Email Hacking dibyajit dashPIET ORISSA what exactly HACKING
Email Hacking dibyajit dash@PIET, ORISSA
what exactly HACKING is ? ->Hacking is a process to bypass the security mechanisms of an information system or network. These are two types: Local hacking is done in local area where we physical access , like through printer etc. Remote hacking: Remote hacking is done remotely by taking advantages of the vulnerability of the target system. dibyajit dash@PIET, ORISSA

Internet Protocol Stack Application Layer SMTP HTTP Bit. Torrent RTSP Transport Layer IP Network Layer Link Layer Physical Layer UDP TCP Ethernet Cables dibyajit dash@PIET, ORISSA 802. 11(b, a, g) / Wi. Fi Fiber Optics Radio
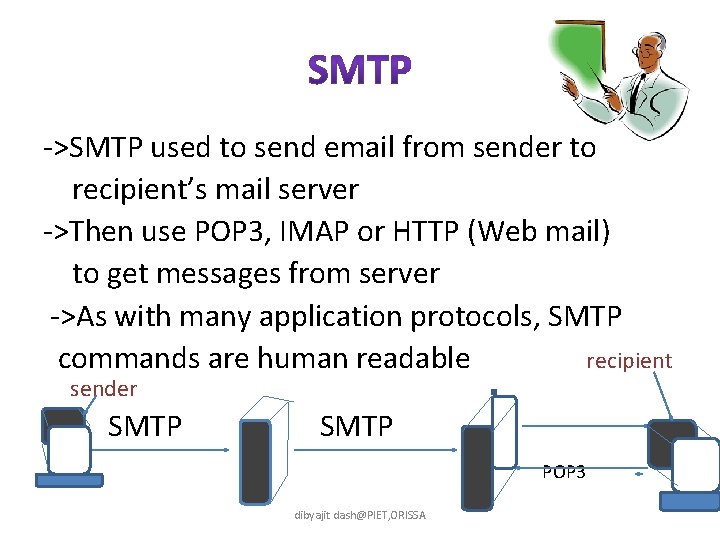
->SMTP used to send email from sender to recipient’s mail server ->Then use POP 3, IMAP or HTTP (Web mail) to get messages from server ->As with many application protocols, SMTP commands are human readable recipient sender SMTP POP 3 dibyajit dash@PIET, ORISSA
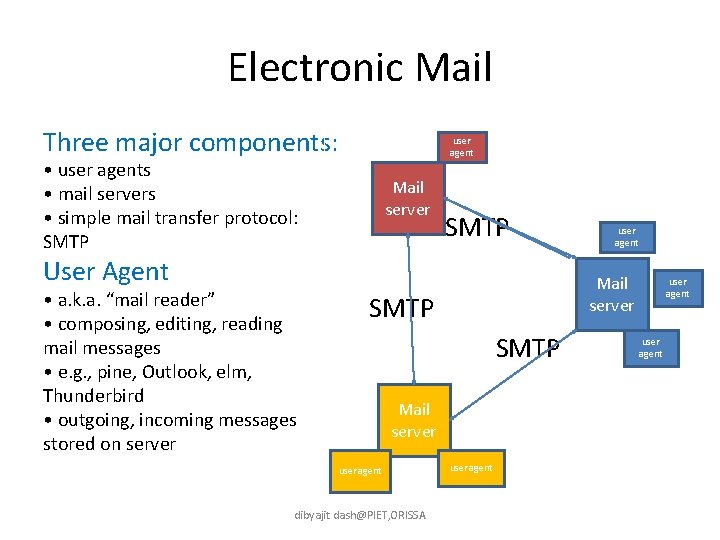
Electronic Mail Three major components: user agent • user agents • mail servers • simple mail transfer protocol: SMTP Mail server SMTP User Agent • a. k. a. “mail reader” • composing, editing, reading mail messages • e. g. , pine, Outlook, elm, Thunderbird • outgoing, incoming messages stored on server Mail server SMTP Mail server user agent dibyajit dash@PIET, ORISSA user agent
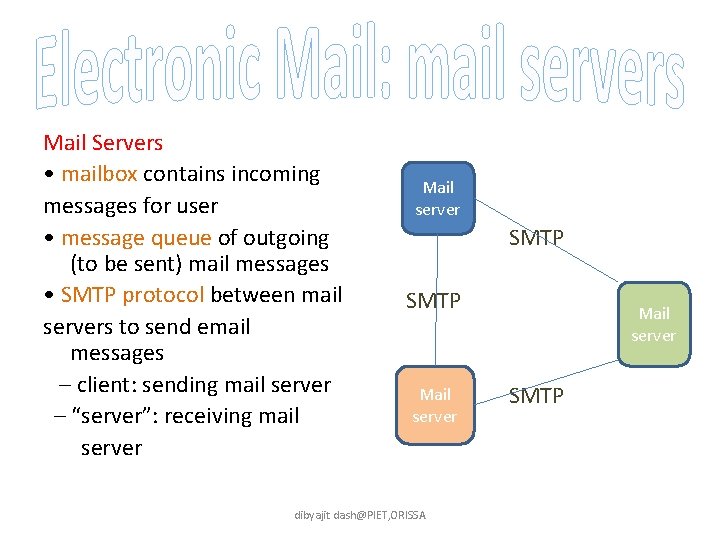
Mail Servers • mailbox contains incoming messages for user • message queue of outgoing (to be sent) mail messages • SMTP protocol between mail servers to send email messages – client: sending mail server – “server”: receiving mail server Mail server SMTP Mail server dibyajit dash@PIET, ORISSA Mail server SMTP
Sending Server to Receiving Server • three phases of transfer – handshaking (greeting) – transfer of messages – closure • command/response interaction – commands: ASCII text: HELO, MAIL, RCPT, DATA, QUIT, etc. – response: status code and phrase • messages must be in 7 -bit ASCII dibyajit dash@PIET, ORISSA
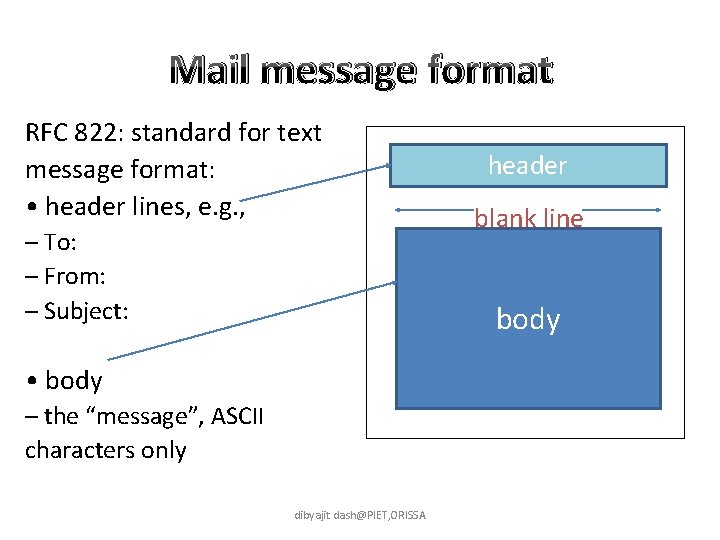
Mail message format RFC 822: standard for text message format: • header lines, e. g. , – To: – From: – Subject: header blank line body • body – the “message”, ASCII characters only dibyajit dash@PIET, ORISSA
MORE MAIL ACCESS PROTOCOLS • SMTP: delivery/storage to receiver’s server • Mail access protocol: retrieval from server – POP: Post Office Protocol [RFC 1939] • authorization (agent <-->server) and download – IMAP: Internet Mail Access Protocol [RFC 1730] • more features (more complex) • manipulation of stored messages on server – HTTP: Hotmail , Yahoo! Mail, etc. dibyajit dash@PIET, ORISSA
What is Security? Security is the protection of assets. The three main aspects are: • prevention • detection • re-action dibyajit dash@PIET, ORISSA
Some differences between traditional security and information security • Information can be stolen - but you still have it • Confidential information may be copied and sold - but theft might not be detected • The criminals may be on the other side of the world dibyajit dash@PIET, ORISSA
• Computer Security deals with the prevention and detection of unauthorised actions by users of a computer system. dibyajit dash@PIET, ORISSA
There is no single definition of security What features should a computer security system provide? dibyajit dash@PIET, ORISSA
Confidentiality • The prevention of unauthorized disclosure of information. • Confidentiality is keeping information secret or private. • Confidentiality might be important for military, business or personal reasons. dibyajit dash@PIET, ORISSA
Security systems • A security system is not just a computer package. It also requires security conscious personnel who respect the procedures and their role in the system. • Conversely, a good security system should not rely on personnel having security expertise. dibyajit dash@PIET, ORISSA
Risk Analysis • The disadvantages of a security system are that they are time-consuming, costly, and impede management and smooth running of the organization. • Risk analysis is the study of the cost of a particular system against the benefits of the system. dibyajit dash@PIET, ORISSA
There a number of design considerations: • Does the system focus on the data, operations or the users of the system? • What level should the security system operate from? Should it be at the level of hardware, operating system or applications package? • Should it be simple or sophisticated? • In a distributed system, should the security be centralised or spread? • How do you secure the levels below the level of the security system? dibyajit dash@PIET, ORISSA

By now you should have some idea about • Why we need computer security (prevention, detection and re-action) • What a computer security system does (confidentiality, integrity, availability, nonrepudiation, authentication, access control, accountability) • What computer security exerts do (design, implement and evaluate security systems) dibyajit dash@PIET, ORISSA

Thank You… dibyajit dash@PIET, ORISSA
Dibyajit Dash dibyajit dash@PIET, ORISSA
- Slides: 20