EE 5900 CyberPhysical Systems RMS and EDF Scheduling
EE 5900 Cyber-Physical Systems RMS and EDF Scheduling 1
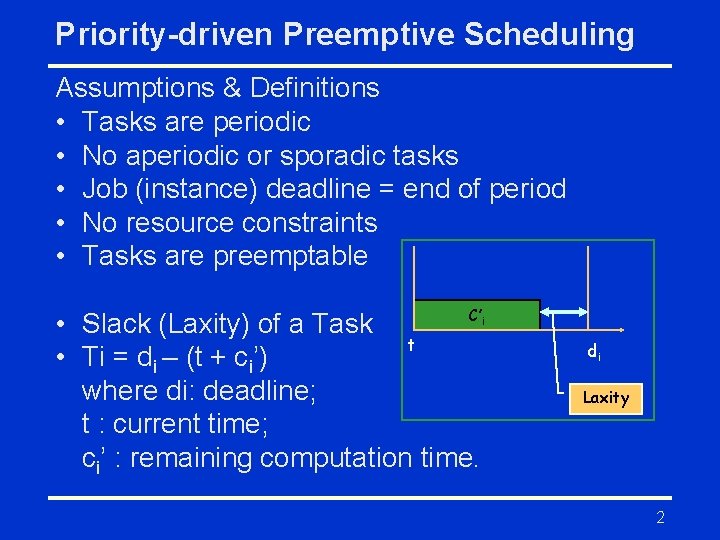
Priority-driven Preemptive Scheduling Assumptions & Definitions • Tasks are periodic • No aperiodic or sporadic tasks • Job (instance) deadline = end of period • No resource constraints • Tasks are preemptable C’ • Slack (Laxity) of a Task t • Ti = di – (t + ci’) where di: deadline; t : current time; ci’ : remaining computation time. i di Laxity 2
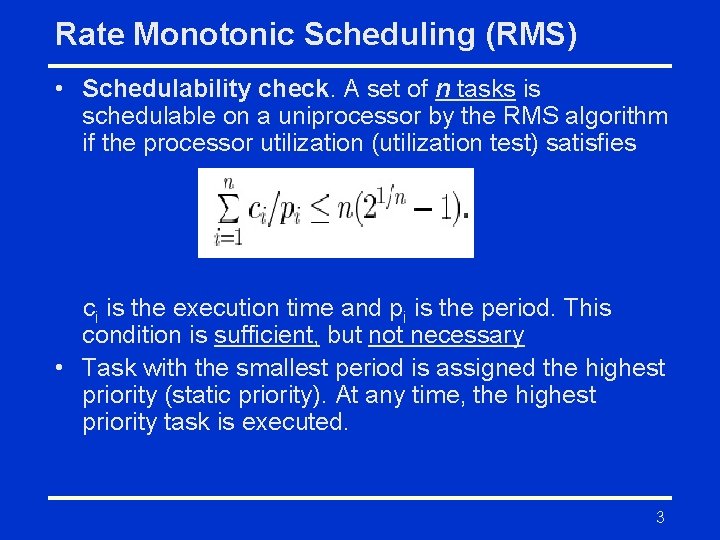
Rate Monotonic Scheduling (RMS) • Schedulability check. A set of n tasks is schedulable on a uniprocessor by the RMS algorithm if the processor utilization (utilization test) satisfies ci is the execution time and pi is the period. This condition is sufficient, but not necessary • Task with the smallest period is assigned the highest priority (static priority). At any time, the highest priority task is executed. 3
![RMS Scheduler - Example 1 Task set: Ti = (ci, pi) [computation time, period] RMS Scheduler - Example 1 Task set: Ti = (ci, pi) [computation time, period]](http://slidetodoc.com/presentation_image/c4ede172b170971714000da3f62c73ea/image-4.jpg)
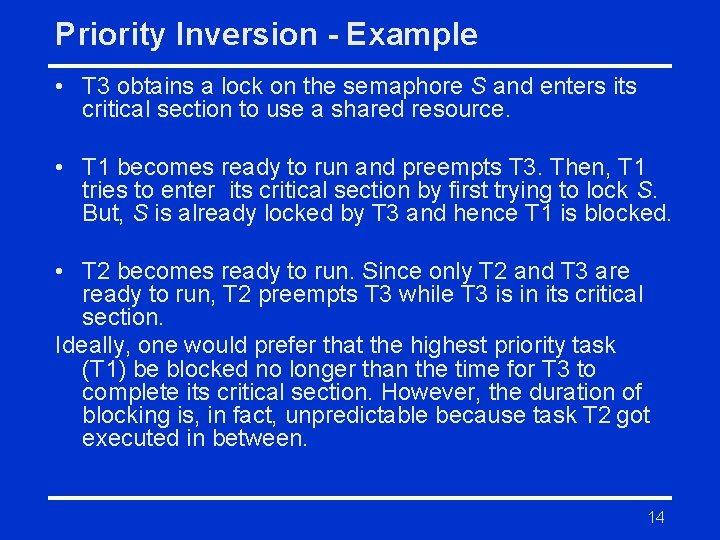
RMS Scheduler - Example 1 Task set: Ti = (ci, pi) [computation time, period] T 1 = (2, 4) and T 2 = (1, 8) Schedulability check: 2/4 + 1/8 = 0. 5 + 0. 125 = 0. 625 ≤ 2(√ 2 -1) = 0. 82 Active Tasks : {T 2} Active Tasks : {T 1, T 2} T 11 0 Active Tasks : {T 1} T 2 1 2 T 12 3 4 6 8 4
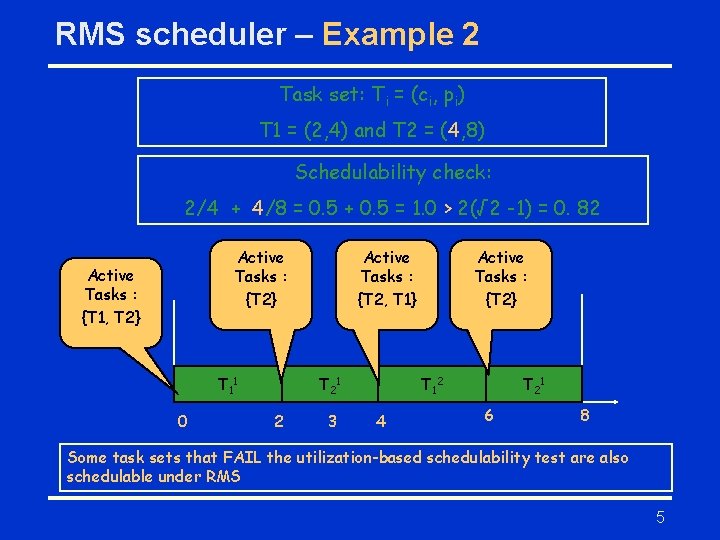
RMS scheduler – Example 2 Task set: Ti = (ci, pi) T 1 = (2, 4) and T 2 = (4, 8) Schedulability check: 2/4 + 4/8 = 0. 5 + 0. 5 = 1. 0 > 2(√ 2 -1) = 0. 82 Active Tasks : {T 2} Active Tasks : {T 1, T 2} T 11 0 Active Tasks : {T 2, T 1} T 2 1 2 3 Active Tasks : {T 2} T 12 4 T 2 1 6 8 Some task sets that FAIL the utilization-based schedulability test are also schedulable under RMS 5
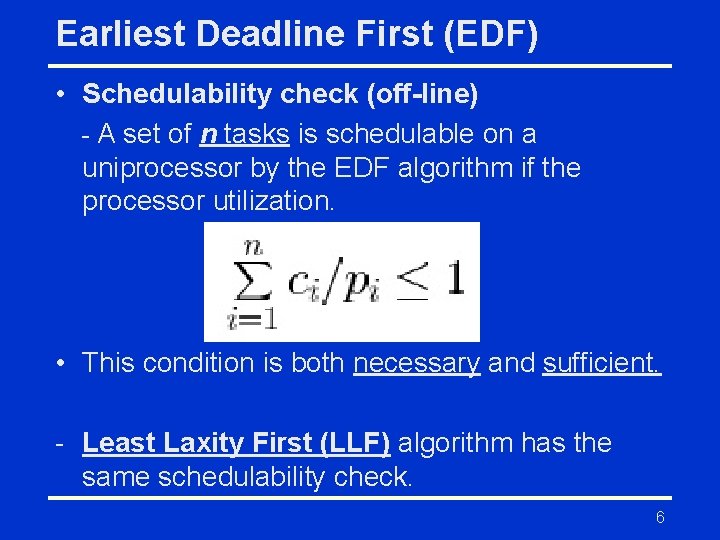
Earliest Deadline First (EDF) • Schedulability check (off-line) - A set of n tasks is schedulable on a uniprocessor by the EDF algorithm if the processor utilization. • This condition is both necessary and sufficient. - Least Laxity First (LLF) algorithm has the same schedulability check. 6
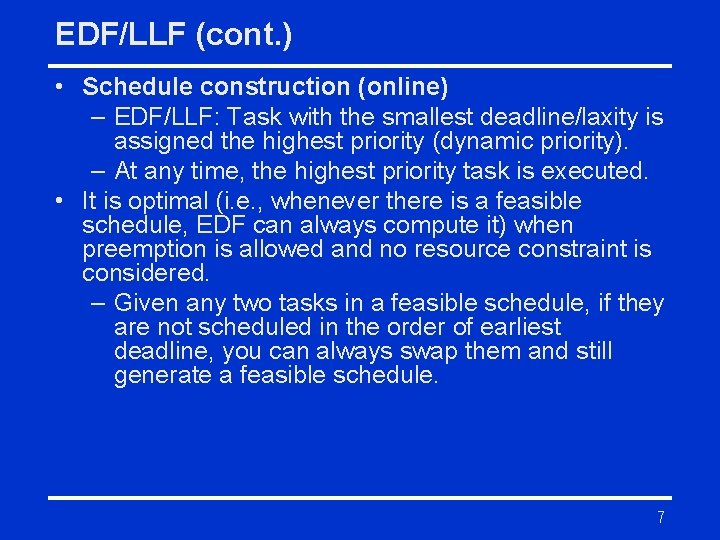
EDF/LLF (cont. ) • Schedule construction (online) – EDF/LLF: Task with the smallest deadline/laxity is assigned the highest priority (dynamic priority). – At any time, the highest priority task is executed. • It is optimal (i. e. , whenever there is a feasible schedule, EDF can always compute it) when preemption is allowed and no resource constraint is considered. – Given any two tasks in a feasible schedule, if they are not scheduled in the order of earliest deadline, you can always swap them and still generate a feasible schedule. 7
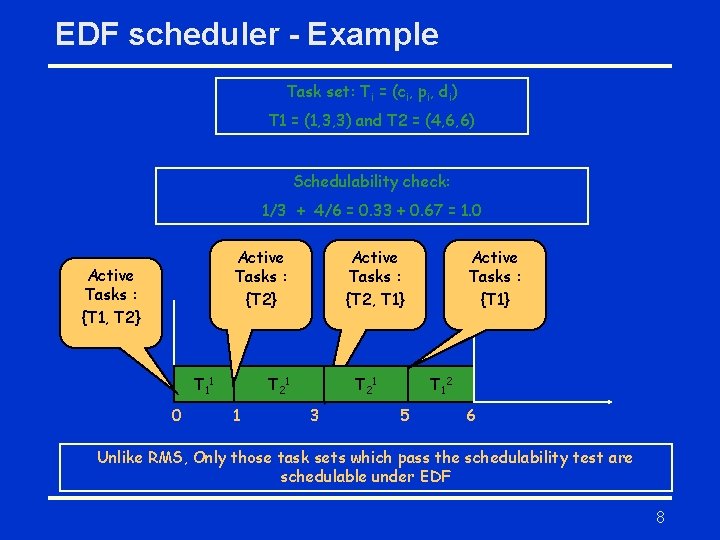
EDF scheduler - Example Task set: Ti = (ci, pi, di) T 1 = (1, 3, 3) and T 2 = (4, 6, 6) Schedulability check: 1/3 + 4/6 = 0. 33 + 0. 67 = 1. 0 Active Tasks : {T 2} Active Tasks : {T 1, T 2} T 11 0 Active Tasks : {T 2, T 1} T 2 1 1 T 2 1 3 Active Tasks : {T 1} T 12 5 6 Unlike RMS, Only those task sets which pass the schedulability test are schedulable under EDF 8
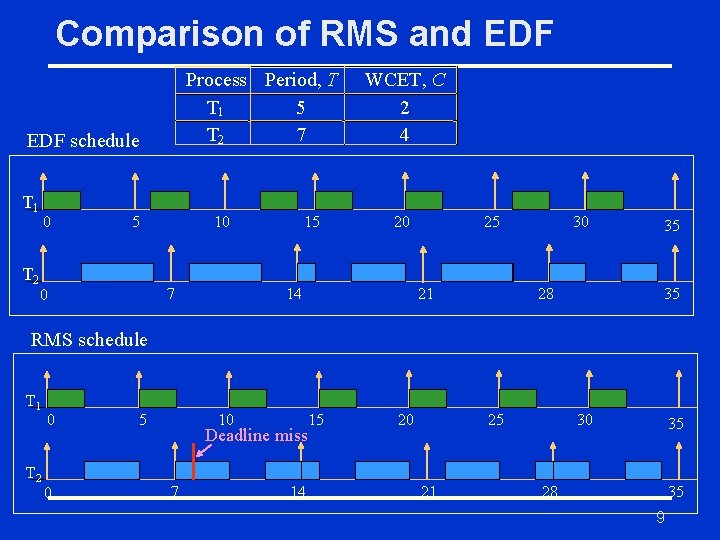
Comparison of RMS and EDF Process Period, T T 1 5 T 2 7 EDF schedule T 1 T 2 0 5 10 7 0 15 WCET, C 2 4 20 14 25 21 30 28 35 35 RMS schedule T 1 T 2 0 0 5 10 Deadline miss 7 14 15 20 25 21 30 35 28 35 9
Resource sharing • • Periodic tasks Task can have resource access Semaphore is used for mutual exclusion RMS scheduling 10
Background – Task State diagram • Ready State: waiting in ready queue • Running State: CPU executing the task • Blocked: waiting in the semaphore queue until the shared resource is free • Semaphore types – mutex (binary semaphore), counting semaphore 11
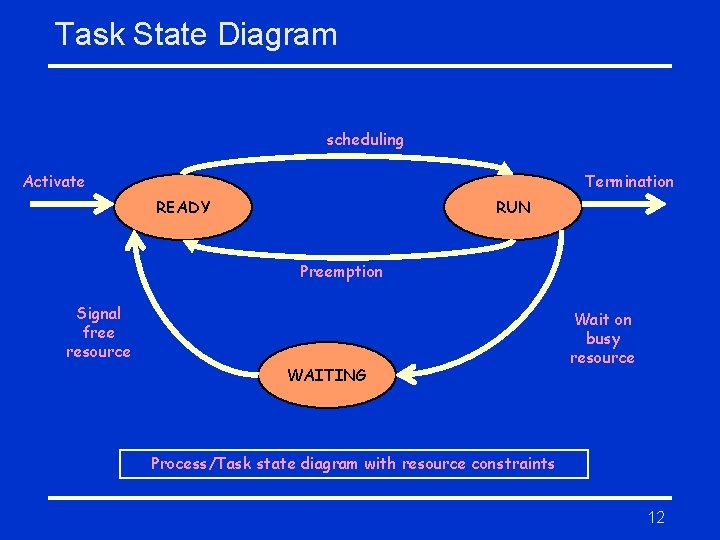
Task State Diagram scheduling Activate Termination READY RUN Preemption Signal free resource WAITING Wait on busy resource Process/Task state diagram with resource constraints 12
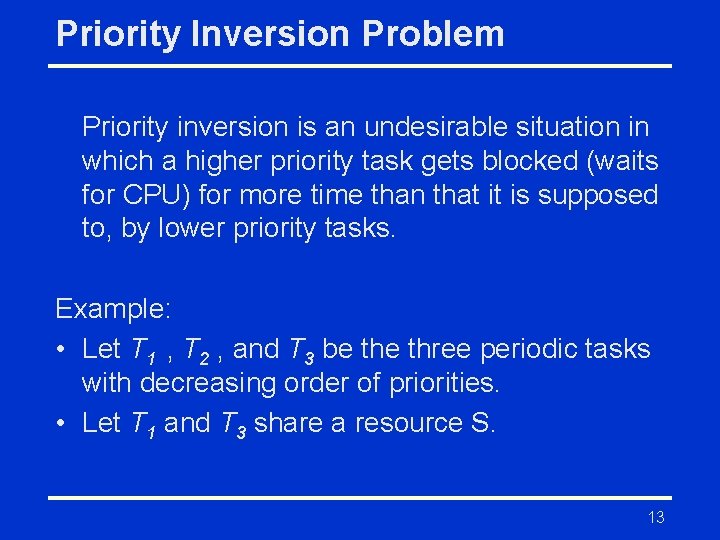
Priority Inversion Problem Priority inversion is an undesirable situation in which a higher priority task gets blocked (waits for CPU) for more time than that it is supposed to, by lower priority tasks. Example: • Let T 1 , T 2 , and T 3 be three periodic tasks with decreasing order of priorities. • Let T 1 and T 3 share a resource S. 13
Priority Inversion - Example • T 3 obtains a lock on the semaphore S and enters its critical section to use a shared resource. • T 1 becomes ready to run and preempts T 3. Then, T 1 tries to enter its critical section by first trying to lock S. But, S is already locked by T 3 and hence T 1 is blocked. • T 2 becomes ready to run. Since only T 2 and T 3 are ready to run, T 2 preempts T 3 while T 3 is in its critical section. Ideally, one would prefer that the highest priority task (T 1) be blocked no longer than the time for T 3 to complete its critical section. However, the duration of blocking is, in fact, unpredictable because task T 2 got executed in between. 14
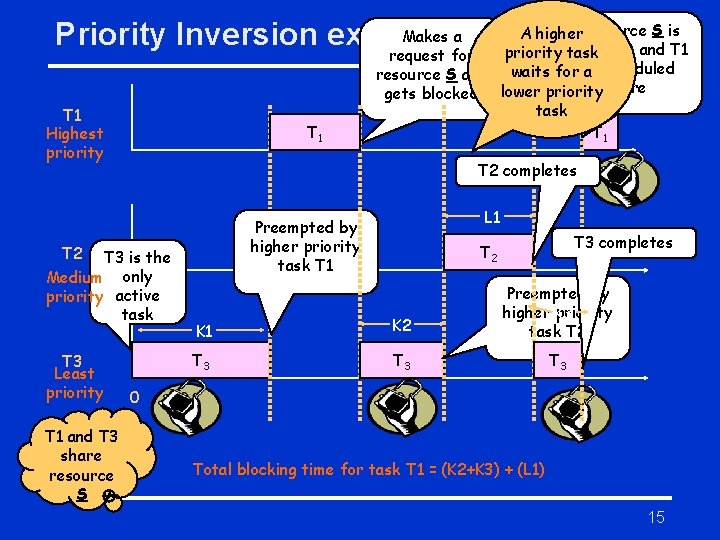
Makes a Priority Inversion example T 1 Highest priority T 1 T 2 completes T 3 is the Medium only priority active task T 1 and T 3 share resource S L 1 Preempted by higher priority task T 1 T 2 T 3 Least priority A higher. Resource S is available and T 1 priority task request for is scheduled resource S and waits for a gets blocked lower priority here task T 1 T 3 completes T 2 K 1 K 2 Preempted by higher K 3 priority task T 2 T 3 T 3 0 Total blocking time for task T 1 = (K 2+K 3) + (L 1) 15
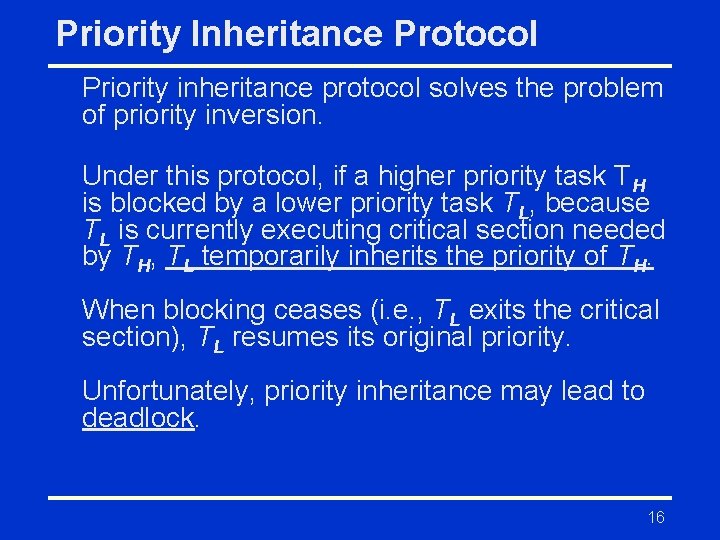
Priority Inheritance Protocol Priority inheritance protocol solves the problem of priority inversion. Under this protocol, if a higher priority task TH is blocked by a lower priority task TL, because TL is currently executing critical section needed by TH, TL temporarily inherits the priority of TH. When blocking ceases (i. e. , TL exits the critical section), TL resumes its original priority. Unfortunately, priority inheritance may lead to deadlock. 16
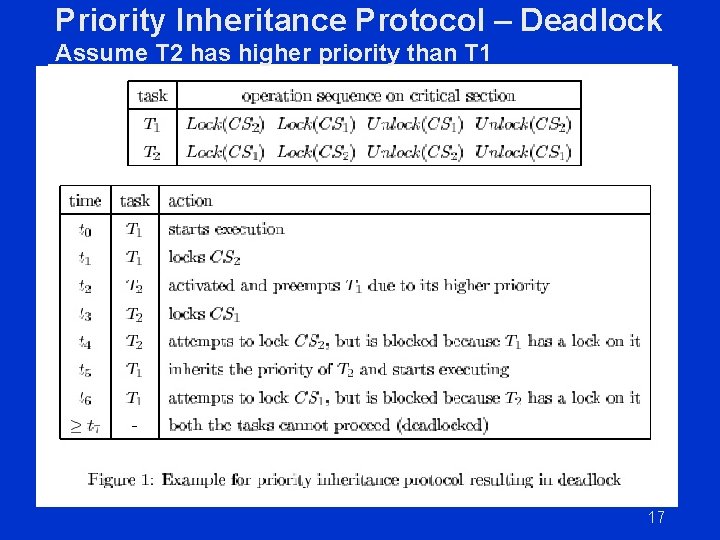
Priority Inheritance Protocol – Deadlock Assume T 2 has higher priority than T 1 17
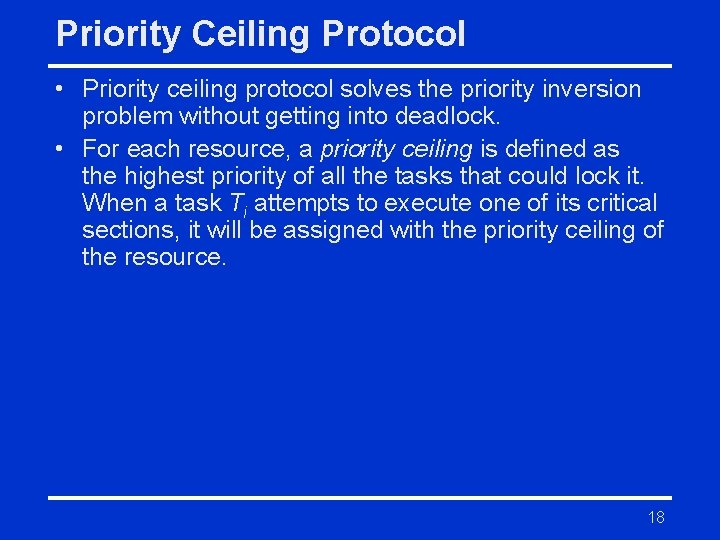
Priority Ceiling Protocol • Priority ceiling protocol solves the priority inversion problem without getting into deadlock. • For each resource, a priority ceiling is defined as the highest priority of all the tasks that could lock it. When a task Ti attempts to execute one of its critical sections, it will be assigned with the priority ceiling of the resource. 18
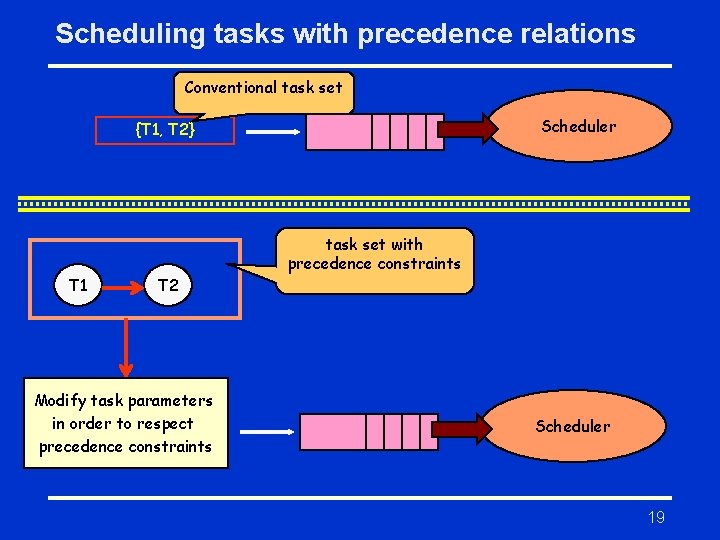
Scheduling tasks with precedence relations Conventional task set Scheduler {T 1, T 2} T 1 T 2 Modify task parameters in order to respect precedence constraints task set with precedence constraints Scheduler 19
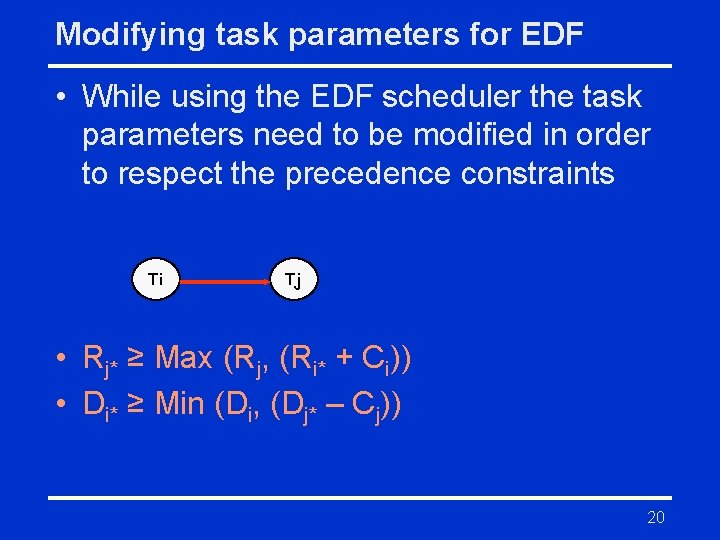
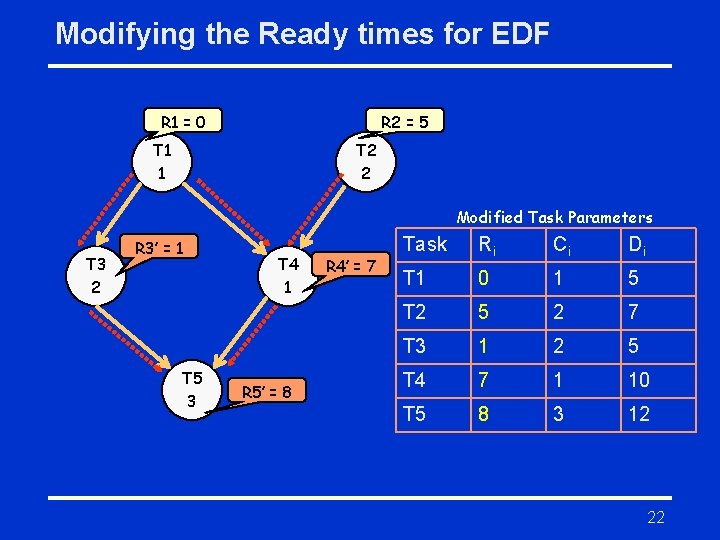
Modifying task parameters for EDF • While using the EDF scheduler the task parameters need to be modified in order to respect the precedence constraints Ti Tj • Rj* ≥ Max (Rj, (Ri* + Ci)) • Di* ≥ Min (Di, (Dj* – Cj)) 20
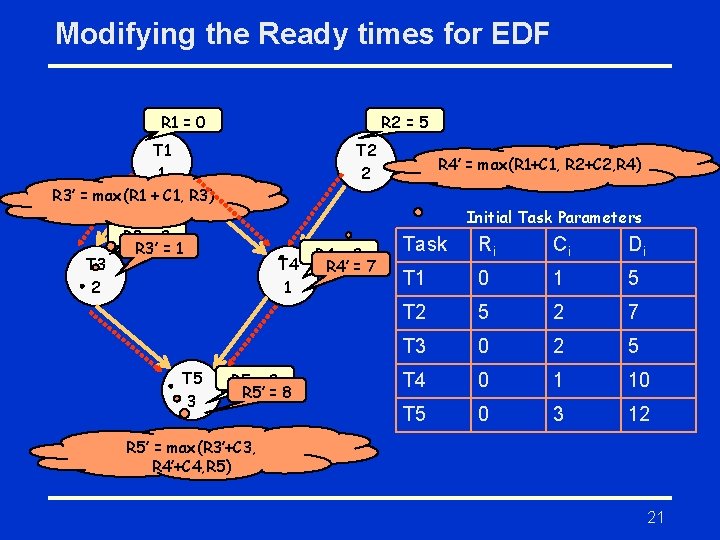
Modifying the Ready times for EDF R 1 = 0 R 2 = 5 T 1 1 R 3’ = max(R 1 + C 1, R 3) T 3 2 T 2 2 Initial Task Parameters R 3 = 0 R 3’ = 1 T 5 3 R 4’ = max(R 1+C 1, R 2+C 2, R 4) T 4 1 R 5 = 0 R 5’ = 8 R 4 = 0 R 4’ = 7 Task Ri Ci Di T 1 0 1 5 T 2 5 2 7 T 3 0 2 5 T 4 0 1 10 T 5 0 3 12 R 5’ = max(R 3’+C 3, R 4’+C 4, R 5) 21
Modifying the Ready times for EDF R 1 = 0 R 2 = 5 T 1 1 T 2 2 Modified Task Parameters T 3 2 R 3’ = 1 T 5 3 T 4 1 R 5’ = 8 R 4’ = 7 Task Ri Ci Di T 1 0 1 5 T 2 5 2 7 T 3 1 2 5 T 4 7 1 10 T 5 8 3 12 22
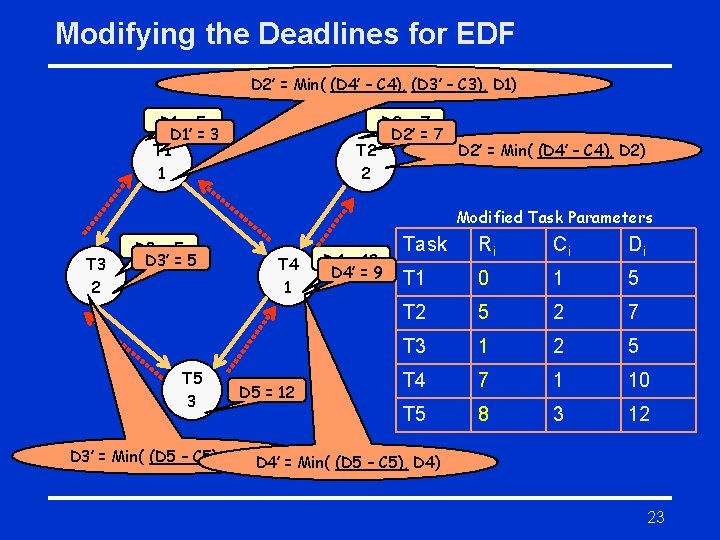
Modifying the Deadlines for EDF D 2’ = Min( (D 4’ – C 4), (D 3’ – C 3), D 1) D 1 = 5 D 1’ = 3 T 1 1 T 2 2 D 2 = 7 D 2’ = Min( (D 4’ – C 4), D 2) Modified Task Parameters T 3 2 D 3 = 5 D 3’ = 5 T 5 3 T 4 1 D 5 = 12 D 4 = 10 D 4’ = 9 Task Ri Ci Di T 1 0 1 5 T 2 5 2 7 T 3 1 2 5 T 4 7 1 10 T 5 8 3 12 D 3’ = Min( (D 5 – C 5), D 3) D 4’ = Min( (D 5 – C 5), D 4) 23
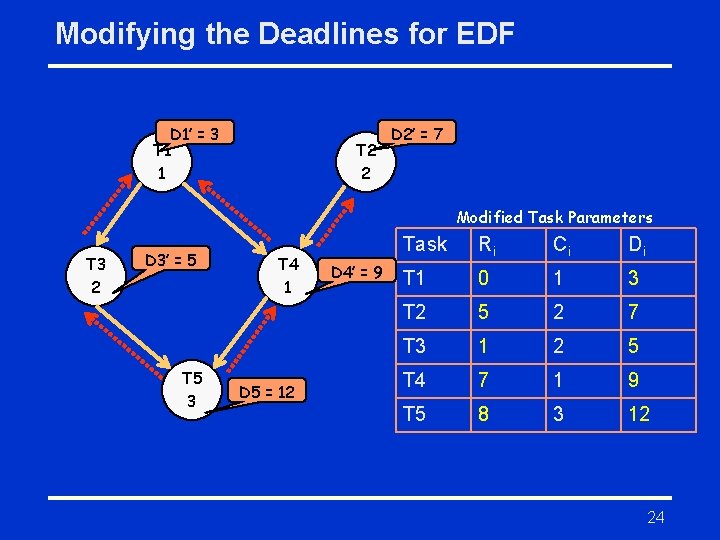
Modifying the Deadlines for EDF D 1’ = 3 T 1 1 T 2 2 D 2’ = 7 Modified Task Parameters T 3 2 D 3’ = 5 T 5 3 T 4 1 D 5 = 12 D 4’ = 9 Task Ri Ci Di T 1 0 1 3 T 2 5 2 7 T 3 1 2 5 T 4 7 1 9 T 5 8 3 12 24
Summary • • • What are RMS and EDF? Do they have fixed or dynamic priority? What is the resource sharing? What is the precedence constraint? How to update task parameters in EDF? 25
- Slides: 25