EJB Security CSCI 5931 Web Security Kartikeya Kakarala
EJB Security CSCI 5931 Web Security Kartikeya Kakarala Young Ho Choung
Contents – Introduction – Traditional Client/Server Architecture – Multi-tier Architecture – EJB Architecture & its Roles – EJB Security model – Method Permissions – Programmatic Security – Conclusions – References
Enterprise Java Beans Introduction • Enterprise Java Beans (EJB) is a standard server side component model • The EJB architecture logically extends the Java Beans component model to support server components • An EJB is a non-visual Java Bean that runs on a server
Introduction(cont. . ) • An EJB is – – – A collection of Java classes An XML file Bundled into a single unit The Java classes must follow certain rules The Java classes must provide callback methods
Traditional Client/Server Architecture • In a traditional client/server application, the client application contains: – presentation logic(windows and control manipulation) – business logic(algorithms and business rules) – data manipulation logic(database connections and SQL Queries)
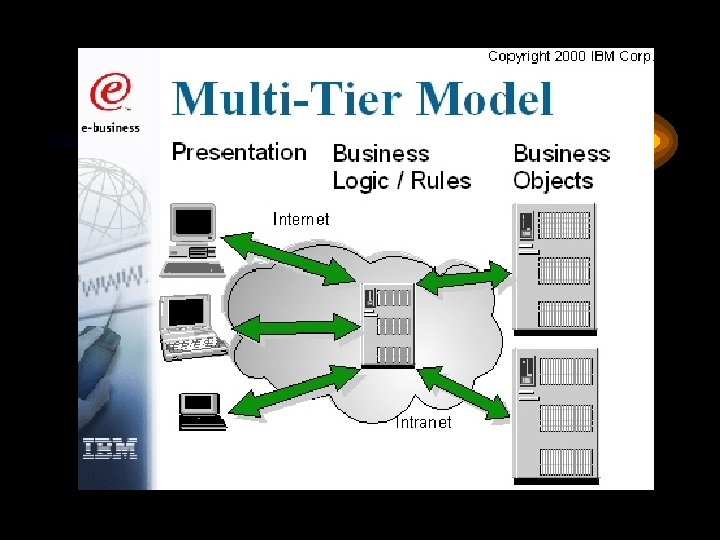
Multi-tier Architecture • Client applications contain only presentation logic – a thin client • Business logic and data access logic are partitioned into separate components and deployed onto one or more servers
EJB Architecture • EJB Architecture is gaining broad acceptance due to it’s high value benefits that address directly the needs of today's diverse server development community like – – – – Scalability Simplicity Ease of development Security Interoperability Component based computing Application Containers
EJB Architecture Roles • Various EJB Architecture roles handle EJB development and deployment. They are: – – – Bean Provider Application Assembler Deployer EJB Service Provider EJB Container Provider System Administrator
Bean Provider • The Bean Provider – Writes the individual Enterprise Java Beans. – Can be a Business entity or system encapsulated as entity or session beans. – Creates deployment descriptor.
Application Assembler • An Application Assembler – Creates a full application from individual beans – May also create JSP’s and servlets that utilize those beans. – Edits the Deployment Descriptors to fit the application.
Deployer • A Deployer – Deploys the application into a running EJB Server. – Sets up interaction between architecture as envisioned by the assembler and actual environment in which it runs.
EJB Service Provider & EJB Container Provider • The EJB Service Provider & EJB Container Provider Work together to write the EJB Server. – Figure displaying the EJB model
System Administrator • The System Administrator – Takes care of the computer systems that run the EJB Server and related services. – Administrates Operating systems and network related to the server.
EJB Security model • EJB 1. 1 security model is – Role based, and helps to restrict access to beans and their methods based on a client’s role. – It provides an easy way to control who can call which beans and methods and automatically establishes the identity of the caller. – Example of defining roles is an online banking application pg 239, 240
Examples of Security Goals – A customer can access only her own account – A trader can only execute transactions that have a value less than one million Swiss francs – A tax inspector is prohibited from modifying her own tax liability data – An underage subscriber does not have access to an Xrated online movie
Method Permissions • Access to the beans and their methods can be made limited based on their roles. • For this each role must be listed in the deployment descriptor. • Method permissions are defined using method permission elements. • Each method permission element contains a rolename element and one or more EJBs and their methods, as defined by ejb-name and method-name elements. Sample of the method pg 240 -241.
Programmatic Security • Normally Application Assembler and the Deployer configure security in a EJB server. • Programmatically sometimes bean provider has to access some security information, for which EJB provides 2 methods – Principal get. Caller. Principal() – Boolean is. Caller. In. Role(String role. Name)
First Method • get. Caller. Principal() – It returns a Principal object corresponding to the identity of the caller. – It allows the use of the identity of the caller inside the code of the bean. – Example : -If we want a customer to view their own balance but nobody else’s. We could do that by calling the principal of the caller and use that to fetch their account. – pg 242.
Second Method • is. Caller. In. Role() – Boolean function returning true if the caller is in the role or returns false – Used usually when simple permissions are not enough. – Example: - if we have a situation where we need to give permission to bankers to only add up to 1000$ to an account at a time and admin be given all rights. This can be done as Pg 243
Security-role-ref Element • The Security-role-ref element – It alerts the Application assembler and the Deployer if a particular role has dependency in a bean. – < Security-role-ref > <description> This security role will have no limit on the size of transaction </description> <role-name>admin</role-name> < /Security-role-ref > – Pg 243
Conclusions • EJB Security focus on minimal programmatic and declarative access control mechanisms. • This mechanism provides role-based access control for EJB. • Access restriction can be successfully obtained using EJB Security model.
References • Garms, Jess and Daniel Somerfield. Professional Java Security. Wrox. 2001. (ISBN: 1861004257) • Article on EJB Security by Paul Perrone, http: //www. informit. com • www. ibm. com/research/security • www. javaworld. com/javaworld/jw-02 -2002/ jw-0215 ejbsecurity. html • www. java. sun. com/ejbsecurity
- Slides: 23