Elliptic Curve Cryptosystem And Its Applications Mostly by
Elliptic Curve Cryptosystem And Its Applications Mostly by 游菀瑄
Outline n Elliptic Curve n n n Basic definition Operations:addition & scalar Elliptic Curve Cryptosystem n Security considerations n ECC n n n vs. RSA comparison Implementation considerations Applications Conclusions
Some messages: How secure are RSA and Diffie-Hellman? There are known subexponential (but superpolynomial) algorithms for breaking RSA and Diffie-Hellman based on modular arithmetic. Elliptic Curve Cryptography(ECC) is important because the mathematicians do not (yet? ) have subexponential algorithms for breaking it. Therefore, it is believed to be secure with much smaller key sizes, which is important for performance. ECC is a candidate replacement for public key cryptographic schemes like RSA, Diffie-Hellman, El. Gamal, DSS, etc. For some of these cryptographic schemes, one can replace modular multiplication by elliptic curve multiplication directly, resulting in algorithms referred to as ECC Diffie-Hellman, ECC El. Gamal, etc.
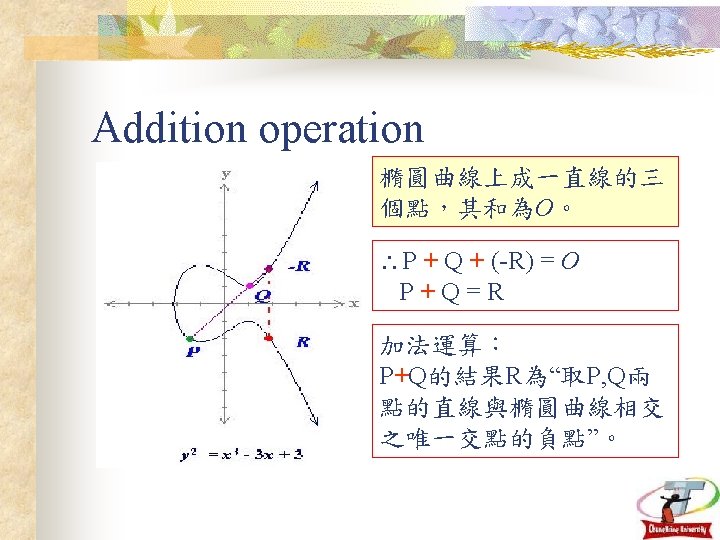
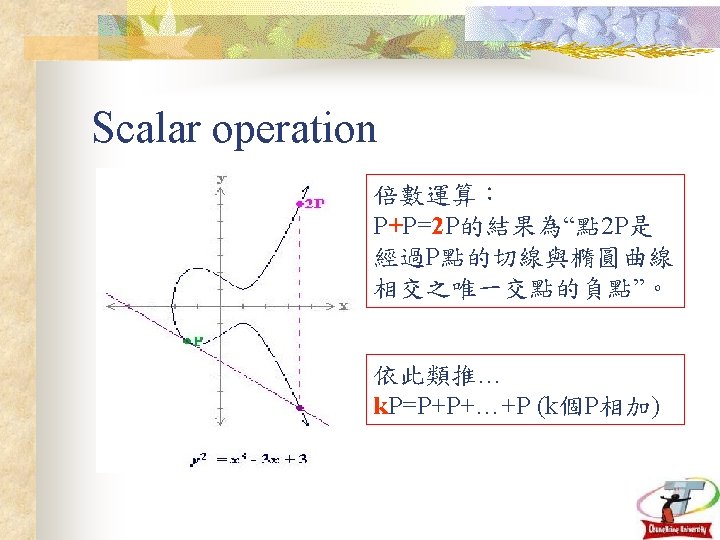
An elliptic curve is a set of points on the coordinate plane satisfying an equation of the form y 2 = x 3 + ax + b. In order to use elliptic curves for, say , Diffie-Hellman, there needs to be some mathematical operation on two points in the set that will always produce a point also in the set. Let’s call that operation multiplication, although in ECC it will not look like the multiplication you are used to. And the operation has to be associative, so that you can use the repeated squaring trick to raise a number to a large power in time linear with the length of the exponent. In other words, to “exponentiate” a point by 128, you should be able to “multiply” the point by itself, then multiply the result by itself, again and again, etc. Since “multiplication” is associative, it will be true that (gx)y = gxy = (gy)x. And it is also important that doing discrete logs is hard.
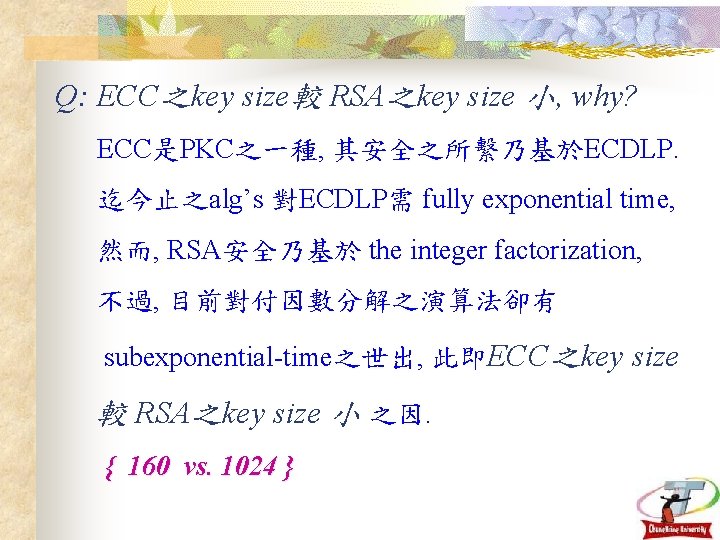
Q: ECC之key size較 RSA之key size 小, why? ECC是PKC之一種, 其安全之所繫乃基於ECDLP. 迄今止之alg’s 對ECDLP需 fully exponential time, 然而, RSA安全乃基於 the integer factorization, 不過, 目前對付因數分解之演算法卻有 subexponential-time之世出, 此即ECC之key size 較 RSA之key size 小 之因. { 160 vs. 1024 }
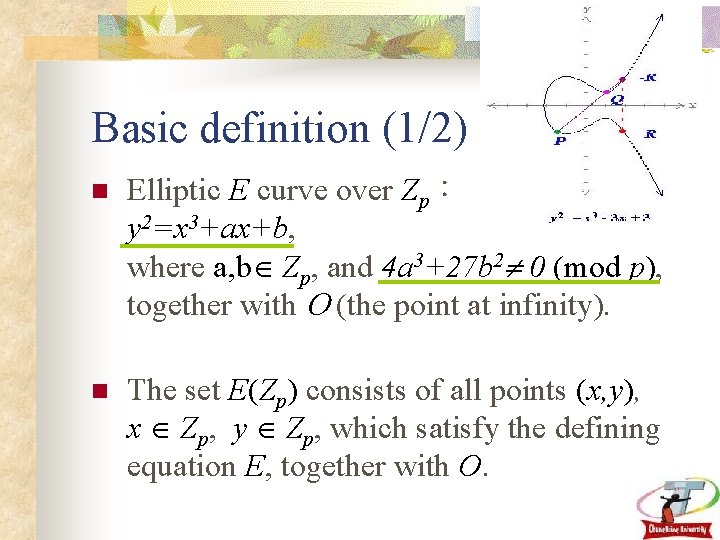
Basic definition (1/2) n Elliptic E curve over Zp: y 2=x 3+ax+b, where a, b Zp, and 4 a 3+27 b 2 0 (mod p), together with (the point at infinity). n The set E(Zp) consists of all points (x, y), x Zp, y Zp, which satisfy the defining equation E, together with O.
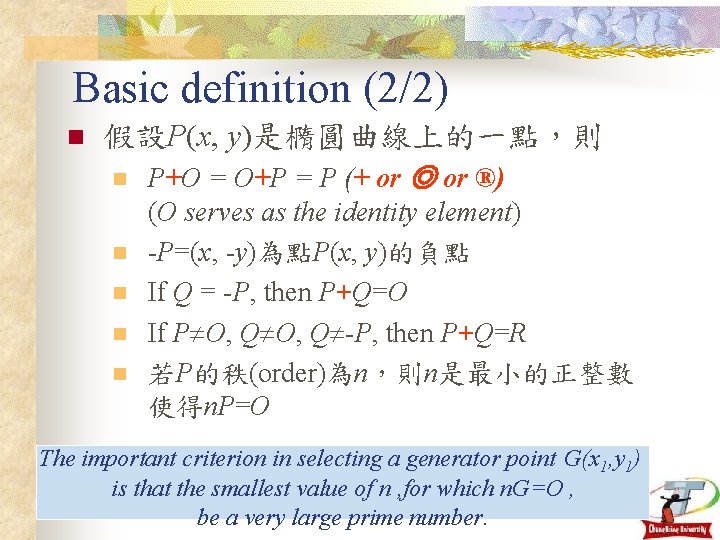
Basic definition (2/2) n 假設P(x, y)是橢圓曲線上的一點,則 n n n P+O = O+P = P (+ or ◎ or ®) (O serves as the identity element) -P=(x, -y)為點P(x, y)的負點 If Q = -P, then P+Q=O If P O, Q -P, then P+Q=R 若P的秩(order)為n,則n是最小的正整數 使得n. P=O The important criterion in selecting a generator point G(x 1, y 1) is that the smallest value of n , for which n. G=O , be a very large prime number.
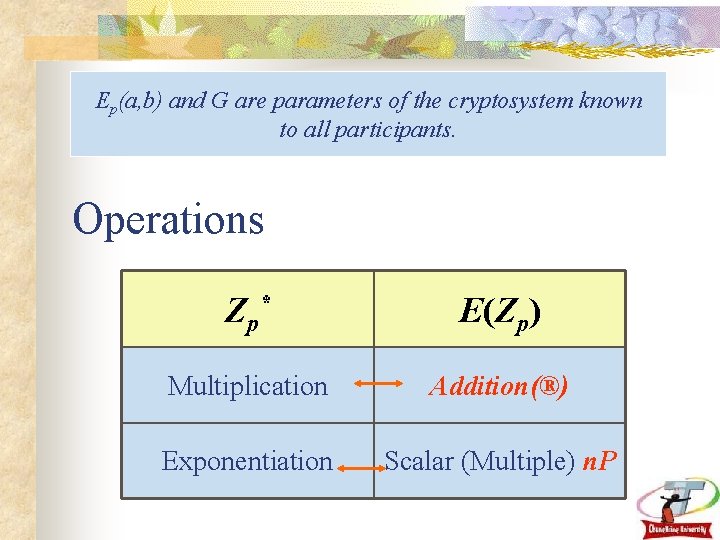
Ep(a, b) and G are parameters of the cryptosystem known to all participants. Operations Z p* E(Zp) Multiplication Addition(®) Exponentiation Scalar (Multiple) n. P
Elliptic curves are interesting because they provide a way of constructing “elements” and “rules of combining” that produce groups. These groups have enough familiar properties to build cryptographic algorithms, but they don’t have certain properties that may facilitate cryptanalysis. For example, there is no good notion of “smooth. ” That is, there is no set of small elements in terms of which a random element has a good chance of being expressed by a simple algorithm. Hence, index calculus discrete logarithm algorithm do not work. Elliptic curves over the finite field GF(2 n) are particularly interesting. The arithmetic processors for the underlying field are easy to construct and are relatively simple to implement for n in the range of 130 to 200. These systems have the potential to provide small and low-cost public-key cryptosystems. Many public-key algorithms, like Diffie-Hellman, El. Gamal, and Schnorr, can be implemented in elliptic curves over finite fields.
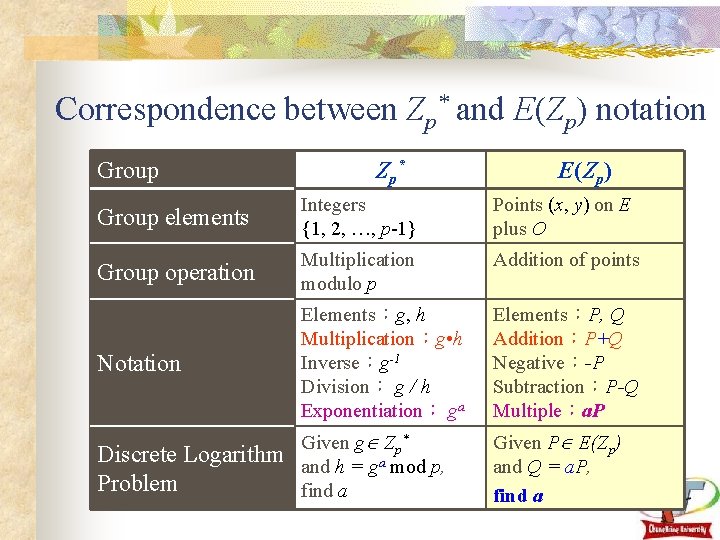
Correspondence between Zp* and E(Zp) notation Group Zp* E(Zp) Group elements Integers {1, 2, …, p-1} Points (x, y) on E plus O Group operation Multiplication modulo p Addition of points Notation Elements:g, h Multiplication:g • h Inverse:g-1 Division: g / h Exponentiation: ga Elements:P, Q Addition:P+Q Negative:-P Subtraction:P-Q Multiple:a. P Discrete Logarithm Problem Given g Zp* and h = ga mod p, find a Given P E(Zp) and Q = a. P, find a
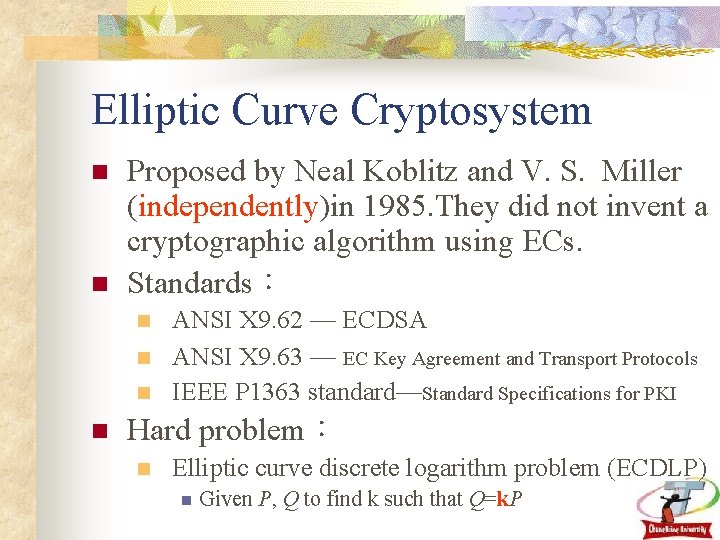
Elliptic Curve Cryptosystem n n Proposed by Neal Koblitz and V. S. Miller (independently)in 1985. They did not invent a cryptographic algorithm using ECs. Standards: n n ANSI X 9. 62 — ECDSA ANSI X 9. 63 — EC Key Agreement and Transport Protocols IEEE P 1363 standard—Standard Specifications for PKI Hard problem: n Elliptic curve discrete logarithm problem (ECDLP) n Given P, Q to find k such that Q=k. P
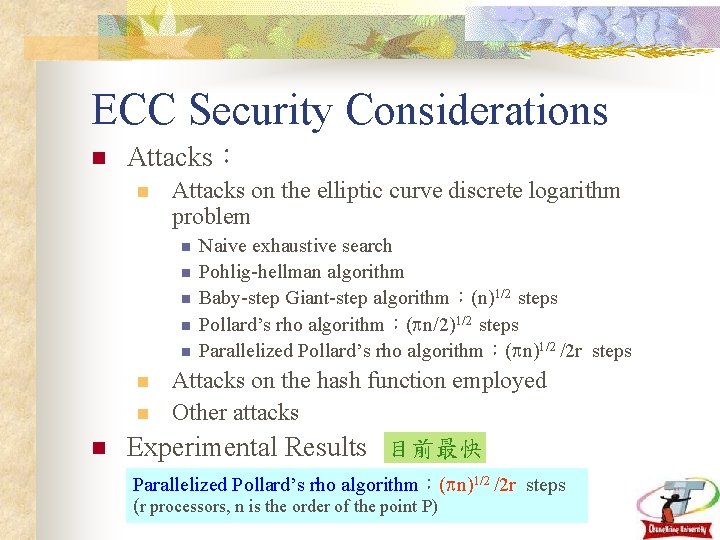
ECC Security Considerations n Attacks: n Attacks on the elliptic curve discrete logarithm problem n n n Naive exhaustive search Pohlig-hellman algorithm Baby-step Giant-step algorithm:(n)1/2 steps Pollard’s rho algorithm:( n/2)1/2 steps Parallelized Pollard’s rho algorithm:( n)1/2 /2 r steps Attacks on the hash function employed n Other attacks n Experimental Results 目前最快 n Parallelized Pollard’s rho algorithm:( n)1/2 /2 r steps (r processors, n is the order of the point P)
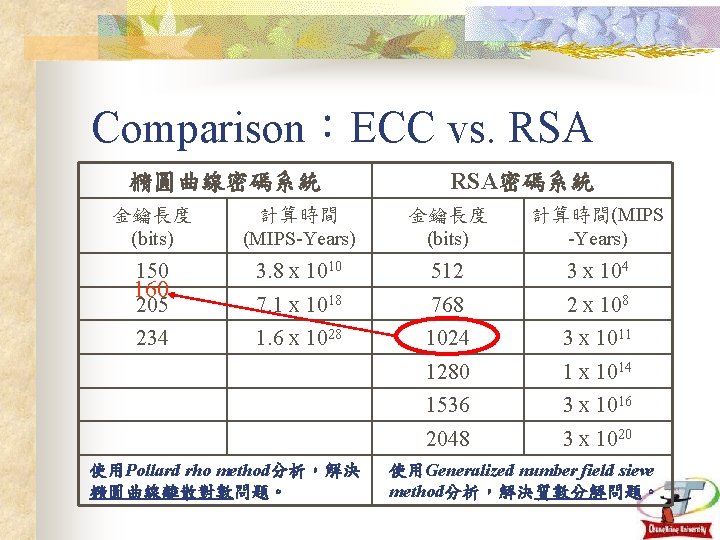
Comparison:ECC vs. RSA 橢圓曲線密碼系統 RSA密碼系統 金鑰長度 (bits) 計算時間 (MIPS-Years) 金鑰長度 (bits) 計算時間(MIPS -Years) 150 3. 8 x 1010 512 3 x 104 205 7. 1 x 1018 768 2 x 108 234 1. 6 x 1028 1024 3 x 1011 1280 1 x 1014 1536 3 x 1016 2048 3 x 1020 160 使用Pollard rho method分析,解決 橢圓曲線離散對數問題。 使用Generalized number field sieve method分析,解決質數分解問題。
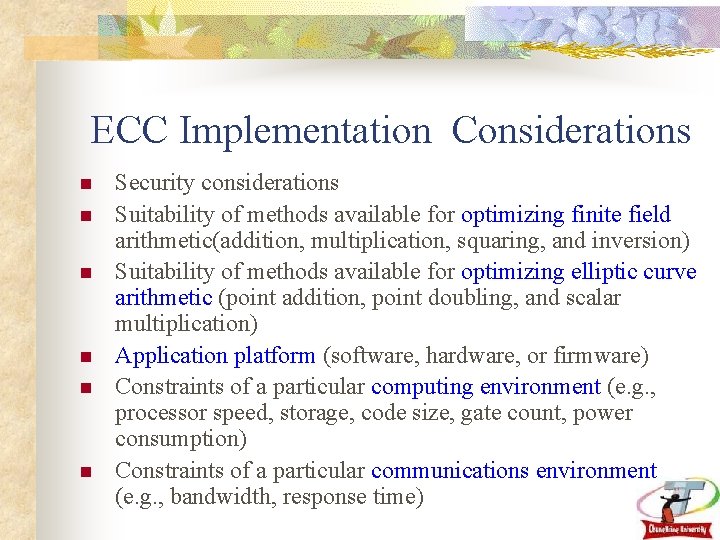
ECC Implementation Considerations n n n Security considerations Suitability of methods available for optimizing finite field arithmetic(addition, multiplication, squaring, and inversion) Suitability of methods available for optimizing elliptic curve arithmetic (point addition, point doubling, and scalar multiplication) Application platform (software, hardware, or firmware) Constraints of a particular computing environment (e. g. , processor speed, storage, code size, gate count, power consumption) Constraints of a particular communications environment (e. g. , bandwidth, response time)
Applications n n n Key Exchange (analogous to DH) Encryption & Decryption (analogous to El. Gamal) Digital Signature (analogous to DSA) Authentication ……
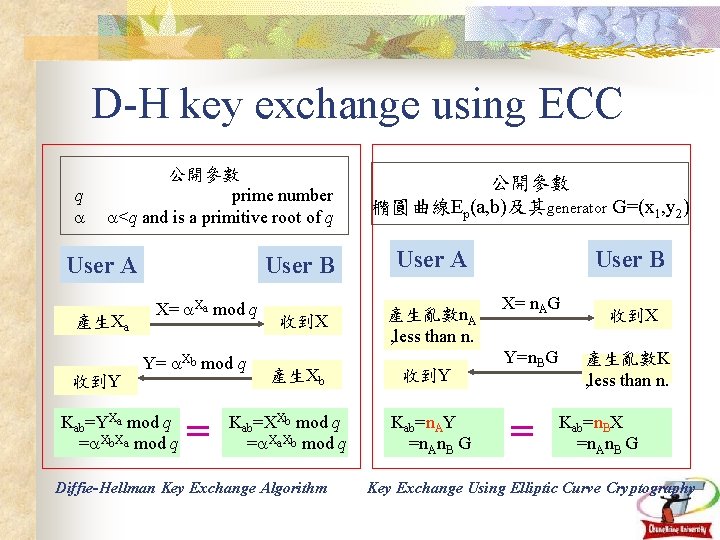
D-H key exchange using ECC q 公開參數 prime number <q and is a primitive root of q User A 產生Xa 收到Y X= Xa mod q Y= Xb mod q Kab=YXa mod q = Xb. Xa mod q = 公開參數 橢圓曲線Ep(a, b)及其generator G=(x 1, y 2) User B User A 收到X 產生亂數n. A , less than n. 產生Xb Kab=XXb mod q = Xa. Xb mod q Diffie-Hellman Key Exchange Algorithm 收到Y Kab=n. AY =n. An. B G User B X= n. AG Y=n. BG = 收到X 產生亂數K , less than n. Kab=n. BX =n. An. B G Key Exchange Using Elliptic Curve Cryptography
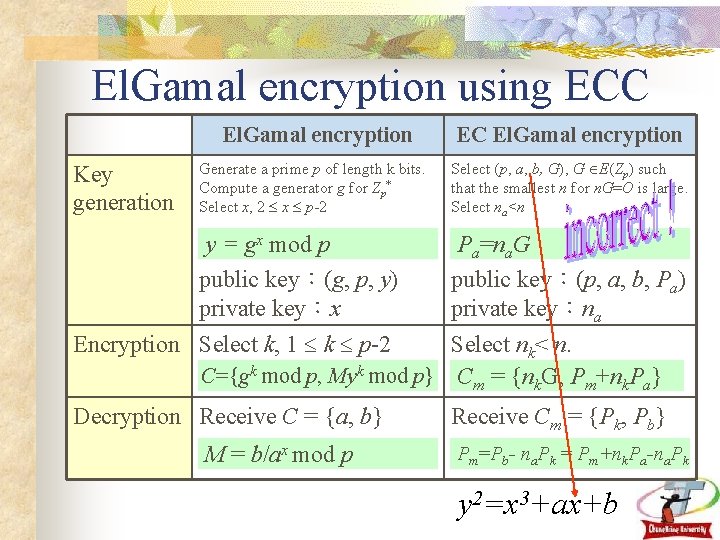
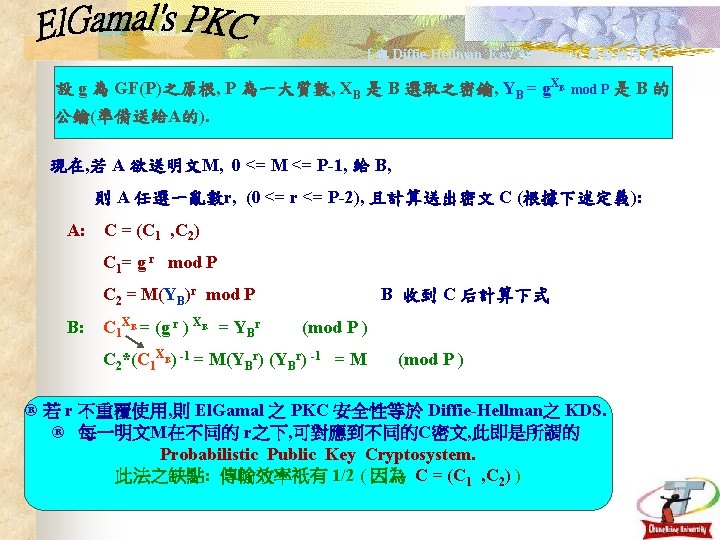
El. Gamal encryption using ECC El. Gamal encryption Key generation EC El. Gamal encryption Generate a prime p of length k bits. Compute a generator g for Zp* Select x, 2 x p-2 Select (p, a, b, G), G E(Zp) such that the smallest n for n. G=O is large. Select na<n y = gx mod p public key:(g, p, y) private key:x Pa=na. G public key:(p, a, b, Pa) private key:na Encryption Select k, 1 k p-2 Select nk< n. C={gk mod p, Myk mod p} Cm = {nk. G, Pm+nk. Pa} Decryption Receive C = {a, b} M = b/ax mod p Receive Cm = {Pk, Pb} Pm=Pb- na. Pk = Pm+nk. Pa-na. Pk y 2=x 3+ax+b
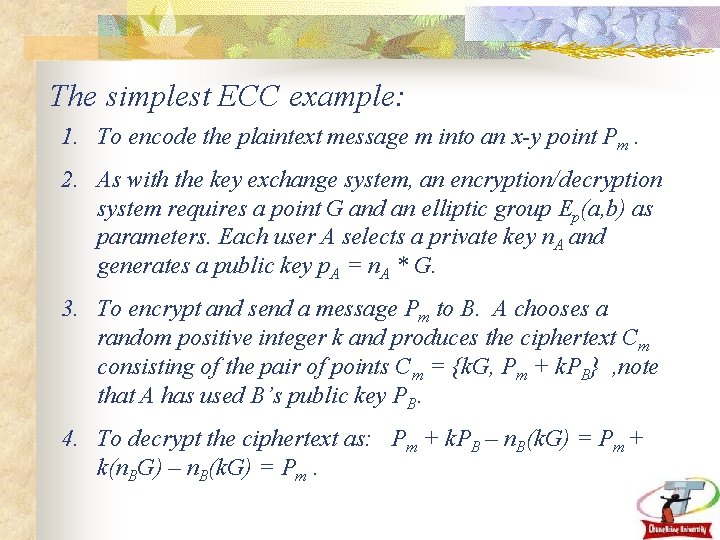
The simplest ECC example: 1. To encode the plaintext message m into an x-y point Pm. 2. As with the key exchange system, an encryption/decryption system requires a point G and an elliptic group Ep(a, b) as parameters. Each user A selects a private key n. A and generates a public key p. A = n. A * G. 3. To encrypt and send a message Pm to B. A chooses a random positive integer k and produces the ciphertext Cm consisting of the pair of points Cm = {k. G, Pm + k. PB} , note that A has used B’s public key PB. 4. To decrypt the ciphertext as: Pm + k. PB – n. B(k. G) = Pm + k(n. BG) – n. B(k. G) = Pm.
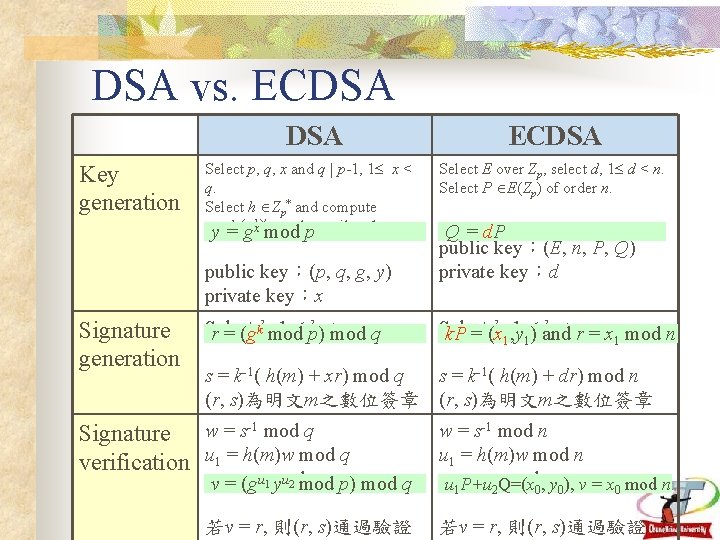
DSA vs. ECDSA Key generation Select p, q, x and q | p-1, 1 x < q. Select h Zp* and compute gy== h (p-1)/q mod pp until g 1. gx mod public key:(p, q, g, y) private key:x Signature generation ECDSA Select E over Zp, select d, 1 d < n. Select P E(Zp) of order n. Q = d. P public key:(E, n, P, Q) private key:d Select 1 p) k <mod q. q r = (gkk, mod Select k, , y 1 k < n. k. P = (x 1 1) and r = x 1 mod n s = k-1( h(m) + xr) mod q (r, s)為明文m之數位簽章 s = k-1( h(m) + dr) mod n (r, s)為明文m之數位簽章 Signature w = s-1 mod q verification u 1 = h(m)w mod q uv 2 == (g rwu 1 mod q p) mod q yu 2 mod w = s-1 mod n u 1 = h(m)w mod n uu 21 P+u = rw 2 Q=(x mod 0, ny 0), v = x 0 mod n 若v = r, 則(r, s)通過驗證
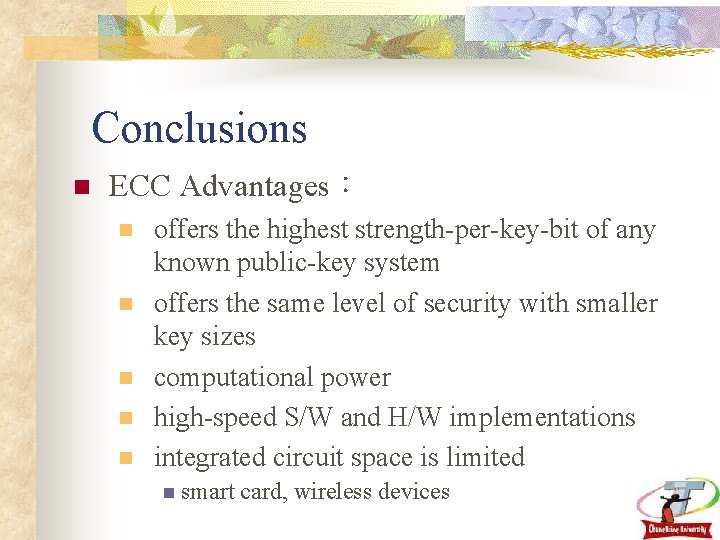
Conclusions n ECC Advantages: n n n offers the highest strength-per-key-bit of any known public-key system offers the same level of security with smaller key sizes computational power high-speed S/W and H/W implementations integrated circuit space is limited n smart card, wireless devices
References n ECC Whitepapers http: //www. certicom. com/research/weccrypt. html n Elliptic Curves and Cryptography Dr. Dobb’s Journal April 1997 n The Elliptic Curve Digital Signature Algorithm (ECDSA) http: //www. certicom. com/pdfs/whitepapers/ecdsa. pdf n ECC Tutorial http: //www. certicom. com/resources/ecc_tutorial. html n 橢圓曲線密碼系統於GSM網路上的應用 n 設計植基於自我驗證公開金鑰系統之安全線上電子拍賣機制 n 行動電子商務環境下安全機制之研究
- Slides: 24