EMC Documentum Trusted Content Services Copyright 2008 EMC

- Slides: 9
EMC Documentum Trusted Content Services © Copyright 2008 EMC Corporation. All rights reserved. 1

EMC Documentum Trusted Content Services EMC Documentum offers unparalleled protection for the most security-conscious organizations. Trusted Content Services extends the already robust security features of the content server with enhanced access controls and encryption. Risk Minimization Information security breaches exposing personal data, classified documents, credit card information, and financial documents can cost a company millions of dollars. Regulation Compliance Increased regulation around the capture, storage, and retention of information has increased the demands on IT departments to ensure companies are in compliance. © Copyright 2008 EMC Corporation. All rights reserved. 2
EMC Documentum Trusted Content Services Encrypted File Stores Documentum products encrypt all data traffic. With Documentum Trusted Content Services (TCS), the content files can be encrypted as well. Digital Shredding Trusted Content Services’ digital shredding irrevocably destroys content at an operating system level by overwriting the data on the storage device. Logic-Based and Dynamic Access Controls The additional access controls in TCS give organizations the ability to define entitlements at a more granular level. Electronic Signatures Documentum Trusted Content Services provides the capability to sign documents electronically. © Copyright 2008 EMC Corporation. All rights reserved. 3
Data Encryption: Content and Communications Encrypted File Stores Documentum products encrypt all data traffic. With Documentum Trusted Content Services (TCS), the content files can be encrypted as well. Encryption of content files – – Algorithm used = 3 DES-CBC, Key length = 192 -bit (168 -bit effective) Selective by file store Full-text search still enabled Accessed by users and applications as if unencrypted Benefits – – Ensures content security even if OS security is compromised Protects against “rogue” administrators Secure backups Secure storage media disposal © Copyright 2008 EMC Corporation. All rights reserved. 4
Digital Shredding Trusted Content Services’ digital shredding irrevocably destroys content at an operating system level by overwriting the data on the storage device. Permanently destroys file data as a result of issuing OS delete/unlink command Shreds content on both file systems and content addressed storage (EMC Centera) Supports record management applications Number of overwrites is configurable (default is 3 X) © Copyright 2008 EMC Corporation. All rights reserved. 5
Logic-Based and Dynamic Access Controls The additional access controls in TCS give organizations the ability to define entitlements at a more granular level. Dynamic access based on variable parameters such as time, geographic location, and login connection Multi-dimension groupings – “Top Secret” AND “U. S. Citizens” – “In U. S. ” OR “in Japan” Configurable default to highest or lowest access designation RET T © Copyright 2008 EMC Corporation. All rights reserved. EC OP S 6
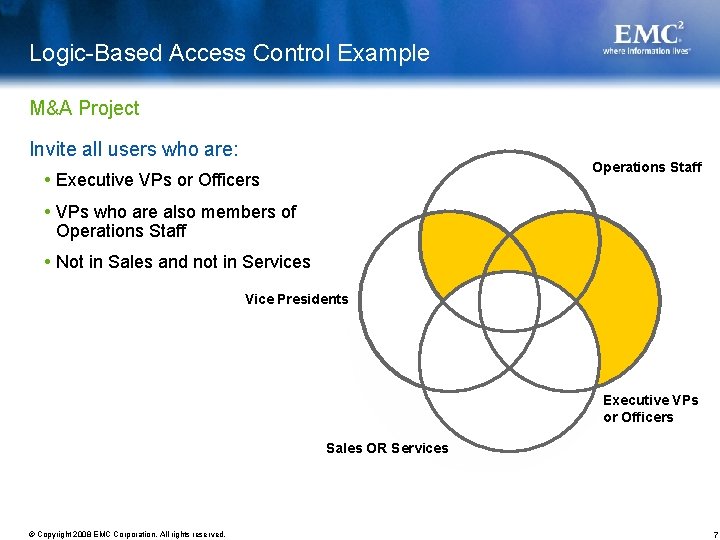
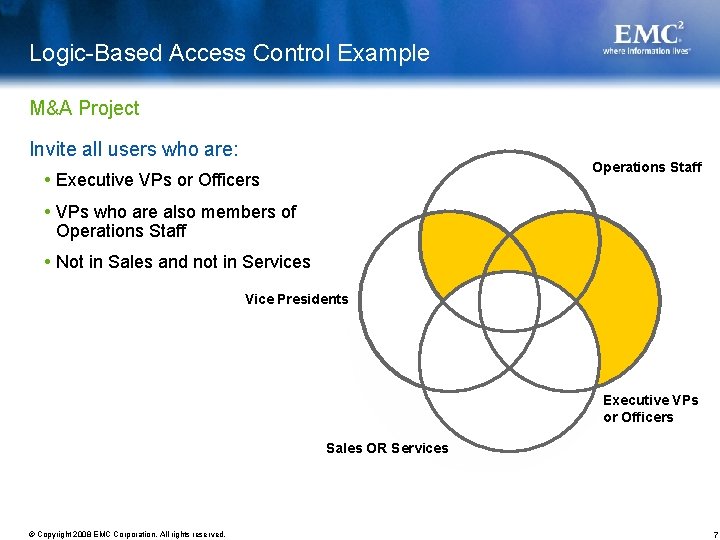
Logic-Based Access Control Example M&A Project Invite all users who are: Operations Staff Executive VPs or Officers VPs who are also members of Operations Staff Not in Sales and not in Services Vice Presidents Executive VPs or Officers Sales OR Services © Copyright 2008 EMC Corporation. All rights reserved. 7
Electronic Signatures Documentum Trusted Content Services provides the capability to sign documents electronically. Approval signatures securely linked to document Modification attempts invalidate signature Display signature information when viewed: – Full name – The date and time of the signing – The justification for the signature Define valid signatories for document types Compliant with regulatory requirements such as FDA’s 21 CFR Part 11 © Copyright 2008 EMC Corporation. All rights reserved. 8