Examining ICMP packet Header Field https atlas arbor
Examining ICMP packet Header Field
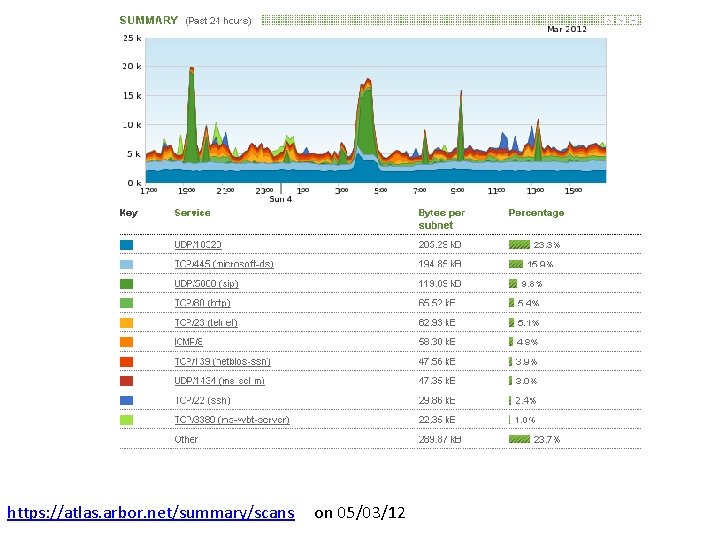
https: //atlas. arbor. net/summary/scans on 05/03/12
• ICMP stands for the Internet Control Message Protocol, and it was designed to send control messages between routers and hosts. • For example, an ICMP packet may be sent when a router is experiencing congestion or when a destination host is unavailable.
• An ICMP header follows the IP header in an IP packet, but it is not considered to be a Layer 4 header like TCP or UDP. • Instead, ICMP is considered to be an integral part of IP; in fact, every vendor's implementation of IP is required to include ICMP.
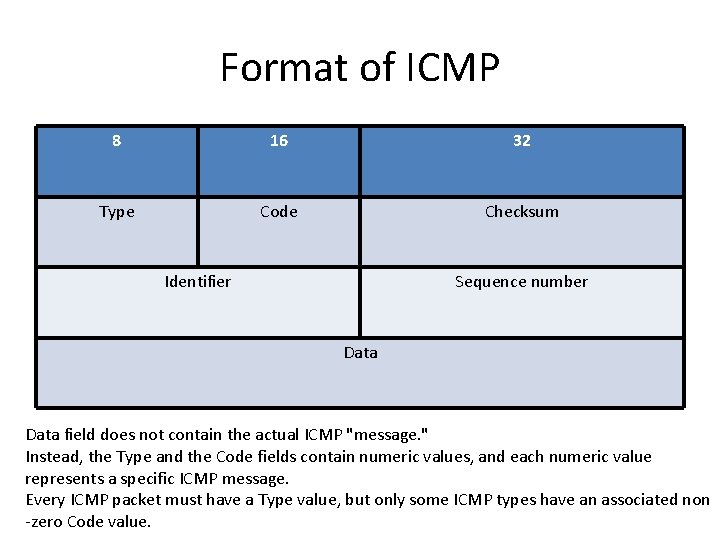
Format of ICMP 8 16 32 Type Code Checksum Identifier Sequence number Data field does not contain the actual ICMP "message. " Instead, the Type and the Code fields contain numeric values, and each numeric value represents a specific ICMP message. Every ICMP packet must have a Type value, but only some ICMP types have an associated non -zero Code value.
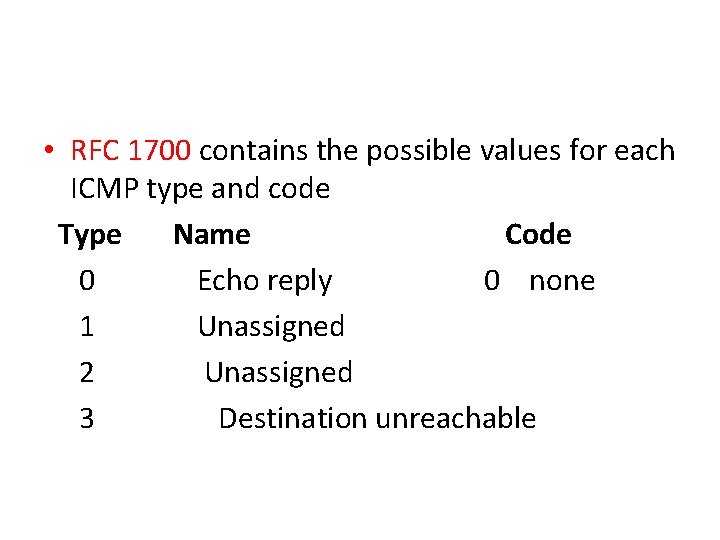
• RFC 1700 contains the possible values for each ICMP type and code Type Name Code 0 Echo reply 0 none 1 Unassigned 2 Unassigned 3 Destination unreachable
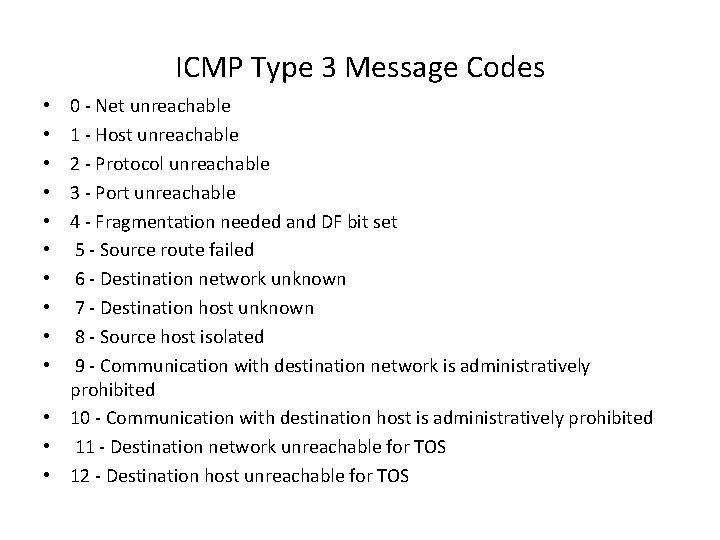
ICMP Type 3 Message Codes 0 - Net unreachable 1 - Host unreachable 2 - Protocol unreachable 3 - Port unreachable 4 - Fragmentation needed and DF bit set 5 - Source route failed 6 - Destination network unknown 7 - Destination host unknown 8 - Source host isolated 9 - Communication with destination network is administratively prohibited • 10 - Communication with destination host is administratively prohibited • 11 - Destination network unreachable for TOS • 12 - Destination host unreachable for TOS • • •
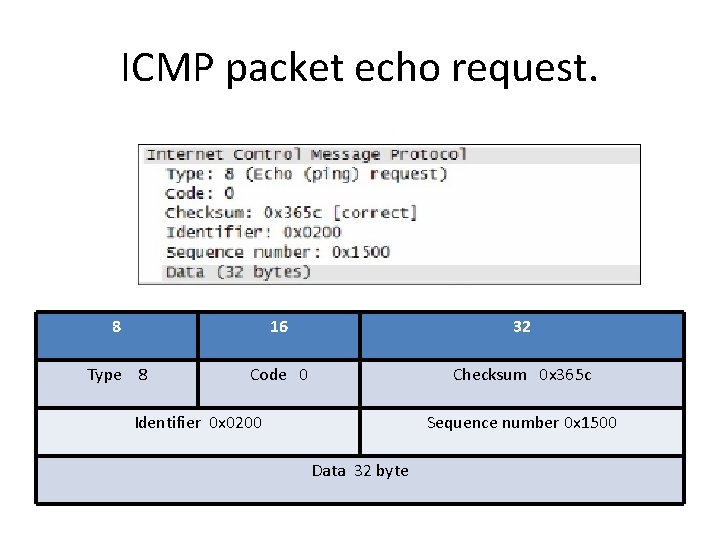
ICMP packet echo request. 8 16 32 Type 8 Code 0 Checksum 0 x 365 c Identifier 0 x 0200 Sequence number 0 x 1500 Data 32 byte
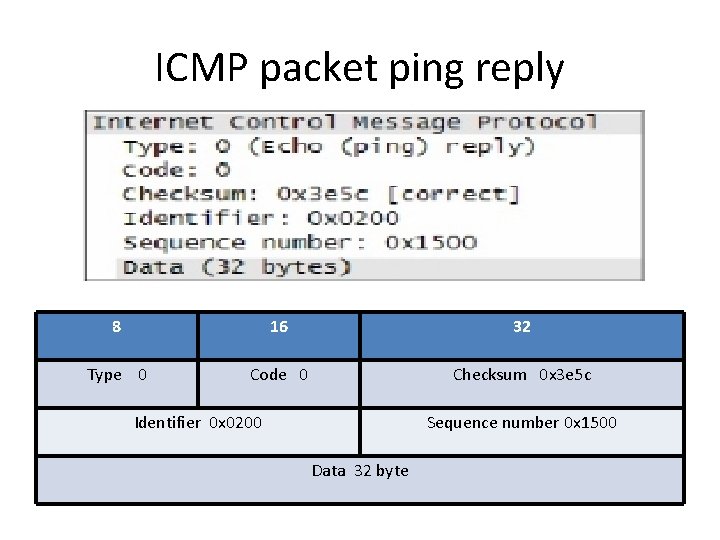
ICMP packet ping reply 8 16 32 Type 0 Code 0 Checksum 0 x 3 e 5 c Identifier 0 x 0200 Sequence number 0 x 1500 Data 32 byte
• At the TCP/IP Network layer, communication between devices is not guaranteed. • However, ICMP does provide minimal checks for a reply to match the request. • From the information provided in the ICMP messages, how does the sender know that the reply is to a specific echo?
ICMP based Attacks • Attacks that use ICMP "hard" error messages • Attacks that use ICMP "fragmentation needed and Don't Fragment (DF) bit set" messages, also known as Path Maximum Transmission Unit Discovery (PMTUD) attacks • Attacks that use ICMP "source quench" messages Successful attacks may cause connection resets or reduction of throughput in existing connections, depending on the attack type.
"Hard" ICMP Errors • • The ICMP protocol was first defined in RFC 792, published in September of 1981. Referring to TCP connections, ICMP errors are classified as either "hard" or "soft". A "hard" error results in the TCP connection being torn down, much the same as if a RST packet was received. There are three ICMP type 3 'destination unreachable' errors that are defined in RFC 1122 as hard errors. Code 2, 'protocol unreachable', code 3, 'port unreachable', and possibly code 4, 'fragmentation needed and don't fragment bit set' are all hard errors that if received can cause a TCP stack to tear down an existing connection. (Code 4 is only a 'hard' error if Path MTU discovery is not implemented. ) Other ICMP errors are considered "soft" errors. "Soft" errors are reported to the application affected, but the connection continues. solution for the "hard" ICMP error flaw is to simply treat them like "soft" ICMP errors. "If treated that way, " he said, "the stack becomes immune to the problem. " As to why the ICMP stack was designed this way in the first place, "the basic idea of hard errors was to avoid keeping TCP connections from retrying and retrying lots of times, ”. "Maybe it made sense many years ago when you didn't have the processing power you have now, but these days there is no problem with just letting the TCP connection eventually timeout when there is a legitimate network problem. "
Another classification ICMP messages are classified into 2 main categories: 1) ICMP Error Messages 2) ICMP Query Messages • Its goals and features as outlined in RFC 792 is to provide a means to send error messages for non-transient error conditions, and to provide a way to probe the network in order to determine general characteristics about the network.
• Ping the valid IP address • Ping invalid IP address
ICMP Utilities • Windows uses an ICMP-only traceroute-like utility called 'tracert'. • UNIX, Linux and BSD based systems use a UDP -based traceroute. • By default the Linux version of the traceroute application uses UDP to perform its tracing, but it also provides an argument (-I) that allows the tool to use ICMP instead.
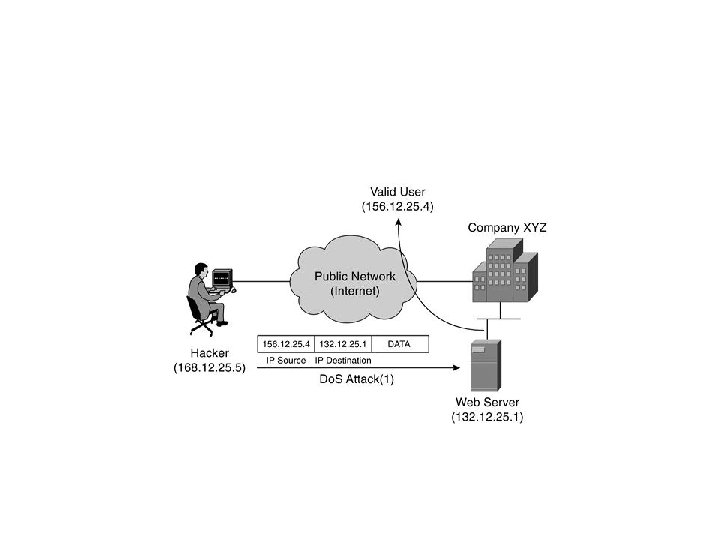
How can ICMP packets be misused by a hacker to gain access to internal network resources? What weakness of ICMP packets enables such attacks? Answer: ICMP does not provide for authentication to verify the destination address, which enables a hacker to insert a false destination IP in the header. If a hacker sends a flood of ICMP Echo requests to a host that does not exist, some hosts may crash. If the host is one that performs important services such as DNS, the hacker can gain access to internal hosts and redirect them to his own computer, where he can then attempt to gather private information such as passwords.
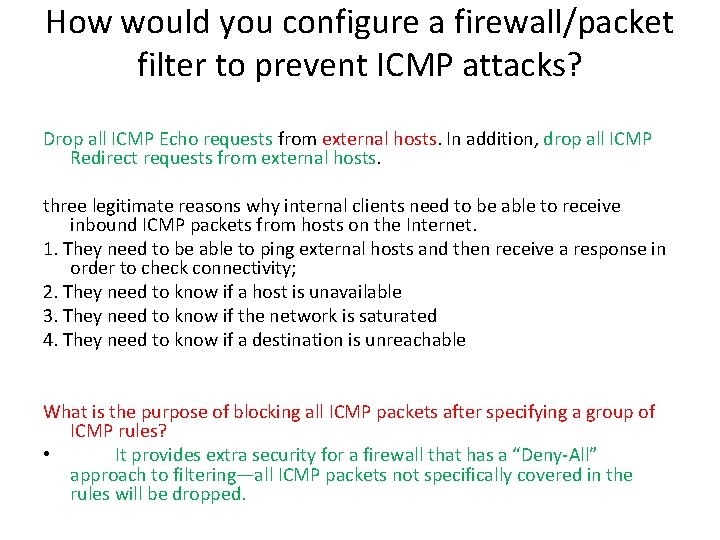
How would you configure a firewall/packet filter to prevent ICMP attacks? Drop all ICMP Echo requests from external hosts. In addition, drop all ICMP Redirect requests from external hosts. three legitimate reasons why internal clients need to be able to receive inbound ICMP packets from hosts on the Internet. 1. They need to be able to ping external hosts and then receive a response in order to check connectivity; 2. They need to know if a host is unavailable 3. They need to know if the network is saturated 4. They need to know if a destination is unreachable What is the purpose of blocking all ICMP packets after specifying a group of ICMP rules? • It provides extra security for a firewall that has a “Deny-All” approach to filtering—all ICMP packets not specifically covered in the rules will be dropped.
• Many commonly-used network utilities are based on ICMP messages. • The tracert (traceroute), Pathping commands are implemented by transmitting UDP datagrams with specially set IP TTL header fields, and looking for ICMP Time to live exceeded in transit (above) and "Destination unreachable" messages generated in response. • The related ping utility is implemented using the ICMP "Echo request" and "Echo reply" messages.
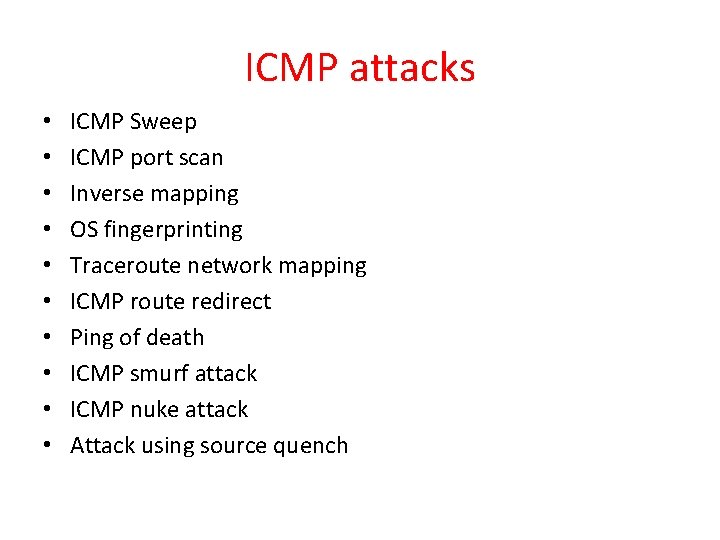
ICMP attacks • • • ICMP Sweep ICMP port scan Inverse mapping OS fingerprinting Traceroute network mapping ICMP route redirect Ping of death ICMP smurf attack ICMP nuke attack Attack using source quench
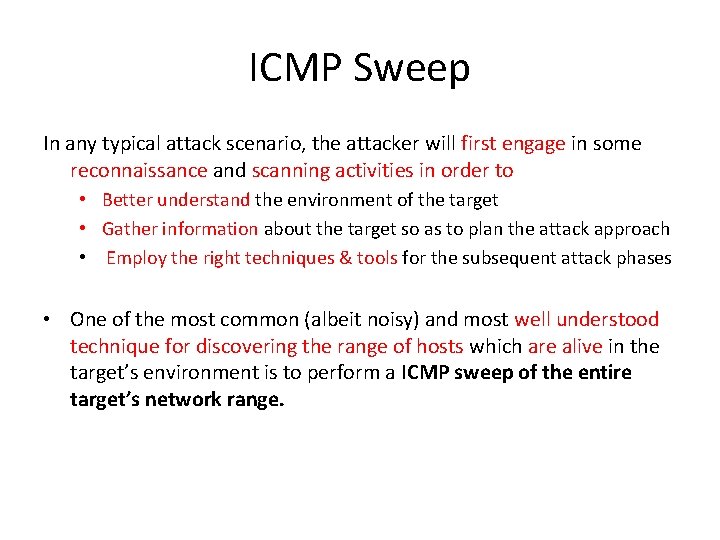
ICMP Sweep In any typical attack scenario, the attacker will first engage in some reconnaissance and scanning activities in order to • Better understand the environment of the target • Gather information about the target so as to plan the attack approach • Employ the right techniques & tools for the subsequent attack phases • One of the most common (albeit noisy) and most well understood technique for discovering the range of hosts which are alive in the target’s environment is to perform a ICMP sweep of the entire target’s network range.
• An ICMP sweep involves essentially sending a series of ICMP request packets to the target network range and from the list of ICMP replies infer whether certain hosts are alive and connected to the target’s network for further probing • Although the above attack can be done manually via a very simple command ping, many automated scanning tools (E. g. nmap (http: //www. insecure. org/nmap) and Superscan (http: //www. foundstone. com/rdlabs/proddesc/superscan. html)) will speed up the entire scanning process by performing such a scan on all possible IP address range given a target network.
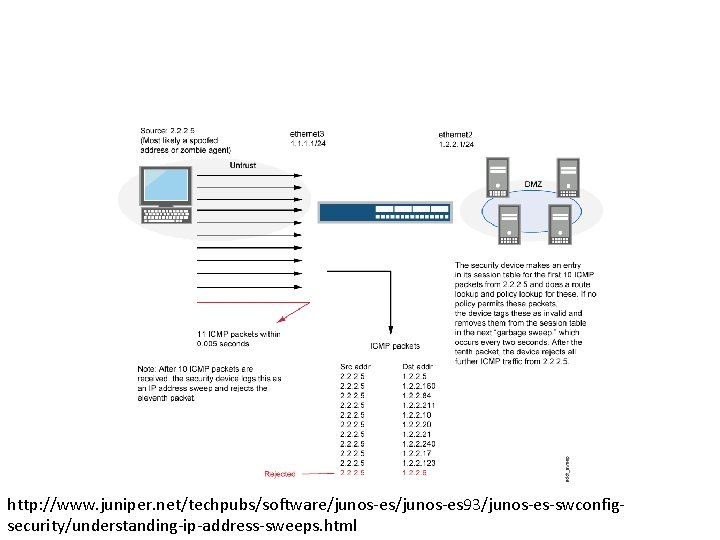
http: //www. juniper. net/techpubs/software/junos-es 93/junos-es-swconfigsecurity/understanding-ip-address-sweeps. html
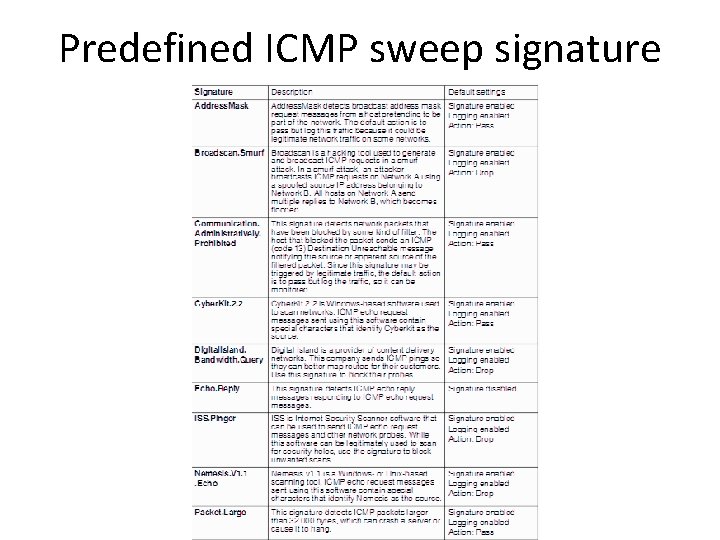
Predefined ICMP sweep signature
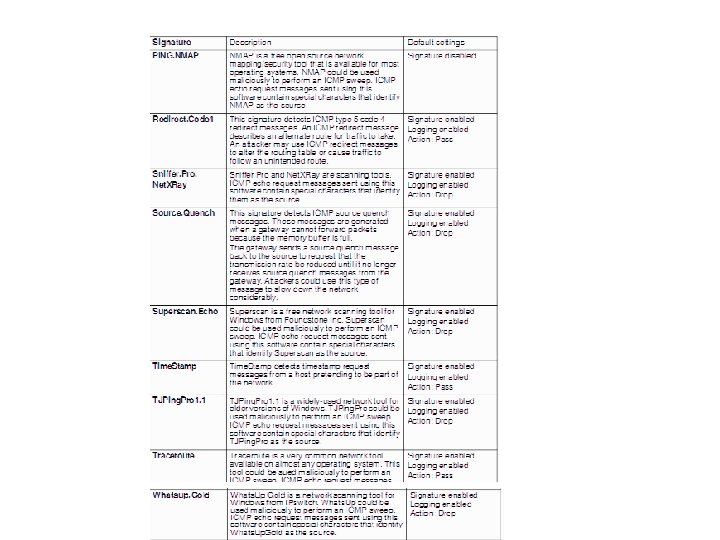
• The ICMP Sweep threshold maximum is set to 128 ICMP packets per second Port Scan threshold maximum is set to 512 Syn/sec
ICMP port scan
Firewalk • • Developing further from the traceroute idea, this next technique (Firewalk) can be used to identify ports that are open on a packet filtering firewall. The purpose of doing so is really to map out the filtering rules that are being set up in a packet filtering firewall. Firewalking is typically done in 2 phases: phase 1 involves doing a traceroute from the attacker to the target firewall to ascertain the number of hops it will take for a packet to reach the firewall. During the scanning phase, TTL value of packets will be set to one greater than the firewall and send to a known host behind the firewall. If an ICMP “time exceeded” message is received, that would mean that the packet has managed to get past the firewall and thus causing an ICMP packet to be returned by the known host because TTL value has now reached zero, otherwise it can be deduced that there is a filtering rule on the firewall which stops the traffic. Firewalk can be found at (http: //www. packetstormsecurity. com/UNIX/audit/firewalk/).
Inverse mapping Inverse Mapping is a technique used to map internal networks or hosts that are protected by a filtering device. • Usually some of those systems are not reachable from the Internet. Networks are protected by filtering devices, such as, firewalls and gateways that prevent internal hosts from being reached externally. An Inverse Mapping attack is illustrated below: Step 1. Attacker sends an ICMP reply message to a range of IP addresses presumably behind a filtering device. Step 2. Upon receiving the series of ICMP reply messages, since the filtering device does not keep state of the list of ICMP requests, it will allow these packets to their destination. Step 3. If there is an internal router, the router will respond with a ICMP “Host Unreachable” for every host that it cannot reach, thus giving the attacker knowledge of all hosts which are present behind the filtering device.
OS fingerprinting • • Before any attack can be launched, other than knowing the existence of the target host, it would be extremely beneficial to know the underlying operating system as well as the list of services that it runs. While port scanners can determine the types of services that are being offered on the system, ICMP could again be engaged in helping the attacker determine the underlying operating system. The advantage of using ICMP protocol in a remote OS fingerprinting exercise offers the attacker a more stealthy way in OS identification process. In some instances only a single packet is sent to determine the operating system used by the target system. Remote OS Fingerprinting is a technique that exploits the fact that different operating system vendors have built a slightly different way of handling network traffic. • A remote OS Fingerprinting attack is illustrated below: Step 1. Attacker sends an UDP packet with DF bit set to a target host whose UDP port is closed. Step 2. An ICMP “Destination unreachable port” message will be returned to the attacker. Step 3. Due to the fact that different hosts will send a slightly different ICMP packet back, operating systems can be determined by examining several bits in the return packet.
• • • E. g. If we look at the precedence bits field of the packet and the value is 0 xc 0, the underlying operating system can most likely be deduced to be a Linux kernel 2. 0. x / 2. 2. x /2. 4. x based machine or a Cisco based router or a Extreme Networks switch. In this instance, to differentiate between the Linux kernel and that of the networking device, ICMP Error Quoting size fingerprinting method can be employed. In this method, the returned ICMP packet is inspected for the number of bytes that are being returned. Linux kernel will return a different number of bytes as compared to networking device, thus we are able to differentiate them. One step further is to be able to differentiate between the various versions of the Linux kernel. In this case we will be looking at the IP TTL value set in the packet, Linux kernel 2. 0. x has got an initial value of 64 whereas 2. 2. x and 2. 4. x will use an initial value of 255. Now to differentiate between the 2. 2. x and 2. 4. x is to look at the IP ID value of the packet, 2. 4. 1 – 2. 4. 4 has got a value equals to zero unlike 2. 2. x. Thus just by looking at 1 return packet from the target, the attacker is able to drill down to the type and version of the underlying operating system. Other techniques like checking how a host responds to a crafted ICMP timestamp request are also employed to differentiate between operating systems. X Probe available at (http: //xprobe. sourceforge. net/) is a tool build to allow you do the above in an automated manner.
Phase 2 – Exploiting Systems • Often an attacker will need to identify what system they are about to attack before they can exploit a vulnerability. • In this technique, the attacker relies upon the operating system manufacturer to have built their communications system slightly differently from other operating systems, the steps to recreate this technique are: • The attacker sends malformed ICMP packets to the destination. • The destination host will respond with numerous answers to the given requests. • Each operating system will send slightly different results back to the host. • The installed operating system is determined by a process of elimination by evaluating the responses. • This flaw in the development of the operating system, allows specially designed tools to examine the structure of the returned ICMP data and determine the likely operating system.
Traceroute network mapping • • • This command sends out progressively a series of packets with an increasing TTL (Time to Live) value set. When an intermediate router receives a forwarding packet, it’ll decrement the TTL value of the packet before forwarding it to the next router. At this time if the TTL value of the packet reaches zero, an ICMP “time exceeded” message will be send back to the originating host. By sending the packet with initial TTL value of 1 will allow the first router in the path of the packet to now send back an ICMP “time exceeded” message which will then allow the attacker to know the IP address of the first router. Subsequent packets are send by increasing the TTL value in the packet by 1 each time, thus the attacker will be able to know every hop between him and the target. • Using this technique, the attacker could not only trace the path taken by a packet as it travels to the target but also gives him information on the topology of the target network. • This information is crucial in allowing the attacker plan his approach when attacking the network. • A network-mapping tool like Cheops (http: //www. marko. net/cheops) would allow the attacker to quickly map out the entire target network using ping and traceroute. This tool is a very noisy tool from a traffic perspective and can be easily picked up by any intrusion detection system as well as firewall logs.
ICMP route redirect • An ICMP Route Redirect message is sent when a gateway receives an IP traffic from a host and finds in its routing table that its next gateway to be routed to for this traffic is on the same network as the host.
Step 1. Attacker manages to take over a secondary gateway G 1 of the source host. Step 2. Attacker sends a TCP open packet to source host acting as destination host. Step 3. While a reply is in transit from the source host to the destination host through gateway G 2, the attacker sends an ICMP route redirect message to source host spoofing as G 2. Step 4. Source host will accept the route change control message as valid and thus changes its routing table to now route all traffic bound for destination host through Gateway G 1. Step 5. Now attacker will quietly read/modify and forward all traffic bound for destination host to Gateway G 2 acting as a Man-In-The-Middle host.
• One of the main functions of ICMP is to provide the ability to redirect routing. • For example another route has been found to be more efficient or a route failure been discovered. • The route redirect technique exploits this function by allowing a false ICMP packet to be transmitted telling a target host that they must route information through a new gateway, the “attacker”. • After the traffic is re-routed through the attacker, it can be monitored using a packet sniffing application.
ICMP informational messages • By sending “oversized” ICMP messages to a target host could potentially crash / reboot the target host. • This is due to the fact that some OS does not know how to handle packets that are larger than the maximum size as stipulated in RFC. • The TCP/IP specification allows for a maximum of 65536 octets in a single packet of information. • This exploit can easily be exploited through the use of the ping command (with a flag to indicate the size of the packet to be send) by using a packet size greater than 65536 octets. • Some OS will perform checks on the size of the outgoing packets • and will not allow packets greater than 65536 octets. • There are many tools that are available for download that will allow the attacker to create customized ping packets. • One such example is hping 2 (http: //www. securityfocus. com/tools/641).
• • If the target host is not properly patched, the OS will freeze or reboot after receiving just oversized packet. By exploiting the nature of fragmentation as well as oversized ICMP packets, another exploit is possible that will cause some OS to stop responding and have to resort to a reboot to recover from these attacks. SSPing (http: //packetstormsecurity. org/Exploit_Code_Archive/ssping. zip) is a tool that does just that. Developing further from this idea is another tool Jolt 2 (http: //razor. bindview. com/publish/advisories/adv_Jolt 2. html) In this attack, sending large numbers of identical fragmented IP packets to the target host will cause the host to stop responding for the period of time when the attack is in progress. Another tool teardrop (http: //packetstormsecurity. org/Exploit_Code_Archive/teardrop. c) sends a stream of fragmented packets to the target host and asks it to put them back together. When the host tries to do so, it discovers that the packets are not the size they say they are. This causes the target host to hang and require a re-boot before it will function again.
ICMP Router Discovery Messages • Before a host is able to send a message to a host outside its own subnet, it must be able to identify the address of the immediate router. • This is typically done through reading a configuration file upon startup and on some multicast network by listening to routing protocol traffic. • An extension to the ICMP protocol called “ICMP Router Discovery Protocol” (defined in RFC 1256 - http: //www. faqs. org/rfcs/rfc 1256. html) is able to use “router advertisement” as well as “router solicitation” messages to allow hosts to find out the IP addresses of the router that is attached to their immediate network. • When a host is being started up, it will make use of the “router solicitation” messages to check for the address of the immediate router. • Since these messages are not authenticated, attackers on the same subnet as the host can spoof these messages.
ICMP Router Discovery Messages A possible attack scenario: Step 1. Host boots up and issues a “router solicitation” message to find out the default router on the network. Step 2. Attacker listens in to the message and spoofs a reply to that host. Step 3. The default route of the host is now set to the attacker’s IP address that the attacker has included in his reply. Step 4. Now the attacker could employ either sniffing, man-in-themiddle attack for all traffic outbound through the attacker’s machine. Step 5. Denial of service attack is also possible by not forwarding any packets onto the correct subnet.
ICMP Floods • By flooding the target host with great amounts of ICMP messages will leave the attacked host and its associated network with degraded performance or even total denial of service in some instance. • Smurf (http: //cs. baylor. edu/~donahoo/NIUNet/hacki ng/smurf. c) attacks are clever: • They use whole networks
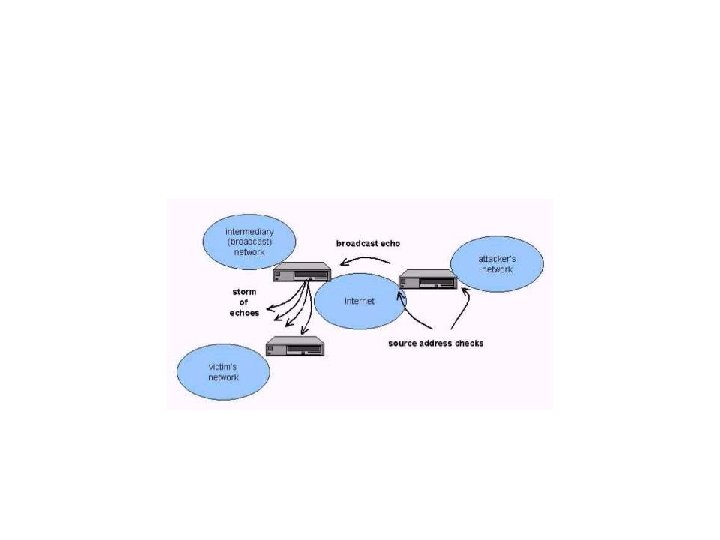
Step 1. Attacker finds some intermediary network that will respond to the network’s broadcast address. Step 2. Attacker spoofs the IP address of the victim host and sends a great number of ICMP echo request packets to the broadcast address of the above intermediary networks. Step 3. Now all the hosts on that network will respond to that ICMP echo request with a corresponding ICMP reply request back to the spoofed IP address (the victim). Step 4. This will send a whole bunch of ICMP echo replies to the victim and its network thus causing network degradation or a total denial of service.
• Phase 3 - Keeping Access & Covering The Tracks After an attacker has successfully compromised a system, • one of the ways to hide information as it is being transmitted across a network is to use a technique called tunneling. • Tunneling involves hiding one protocol inside another protocol. Loki 2 is one such implementation discussed in (http: //www. phrack. org/show. php? p=51) which uses ICMP and UDP protocol tunneling to obtain a reverse shell from an attacked system. • The steps to using Loki 2 is illustrated below: Step 1. Attacker gets root on a victim system. Step 2. Attacker gets Loki 2 and compiles it on the machine. Step 3. Attacker now launches Loki 2 client on the attacking machine and gets a reverse shell on the victim host. Step 4. Now attacker has shell access to victim’s machine while tunneling traffic through normal ICMP data packets.
• In such an attack, the traffic that is being exchanged between the Loki client & Loki server is almost covert as there are no listening ports opened on the victim machine and even the traffic could be encrypted with an encryption algorithm like Blowfish or DH for additional covertness. • Loki 2 when implemented as a kernel module would be even stealthier as it would not even have a process that will sit and wait for the ICMP traffic that can potentially be detected by an alert administrator. • Taking stock of the recent Distributed Denial Of Service (DDOS) attacks, we have seen that ICMP have been used in almost all of those tools for covert communications between the DDOS client and the attacker’s handler program. • Few examples are TFN 2 K and Stacheldraht
Ping of death • The attacker sends excessively large ICMP messages to a target host. • Exploiting the weakness in operating system’s implementation of the TCP/IP specification, the attacker can send an ICMP packet greater than the maximum of 65535 octets allowed. • The host may become unavailable as a buffer overflow may be created based on the operating system. • The computer may crash, force a reboot or make the host hang. • A similar attack can be achieved by sending multiple fragmented ICMP packets that requires the operating system to restructure the data on arrival. • On examination, the operating system discovers that the packets are not the size they say they are and as a result it forces the machine to hang or reboot.
ICMP smurf attack • This attack exploits the weakness in the ICMP and IP protocols by forging the original source address of the packet with the address of the machine to be attack. • This “spoofing” hides the attacker, and begins a chain reaction of network disruption.
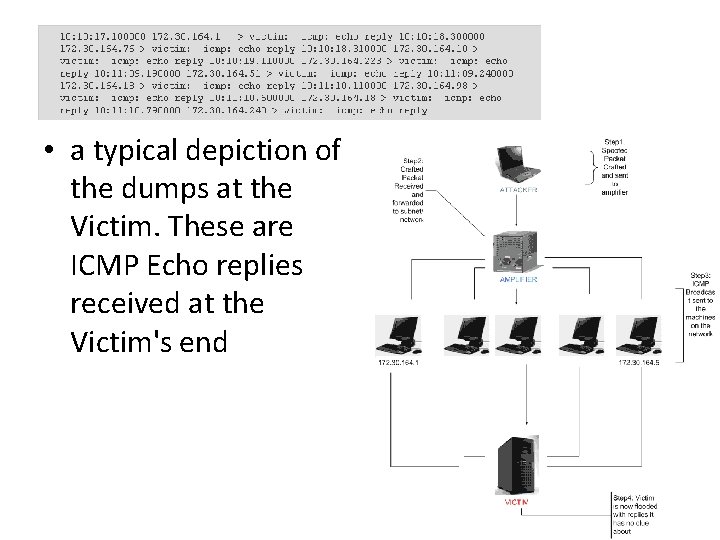
• a typical depiction of the dumps at the Victim. These are ICMP Echo replies received at the Victim's end
How to protect against Smurf attacks • • • Step 1. Amplifier Configuration. The router should be configured so that it does not forward directed broadcasts onto networks. It is important to note that the broadcast has to be disabled on all the routers and not merely just the external ones. Command "no ip directed-broadcast" on Cisco routers should do the job in most cases. This will also ensure that employees on the internal network won't be able to launch Smurf attacks. However it is also advisable that one has a filtering device (such as a firewall) on the perimeter, thereby providing an extra layer of security. Step 2. Configure the server operating systems. Servers should be configured so that they will not respond to a directed broadcast request. Free. BSD is one such system which by default does not respond to this request. Other systems can be similarly configured, and this will be discussed in the next section. Step 3. Victim issues. As mentioned earlier, not much can be done at the victim's end and damage will be done unless victim's ISP takes some actions to block these ICMP Echo Reply floods. Even if the victim's parameter router denies the ICMP Echo Reply, the link from the ISP to the victim's site will suffer.
ICMP nuke attack • A Nuke is an old denial-of-service attack against computer networks consisting of fragmented or otherwise invalid ICMP packets sent to the target. • It can be achieved by using a modified ping utility to repeatedly send this corrupt data, thus slowing down the affected computer until it comes to a complete stop. • Nukes send a packet of information that the target OS can't handle, which causes the system to crash. • A specific example of a nuke attack that gained some prominence is the Win. Nuke, which exploited the vulnerability in the Net. BIOS handler in Windows 95. • A string of out-of-band (OOB) data was sent to TCP port 139 of the victim's machine, causing it to lock up and display a Blue Screen of Death (BSOD). • Port 139 is the Net. BIOS port, which does not accept packets unless the flag OOB is set in the incoming packet. • The machine is unable to handle this packet and exhibits odd behavior, ranging from a lost Internet connection to a denial of service and system crash.
Attack using source quench • ICMP source quench messages are generated when a gateway device runs out of buffer space. • It is an informational message that is generated in an attempt to inform the remote host generating the traffic to limit the speed at which it is sending network traffic to the remote host. • Denial of Service attackers could potentially use ICMP source quench datagrams to rate limit a remote host that listens to unsolicited ICMP source quench datagrams. • The attacker needs to guess the sequence number and also match • the same with that of the connection. • The need to guess the connection source port will lead to many Source Quench messages which do not correspond to an existing connection.
• An ICMP source quench message (ICMP type 4, code 0) is designed to be issued when a router is unable to handle the volume of packets coming in. • It is a request for the sender to lower the volume of incoming traffic. • When a router between two endpoints or the remote endpoint itself begins to run out of buffer space for processing incoming packets, it can send a source quench ICMP packet to the endpoint from where the traffic originated. • As defined in RFC 792, when an endpoint receives a source quench packet it should slow the rate at which it is sending out packets. • After ten minutes, the endpoint should gradually increase the rate at which it's sending packets up to the original rate.
• • • However, this method of flow control is long out-of-date, with RFC 1812 saying the routers should not issue these packets. Nevertheless, a source quench packet was detected. This event may be indicative of an attacker attempting to perform a denial of service in the form of lowered bandwidth. In this case of such an attack, the attacker would construct the ICMP payload so that it corresponds to a TCP packet with IP addresses and ports corresponding to the connection being targeted. The attacker may need to make the sequence number match that of the connection as well, guessing if needed. This, combined with the possible need to guess the connection source port, may mean there a number of Source Quench messages, with most not closely corresponding to an existing connection. It should also be noted that these packets are normally left unfiltered by most packet-filtering firewalls and other intrusion prevention devices. source quench messages can also be abused. If the messages are spoofed at a high enough rate, a TCP connection can be slowed to a crawl. "While this would not reset the connection, ”, "it would certainly degrade the performance of the data transfer taking place. “ Fortunately the solution is, "you can just completely disable ICMP source quenching for TCP because the TCP protocol has its own handling for these conditions, and routers, as specified by RFC 1812, should not be sending source quench packets either. "
Experimental Setup • • Send from the attack platforms attack IP packets containing ICMP source quench messages used to request the target to decrease traffic rate. The parameters defined includes – – – TOS randomized, TTL set at 64, randomized identifiers, IP options enabled and other IPv 4 header settings. The protocol field set at 1 for ICMP protocol. Binary string payload consists of ICMP type set at 04 and ICMP code at 00. All three interfaces (SIP, billing and admin) targeted for this attack. • Repeat this attack with packet rate ranging from 199 packets/sec to 100, 000 packets/sec and randomizing the source IP address and MAC address. • • • Observations The attacks were blocked and the server log indicated that the IP addresses (static and spoofed random addresses) of the attack platform were blacklisted for 30 seconds. No calls were dropped and the SIP phones did not lose service. http: //wiki. siemens-enterprise. com/images/6/6 b/Miercom-OSC-Voice-V 4 -Certified-Secure-Report. pdf
ICMP Ping Flood attacks • Ping Floods are where an attacker floods the victim's network with large number of ICMP Echo Requests - such as by flooding the network as fast as possible. • In this scenario, filtering the incoming packets might help, however, if the victim is on a modem instead of a high-speed connection, nothing can be done. • However the catch in this attack is that if not done properly the attacker can also be counter-attacked, so he needs to be on a faster network than the victim. • In most cases, mitigating this attack involves isolating spoofed IPs. • This attack is easy to perform since there are many tools on Internet and little knowledge is required to execute a ping flood.
Fraggle attacks • A Fraggle attack is a Smurf variant that uses UDP instead of ICMP. • In this case, the ports echo, chargen, daytime, qotd are used to trigger responses. • These ports are also susceptible to a pingpong attack, and therefore these servers should be turned off or blocked.
ICMP Fragment Protection • Number of ICMP fragments. • Because ICMP packets contain very short messages, there is no legitimate reason for ICMP packets to be fragmented. • If an ICMP packet is so large that it must be fragmented, something is amiss.
Ping of Death Attack • Protection • ICMP ping of death counter. Ping of death occurs when IP packets are sent that exceed the maximum legal length (65, 535 bytes).

• To continuously monitor multiple Snort sensors just to make sure everybody is up and running. This rule is as follows: • alert icmp 192. 168. 1. 4 any -> 192. 168. 1. 1 any (msg: "HEARTBEAT"; ) • My Snort sensor IP address is 192. 168. 1. 4 and gateway address is 192. 168. 1. 1. I • run the following command through cron daemon on the Linux machine to trigger this rule every 10 minutes. • ping -n 1 192. 168. 1. 1 • The command sends exactly one ICMP packet to the gateway machine. This packet causes an alert entry to be created. If there is no alert every 10 minutes, there is something wrong with the sensor.
• In case of TCP or UDP protocol, the port parts determine the source and destination ports of a packet on which the rule is applied. • In case of network layer protocols like IP and ICMP, port numbers have no significance.
• One particular issue is that in some cases a packet which causes an error to be reported back via ICMP might be so large as not to entirely fit within the ICMP message returned. • In such cases, it might not be possible for the receiver of the ICMP message to independently authenticate the portion of the returned message. • This could mean that the host receiving such an ICMP message would either trust an unauthenticated ICMP message, which might in turn create some security problem, or not trust and hence not react appropriately to some legitimate ICMP message that should have been reacted to. • It is not clear that this issue can be fully resolved in the presence of packets that are the same size as or larger than the minimum IP MTU. • Similar complications arise if an encrypted packet causes an ICMP error message to be sent and that packet is truncated.
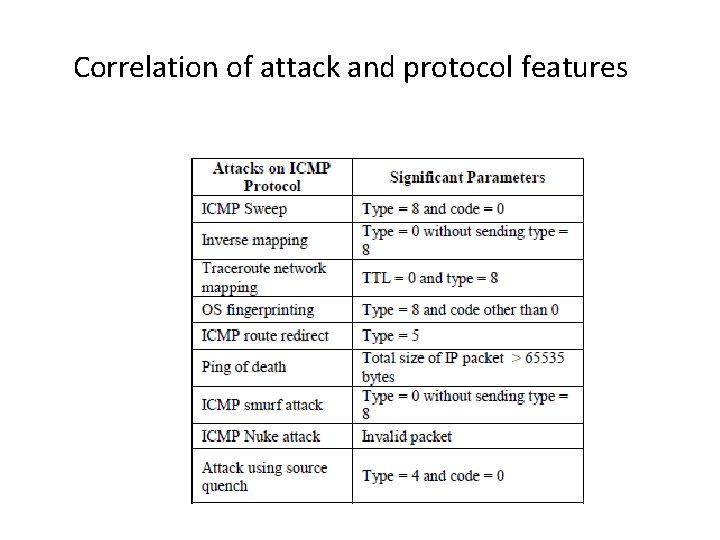
Correlation of attack and protocol features
Experiment setup • Network setup: Two of the hosts to launch ICMP based attacks on the third host • Use wireshark to collect the packet captures in the victim system • launched ICMP sweep, smurf, OS fingerprinting and traceroute on the victim host from attacking hosts • nmap , sing and traceroute tools to launch attacks. • created dataset of network traces having ICMP attack data on it. Save in standard pcap format. • Carry out other internet activity by the users and record this legitimate traffic also in the file. • Apply for reduction of the dataset • Mark suspicious packets ICMP packets • Create Database of attributes of the marked packets.
Teardrop attack • In a Teardrop attack, the length and fragmentation offset fields of sequential IP packets are modified causing the target system to and crash. • This is a rarely seen attack these days as most modern TCP/IP stacks handle such malformed packets gracefully. • win. Nuke, Ssping
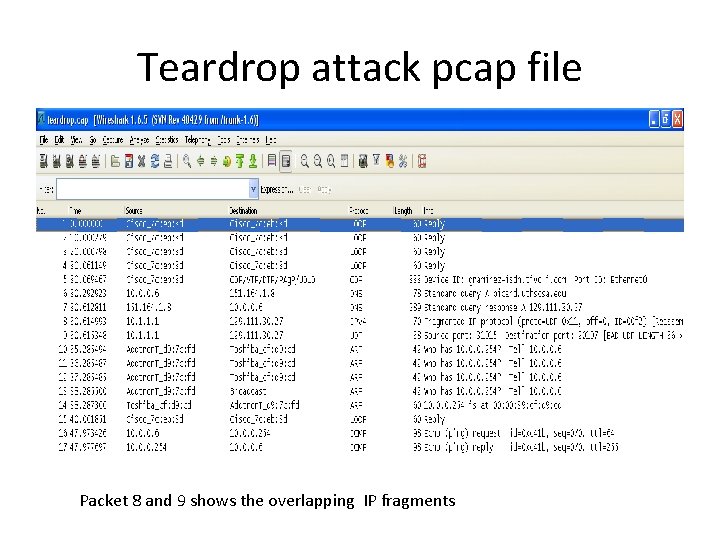
Teardrop attack pcap file Packet 8 and 9 shows the overlapping IP fragments
• ICMP can be used in many phases of an attacker’s advance in a system compromise. • In many instances, tools are easily available on the Internet for download. • ICMP is not just being used in the reconnaissance & scanning phase which is most understood but it has also been used for exploiting systems as well as in certain instances as a covert channel for attacker’s communication.
ICMP attack against TCP • mechanism called "Path MTU Discovery" (PMTUD), which makes use of ICMP error messages of type 3 (Destination Unreachable), code 4 (fragmentation needed and DF bit set) to allow hosts to determine the MTU of an arbitrary internet path. For obvious reasons, those systems implementing the Path MTU Discovery (PMTUD) mechanism do not treat ICMP error messages of type 3 code 4 as hard errors.
• • This signature detects MTU values less than the minimal in an ICMP V 4 Packet (Type: 3 and Code: 4). ICMP functionality named 'Path MTU Discovery' (PMTUD) is available. When this functionality is used by network hosts, the 'hard' error Type 3, code 4 (Fragmentation needed and DF bit set) for IPV 4 networks is not treated as a hard error, rather as a method to determine the MTU of a connection. For IPv 6 the ICMP message Type 2, code 0 (Packet too big) is employed in a similar manner. PMTUD allows a network node to determine the MTU of an arbitrary network path. An attack against ICMP PMTUD is reported to affect multiple vendors when they are configured to employ PMTUD. If PMTUD is disabled PMTU packets may potentially be employed to trigger a blind connection-reset. By sending a suitable forged ICMP message to a target host, (Type 3, code 4 Fragmentation needed and DF bit set for IPV 4 networks, and Type 2, code 0 Packet too big for IPV 6 networks), an attacker may reduce the MTU for a given connection. The ICMP header will need to contain the source and destination IP address and port pair of the targeted connection. This would result in a degradation of connection performance. The minimum MTU for IPv 4 networks is 68 octets and 1280 octets for IPV 6 networks. A remote attacker may exploit this issue to degrade the performance of TCP connections and partially deny service for legitimate users.
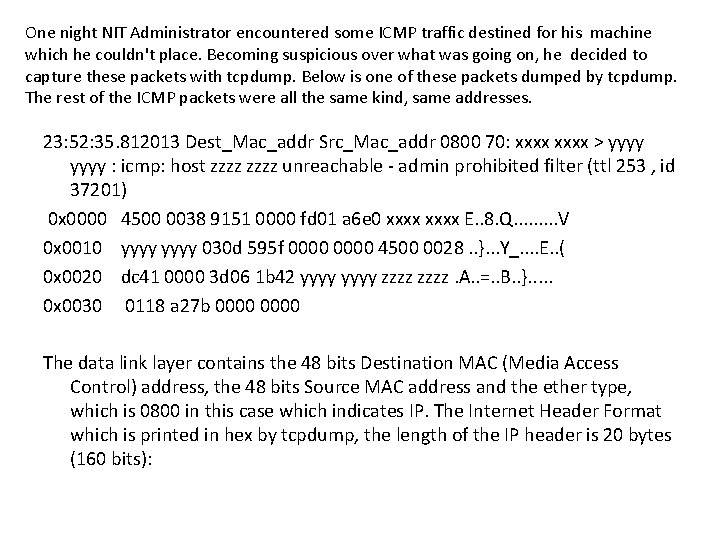
One night NIT Administrator encountered some ICMP traffic destined for his machine which he couldn't place. Becoming suspicious over what was going on, he decided to capture these packets with tcpdump. Below is one of these packets dumped by tcpdump. The rest of the ICMP packets were all the same kind, same addresses. 23: 52: 35. 812013 Dest_Mac_addr Src_Mac_addr 0800 70: xxxx > yyyy : icmp: host zzzz unreachable - admin prohibited filter (ttl 253 , id 37201) 0 x 0000 4500 0038 9151 0000 fd 01 a 6 e 0 xxxx E. . 8. Q. . V 0 x 0010 yyyy 030 d 595 f 0000 4500 0028. . }. . . Y_. . E. . ( 0 x 0020 dc 41 0000 3 d 06 1 b 42 yyyy zzzz. A. . =. . B. . }. . . 0 x 0030 0118 a 27 b 0000 The data link layer contains the 48 bits Destination MAC (Media Access Control) address, the 48 bits Source MAC address and the ether type, which is 0800 in this case which indicates IP. The Internet Header Format which is printed in hex by tcpdump, the length of the IP header is 20 bytes (160 bits):
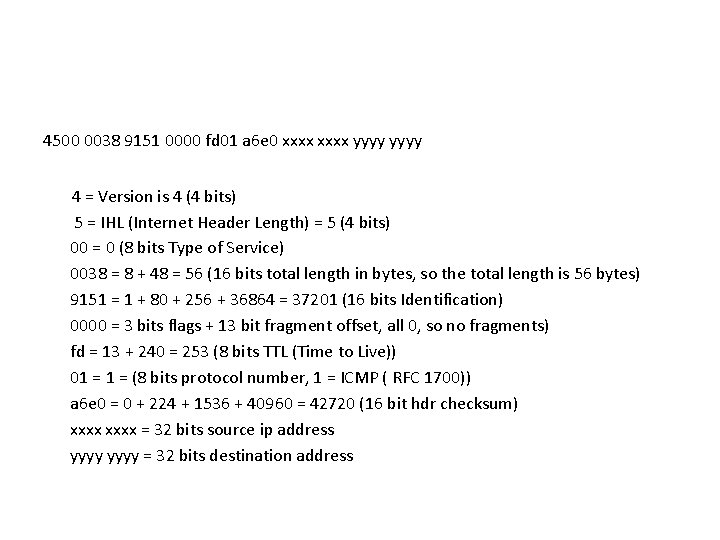
4500 0038 9151 0000 fd 01 a 6 e 0 xxxx yyyy 4 = Version is 4 (4 bits) 5 = IHL (Internet Header Length) = 5 (4 bits) 00 = 0 (8 bits Type of Service) 0038 = 8 + 48 = 56 (16 bits total length in bytes, so the total length is 56 bytes) 9151 = 1 + 80 + 256 + 36864 = 37201 (16 bits Identification) 0000 = 3 bits flags + 13 bit fragment offset, all 0, so no fragments) fd = 13 + 240 = 253 (8 bits TTL (Time to Live)) 01 = (8 bits protocol number, 1 = ICMP ( RFC 1700)) a 6 e 0 = 0 + 224 + 1536 + 40960 = 42720 (16 bit hdr checksum) xxxx = 32 bits source ip address yyyy = 32 bits destination address
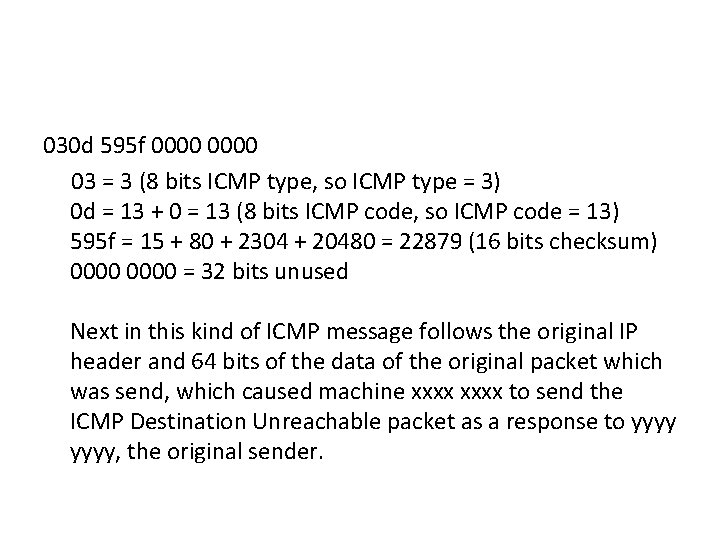
030 d 595 f 0000 03 = 3 (8 bits ICMP type, so ICMP type = 3) 0 d = 13 + 0 = 13 (8 bits ICMP code, so ICMP code = 13) 595 f = 15 + 80 + 2304 + 20480 = 22879 (16 bits checksum) 0000 = 32 bits unused Next in this kind of ICMP message follows the original IP header and 64 bits of the data of the original packet which was send, which caused machine xxxx to send the ICMP Destination Unreachable packet as a response to yyyy, the original sender.
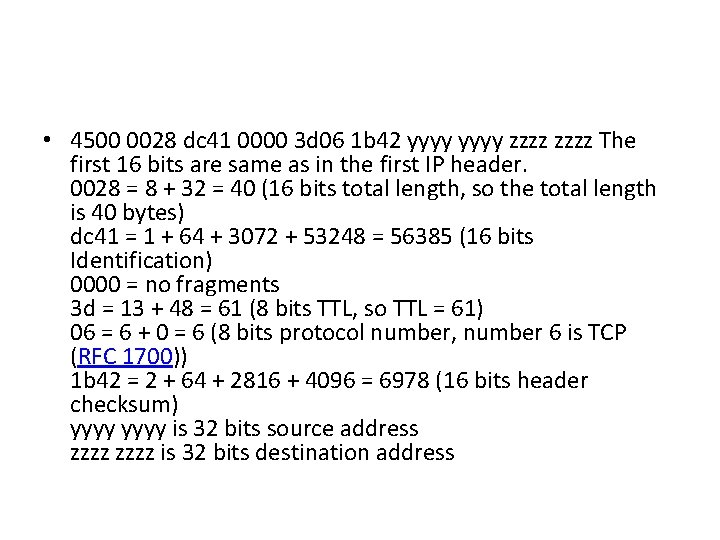
• 4500 0028 dc 41 0000 3 d 06 1 b 42 yyyy zzzz The first 16 bits are same as in the first IP header. 0028 = 8 + 32 = 40 (16 bits total length, so the total length is 40 bytes) dc 41 = 1 + 64 + 3072 + 53248 = 56385 (16 bits Identification) 0000 = no fragments 3 d = 13 + 48 = 61 (8 bits TTL, so TTL = 61) 06 = 6 + 0 = 6 (8 bits protocol number, number 6 is TCP (RFC 1700)) 1 b 42 = 2 + 64 + 2816 + 4096 = 6978 (16 bits header checksum) yyyy is 32 bits source address zzzz is 32 bits destination address
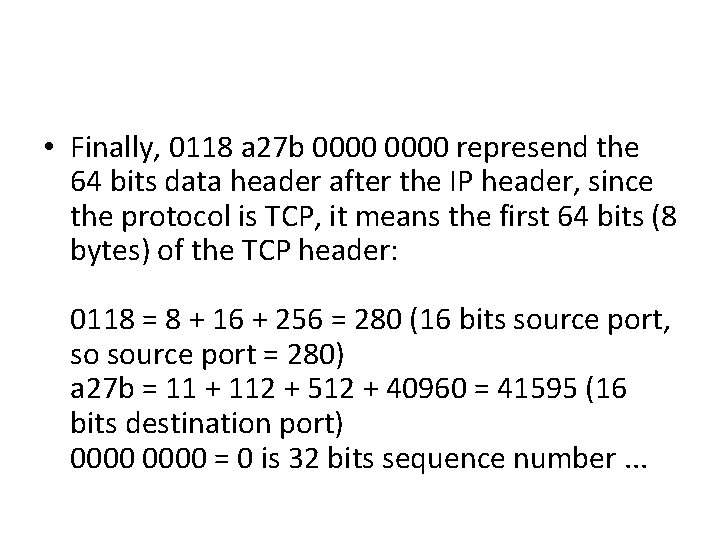
• Finally, 0118 a 27 b 0000 represend the 64 bits data header after the IP header, since the protocol is TCP, it means the first 64 bits (8 bytes) of the TCP header: 0118 = 8 + 16 + 256 = 280 (16 bits source port, so source port = 280) a 27 b = 11 + 112 + 512 + 40960 = 41595 (16 bits destination port) 0000 = 0 is 32 bits sequence number. . .
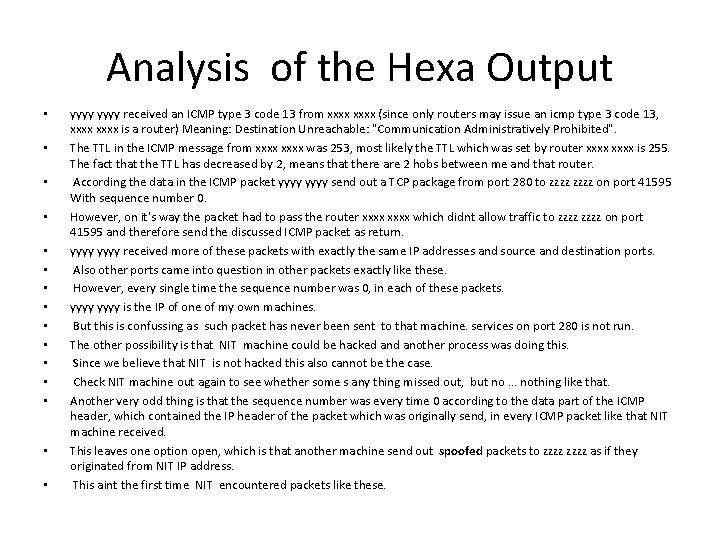
Analysis of the Hexa Output • • • • yyyy received an ICMP type 3 code 13 from xxxx (since only routers may issue an icmp type 3 code 13, xxxx is a router) Meaning: Destination Unreachable: "Communication Administratively Prohibited". The TTL in the ICMP message from xxxx was 253, most likely the TTL which was set by router xxxx is 255. The fact that the TTL has decreased by 2, means that there are 2 hobs between me and that router. According the data in the ICMP packet yyyy send out a TCP package from port 280 to zzzz on port 41595 With sequence number 0. However, on it's way the packet had to pass the router xxxx which didnt allow traffic to zzzz on port 41595 and therefore send the discussed ICMP packet as return. yyyy received more of these packets with exactly the same IP addresses and source and destination ports. Also other ports came into question in other packets exactly like these. However, every single time the sequence number was 0, in each of these packets. yyyy is the IP of one of my own machines. But this is confussing as such packet has never been sent to that machine. services on port 280 is not run. The other possibility is that NIT machine could be hacked another process was doing this. Since we believe that NIT is not hacked this also cannot be the case. Check NIT machine out again to see whether some s any thing missed out, but no. . . nothing like that. Another very odd thing is that the sequence number was every time 0 according to the data part of the ICMP header, which contained the IP header of the packet which was originally send, in every ICMP packet like that NIT machine received. This leaves one option open, which is that another machine send out spoofed packets to zzzz as if they originated from NIT IP address. This aint the first time NIT encountered packets like these.
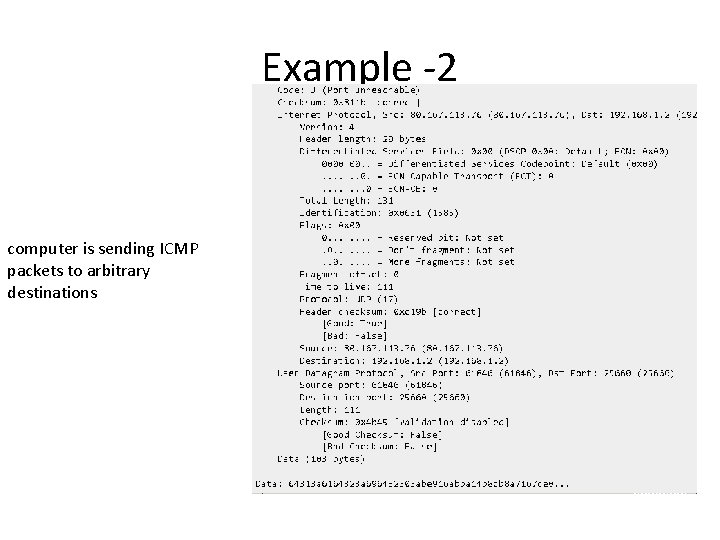
Example -2 computer is sending ICMP packets to arbitrary destinations
Analysis of the Dump • This is normal, and alone should not be reason for any worries. • the computer with IP 80. 167. 113. 76 sent an UDP packet to your computer, to port 25660. • Nothing is running in the computer waiting for UDP packets in this port. The computer sends this ICMP packet back to the origin telling that nothing was reached at the given port (ICMP Type=3 Code=3 → Port unreachable). • The ICMP packet contains a copy of the headers of the packet originally sent (in the opposite direction). • If this information is received from a packet sniffer (wireshark? ), then look for an incoming UDP packet from that IP arriving before this packet. • an ISP is dynamically assigns IP addresses to users. • Probably the current IP address was being used by someone running some P 2 P application, and the IP plus this port combination was cached on someone else's application, and then that one tried to connect back to the original user who was using this IP. Alternate Solution • install a stateful firewall that simply DROPs packets for non-tracked sessions. • Instead of sending a "Port Unreachable" message to the origin, the firewall simply drops the original packet since it will not be in its internal connection table.
• tcpdump -nnv. XSs 0 -c 2 icmp
• How to Detect if a Linux server is under an ICMP SMURF attack • ICMP attack is still heavily used, even though it’s already old fashioned and there are plenty of other Denial of Service attack types, one of the quickest way to find out if a server is under an ICMP attack is through the command: server: ~# while : ; do netstat -s| grep -i icmp | egrep 'received|sent' ; sleep 1; done 120026 ICMP messages received 1769507 ICMP messages sent
Tribe flood Network • The Tribe Flood Network or TFN is a set of computer programs to conduct various DDo. S attacks such as ICMP flood, SYN flood, UDP flood and Smurf attack. • Tribal Flood Network (TFN), like trinoo, is a classic DDo. S attack, using a master program and multiple agents on multiple compromised systems. Unlike trinoo it can spoof the source IP for the agents, and can generate multiple types of attack (including UDP flood, TCP SYN flood, ICMP echo request flood, and ICMP directed broadcast). TFN 2 K is a more sophisticated version of the original TFN. • First TFN initiated attacks are described in CERT Incident Note 99 -04 • TFN 2 K was written by Mixter, a security professional and hacker based in Germany.
• Wi-Fi Protected Setup (WPS) PIN Brute Force attack. • ICMP Tunneled Traffic Detection – ICMP tunneling is the practice of encapsulating Transmission Control Protocol (TCP) traffic inside ICMP packets. This technique can also be used to bypass payment and gain unauthorized connectivity through Wi-Fi Hotspots or other protected guest access portals.
References • • • Penetration Testing: Network Threat Testing, EC council Press Network Intrusion Detection 3 rd edition by Stephen Northcutt and Judy Novak. Atul Kant Kaushik and R. C. Joshi, "Network Forensic System for ICMP Attacks", International Journal of Computer Applications (0975 – 8887), Volume 2 – No. 3, May 2010, pp-14 -21 http: //code. google. com/p/bonesi/ Mitko Bogdanoski, and Aleksandar Risteski, Wireless Network Behavior under ICMP Ping Flood Do. S Attack and Mitigation Techniques, International Journal of Communication Networks and Information Security (IJCNIS) Vol. 3, No. 1, April 2011 http: //www. eventhelix. com/Realtime. Mantra/Networking/ http: //www. visualland. net/author/editor/ae 1. 0/AE. php http: //tools. ietf. org/html/draft-ietf-tsvwg-source-quench-06 http: //tools. ietf. org/id/draft-gont-tcpm-icmp-attacks-03. txt http: //ddos. arbornetworks. com/2012/02/ddos-tools/ http: //ddos. arbornetworks. com/2012/02/ddos-attacks-in-russia/
- Slides: 82