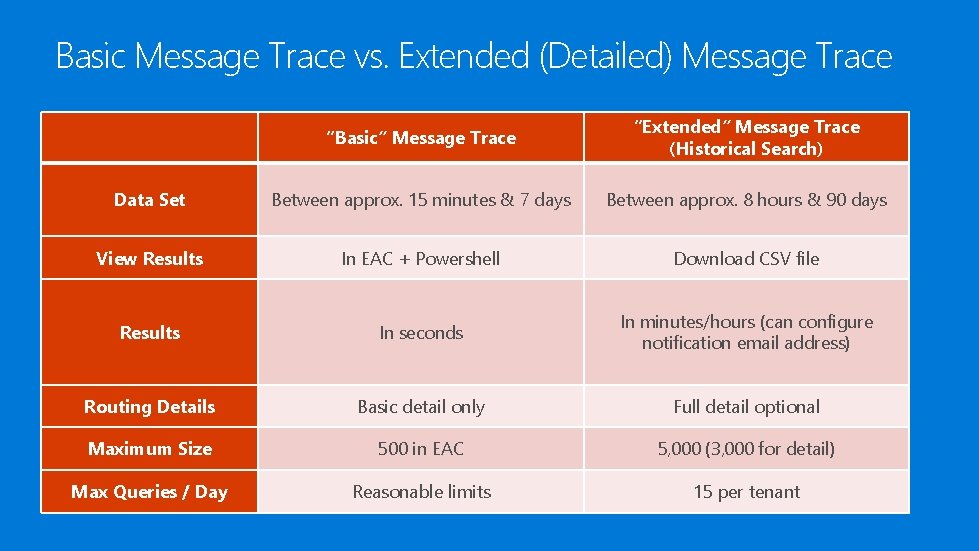
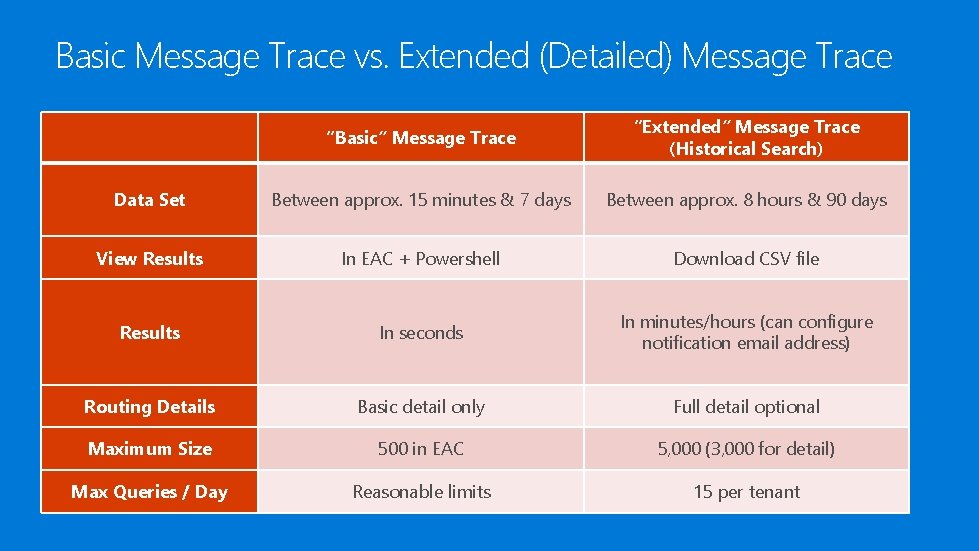
Basic Message Trace vs. Extended (Detailed) Message Trace “Basic” Message Trace “Extended” Message Trace (Historical Search) Data Set Between approx. 15 minutes & 7 days Between approx. 8 hours & 90 days View Results In EAC + Powershell Download CSV file Results In seconds In minutes/hours (can configure notification email address) Routing Details Basic detail only Full detail optional Maximum Size 500 in EAC 5, 000 (3, 000 for detail) Max Queries / Day Reasonable limits 15 per tenant


Accepted Domains, Remote Domains & Connectors


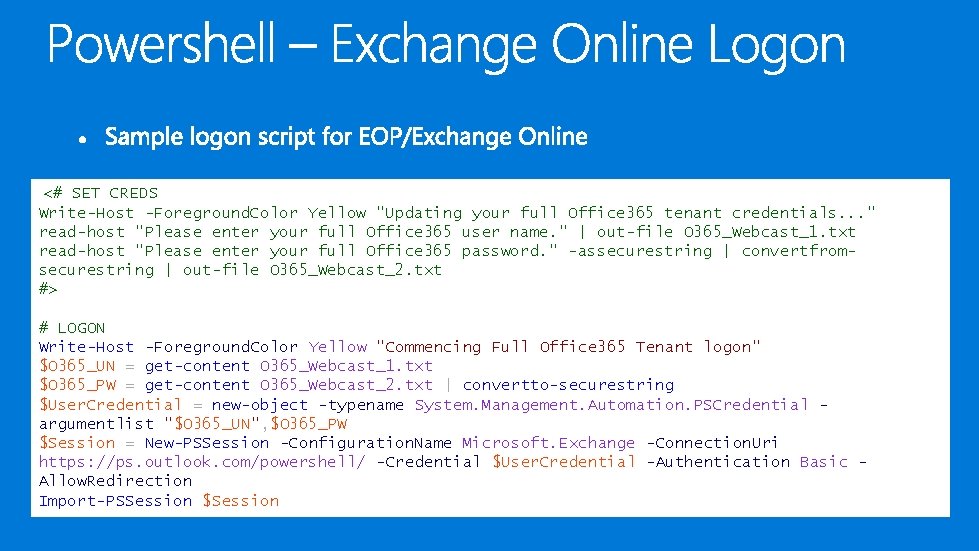
Powershell
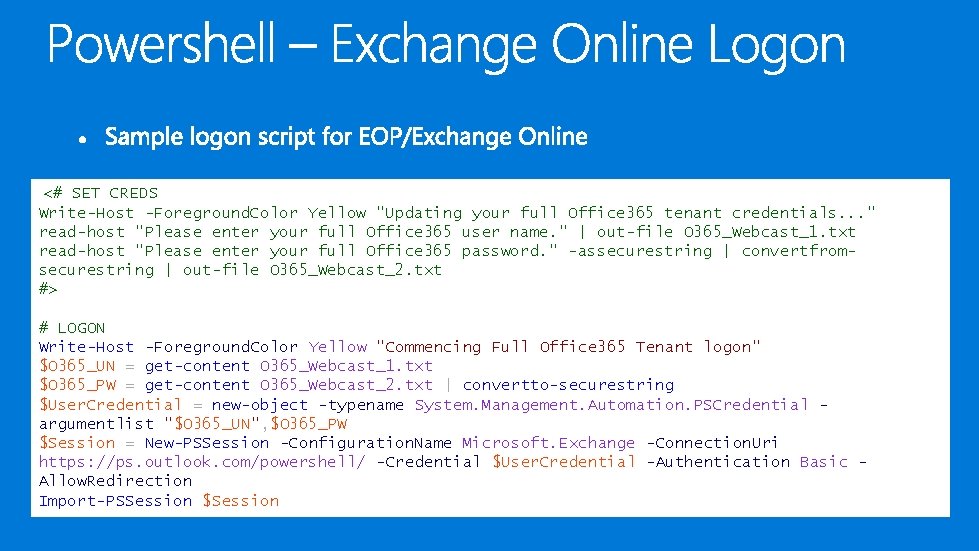
<# SET CREDS Write-Host -Foreground. Color Yellow "Updating your full Office 365 tenant credentials. . . " read-host "Please enter your full Office 365 user name. " | out-file O 365_Webcast_1. txt read-host "Please enter your full Office 365 password. " -assecurestring | convertfromsecurestring | out-file O 365_Webcast_2. txt #> # LOGON Write-Host -Foreground. Color Yellow "Commencing Full Office 365 Tenant logon" $O 365_UN = get-content O 365_Webcast_1. txt $O 365_PW = get-content O 365_Webcast_2. txt | convertto-securestring $User. Credential = new-object -typename System. Management. Automation. PSCredential argumentlist "$O 365_UN", $O 365_PW $Session = New-PSSession -Configuration. Name Microsoft. Exchange -Connection. Uri https: //ps. outlook. com/powershell/ -Credential $User. Credential -Authentication Basic Allow. Redirection Import-PSSession $Session
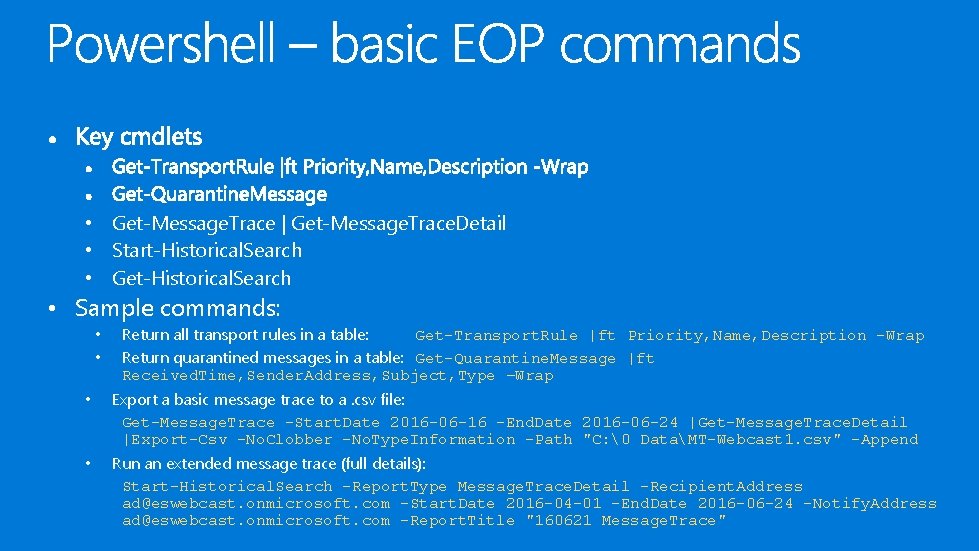
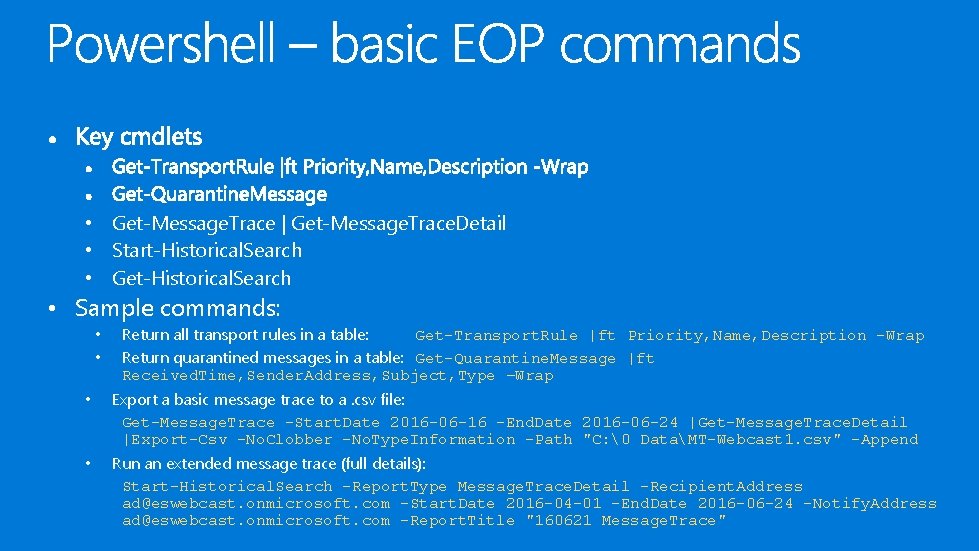
• Get-Message. Trace | Get-Message. Trace. Detail • Start-Historical. Search • Get-Historical. Search • Sample commands: • • Return all transport rules in a table: Get-Transport. Rule |ft Priority, Name, Description -Wrap Return quarantined messages in a table: Get-Quarantine. Message |ft Received. Time, Sender. Address, Subject, Type –Wrap • Export a basic message trace to a. csv file: Get-Message. Trace -Start. Date 2016 -06 -16 -End. Date 2016 -06 -24 |Get-Message. Trace. Detail |Export-Csv -No. Clobber -No. Type. Information -Path "C: � DataMT-Webcast 1. csv" -Append • Run an extended message trace (full details): Start-Historical. Search -Report. Type Message. Trace. Detail -Recipient. Address ad@eswebcast. onmicrosoft. com -Start. Date 2016 -04 -01 -End. Date 2016 -06 -24 -Notify. Address ad@eswebcast. onmicrosoft. com -Report. Title "160621 Message. Trace"

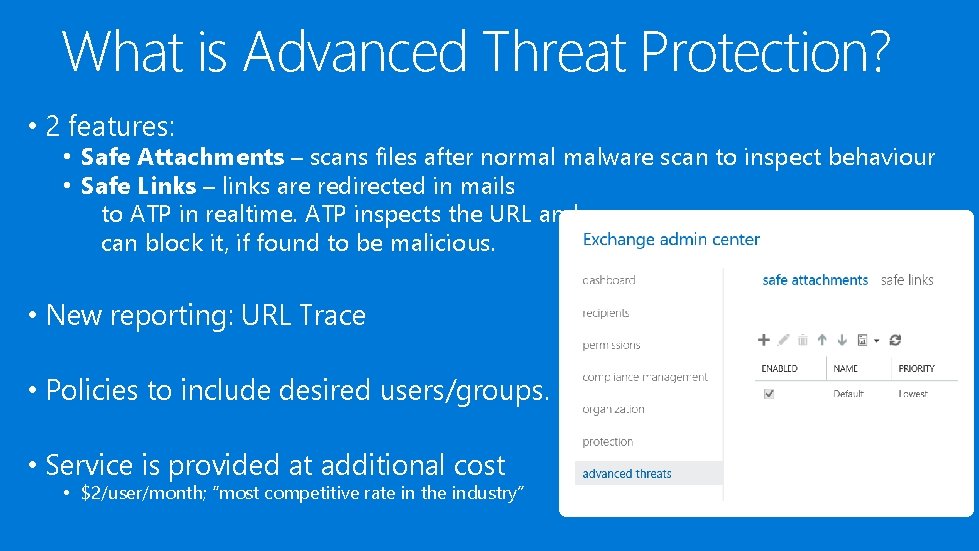
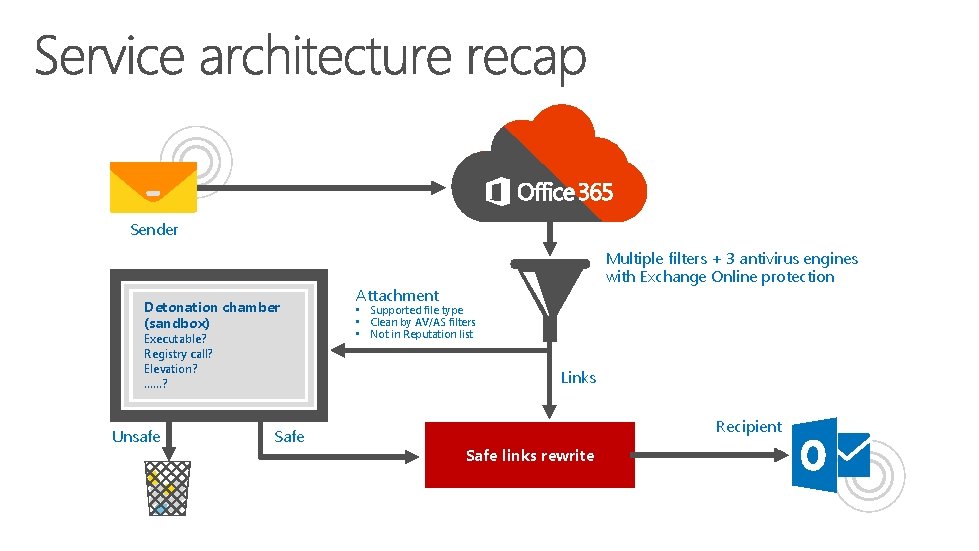
Advanced Threat Protection
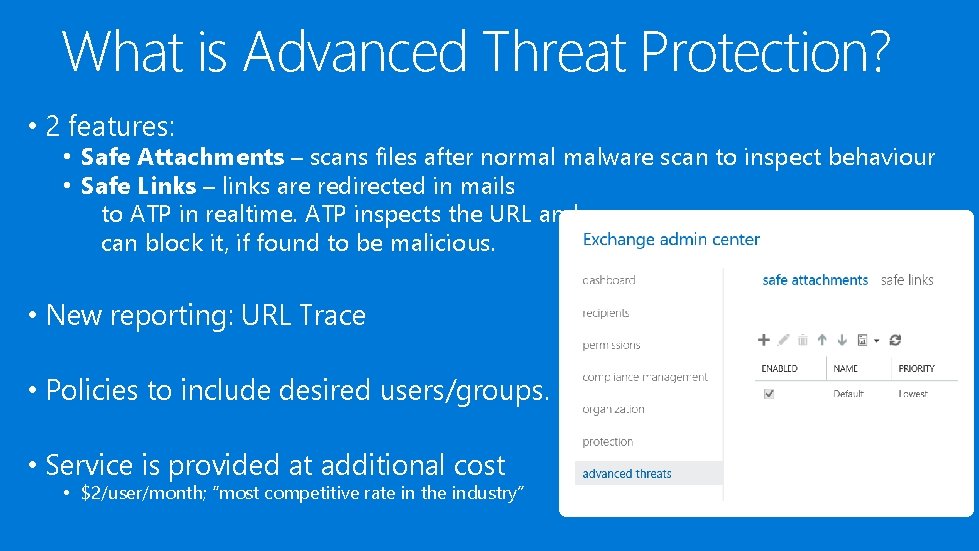
What is Advanced Threat Protection? • 2 features: • Safe Attachments – scans files after normal malware scan to inspect behaviour • Safe Links – links are redirected in mails to ATP in realtime. ATP inspects the URL and can block it, if found to be malicious. • New reporting: URL Trace • Policies to include desired users/groups. • Service is provided at additional cost • $2/user/month; “most competitive rate in the industry”
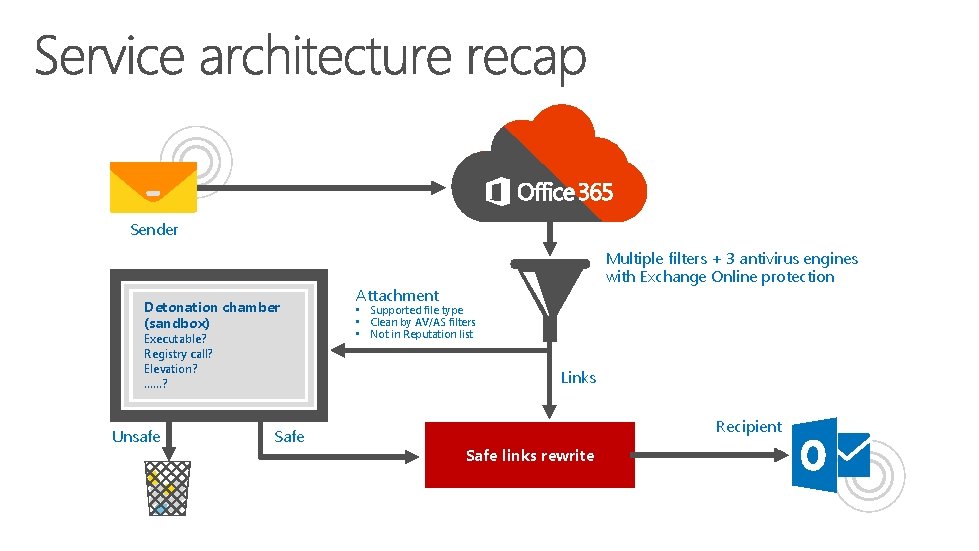
Sender Detonation chamber (sandbox) Executable? Registry call? Elevation? ……? Unsafe Multiple filters + 3 antivirus engines with Exchange Online protection Attachment • Supported file type • Clean by AV/AS filters • Not in Reputation list Links Safe Recipient Safe links rewrite