Eco Struxure IT Cybersecurity Confidential Property of Schneider

Eco. Struxure IT Cybersecurity Confidential Property of Schneider Electric |
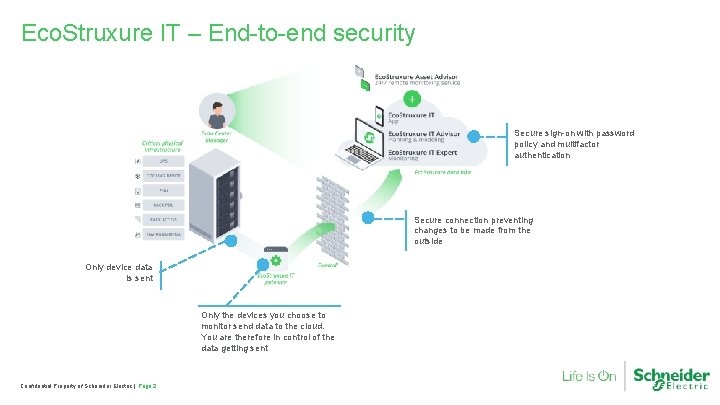
Eco. Struxure IT – End-to-end security Secure sign-on with password policy and multifactor authentication Secure connection preventing changes to be made from the outside Only device data is sent Only the devices you choose to monitor send data to the cloud. You are therefore in control of the data getting sent Confidential Property of Schneider Electric | Page 2
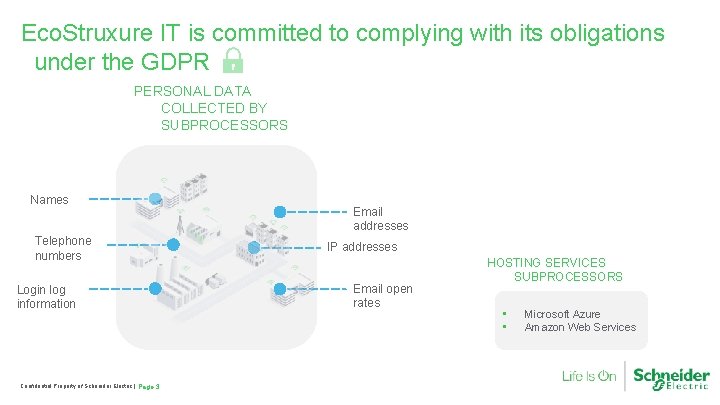
Eco. Struxure IT is committed to complying with its obligations under the GDPR PERSONAL DATA COLLECTED BY SUBPROCESSORS Names Telephone numbers Login log information Confidential Property of Schneider Electric | Page 3 Email addresses IP addresses Email open rates HOSTING SERVICES SUBPROCESSORS • • Microsoft Azure Amazon Web Services
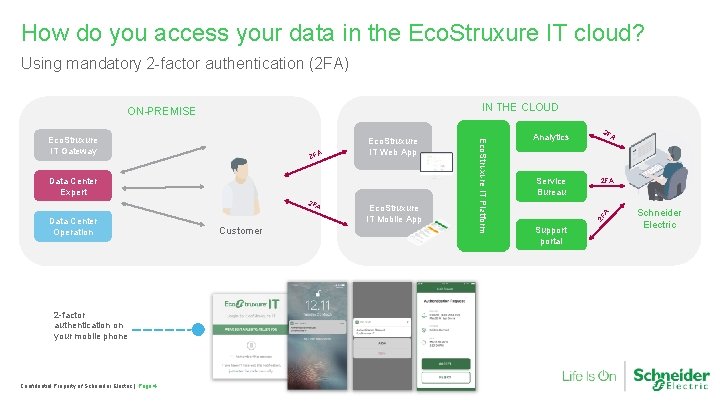
How do you access your data in the Eco. Struxure IT cloud? Using mandatory 2 -factor authentication (2 FA) IN THE CLOUD Data Center Expert 2 FA Data Center Operation 2 -factor authentication on your mobile phone Confidential Property of Schneider Electric | Page 4 Customer Eco. Struxure IT Mobile App Analytics Service Bureau 2 F A 2 FA Eco. Struxure IT Web App Eco. Struxure IT Platform Eco. Struxure IT Gateway 2 F ON-PREMISE Supportal Schneider Electric
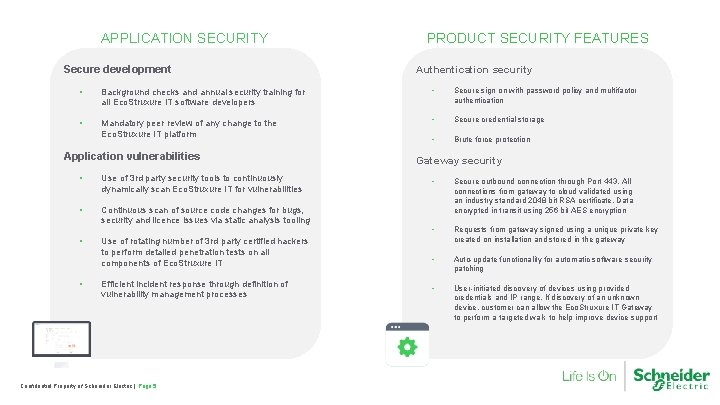
APPLICATION SECURITY Secure development PRODUCT SECURITY FEATURES Authentication security • Background checks and annual security training for all Eco. Struxure IT software developers • Secure sign on with password policy and multifactor authentication • Mandatory peer review of any change to the Eco. Struxure IT platform • Secure credential storage • Brute force protection Application vulnerabilities • Use of 3 rd party security tools to continuously dynamically scan Eco. Struxure IT for vulnerabilities • Continuous scan of source code changes for bugs, security and licence issues via static analysis tooling • Use of rotating number of 3 rd party certified hackers to perform detailed penetration tests on all components of Eco. Struxure IT • Efficient incident response through definition of vulnerability management processes Confidential Property of Schneider Electric | Page 5 Gateway security • Secure outbound connection through Port 443. All connections from gateway to cloud validated using an industry standard 2048 bit RSA certificate. Data encrypted in transit using 256 bit AES encryption • Requests from gateway signed using a unique private key created on installation and stored in the gateway • Auto-update functionality for automatic software security patching • User-initiated discovery of devices using provided credentials and IP range. If discovery of an unknown device, customer can allow the Eco. Struxure IT Gateway to perform a targeted walk to help improve device support
DATA CENTER & NETWORK SECURITY • Eco. Struxure IT servers hosted in the United States on Microsoft Azure Cloud, EU-US Privacy Shield certified • Network security • Access to Eco. Struxure IT Production Network restricted by explicit need-to-know basis • Use of Azure always-on traffic monitoring and realtime mitigation of common network-level attacks • • Continuous employment of rotating number of 3 rd party certified hackers to perform detailed penetration tests of Eco. Struxure IT platform Data privacy at Schneider Electric: https: //www. schneider-electric. com/en/aboutus/legal/data-privacy. jsp • Eco. Struxure IT is committed to complying with its obligations under the GDPR. Sharing of personal information with 3 rd party data processors on a need-to-know basis • Collection of machine data only, tagged to specific customer. No access from Eco. Struxure IT to data stored on customer server • Use of customer machine data to optimize Eco. Struxure IT products and services • First cybersecurity certification planned in H 1 2019 • • • DATA PRIVACY Continuous monitoring and scanning of Eco. Struxure IT system for potential security vulnerabilities. Validation of connections to Eco. Struxure IT cloud using industry standard 2048 bit RSA certificate. Encryption of data in transit and at rest using 256 bit AES encryption Deployment of components of Eco. Struxure IT platform in high availability configuration to eliminate single point of failure. Data back up to prevent data loss Confidential Property of Schneider Electric | Page 6
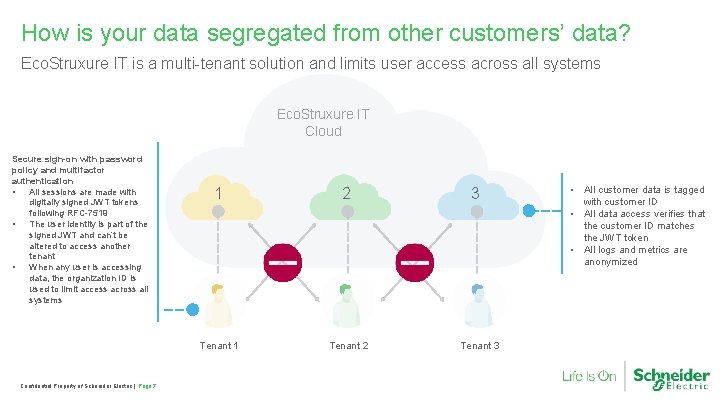
How is your data segregated from other customers’ data? Eco. Struxure IT is a multi-tenant solution and limits user access across all systems Eco. Struxure IT Cloud Secure sign-on with password policy and multifactor authentication • All sessions are made with digitally signed JWT tokens following RFC-7519 • The user identity is part of the signed JWT and can’t be altered to access another tenant • When any user is accessing data, the organization ID is used to limit access across all systems Confidential Property of Schneider Electric | Page 7 1 2 Tenant 1 Tenant 2 3 Tenant 3 • All customer data is tagged with customer ID • All data access verifies that the customer ID matches the JWT token • All logs and metrics are anonymized
What is the Eco. Struxure IT Gateway? The Eco. Struxure IT Gateway software collects data from your devices and sends it to the Eco. Struxure IT cloud. It is an enabler of the Eco. Struxure IT solution. Before you can start monitoring your devices with Eco. Struxure IT: ü Ask your security expert for approval ü Allow the installation of the Windows or Linux -based Eco. Struxure IT Gateway Software ü Allow the configuration of the Firewall for one outbound-only connection Confidential Property of Schneider Electric | Page 8
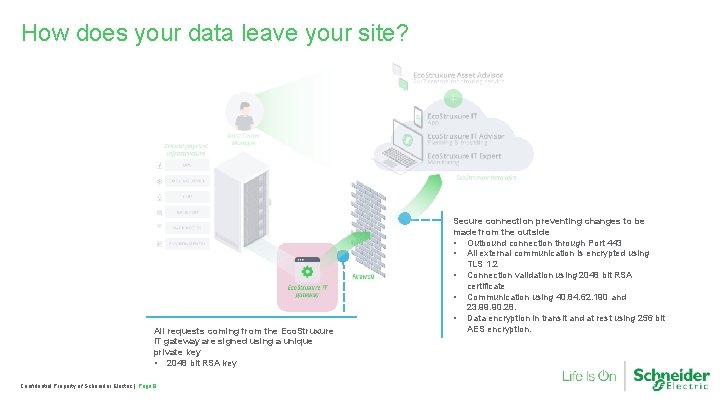
How does your data leave your site? All requests coming from the Eco. Struxure IT gateway are signed using a unique private key • 2048 bit RSA key Confidential Property of Schneider Electric | Page 9 Secure connection preventing changes to be made from the outside • Outbound connection through Port 443 • All external communication is encrypted using TLS 1. 2 • Connection validation using 2048 bit RSA certificate • Communication using 40. 84. 62. 190 and 23. 99. 90. 28. • Data encryption in transit and at rest using 256 bit AES encryption.
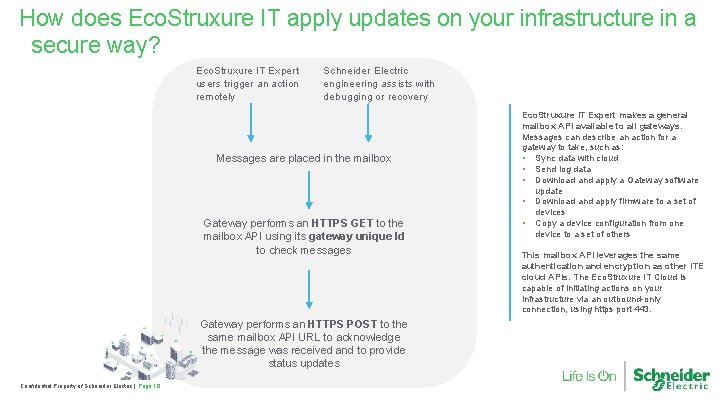
How does Eco. Struxure IT apply updates on your infrastructure in a secure way? Eco. Struxure IT Expert users trigger an action remotely Schneider Electric engineering assists with debugging or recovery Messages are placed in the mailbox Gateway performs an HTTPS GET to the mailbox API using its gateway unique Id to check messages Gateway performs an HTTPS POST to the same mailbox API URL to acknowledge the message was received and to provide status updates Confidential Property of Schneider Electric | Page 10 Eco. Struxure IT Expert makes a general mailbox API available to all gateways. Messages can describe an action for a gateway to take, such as: • Sync data with cloud • Send log data • Download and apply a Gateway software update • Download and apply firmware to a set of devices • Copy a device configuration from one device to a set of others This mailbox API leverages the same authentication and encryption as other ITE cloud APIs. The Eco. Struxure IT Cloud is capable of initiating actions on your infrastructure via an outbound-only connection, using https port 443.
Schneider Electric security test report sharing policy Our intent • To help protect our customers’ investment in our products and solutions. • Schneider Electric does not provide detailed security test reports or release detailed information about specific security vulnerabilities or enhancements unless they are associated with a publicly disclosed vulnerability and resolution. What we can do • Provide a summary version of a security test report upon request and under non-disclosure agreement (NDA). • It may detail scope, approach, qualifications, categorical results, and mitigation status, as applicable. • Contact your sales representative for more information. Learn more about our security test sharing policy Confidential Property of Schneider Electric | Page 11
Additional cybersecurity resources Eco. Struxure IT security webpage https: //ecostruxureit. com/security/ Confidential Property of Schneider Electric | Page 12 Eco. Struxure IT list of subprocessors https: //ecostruxureit. com/subprocessors-and-subcontractors

- Slides: 13