ECE 424 Embedded Systems Design Networking Connectivity Chapter
ECE 424 Embedded Systems Design Networking Connectivity Chapter 12 Ning Weng
Networking Overview • Goal: key concepts and system details to integrate network connectivity into embedded systems Ning Weng ECE 424 2
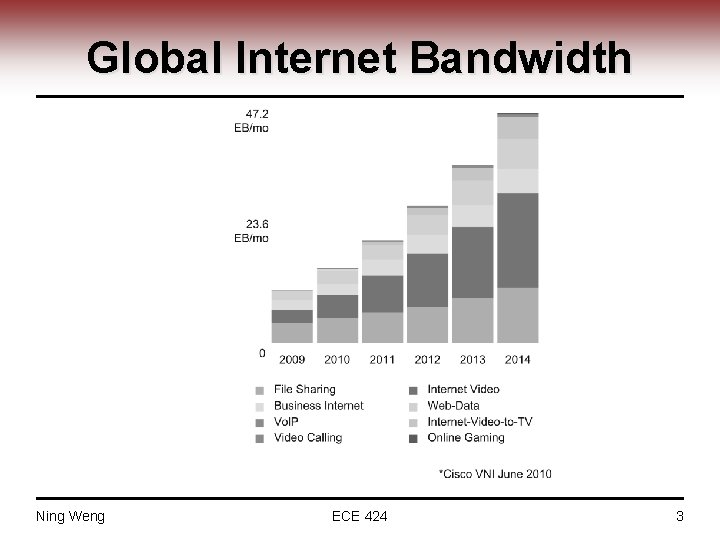
Global Internet Bandwidth Ning Weng ECE 424 3
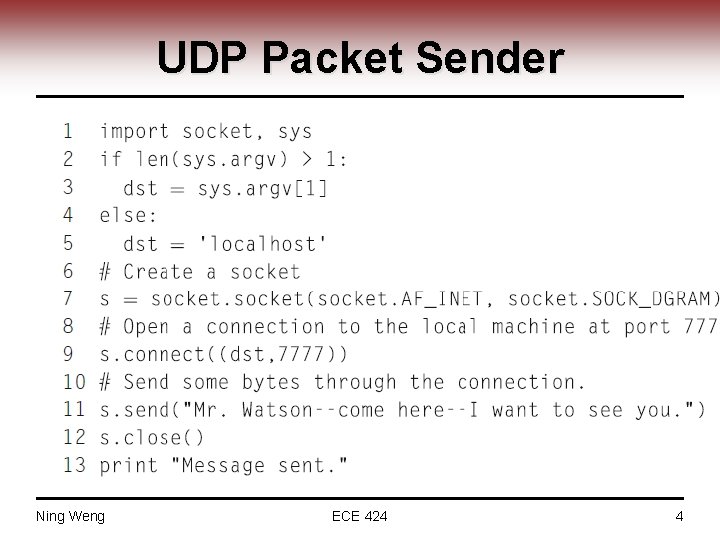
UDP Packet Sender Ning Weng ECE 424 4
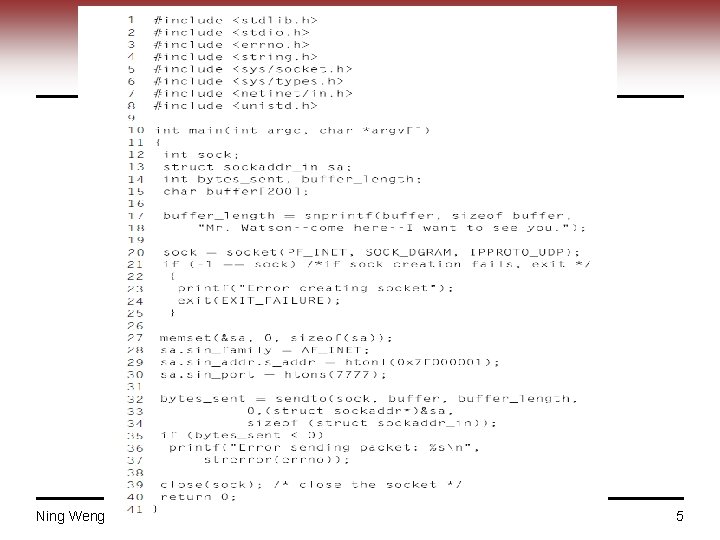
UDP Packet Sender in C Ning Weng ECE 424 5
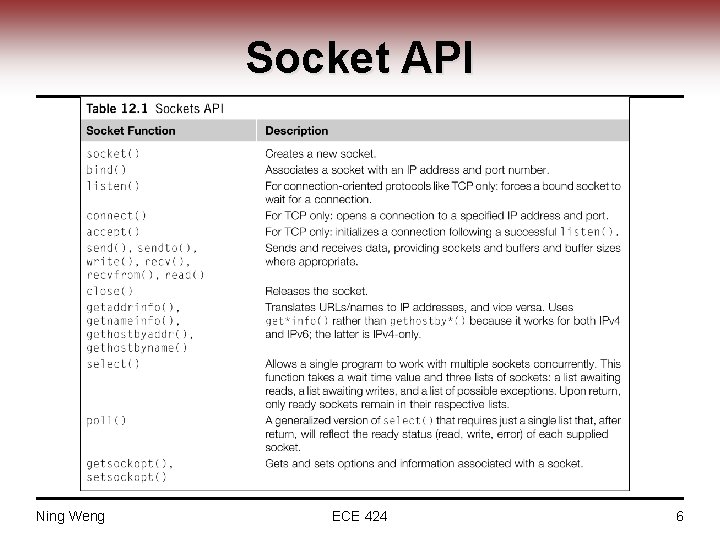
Socket API Ning Weng ECE 424 6
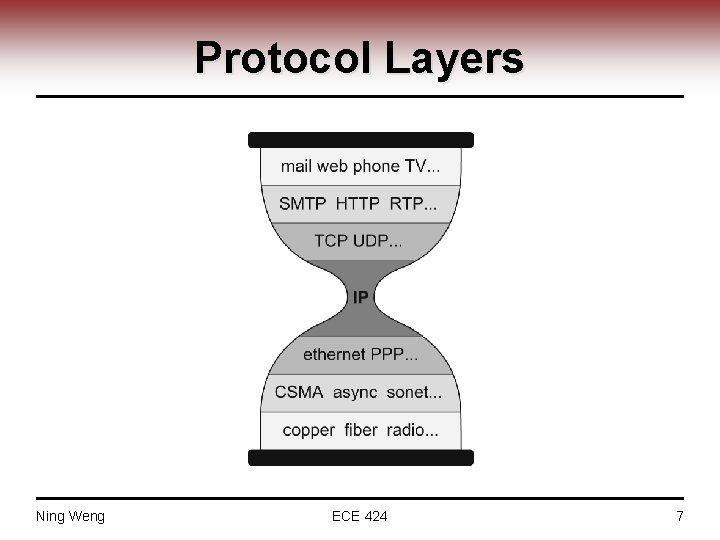
Protocol Layers Ning Weng ECE 424 7
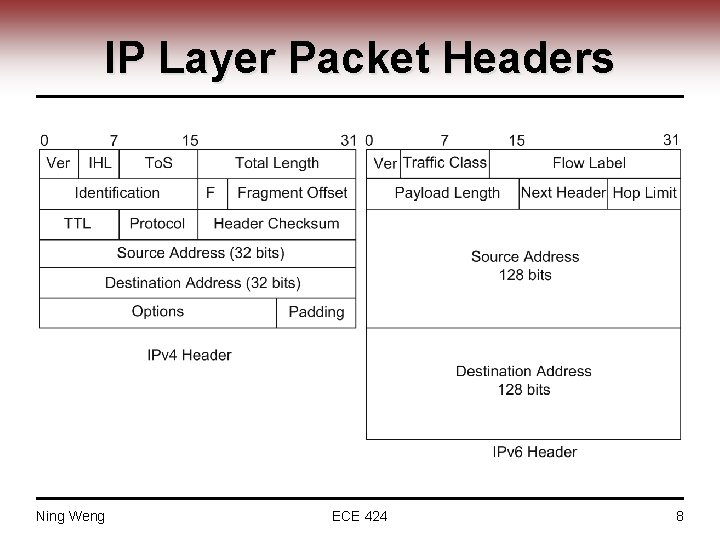
IP Layer Packet Headers Ning Weng ECE 424 8
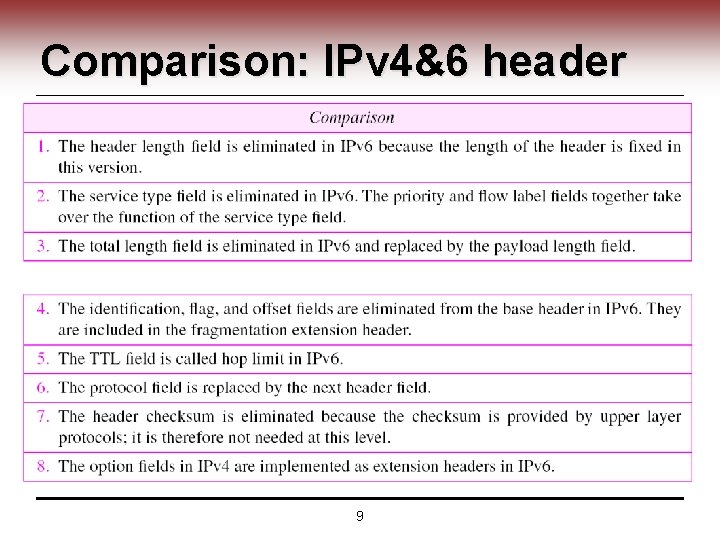
Comparison: IPv 4&6 header 9
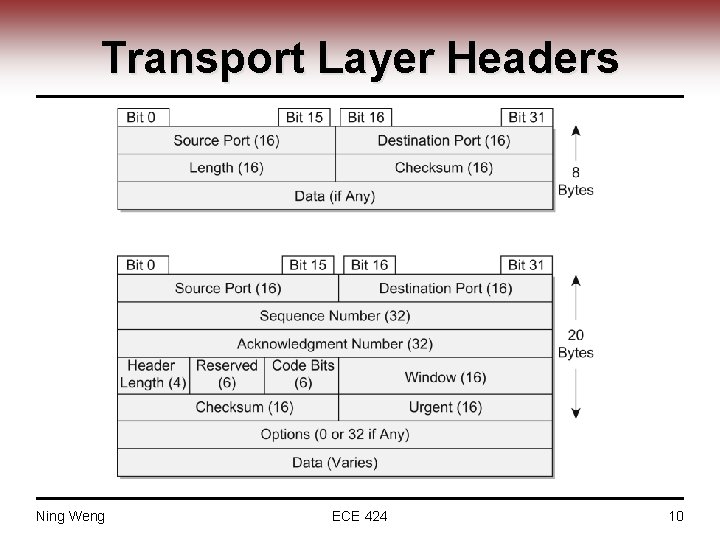
Transport Layer Headers Ning Weng ECE 424 10
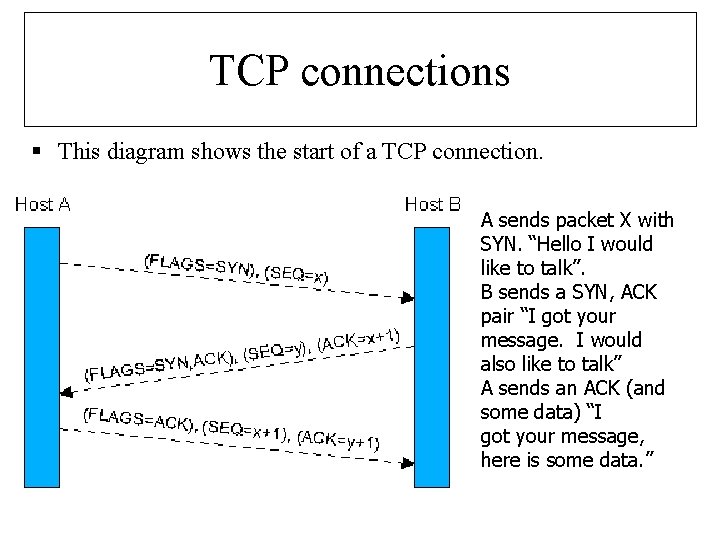
TCP connections § This diagram shows the start of a TCP connection. A sends packet X with SYN. “Hello I would like to talk”. B sends a SYN, ACK pair “I got your message. I would also like to talk” A sends an ACK (and some data) “I got your message, here is some data. ”
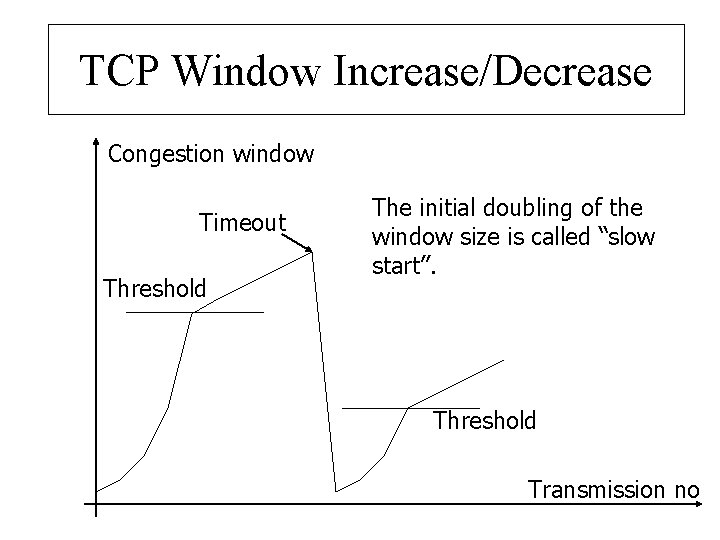
TCP Window Increase/Decrease Congestion window Timeout Threshold The initial doubling of the window size is called “slow start”. Threshold Transmission no
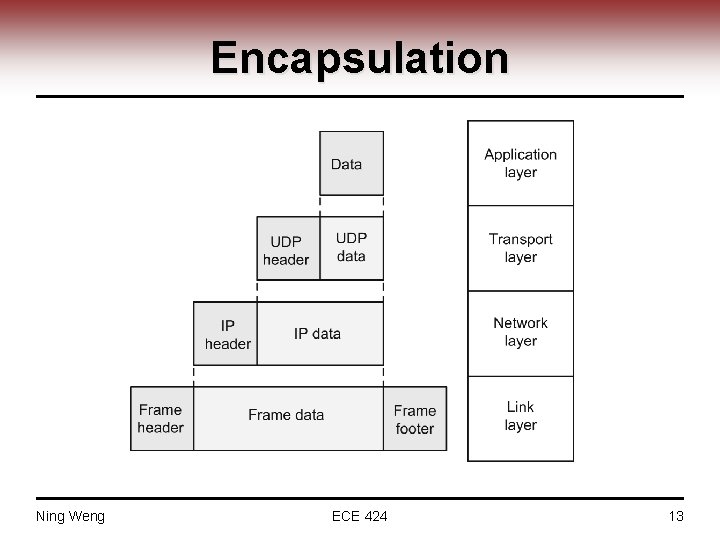
Encapsulation Ning Weng ECE 424 13
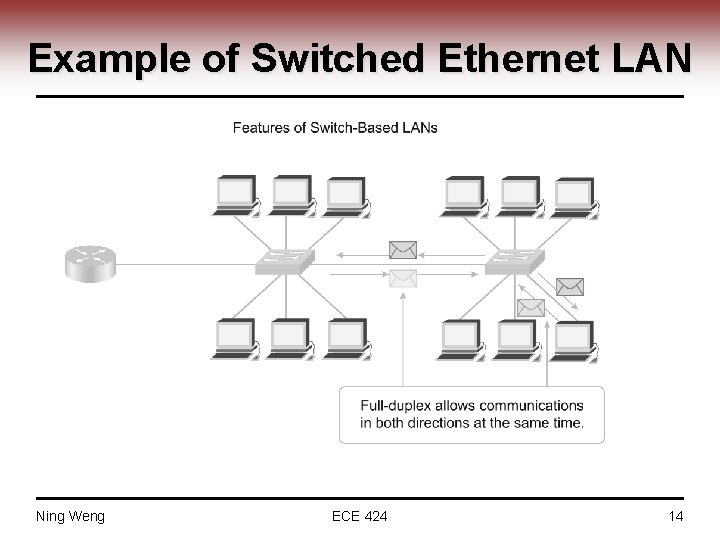
Example of Switched Ethernet LAN Ning Weng ECE 424 14
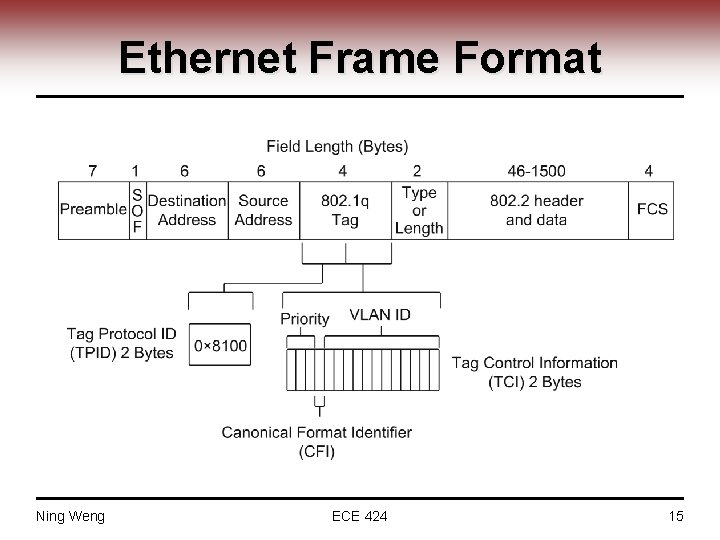
Ethernet Frame Format Ning Weng ECE 424 15
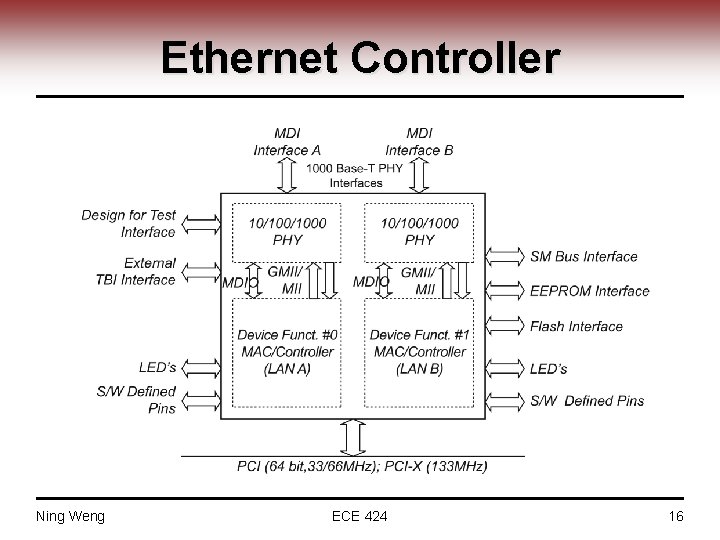
Ethernet Controller Ning Weng ECE 424 16
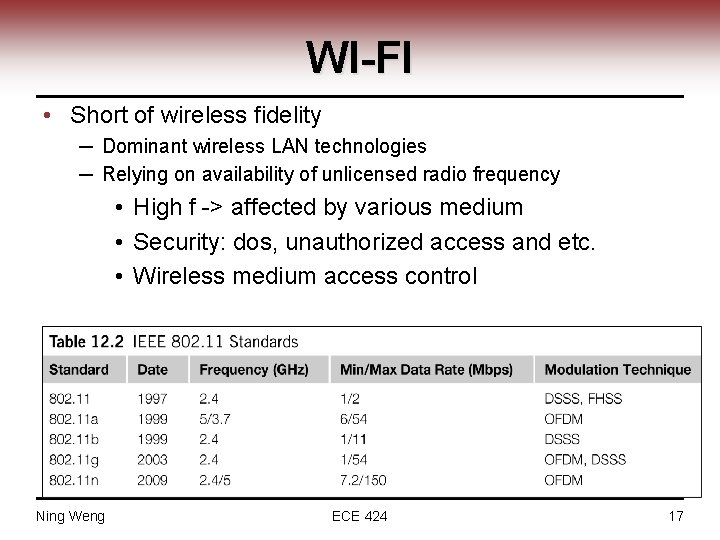
WI-FI • Short of wireless fidelity ─ Dominant wireless LAN technologies ─ Relying on availability of unlicensed radio frequency • High f -> affected by various medium • Security: dos, unauthorized access and etc. • Wireless medium access control Ning Weng ECE 424 17
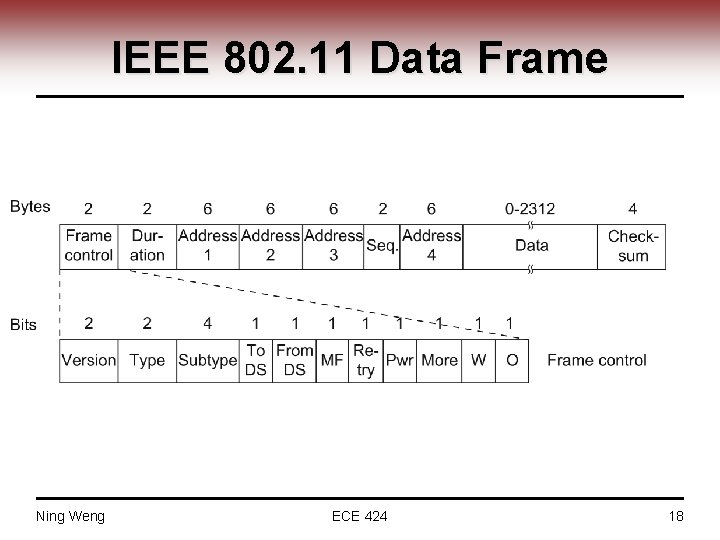
IEEE 802. 11 Data Frame Ning Weng ECE 424 18
Basic Security Strategies • Block your Service Set Identifier (SSID) from being broadcast. ─ Wireless beacon so PCs can easily find the access point. • Change the default network name in the access point. • Change the default access point password. • Center the access point in the middle of the building/house.
Media Access Control (MAC) Filtering • Every network device has a unique MAC address ─ Allocated by the manufacturer. • MAC Filtering only allows certain addresses access. • Mostly for home use. ─ Tedious to implement on a large scale
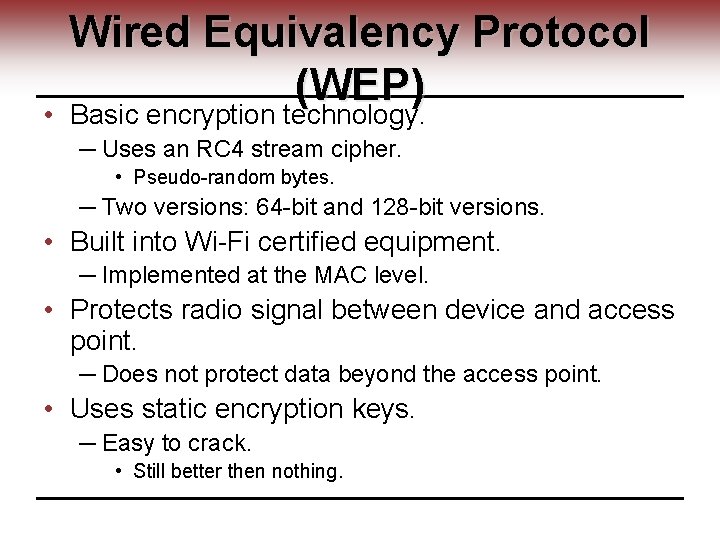
Wired Equivalency Protocol (WEP) • Basic encryption technology. ─ Uses an RC 4 stream cipher. • Pseudo-random bytes. ─ Two versions: 64 -bit and 128 -bit versions. • Built into Wi-Fi certified equipment. ─ Implemented at the MAC level. • Protects radio signal between device and access point. ─ Does not protect data beyond the access point. • Uses static encryption keys. ─ Easy to crack. • Still better then nothing.
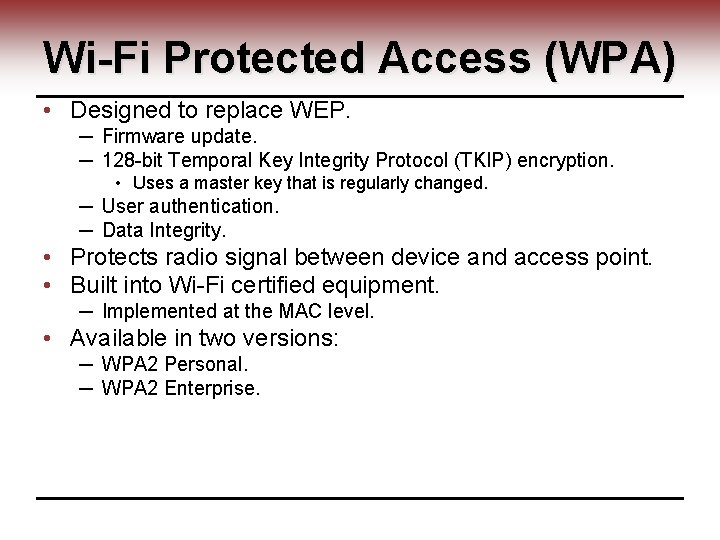
Wi-Fi Protected Access (WPA) • Designed to replace WEP. ─ Firmware update. ─ 128 -bit Temporal Key Integrity Protocol (TKIP) encryption. • Uses a master key that is regularly changed. ─ User authentication. ─ Data Integrity. • Protects radio signal between device and access point. • Built into Wi-Fi certified equipment. ─ Implemented at the MAC level. • Available in two versions: ─ WPA 2 Personal. ─ WPA 2 Enterprise.
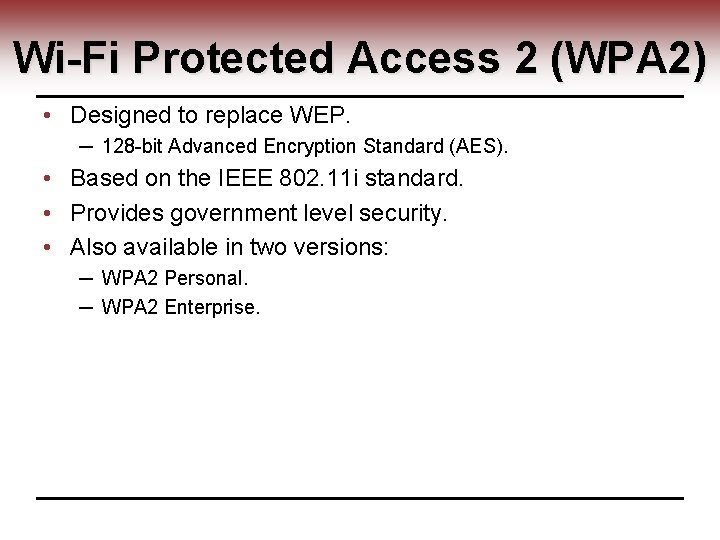
Wi-Fi Protected Access 2 (WPA 2) • Designed to replace WEP. ─ 128 -bit Advanced Encryption Standard (AES). • Based on the IEEE 802. 11 i standard. • Provides government level security. • Also available in two versions: ─ WPA 2 Personal. ─ WPA 2 Enterprise.
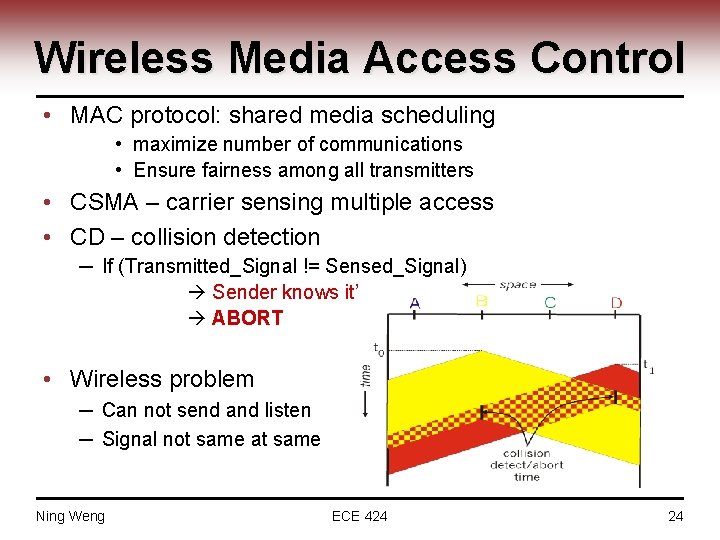
Wireless Media Access Control • MAC protocol: shared media scheduling • maximize number of communications • Ensure fairness among all transmitters • CSMA – carrier sensing multiple access • CD – collision detection ─ If (Transmitted_Signal != Sensed_Signal) Sender knows it’s a Collision ABORT • Wireless problem ─ Can not send and listen ─ Signal not same at same Ning Weng ECE 424 24
Bluetooth Overview • Bluetooth is a global, RF-based (ISM band: 2. 4 GHz), short-range, connectivity solution for portable, personal devices ─ it is not just a radio, it is an end-to-end solution • The Bluetooth spec comprises ─ a HW & SW protocol specification ─ usage case scenario profiles and interoperability requirements • IEEE 802. 15. 1 is working on standardizing the PHY and MAC layers in Bluetooth • More Info: ─ http: //www. bluetooth. org ─ http: //ieee 802. org/15/pub/TG 1. html 25
Bluetooth - Piconet • • • A collection of devices connected via Bluetooth technology in an ad hoc fashion. A piconet starts with two connected devices, and may grow to eight connected devices. All Bluetooth devices are peer units and have identical implementations. However, when establishing a piconet, one unit will act as a Master and the other(s) as slave(s) for the duration of the piconet connection.
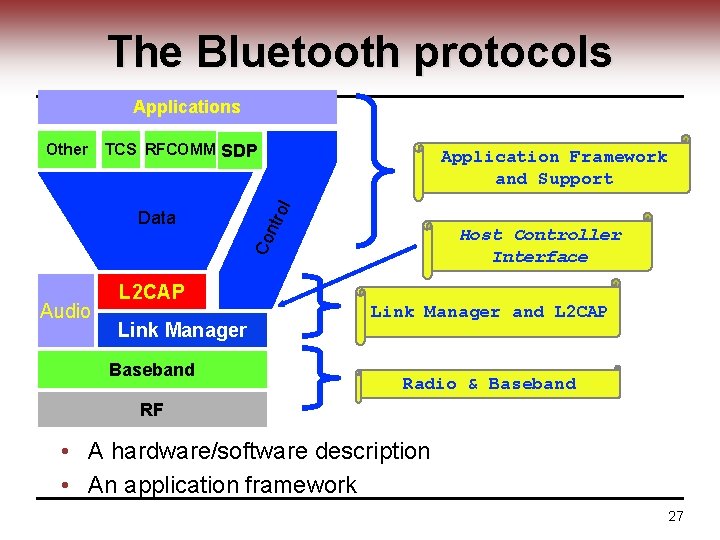
The Bluetooth protocols Applications TCS RFCOMM SDP ol Host Controller Interface Co Data Application Framework and Support ntr Other Audio L 2 CAP Link Manager Baseband Link Manager and L 2 CAP Radio & Baseband RF • A hardware/software description • An application framework 27
Linux Networking • Networking utilities ─ Ipcofig ─ Netstat • Socket implementations • Networking kernel structures Ning Weng ECE 424 28
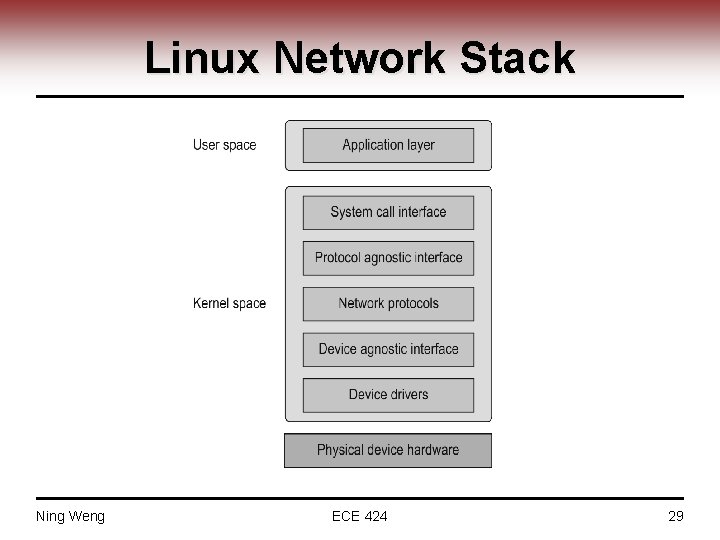
Linux Network Stack Ning Weng ECE 424 29
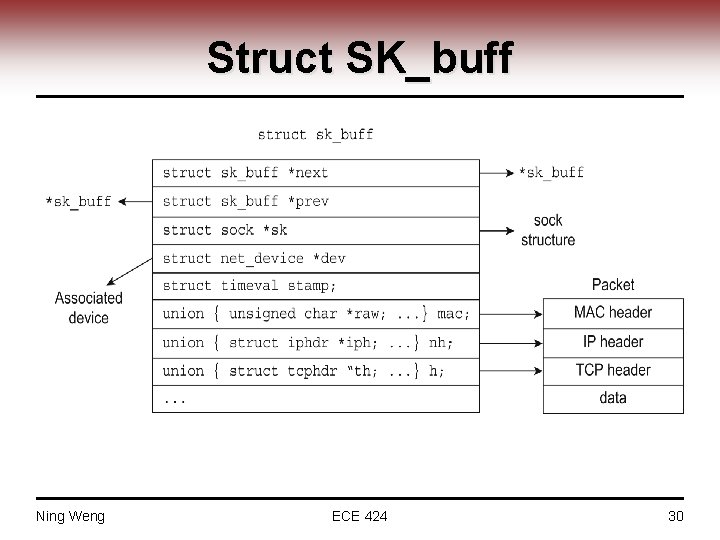
Struct SK_buff Ning Weng ECE 424 30
- Slides: 30