Email Basics Encryption Passwords and SPAM Presenter Melissa
E-mail Basics, Encryption, Passwords, and SPAM Presenter: Melissa Dark CERIAS, Purdue University
Contact Information: Judy Lewandowski K-12 Outreach Coordinator CERIAS, Purdue University http: //www. cerias. purdue. edu/K-12 judy. L@cerias. purdue. edu 765. 496. 6762
Today’s Overview: • E-mail Basics • Encryption • Passwords • SPAM
E-mail Basics n E-mail is similar to a postcard. n E-mail is *not* secure—nor is it private. n Encryption is the only way to help in preventing others from reading your e -mail.
Email Security Fundamentals n Question n Use Unsolicited Documents. attachments only when necessary. n Question ALL executable programs received via email. n Notify n Pay the sender of infected emails! attention to file extensions. . .
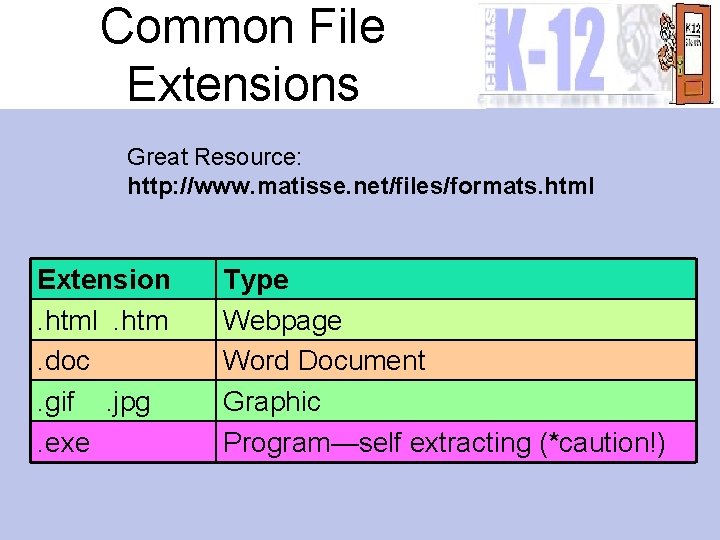
Common File Extensions Great Resource: http: //www. matisse. net/files/formats. html Extension. html. htm. doc. gif. jpg. exe Type Webpage Word Document Graphic Program—self extracting (*caution!)
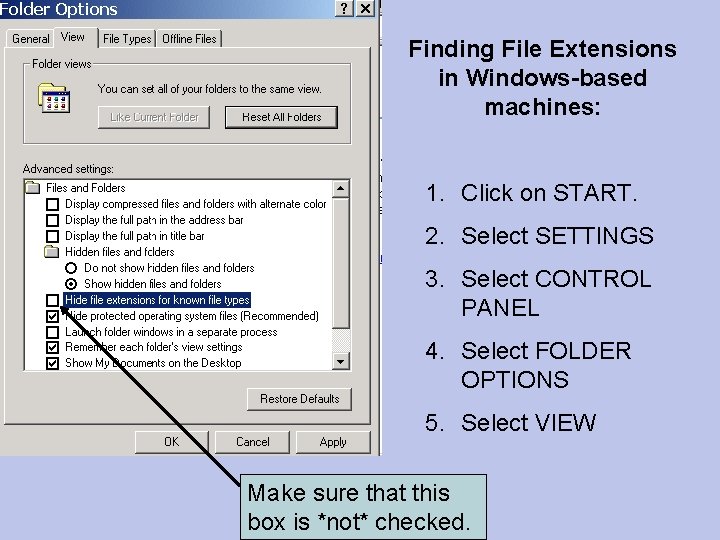
Finding File Extensions in Windows-based machines: 1. Click on START. 2. Select SETTINGS 3. Select CONTROL PANEL 4. Select FOLDER OPTIONS 5. Select VIEW Make sure that this box is *not* checked.
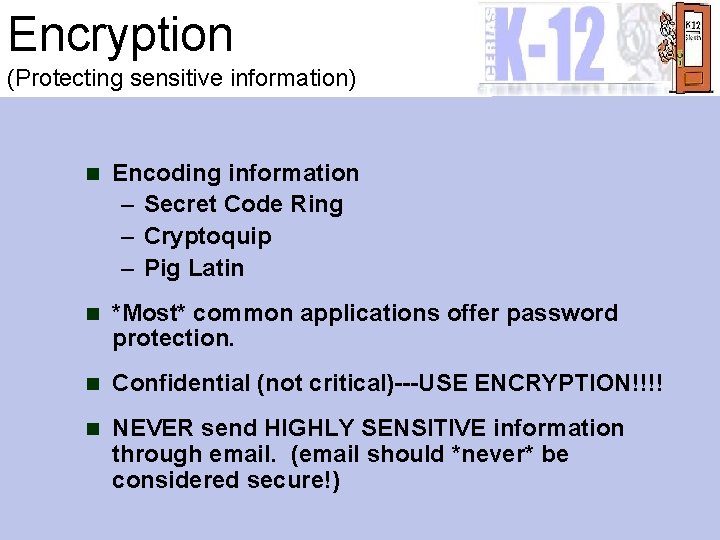
Encryption (Protecting sensitive information) n Encoding information – Secret Code Ring – Cryptoquip – Pig Latin n *Most* common applications offer password protection. n Confidential (not critical)---USE ENCRYPTION!!!! n NEVER send HIGHLY SENSITIVE information through email. (email should *never* be considered secure!)
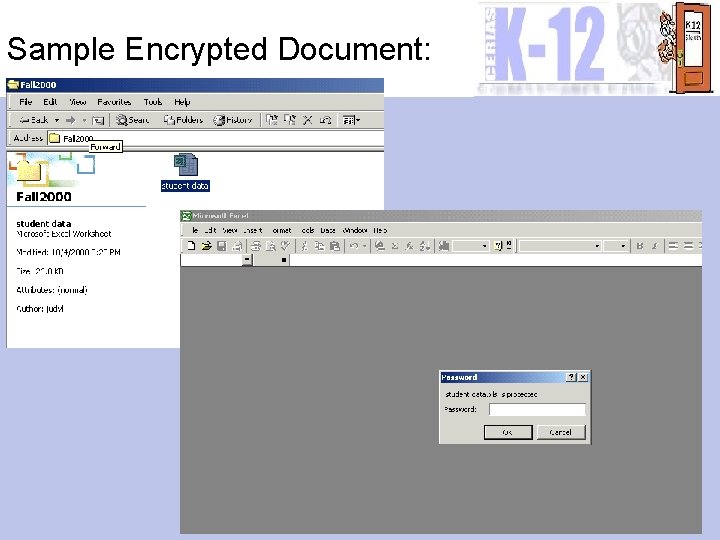
Sample Encrypted Document:
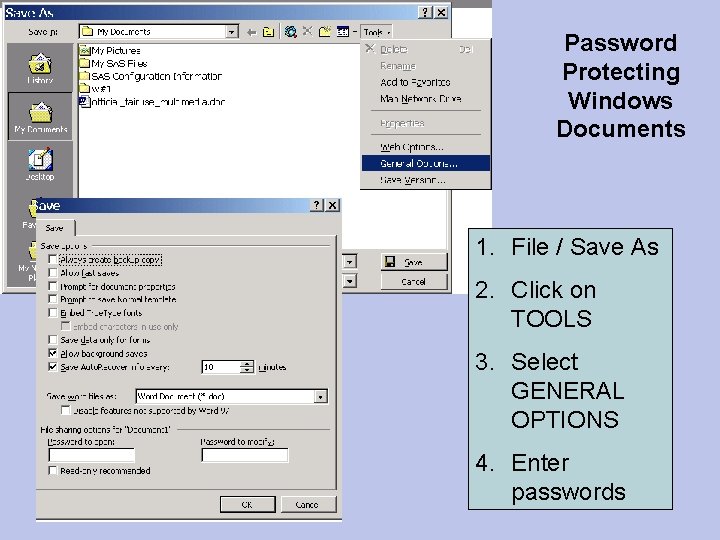
Password Protecting Windows Documents 1. File / Save As 2. Click on TOOLS 3. Select GENERAL OPTIONS 4. Enter passwords
Encryption Practice. . . n Open Microsoft Word. n Type in a sentence. n Follow the directions---password protect the document. n Close the document. n Re-open it using your password.
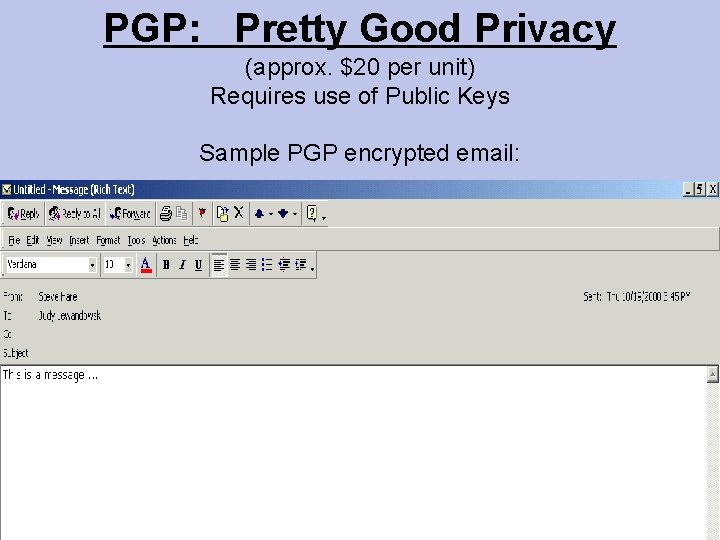
PGP: Pretty Good Privacy (approx. $20 per unit) Requires use of Public Keys Sample PGP encrypted email:
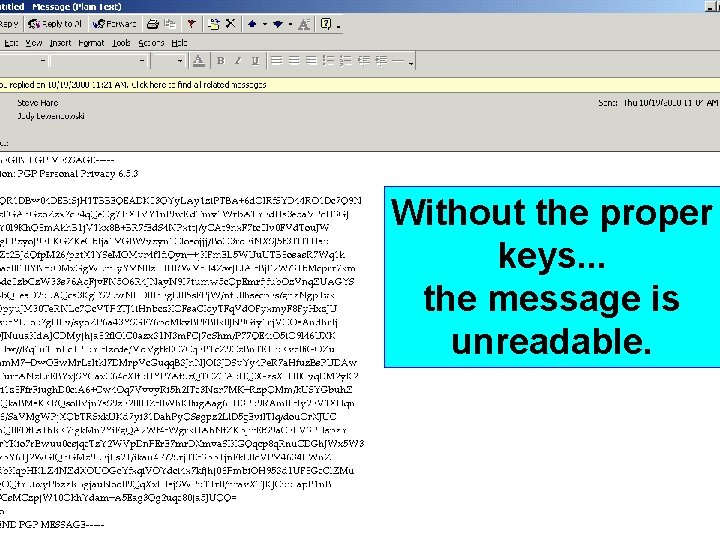
Without the proper keys. . . the message is unreadable.
Key Component to Encryption:
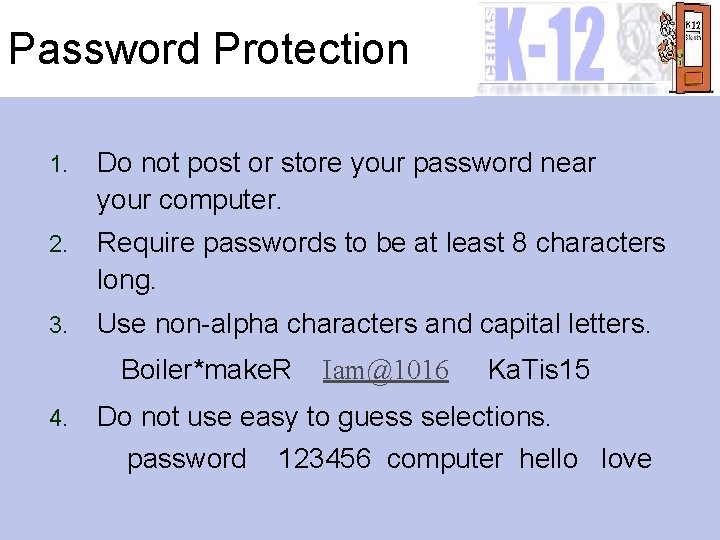
Password Protection 1. Do not post or store your password near your computer. 2. Require passwords to be at least 8 characters long. 3. Use non-alpha characters and capital letters. Boiler*make. R 4. Iam@1016 Ka. Tis 15 Do not use easy to guess selections. password 123456 computer hello love
Passwords Continued… 5. Use non-personal selections. Avoid: name, spouse’s name, kids, ss# 6. Maintain zero tolerance for password sharing. 7. Avoid typing your password when someone is watching. Urge users to change passwords. (2 -3 weeks!) 9. Always remember to log out! 10. Constantly reinforce the importance of password security. 8.
Password Practice: Write a “smart” password for the following fictional teacher. Be sure to follow all of the recommendations! Samuel W. Miller Greentown High School Social Studies Teacher Harvard Graduate Likes to play golf Has four children 1 wife named Betty Enjoys woodworking
BREAK!!!!!! Please be back at. . .
SPAM n Internet “Junk” Mail – Commercial – Personal Unsolicited email—usually sent to many people n According to the Gartner Group, a research firm, about 90% of email users receive spam. n Never Respond to Spam. n Do not sign up for “Spam Removal” lists. n – Sincere v. Spam Collectors
Types of Spam n Chain Letters: – A message that urges readers to pass the letter on in order to receive a reward. n Hoaxes: – Chain letter that is based upon a fictitious scenario or circumstance. n Urban Legends: – Email messages providing “safety” messages or warnings.
The Pros and Cons of Spam A Brainstorming Activity….
Why Should I be Concerned about Spam? n Costs Money. – Recipient of the advertisement pays for the connection time, disk space, bandwidth, etc. n Lost Productivity. – Time, Time n Clogged Email. – May be prevent receipt of important messages. n Discourages Internet Use. – May discourage others from seeing the benefits of the WWW.
Raising SPAM Awareness Activity Check the legitimacy of a message BEFORE they send it on. n Directions: Each group has been given a keyword. Go to the Urban Legends site (http: //www. urbanlegends. com) search engine and search for SPAM dealing with your selection. n n Skim through the choices and pick the best one to share with the group! Explain why it is a hoax.
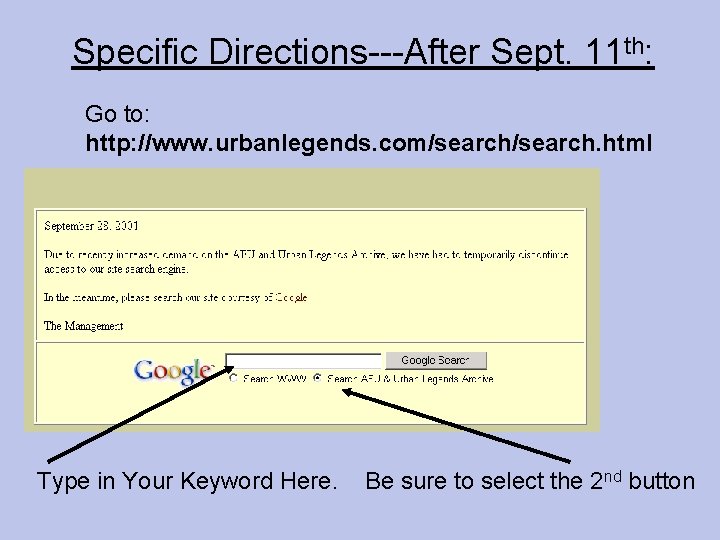
Specific Directions---After Sept. 11 th: Go to: http: //www. urbanlegends. com/search. html Type in Your Keyword Here. Be sure to select the 2 nd button
SPAM Awareness Activity: Debriefing n n n Coke Gap ATM Needles Intel Taco Bell n n n Pets Spiders Perfume Cracker 809 Disney

Resources to Find the Truth About Spam: n http: //www. urbanlegends. com n http: //www. urbanmyths. com n http: //www. earthlink. net/internet/security/spam n http: //www. mcs. com/~jcr/junkmail. html n http: //www. junkbusters. com
Ways to Reduce Your Daily Intake of Spam n Use a “dummy” account for online promotions, games, etc. n Request that your information be removed from Internet “white pages”. n Be sure to HIDE your information when joining a listserv or mailing list. n Cut and Paste funny stories, poems, etc. – Encourage others to do the same!
Virus Protection & Firewalls A Few Brief Comments. . n Update Anti-Virus Frequently!!! n Use a Firewall: – http: //www. zonealarm. com • • FREE VERY Effective Easy to Use Blocks Incoming/Outgoing
Questions? ? ?
- Slides: 31