Espoo 12 th of February 2002 Stream Control
Espoo, 12 th of February, 2002 Stream Control Transmission Protocol The design of a new reliable transport protocol for IP networks Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
Espoo, 12 th of February, 2002 Table of contents /Why a new reliable transport protocol? /Datagram structure of SCTP. /The SYN attack in TCP /Establishment procedure in SCTP. /Transmission of data. /Taking profit of multihomed hosts. /The Head Of Line (HOL) blocking in TCP. /Avoiding the HOL blocking in TCP using several connections. /Avoiding the HOL blocking in SCTP using several streams. /Avoiding the HOL blocking in SCTP using unordered DATA chunks. /The path heartbeat mechanism. /Reporting non fatal errors in SCTP. /Aborting associations in SCTP. /Gracefully termination of an association. /Summarizing: Main characteristics of SCTP Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
Espoo, 12 th of February, 2002 Why a new reliable transport protocol? /There is an increasing interest in merging IP and telephony networks. /Among the problems that TCP has regarding telephony signaling transport we can cite: • • It suffers from the so-called Head Of Line (HOL) blocking. It is stream oriented. There are no message delimiters. TCP is not designed to be multihomed. It is relatively vulnerable to denial of service attacks. /TCP is very difficult to extend. These problems could not be solved by any TCP extension. /The SIGTRAN working group of the IETF started to design a new reliable transport protocol in summer 1998. /The initial design was called Multi-Network Datagram Transmission Protocol (MDTP). It ran on top of UDP instead of directly over IP. /The design of SCTP took about two years and a half. SCTP specifications are published in RFC 2960. However, a second version of them will be published soon. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
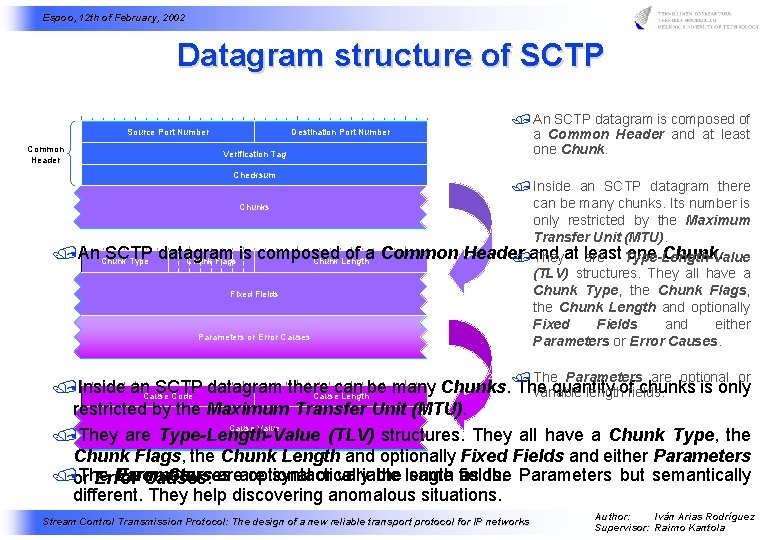
Espoo, 12 th of February, 2002 Datagram structure of SCTP 00 01 02 03 04 05 06 07 08 09 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 Source Port Number Common Header Destination Port Number Verification Tag / An SCTP datagram is composed of a Common Header and at least one Chunk. Checksum / Inside an SCTP datagram there can be many chunks. Its number is Chunks only restricted by the Maximum 00 01 02 03 04 05 06 07 08 09 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 Transfer Unit (MTU). /An Chunk SCTP datagram is composed of a Common Header one Chunk. /and Theyat least are Type-Length-Value Chunk Flags Chunk Length Type (TLV) structures. They all have a Chunk Type, the Chunk Flags, Fixed Fields the Chunk Length and optionally Fixed Fields and either Parameters or Error Causes. / The Parameters are optional or 00 01 02 03 04 05 06 07 08 09 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 /Inside an SCTP datagram there can be many Chunks. The quantity chunks is only variable lengthoffields. Cause Code Cause Length Parameter Type Parameter Length restricted by the Maximum Transfer Unit (MTU). Cause Value Parameter Value /They are Type-Length-Value (TLV) structures. They all have a Chunk Type, the Chunk Flags, the Chunk Length and optionally Fixed Fields and either Parameters /or The Parameters Error Causes areare optional syntactically or variable the length same fields. as the Parameters but semantically Error Causes. different. They help discovering anomalous situations. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
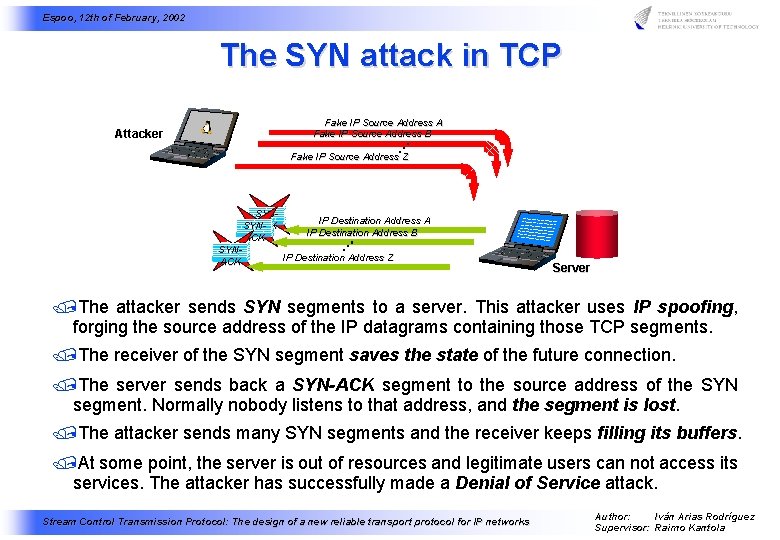
Espoo, 12 th of February, 2002 The SYN attack in TCP Attacker Fake IP Source Address A Fake IP Source Address B Fake IP Source Address Z SYNIP Destination Address A ACK SYNIP Destination Address B ACK SYNIP Destination Address Z ACK SYN SYN Server /The attacker sends SYN segments to a server. This attacker uses IP spoofing, forging the source address of the IP datagrams containing those TCP segments. /The receiver of the SYN segment saves the state of the future connection. /The server sends back a SYN-ACK segment to the source address of the SYN segment. Normally nobody listens to that address, and the segment is lost. /The attacker sends many SYN segments and the receiver keeps filling its buffers. /At some point, the server is out of resources and legitimate users can not access its services. The attacker has successfully made a Denial of Service attack. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
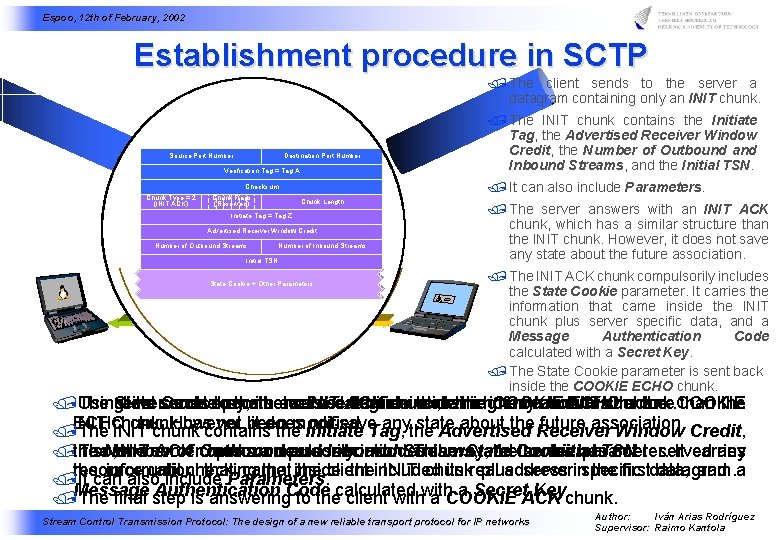
Espoo, 12 th of February, 2002 Establishment procedure in SCTP / The client sends to the server a datagram containing only an INIT chunk. Source Port Number Destination Port Number Verification Tag =0 A Verification Tag = Tag / It can also include Parameters. Checksum Chunk Type = 1 2 (INIT) ACK) Chunk Flags (Reserved) Chunk Length Source Port Number Initiate Tag = Tag Destination A Z Verification Tag = Tag Z Advertised Receiver Window Credit Source Port Number Destination Port Number of Outbound Streams. Checksum. Number of Inbound Streams Chunk Type = 10 Chunk Flags Verification Tag = Tag A Chunk Length Initial TSN (COOKIE ECHO) (Reserved) Chunk Type = 11 (COOKIE ACK) Checksum Received Cookie Parameters State Cookie + Other Parameters Chunk Flags Chunk Length (Reserved) Source Port Number Destination Port Number Source. Verification Port Number Tag = 0 Destination Port Number Verification Tag = Tag A Chunk Type = 1 Chunk Flags (INIT) (Reserved) Checksum Chunk Flags Chunk Length (INITType ACK)= 2 (Reserved) Source Port Number Chunk Length Initiate Tag = Tag A Verification Tag Initiate = Tag ZTag = Tag Z Advertised Receiver Window Credit Checksum Receiver Window Credit Number of Outbound Streams. Advertised. Number of Inbound Streams Chunk Type = 10 Chunk Flags (COOKIE ECHO) (Reserved) Source Port Number Destination Port Number Length of Inbound Streams Number of Outbound Streams Chunk Number Initial TSN Verification Tag = A Initial TSN Received Cookie. Checksum Parameters Chunk Type = 11 Chunk Flags (COOKIE ACK) (Reserved) Cookie + Other Parameters. Chunk Length / The INIT chunk contains the Initiate Tag, the Advertised Receiver Window Credit, the Number of Outbound and Inbound Streams, and the Initial TSN. / The server answers with an INIT ACK chunk, which has a similar structure than the INIT chunk. However, it does not save any state about the future association. / The INIT ACK chunk compulsorily includes the State Cookie parameter. It carries the information that came inside the INIT chunk plus server specific data, and a Message Authentication Code calculated with a Secret Key. / The State Cookie parameter is sent back inside the COOKIE ECHO chunk. /The Using State client server its secret Cookie sends answers to key, parameter the with the server anserver INIT isasent datagram ACK verifies back chunk, inside containing thatwhich the information COOKIE has onlyaan similar INIT ECHO inside chunk. structure chunk. the COOKIE than the INIT chunk However, hascontains not been it does not save anythe state about the Receiver future association. /ECHO The chunk. INIT chunk themodified. Initiate Tag, Advertised Window Credit, /the The If so, Number INIT the server ACK of Outbound chunk openscompulsorily a new andassociation. Inbound includes Streams, This theway, State and the. Cookie the server Initial has parameter. TSN. not reserved It carries any the information until checking that. Parameters. came that inside the client theincluded INIT chunk its real plus address serverinspecific the firstdata, datagram. and a /resource It can also include Authentication a Secret. ACK Key. chunk. /Message The final step is answering. Code to thecalculated client with a COOKIE Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
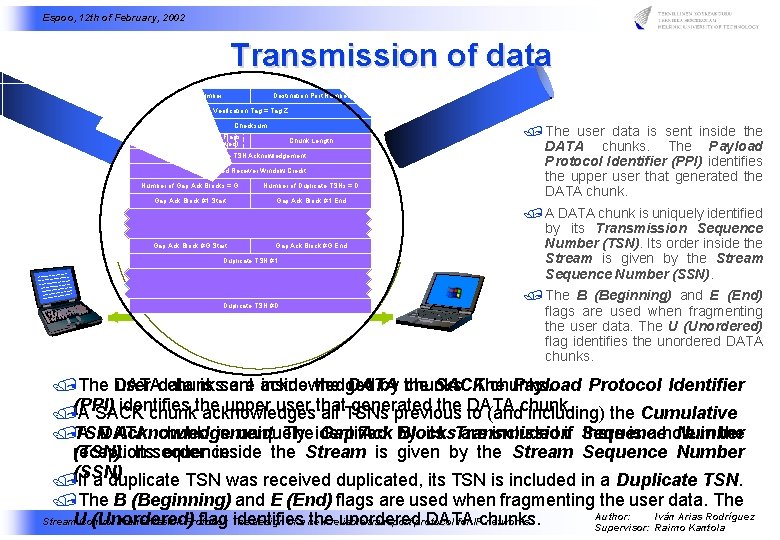
Espoo, 12 th of February, 2002 Transmission of data Source Port Number Destination Port Number Verification Tag = Tag Z Checksum Chunk Type = 3 (SACK) Chunk Flags ( Reserved) Chunk Length Cumulative TSN Acknowledgement Source Port Number Destination Port Number Advertised Receiver Window Credit Verification Tag = Tag Z Number of Gap Ack Blocks = G Number of Duplicate TSNs = D Checksum Gap Ack Block #1 Start Gap Ack Block #1 End Chunk Type = 0 Chunk Length Reserved U B E (DATA). . . Transmission Sequence Number Stream Identifier Stream Sequence Number Gap Ack Block #G Start Gap Ack Block #G End Payload Protocol Identifier Duplicate TSN #1 User Data. . . Source Port Number Destination Port Number / The user data is sent inside the DATA chunks. The Payload Protocol Identifier (PPI) identifies the upper user that generated the DATA chunk. / A DATA chunk is uniquely identified by its Transmission Sequence Number (TSN). Its order inside the Stream is given by the Stream Sequence Number (SSN). Verification Tag = Tag Z Chunk Type = 3 (SACK) Checksum Chunk Flags ( Reserved) Chunk Length Cumulative TSN Acknowledgement Advertised Receiver Window Credit Number of Gap Ack Blocks = G Source Port Number of Duplicate TSNs = D Destination Port Number Gap Ack Block #1 Start Gap Verification Tag = Tag Z Ack Block #1 End Checksum Chunk Type = 0 Reserved U B E. . . (DATA) Chunk Length Sequence Gap Number Gap Ack Block Transmission #G Start Ack Block #G End Duplicate TSN #D Stream Identifier Stream Sequence Number Duplicate TSN #1 Payload Protocol Identifier. . . User Data Duplicate TSN #D / The B (Beginning) and E (End) flags are used when fragmenting the user data. The U (Unordered) flag identifies the unordered DATA chunks. /The DATA user data chunks is sent are acknowledged inside the DATA by the chunks. SACK The chunks. Payload Protocol Identifier identifies upper user that generated the to DATA /(PPI) A SACK chunkthe acknowledges all TSNs previous (andchunk. including) the Cumulative /TSN A DATA Acknowledgement. chunk is uniquely The identified Gap Ack Blocks by its Transmission are included if Sequence there is a hole Number in the reception (TSN). Itssequence. order inside the Stream is given by the Stream Sequence Number /(SSN). If a duplicate TSN was received duplicated, its TSN is included in a Duplicate TSN. /The B (Beginning) and E (End) flags are used when fragmenting the user data. The Author: Iván Arias Rodríguez (Unordered) flag The identifies thereliable unordered DATA Stream. U Control Transmission Protocol: design of a new transport protocol for IPchunks. networks Supervisor: Raimo Kantola
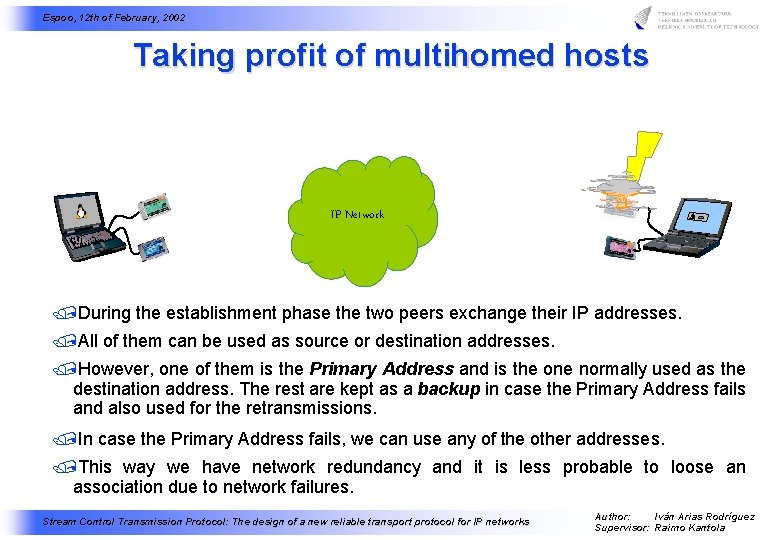
Espoo, 12 th of February, 2002 Taking profit of multihomed hosts Source Port Number Source Destination Port Number Destination Verification Tag = = Tag Z Z Chunk Type = =3 3 (SACK) Chunk Type (SACK) Checksum Chunk Flags Reserved) Chunk Flags (( Reserved) Chunk Length Chunk Cumulative TSN Acknowledgement Cumulative Advertised Receiver Window Credit Advertised Number of of Gap Ack Blocks = =G G Number of of Duplicate TSNs = =D D Number Gap Ack Block #1 #1 Start Gap Ack Block #1 #1 End Gap. . . Source Port Number Destination Port Number Source Port Number Verification Tag = Tag Z Checksum Chunk Type = 0 Reserved U B E (DATA) Gap Ack Block #G #G End Gap Duplicate TSN #1 #1 Duplicate. . . Stream Identifier Destination Port Number Verification Tag = Tag Z Checksum Chunk Type = 0 Reserved U B E (DATA) Chunk Length Transmission Sequence Number Gap Ack Block #G #G Start Gap Chunk Length Transmission Sequence Number Stream Identifier Stream Sequence Number Payload Protocol Identifier User Data Duplicate TSN #D #D Source Port Number Destination Port Number Verification Tag = Tag Z Chunk Type = 3 (SACK) Checksum Chunk Flags ( Reserved) Chunk Length Cumulative TSN Acknowledgement Advertised Receiver Window Credit Number of Gap Ack Blocks = G IP Network Source Port Number of Duplicate TSNs = D Gap Ack Block #1 Start Destination Port Number Verification Tag = Tag Z Gap Ack Block #1 End Checksum Chunk Type = 0 Reserved U B E (DATA) . . . Gap Ack Block #G Start Chunk Length Transmission Sequence Number Gap Ack Block #G End Stream Identifier Duplicate TSN #1 Stream Sequence Number Payload Protocol Identifier. . . User Data Duplicate TSN #D /During the establishment phase the two peers exchange their IP addresses. /All of them can be used as source or destination addresses. /However, one of them is the Primary Address and is the one normally used as the destination address. The rest are kept as a backup in case the Primary Address fails and also used for the retransmissions. /In case the Primary Address fails, we can use any of the other addresses. /This way we have network redundancy and it is less probable to loose an association due to network failures. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
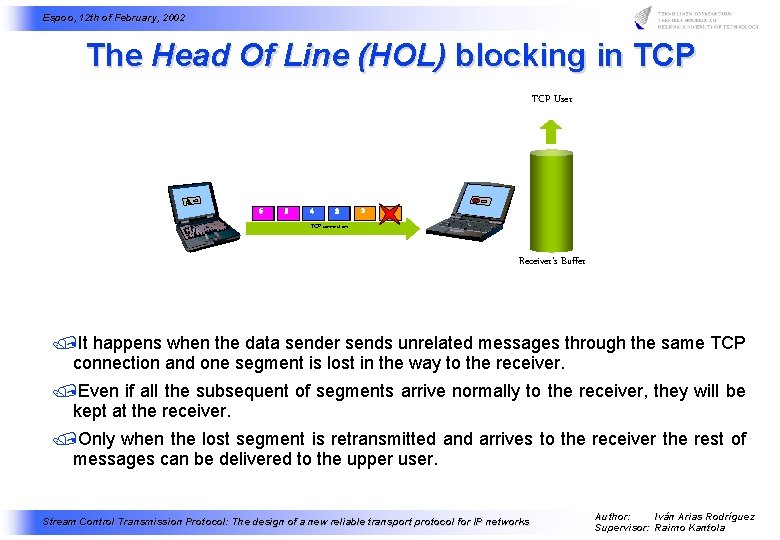
Espoo, 12 th of February, 2002 The Head Of Line (HOL) blocking in TCP User 6 5 4 3 2 1 1 2 32 324 5324 65234 514236 TCP connection Receiver's Buffer /It happens when the data sender sends unrelated messages through the same TCP connection and one segment is lost in the way to the receiver. /Even if all the subsequent of segments arrive normally to the receiver, they will be kept at the receiver. /Only when the lost segment is retransmitted and arrives to the receiver the rest of messages can be delivered to the upper user. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
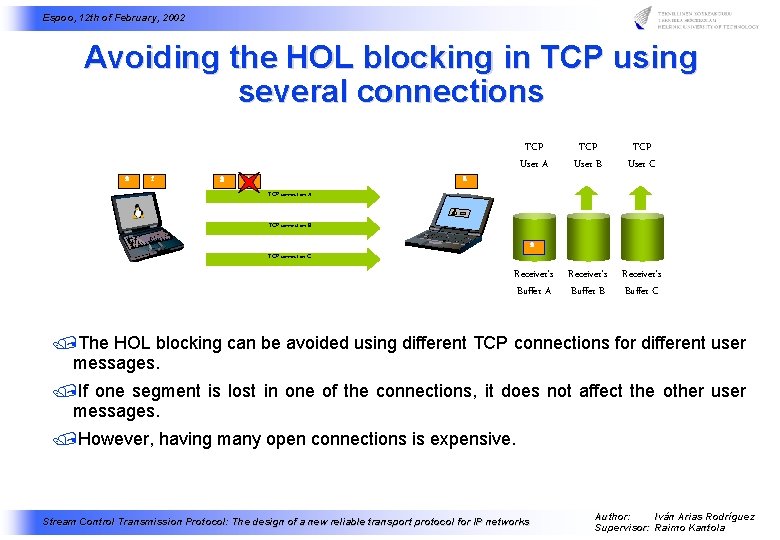
Espoo, 12 th of February, 2002 Avoiding the HOL blocking in TCP using several connections 2 1 2 TCP User A TCP User B TCP User C 2 1 2 Receiver's Buffer A Receiver's Buffer B Receiver's Buffer C 2 1 TCP connection A 2 2 TCP connection B 2 1 1 TCP connection C /The HOL blocking can be avoided using different TCP connections for different user messages. /If one segment is lost in one of the connections, it does not affect the other user messages. /However, having many open connections is expensive. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
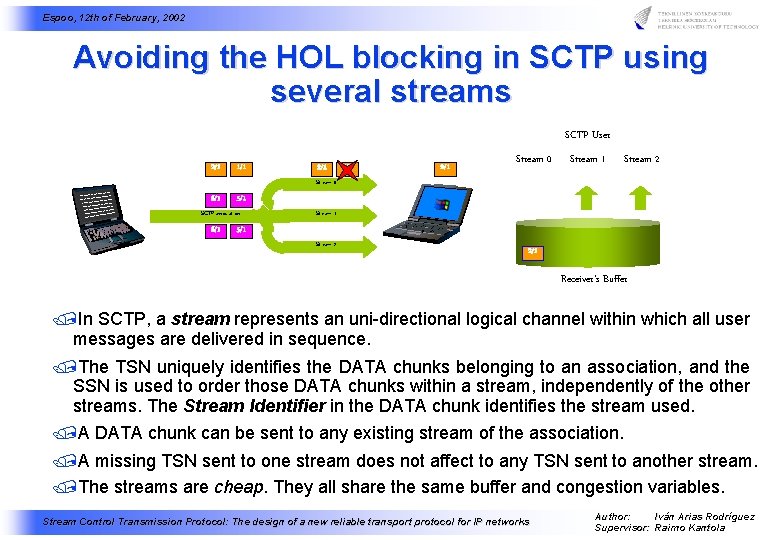
Espoo, 12 th of February, 2002 Avoiding the HOL blocking in SCTP using several streams SCTP User 2/1 1/1 Stream 0 Stream 1 Stream 2 2/1 3/1 4/1 5/1 6/1 Stream 0 6/1 2/1 5/1 1/1 SCTP association 6/1 4/1 2/1 3/1 Stream 1 5/1 6/1 Stream 2 5/1 Receiver's Buffer /In SCTP, a stream represents an uni-directional logical channel within which all user messages are delivered in sequence. /The TSN uniquely identifies the DATA chunks belonging to an association, and the SSN is used to order those DATA chunks within a stream, independently of the other streams. The Stream Identifier in the DATA chunk identifies the stream used. /A DATA chunk can be sent to any existing stream of the association. /A missing TSN sent to one stream does not affect to any TSN sent to another stream. /The streams are cheap. They all share the same buffer and congestion variables. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
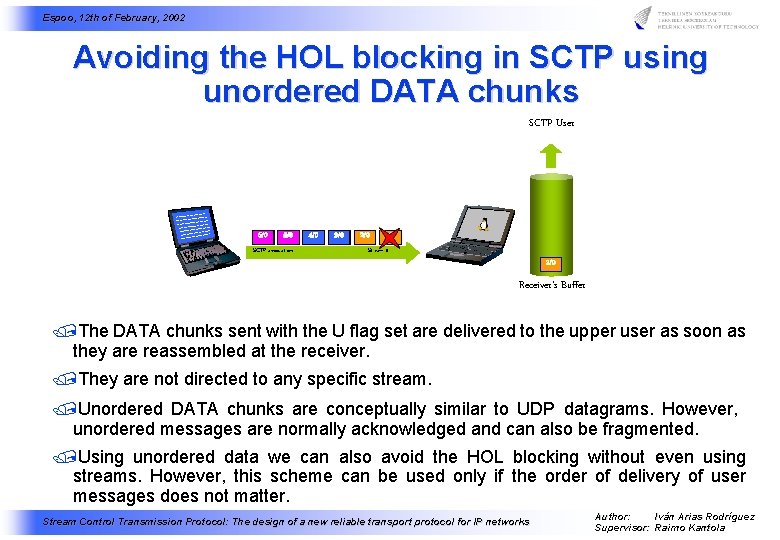
Espoo, 12 th of February, 2002 Avoiding the HOL blocking in SCTP using unordered DATA chunks SCTP User 6/0 5/0 SCTP association 4/0 3/0 2/0 1 2/0 3/0 2/0 5/0 4/0 2/0 3/0 5/0 6/0 5/0 2/0 3/0 4/0 6/0 Stream 0 Receiver's Buffer /The DATA chunks sent with the U flag set are delivered to the upper user as soon as they are reassembled at the receiver. /They are not directed to any specific stream. /Unordered DATA chunks are conceptually similar to UDP datagrams. However, unordered messages are normally acknowledged and can also be fragmented. /Using unordered data we can also avoid the HOL blocking without even using streams. However, this scheme can be used only if the order of delivery of user messages does not matter. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
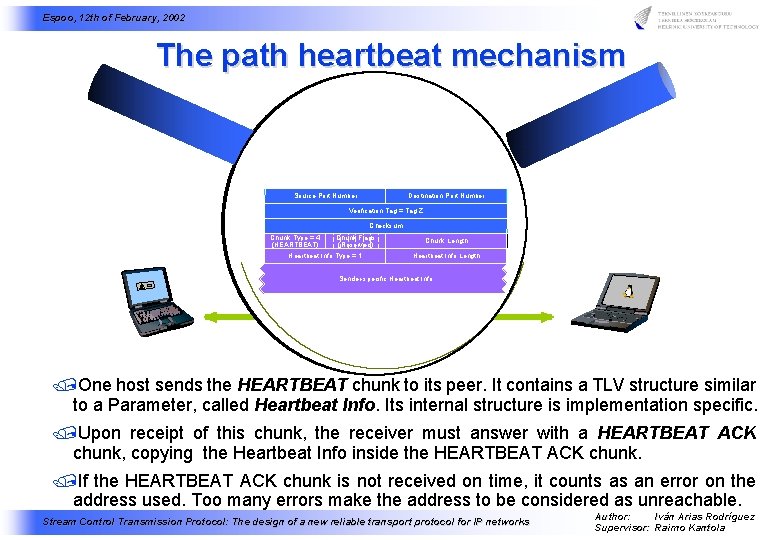
Espoo, 12 th of February, 2002 The path heartbeat mechanism Source Port Number Destination Port Number Verification Tag = Tag A Z Checksum Chunk Type = 5= 4 (HEARTBEAT) (HEARTBEAT A. ) Chunk Flags (Reserved) Heartbeat Info Type = 1= 1 Chunk Length Heartbeat Info Length Sender-specific Heartbeat Info Source Port Number Destination Port Number Verification Tag = Tag Z Verification Tag = Tag A Checksum Chunk Type = 4 Chunk Flags (HEARTBEAT) Checksum Chunk Type =(Reserved) 5 Chunk Flags (HEARTBEAT A. ) Chunk Length (Reserved) Chunk Length Heartbeat Info Type = 1 Heartbeat Info Length Sender-specific Heartbeat Info /One host sends the HEARTBEAT chunk to its peer. It contains a TLV structure similar to a Parameter, called Heartbeat Info. Its internal structure is implementation specific. /Upon receipt of this chunk, the receiver must answer with a HEARTBEAT ACK chunk, copying the Heartbeat Info inside the HEARTBEAT ACK chunk. /If the HEARTBEAT ACK chunk is not received on time, it counts as an error on the address used. Too many errors make the address to be considered as unreachable. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
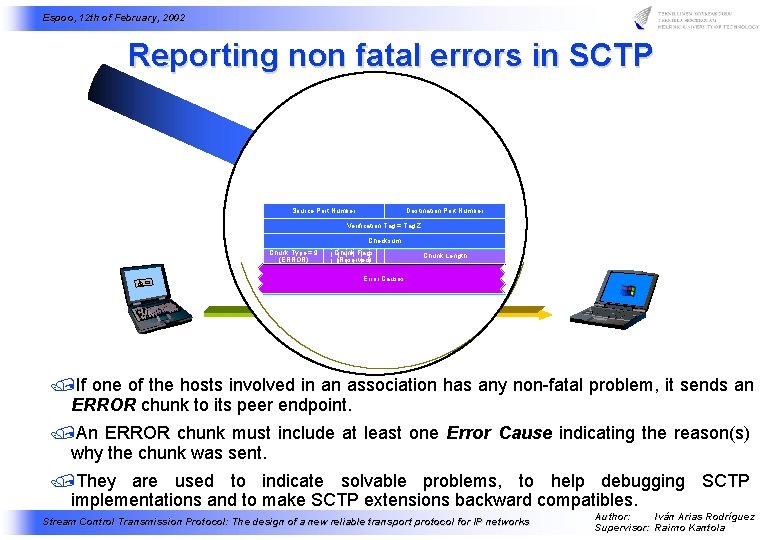
Espoo, 12 th of February, 2002 Reporting non fatal errors in SCTP Source Port Number Destination Port Number Verification Tag = Tag Z Checksum Chunk Type = 9 (ERROR) Chunk Flags (Reserved) Chunk Length Error Causes Source Port Number Destination Port Number Verification Tag = Tag Z Chunk Typ = 9 (ERROR) Checksum Chunk Flags (Reserved) Chunk Length Parameters /If one of the hosts involved in an association has any non-fatal problem, it sends an ERROR chunk to its peer endpoint. /An ERROR chunk must include at least one Error Cause indicating the reason(s) why the chunk was sent. /They are used to indicate solvable problems, to help debugging SCTP implementations and to make SCTP extensions backward compatibles. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
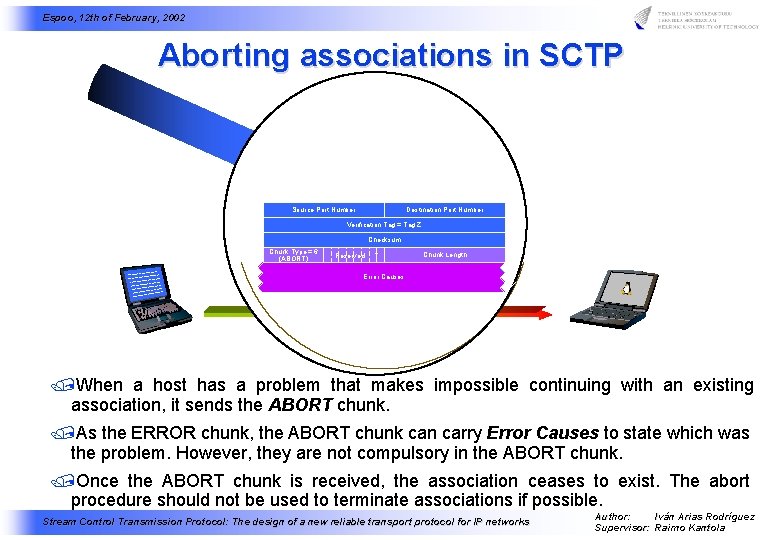
Espoo, 12 th of February, 2002 Aborting associations in SCTP Source Port Number Destination Port Number Verification Tag = Tag Z Checksum Chunk Type = 6 (ABORT) Reserved Chunk Length T Error Causes Source Port Number Destination Port Number Verification Tag = Tag Z Chunk Typ = 6 (ABORT) Reserveddf Checksum T Chunk Length Parameters /When a host has a problem that makes impossible continuing with an existing association, it sends the ABORT chunk. /As the ERROR chunk, the ABORT chunk can carry Error Causes to state which was the problem. However, they are not compulsory in the ABORT chunk. /Once the ABORT chunk is received, the association ceases to exist. The abort procedure should not be used to terminate associations if possible. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
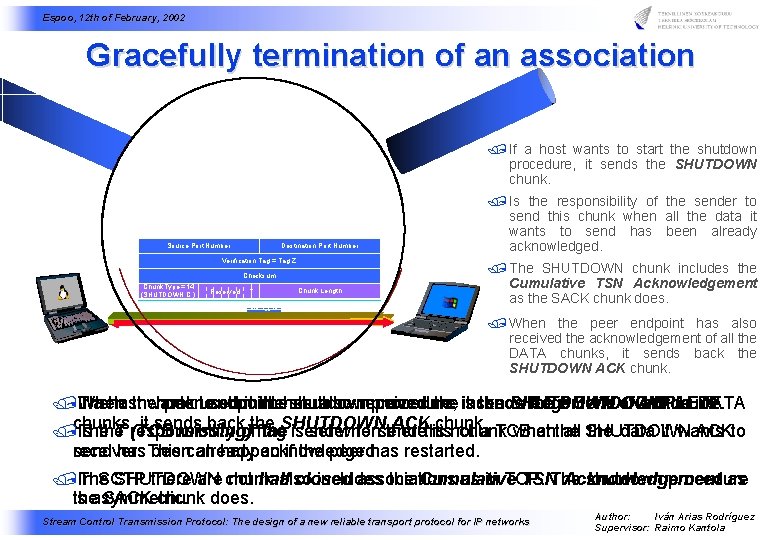
Espoo, 12 th of February, 2002 Gracefully termination of an association / If a host wants to start the shutdown procedure, it sends the SHUTDOWN chunk. Source Port Number Destination Port Number Verification Tag = Tag Z Z Verification Tag = Tag A Checksum Chunk Type = 8 (SHUTDOWN) Chunk. Type==14 9 Chunk A. ) (SHUTDOWN C. ) Chunk Flags Checksum Chunk Length (Reserved) Chunk Flags Reserved T TSN ACK Chunk Length Cumulative (Reserved) Source Port Number Verification Tag = Tag Z Source Port Number Destination Port Number Checksum Verification Tag = Tag Z Chunk (Reserved) Source. Flags Port Number Destination Port Number Chunk Length Checksum Verification Tag = Tag A Chunk Flags (Reserved) Chunk Length Received Cookie Checksum Chunk Type =A. ) 9 Chunk Flags (SHUTDOWN (Reserved) Cumulative TSN ACK Chunk Length / Is the responsibility of the sender to send this chunk when all the data it wants to send has been already acknowledged. / The SHUTDOWN chunk includes the Cumulative TSN Acknowledgement as the SACK chunk does. Chunk Type = 10 (COOKIE ECHO) Chunk Type = 8 (SHUTDOWN) / When the peer endpoint has also received the acknowledgement of all the DATA chunks, it sends back the SHUTDOWN ACK chunk. /When The If a host last the chunk wants peerto used endpoint start in thehas shutdown also received procedure, procedure the is itacknowledgement sends the SHUTDOWN of COMPLETE. all the chunk. DATA it sends backofthe ACKthis chunk. /chunks, The Is the T (TCB responsibility missing) flag the. SHUTDOWN is sender set when to send there is not chunk a TCB when at the all SHUTDOWN the data it wants ACKto receiver. send has This beencan already happen acknowledged. if the peer has restarted. /In The SCTP SHUTDOWN there are chunk not half also closed includes associations the Cumulative as in TCP. TSNThe Acknowledgement shutdown procedure as is theasymmetric. SACK chunk does. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
Espoo, 12 th of February, 2002 Summarizing: Main characteristics of SCTP /It is able to take profit of multihomed hosts. /It can avoid the SYN attack thanks to its cookie mechanism. /The existence of independent streams helps avoiding the HOL blocking. /It is message-oriented as UDP, but at the same time reliable as TCP is. /It is able to notify error conditions, thus making possible solving certain errors at the transport level. /It is highly inspired in TCP. Most of the optional features of TCP are compulsory in SCTP. The congestion avoidance mechanism is the same as in TCP. /SCTP uses a very similar socket interface than the one TCP uses. /There already some open source SCTP implementations. /SCTP performance is at least as good as TCP's one. Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
Espoo, 12 th of February, 2002 Questions? Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
Espoo, 12 th of February, 2002 Extra slides Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
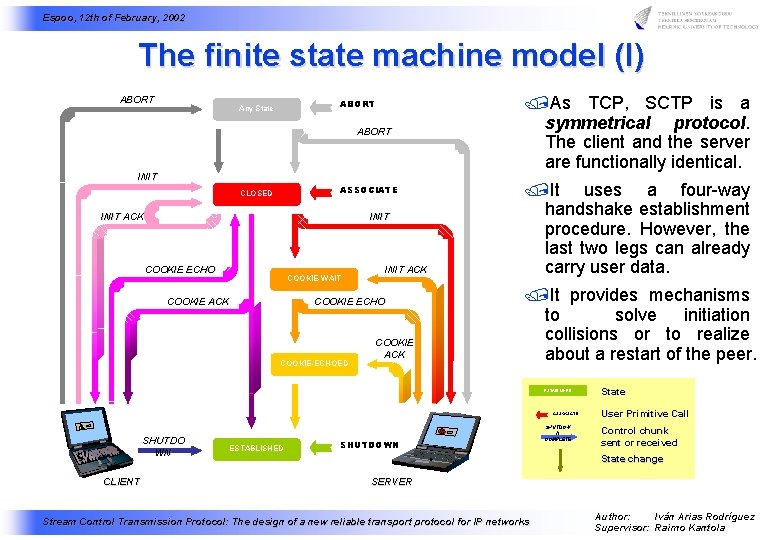
Espoo, 12 th of February, 2002 The finite state machine model (I) ABORT Any State ABORT INIT ASSOCIATE CLOSED INIT ACK INIT COOKIE ECHO COOKIE-WAIT COOKIE ACK INIT ACK COOKIE ECHO COOKIE-ECHOED COOKIE ACK /As TCP, SCTP is a symmetrical protocol. The client and the server are functionally identical. /It uses a four-way handshake establishment procedure. However, the last two legs can already carry user data. /It provides mechanisms to solve initiation collisions or to realize about a restart of the peer. ESTABLISHED ASSOCIATE SHUTDO WN CLIENT ESTABLISHED SHUTDOWN SHUTDOW N COMPLETE State User Primitive Call Control chunk sent or received State change SERVER Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
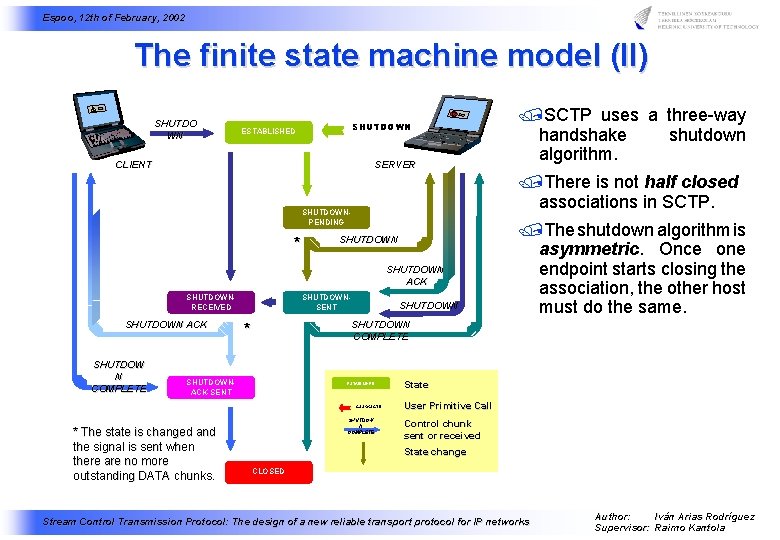
Espoo, 12 th of February, 2002 The finite state machine model (II) SHUTDO WN SHUTDOWN ESTABLISHED CLIENT SERVER /There is not half closed associations in SCTP. SHUTDOWNPENDING * SHUTDOWN ACK SHUTDOWNRECEIVED SHUTDOWN ACK SHUTDOW N COMPLETE SHUTDOWNSENT SHUTDOWN /The shutdown algorithm is asymmetric. Once one endpoint starts closing the association, the other host must do the same. SHUTDOWN COMPLETE * SHUTDOWNACK-SENT ESTABLISHED ASSOCIATE * The state is changed and the signal is sent when there are no more outstanding DATA chunks. /SCTP uses a three-way handshake shutdown algorithm. SHUTDOW N COMPLETE State User Primitive Call Control chunk sent or received State change CLOSED Stream Control Transmission Protocol: The design of a new reliable transport protocol for IP networks Author: Iván Arias Rodríguez Supervisor: Raimo Kantola
- Slides: 21