Evolution of the threat Cyber has been coopted

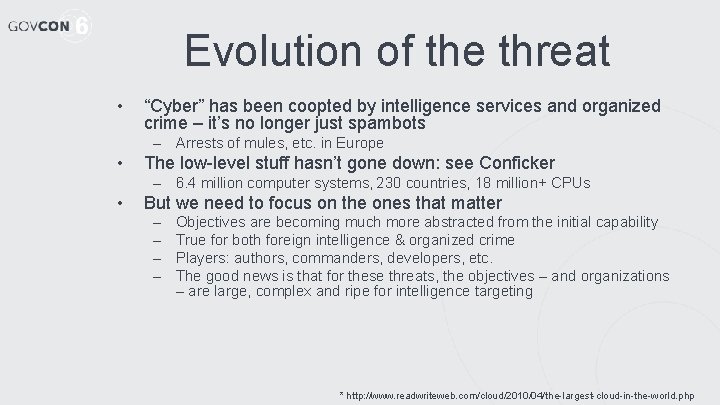
Evolution of the threat • “Cyber” has been coopted by intelligence services and organized crime – it’s no longer just spambots – Arrests of mules, etc. in Europe • The low-level stuff hasn’t gone down: see Conficker – 6. 4 million computer systems, 230 countries, 18 million+ CPUs • But we need to focus on the ones that matter – – Objectives are becoming much more abstracted from the initial capability True for both foreign intelligence & organized crime Players: authors, commanders, developers, etc. The good news is that for these threats, the objectives – and organizations – are large, complex and ripe for intelligence targeting * http: //www. readwriteweb. com/cloud/2010/04/the-largest-cloud-in-the-world. php
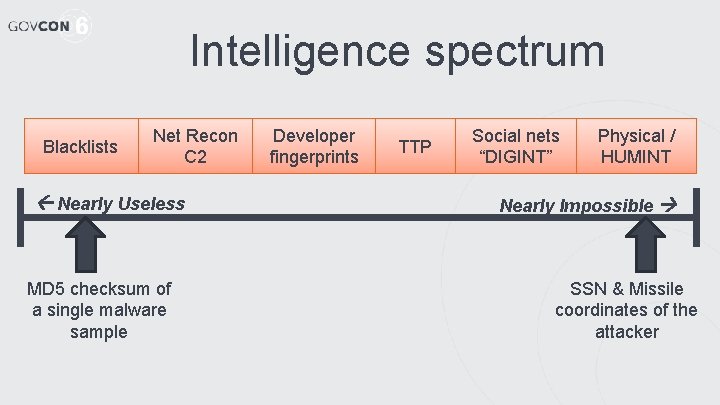
Intelligence spectrum Blacklists Net Recon C 2 Nearly Useless MD 5 checksum of a single malware sample Developer fingerprints TTP Social nets “DIGINT” Physical / HUMINT Nearly Impossible SSN & Missile coordinates of the attacker
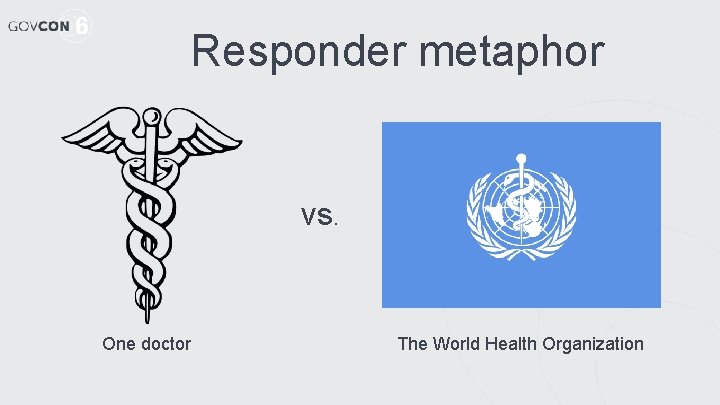
Responder metaphor vs. One doctor The World Health Organization
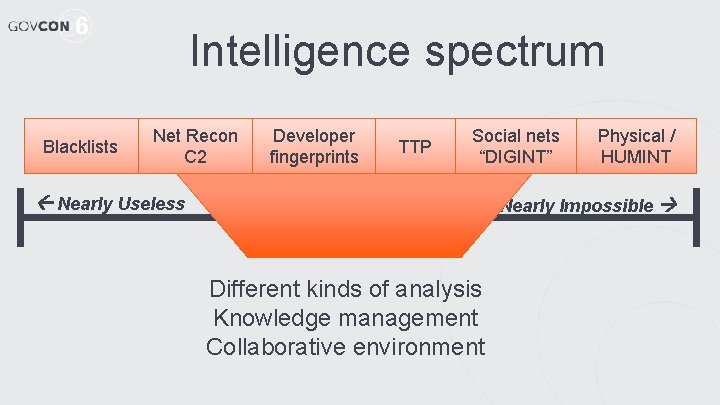
Intelligence spectrum Blacklists Net Recon C 2 Developer fingerprints TTP Social nets “DIGINT” Nearly Useless Physical / HUMINT Nearly Impossible Different kinds of analysis Knowledge management Collaborative environment
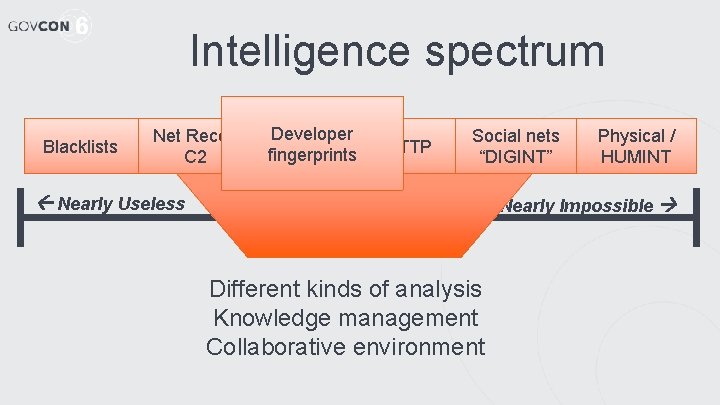
Intelligence spectrum Blacklists Net Recon C 2 Developer fingerprints TTP Social nets “DIGINT” Nearly Useless Physical / HUMINT Nearly Impossible Different kinds of analysis Knowledge management Collaborative environment
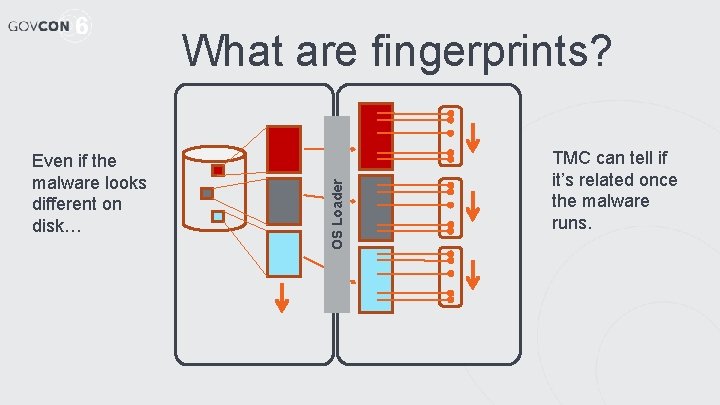
Even if the malware looks different on disk… OS Loader What are fingerprints? TMC can tell if it’s related once the malware runs.
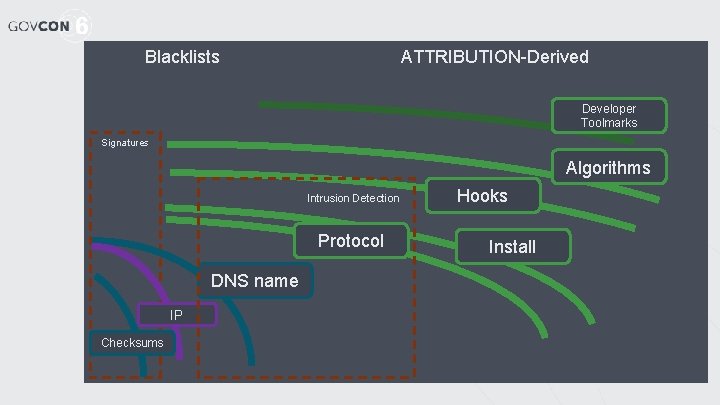
Blacklists ATTRIBUTION-Derived Developer Toolmarks Signatures Algorithms Intrusion Detection Protocol DNS name IP Checksums Hooks Install
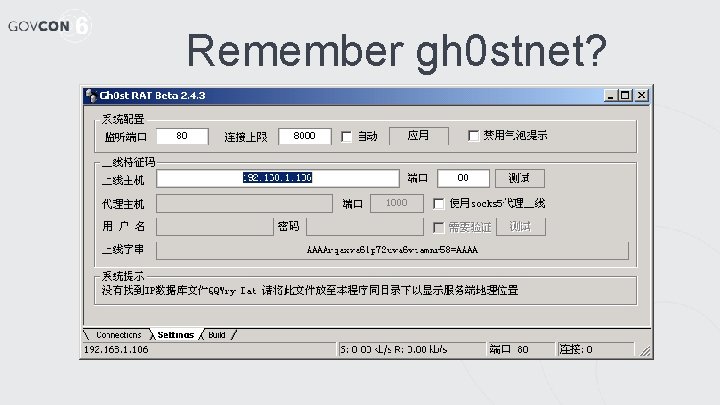
Remember gh 0 stnet?
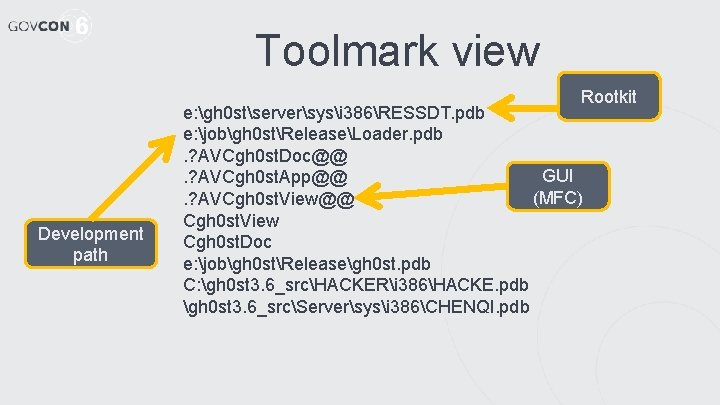
Toolmark view Rootkit Development path e: gh 0 stserversysi 386RESSDT. pdb e: jobgh 0 stReleaseLoader. pdb. ? AVCgh 0 st. Doc@@ GUI. ? AVCgh 0 st. App@@ (MFC). ? AVCgh 0 st. View@@ Cgh 0 st. View Cgh 0 st. Doc e: jobgh 0 stReleasegh 0 st. pdb C: gh 0 st 3. 6_srcHACKERi 386HACKE. pdb gh 0 st 3. 6_srcServersysi 386CHENQI. pdb
Integrated workflow • Having visual map of threats • Integrated w/ complete incident handling process – strategic threat process • Arcsight, centaur… • Need context to understand threat (v. incident) • Usable by folks less technical than malware analysts • Can help develop response
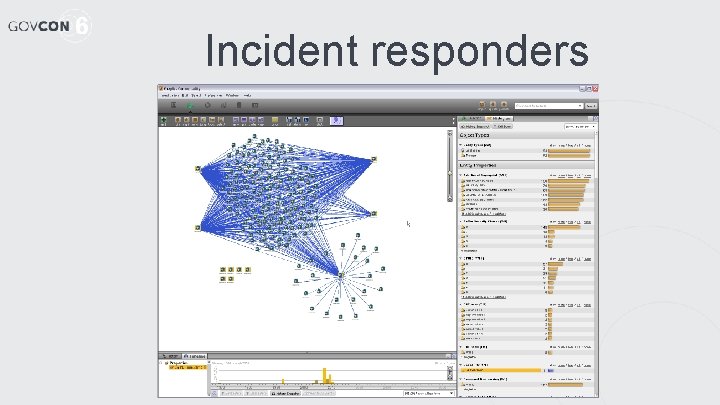
Incident responders
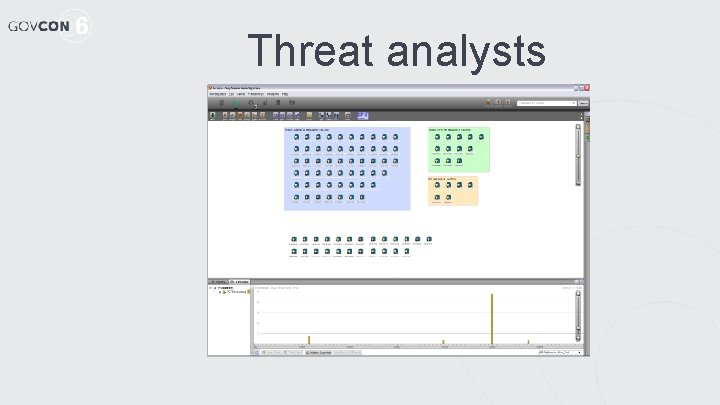
Threat analysts
Threat analysts
Fusion = Attribution • Fusion methodology integrating data from – – – • • Network-based technical collection Toolmarks Open source data Key informant interviews Field investigations Hacker forums Visual analysis Collective memory of prior attacks Still requires skilled analysts But it’s not magic.
Fusion = Attribution • Fusion methodology integrating data from – – – • • Network-based technical collection Toolmarks Open source data Key informant interviews Field investigations Hacker forums Visual analysis Collective memory of prior attacks Still requires skilled analysts But it’s not magic.
- Slides: 16