EIPS On Location Privacy in Fingerprintingbased Indoor Positioning
EIPS On Location Privacy in Fingerprintingbased Indoor Positioning System: An Encryption Approach Wenlu Wang
01 IPS 02 Motivation 03 Preliminary 04 Overview 05 EIPS 06 Experiments 2
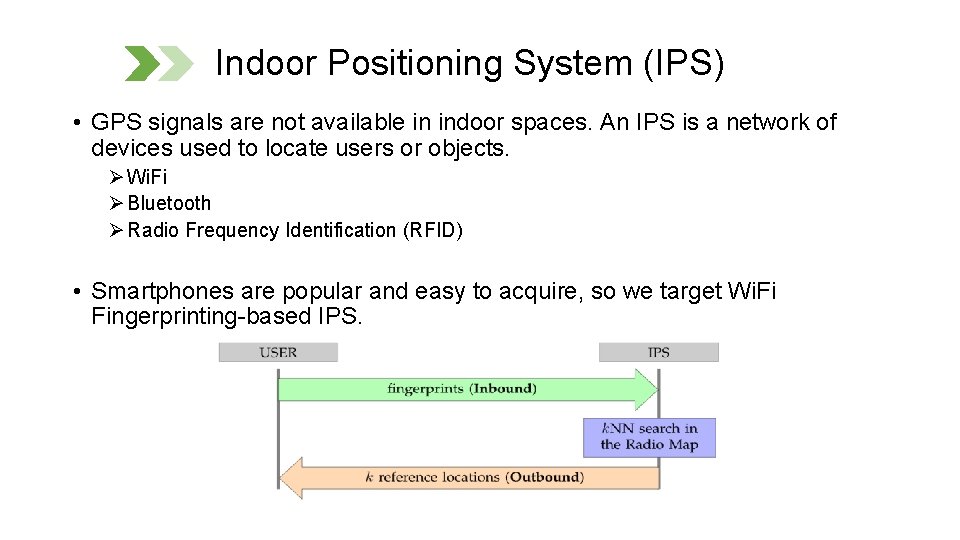
Indoor Positioning System (IPS) • GPS signals are not available in indoor spaces. An IPS is a network of devices used to locate users or objects. Ø Wi. Fi Ø Bluetooth Ø Radio Frequency Identification (RFID) • Smartphones are popular and easy to acquire, so we target Wi. Fi Fingerprinting-based IPS.
![[IPS] Off-line Radio Map initialization Reference Location Access Point (AP) RSS 1 RSS 2 [IPS] Off-line Radio Map initialization Reference Location Access Point (AP) RSS 1 RSS 2](http://slidetodoc.com/presentation_image/7d794bbb8e2469979a4cc45aff644d43/image-4.jpg)
[IPS] Off-line Radio Map initialization Reference Location Access Point (AP) RSS 1 RSS 2 RSS 3 RSS 4 Figure ref: Indoor Positioning Using Adaptive KNN Algorithm Based Fingerprint Technique. In International Conference on Broadband Communications, Networks and Systems Store the received signal strength (RSS) at all the reference locations, named as Radio Map. <[RSS 1, RSS 2, RSS 3, RSS 4], coordinate of >
![[IPS] Online localization [IPS] Online localization](http://slidetodoc.com/presentation_image/7d794bbb8e2469979a4cc45aff644d43/image-5.jpg)
[IPS] Online localization
01 IPS 02 Motivation 03 Preliminary 04 Overview 05 EIPS 06 Experiments 6
![Motivation • [Privacy Concerns] The localization operations are uncontrollable by users since the Radio Motivation • [Privacy Concerns] The localization operations are uncontrollable by users since the Radio](http://slidetodoc.com/presentation_image/7d794bbb8e2469979a4cc45aff644d43/image-7.jpg)
Motivation • [Privacy Concerns] The localization operations are uncontrollable by users since the Radio Map are stored and operated on the server-side. The server is able to track a user at a fine granularity. • [SOTA] TVM retrieves extra reference records to anonymize the real ones using bloom filter, which incurs extensive memory cost on smart phones. • [Challenges] I. II. An IPS should not receive a user’s query (e. g. , fingerprints) in plain text. An IPS should not be able to infer a user’s location based on the query.
01 IPS 02 Motivation 03 Preliminary 04 Overview 05 EIPS 06 Experiments 8
Preliminary • IPS involves k. NN search -> We propose to use a privacy-preserving encryption-based k. NN search: Asymmetric Scalar-product Preserving Encryption (ASPE). • ASPE does not resist known plain text attack (KPA). • We introduce a centralized server (who holds the encryption key), called EDS (Encryption & Decryption Server). • Alleviate the burden of smartphones. • EDS is neutral.
01 IPS 02 Motivation 03 Preliminary 04 Overview 05 EIPS 06 Experiments 10
Overview We propose to develop a bidirectional commutative cipher to resist KPA with the help of EDS. Ø Commutative Cipher + ASPE: privacy-preserving k. NN Ø We propose our own additional operations to resist KPA. Benefit I: We use encrypted databases that support encrypted query. Benefit II: Our proposed communication scheme resists KPA. In summary, we tackle the technical challenges of enabling users to acquire their positions from IPS while preserving their privacy.
Main Ideas ØInstead of anonymizing the real locations using extra fake records, we use encryption to achieve anonymity. ØEncryption is considerably vulnerable towards KPA, we take advantages of features of ASPE, commutative ciphers, and cryptographic techniques to address this challenge.
Pros Ø No computational or memory requirement for smartphones. Ø Highly secure under privacy attacks. Cons Ø Increase the number of transitions. Ø Another party EDS is introduced.
01 IPS 02 Motivation 03 Preliminary 04 Overview 05 EIPS 06 Experiments 14
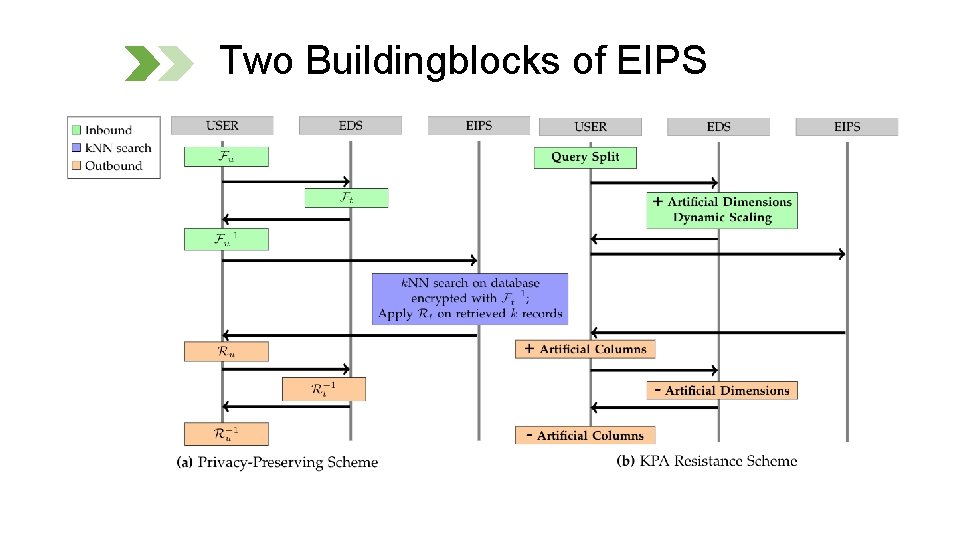
Two Buildingblocks of EIPS
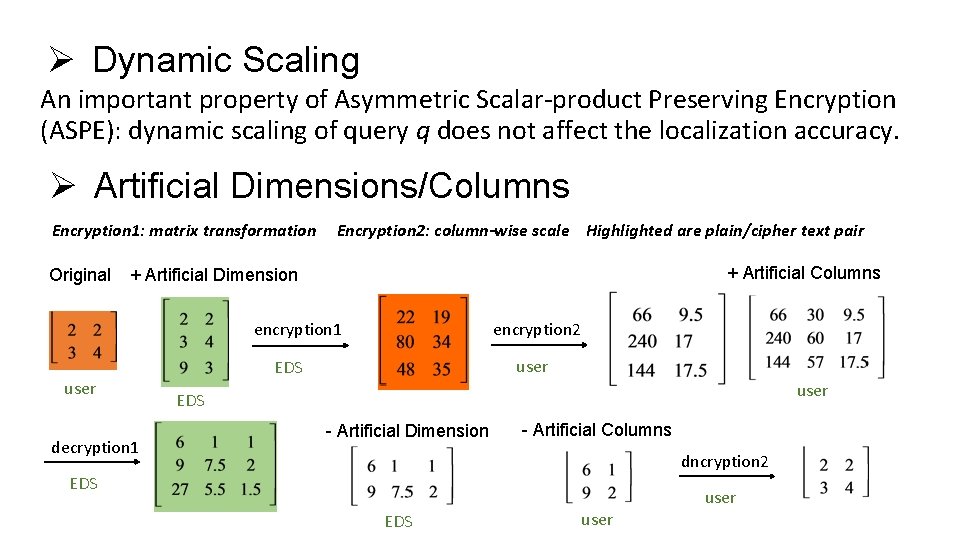
Ø Dynamic Scaling An important property of Asymmetric Scalar-product Preserving Encryption (ASPE): dynamic scaling of query q does not affect the localization accuracy. Ø Artificial Dimensions/Columns Encryption 1: matrix transformation Original Encryption 2: column-wise scale Highlighted are plain/cipher text pair + Artificial Columns + Artificial Dimension encryption 1 user decryption 1 encryption 2 user EDS - Artificial Dimension - Artificial Columns dncryption 2 EDS user
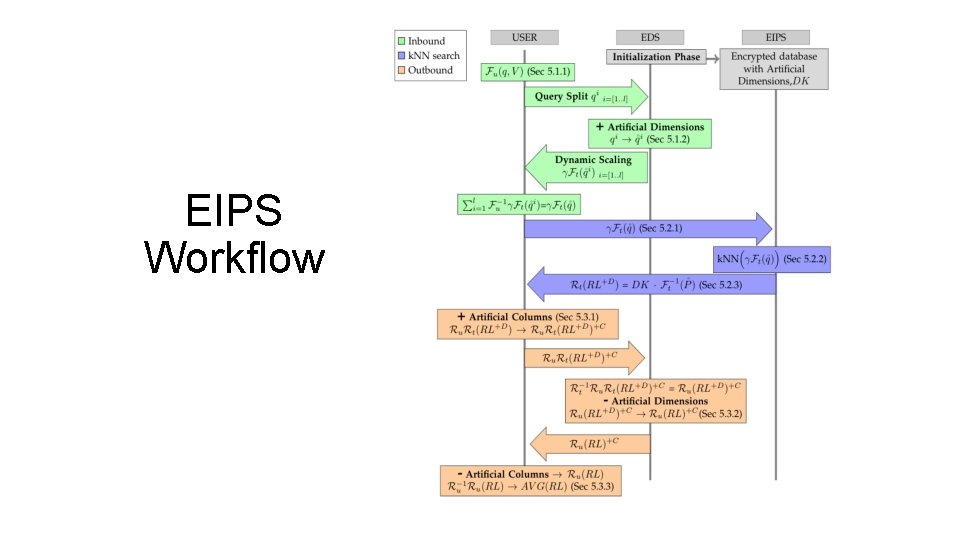
EIPS Workflow
01 IPS 02 Motivation 03 Preliminary 04 Overview 05 EIPS 06 Experiments 18
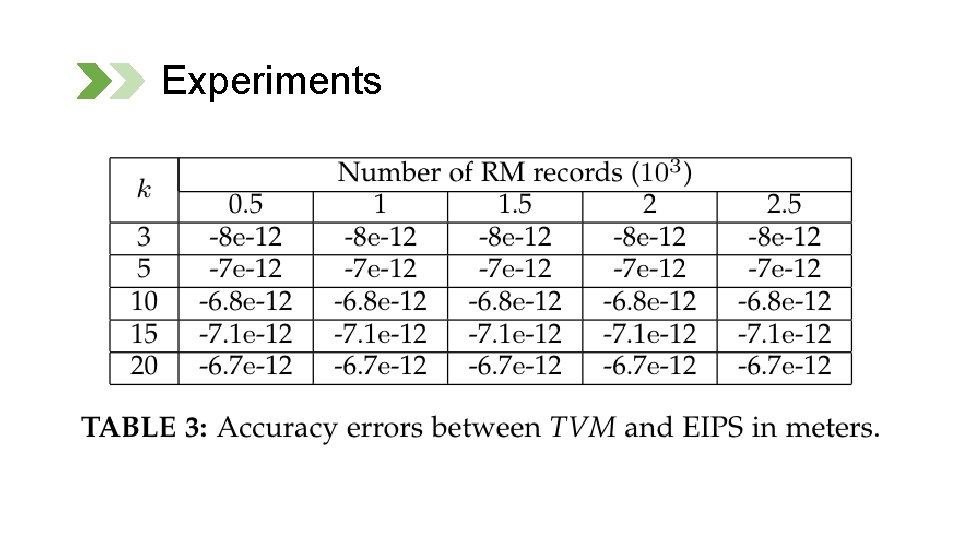
Experiments
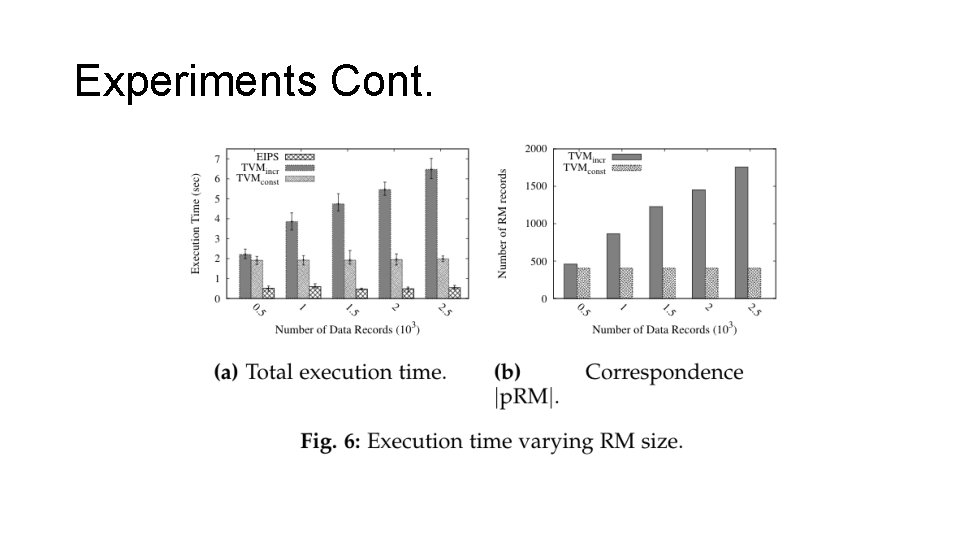
Experiments Cont.
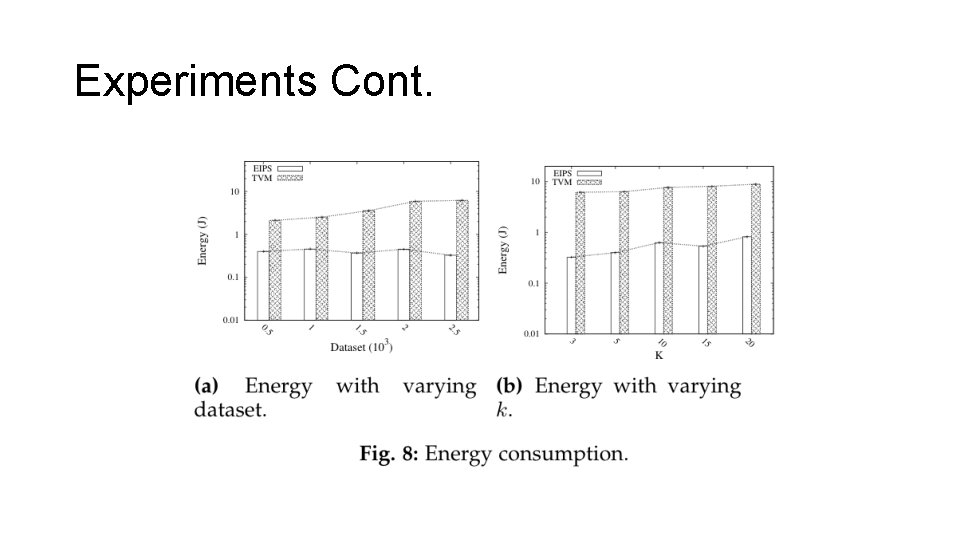
Experiments Cont.
Conclusion EIPS achieves Ø high accuracy Ø efficient execution time Ø low energy cost
Thank you!
- Slides: 23