Enhancing the Bootstrapping Network in Cloudbased Onion Routing
Enhancing the Bootstrapping Network in Cloud-based Onion Routing (COR) Kevin Snider CS 7000 Master’s Thesis Defense University of Colorado at Colorado Springs
Introduction • Tor (The onion router) • Purpose • Preserve Privacy & Anonymity • Usage 1 2 • Individuals uncomfortable with online tracking/surveillance • Censorship Resistance • Free Speech • Whistleblowers UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 3 4 2
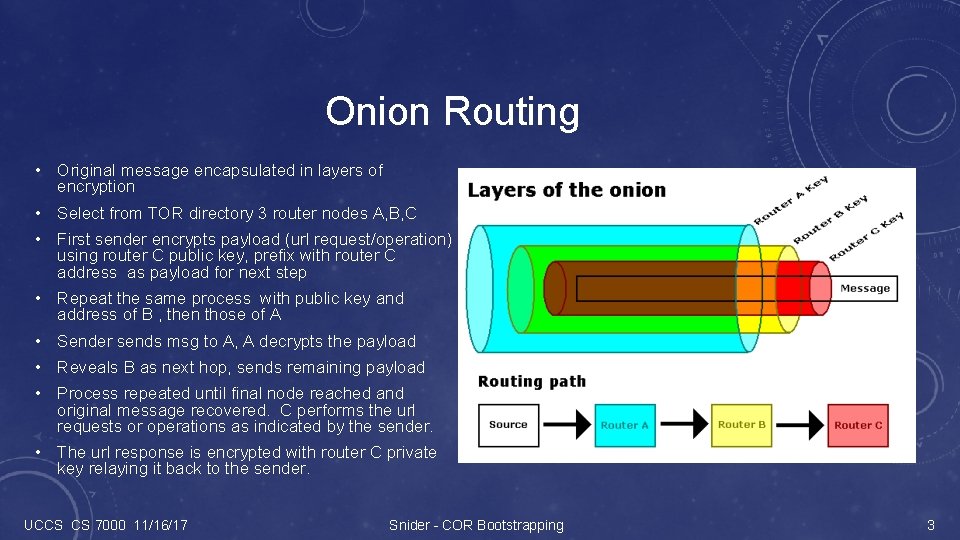
Onion Routing • Original message encapsulated in layers of encryption • Select from TOR directory 3 router nodes A, B, C • First sender encrypts payload (url request/operation) using router C public key, prefix with router C address as payload for next step • Repeat the same process with public key and address of B , then those of A • Sender sends msg to A, A decrypts the payload • Reveals B as next hop, sends remaining payload • Process repeated until final node reached and original message recovered. C performs the url requests or operations as indicated by the sender. 5 • The url response is encrypted with router C private key relaying it back to the sender. UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 3
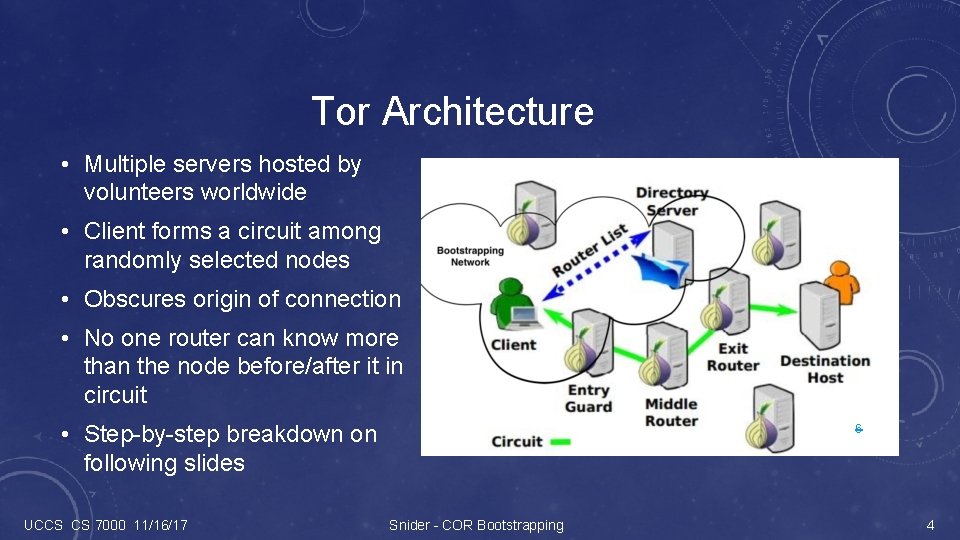
Tor Architecture • Multiple servers hosted by volunteers worldwide • Client forms a circuit among randomly selected nodes • Obscures origin of connection • No one router can know more than the node before/after it in circuit • Step-by-step breakdown on following slides UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 6 4
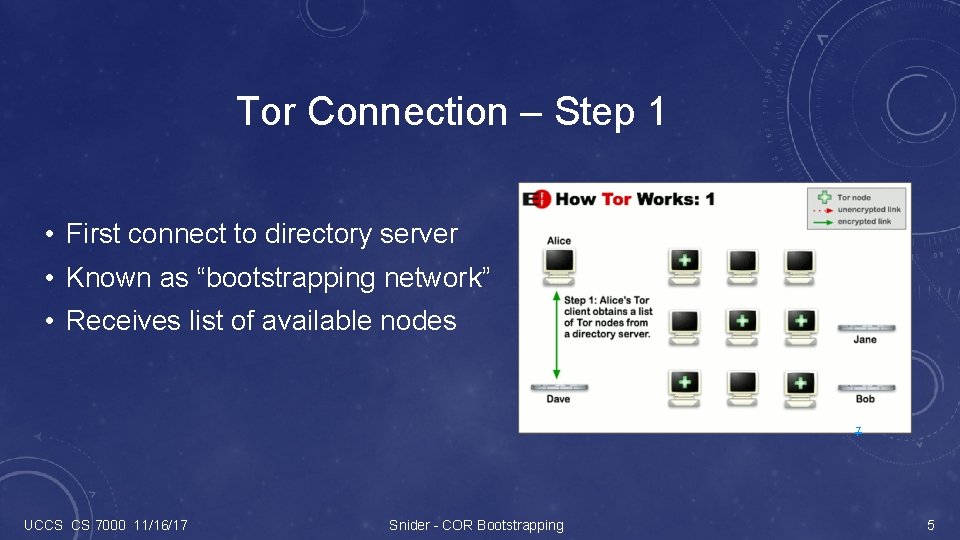
Tor Connection – Step 1 • First connect to directory server • Known as “bootstrapping network” • Receives list of available nodes 7 UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 5
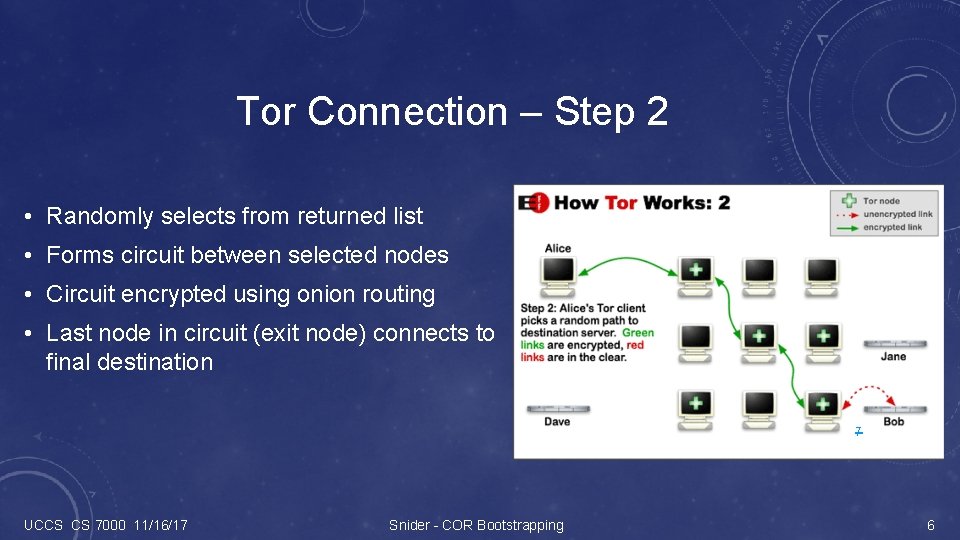
Tor Connection – Step 2 • Randomly selects from returned list • Forms circuit between selected nodes • Circuit encrypted using onion routing • Last node in circuit (exit node) connects to final destination 7 UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 6
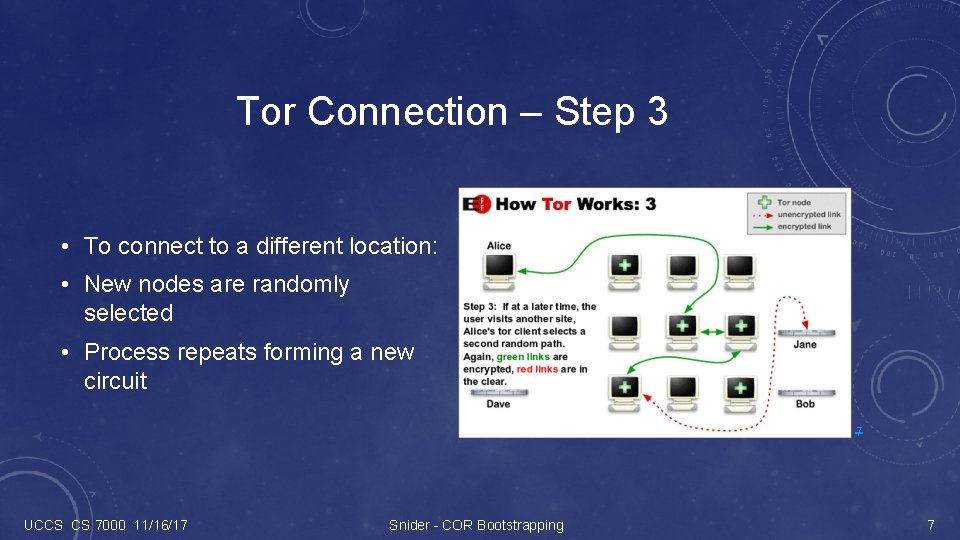
Tor Connection – Step 3 • To connect to a different location: • New nodes are randomly selected • Process repeats forming a new circuit 7 UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 7
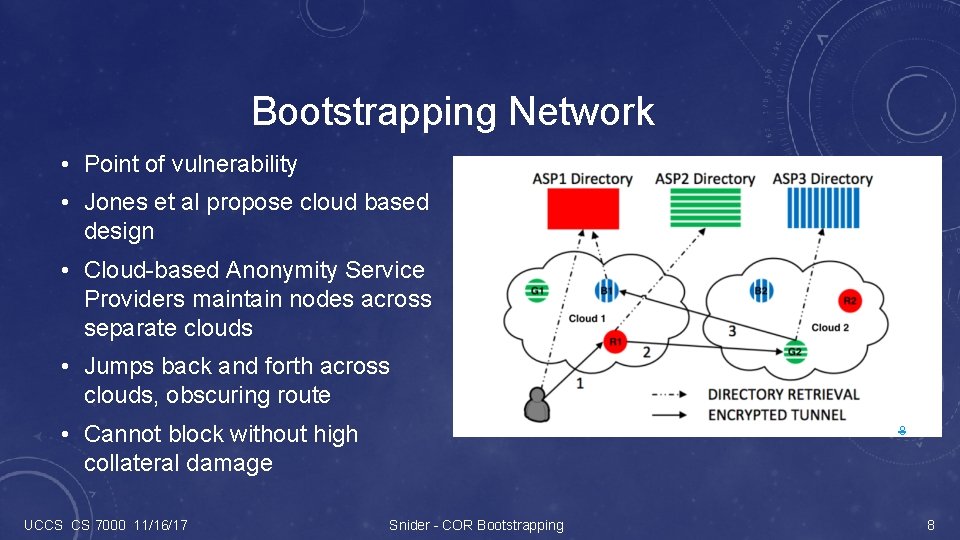
Bootstrapping Network • Point of vulnerability • Jones et al propose cloud based design • Cloud-based Anonymity Service Providers maintain nodes across separate clouds • Jumps back and forth across clouds, obscuring route • Cannot block without high collateral damage UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 8 8
Related Work • Theory & Origins • Bootstrapping • Reed 1998 • Lincoln 2012 • Dingledine 2004 • Jones 2011 • Mc. Coy 2008 • Cloud-based • Censorship Resistance Systems • Khattak 2016 • Brubaker 2014 • Jones 2011 • Tschantz 2016 UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 9
Thesis Goal: Design and implement an efficient bootstrapping network framework to • Allow an ASP to provide anonymity services on a cloud-based architecture • Provide to a client the ability to set up a secure bootstrapping circuit that protects their privacy. Tasks: • Create virtual machines on different AWS regions to simulate different cloud-service providers • Create ASP service • Create client-side software tool • Create relay service • Document design and implementation, evaluate performance UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 10
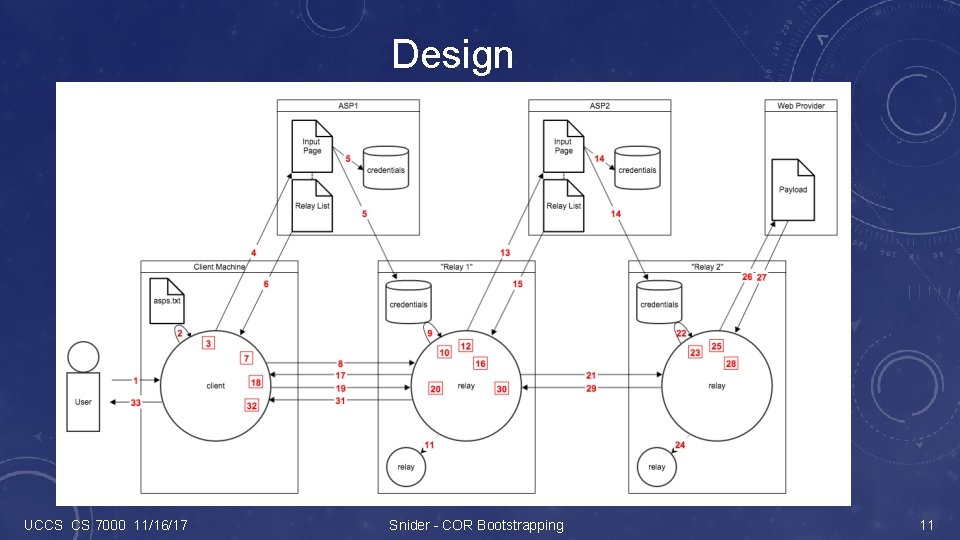
Design UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 11
Implementation • Amazon Web Services (AWS) EC 2 • 3 regions: Oregon, Ohio, Virginia • 13 Amazon Linux AMI t 2. micro instances • 3 ASP servers • 9 relays (3 in each region, one for each ASP) • 1 to simulate client • ASP • HTTPS-enable Apache web server • HTML input page, PHP script • My. SQL database instance • Relay • Same webserver functionality • C socket program • Client • C socket program UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 12
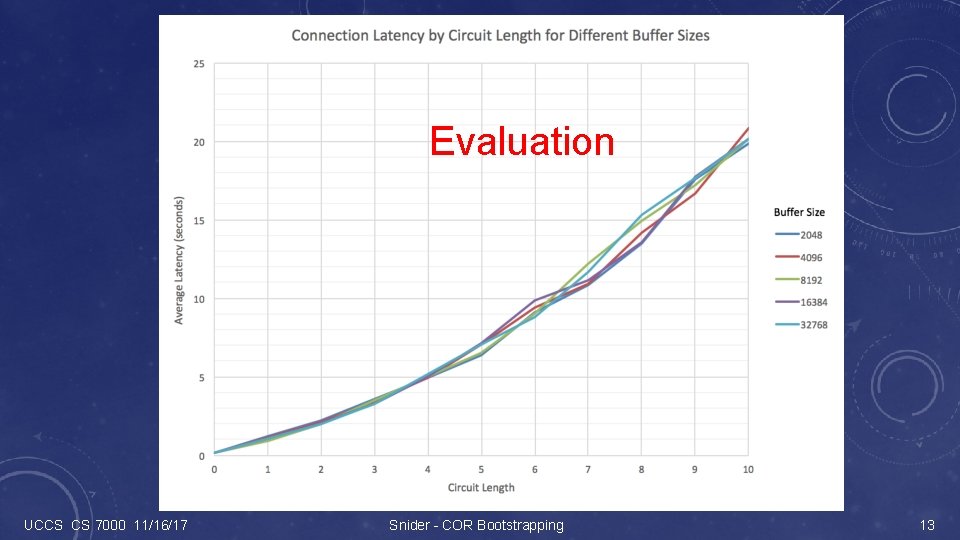
Evaluation UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 13
Lessons Learned • Importance of solid design • C socket programming, client-server model • RSA and AES encryption routines, proper application of each method • Apache httpd service installation and configuration • My. SQL service installation and configuration, basic database management commands • Expanded HTML webpage programming skills • Proper use and reasons for Base 64 and URL encoding • PHP scripting, including Base-64 encoding, Curl, My. SQL, etc. commands • HTTPS protocols, key management schemes UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 14
Future Directions • Fixed buffer size • Hard-coded to single port • Credentials validation before fork • Repeated memmove calls in message building • Returns base HTML, no interaction UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 15
Conclusion • I have designed and implemented a Bootstrap Network on AWS cloud with three regions for TOR network. • It is capable of zigzac through instances provided by different ASP providers based on the user’s specified circuit length. • The keys are generated by the sender uploaded to the ASP for distributing to the instances. • The performance of the bootstrap circuit is ? (# of msec for 10 hops; and web page access through the relay ciricuit is #Kbytes/sec) UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 16
Demonstration UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 17
References • Jones, N. , Arye, M. , Cesareo, J. , & Freedman, M. J. (2011, August). Hiding Amongst the Clouds: A Proposal for Cloud-based Onion Routing. In FOCI. Available: http: //static. usenix. org/events/foci 11/tech/final_files/Jones. pdf • Dingledine, R. , Mathewson, N. , & Syverson, P. (2004). Tor: The second-generation onion router. In 13 th USENIX Security Symposium, Aug. 2004. Available: http: //oai. dtic. mil/oai? verb=get. Record&metadata. Prefix=html&identifier=ADA 465464 • Tschantz, M. C. , Afroz, S. , & Paxson, V. (2016, May). So. K: Towards Grounding Censorship Circumvention in Empiricism. In Security and Privacy (SP), 2016 IEEE Symposium on (pp. 914 -933). IEEE. Available: https: //censorbib. nymity. ch/pdf/Tschantz 2016 a. pdf • Lincoln, P. , Mason, I. , Porras, P. A. , Yegneswaran, V. , Weinberg, Z. , Massar, J. , . . . & Boneh, D. (2012, August). Bootstrapping Communications into an Anti-Censorship System. In FOCI. Available: https: //www. usenix. org/system/files/conference/foci 12 -final 7. pdf • Khattak, S. , Elahi, T. , Simon, L. , Swanson, C. M. , Murdoch, S. J. , & Goldberg, I. (2016). So. K: Making Sense of Censorship Resistance Systems. Proceedings on Privacy Enhancing Technologies, 2016(4), 37 -61. Available: https: //www. degruyter. com/downloadpdf/j/popets. 2016. issue-4/popets-2016 -0028. pdf • Brubaker, C. , Houmansadr, A. , & Shmatikov, V. (2014, July). Cloudtransport: Using cloud storage for censorship-resistant networking. In International Symposium on Privacy Enhancing Technologies Symposium (pp. 1 -20). Springer International Publishing. Available: https: //www. freehaven. net/anonbib/cache/pets 14 -cloudtransport. pdf • Mc. Coy, D. , Bauer, K. , Grunwald, D. , Kohno, T. , & Sicker, D. (2008, July). Shining light in dark places: Understanding the Tor network. In International Symposium on Privacy Enhancing Technologies Symposium (pp. 63 -76). Springer Berlin Heidelberg. Available: https: //pdfs. semanticscholar. org/97 cd/66 eb 1 c 75 f 2 b 5 d 4 c 91 c 7 d 2 d 6661 b 56 d 6988 bc. pdf • Reed, M. G. , Syverson, P. F. , & Goldschlag, D. M. (1998). Anonymous connections and onion routing. IEEE Journal on Selected areas in Communications, 16(4), 482 -494. Available: http: //www. dtic. mil/cgi-bin/Get. TRDoc? AD=ADA 465335 • Elgzil, A. (2017). Anonymity Software-Defined-Network-Based Onion Routing (SOR). UCCS CS Ph. D Dissertation Proposal. http: //walrus. uccs. edu/~gsc/pub/phd/aelgzil/doc/Thesis_Proposal_SOR_Elgzil_Abdelhamid. V 2. docx • Images • • [1] https: //gigaom. com/wp-content/uploads/sites/1/2012/02/internet-privacy-spy-computer-magnifying-glass-o. jpg? quality=80&strip=allll [2] https: //blogs-images. forbes. com/jacobmorgan/files/2014/09/6 a 00 d 8341 bf 67 c 53 ef 014 e 6008 bc 8 c 970 c-800 wi. jpg? width=960 [3] https: //openclipart. org/image/2400 px/svg_to_png/272337/no_censorship. png [4] http: //chinalawandpolicy. com/wp-content/uploads/2010/07/blocked-in-china-censorship-320 x 240. gif [5] https: //www. maketecheasier. com/assets/uploads/2013/02/advor-layers. png [6] http: //walrus. uccs. edu/~gsc/pub/phd/aelgzil/doc/Thesis_Proposal_SOR_Elgzil_Abdelhamid. V 2. docx [7] https: //www. torproject. org/about/overview. html. en [8] http: //static. usenix. org/events/foci 11/tech/final_files/Jones. pdf UCCS CS 7000 11/16/17 Snider - COR Bootstrapping 18
Questions?
- Slides: 19