Efficient Identification of Design Patterns with Bitvector Algorithm
Efficient Identification of Design Patterns with Bit-vector Algorithm Design recovery to maintain Presenter: Shin joon choul Applied Software Engineering Lab, UOU March - 2007 1/20
Contents n Introduction l l n Sample Algorithm Procedure l l n Design recovery Bio-informatics Bit-vector algorithm Design Pattern - Composite Simple Program Structure Development Procedure l 4 Step n Results n Conclusion Applied Software Engineering Lab, UOU April - 2007 2/20
Introduction - Design Recovery • Efficiently Maintain Applied Software Engineering Lab, UOU April - 2007 3/20
Introduction - Bit Vector n The structure of DNA and RNA are very similar. They are both ordered sequences of 4 types of substances: ACGT for DNA, and ACGU for RNA. l l n DNA is string(ACGT). l n ex) AAACGTTTCCGGAATGG find TCC For Searching "Matching DNA", use Bit Vector Algorithm. Program source is string too. l We can use Bit Vector Applied Software Engineering Lab, UOU April - 2007 4/20
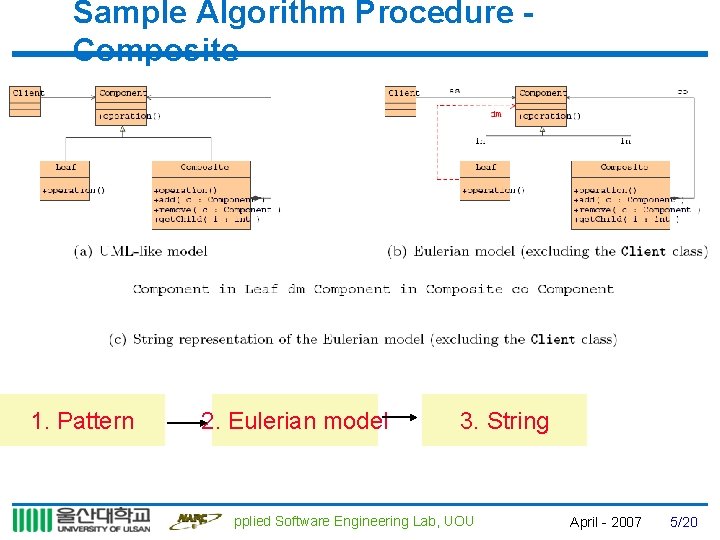
Sample Algorithm Procedure Composite 1. Pattern 2. Eulerian model 3. String Applied Software Engineering Lab, UOU April - 2007 5/20
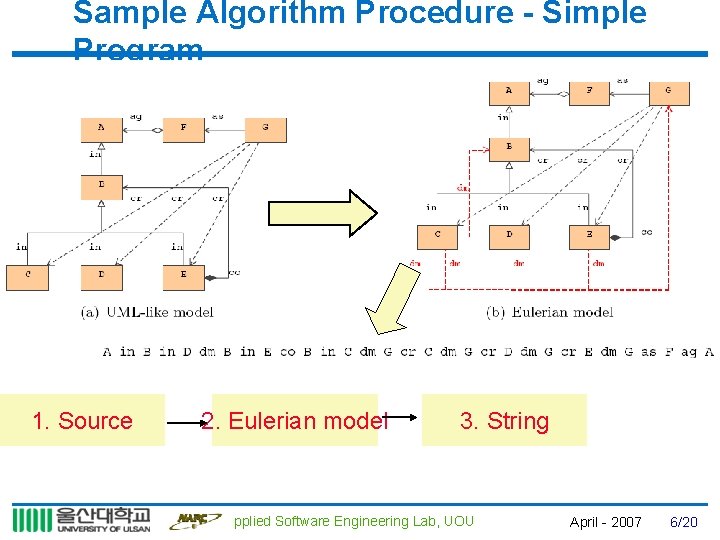
Sample Algorithm Procedure - Simple Program 1. Source 2. Eulerian model 3. String Applied Software Engineering Lab, UOU April - 2007 6/20
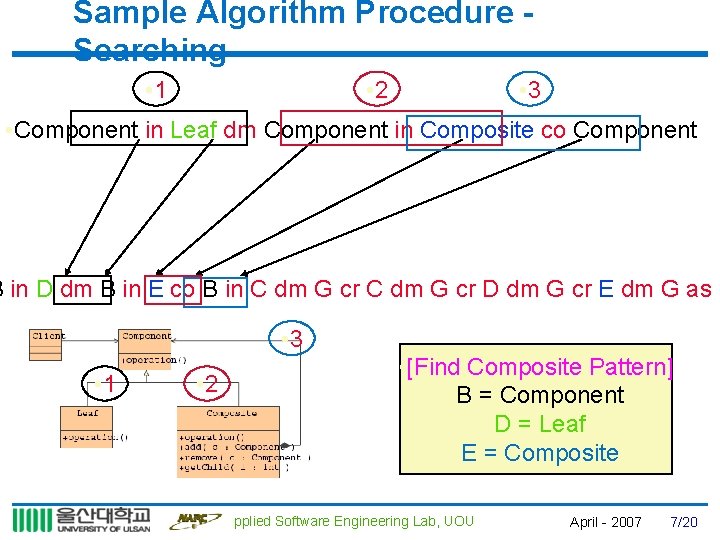
Sample Algorithm Procedure Searching • 1 • 2 • 3 • Component in Leaf dm Component in Composite co Component B in D dm B in E co B in C dm G cr D dm G cr E dm G as F • 3 • 1 • 2 • [Find Composite Pattern] • B = Component • D = Leaf • E = Composite Applied Software Engineering Lab, UOU April - 2007 7/20
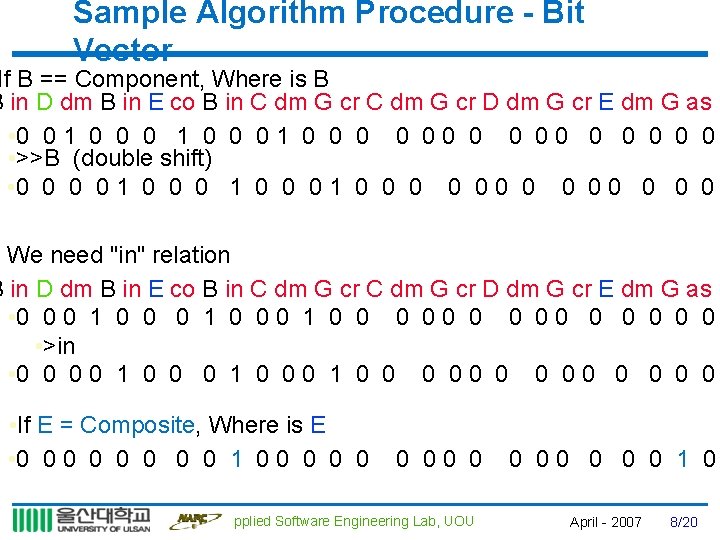
Sample Algorithm Procedure - Bit Vector If B == Component, Where is B B in D dm B in E co B in C dm G cr D dm G cr E dm G as F • 0 0 1 0 0 0 0 0 • >>B (double shift) • 0 0 1 0 0 0 0 We need "in" relation B in D dm B in E co B in C dm G cr D dm G cr E dm G as F • 0 0 0 1 0 0 0 0 • >in • 0 0 1 0 0 0 0 • If E = Composite, Where is E • 0 0 0 0 1 0 0 0 00 0 Applied Software Engineering Lab, UOU 0 00 0 1 0 April - 2007 8/20
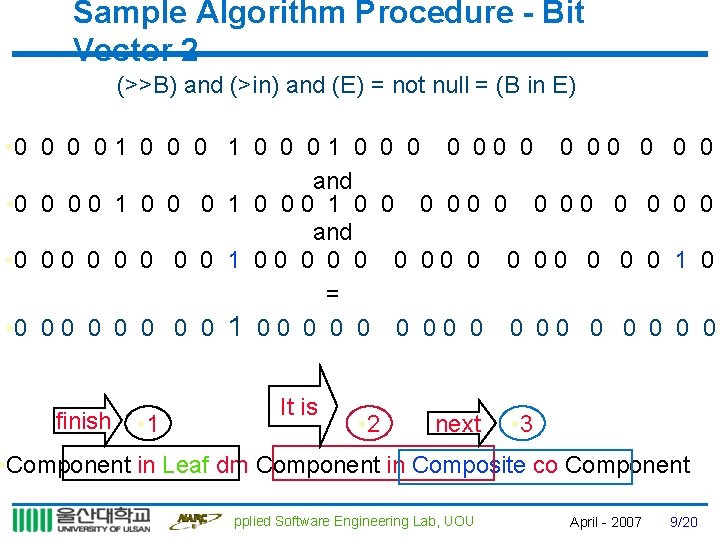
Sample Algorithm Procedure - Bit Vector 2 (>>B) and (>in) and (E) = not null = (B in E) • 0 0 0 0 1 0 0 0 1 0 0 0 0 0 0 and • 0 0 0 0 1 0 0 0 0 = • 0 0 0 0 1 0 0 0 0 finish • 1 It is • 2 next 0 0 1 0 0 0 • 3 • Component in Leaf dm Component in Composite co Component Applied Software Engineering Lab, UOU April - 2007 9/20
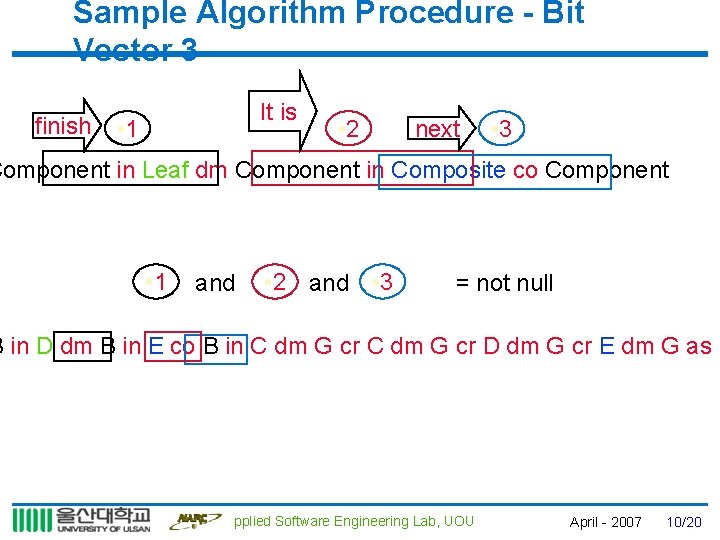
Sample Algorithm Procedure - Bit Vector 3 finish It is • 1 • 2 next • 3 Component in Leaf dm Component in Composite co Component • 1 and • 2 and • 3 = not null B in D dm B in E co B in C dm G cr D dm G cr E dm G as F Applied Software Engineering Lab, UOU April - 2007 10/20
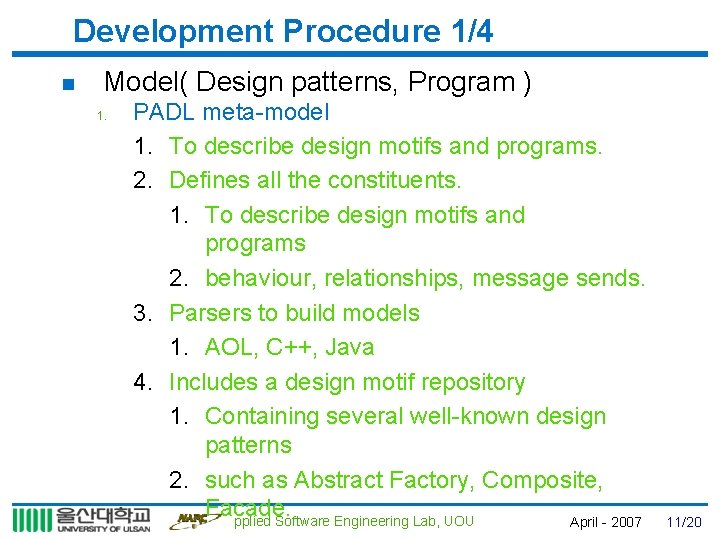
Development Procedure 1/4 n Model( Design patterns, Program ) 1. PADL meta-model 1. To describe design motifs and programs. 2. Defines all the constituents. 1. To describe design motifs and programs 2. behaviour, relationships, message sends. 3. Parsers to build models 1. AOL, C++, Java 4. Includes a design motif repository 1. Containing several well-known design patterns 2. such as Abstract Factory, Composite, Facade. Applied Software Engineering Lab, UOU April - 2007 11/20
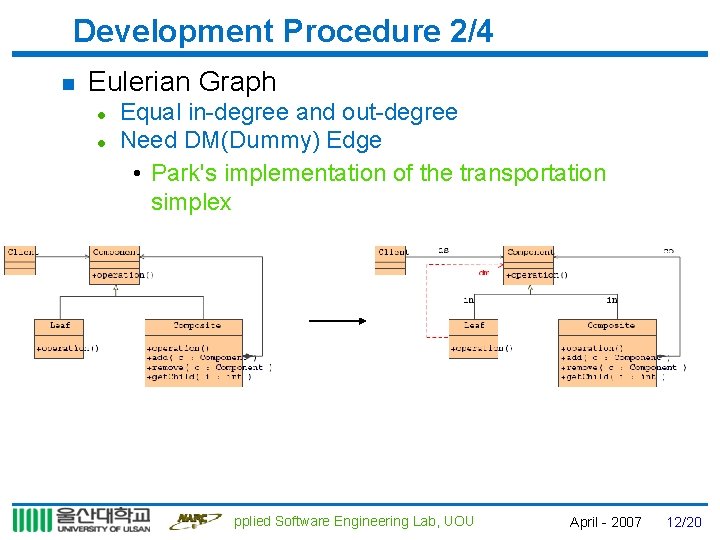
Development Procedure 2/4 n Eulerian Graph l l Equal in-degree and out-degree Need DM(Dummy) Edge • Park's implementation of the transportation simplex Applied Software Engineering Lab, UOU April - 2007 12/20
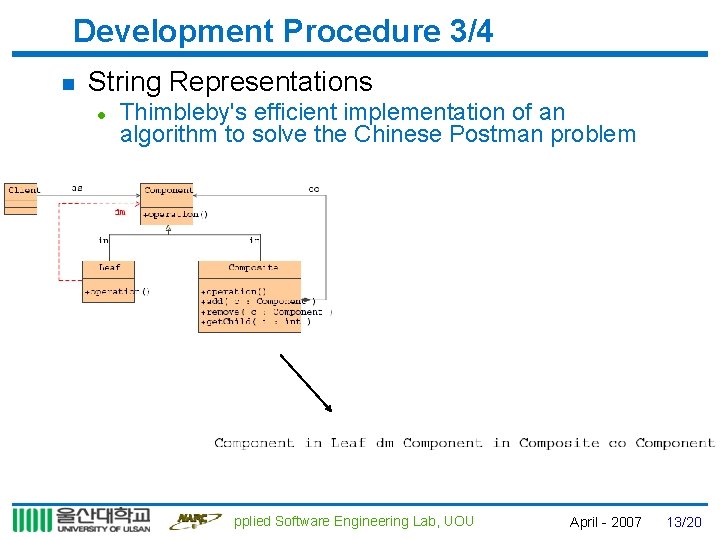
Development Procedure 3/4 n String Representations l Thimbleby's efficient implementation of an algorithm to solve the Chinese Postman problem Applied Software Engineering Lab, UOU April - 2007 13/20
Development Procedure 4/4 n Iterative bit-vector algorithm l l In Java using the Eclipse platform. We use a sparse vector(bit string) • majority of the bits in the vectors are 0 • Hash map and only the 1 -valued bits are stored. Applied Software Engineering Lab, UOU April - 2007 14/20
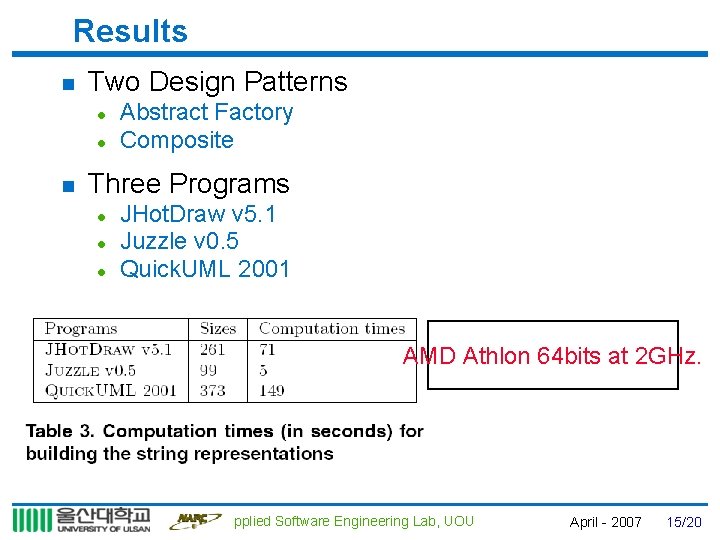
Results n Two Design Patterns l l n Abstract Factory Composite Three Programs l l l JHot. Draw v 5. 1 Juzzle v 0. 5 Quick. UML 2001 AMD Athlon 64 bits at 2 GHz. Applied Software Engineering Lab, UOU April - 2007 15/20
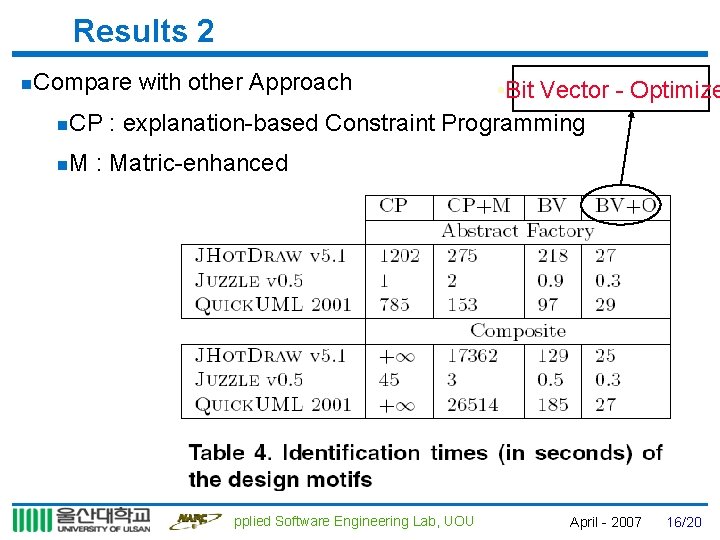
Results 2 n. Compare with other Approach • Bit Vector - Optimize n. CP : explanation-based Constraint Programming n. M : Matric-enhanced Applied Software Engineering Lab, UOU April - 2007 16/20
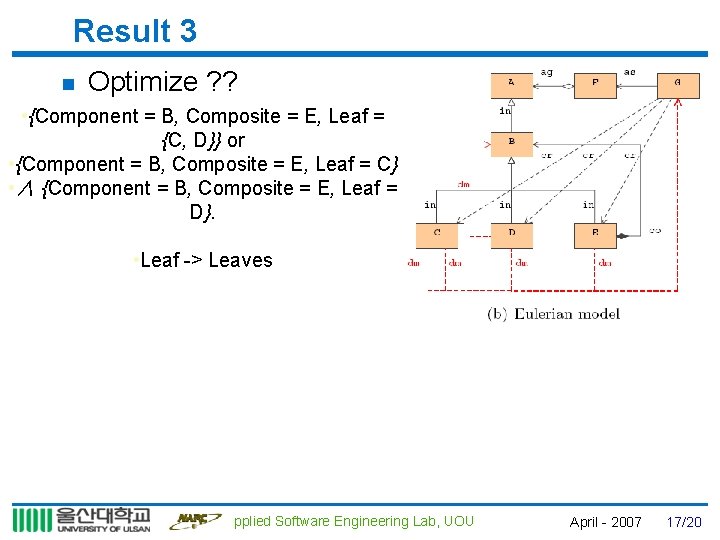
Result 3 n Optimize ? ? • {Component = B, Composite = E, Leaf = {C, D}} or • {Component = B, Composite = E, Leaf = C} • ∧ {Component = B, Composite = E, Leaf = D}. • Leaf -> Leaves Applied Software Engineering Lab, UOU April - 2007 17/20
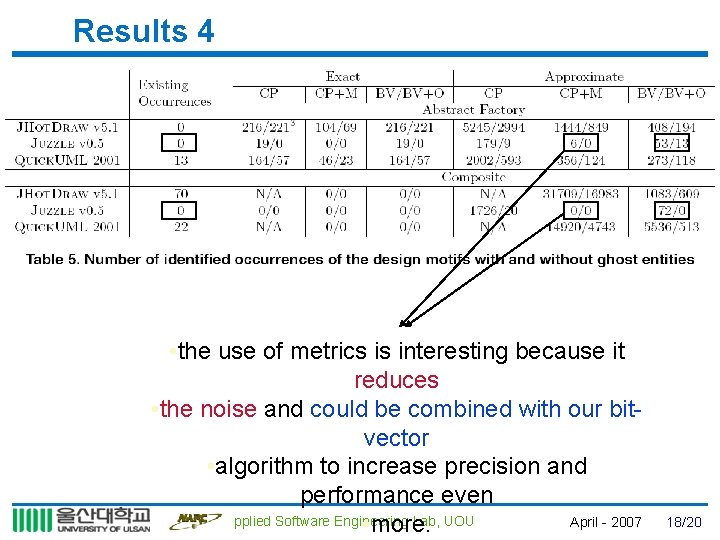
Results 4 • the use of metrics is interesting because it reduces • the noise and could be combined with our bitvector • algorithm to increase precision and performance even Applied Software Engineering Lab, UOU April - 2007 • more. 18/20
Conclusion n We presented an adaptation of bio-informatics bitvector algorithms to the software maintenance problem of design pattern identification. n We implemented our approach and showed its efficiency on three small-to-medium size programs and the quality of its results, including its approximation capabilities. n Some design patterns also specify what must not be found. For example, the Adaptee role in the Adapter design motif must not know the Adapter role. n As future work l l string representation -> Build automatically. string representation -> Search their Applied Software Lab, UOU April - 2007 emplacements in the. Engineering program. 19/20
4배수 만들기 페이지 Applied Software Engineering Lab, UOU April - 2007 20/20
- Slides: 20