Encryption Overview For VERITAS Net Backup Why Encrypt

Encryption Overview For VERITAS Net. Backup
Why Encrypt Backups? § Lost backup tapes and potential fraudulent activity have real financial costs – Violates the internal control process of Sarbanes-Oxley Act – Financial losses from fraud (e. g. , settlements, monitoring services) – Corporate brand, public relations impact, and customer confidence impact § Concentrated amount of data on highly portable backup tapes – Impact of tape loss 2 - 5 x greater than online breaches / stolen hardware 1 – Multiple copies of unencrypted backup tapes increases exposure § Backup / tape service providers can and do lose data – Iron Mountain had 4 instances of lost tapes (Jan – May 2005) – Iron Mountain recommends encryption of customer data § Public disclosure of data loss impacts your company – California law requires any company with a California customer record to report loss of data that comprises privacy – 22 other states considering legislation similar to California (1) Based on reported data losses Jan-May 2005 – www. privacyrights. org
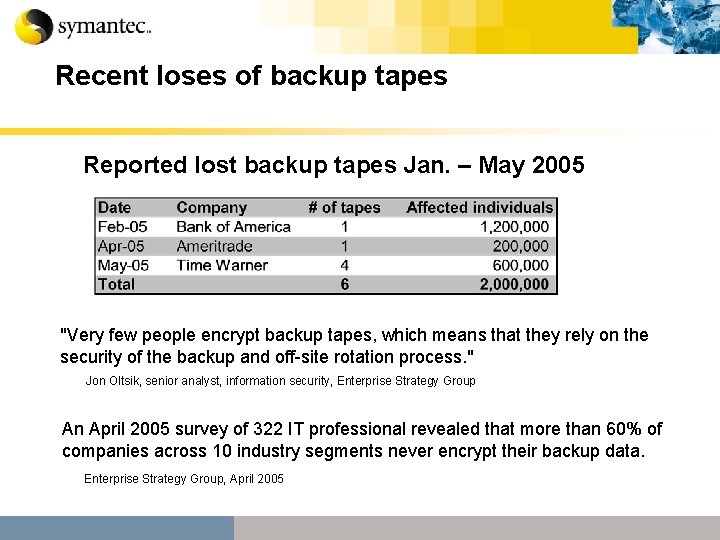
Recent loses of backup tapes Reported lost backup tapes Jan. – May 2005 "Very few people encrypt backup tapes, which means that they rely on the security of the backup and off-site rotation process. " Jon Oltsik, senior analyst, information security, Enterprise Strategy Group An April 2005 survey of 322 IT professional revealed that more than 60% of companies across 10 industry segments never encrypt their backup data. Enterprise Strategy Group, April 2005
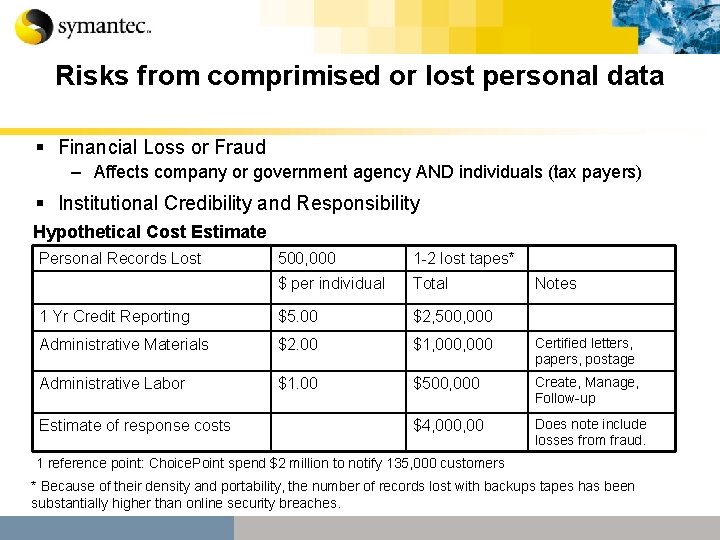
Risks from comprimised or lost personal data § Financial Loss or Fraud – Affects company or government agency AND individuals (tax payers) § Institutional Credibility and Responsibility Hypothetical Cost Estimate Personal Records Lost 500, 000 1 -2 lost tapes* $ per individual Total 1 Yr Credit Reporting $5. 00 $2, 500, 000 Administrative Materials $2. 00 $1, 000 Certified letters, papers, postage Administrative Labor $1. 00 $500, 000 Create, Manage, Follow-up $4, 000, 00 Does note include losses from fraud. Estimate of response costs Notes 1 reference point: Choice. Point spend $2 million to notify 135, 000 customers * Because of their density and portability, the number of records lost with backups tapes has been substantially higher than online security breaches.
Where to start with backup encryption § Common themes for thinking about backup security – Control and protection of data – Access to local and backup data – Ensuring that backups of critical data are maintained § Target data for encryption – Customer data or other content with private data (e. g. , forms with a social security number only) – Intellectual property – Sensitive corporate and financial data § Understand regulations or laws that impact you – Health Information Portability Act (HIPPA) & Sarbanes-Oxley – California Senate Bill 1386 – disclosure of security breach
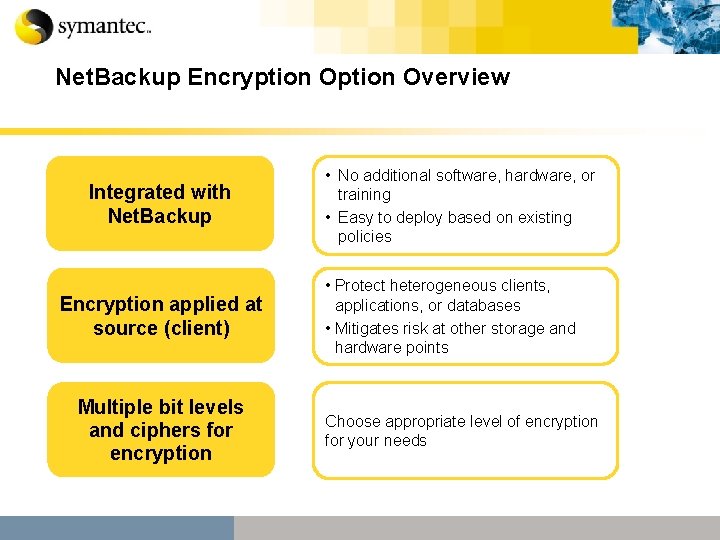
Net. Backup Encryption Overview Integrated with Net. Backup Encryption applied at source (client) Multiple bit levels and ciphers for encryption • No additional software, hardware, or training • Easy to deploy based on existing policies • Protect heterogeneous clients, applications, or databases • Mitigates risk at other storage and hardware points Choose appropriate level of encryption for your needs
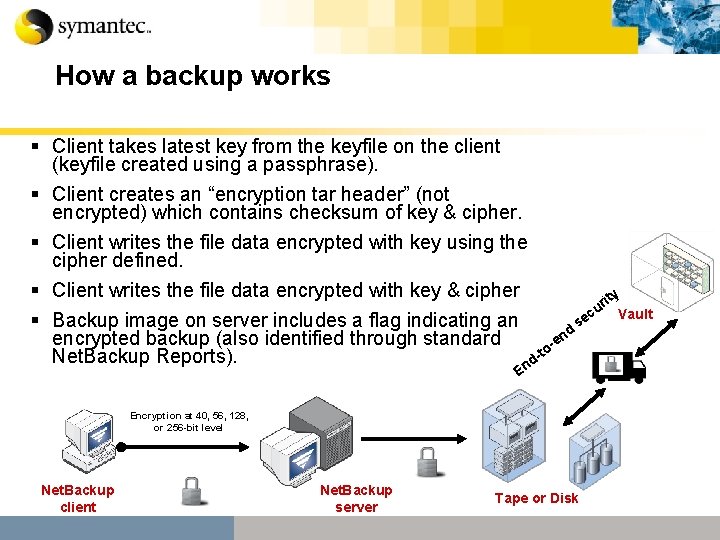
How a backup works § Client takes latest key from the keyfile on the client (keyfile created using a passphrase). § Client creates an “encryption tar header” (not encrypted) which contains checksum of key & cipher. § Client writes the file data encrypted with key using the cipher defined. § Client writes the file data encrypted with key & cipher ity r cu Vault e § Backup image on server includes a flag indicating an s d n encrypted backup (also identified through standard -e o t Net. Backup Reports). nd E Encryption at 40, 56, 128, or 256 -bit level Net. Backup client Net. Backup server Tape or Disk
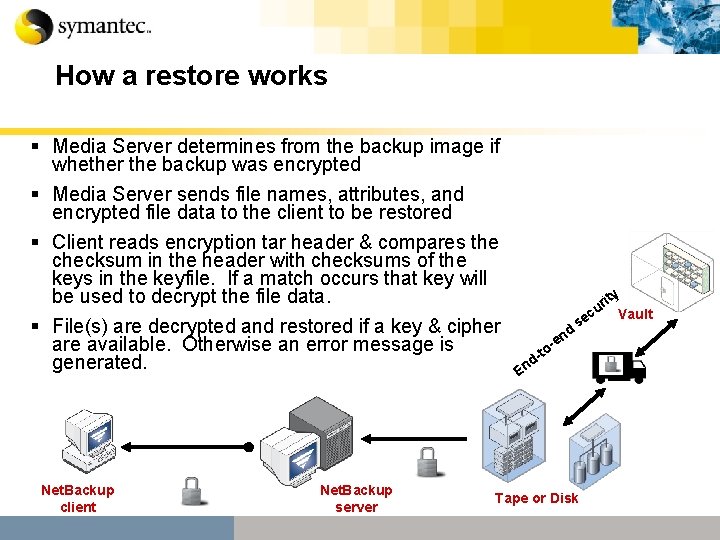
How a restore works § Media Server determines from the backup image if whether the backup was encrypted § Media Server sends file names, attributes, and encrypted file data to the client to be restored § Client reads encryption tar header & compares the checksum in the header with checksums of the keys in the keyfile. If a match occurs that key will be used to decrypt the file data. § File(s) are decrypted and restored if a key & cipher are available. Otherwise an error message is generated. Net. Backup client Net. Backup server d en s - to d- ity r u Vault ec En Tape or Disk
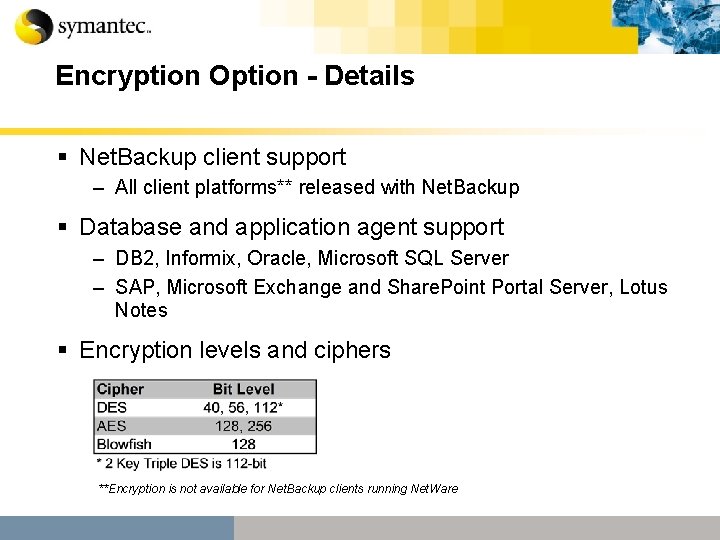
Encryption Option - Details § Net. Backup client support – All client platforms** released with Net. Backup § Database and application agent support – DB 2, Informix, Oracle, Microsoft SQL Server – SAP, Microsoft Exchange and Share. Point Portal Server, Lotus Notes § Encryption levels and ciphers **Encryption is not available for Net. Backup clients running Net. Ware
Keyfile Management § A keyfile is required to restore encrypted data § Keyfile management and encryption policies should be clearly defined across the organization regardless of whether software or hardware is used for encryption § In the event of a lost keyfile, Net. Backup can generate a new one if the user knows the pass phrase used to create the keyfile associated with the backup § For keyfile management Net. Backup recommends either: – Manual Retention: Writing successive pass phrases on paper and placing in a secure location – Automatic Retention: Create a non-encrypted policy to backup client keyfiles to a separate and secure location – Minimize complexity behind pass phrase and keyfile management
Summary § Encrypting data is far less costly than the resource use and money associated with data loss § Backup tapes can be stolen or lost regardless of the physical location where they reside § Software encryption option available today for Net. Backup: – – Centralized deployment to clients with standard Net. Backup process Easy to target data for encryption through use of policies Cost effective to deploy on a per client basis as needs dictate Customers have a choice of ciphers (AES, DES, Blowfish) and bit levels (40, 56, 128, 256) § Security of sensitive backup data required by law in some industries
& QUESTIONS ANSWERS
Other articles and sources of interest § So you think your data is secure (Computer World Quick. Link# 56000) http: //www. computerworld. com/securitytopics/security/story/0, 10801, 103869, 00. html § Are companies prepared for a security breach? (Computer World Quick. Link# 56495 ) http: //www. computerworld. com/securitytopics/security/privacy/story/0, 10801, 104311, 00. html? SKC=security-104311 § Choice. Point – Feb 2005 breech – What it cost (Computer World Quick. Link# 56527 ) http: //www. computerworld. com/securitytopics/security/privacy/story/0, 10801, 104276, 00. html? from=story%5 Fkc § Chronology of security breaches in 2005 http: //www. privacyrights. org
- Slides: 13