EEC484584 Computer Networks Lecture 12 Wenbing Zhao Cleveland
EEC-484/584 Computer Networks Lecture 12 Wenbing Zhao Cleveland State University wenbing@ieee. org 2/26/2021
Outline n n Quiz#3 Result New grading policy Project Data Link layer q Error Detection and Correction We Cover This Sub. Layer in this lecture Medium Access Control (MAC) DLL Data Link 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
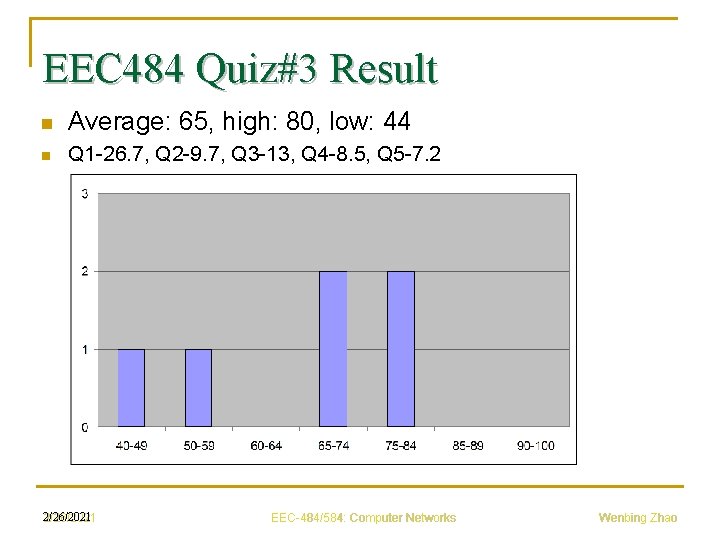
EEC 484 Quiz#3 Result n Average: 65, high: 80, low: 44 n Q 1 -26. 7, Q 2 -9. 7, Q 3 -13, Q 4 -8. 5, Q 5 -7. 2 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
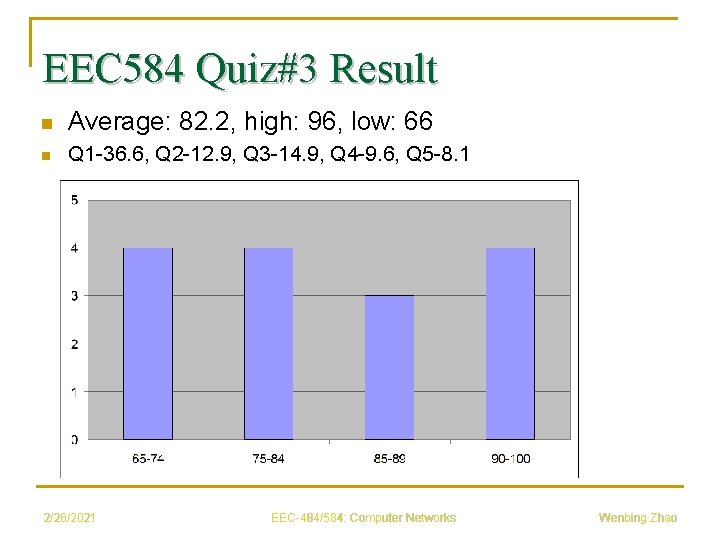
EEC 584 Quiz#3 Result n Average: 82. 2, high: 96, low: 66 n Q 1 -36. 6, Q 2 -12. 9, Q 3 -14. 9, Q 4 -9. 6, Q 5 -8. 1 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
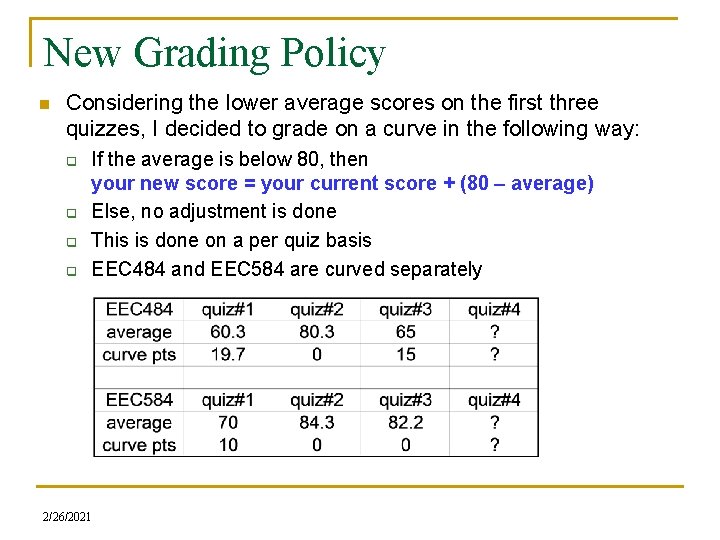
New Grading Policy n Considering the lower average scores on the first three quizzes, I decided to grade on a curve in the following way: q q If the average is below 80, then your new score = your current score + (80 – average) Else, no adjustment is done This is done on a per quiz basis EEC 484 and EEC 584 are curved separately 2/26/2021
EEC 484 Project Walk-through n See demo 2/26/2021
EEC 584 Project Walk-through n n Searching for literature: ACM digital library and Google scholar Example wiki pages q q q n n http: //flyingtiger. pbwiki. com/Open-Shortest-Path-Tree http: //dutkoeec 584 -dns. pbwiki. com/BIND http: //macprotocol. pbwiki. com/ http: //bryanandsteve. pbwiki. com/ http: //samarth. pbwiki. com/Routing-Algorithms Example peer review Turnitin. com account q 2/26/2021 You must submit a turnitin. com report
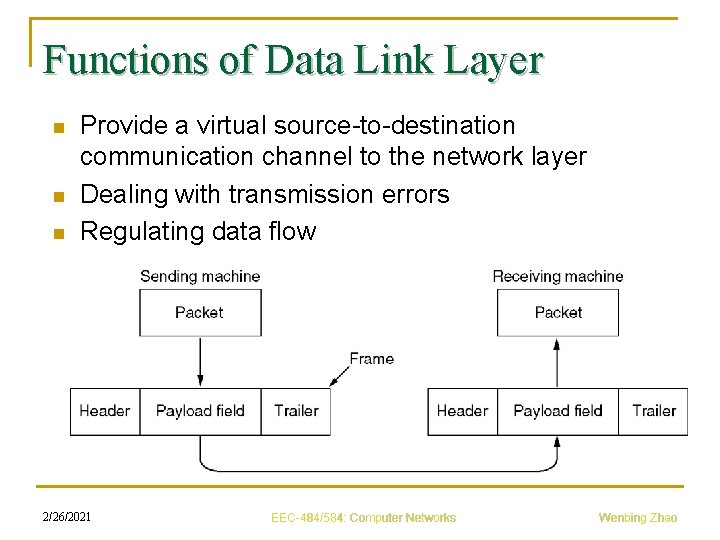
Functions of Data Link Layer n n n Provide a virtual source-to-destination communication channel to the network layer Dealing with transmission errors Regulating data flow 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
Error Detection and Correction n Causes of errors q q q n Transmission errors on phone lines due to thermal noise Data transmission errors due to impulse noise Signals are separated, distorted, recombined Crosstalk between physically adjacent wires Compression and decompression Receiver out of synch with sender Errors usually occur in bursts 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
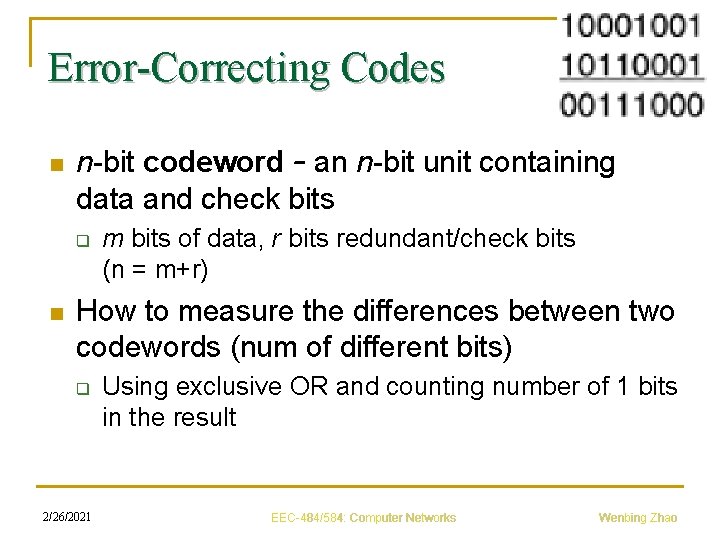
Error-Correcting Codes n n-bit codeword – an n-bit unit containing data and check bits q n m bits of data, r bits redundant/check bits (n = m+r) How to measure the differences between two codewords (num of different bits) q 2/26/2021 Using exclusive OR and counting number of 1 bits in the result EEC-484/584: Computer Networks Wenbing Zhao
Error-Correcting Codes n n Hamming distance – number of bit positions in which two codewords differ If two codewords are a Hamming distance d apart, it will require d single-bit errors to convert one into the other 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
Error-Correcting Codes n Complete code q q n Complete list of all legal codewords: 2 m possible data messages Recall that there are m bits of data Hamming distance of the complete code q 2/26/2021 Find two codewords whose Hamming distance is minimum EEC-484/584: Computer Networks Wenbing Zhao
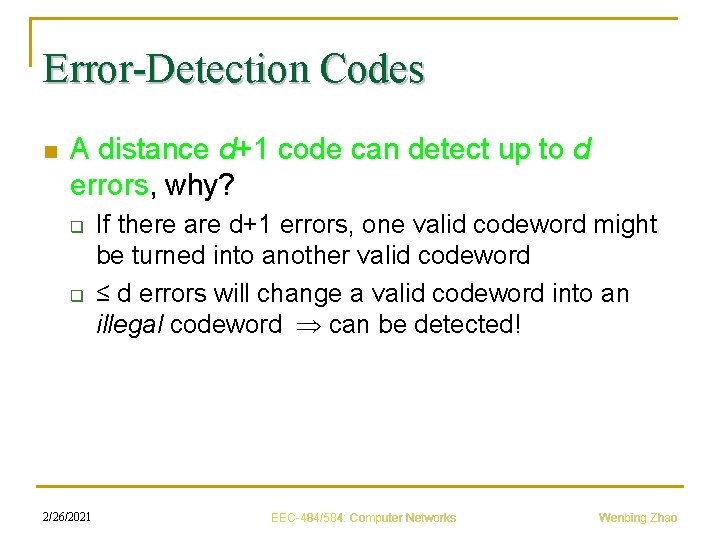
Error-Detection Codes n A distance d+1 code can detect up to d errors, why? q q 2/26/2021 If there are d+1 errors, one valid codeword might be turned into another valid codeword ≤ d errors will change a valid codeword into an illegal codeword can be detected! EEC-484/584: Computer Networks Wenbing Zhao
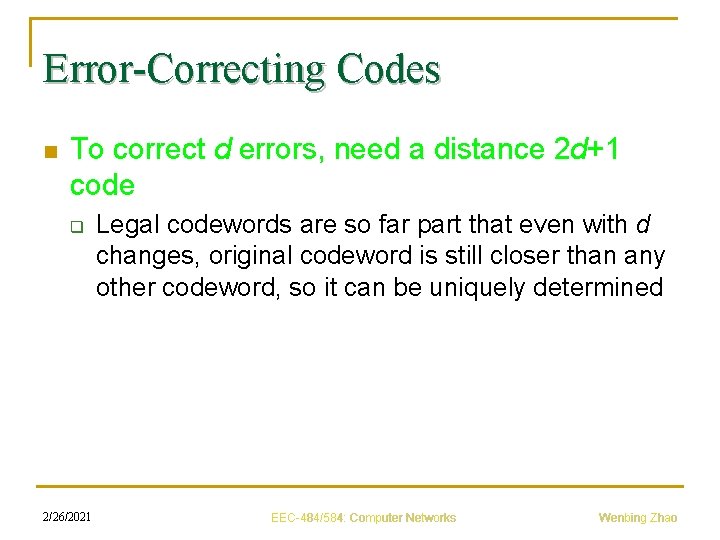
Error-Correcting Codes n To correct d errors, need a distance 2 d+1 code q 2/26/2021 Legal codewords are so far part that even with d changes, original codeword is still closer than any other codeword, so it can be uniquely determined EEC-484/584: Computer Networks Wenbing Zhao
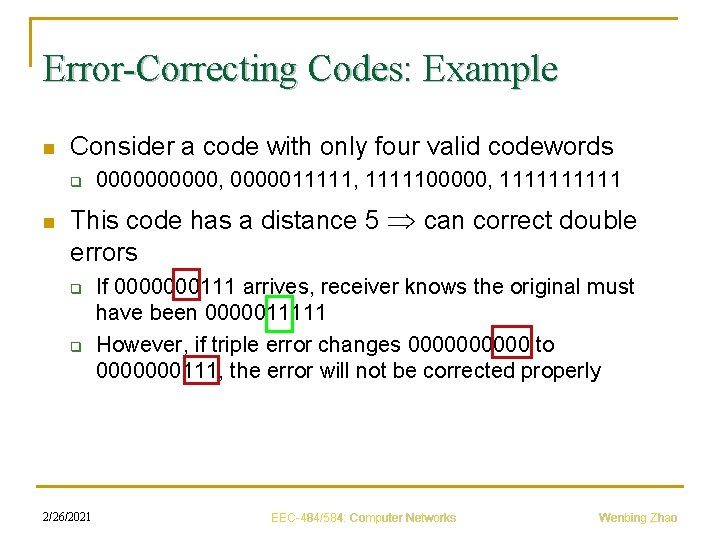
Error-Correcting Codes: Example n Consider a code with only four valid codewords q n 00000, 0000011111, 1111100000, 11111 This code has a distance 5 can correct double errors q q 2/26/2021 If 0000000111 arrives, receiver knows the original must have been 0000011111 However, if triple error changes 00000 to 0000000111, the error will not be corrected properly EEC-484/584: Computer Networks Wenbing Zhao
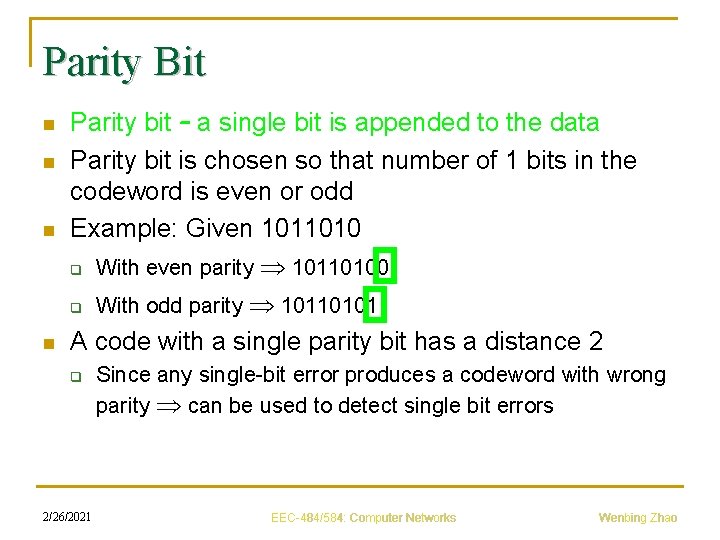
Parity Bit n n Parity bit – a single bit is appended to the data Parity bit is chosen so that number of 1 bits in the codeword is even or odd Example: Given 1011010 q With even parity 10110100 q With odd parity 10110101 A code with a single parity bit has a distance 2 q 2/26/2021 Since any single-bit error produces a codeword with wrong parity can be used to detect single bit errors EEC-484/584: Computer Networks Wenbing Zhao
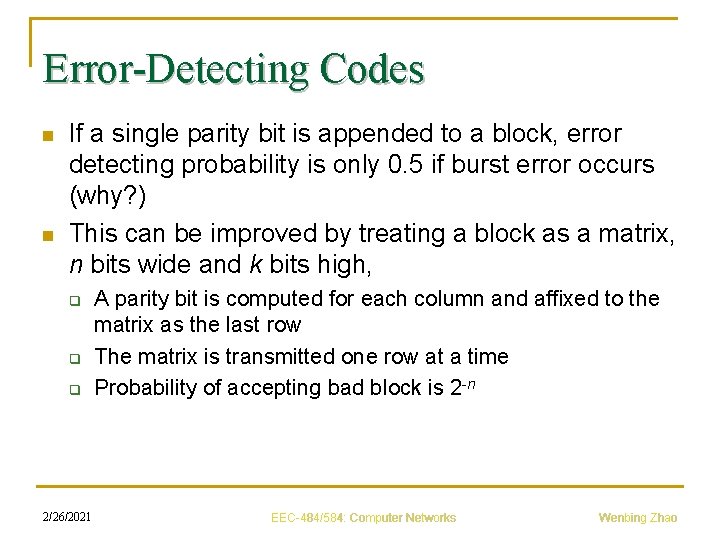
Error-Detecting Codes n n If a single parity bit is appended to a block, error detecting probability is only 0. 5 if burst error occurs (why? ) This can be improved by treating a block as a matrix, n bits wide and k bits high, q q q 2/26/2021 A parity bit is computed for each column and affixed to the matrix as the last row The matrix is transmitted one row at a time Probability of accepting bad block is 2 -n EEC-484/584: Computer Networks Wenbing Zhao
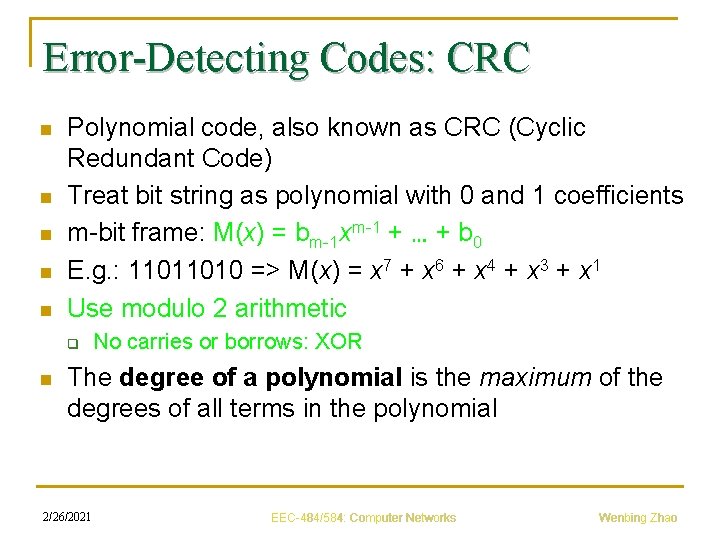
Error-Detecting Codes: CRC n n n Polynomial code, also known as CRC (Cyclic Redundant Code) Treat bit string as polynomial with 0 and 1 coefficients m-bit frame: M(x) = bm-1 xm-1 + … + b 0 E. g. : 11011010 => M(x) = x 7 + x 6 + x 4 + x 3 + x 1 Use modulo 2 arithmetic q n No carries or borrows: XOR The degree of a polynomial is the maximum of the degrees of all terms in the polynomial 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
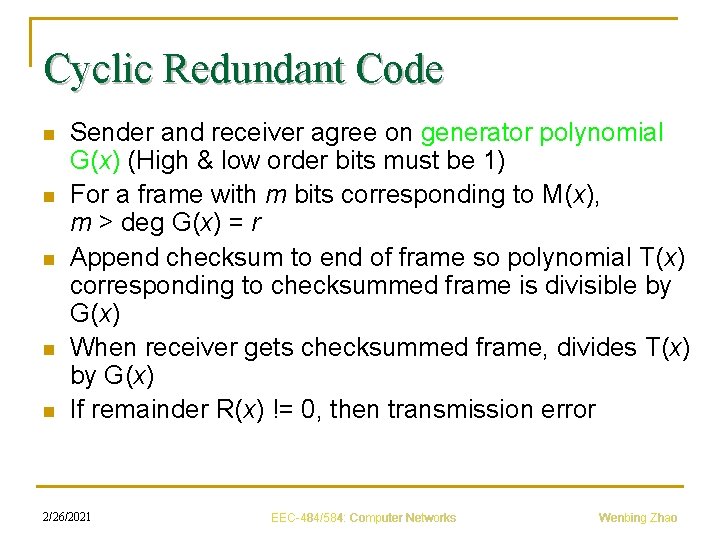
Cyclic Redundant Code n n n Sender and receiver agree on generator polynomial G(x) (High & low order bits must be 1) For a frame with m bits corresponding to M(x), m > deg G(x) = r Append checksum to end of frame so polynomial T(x) corresponding to checksummed frame is divisible by G(x) When receiver gets checksummed frame, divides T(x) by G(x) If remainder R(x) != 0, then transmission error 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
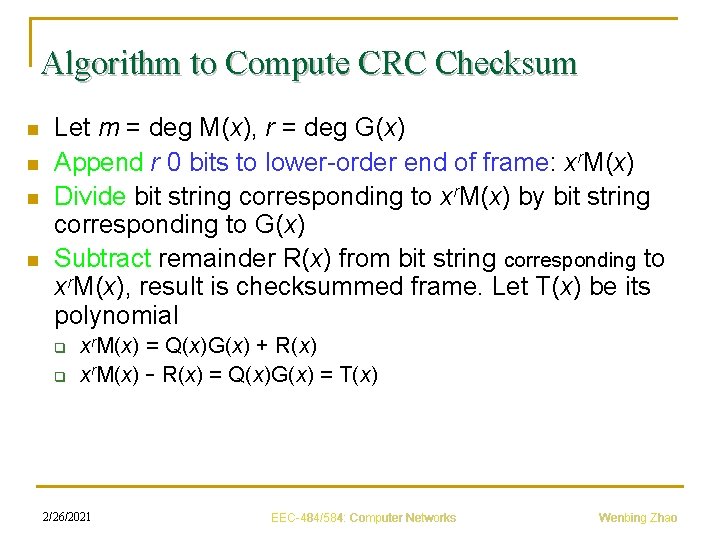
Algorithm to Compute CRC Checksum n n Let m = deg M(x), r = deg G(x) Append r 0 bits to lower-order end of frame: xr. M(x) Divide bit string corresponding to xr. M(x) by bit string corresponding to G(x) Subtract remainder R(x) from bit string corresponding to xr. M(x), result is checksummed frame. Let T(x) be its polynomial q q xr. M(x) = Q(x)G(x) + R(x) xr. M(x) – R(x) = Q(x)G(x) = T(x) 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
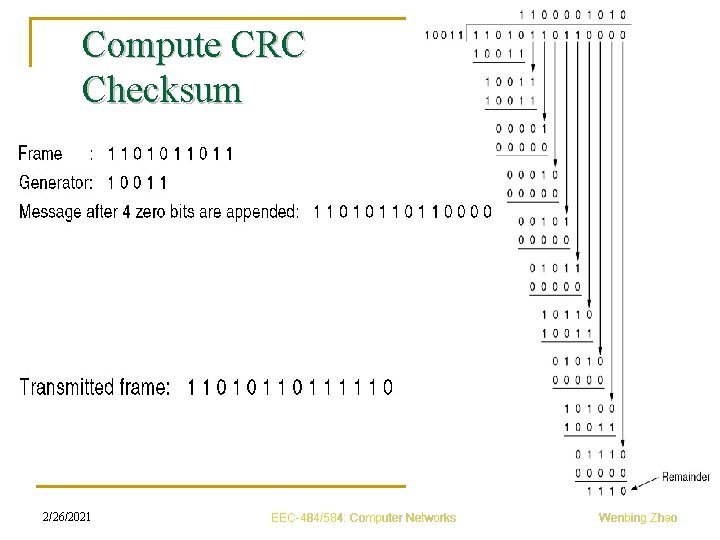
Compute CRC Checksum 2/26/2021 XOR EEC-484/584: Computer Networks Wenbing Zhao
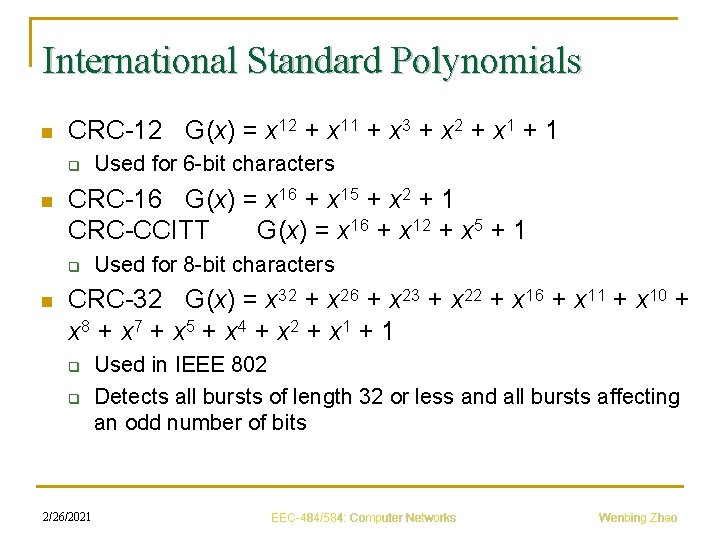
International Standard Polynomials n CRC-12 G(x) = x 12 + x 11 + x 3 + x 2 + x 1 + 1 q n CRC-16 G(x) = x 16 + x 15 + x 2 + 1 CRC-CCITT G(x) = x 16 + x 12 + x 5 + 1 q n Used for 6 -bit characters Used for 8 -bit characters CRC-32 G(x) = x 32 + x 26 + x 23 + x 22 + x 16 + x 11 + x 10 + x 8 + x 7 + x 5 + x 4 + x 2 + x 1 + 1 q q 2/26/2021 Used in IEEE 802 Detects all bursts of length 32 or less and all bursts affecting an odd number of bits EEC-484/584: Computer Networks Wenbing Zhao
Exercise n Q 1. To provide more reliability than a single parity bit can give, an error-detecting coding scheme uses one parity bit for checking all the odd-numbered bits and a second parity bit for all the even-numbered bits. What is the Hamming distance of this code? 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
Exercise n Q 2. A bit stream 10011101 is to be transmitted using the standard CRC method described in the text. The generator polynomial is x 3 + 1. Show the actual bit string transmitted. Suppose third bit from the left is inverted during transmission. Show that this error is detected at the receiver's end. 2/26/2021 EEC-484/584: Computer Networks Wenbing Zhao
- Slides: 24