Effective Security at the Core Ashraf Sheet Infoblox

Effective Security at the Core Ashraf Sheet | Infoblox Regional Manager MEA 1 1 || ©© 2016 Infoblox Inc. All Rights 2013 Infoblox Inc. All Reserved. Rights Reserved.
Agenda • Security Landscape and the Disconnect • Security Challenges • Operational Challenges • DNS: The Malware Control Plane • DNS Attacks Affecting Availability • Infoblox Security at the Core • Summary and Next Steps 2 2 || ©© 2016 Infoblox Inc. All Rights 2013 Infoblox Inc. All Reserved. Rights Reserved.

Today’s Security Landscape 400+ VENDORS 3 3 || ©© 2016 Infoblox Inc. All Rights 2013 Infoblox Inc. All Reserved. Rights Reserved.

The Disconnect. . Security You Want 4 4 || ©© 2016 Infoblox Inc. All Rights 2013 Infoblox Inc. All Reserved. Rights Reserved. Security You Often Get
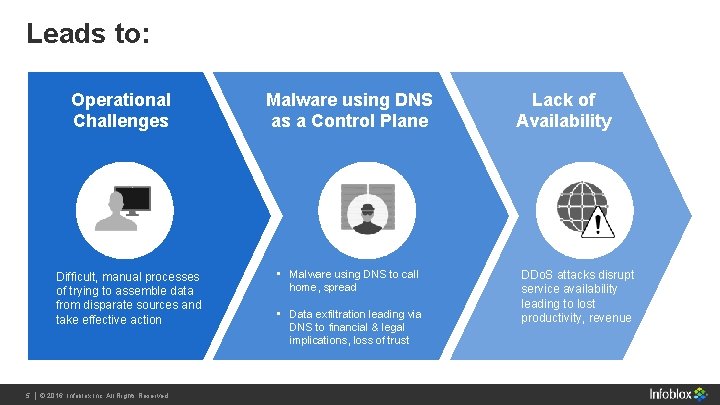
Leads to: Operational Challenges Difficult, manual processes of trying to assemble data from disparate sources and take effective action 5 5 || ©© 2016 Infoblox Inc. All Rights 2013 Infoblox Inc. All Reserved. Rights Reserved. Malware using DNS as a Control Plane • Malware using DNS to call home, spread • Data exfiltration leading via DNS to financial & legal implications, loss of trust Lack of Availability DDo. S attacks disrupt service availability leading to lost productivity, revenue

Operational Challenges Silos Lack of Visibility Lack of Context Lack of Automation These challenges lead to rising costs of security operations, in addition to a poor security posture 6 6 || ©© 2016 Infoblox Inc. All Rights 2013 Infoblox Inc. All Reserved. Rights Reserved.
Gartner’s View on Silos between network, edge, endpoint and data security systems and processes can restrict an organization’s ability to prevent, detect and respond to advanced attacks. Best Practices for Detecting and Mitigating Advanced Threats, 2016 Update 29 March 2016 7 7 || ©© 2016 Infoblox Inc. All Rights 2013 Infoblox Inc. All Reserved. Rights Reserved.

DNS The Malware Control Plane 8 8 || ©© 2016 Infoblox Inc. All Rights 2013 Infoblox Inc. All Reserved. Rights Reserved.
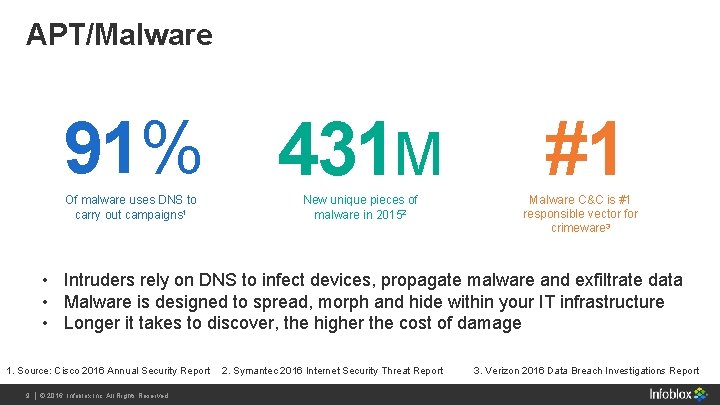
APT/Malware 91% 431 M Of malware uses DNS to carry out campaigns 1 New unique pieces of malware in 20152 #1 Malware C&C is #1 responsible vector for crimeware 3 • Intruders rely on DNS to infect devices, propagate malware and exfiltrate data • Malware is designed to spread, morph and hide within your IT infrastructure • Longer it takes to discover, the higher the cost of damage 1. Source: Cisco 2016 Annual Security Report 9 9 || ©© 2016 Infoblox Inc. All Rights 2013 Infoblox Inc. All Reserved. Rights Reserved. 2. Symantec 2016 Internet Security Threat Report 3. Verizon 2016 Data Breach Investigations Report
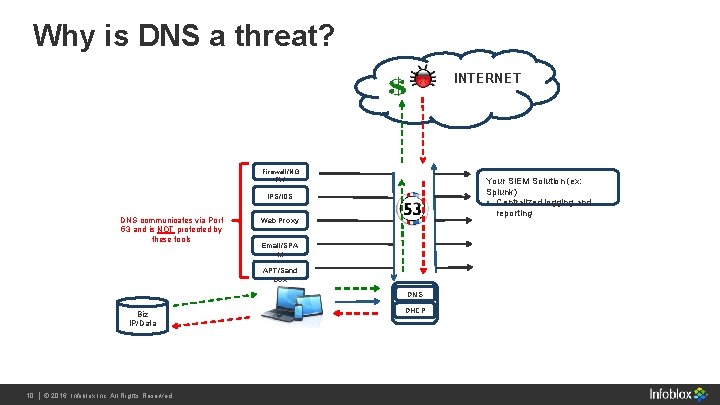
Why is DNS a threat? INTERNET Firewall/NG FW Your SIEM Solution (ex: Splunk) • Centralized logging and reporting IPS/IDS DNS communicates via Port 53 and is NOT protected by these tools Web Proxy Email/SPA M APT/Sand box DNS Biz IP/Data 10 Infoblox Inc. All Rights 10 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved. DHCP
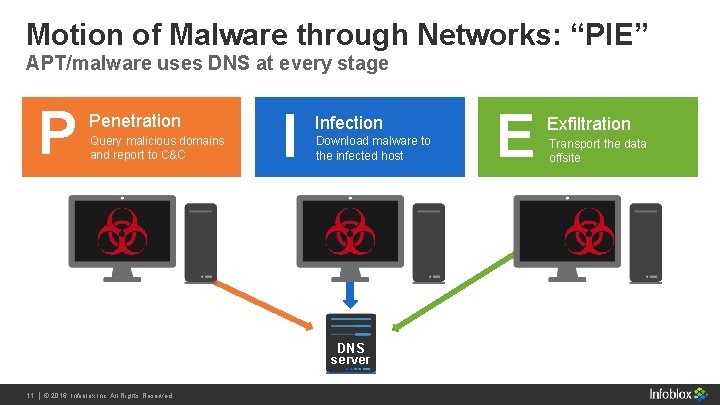
Motion of Malware through Networks: “PIE” APT/malware uses DNS at every stage P Penetration Query malicious domains and report to C&C I Infection Download malware to the infected host DNS server 11 Infoblox Inc. All Rights 11 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved. E Exfiltration Transport the data offsite
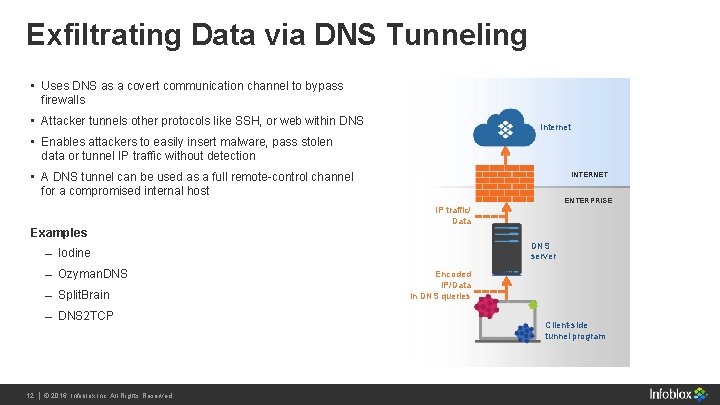
Exfiltrating Data via DNS Tunneling • Uses DNS as a covert communication channel to bypass firewalls • Attacker tunnels other protocols like SSH, or web within DNS Internet • Enables attackers to easily insert malware, pass stolen data or tunnel IP traffic without detection • A DNS tunnel can be used as a full remote-control channel for a compromised internal host INTERNET ENTERPRISE IP traffic/ Data Examples DNS server Iodine Ozyman. DNS Split. Brain DNS 2 TCP 12 Infoblox Inc. All Rights 12 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved. Encoded IP/Data in DNS queries Client-side tunnel program
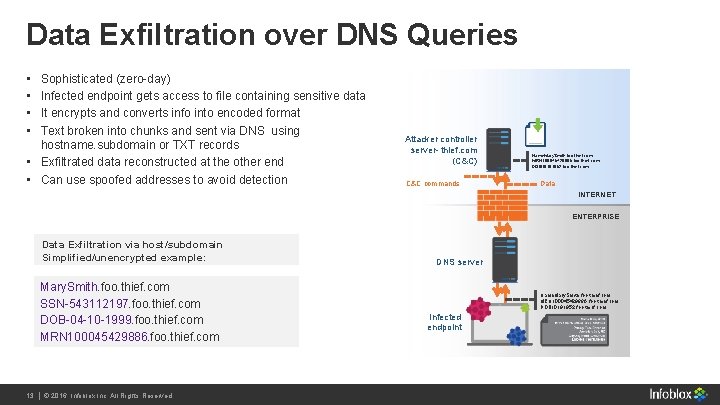
Data Exfiltration over DNS Queries • • Sophisticated (zero-day) Infected endpoint gets access to file containing sensitive data It encrypts and converts info into encoded format Text broken into chunks and sent via DNS using hostname. subdomain or TXT records • Exfiltrated data reconstructed at the other end • Can use spoofed addresses to avoid detection Attacker controller server- thief. com (C&C) C&C commands Name. Mary. Smith. foo. thief. com MRN 100045429886. foo. thief. com DOB 10191952. foo. thief. com Data INTERNET ENTERPRISE Data Exfiltration via host/subdomain Simplified/unencrypted example: Mary. Smith. foo. thief. com SSN-543112197. foo. thief. com DOB-04 -10 -1999. foo. thief. com MRN 100045429886. foo. thief. com 13 Infoblox Inc. All Rights 13 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved. DNS server Name. Mary. Smith. foo. thief. com MRN 100045429886. foo. thief. com DOB 10191952. foo. thief. com Infected endpoint

DNS Attacks Affecting Availability 14 Infoblox Inc. All Rights 14 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved.
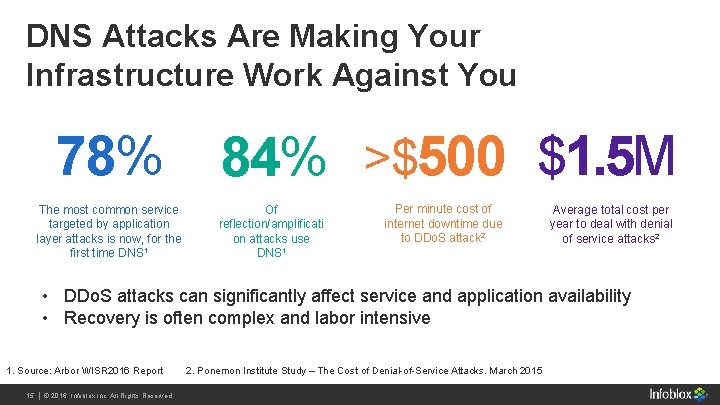
DNS Attacks Are Making Your Infrastructure Work Against You 84% >$500 $1. 5 M 78% The most common service targeted by application layer attacks is now, for the first time DNS 1 Of reflection/amplificati on attacks use DNS 1 Per minute cost of internet downtime due to DDo. S attack 2 Average total cost per year to deal with denial of service attacks 2 • DDo. S attacks can significantly affect service and application availability • Recovery is often complex and labor intensive 1. Source: Arbor WISR 2016 Report 2. Ponemon Institute Study – The Cost of Denial-of-Service Attacks. March 2015 15 Infoblox Inc. All Rights 15 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved.

DNS DDOS Latest Attacks 16 Infoblox Inc. All Rights 16 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved.
Infoblox Security at the CORE 17 Infoblox Inc. All Rights 17 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved.

Ideal Security Solution Reduced risk from malicious activity Tight ecosystem integrations and APIs to share rich network data with existing security systems Automatic blocking of malicious activities at network control points (DNS) 18 Infoblox Inc. All Rights 18 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved. An Ideal Solution Provides the Following Business and network context to help in prioritization of threats Advanced threat intelligence with context Enhanced visibility of threats across diverse infrastructure – physical, virtual or cloud
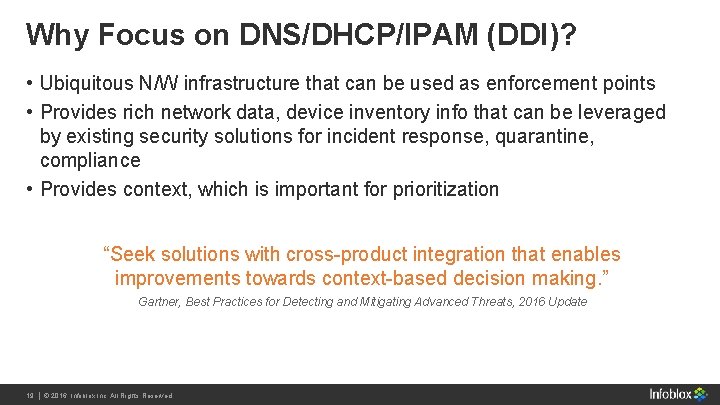
Why Focus on DNS/DHCP/IPAM (DDI)? • Ubiquitous N/W infrastructure that can be used as enforcement points • Provides rich network data, device inventory info that can be leveraged by existing security solutions for incident response, quarantine, compliance • Provides context, which is important for prioritization “Seek solutions with cross-product integration that enables improvements towards context-based decision making. ” Gartner, Best Practices for Detecting and Mitigating Advanced Threats, 2016 Update 19 Infoblox Inc. All Rights 19 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved.
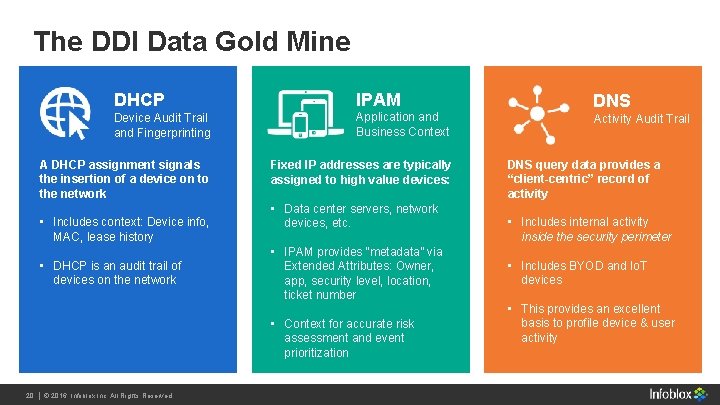
The DDI Data Gold Mine DHCP IPAM Device Audit Trail and Fingerprinting Application and Business Context A DHCP assignment signals the insertion of a device on to the network Fixed IP addresses are typically assigned to high value devices: • Includes context: Device info, MAC, lease history • DHCP is an audit trail of devices on the network • Data center servers, network devices, etc. • IPAM provides “metadata” via Extended Attributes: Owner, app, security level, location, ticket number • Context for accurate risk assessment and event prioritization 20 Infoblox Inc. All Rights 20 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved. DNS Activity Audit Trail DNS query data provides a “client-centric” record of activity • Includes internal activity inside the security perimeter • Includes BYOD and Io. T devices • This provides an excellent basis to profile device & user activity
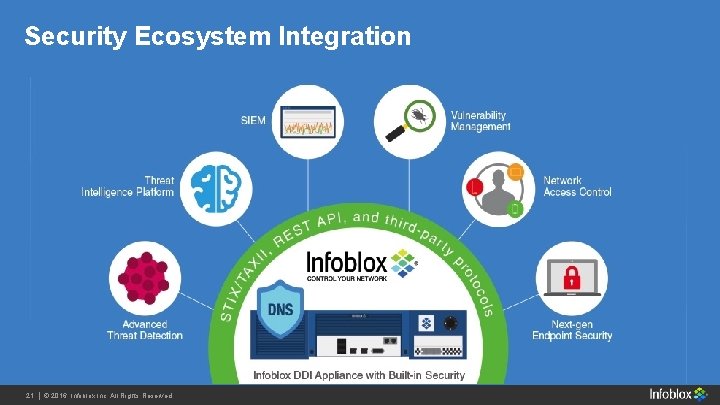
Security Ecosystem Integration 21 Infoblox Inc. All Rights 21 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved.
• Address security challenges starting at the CORE Summary Key Takeaways 22 Infoblox Inc. All Rights 22 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved. • Infoblox Security Solutions provide: DNS Data Exfiltration Prevention Malware Containment & Control DNS Infrastructure Protection Threat Intel with Active. Trust
Next Steps Path to Engagement 23 Infoblox Inc. All Rights 23 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved. • Security Assessment (PCAP) • DNS Data Exfiltration Assessment

Q&A 24 Infoblox Inc. All Rights 24 | | ©© 2016 2013 Infoblox Inc. All Reserved. Rights Reserved.
- Slides: 24