Enabling a Flexible Workforce an insiders view Asif

Enabling a Flexible Workforce, an insider’s view Asif Jinnah Field Desktop Services
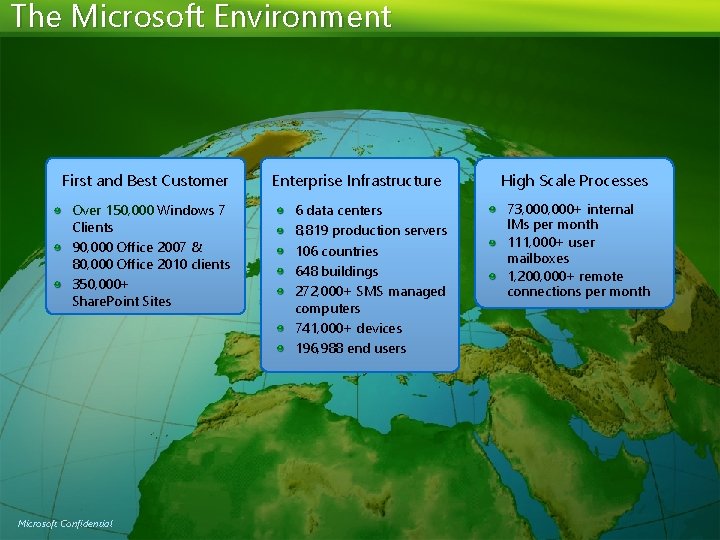
The Microsoft Environment First and Best Customer Over 150, 000 Windows 7 Clients 90, 000 Office 2007 & 80, 000 Office 2010 clients 350, 000+ Share. Point Sites Microsoft Confidential Enterprise Infrastructure 6 data centers 8, 819 production servers 106 countries 648 buildings 272, 000+ SMS managed computers 741, 000+ devices 196, 988 end users High Scale Processes 73, 000+ internal IMs per month 111, 000+ user mailboxes 1, 200, 000+ remote connections per month
Innovative IT as an Enabler. . Microsoft Confidential
Why Go into the Office? Microsoft Confidential
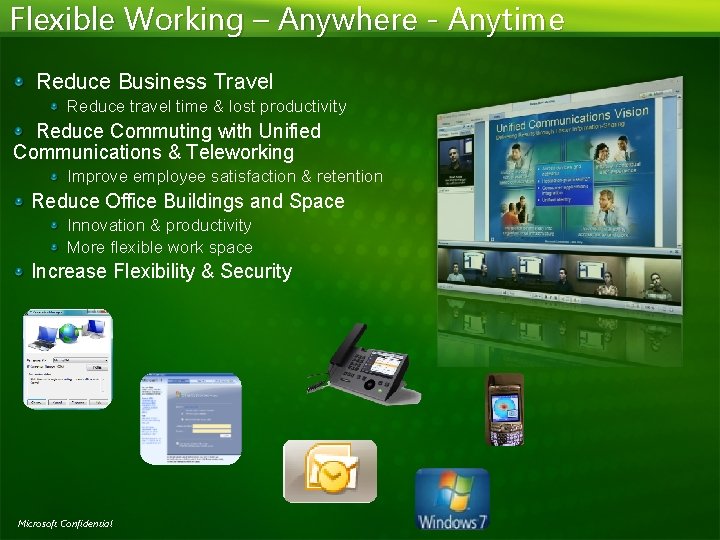
Flexible Working – Anywhere - Anytime Reduce Business Travel Reduce travel time & lost productivity Reduce Commuting with Unified Communications & Teleworking Improve employee satisfaction & retention Reduce Office Buildings and Space Innovation & productivity More flexible work space Increase Flexibility & Security Microsoft Confidential
Preparing the Workforce - Readiness Windows Online Training, Help and Support Work Smart Productivity Training Proactive Role for IT 33, 685 Employees Attended 627, 000 hours in productivity $40 Mil return (Soft ROI) Microsoft Confidential
Microsoft UK Cost Savings In Microsoft UK, the Sales & Marketing and Support Group has seen average cost reductions of over 50% in both T&E and Telecoms, generating savings of £ 3. 6 m ($5. 7 m) saving year on year (over the period from November 2008 to Oct 2009 compared to the previous 12 months) T&E costs savings are 51% T&E (£ 3. 3 m or $5. 2 m) Telecom costs savings are 54% Telecoms (£ 320 k or $505 k) The cost savings are due to the adoption of Unified Communication and Live Meeting and changes in the travel policy. The travel policy changes resulted in many business meetings being hosted online and therefore business continued as before. Microsoft Confidential
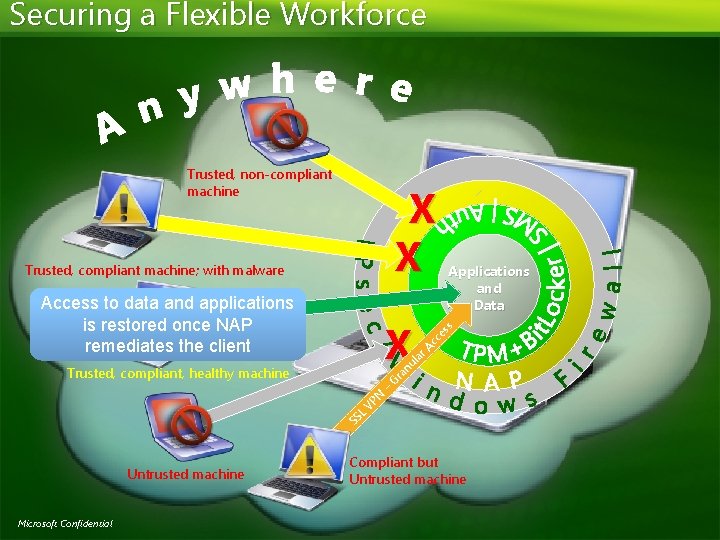
Securing a Flexible Workforce Trusted, non-compliant machine X X Trusted, compliant machine; with malware Access to data and applications is restored once NAP remediates the client X Trusted, compliant, healthy machine SS Untrusted machine Microsoft Confidential L N VP – ss ar l nu a Gr Applications and Data ce Ac Compliant but Untrusted machine
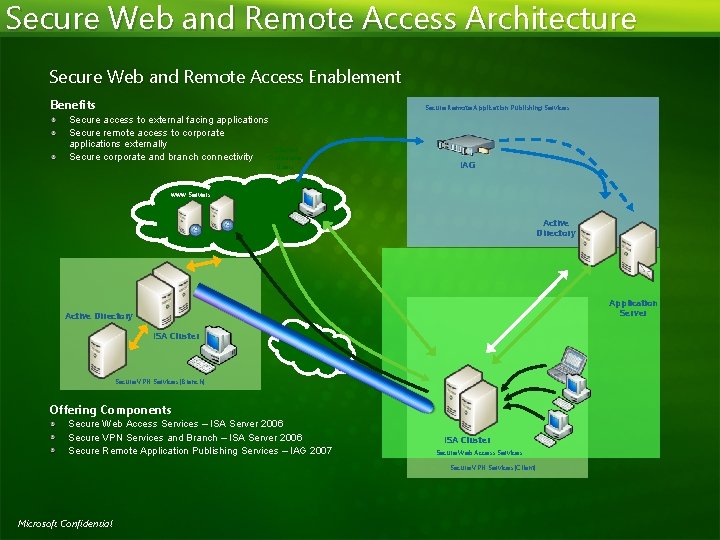
Secure Web and Remote Access Architecture Secure Web and Remote Access Enablement Benefits Secure Remote Application Publishing Services Secure access to external facing applications Secure remote access to corporate applications externally External Corporate Secure corporate and branch connectivity Users IAG www Servers Active Directory Application Server Active Directory ISA Cluster Secure VPN Services (Branch) Offering Components Secure Web Access Services – ISA Server 2006 Secure VPN Services and Branch – ISA Server 2006 Secure Remote Application Publishing Services – IAG 2007 ISA Cluster Secure Web Access Services Secure VPN Services (Client) Microsoft Confidential
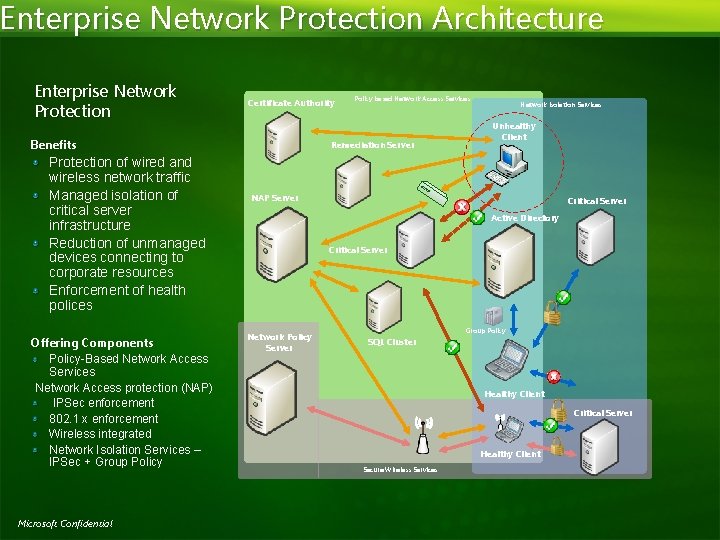
Enterprise Network Protection Architecture Enterprise Network Protection Certificate Authority Benefits Protection of wired and wireless network traffic Managed isolation of critical server infrastructure Reduction of unmanaged devices connecting to corporate resources Enforcement of health polices Offering Components Policy-Based Network Access Services Network Access protection (NAP) IPSec enforcement 802. 1 x enforcement Wireless integrated Network Isolation Services – IPSec + Group Policy Microsoft Confidential Policy based Network Access Services Remediation Server Network Isolation Services Unhealthy Client NAP Server Critical Server Active Directory Critical Server Network Policy Server Group Policy SQL Cluster Healthy Client Critical Server Healthy Client Secure Wireless Services
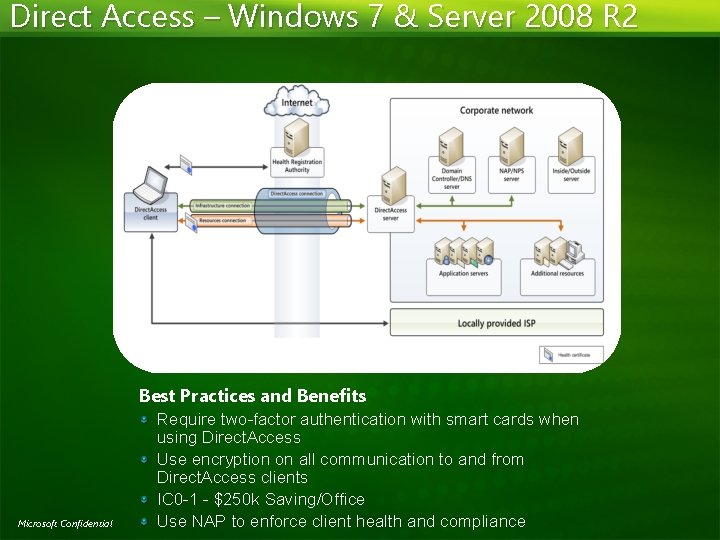
Direct Access – Windows 7 & Server 2008 R 2 Best Practices and Benefits Microsoft Confidential Require two-factor authentication with smart cards when using Direct. Access Use encryption on all communication to and from Direct. Access clients IC 0 -1 - $250 k Saving/Office Use NAP to enforce client health and compliance
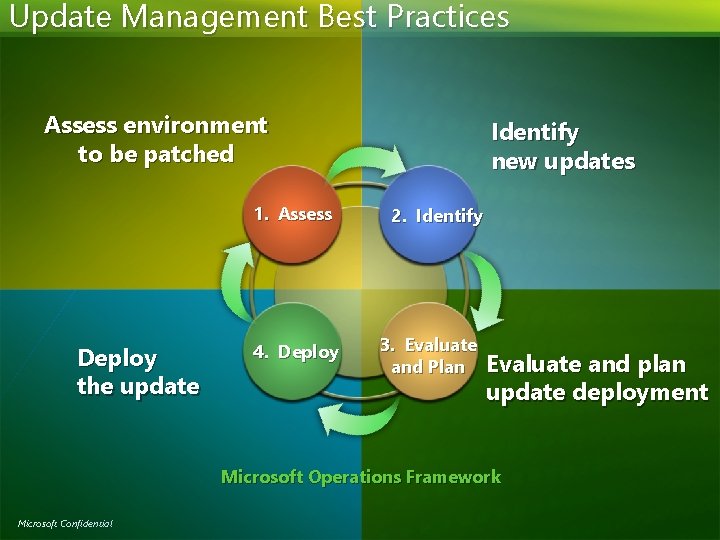
Update Management Best Practices Assess environment to be patched 1. Assess Deploy the update 4. Deploy Identify new updates 2. Identify 3. Evaluate and Plan Evaluate and plan update deployment Microsoft Operations Framework Microsoft Confidential
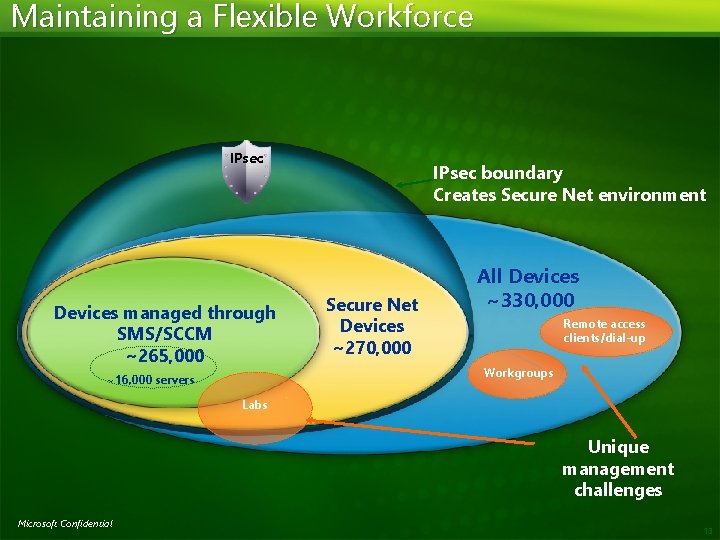
Maintaining a Flexible Workforce IPsec Devices managed through SMS/SCCM ~265, 000 ~16, 000 servers IPsec boundary Creates Secure Net environment Secure Net Devices ~270, 000 All Devices ~330, 000 Remote access clients/dial-up Workgroups Labs Unique management challenges Microsoft Confidential 13
© 2008 Microsoft Corporation. All rights reserved. Microsoft, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U. S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION. Microsoft Confidential
- Slides: 14