Efficient Lattice HIBE in the standard model Shweta
Efficient Lattice (H)IBE in the standard model Shweta Agrawal, Dan Boneh, Xavier Boyen
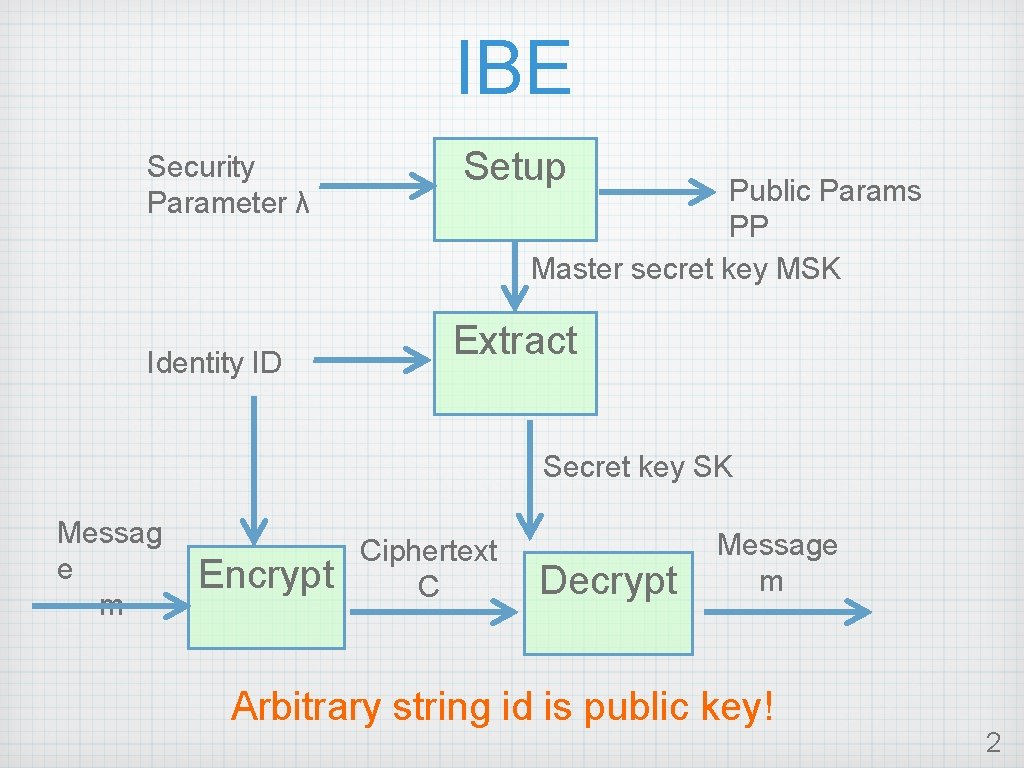
IBE Security Parameter λ Identity ID Setup Public Params PP Master secret key MSK Extract Secret key SK Messag e m Encrypt Ciphertext C Decrypt Message m Arbitrary string id is public key! 2
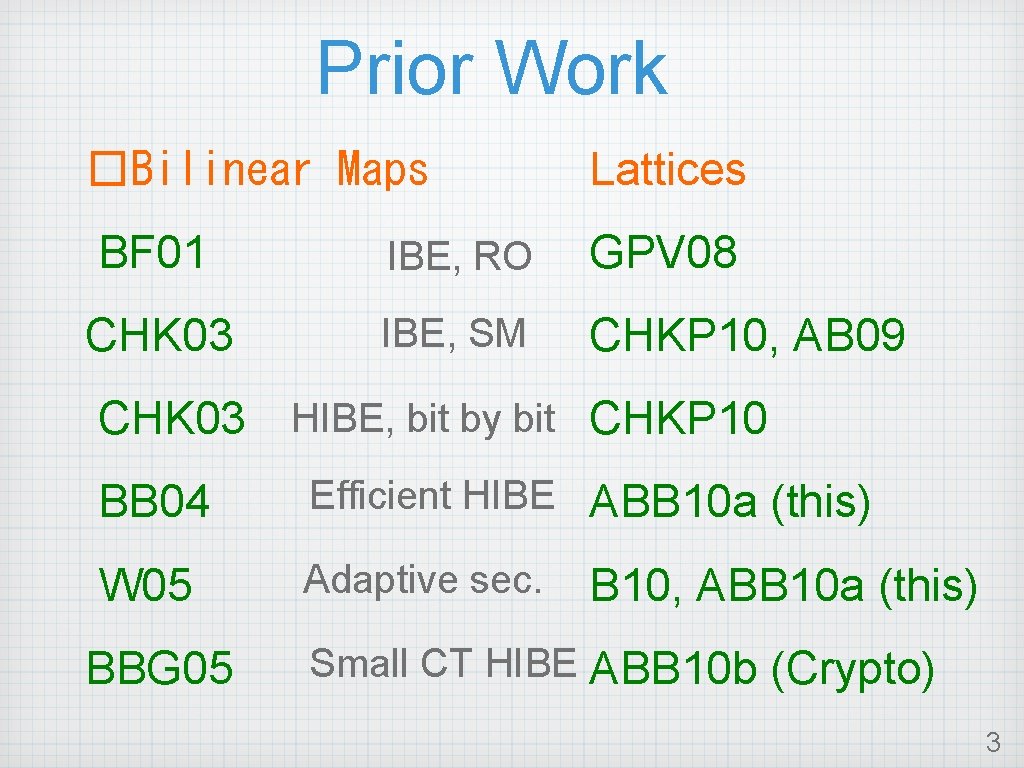
Prior Work �Bilinear Maps Lattices BF 01 IBE, RO GPV 08 CHK 03 IBE, SM CHKP 10, AB 09 CHK 03 HIBE, bit by bit CHKP 10 BB 04 Efficient HIBE ABB 10 a (this) W 05 Adaptive sec. BBG 05 B 10, ABB 10 a (this) Small CT HIBE ABB 10 b (Crypto) 3
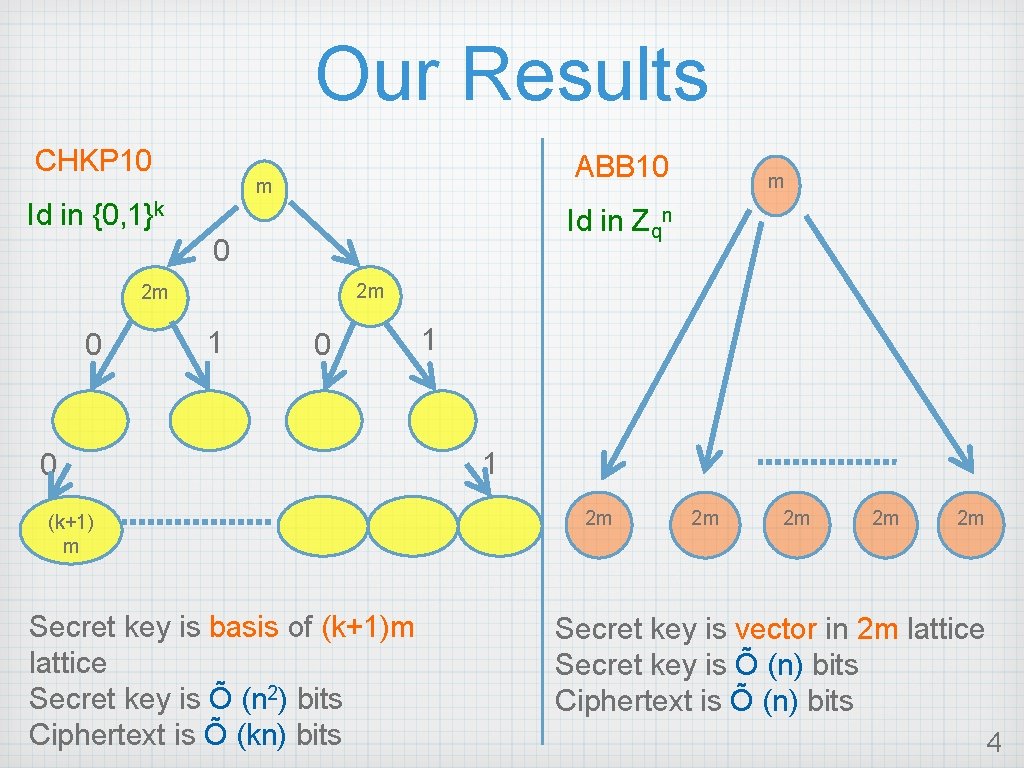
Our Results CHKP 10 ABB 10 m Id in {0, 1}k Id in Zqn 0 2 m 2 m 0 m 1 0 0 (k+1) m Secret key is basis of (k+1)m lattice Secret key is Õ (n 2) bits Ciphertext is Õ (kn) bits 1 1 2 m 2 m 2 m Secret key is vector in 2 m lattice Secret key is Õ (n) bits Ciphertext is Õ (n) bits 4
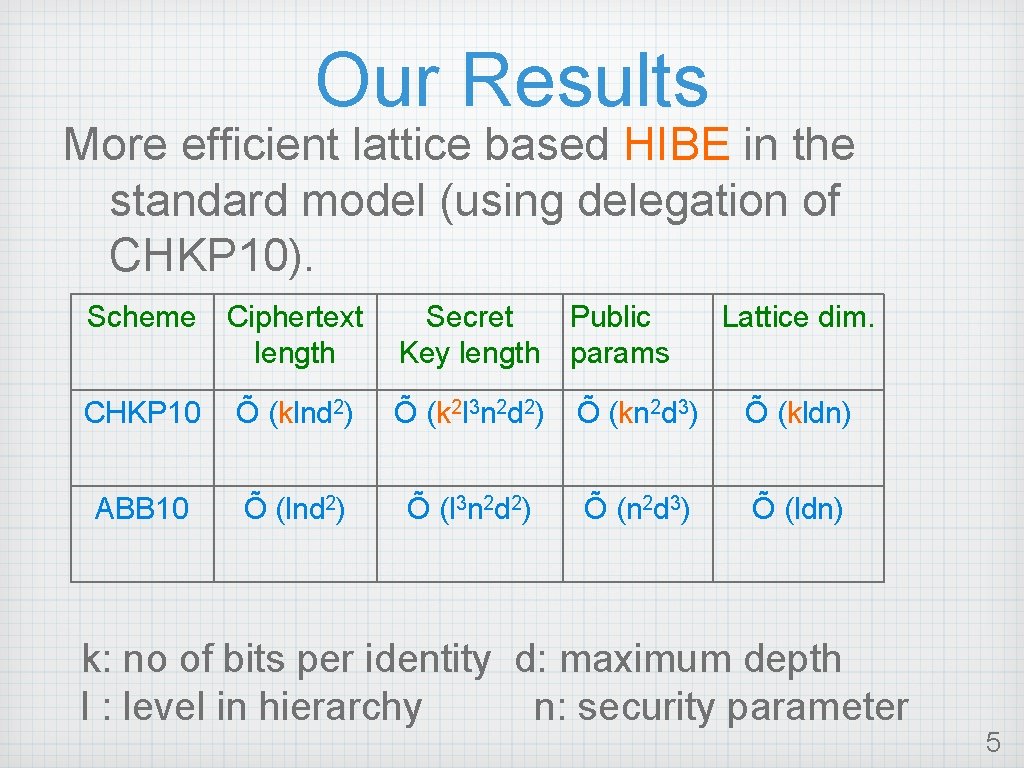
Our Results More efficient lattice based HIBE in the standard model (using delegation of CHKP 10). Scheme Ciphertext length Secret Public Key length params Lattice dim. CHKP 10 Õ (klnd 2) Õ (k 2 l 3 n 2 d 2) Õ (kn 2 d 3) Õ (kldn) ABB 10 Õ (lnd 2) Õ (l 3 n 2 d 2) Õ (n 2 d 3) Õ (ldn) k: no of bits per identity d: maximum depth l : level in hierarchy n: security parameter 5
Why Lattices? Strong hardness guarantees Efficient operations, parallelizable No quantum algorithm (yet) 6
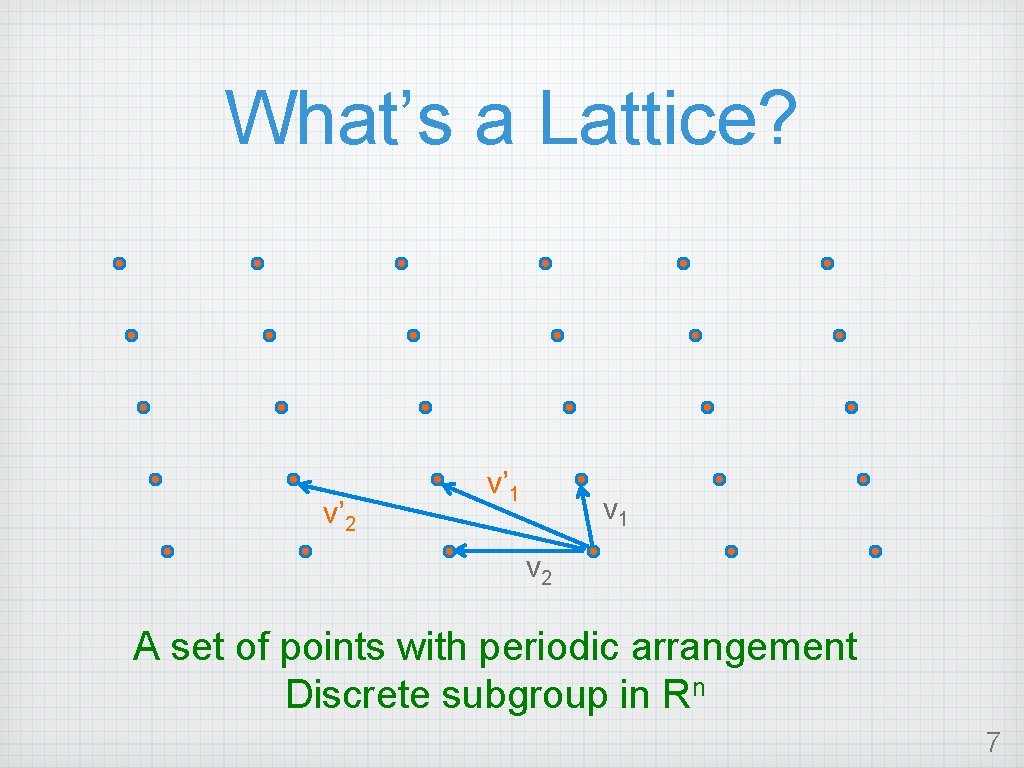
What’s a Lattice? v’ 2 v’ 1 v 2 A set of points with periodic arrangement Discrete subgroup in Rn 7

Parallelepipeds 8
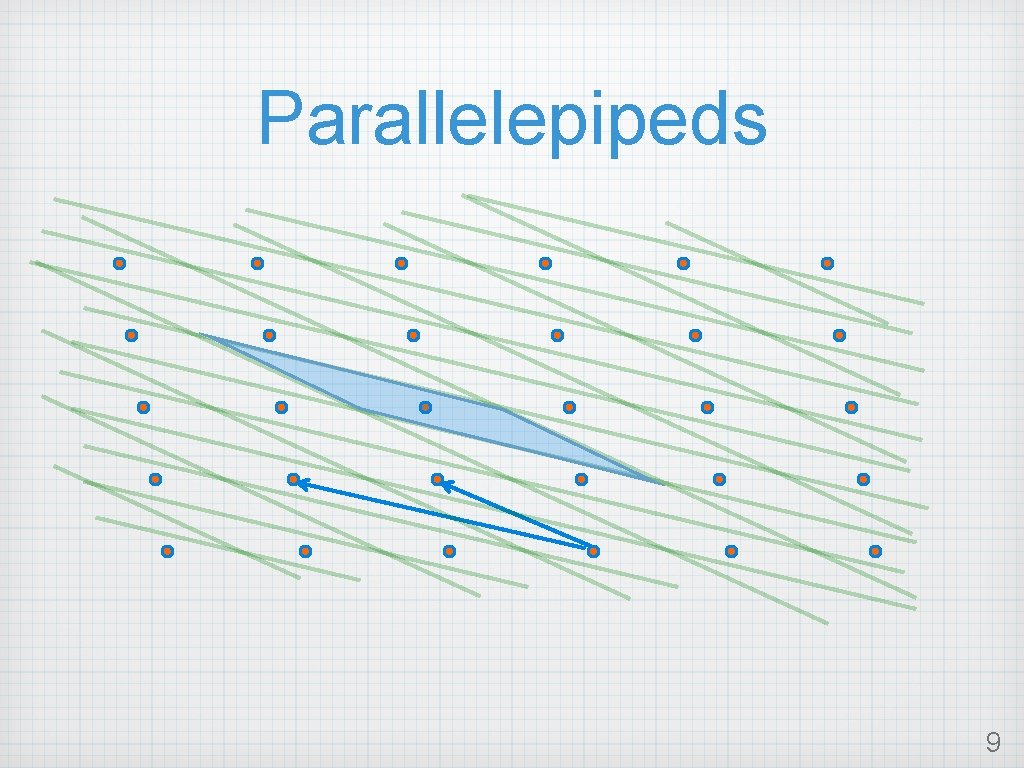
Parallelepipeds 9
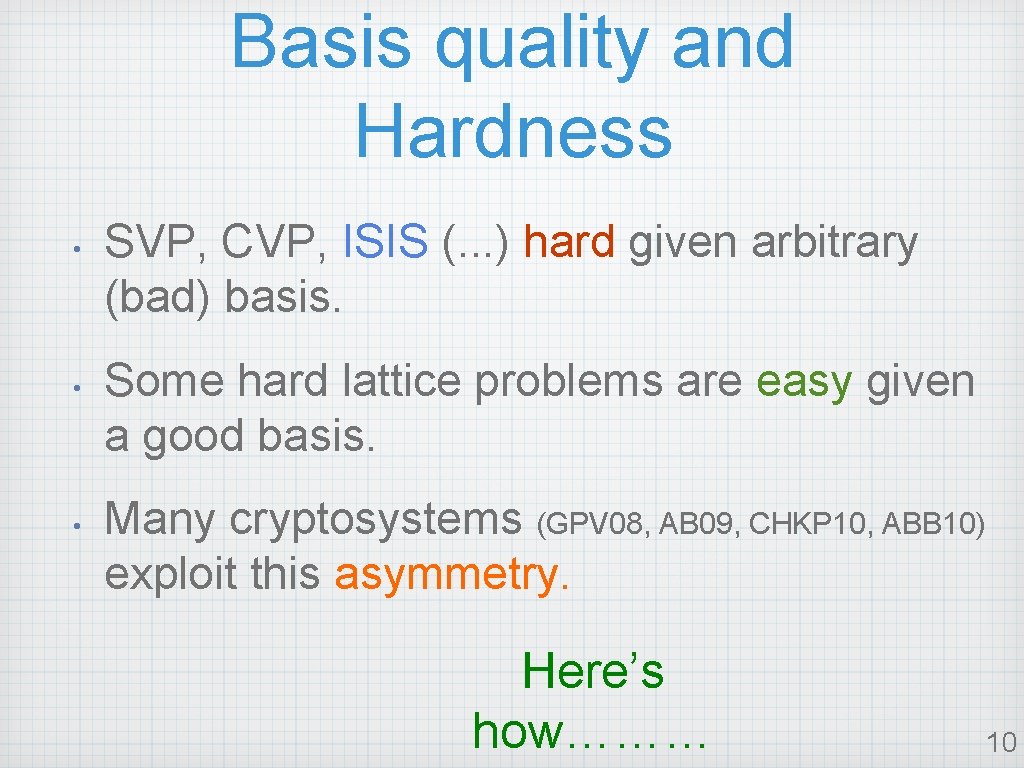
Basis quality and Hardness • • • SVP, CVP, ISIS (. . . ) hard given arbitrary (bad) basis. Some hard lattice problems are easy given a good basis. Many cryptosystems (GPV 08, AB 09, CHKP 10, ABB 10) exploit this asymmetry. Here’s how……… 10
Exploiting Asymmetry(roughly) Make bad basis public key Make good basis private key Encrypt using bad basis, decrypt using good basis Recovering good basis from bad basis is hard ! 11
More precisely…. The private key comes from the ISIS problem…. 12

ISIS (or syndrome decoding) Given matrix A over Zq, syndrome u over Zq, find ``small” (low norm) integer vector z such that Az=u mod q n A z m = u n m Define f. A(z) = Az f. A : space of ``small” m-dim vectors n-dim vectors Solving ISIS (or inverting f. A) is hard !! 13
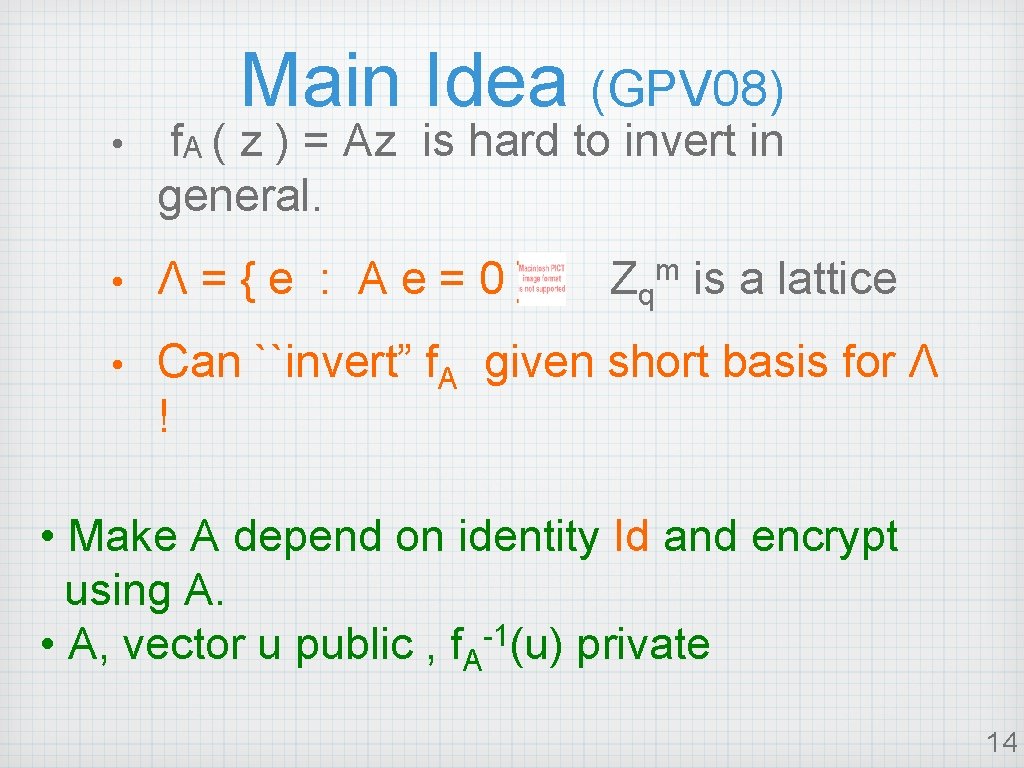
Main Idea (GPV 08) • f. A ( z ) = Az is hard to invert in general. • Λ={e : Ae=0} • Can ``invert” f. A given short basis for Λ ! Zqm is a lattice • Make A depend on identity Id and encrypt using A. • A, vector u public , f. A-1(u) private 14
![Intuition for Constructions Previous Systems [AB 09, CHKP 10] • Master secret key • Intuition for Constructions Previous Systems [AB 09, CHKP 10] • Master secret key •](http://slidetodoc.com/presentation_image_h/263a48dd5d42cb713c09cb405f6473e6/image-15.jpg)
Intuition for Constructions Previous Systems [AB 09, CHKP 10] • Master secret key • Secret Key for (id=01) : basis for F 01 = 0 1 [A 0| A 1 |A 2 ] : basis for A 0 (one block per bit!) • Know how to compute trapdoor for ``extended” matrix [T 1|T 2|T 3] • Encrypt (b, id=01): Uses matrix F 01 15
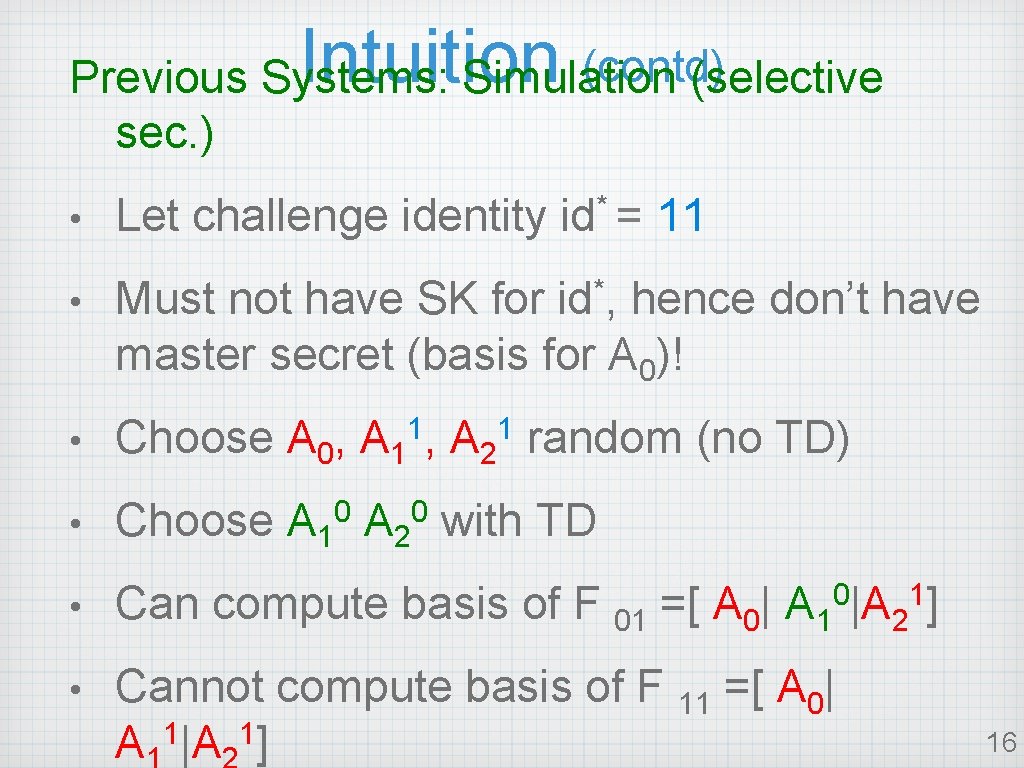
Intuition (contd) Previous Systems: Simulation (selective sec. ) • Let challenge identity id* = 11 • Must not have SK for id*, hence don’t have master secret (basis for A 0)! 1, • Choose A 0, A 1 A 2 random (no TD) • Choose A 10 A 20 with TD • Can compute basis of F 01 =[ A 0| A 10|A 21] • Cannot compute basis of F 11 =[ A 0| 1 1 A |A ] 1 16
![Our new system [ABB 10] n • Id in Zq is encoded ``all at Our new system [ABB 10] n • Id in Zq is encoded ``all at](http://slidetodoc.com/presentation_image_h/263a48dd5d42cb713c09cb405f6473e6/image-17.jpg)
Our new system [ABB 10] n • Id in Zq is encoded ``all at once”! • Master secret: basis for A 0 • Encryption matrix Fid = [A 0| A 1 +id B] • Secret Key for id: = vector in Λ(Fid) Fid fixed dimension ! 17
![Our new System [ABB 10] Simulation: Let challenge identity = * id • Don’t Our new System [ABB 10] Simulation: Let challenge identity = * id • Don’t](http://slidetodoc.com/presentation_image_h/263a48dd5d42cb713c09cb405f6473e6/image-18.jpg)
Our new System [ABB 10] Simulation: Let challenge identity = * id • Don’t have basis for A 0 Fid = [A 0| A 1 +id B] • Have basis for B • Let A 1 = [A 0 R – id* ×B] • Fid = [A 0| A 0 R + (id –id*)B] • Develop algorithm to find basis for Fid given basis for B • Trapdoor vanishes for id = id* Random low norm matrix 18
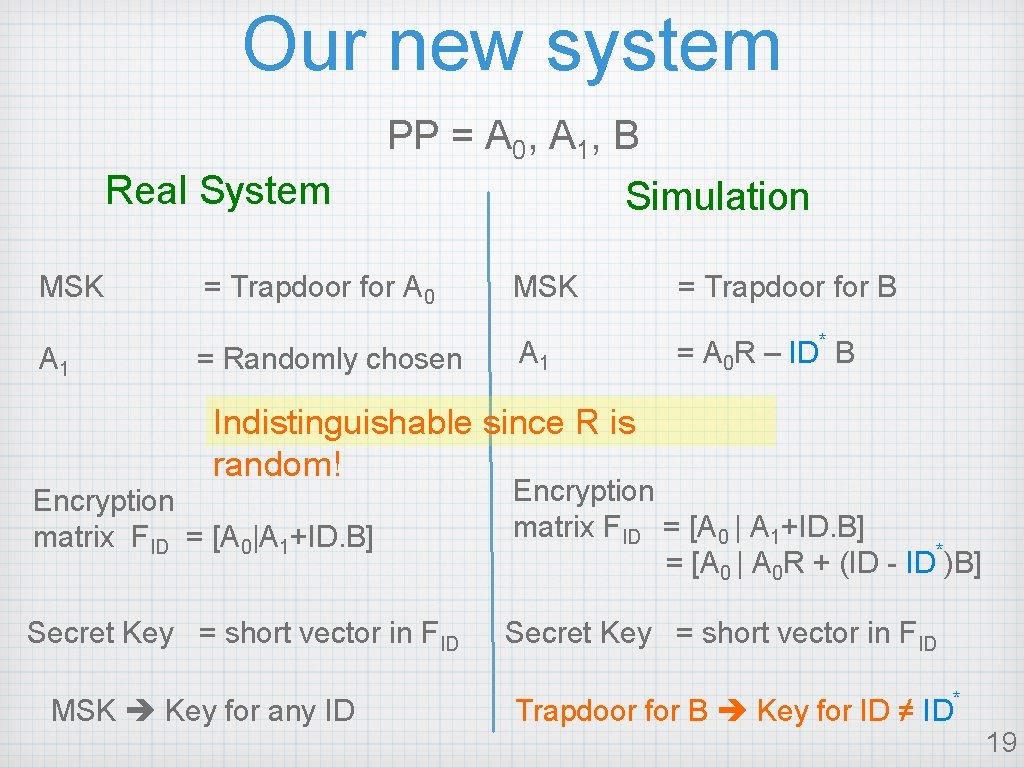
Our new system PP = A 0, A 1, B Real System MSK A 1 = Trapdoor for A 0 = Randomly chosen Simulation MSK A 1 = Trapdoor for B * = A 0 R – ID B Indistinguishable since R is random! Encryption matrix FID = [A 0|A 1+ID. B] Encryption matrix FID = [A 0 | A 1+ID. B] * = [A 0 | A 0 R + (ID - ID )B] Secret Key = short vector in FID MSK Key for any ID Trapdoor for B Key for ID ≠ ID * 19
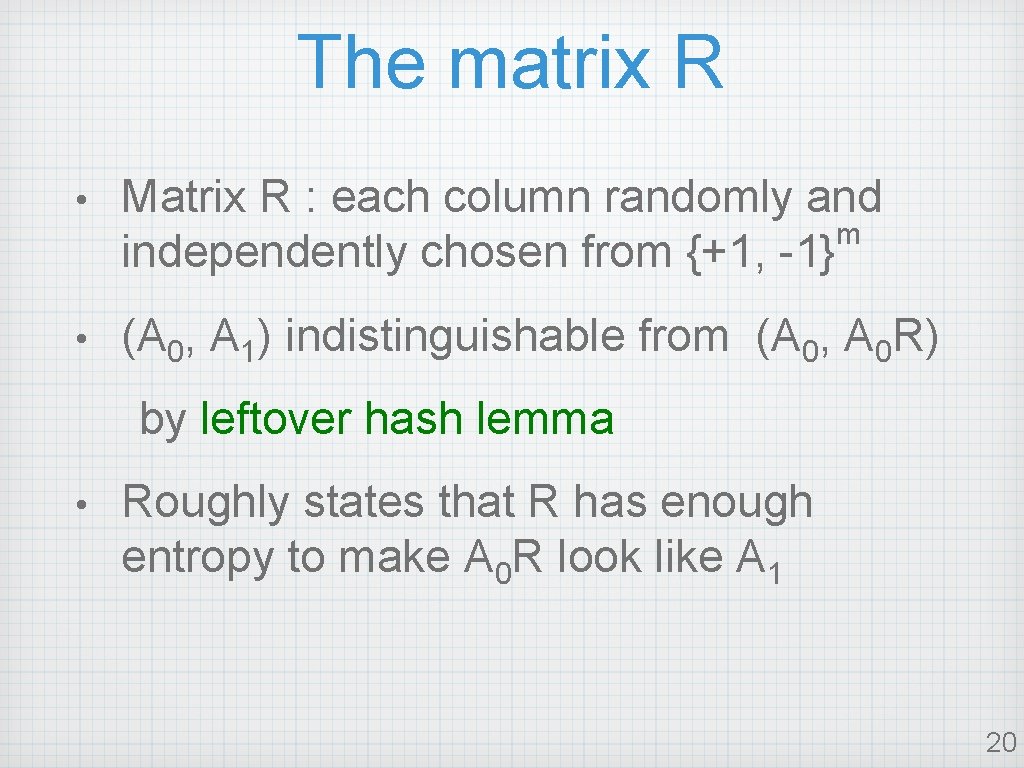
The matrix R • Matrix R : each column randomly and m independently chosen from {+1, -1} • (A 0, A 1) indistinguishable from (A 0, A 0 R) by leftover hash lemma • Roughly states that R has enough entropy to make A 0 R look like A 1 20

Key Generation (Real • Given A 0, u, short basis for Λ(A 0) system) can sample short e s. t. A 0 e = u (GPV 08) • • Have short basis for Λ(A 0), want short vector in Λ(A 0 | A 1) , i. e. e = e 0 e 1 A 0 | A 1 e 0 = 0 e 1 Easy! Pick short e 1 randomly. Solve for short e 0 using short basis for Λ(A 0) 21
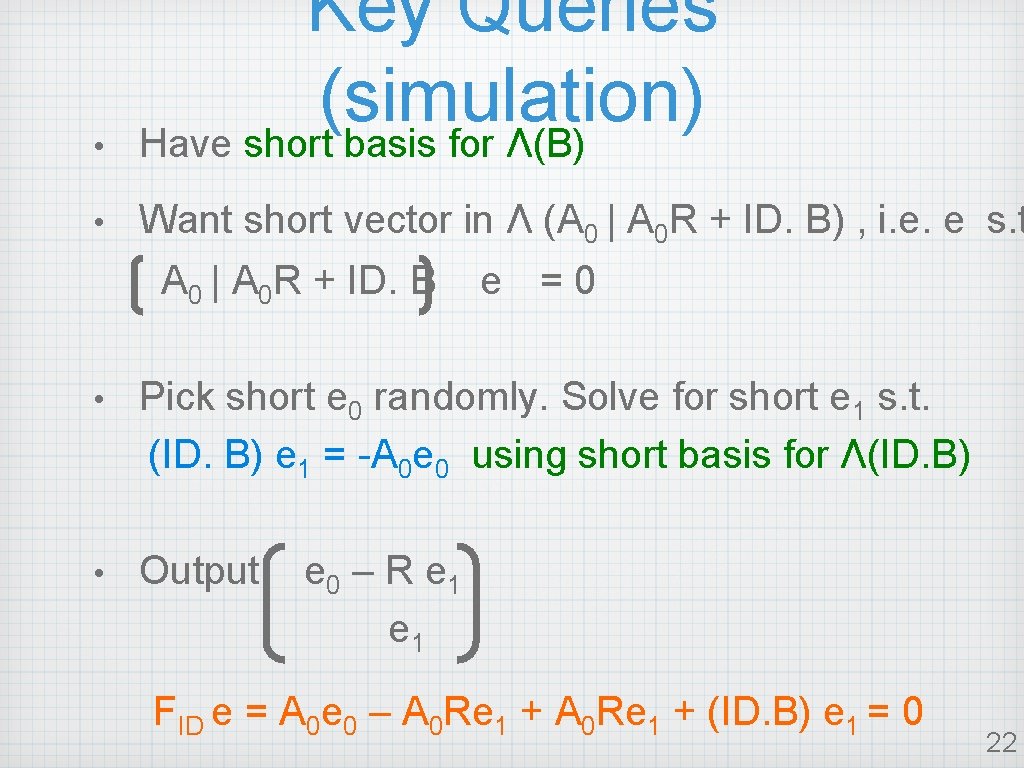
• Key Queries (simulation) Have short basis for Λ(B) • Want short vector in Λ (A 0 | A 0 R + ID. B) , i. e. e s. t A 0 | A 0 R + ID. B e =0 • Pick short e 0 randomly. Solve for short e 1 s. t. (ID. B) e 1 = -A 0 e 0 using short basis for Λ(ID. B) • Output e 0 – R e 1 FID e = A 0 e 0 – A 0 Re 1 + (ID. B) e 1 = 0 22
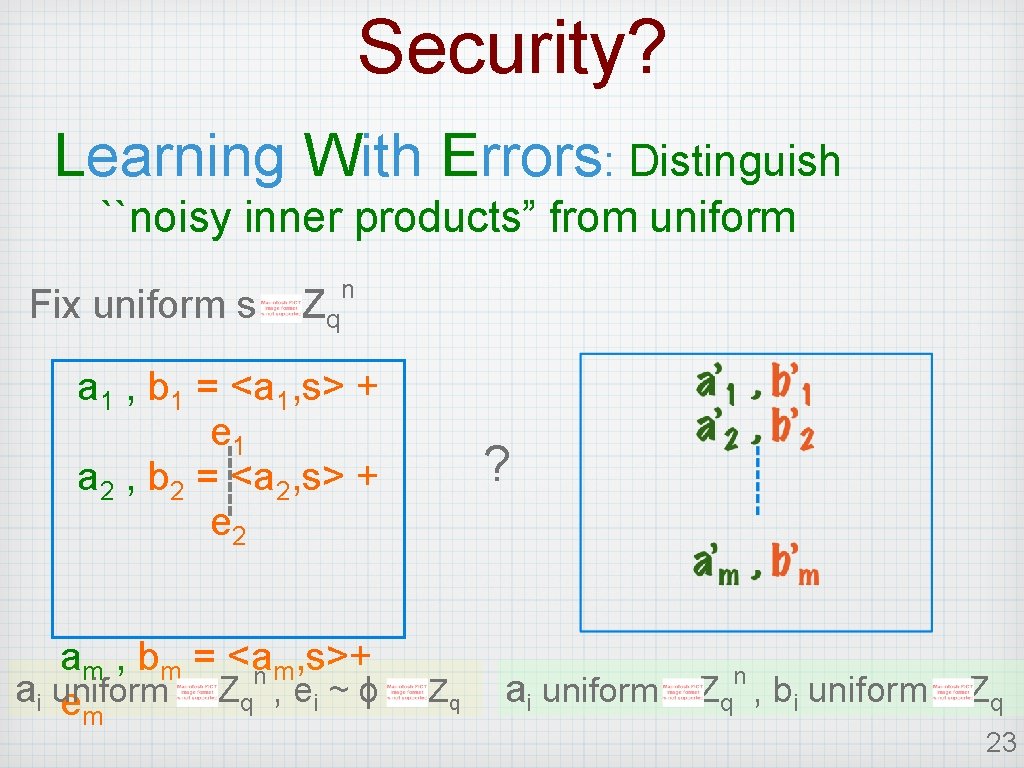
Security? Learning With Errors: Distinguish ``noisy inner products” from uniform Fix uniform s Zq n a 1 , b 1 = <a 1, s> + e 1 a 2 , b 2 = <a 2, s> + e 2 am , bm = <a , s>+ m n ai uniform Zq , e i ~ ϕ em ? Zq n ai uniform Zq , bi uniform Zq 23
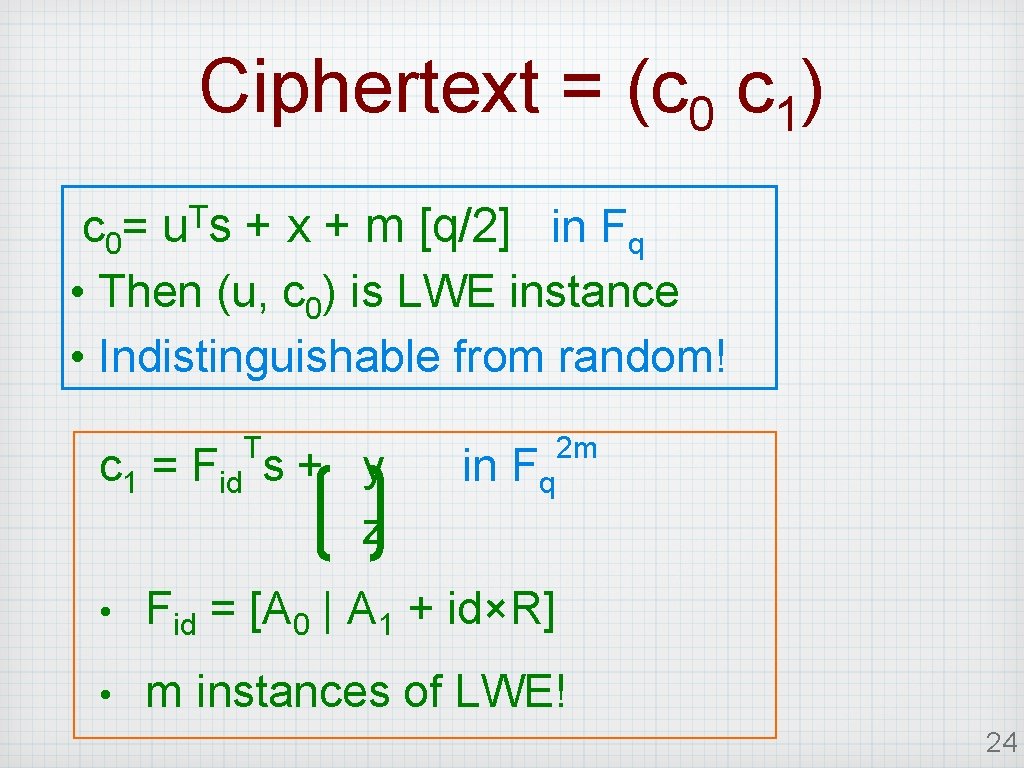
Ciphertext = (c 0 c 1) T u s c 0= + x + m [q/2] in Fq • Then (u, c 0) is LWE instance • Indistinguishable from random! T c 1 = Fid s + y z in Fq 2 m • Fid = [A 0 | A 1 + id×R] • m instances of LWE! 24
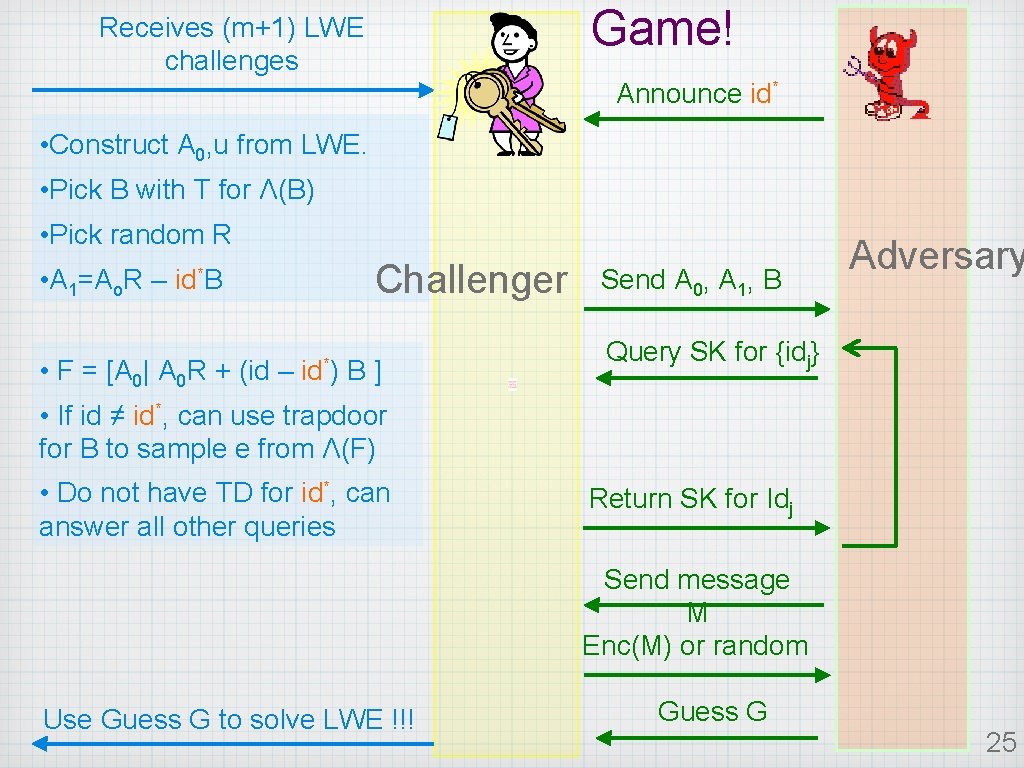
Game! Receives (m+1) LWE challenges Announce id* • Construct A 0, u from LWE. • Pick B with T for Λ(B) • Pick random R • A 1=Ao. R – Challenger id*B • F = [A 0| A 0 R + (id – id*) B] Send A 0, A 1, B Adversary Query SK for {idj} • If id ≠ id*, can use trapdoor for B to sample e from Λ(F) • Do not have TD for id*, can answer all other queries Return SK for Idj Send message M Enc(M) or random Use Guess G to solve LWE !!! Guess G 25
Conclusions • Reviewed existing lattice based IBE • Examined new technique to encrypt without increasing the dimension of the encryption matrix • BB-style IBE and HIBE • About 160 times more efficient than CHKP 10 (k needs to be 160 bits). 26
Thank you! Questions? 27
- Slides: 27