Establishing Pairwise Keys in Distributed Sensor Networks Donggang
Establishing Pairwise Keys in Distributed Sensor Networks Donggang Liu & Peng Ning
Outline • • • Background Research Problem Previous Work Proposed Solutions Conclusion and Future Work
Background • Challenges in Sensor Network Security – Resource constraints • Limited storage, computation, and communication – Expensive mechanisms such as public key cryptography is not practical • Limited resources (e. g. battery power) – Resource consumption attacks – Threat of node compromises • Sensor nodes are usually deployed in an unattended fashion • Subject to node captures
Problem : Pairwise Key Establishment • How to establish pairwise keys between sensor nodes so as to secure the communication ? – Between neighbor nodes – Between arbitrary nodes • Challenges – Resource constraints • Not feasible to use public key cryptography / key distribution center (KDC) – Threat of compromised nodes • Key pre-distribution – No location information before deployment – Naïve methods • Master key • Pairwise Key
Previous Work • Probabilistic key pre-distribution (Eschenauer & Gligor CCS’ 02) – key pre-distribution • random drawing of k keys out of a key pool P w/o replacement • loading of the key ring into each sensor – shared-key discovery • every node discovers its neighbors with which it shares keys – path-key establishment • • assigns a path-key to neighbors w/o shared key q-composite key pre-distribution (Chan et al. SSP’ 03) – Two nodes compute a pairwise key if they share at least q common keys. • Random pairwise key pre-distribution (Chan et al. SSP’ 03) – Randomly pick pairs of sensors and assigns each pair a unique random key.
Previous Work : Problem • Probabilistic key pre-distribution • q-composite key pre-distribution – A small number of compromised nodes may affect a large fraction of pairwise keys • Random pairwise key pre-distribution – Network scalability problem
Proposed Solutions • Polynomial pool based key pre-distribution – Random subset assignment scheme • Higher probability for sensors to establish secure communication • Unless the number of compromised nodes exceeds a threshold, compromise of sensors does not lead to the disclosure of other keys – Grid-based key pre-distribution scheme • Any two sensors can establish a pairwise key when there is no compromised node • Resilient to node capture • No communication overhead during the discovery of shared keys
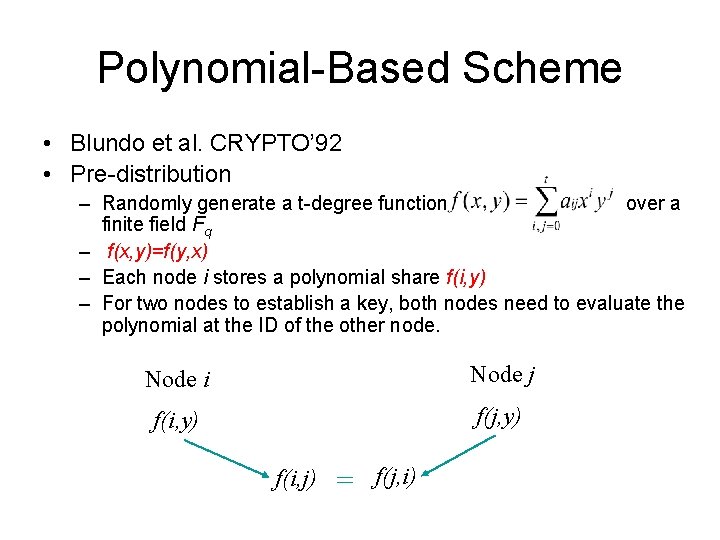
Polynomial-Based Scheme • Blundo et al. CRYPTO’ 92 • Pre-distribution – Randomly generate a t-degree function over a finite field Fq – f(x, y)=f(y, x) – Each node i stores a polynomial share f(i, y) – For two nodes to establish a key, both nodes need to evaluate the polynomial at the ID of the other node. Node i Node j f(i, y) f(j, y) f(i, j) = f(j, i)
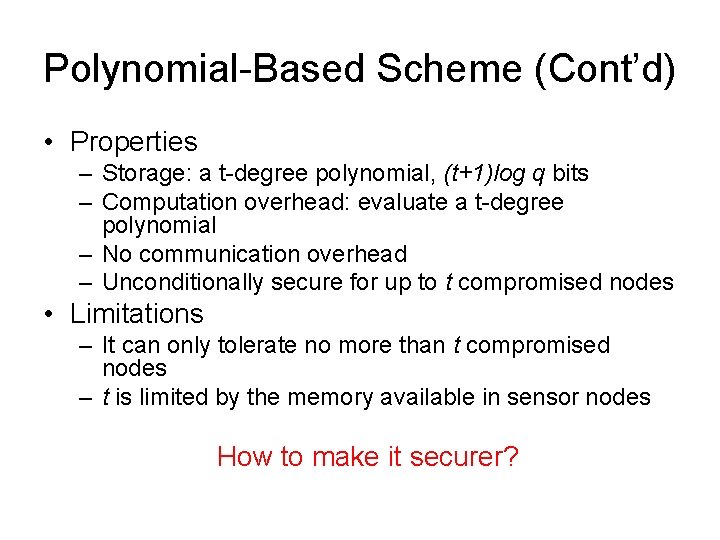
Polynomial-Based Scheme (Cont’d) • Properties – Storage: a t-degree polynomial, (t+1)log q bits – Computation overhead: evaluate a t-degree polynomial – No communication overhead – Unconditionally secure for up to t compromised nodes • Limitations – It can only tolerate no more than t compromised nodes – t is limited by the memory available in sensor nodes How to make it securer?
Polynomial Pool Based Scheme • Main idea – Use a pool of randomly generated polynomials • Three phases – Setup (Pre-distribution) • Initialize the sensors by distributing polynomial shares to them – Direct Key Establishment • Sensors first attempt to set up direct keys – Path Key Establishment • Establish pairwise keys with the help of other sensor
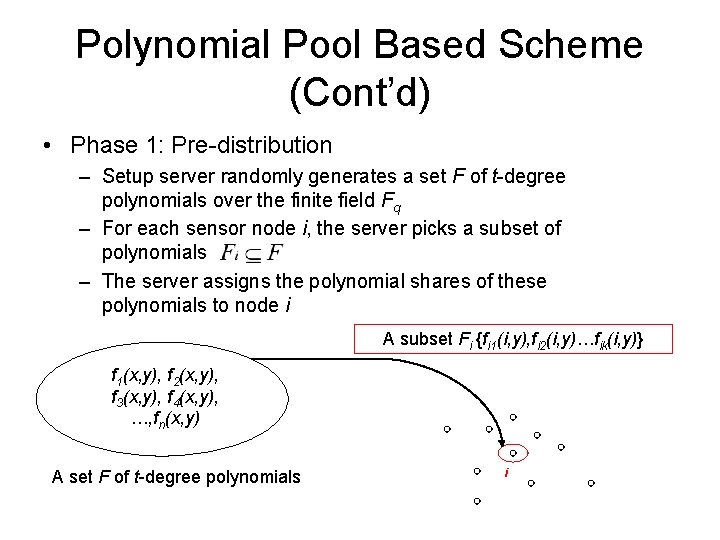
Polynomial Pool Based Scheme (Cont’d) • Phase 1: Pre-distribution – Setup server randomly generates a set F of t-degree polynomials over the finite field Fq – For each sensor node i, the server picks a subset of polynomials – The server assigns the polynomial shares of these polynomials to node i A subset Fi {fi 1(i, y), fi 2(i, y)…fik(i, y)} f 1(x, y), f 2(x, y), f 3(x, y), f 4(x, y), …, fn(x, y) A set F of t-degree polynomials i
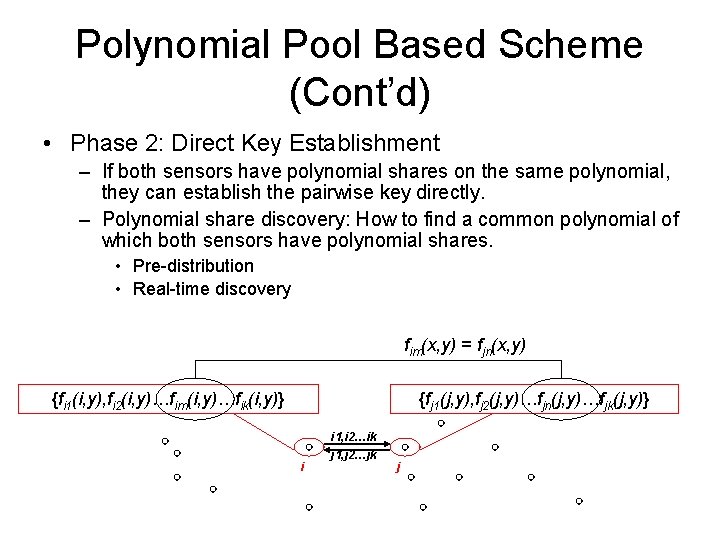
Polynomial Pool Based Scheme (Cont’d) • Phase 2: Direct Key Establishment – If both sensors have polynomial shares on the same polynomial, they can establish the pairwise key directly. – Polynomial share discovery: How to find a common polynomial of which both sensors have polynomial shares. • Pre-distribution • Real-time discovery fim(x, y) = fjn(x, y) {fi 1(i, y), fi 2(i, y)…fim(i, y)…fik(i, y)} {fj 1(j, y), fj 2(j, y)…fjn(j, y)…fjk(j, y)} i i 1, i 2…ik j 1, j 2…jk j
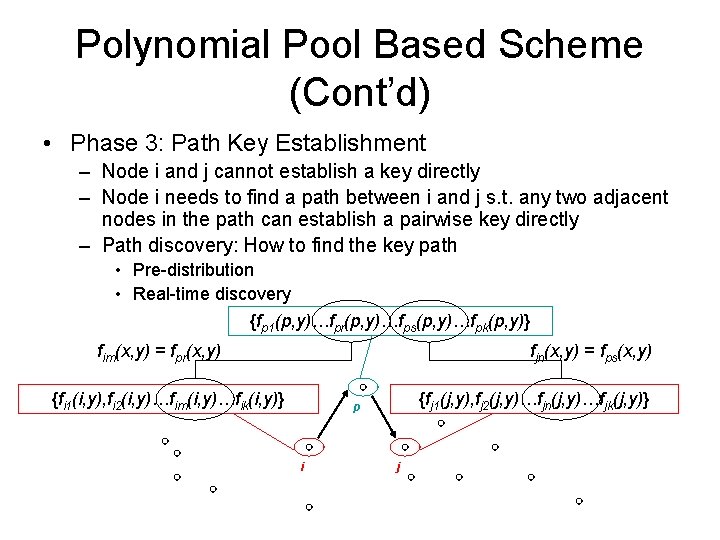
Polynomial Pool Based Scheme (Cont’d) • Phase 3: Path Key Establishment – Node i and j cannot establish a key directly – Node i needs to find a path between i and j s. t. any two adjacent nodes in the path can establish a pairwise key directly – Path discovery: How to find the key path • Pre-distribution • Real-time discovery {fp 1(p, y)…fpr(p, y)…fps(p, y)…fpk(p, y)} fim(x, y) = fpr(x, y) fjn(x, y) = fps(x, y) {fi 1(i, y), fi 2(i, y)…fim(i, y)…fik(i, y)} {fj 1(j, y), fj 2(j, y)…fjn(j, y)…fjk(j, y)} p i j
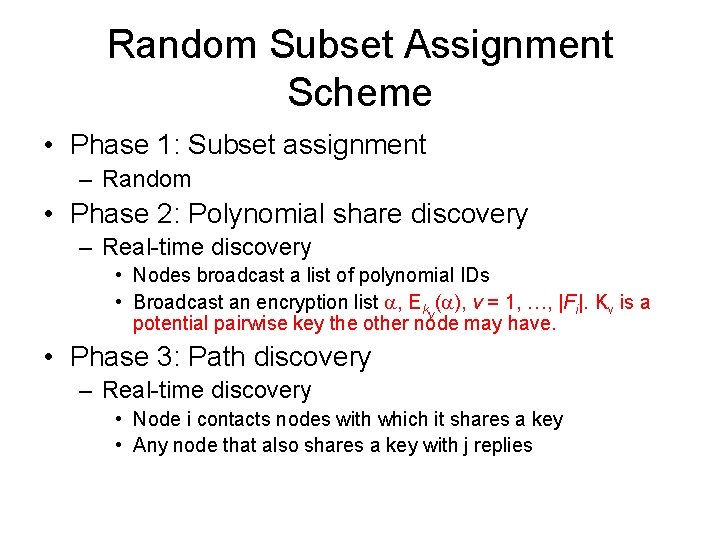
Random Subset Assignment Scheme • Phase 1: Subset assignment – Random • Phase 2: Polynomial share discovery – Real-time discovery • Nodes broadcast a list of polynomial IDs • Broadcast an encryption list , Ekv( ), v = 1, …, |Fi|. Kv is a potential pairwise key the other node may have. • Phase 3: Path discovery – Real-time discovery • Node i contacts nodes with which it shares a key • Any node that also shares a key with j replies
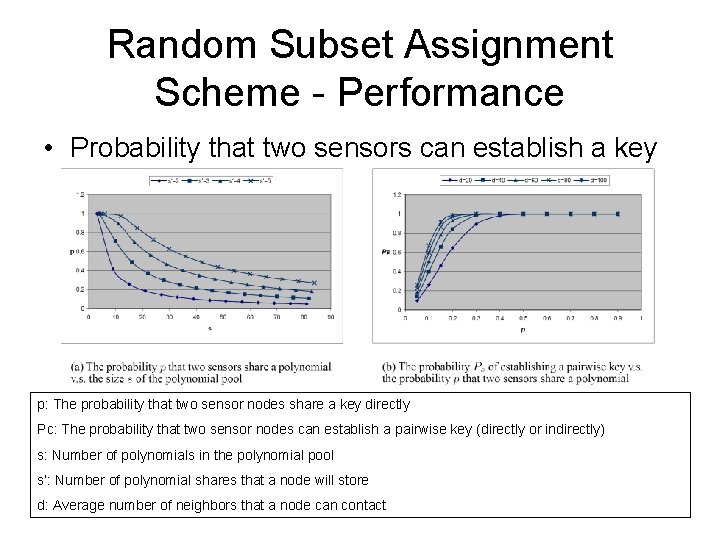
Random Subset Assignment Scheme - Performance • Probability that two sensors can establish a key p: The probability that two sensor nodes share a key directly Pc: The probability that two sensor nodes can establish a pairwise key (directly or indirectly) s: Number of polynomials in the polynomial pool s’: Number of polynomial shares that a node will store d: Average number of neighbors that a node can contact
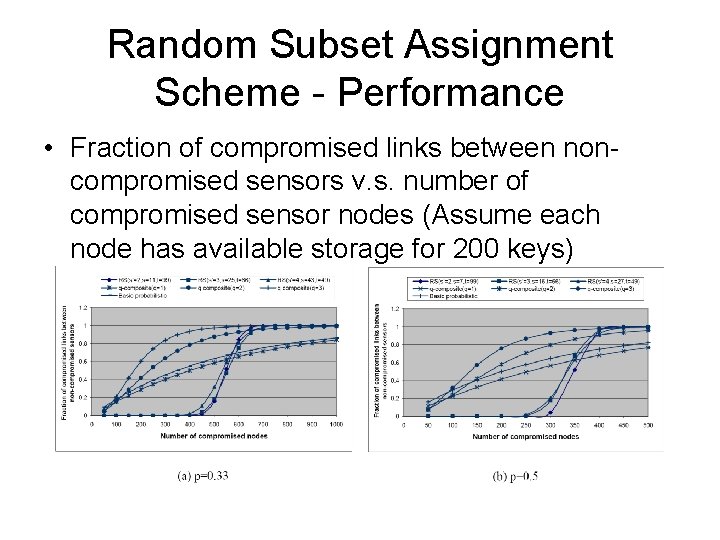
Random Subset Assignment Scheme - Performance • Fraction of compromised links between noncompromised sensors v. s. number of compromised sensor nodes (Assume each node has available storage for 200 keys)
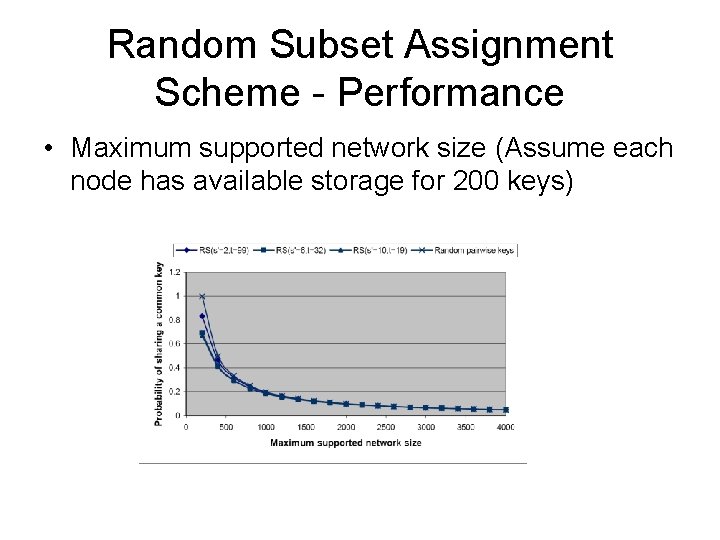
Random Subset Assignment Scheme - Performance • Maximum supported network size (Assume each node has available storage for 200 keys)
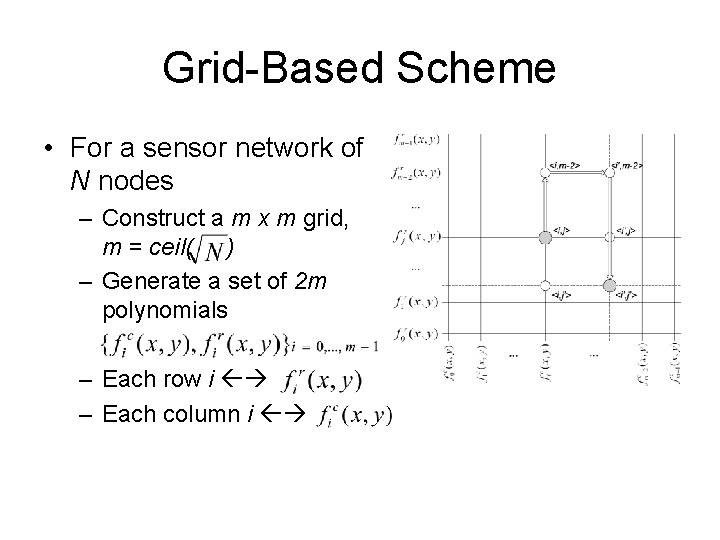
Grid-Based Scheme • For a sensor network of N nodes – Construct a m x m grid, m = ceil( ) – Generate a set of 2 m polynomials – Each row i – Each column i
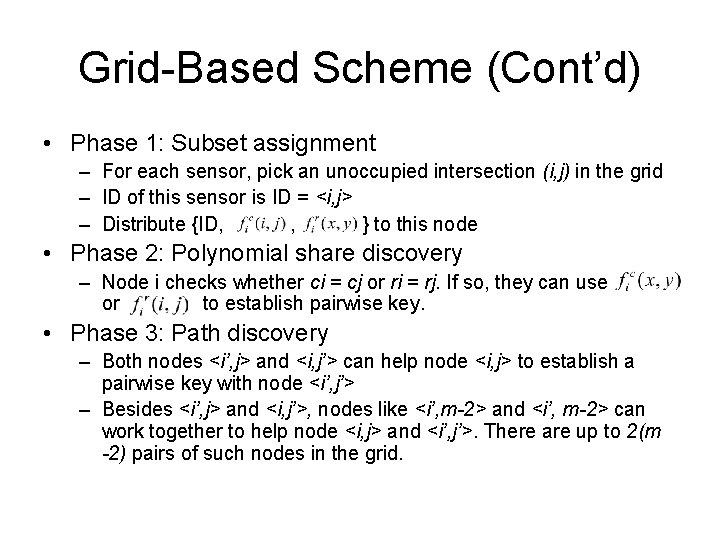
Grid-Based Scheme (Cont’d) • Phase 1: Subset assignment – For each sensor, pick an unoccupied intersection (i, j) in the grid – ID of this sensor is ID = <i, j> – Distribute {ID, , } to this node • Phase 2: Polynomial share discovery – Node i checks whether ci = cj or ri = rj. If so, they can use or to establish pairwise key. • Phase 3: Path discovery – Both nodes <i’, j> and <i, j’> can help node <i, j> to establish a pairwise key with node <i’, j’> – Besides <i’, j> and <i, j’>, nodes like <i’, m-2> and <i’, m-2> can work together to help node <i, j> and <i’, j’>. There are up to 2(m -2) pairs of such nodes in the grid.
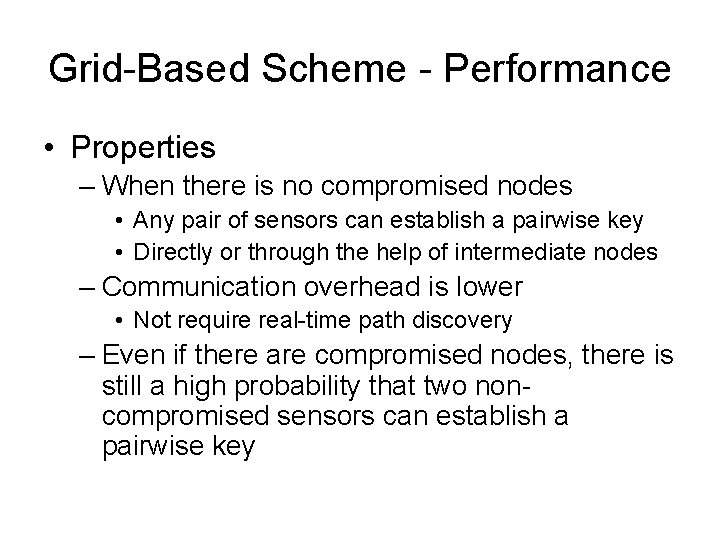
Grid-Based Scheme - Performance • Properties – When there is no compromised nodes • Any pair of sensors can establish a pairwise key • Directly or through the help of intermediate nodes – Communication overhead is lower • Not require real-time path discovery – Even if there are compromised nodes, there is still a high probability that two noncompromised sensors can establish a pairwise key
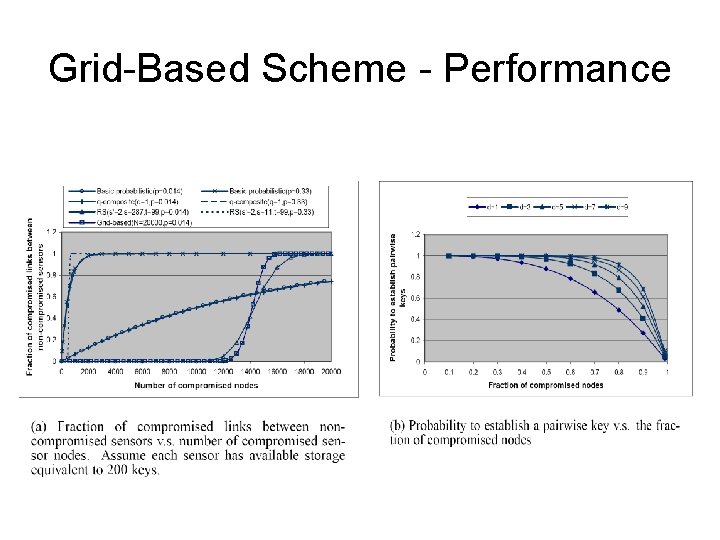
Grid-Based Scheme - Performance
Conclusion and Future Work • Conclusion – Developed a general framework for polynomial poolbased key pre-distribution – Two instantiations • Random subset assignment • Grid-based key pre-distribution • Future work – Grid-based scheme can be extended to a ndimensional or hypercube based scheme – Develop location based schemes • Sensor nodes have low mobility in many applications
- Slides: 22