EEC484584 Computer Networks Lecture 15 Wenbing Zhao wenbingieee
EEC-484/584 Computer Networks Lecture 15 Wenbing Zhao wenbing@ieee. org
2 Outline • Reminder: – Wiki page peer review due tonight (12/1) • Introduction to cryptography Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
3 Cryptography Terminology • Encryption is the process of encoding a message so that its meaning is not obvious – Equivalent terms: encode, encipher • Encryption addresses the need for confidentiality of data • Encryption can also be used to ensure integrity (i. e. , unauthorized change can be detected) • Encryption is the basis of protocols that enable us to provide security while accomplishing system or network tasks Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
4 Cryptography Terminology • Decryption is the reverse process, transforming an encrypted message back into its normal, original form – Equivalent terms: decode, decipher • A system for encryption and decryption is called a cryptosystem Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
5 Cryptography Terminology • The encryption and decryption rules are called encryption and decryption algorithms • Encryption/decryption algorithms often use a device called a key, denoted by K, so that the resulting ciphertext depends on the original plaintext message, the algorithm, and the key value • An encryption scheme that does not require the use of a key is called a keyless cipher Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
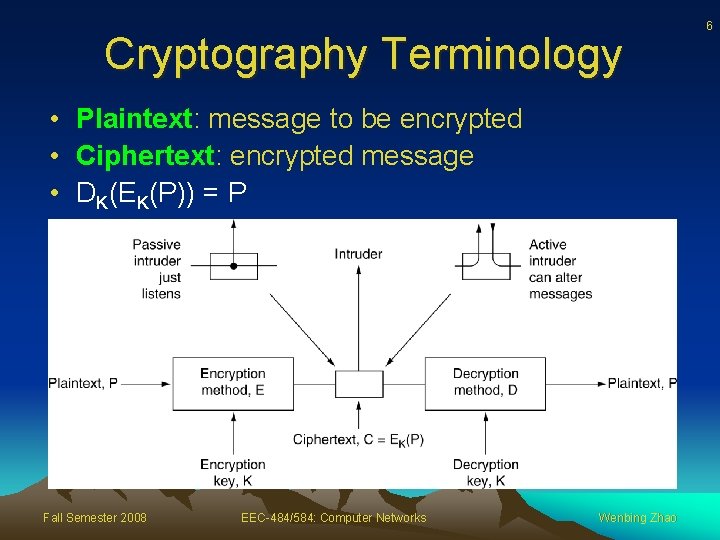
Cryptography Terminology • Plaintext: message to be encrypted • Ciphertext: encrypted message • DK(EK(P)) = P Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao 6
7 Symmetric Encryption • The encryption and decryption keys are the same, so P = D(K, E(K, P)) • D and E are closely related. They are mirrorimage processes • The symmetric systems provide a two-way channel to their users • The symmetry of this situation is a major advantage of this type of encryption, but it also leads to a problem: key distribution Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
8 Asymmetric Encryption • Encryption and decryption keys come in pairs. The decryption key, KD, inverts the encryption of key KE, so that P = D(KD, E(KE, P)) • Asymmetric encryption systems excel at key management Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
9 Cryptology • Cryptology is the research into and study of encryption and decryption; it includes both cryptography and cryptanalysis • Cryptography – art of devising ciphers – Comes from Greek words for “secret writing”. It refers to the practice of using encryption to conceal text • Cryptanalysis – art of breaking ciphers – Study of encryption and encrypted messages, hoping to find the hidden meanings Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
10 Basic Encryption Methods • Substitution ciphers: one letter is exchanged for another • Transposition ciphers: order of letters is rearranged Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
11 Substitution Ciphers • Idea: each letter or group of letters is replaced by another letter or group of letters • Caesar cipher – circularly shift by 3 letters – a -> D, b -> E, … z -> C – More generally, shift by k letters, k is the key • Monoalphabetic cipher – map each letter to some other letter – A b c def … wx yz – Q W E R T Y … V B N M <= the key Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
12 Substitution Ciphers • Not difficult to determine the key using frequencies of letters, pairs of letter etc. , or by guessing a probable word or phrase • Most frequently occurred – Letters: e, t, o, a, n, … – Digrams: th, in, er, re, an, … – Trigrams: the, ing, and, ion, ent – Words: the, of, and, to, a, in, that, … Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
13 Transposition Ciphers • Transposition cipher – reorders (rearrange) symbols but does not disguise them. It is also called permutation • Transpositions try to break established patterns • Both substitution and transport ciphers can be broken using language statistical information Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
14 Columnar Transposition • Plaintext written in rows, number of columns = key length • Key is used to number the columns • Ciphertext read out by columns, starting with column whose key letter is lowest Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
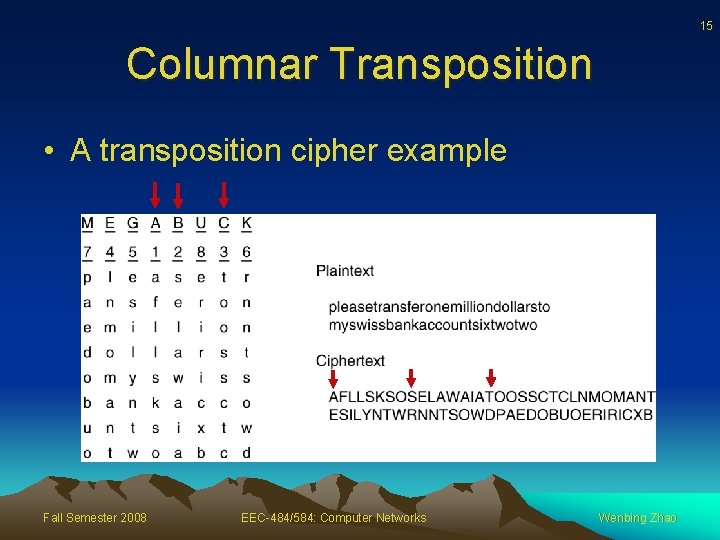
15 Columnar Transposition • A transposition cipher example Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
16 One-Time Pads • One-time pad: construct an unbreakable cipher – – Choose a random bit string as the key Convert the plaintext into a bit string Compute the XOR of these two strings, bit by bit The resulting ciphertext cannot be broken, because in a sufficiently large sample of ciphertext, each letter will occur equally often => there is simply no information in the message because all possible plaintexts of the given length are equally likely Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
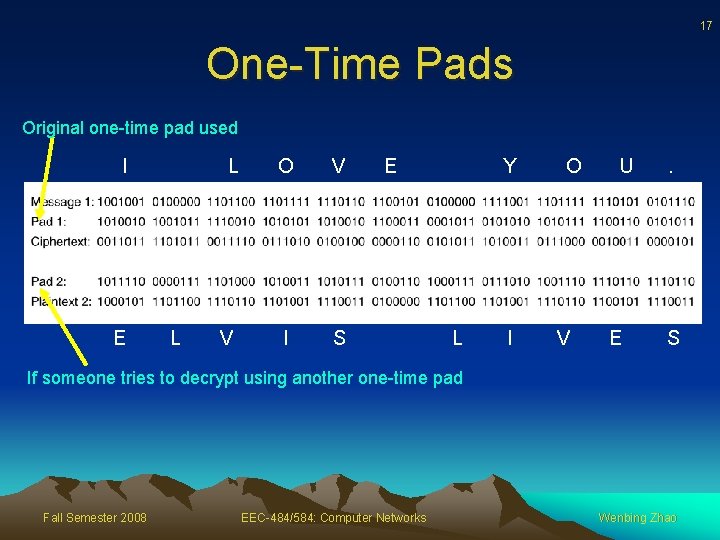
17 One-Time Pads Original one-time pad used I E L L O V V I S E Y L I O V U E . S If someone tries to decrypt using another one-time pad Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
18 One-Time Pads • Disadvantages – The key cannot be memorized, both sender and receiver must carry a written copy with them – Total amount of data can be transmitted is limited by the amount of key available – Sensitive to lost or inserted characters Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
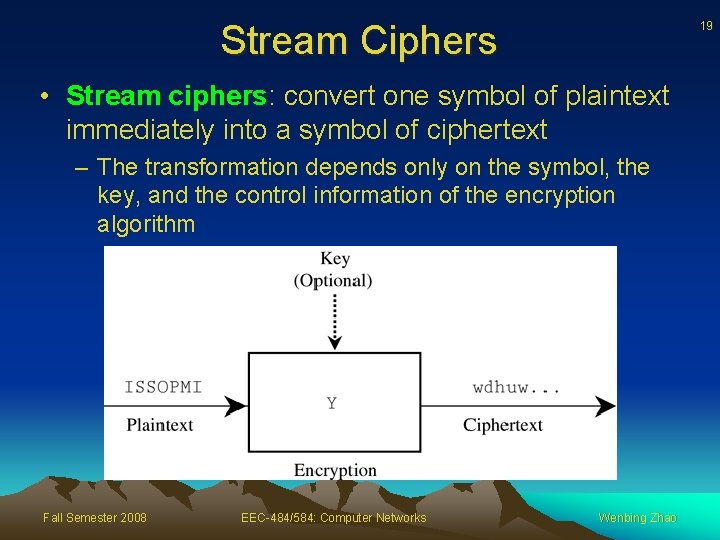
Stream Ciphers 19 • Stream ciphers: convert one symbol of plaintext immediately into a symbol of ciphertext – The transformation depends only on the symbol, the key, and the control information of the encryption algorithm Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
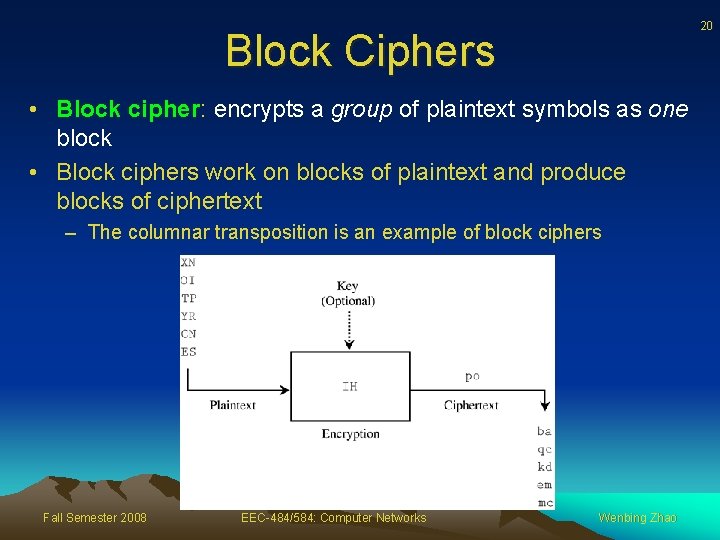
20 Block Ciphers • Block cipher: encrypts a group of plaintext symbols as one block • Block ciphers work on blocks of plaintext and produce blocks of ciphertext – The columnar transposition is an example of block ciphers Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
Cryptanalysis – Breaking Encryption Schemes • Ciphertext-only: cryptanalyst has a quantity of ciphertext and no plaintext • Known plaintext: cryptanalyst has some matched ciphertext and plaintext • Chosen plaintext: cryptanalyst has the ability to encrypt pieces of plaintext of his own choosing Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao 21
22 Symmetric-Key Algorithms • DES – The Data Encryption Standard • AES – The Advanced Encryption Standard • Cipher Modes Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
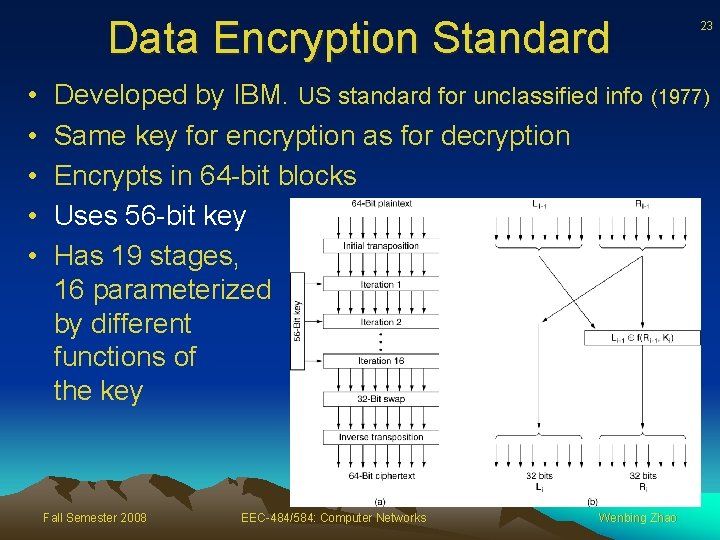
Data Encryption Standard • • • 23 Developed by IBM. US standard for unclassified info (1977) Same key for encryption as for decryption Encrypts in 64 -bit blocks Uses 56 -bit key Has 19 stages, 16 parameterized by different functions of the key Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
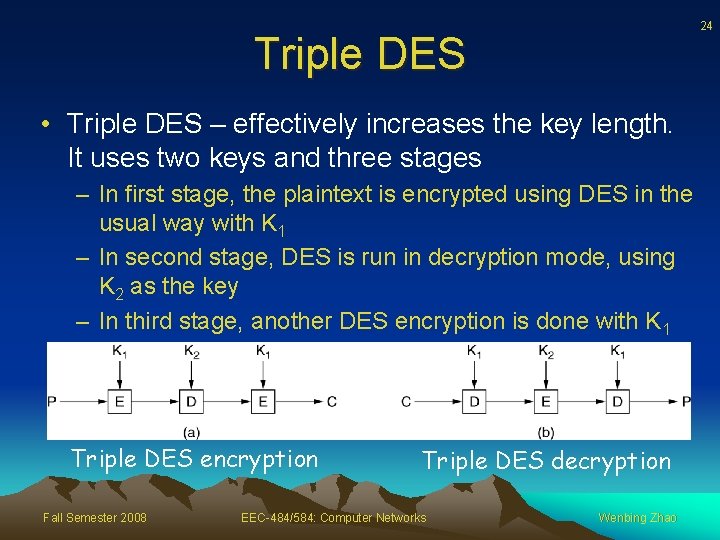
24 Triple DES • Triple DES – effectively increases the key length. It uses two keys and three stages – In first stage, the plaintext is encrypted using DES in the usual way with K 1 – In second stage, DES is run in decryption mode, using K 2 as the key – In third stage, another DES encryption is done with K 1 Triple DES encryption Fall Semester 2008 Triple DES decryption EEC-484/584: Computer Networks Wenbing Zhao
25 AES – The Advanced Encryption Standard • AES is a result of a cryptographic contest – Organized by NIST in 1997 • Rules for AES proposals 1. 2. 3. 4. 5. The algorithm must be a symmetric block cipher The full design must be public Key lengths of 128, 192, and 256 bits supported Both software and hardware implementations required The algorithm must be public or licensed on nondiscriminatory terms • Winner: Rijndael (from two Belgian cryptographers: Joan Daemen and Vincent Rijmen) Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
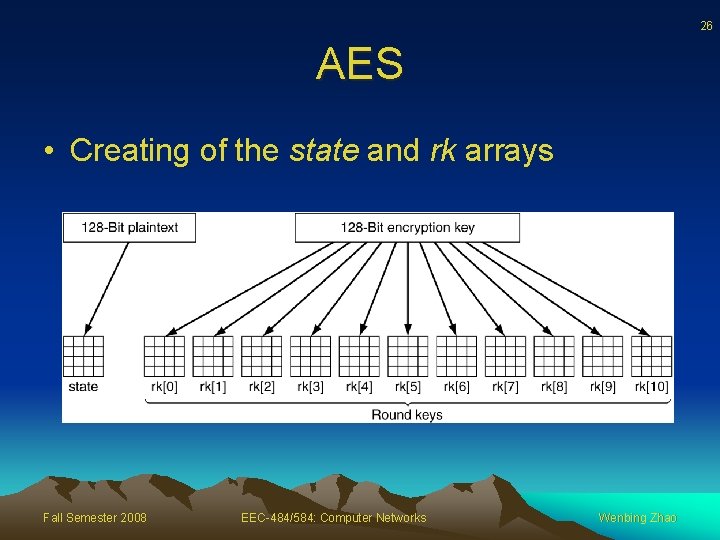
26 AES • Creating of the state and rk arrays Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
27 Cipher Modes • Despite all the complexity, AES and DES (or any block cipher) is basically a monoalphabetic substitution cipher using big characters – Whenever the same plaintext block goes in the front end, the same ciphertext block comes out the back end – If you encrypt the plaintext abcdefgh 100 times with same DES key, you get the same ciphertext 100 times – An intruder can exploit this property to help subvert the cipher Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
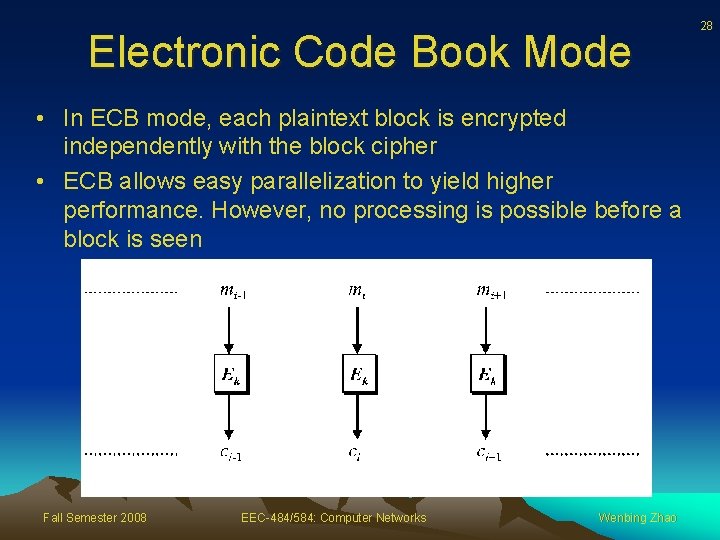
Electronic Code Book Mode • In ECB mode, each plaintext block is encrypted independently with the block cipher • ECB allows easy parallelization to yield higher performance. However, no processing is possible before a block is seen Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao 28
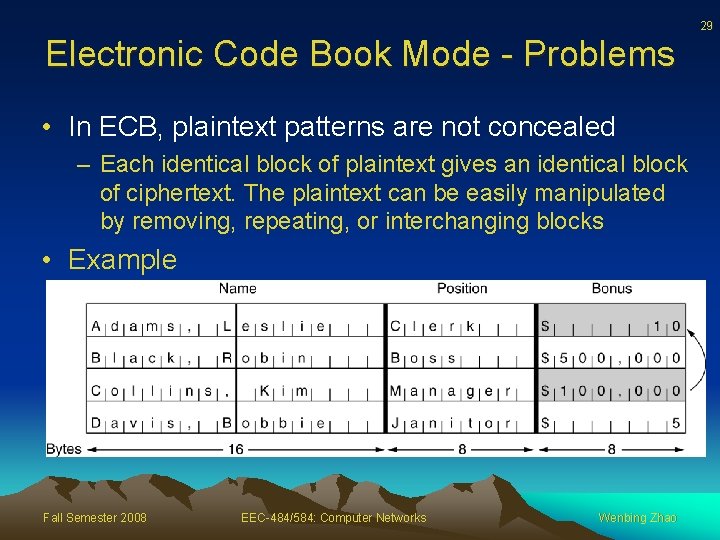
29 Electronic Code Book Mode - Problems • In ECB, plaintext patterns are not concealed – Each identical block of plaintext gives an identical block of ciphertext. The plaintext can be easily manipulated by removing, repeating, or interchanging blocks • Example Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao
Cipher Block Chaining Mode • To avoid the ECB mode problem: replacing a block will cause the plaintext decrypted starting at the replaced to become garbage • Exclusive OR the encrypted text with the next block of plaintext before encryption: C 0 = E(P 0 XOR IV), C 1 = E(P 1 XOR C 0), etc. • Drawback: must wait until full 64 -bit (128 -bit) block to arrive to decrypt Fall Semester 2008 EEC-484/584: Computer Networks Wenbing Zhao 30
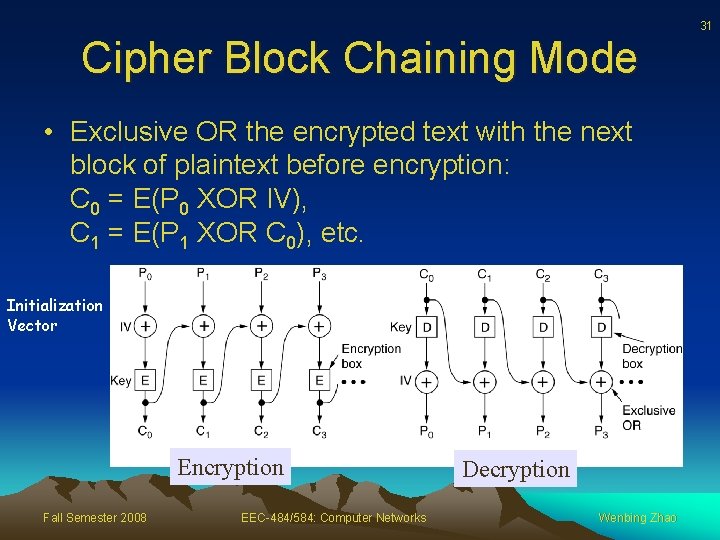
31 Cipher Block Chaining Mode • Exclusive OR the encrypted text with the next block of plaintext before encryption: C 0 = E(P 0 XOR IV), C 1 = E(P 1 XOR C 0), etc. Initialization Vector Encryption Fall Semester 2008 EEC-484/584: Computer Networks Decryption Wenbing Zhao
- Slides: 31