Evading Death by a Silver Bullet Effective Cyber
Evading Death by a Silver Bullet Effective Cyber Security Strategies for Digital Transformations 03/13/2019 Michael Gutsche – Chief Cyber Security Strategist
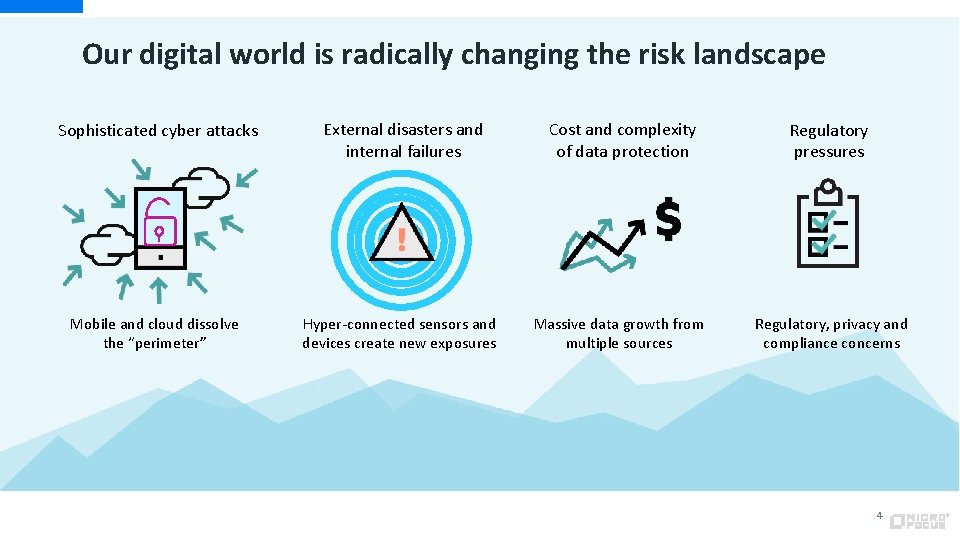
Our digital world is radically changing the risk landscape Sophisticated cyber attacks External disasters and internal failures Cost and complexity of data protection Regulatory pressures Mobile and cloud dissolve the “perimeter” Hyper-connected sensors and devices create new exposures Massive data growth from multiple sources Regulatory, privacy and compliance concerns 4
Today we live in a different world of data everywhere… Connected Cars Smart Infrastructure Mobile Transactions … feeding sensitive information into data lakes
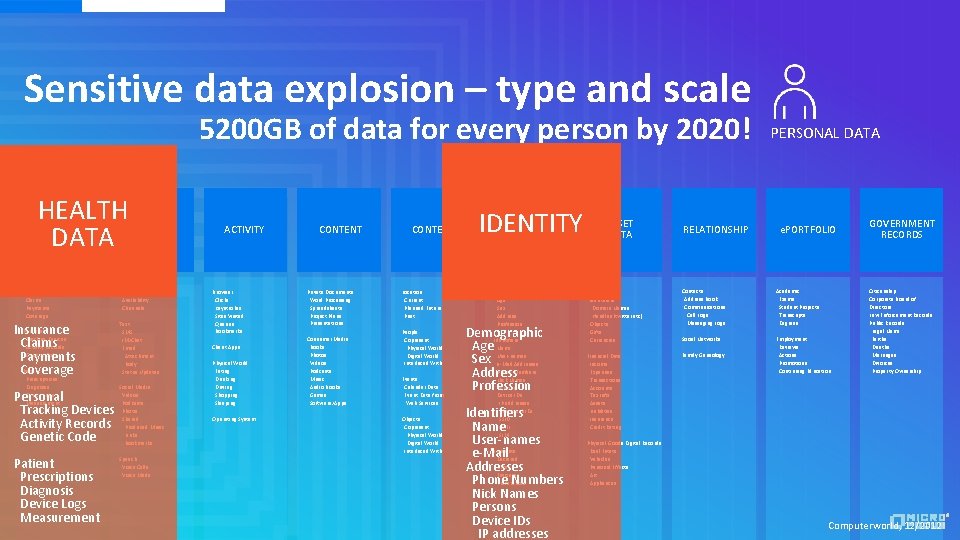
Sensitive data explosion – type and scale 5200 GB of data for every person by 2020! HEALTH DATA Insurance Claims Payments Coverage Personal Insurance Tracking Devices Claims Activity Records Genetic Code Payments Patient Coverage Prescriptions Diagnosis Device Logs Measurement Personal Tracking Devices Activity Records Genetic Code Patient Prescriptions Diagnosis Device Logs Measurement COMM Presence Availability Channels Text SMS IM/Chat Email Attachment Body Status Updates Social Media Videos Podcasts Photis Shared Produced Music Links Bookmarks Speech Voice Calls Voice Mails ACTIVITY Browser Clicks Keystrokes Sites Visited Queries Bookmarks Client Apps Physical World Eating Drinking Driving Shopping Sleeping Operating System CONTENT Private Documents Word Processing Spreadsheets Project Plans Presentations Consumer Media Books Photos Videos Podcasts Music Audio Books Games Software/Apps CONTEXT Location Current Planned Future Past People Copresent Physical World Digital World Interlaced With Events Calendar Data Event Data from Web Services Objects Copresent Physical World Digital World Interlaced With IDENTITY Demographic Age Sex Address Profession Demographic Identifiers Age Name Sex User-names e-Mail Addresses Phone Numbers Address Nick Names Persons Profession Device IDs IP addresses Bluetooth IDs SSID IMEI SIM Identifiers Name User-names Interests e-Mail Declared Llikes Addresses Favorites Phone Numbers Preferences Nick Names Persons Device IDs IP addresses ASSET DATA RELATIONSHIP PERSONAL DATA e. PORTFOLIO Virtual Goods Identifiers Domain Names Handles (twitter etc) Objects Gifts Currencies Contacts Address Book Communications Call Logs Messaging Logs Academic Exams Student Projects Transcripts Degrees Social Networks Financial Data Income Expenses Transactions Accounts Tax Info Assets Liabilities Insurance Credit Rating Family Geneology Employment Reviews Actions Promotions Continuing Education GOVERNMENT RECORDS Citizenship Corporate Board of Directors Law Enforcement Records Public Records Legal Name Births Deaths Marriages Divorces Property Ownership Physical Goods Digital Records Real Estate Vehicles Personal Effects Art Appliances Computerworld, 12/2012
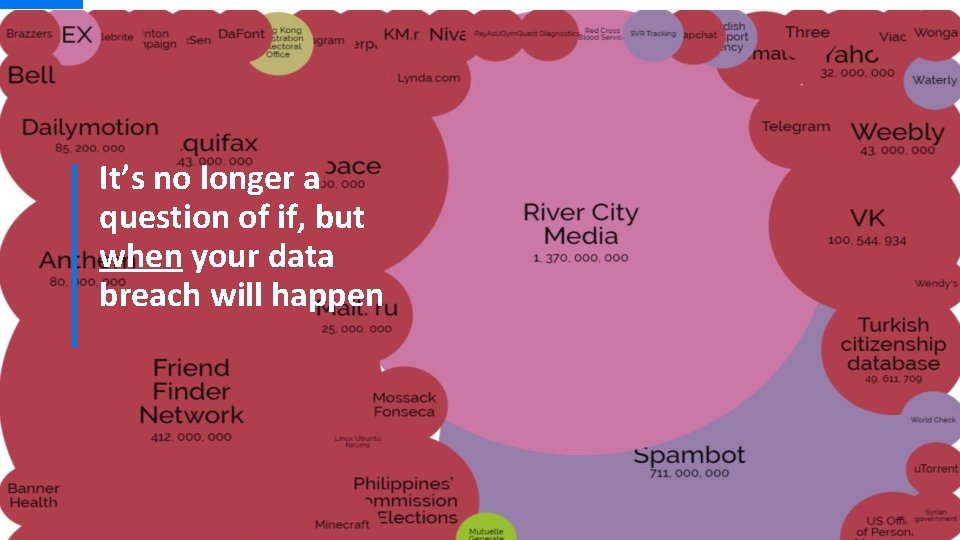
It’s no longer a question of if, but when your data breach will happen

“Silver Bullet” Syndrome 6
![sil·ver bul·let [silver bullet] NOUN 1. a bullet made of silver, used in fiction sil·ver bul·let [silver bullet] NOUN 1. a bullet made of silver, used in fiction](http://slidetodoc.com/presentation_image_h/8da70e8fbb3af9e8d86329e1f0dce362/image-7.jpg)
sil·ver bul·let [silver bullet] NOUN 1. a bullet made of silver, used in fiction as a supposedly magical method of killing werewolves. 2. a simple and seemingly magical solution to a complicated problem. 7 Source: Oxford Dictionary

Organizations continue to invest in point products *On Average, organizations have ~70 different security vendors protecting their environments 8 *Source: ZDNet, Mac. Lean, Asha. (2016, Nov 23) Security Landscape Plagued By Too Many Vendors
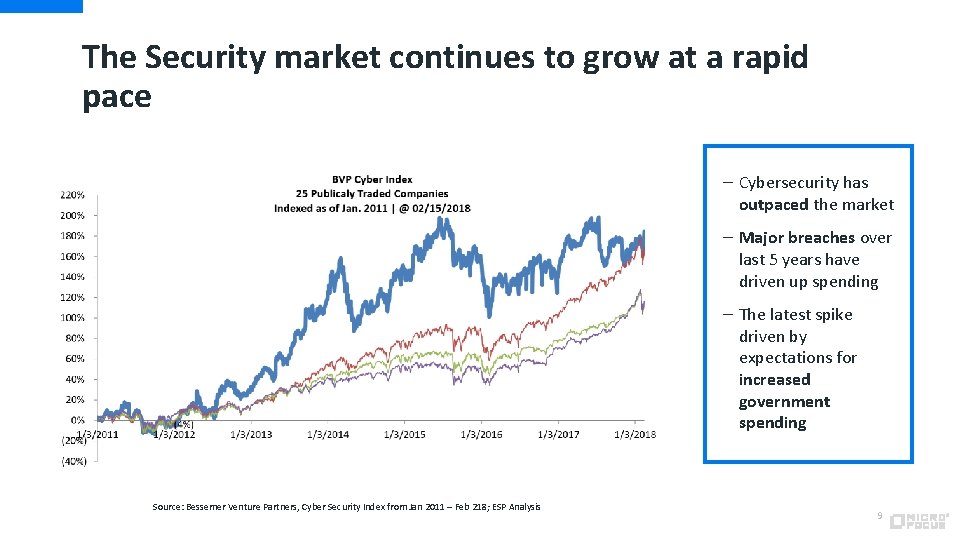
The Security market continues to grow at a rapid pace – Cybersecurity has outpaced the market – Major breaches over last 5 years have driven up spending – The latest spike driven by expectations for increased government spending Source: Bessemer Venture Partners, Cyber Security Index from Jan 2011 – Feb 218; ESP Analysis 9
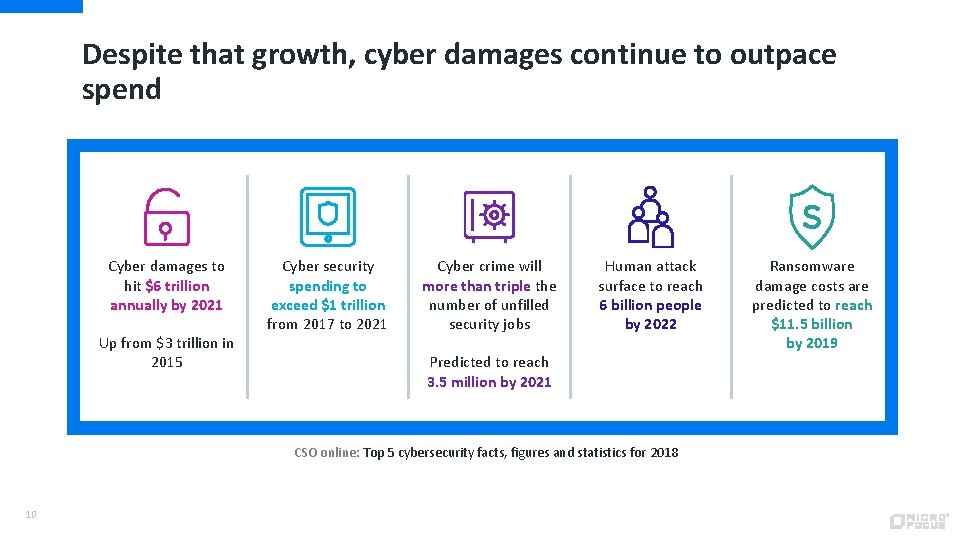
Despite that growth, cyber damages continue to outpace spend Cyber damages to hit $6 trillion annually by 2021 Up from $3 trillion in 2015 Cyber security spending to exceed $1 trillion from 2017 to 2021 Cyber crime will more than triple the number of unfilled security jobs Human attack surface to reach 6 billion people by 2022 Predicted to reach 3. 5 million by 2021 CSO online: Top 5 cybersecurity facts, figures and statistics for 2018 10 Ransomware damage costs are predicted to reach $11. 5 billion by 2019
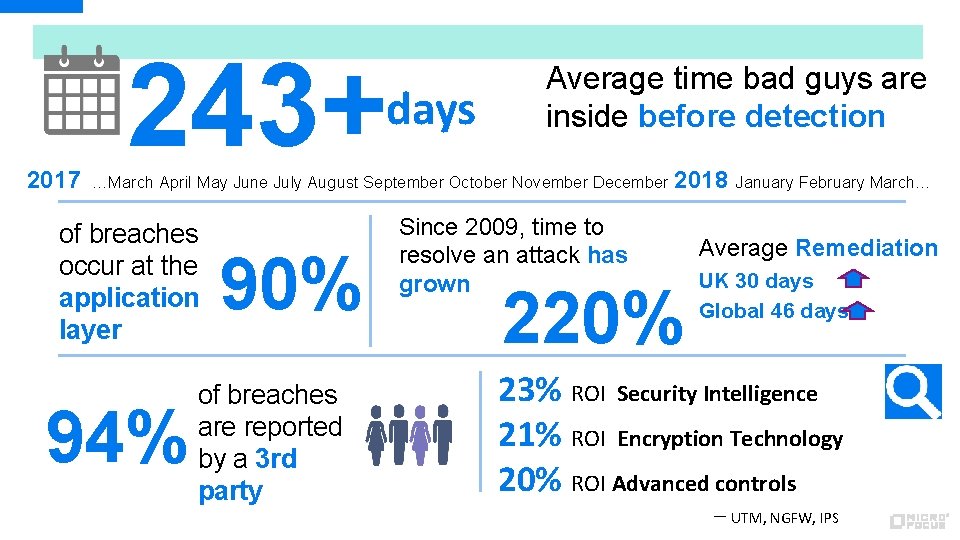
243+ days 2017 Average time bad guys are inside before detection …March April May June July August September October November December of breaches occur at the application layer 94% 90% of breaches are reported by a 3 rd party Since 2009, time to resolve an attack has grown 2018 220% January February March… Average Remediation UK 30 days Global 46 days 23% ROI Security Intelligence 21% ROI Encryption Technology 20% ROI Advanced controls – UTM, NGFW, IPS
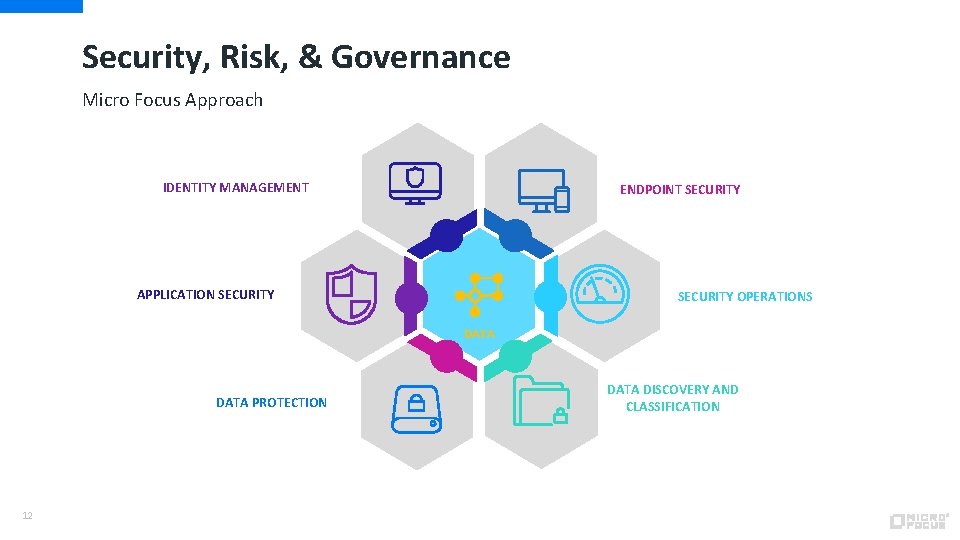
Security, Risk, & Governance Micro Focus Approach IDENTITY MANAGEMENT ENDPOINT SECURITY APPLICATION SECURITY OPERATIONS DATA PROTECTION 12 DATA DISCOVERY AND CLASSIFICATION

Security, Risk, & Governance Micro Focus Portfolio IDENTITY & ACCESS MANAGEMENT - NETIQ - GOVERNANCE - PIM/PAM - SSO, SSPR, MFA APPLICATION SECURITY - FORIFY SCA - WEBINSPECT - APPDEFENDER - FORTIFY ON DEMAND - 13 DATA PROTECTION - VOLTAGE SECURE DATA - VOLTAGE SECURE MAIL COVERTIX FOR UNSTRUCTURED DATA - ANALYTICS & MACHINE LEARNING VERTICA ENDPOINT SECURITY - PATCH MANGEMENT CONFIGURATION MANGEMENT - DISK ENCRYPTION SECURITY OPERATIONS - ARCSIGHT/SENTINEL - INVESTIGATE - LOGGER - UEBA DATA GOVERNANCE, CLASSIFICAION AND ARCHIVING - STRUCTURED DATA MANAGER - CONTENT MANGER - CONTROL POINT
Thank you www. microfocus. com

Data Centric Security “protecting what matters”
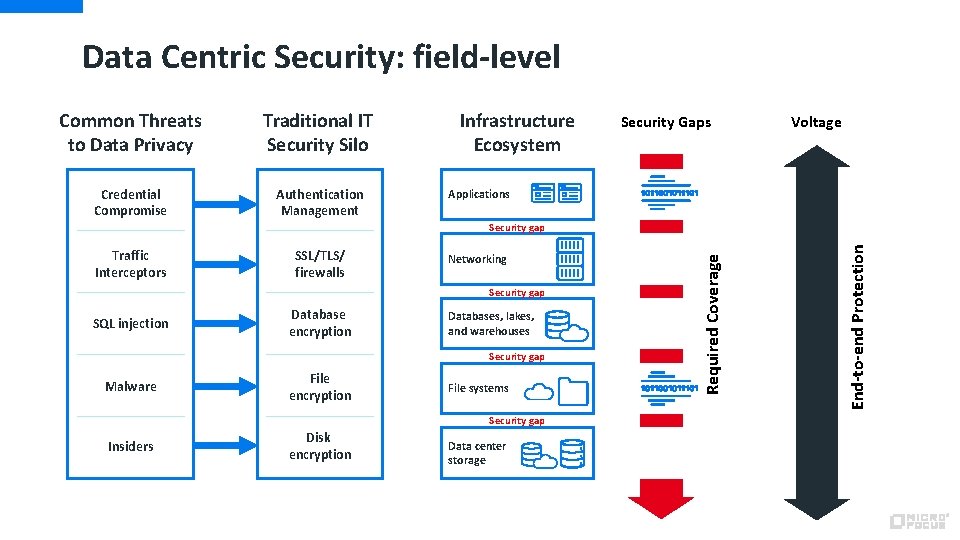
Data Centric Security: field-level Common Threats to Data Privacy Traditional IT Security Silo Credential Compromise Authentication Management Infrastructure Ecosystem Security Gaps Voltage Applications SSL/TLS/ firewalls Networking Security gap SQL injection Database encryption Databases, lakes, and warehouses Security gap Malware File encryption File systems Security gap Insiders Disk encryption Data center storage End-to-end Protection Traffic Interceptors Required Coverage Security gap
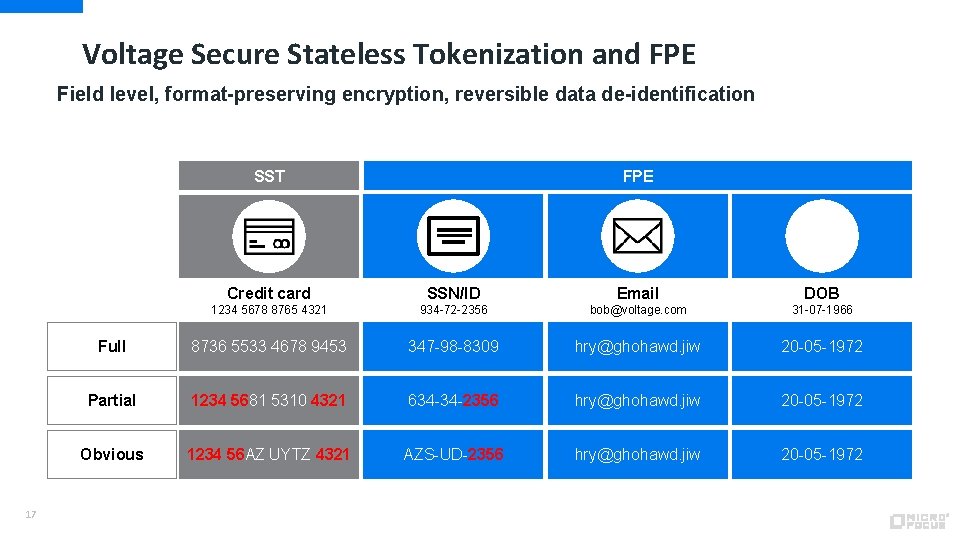
Voltage Secure Stateless Tokenization and FPE Field level, format-preserving encryption, reversible data de-identification SST 17 FPE Credit card SSN/ID Email DOB 1234 5678 8765 4321 934 -72 -2356 bob@voltage. com 31 -07 -1966 Full 8736 5533 4678 9453 347 -98 -8309 hry@ghohawd. jiw 20 -05 -1972 Partial 1234 5681 5310 4321 634 -34 -2356 hry@ghohawd. jiw 20 -05 -1972 Obvious 1234 56 AZ UYTZ 4321 AZS-UD-2356 hry@ghohawd. jiw 20 -05 -1972
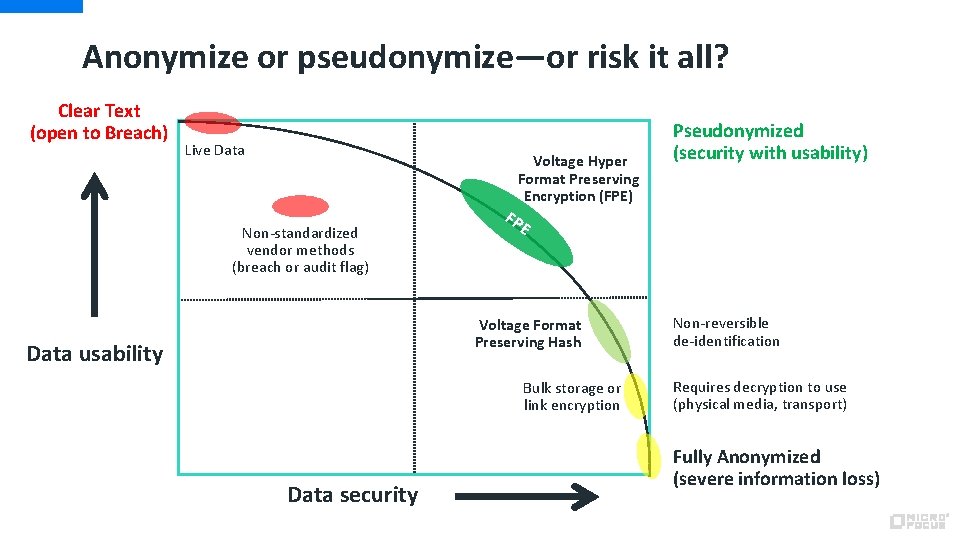
Anonymize or pseudonymize—or risk it all? Clear Text (open to Breach) Live Data Voltage Hyper Format Preserving Encryption (FPE) Non-standardized vendor methods (breach or audit flag) FP E Voltage Format Preserving Hash Data usability Bulk storage or link encryption Data security Pseudonymized (security with usability) Non-reversible de-identification Requires decryption to use (physical media, transport) Fully Anonymized (severe information loss)

Application Security “the new perimeter”
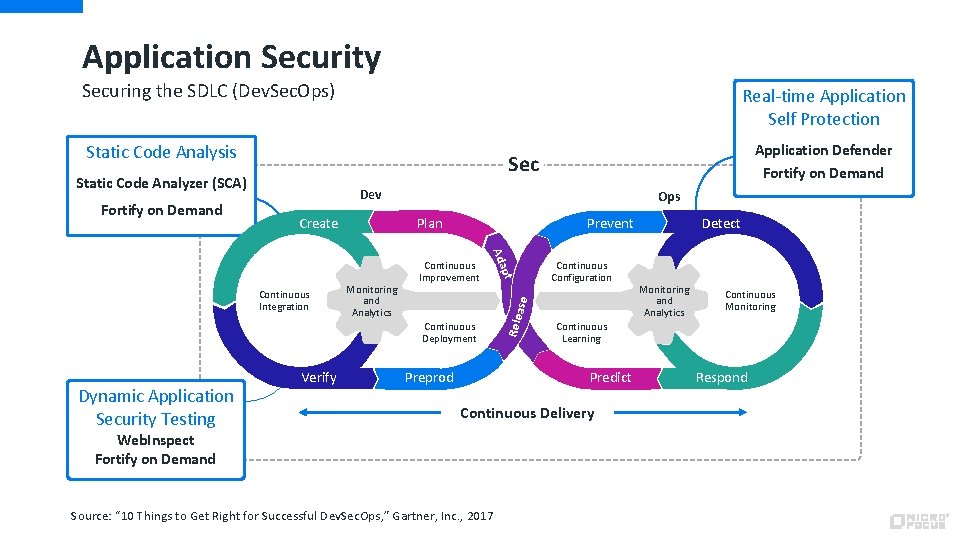
Application Security Securing the SDLC (Dev. Sec. Ops) Real-time Application Self Protection Static Code Analysis Sec Static Code Analyzer (SCA) Dev Continuous Improvement Continuous Deployment Dynamic Application Security Testing Verify pt Monitoring and Analytics Prevent Ada Continuous Integration Plan Continuous Configuration ase Create Ops Preprod Rele Fortify on Demand Application Defender Fortify on Demand Continuous Delivery Source: “ 10 Things to Get Right for Successful Dev. Sec. Ops, ” Gartner, Inc. , 2017 Monitoring and Analytics Continuous Monitoring Continuous Learning Predict Web. Inspect Fortify on Demand Detect Respond
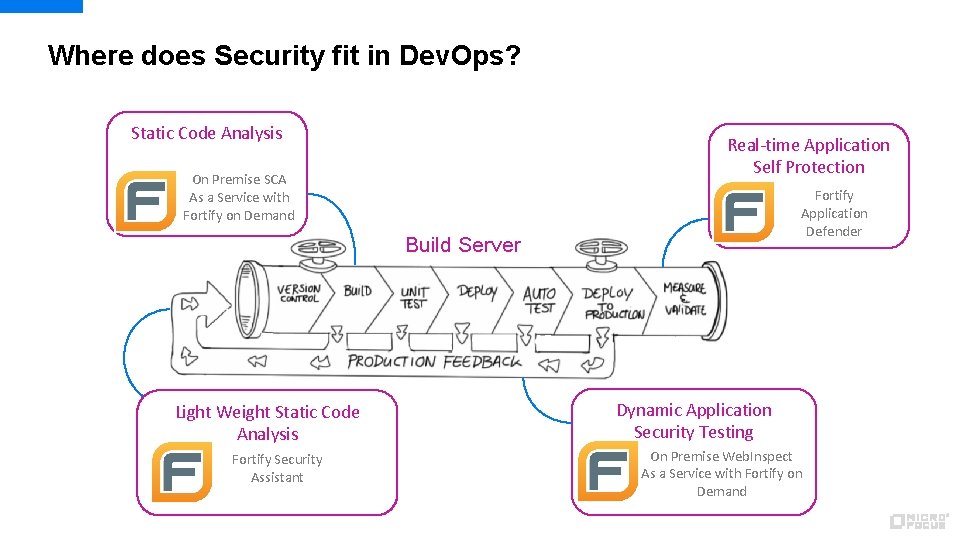
Where does Security fit in Dev. Ops? Static Code Analysis Real-time Application Self Protection On Premise SCA As a Service with Fortify on Demand Fortify Application Defender Build Server Light Weight Static Code Analysis Fortify Security Assistant Dynamic Application Security Testing On Premise Web. Inspect As a Service with Fortify on Demand
- Slides: 21