ETSI Technical Committee Lawful Interception ETSITC LI 1
- Slides: 17
ETSI Technical Committee Lawful Interception ETSI/TC LI 1 Peter van der Arend (Royal KPN) Chairman ETSI/TC LI
Why LI 2 The providers of public telecommunications networks and services are legally required to make available to the authorities the information necessary to enable them to investigate telecommunications.
History • ETSI/TC Security Techniques Advisory Group (STAG) (1991) 3 • ETSI/TC Security (TC SEC) – Working Group Lawful Interception (SEC-WGLI) (1997) • ETSI/TC Lawful Interception (TC LI) (Oct 2002)
Terms of Reference 4 • To develop a suite of standards that allow ETSI standards to support industry compliance to the requirements of national and international law. • To capture the requirements of “Law Enforcement Agencies” and translating those into requirements to be applied to technical specifications. • To develop and publish handover interfaces, and of rules for the carriage of technology specific interception across these interfaces.
Relationships inside ETSI 5 • • • 3 GPP (SA 3 -LI) (LI for UMTS) TC AT (LI for IP Cablecom) TC SPAN & EP TIPHON ---> TISPAN PLT (LI for Powerline Communications) EP TETRA TC MTS
Relationships outside ETSI 6 • • • National and Regional Law Enforcement Agencies OASIS (TC Legal. XML-LI) T 1 S 1 LAES AHG ANSI
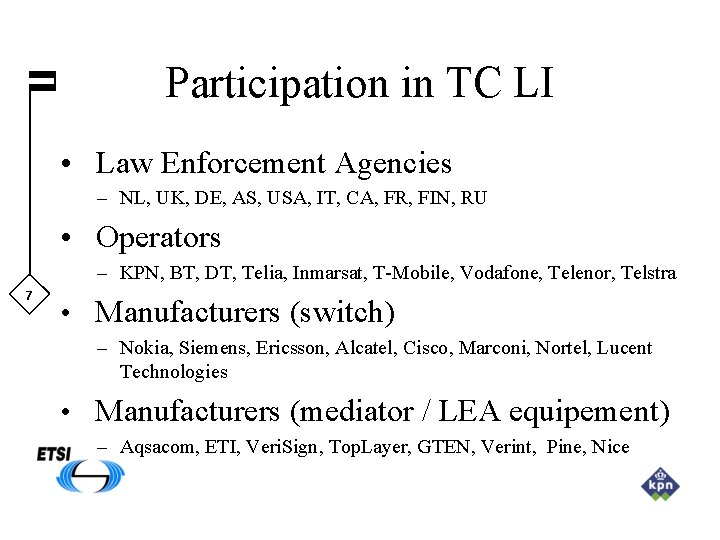
Participation in TC LI • Law Enforcement Agencies – NL, UK, DE, AS, USA, IT, CA, FR, FIN, RU • Operators – KPN, BT, DT, Telia, Inmarsat, T-Mobile, Vodafone, Telenor, Telstra 7 • Manufacturers (switch) – Nokia, Siemens, Ericsson, Alcatel, Cisco, Marconi, Nortel, Lucent Technologies • Manufacturers (mediator / LEA equipement) – Aqsacom, ETI, Veri. Sign, Top. Layer, GTEN, Verint, Pine, Nice
LEA requirements • TS 101 331: Requirements of Law Enforcement Agencies 8 – Provides guidance in the area of co-operation by network operators/service providers with the lawful interception of telecommunications. – Provides a set of requirements relating to handover interfaces for the interception.
Other specifications 9 • ES 201 158 Requirements for Network Functions • ES 201 671 / TS 101 671 Handover Interface for the Lawful Interception of Telecommunications Traffic • TR 102 053 Notes on ISDN LI functionalities • TR 101 943 Concepts of Interception in a Generic Network Architecture. • TR 101 944 Issues on IP Interception.
Handover Interface Concept 10
Latest published specifications • Delivery of IP based interception TS 102 232 HI 2 and HI 3 interfaces for handover via IP networks 11 • Service specific details for E-Mail Services TS 102 233 Description for handover of E-mail messages • Service specific details for Internet Access Services TS 102 234 Description for handover of Internet Access Information and TCP/IP information
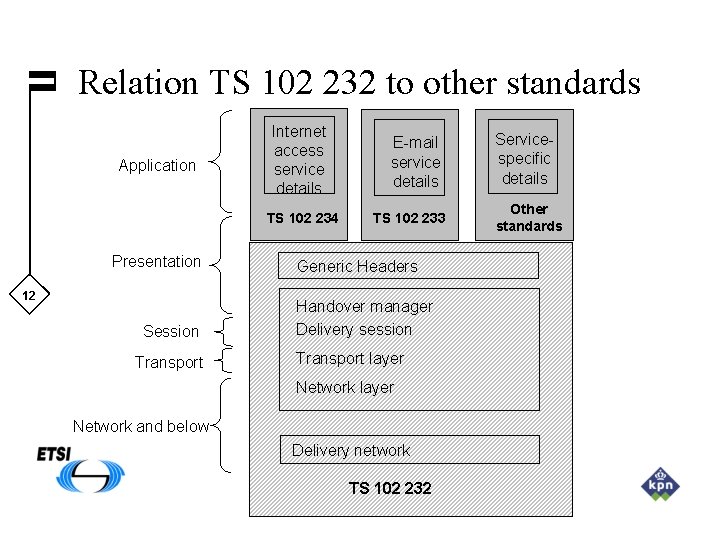
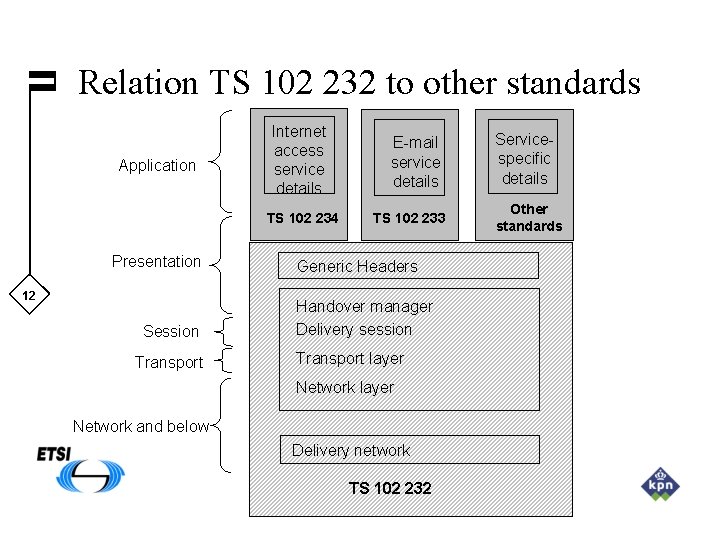
Relation TS 102 232 to other standards Application Internet access service details TS 102 234 Presentation 12 Session Transport E-mail service details TS 102 233 Generic Headers Handover manager Delivery session Transport layer Network and below Delivery network TS 102 232 Servicespecific details Other standards
Actual working issues 13 • DTR 00014: Lawful Interception of public Wireless LAN Internet Access • General update of: TR 101 943 Concepts of Interception in a Generic Network Architecture • Keeping up to date of the LI specifications
LI standards in 3 GPP (UMTS) 14 • TS 133 106 Lawful interception requirements • TS 133 107 Lawful interception architecture and functions • TS 133 108 Handover interface for Lawful Interception
Future developments 15 • • Lawful Interception of IP Cablecom Lawful Interception of TIPHON Lawful Interception of third generation mobile systems Maintenance of existing documents; especially ES 201 671 / TS 101 671 and TS 101 331.
More details on ETSI/TC LI can be found on: 16 http: //portal. etsi. org/li/Summary. asp
17