EECS 122 Encoding Framing Error Detection and Recovery
- Slides: 36
EECS 122: Encoding, Framing, Error Detection and Recovery Computer Science Division Department of Electrical Engineering and Computer Sciences University of California, Berkeley, CA 94720 -1776 EECS 122 - UCB Katz, Stoica F 04
Overview Ø § § Encoding Framing Error detection & correction Katz, Stoica F 04 2
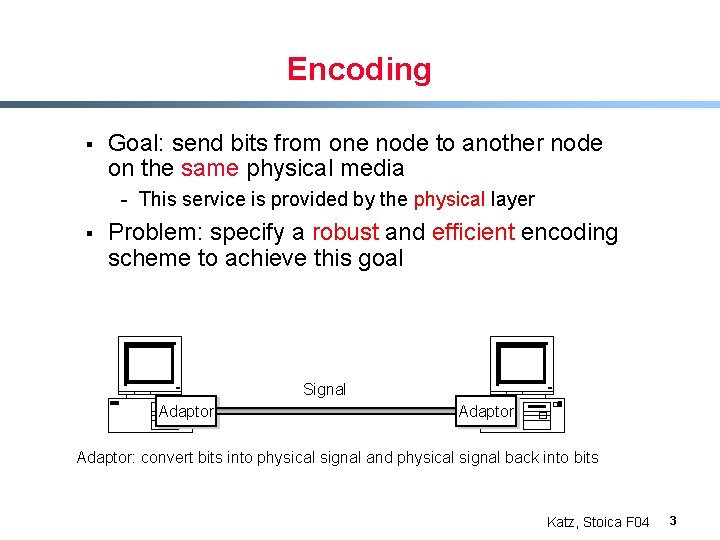
Encoding § Goal: send bits from one node to another node on the same physical media - This service is provided by the physical layer § Problem: specify a robust and efficient encoding scheme to achieve this goal Signal Adaptor: convert bits into physical signal and physical signal back into bits Katz, Stoica F 04 3
Assumptions § § Use two discrete signals, high and low, to encode 0 and 1 The transmission is synchronous, i. e. , there is a clock used to sample the signal - In general, the duration of one bit is equal to one or two clock ticks Katz, Stoica F 04 4
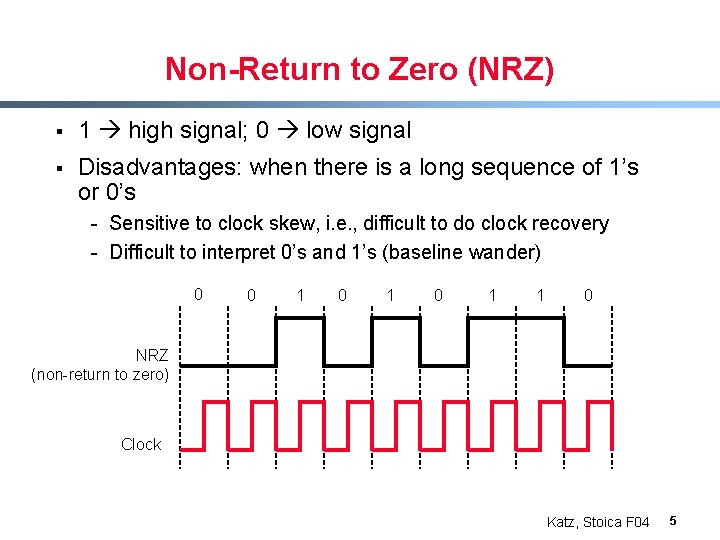
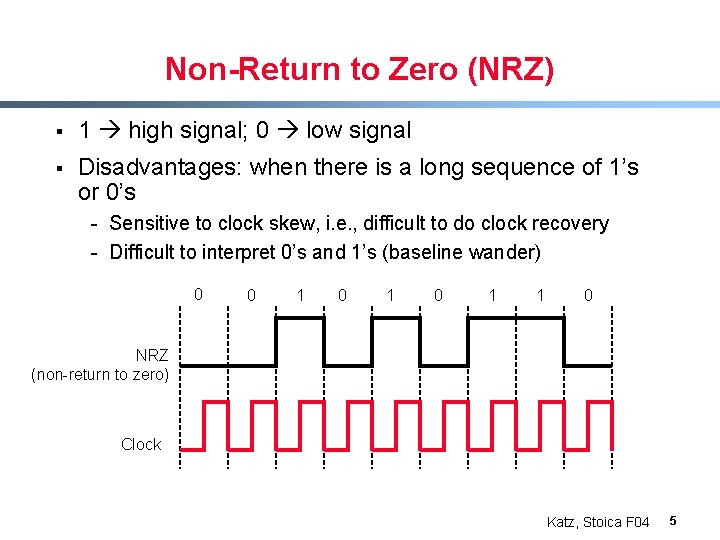
Non-Return to Zero (NRZ) § 1 high signal; 0 low signal § Disadvantages: when there is a long sequence of 1’s or 0’s - Sensitive to clock skew, i. e. , difficult to do clock recovery - Difficult to interpret 0’s and 1’s (baseline wander) 0 0 1 0 1 1 0 NRZ (non-return to zero) Clock Katz, Stoica F 04 5
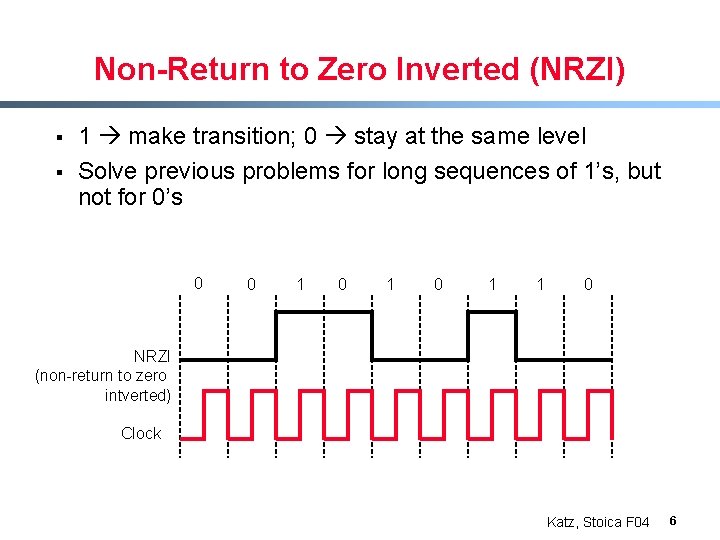
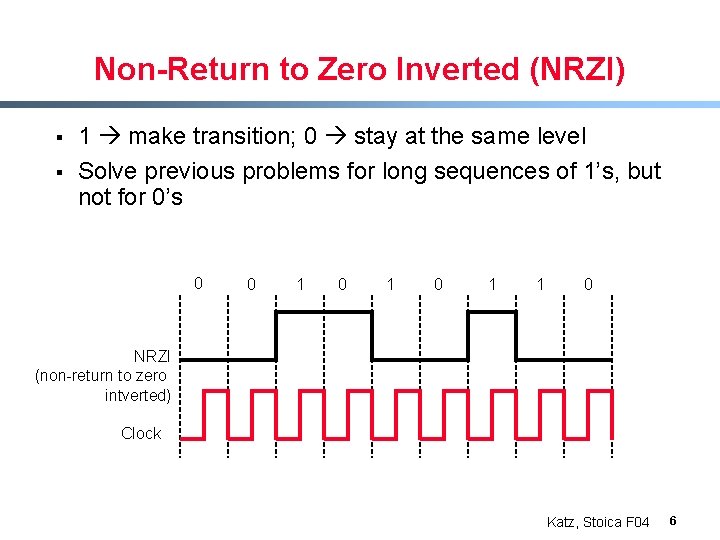
Non-Return to Zero Inverted (NRZI) § § 1 make transition; 0 stay at the same level Solve previous problems for long sequences of 1’s, but not for 0’s 0 0 1 0 1 1 0 NRZI (non-return to zero intverted) Clock Katz, Stoica F 04 6
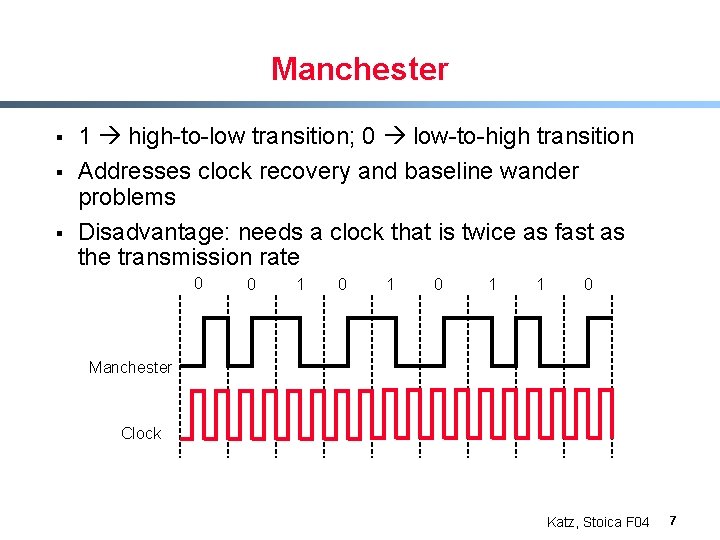
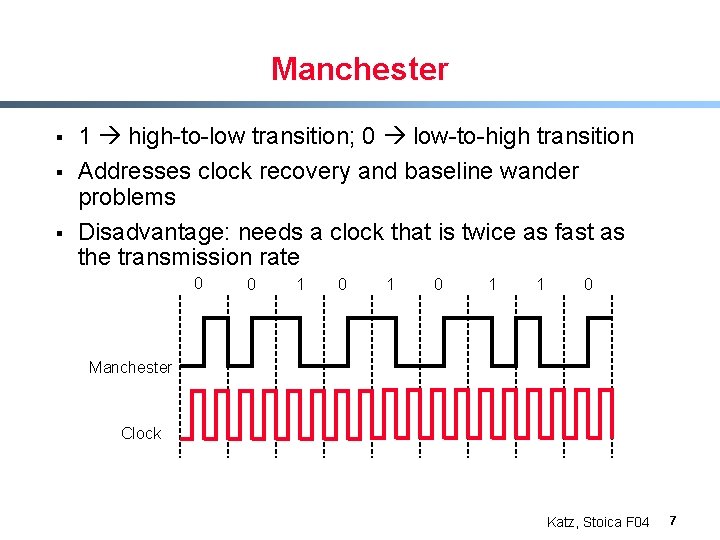
Manchester § § § 1 high-to-low transition; 0 low-to-high transition Addresses clock recovery and baseline wander problems Disadvantage: needs a clock that is twice as fast as the transmission rate 0 0 1 0 1 1 0 Manchester Clock Katz, Stoica F 04 7
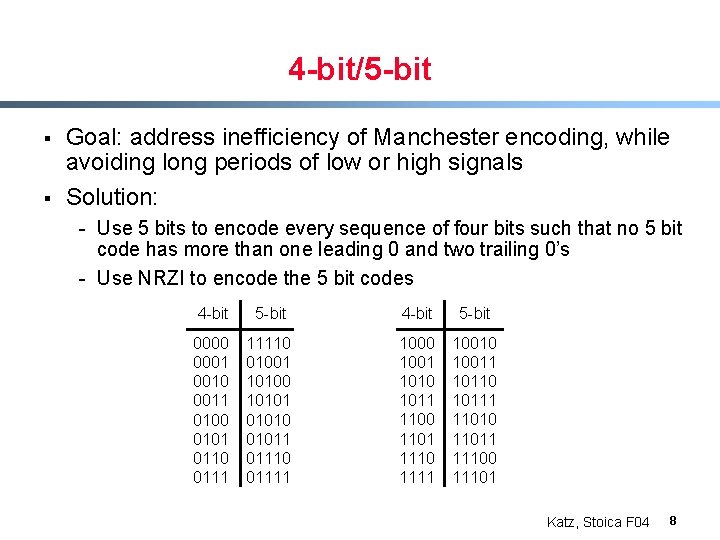
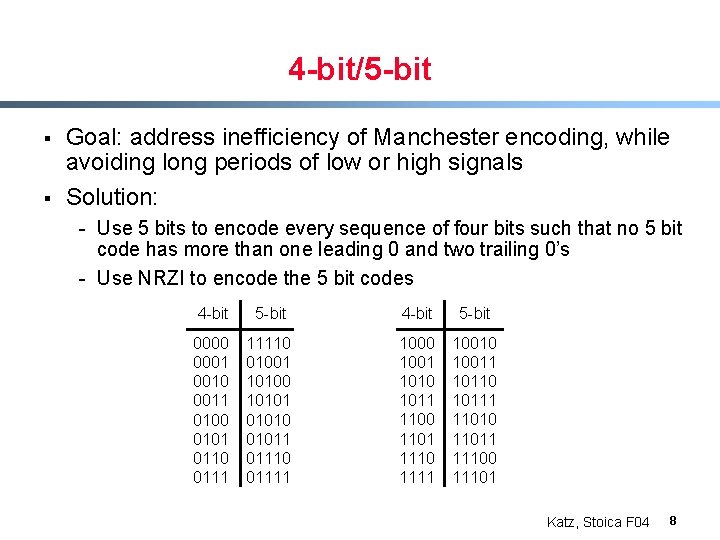
4 -bit/5 -bit § § Goal: address inefficiency of Manchester encoding, while avoiding long periods of low or high signals Solution: - Use 5 bits to encode every sequence of four bits such that no 5 bit code has more than one leading 0 and two trailing 0’s - Use NRZI to encode the 5 bit codes 4 -bit 5 -bit 0000 0001 0010 0011 0100 0101 0110 0111 11110 01001 10100 101010 01011 01110 01111 1000 1001 1010 1011 1100 1101 1110 1111 10010 10011 10110 10111 11010 11011 11100 11101 Katz, Stoica F 04 8
Overview § Ø § Encoding Framing Error detection & Correction Katz, Stoica F 04 9
Framing § Goal: send a block of bits (frames) between nodes connected on the same physical media - This service is provided by the data link layer § § Use a special byte (bit sequence) to mark the beginning (and the end) of the frame Problem: what happens if this sequence appears in the data payload? Katz, Stoica F 04 10
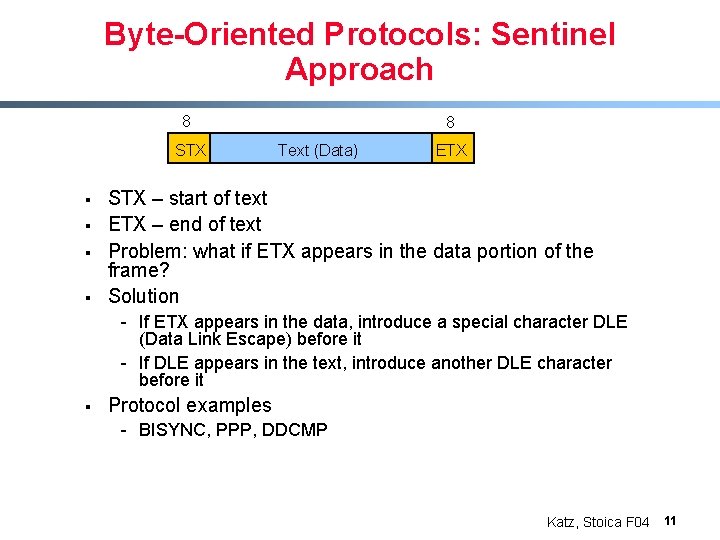
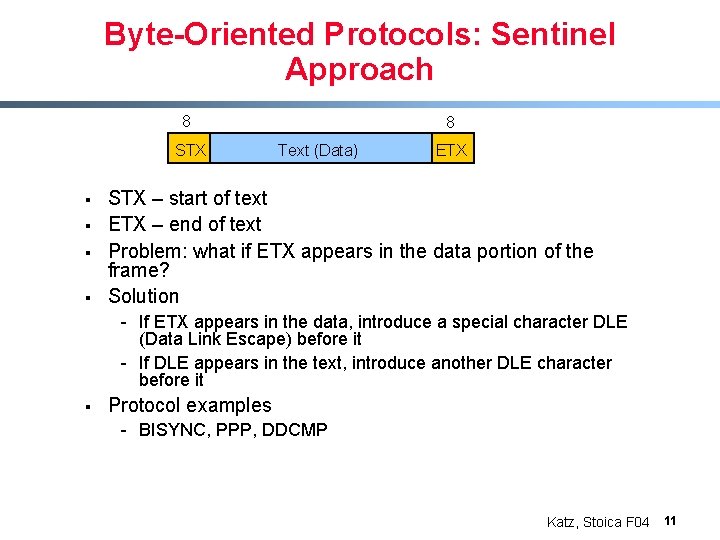
Byte-Oriented Protocols: Sentinel Approach 8 STX § § 8 Text (Data) ETX STX – start of text ETX – end of text Problem: what if ETX appears in the data portion of the frame? Solution - If ETX appears in the data, introduce a special character DLE (Data Link Escape) before it - If DLE appears in the text, introduce another DLE character before it § Protocol examples - BISYNC, PPP, DDCMP Katz, Stoica F 04 11
Byte-Oriented Protocols: Byte Counting Approach § Sender: - Insert the length of the data (in bytes) at the beginning of the frame, i. e. , in the frame header § Receiver: - Extract this length and decrement it every time a byte is read; when this counter becomes zero, we are done Katz, Stoica F 04 12
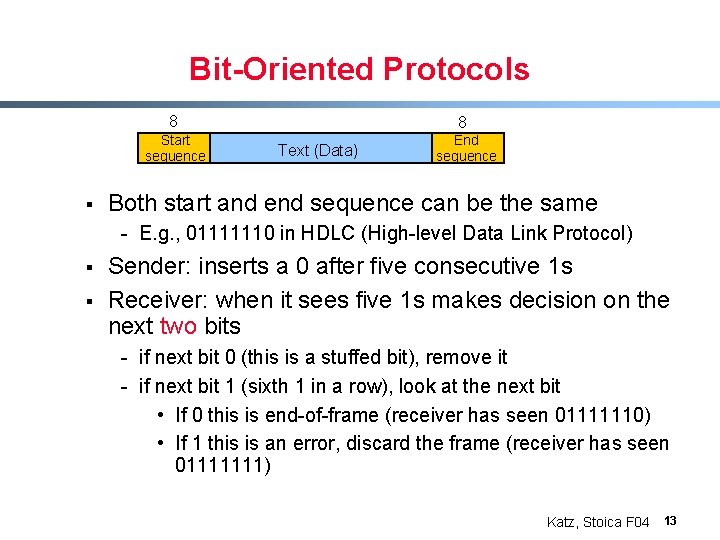
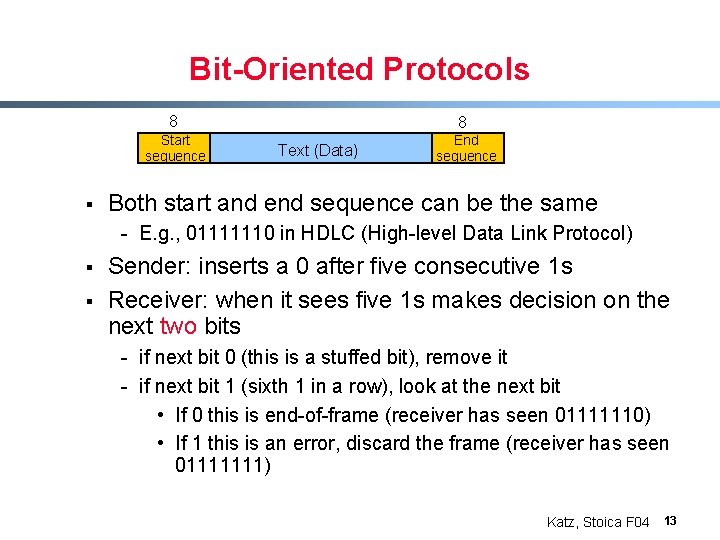
Bit-Oriented Protocols 8 Start sequence § 8 Text (Data) End sequence Both start and end sequence can be the same - E. g. , 01111110 in HDLC (High-level Data Link Protocol) § § Sender: inserts a 0 after five consecutive 1 s Receiver: when it sees five 1 s makes decision on the next two bits - if next bit 0 (this is a stuffed bit), remove it - if next bit 1 (sixth 1 in a row), look at the next bit • If 0 this is end-of-frame (receiver has seen 01111110) • If 1 this is an error, discard the frame (receiver has seen 01111111) Katz, Stoica F 04 13
Clock-Based Framing (SONET) § § SONET (Synchronous Optical NETwork) Example: SONET ST-1: 51. 84 Mbps Katz, Stoica F 04 14
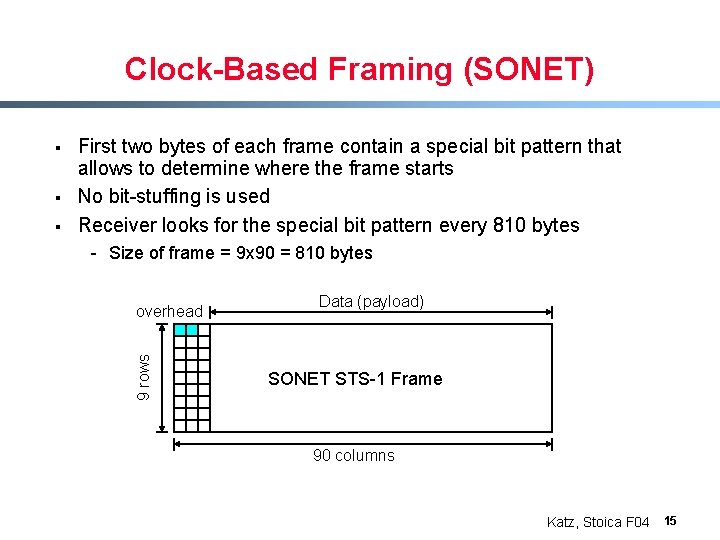
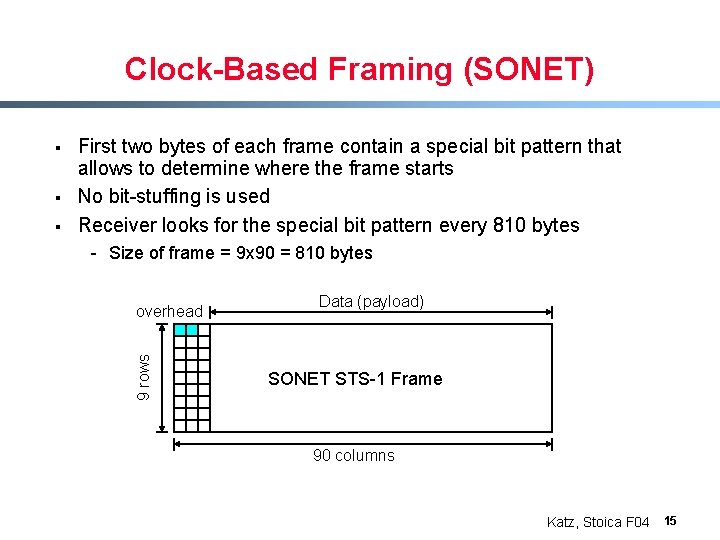
Clock-Based Framing (SONET) § § First two bytes of each frame contain a special bit pattern that allows to determine where the frame starts No bit-stuffing is used Receiver looks for the special bit pattern every 810 bytes - Size of frame = 9 x 90 = 810 bytes overhead 9 rows § Data (payload) SONET STS-1 Frame 90 columns Katz, Stoica F 04 15
Clock-Based Framing (SONET) § Details: - Overhead bytes are encoded using NRZ - To avoid long sequences of 0’s or 1’s the payload is XOR-ed with a special 127 -bit patter with many transitions from 1 to 0 - Duration of a frame is 51. 84 usec (51. 84 Mbps for STS-1) Katz, Stoica F 04 16
High Level View § § Goal: transmit correct information Problem: bits can get corrupted - Electrical interference, thermal noise § Solution - Detect errors - Recover from errors • Correct errors • Retransmission (already done this!) Katz, Stoica F 04 17
Overview § § Ø Encoding Framing Error detection & Correction Katz, Stoica F 04 18
Error Detection (and Correction) § § § Problem: detect bit errors in packets (frames) Solution: add extra bits to each packet Goals: - Reduce overhead, i. e. , reduce the number of added bits - Increase the number and the type of bit error patterns that can be detected § Examples: - Two-dimensional parity - Checksum - Cyclic Redundancy Check (CRC) Katz, Stoica F 04 19
Overview § § Ø Encoding Framing Error detection & Correction Ø Two-dimensional parity - Checksum - Cyclic Redundancy Check (CRC) Katz, Stoica F 04 20
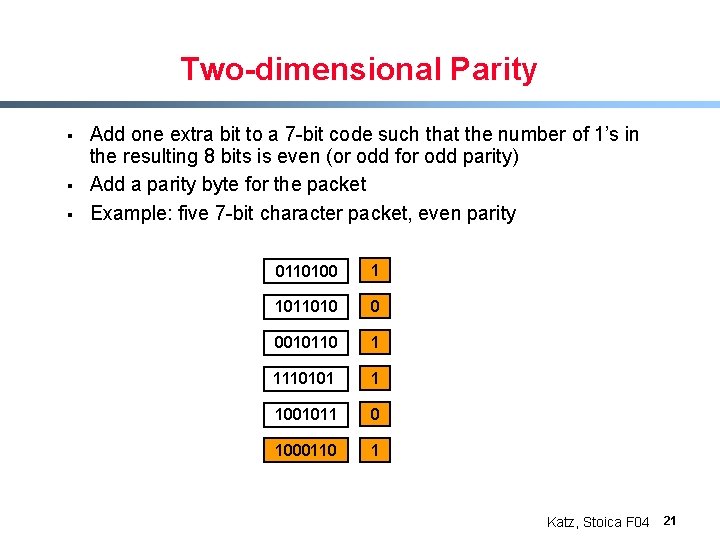
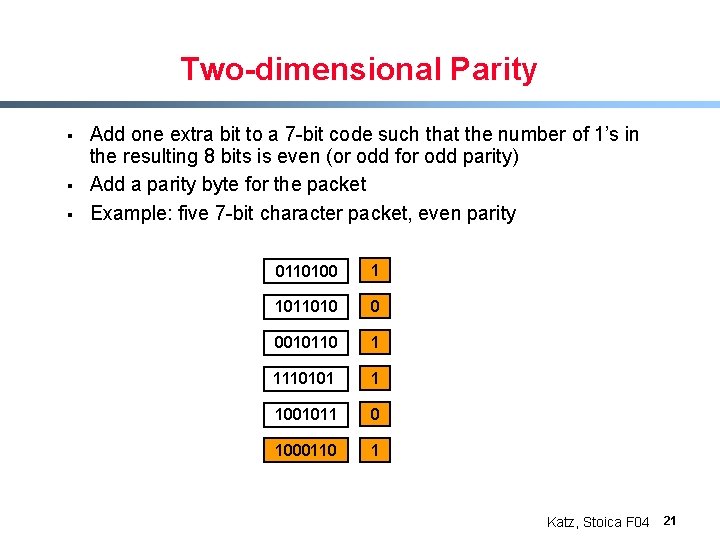
Two-dimensional Parity § § § Add one extra bit to a 7 -bit code such that the number of 1’s in the resulting 8 bits is even (or odd for odd parity) Add a parity byte for the packet Example: five 7 -bit character packet, even parity 0110100 1 1011010 0 0010110 1 1110101 1 1001011 0 1000110 1 Katz, Stoica F 04 21
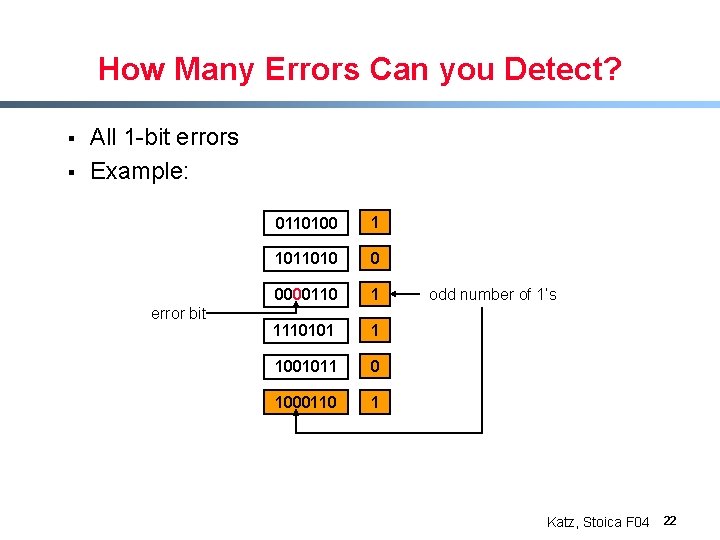
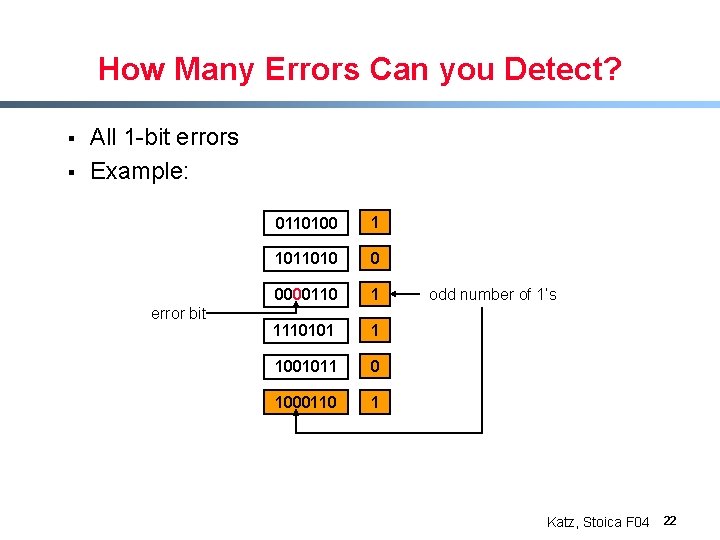
How Many Errors Can you Detect? § § All 1 -bit errors Example: error bit 0110100 1 1011010 0 0000110 1 1110101 1 1001011 0 1000110 1 odd number of 1’s Katz, Stoica F 04 22
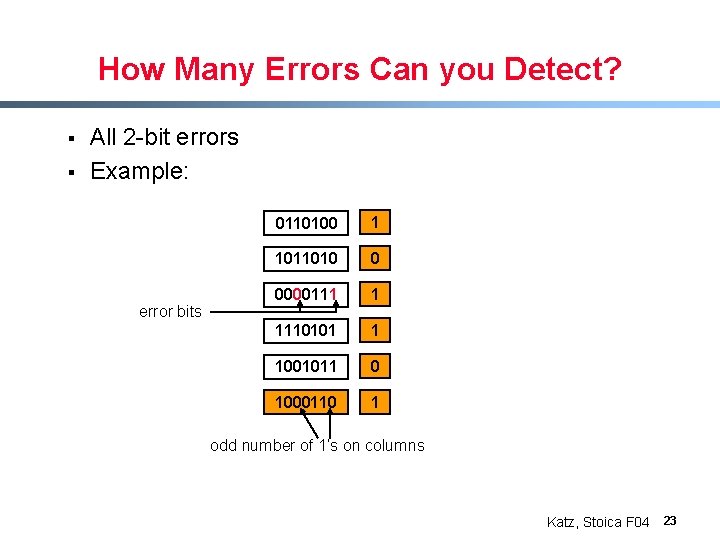
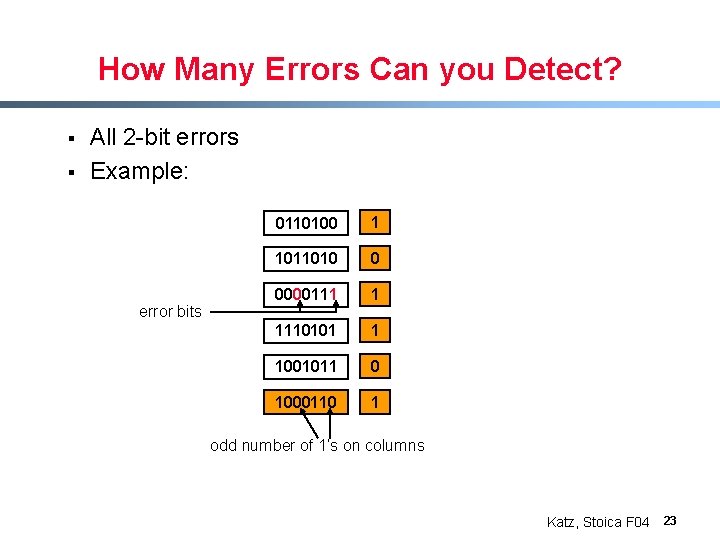
How Many Errors Can you Detect? § § All 2 -bit errors Example: error bits 0110100 1 1011010 0 0000111 1 1110101 1 1001011 0 1000110 1 odd number of 1’s on columns Katz, Stoica F 04 23
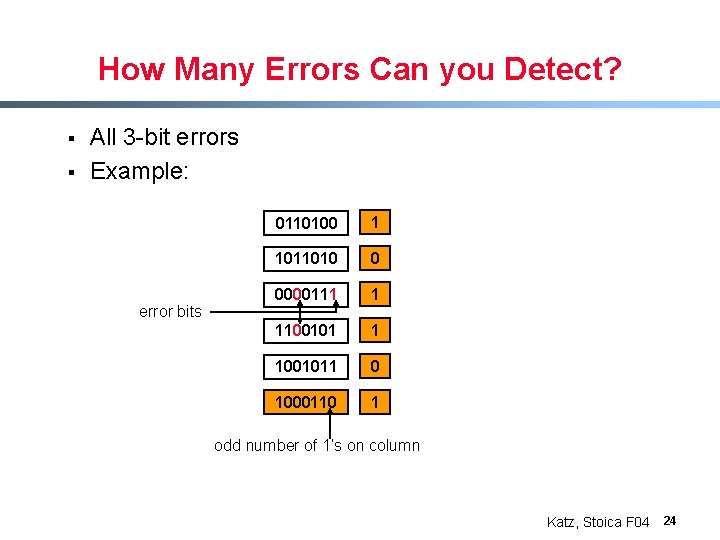
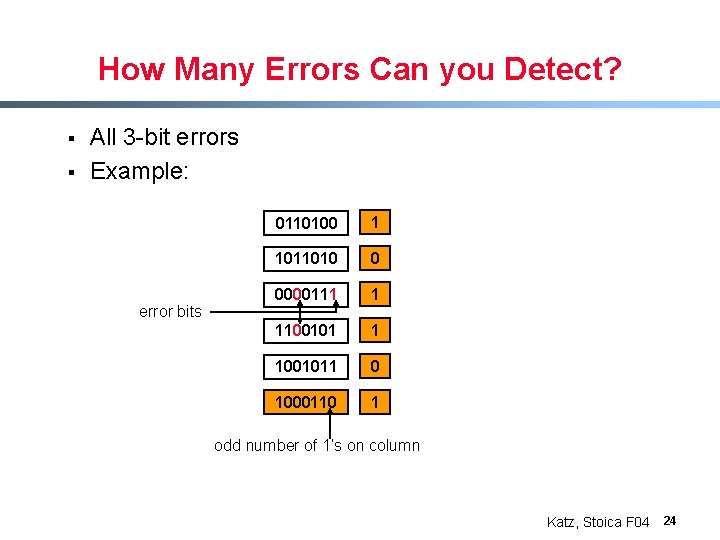
How Many Errors Can you Detect? § § All 3 -bit errors Example: error bits 0110100 1 1011010 0 0000111 1 1100101 1 1001011 0 1000110 1 odd number of 1’s on column Katz, Stoica F 04 24
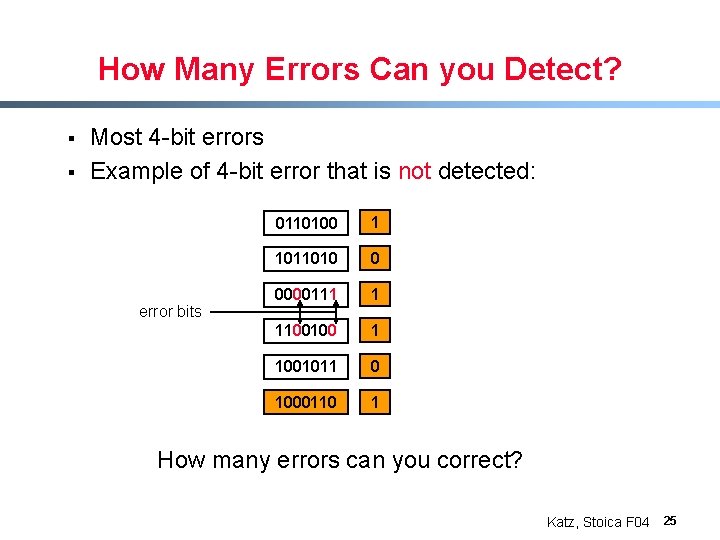
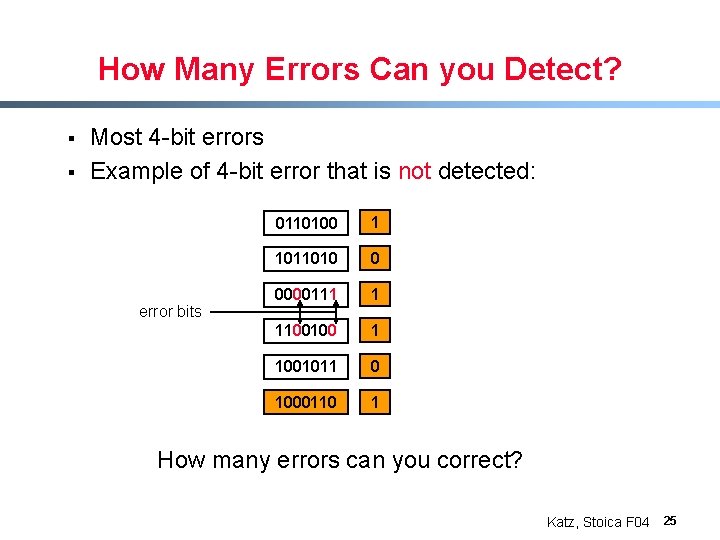
How Many Errors Can you Detect? § § Most 4 -bit errors Example of 4 -bit error that is not detected: error bits 0110100 1 1011010 0 0000111 1 1100100 1 1001011 0 1000110 1 How many errors can you correct? Katz, Stoica F 04 25
Overview § § Ø Encoding Framing Error detection & Correction - Two-dimensional parity Ø Checksum - Cyclic Redundancy Check (CRC) Katz, Stoica F 04 26
Checksum § § Sender: add all words of a packet and append the result (checksum) to the packet Receiver: add all words of a packet and compare the result with the checksum Can detect all 1 -bit errors Example: Internet checksum - Use 1’s complement addition Katz, Stoica F 04 27
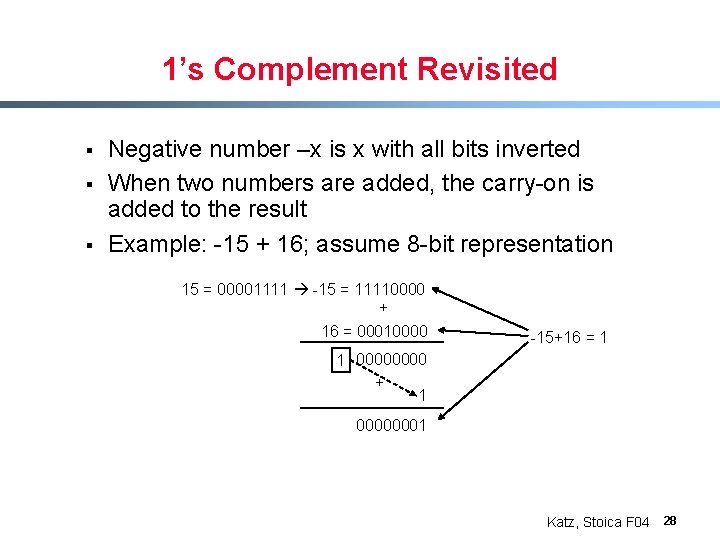
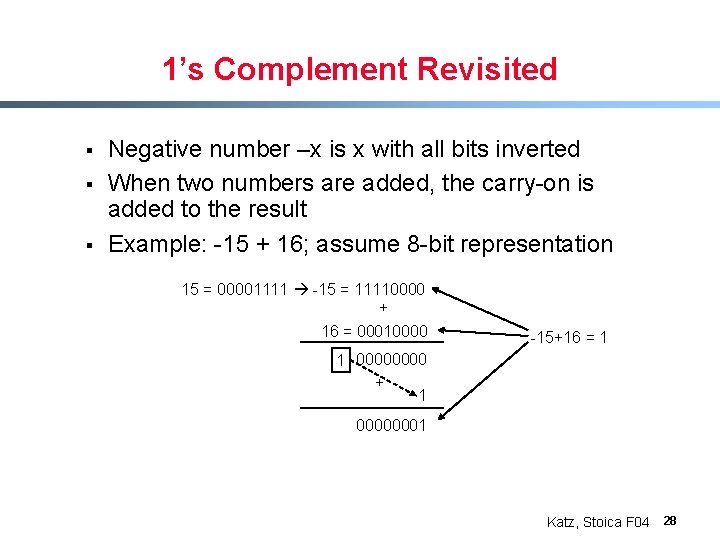
1’s Complement Revisited § § § Negative number –x is x with all bits inverted When two numbers are added, the carry-on is added to the result Example: -15 + 16; assume 8 -bit representation 15 = 00001111 -15 = 11110000 + 16 = 00010000 -15+16 = 1 1 0000 + 1 00000001 Katz, Stoica F 04 28
Overview § § Ø Encoding Framing Error detection & Correction - Two-dimensional parity - Checksum Ø Cyclic Redundancy Check (CRC) Katz, Stoica F 04 29
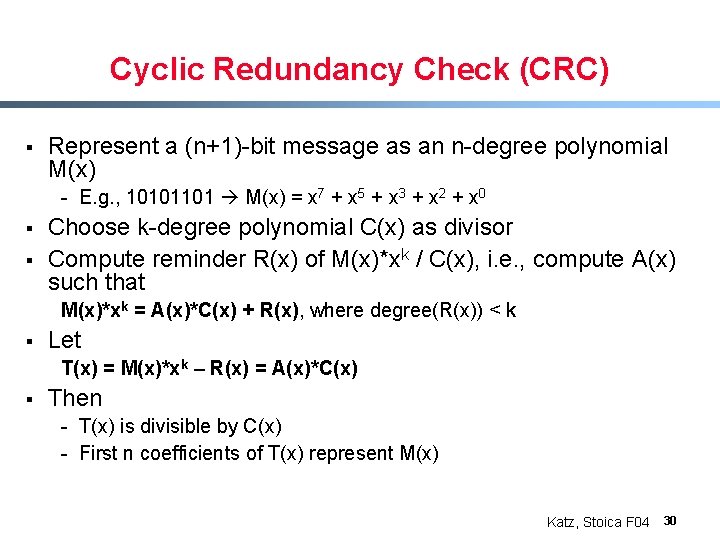
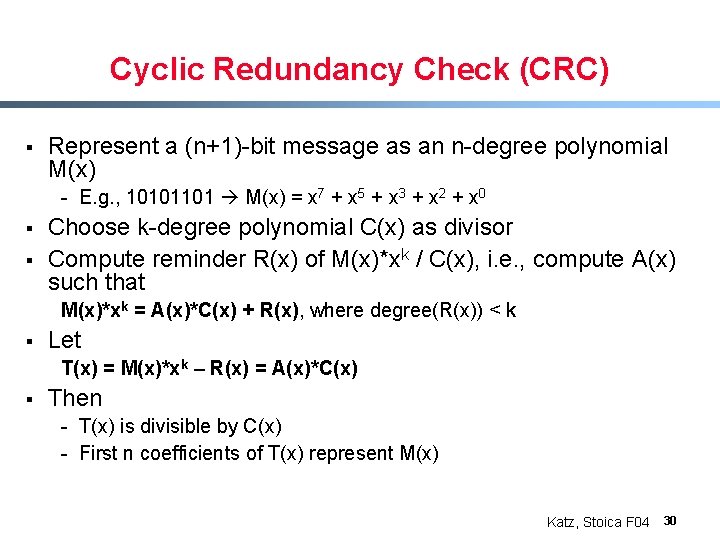
Cyclic Redundancy Check (CRC) § Represent a (n+1)-bit message as an n-degree polynomial M(x) - E. g. , 10101101 M(x) = x 7 + x 5 + x 3 + x 2 + x 0 § § Choose k-degree polynomial C(x) as divisor Compute reminder R(x) of M(x)*xk / C(x), i. e. , compute A(x) such that M(x)*xk = A(x)*C(x) + R(x), where degree(R(x)) < k § Let T(x) = M(x)*xk – R(x) = A(x)*C(x) § Then - T(x) is divisible by C(x) - First n coefficients of T(x) represent M(x) Katz, Stoica F 04 30
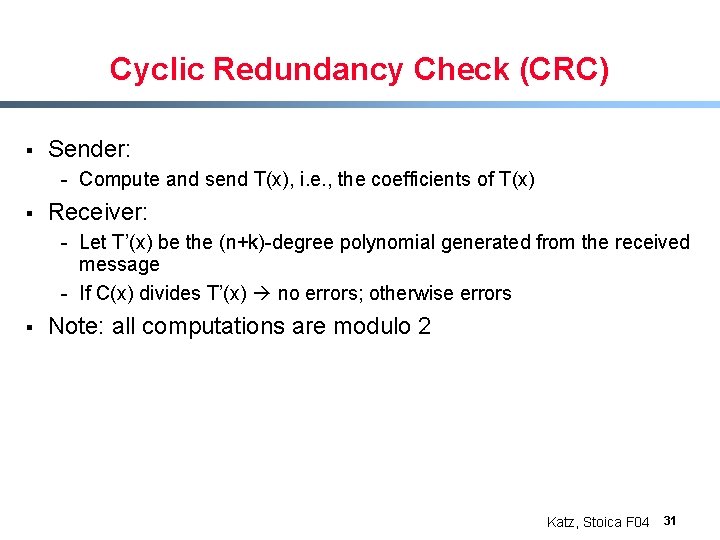
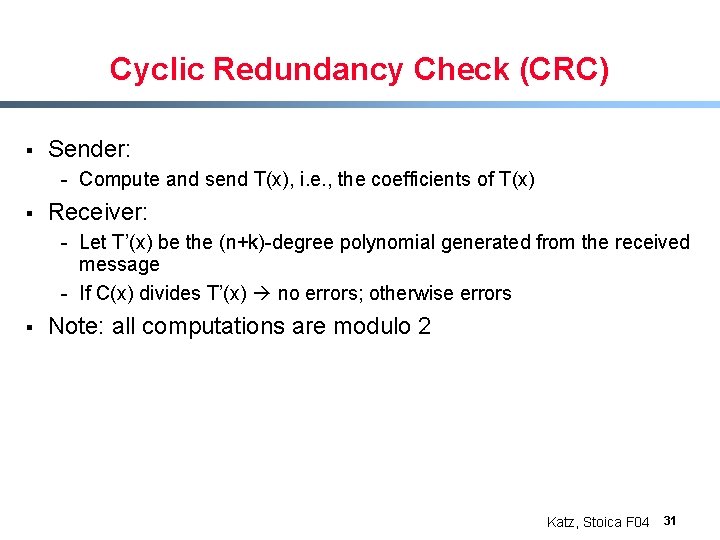
Cyclic Redundancy Check (CRC) § Sender: - Compute and send T(x), i. e. , the coefficients of T(x) § Receiver: - Let T’(x) be the (n+k)-degree polynomial generated from the received message - If C(x) divides T’(x) no errors; otherwise errors § Note: all computations are modulo 2 Katz, Stoica F 04 31
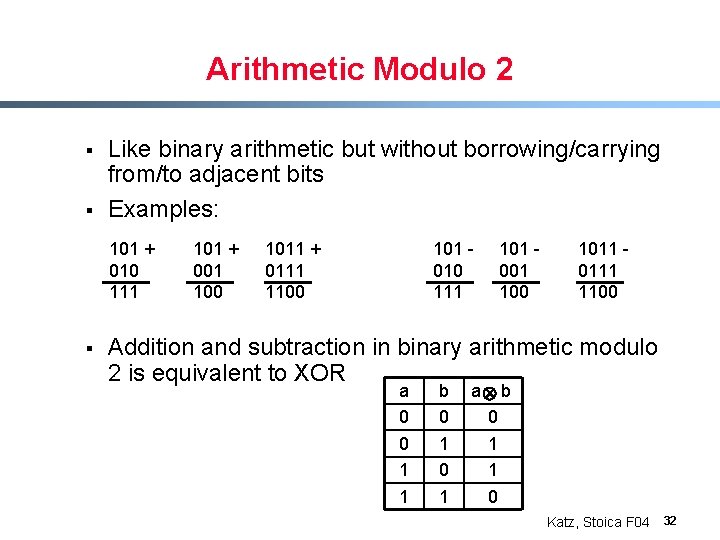
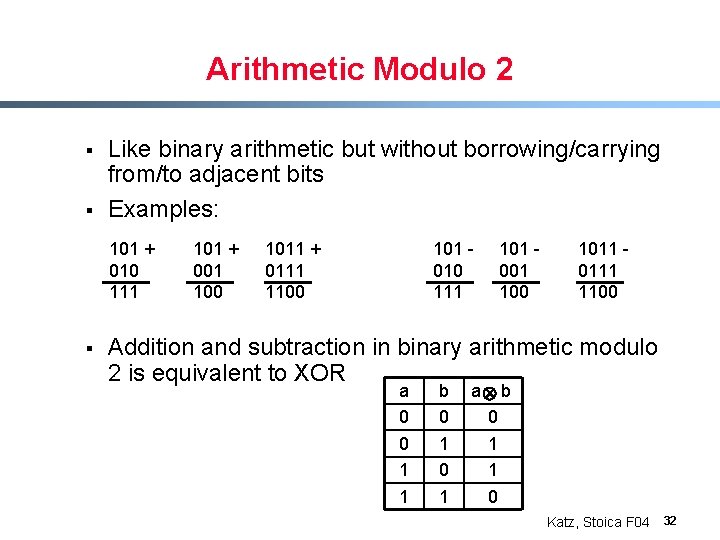
Arithmetic Modulo 2 § § Like binary arithmetic but without borrowing/carrying from/to adjacent bits Examples: 101 + 010 111 § 101 + 001 100 1011 + 0111 1100 101 010 111 101 001 100 1011 0111 1100 Addition and subtraction in binary arithmetic modulo 2 is equivalent to XOR a 0 0 1 1 b 0 1 a b 0 1 1 0 Katz, Stoica F 04 32
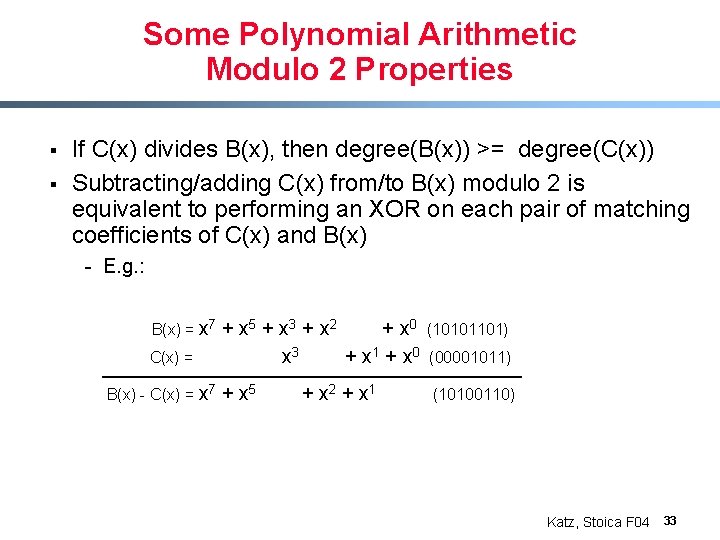
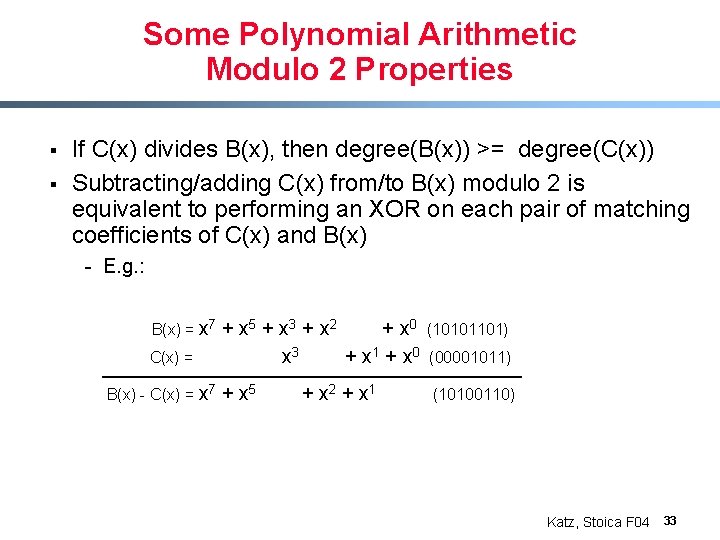
Some Polynomial Arithmetic Modulo 2 Properties § § If C(x) divides B(x), then degree(B(x)) >= degree(C(x)) Subtracting/adding C(x) from/to B(x) modulo 2 is equivalent to performing an XOR on each pair of matching coefficients of C(x) and B(x) - E. g. : B(x) = x 7 C(x) = B(x) - C(x) = x 7 + x 5 + x 3 + x 2 + x 0 x 3 + x 1 + x 0 + x 5 + x 2 + x 1 (10101101) (00001011) (10100110) Katz, Stoica F 04 33
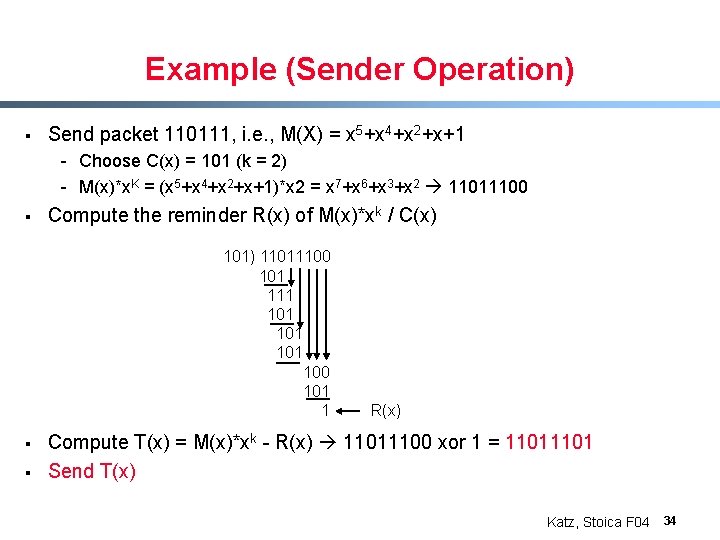
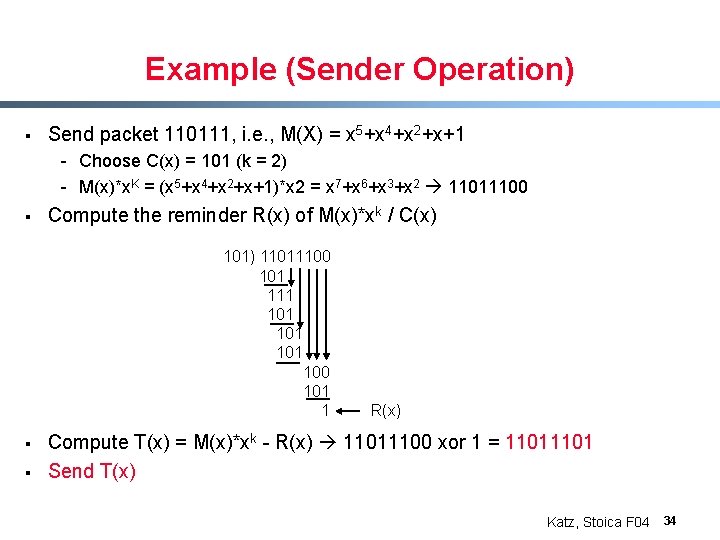
Example (Sender Operation) § Send packet 110111, i. e. , M(X) = x 5+x 4+x 2+x+1 - Choose C(x) = 101 (k = 2) - M(x)*x. K = (x 5+x 4+x 2+x+1)*x 2 = x 7+x 6+x 3+x 2 11011100 § Compute the reminder R(x) of M(x)*xk / C(x) 101) 11011100 101 111 101 100 101 1 § § R(x) Compute T(x) = M(x)*xk - R(x) 11011100 xor 1 = 1101 Send T(x) Katz, Stoica F 04 34
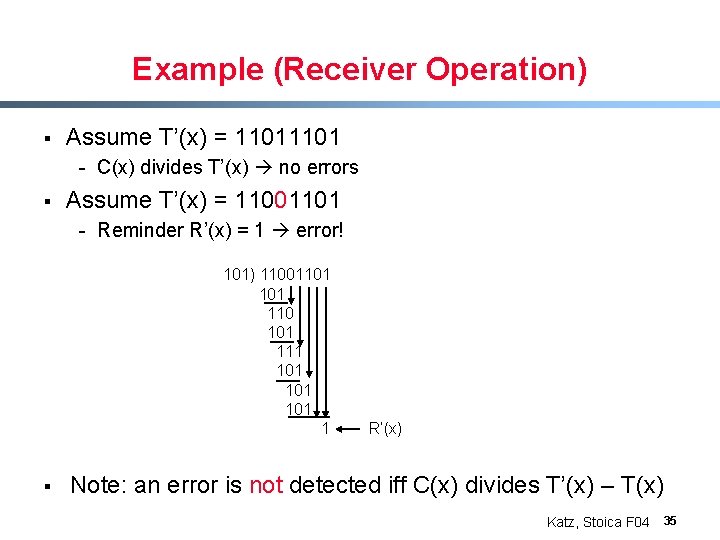
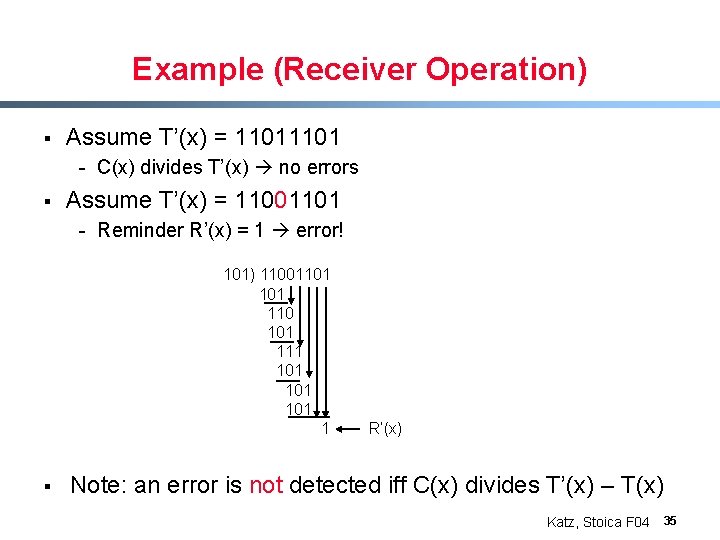
Example (Receiver Operation) § Assume T’(x) = 1101 - C(x) divides T’(x) no errors § Assume T’(x) = 11001101 - Reminder R’(x) = 1 error! 101) 11001101 110 101 111 101 101 1 § R’(x) Note: an error is not detected iff C(x) divides T’(x) – T(x) Katz, Stoica F 04 35
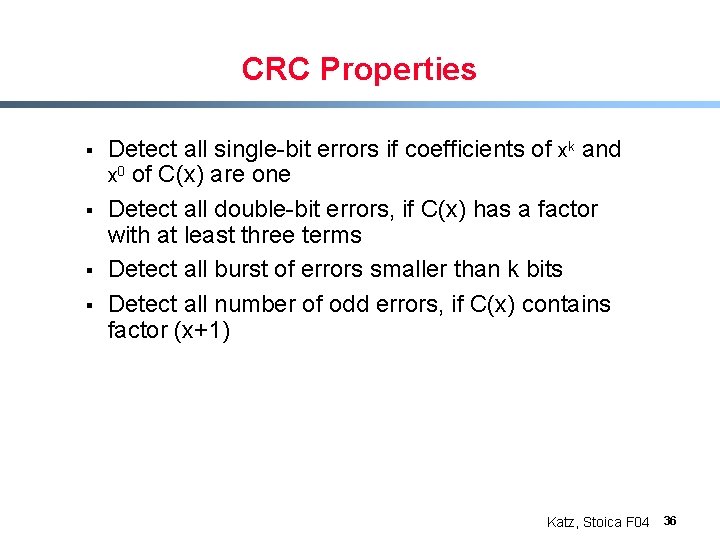
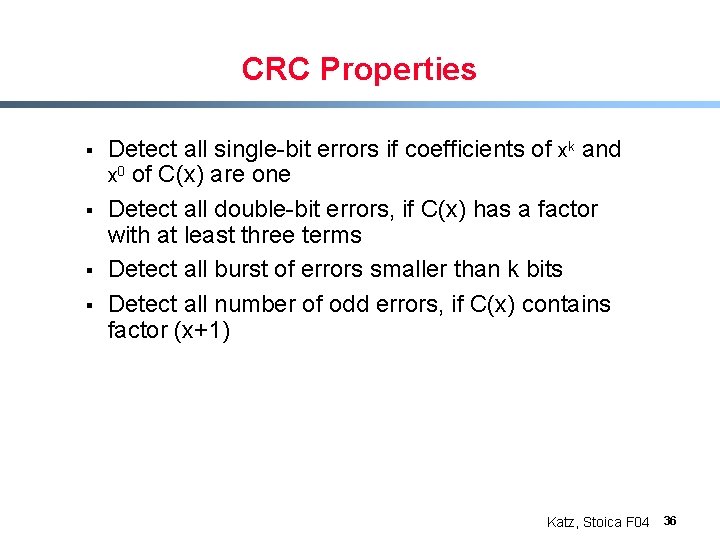
CRC Properties § § Detect all single-bit errors if coefficients of xk and x 0 of C(x) are one Detect all double-bit errors, if C(x) has a factor with at least three terms Detect all burst of errors smaller than k bits Detect all number of odd errors, if C(x) contains factor (x+1) Katz, Stoica F 04 36