e Commerce Technology 20 751 Lecture 4 Web
e. Commerce Technology 20 -751 Lecture 4: Web Architecture
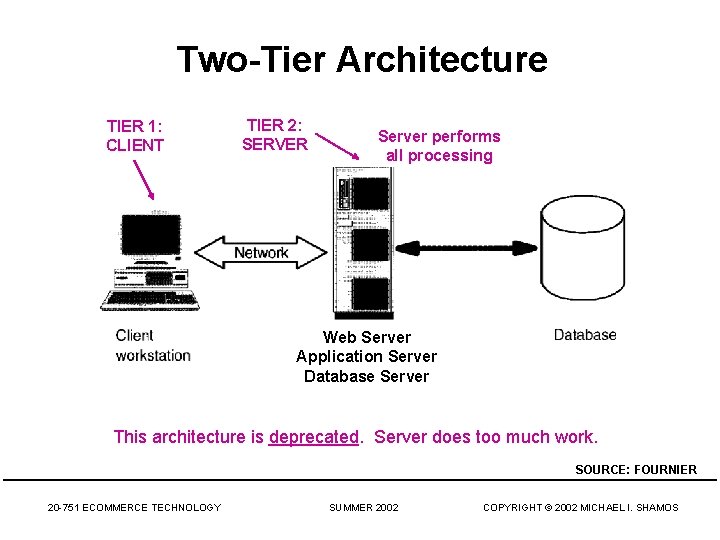
Two-Tier Architecture TIER 1: CLIENT TIER 2: SERVER Server performs all processing Web Server Application Server Database Server This architecture is deprecated. Server does too much work. SOURCE: FOURNIER 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
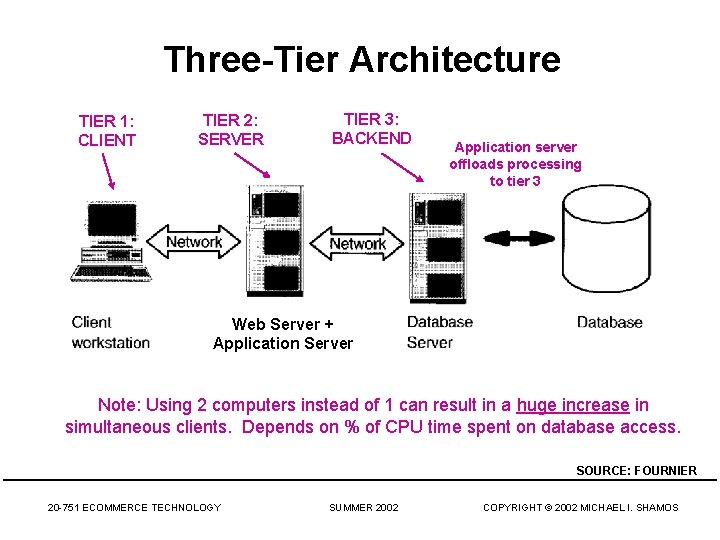
Three-Tier Architecture TIER 1: CLIENT TIER 2: SERVER TIER 3: BACKEND Application server offloads processing to tier 3 Web Server + Application Server Note: Using 2 computers instead of 1 can result in a huge increase in simultaneous clients. Depends on % of CPU time spent on database access. SOURCE: FOURNIER 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
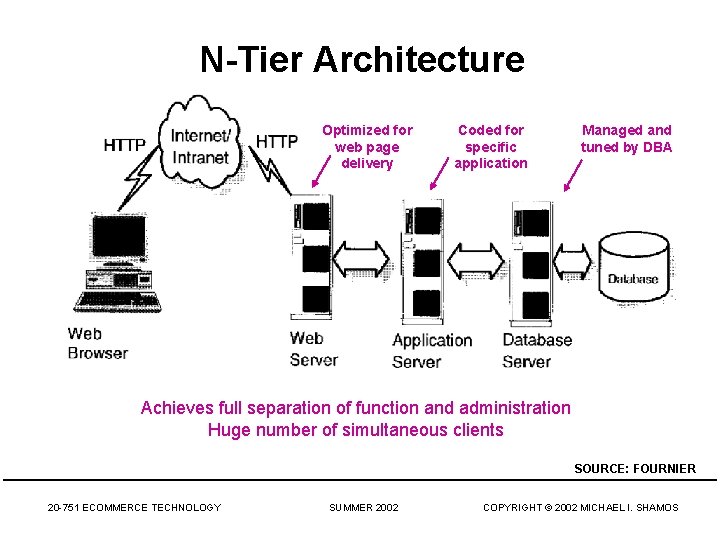
N-Tier Architecture Optimized for web page delivery Coded for specific application Managed and tuned by DBA Achieves full separation of function and administration Huge number of simultaneous clients SOURCE: FOURNIER 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
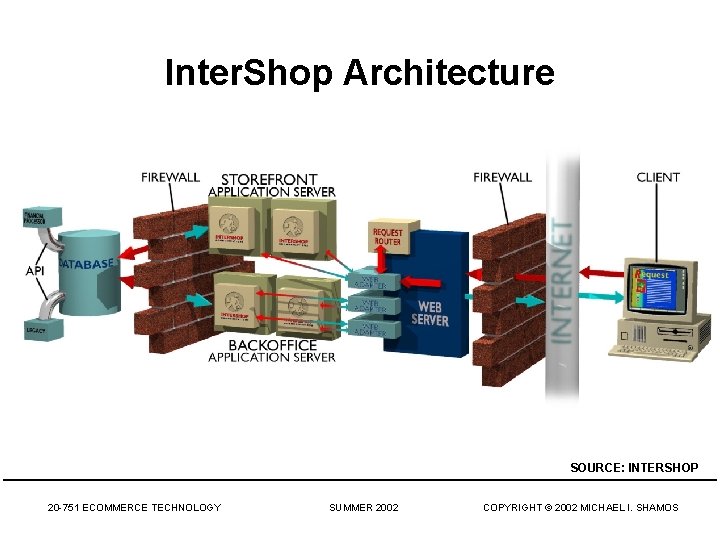
Inter. Shop Architecture SOURCE: INTERSHOP 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
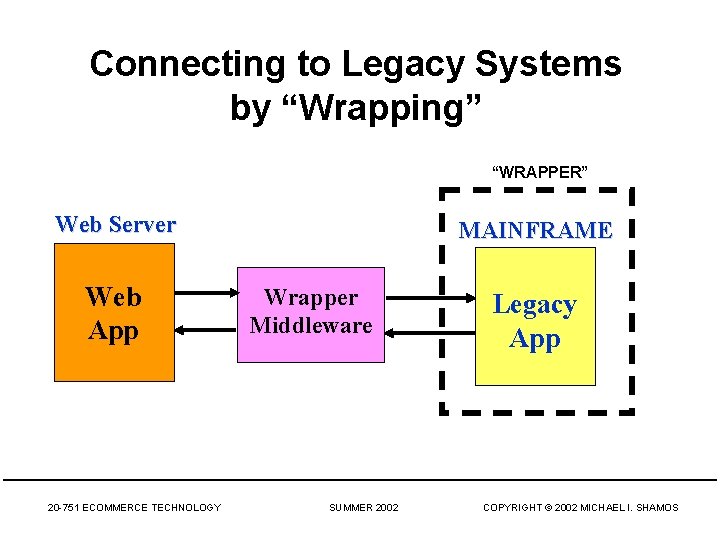
Connecting to Legacy Systems by “Wrapping” “WRAPPER” Web Server Web App 20 -751 ECOMMERCE TECHNOLOGY MAINFRAME Wrapper Middleware SUMMER 2002 Legacy App COPYRIGHT © 2002 MICHAEL I. SHAMOS
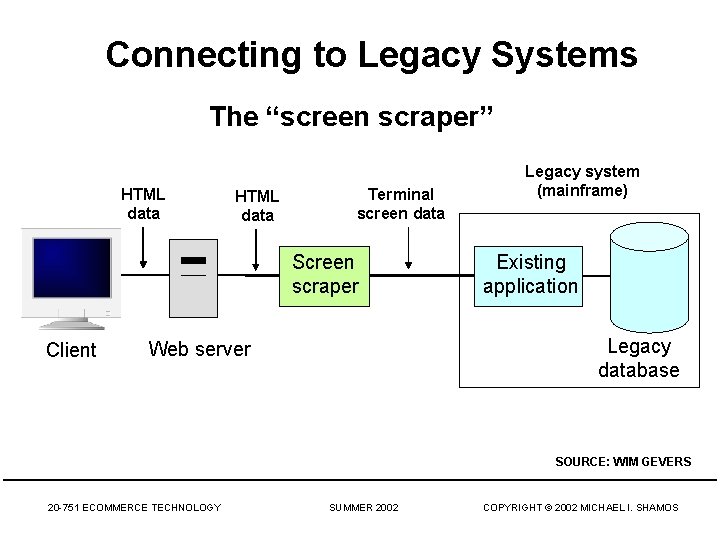
Connecting to Legacy Systems The “screen scraper” HTML data Terminal screen data Screen scraper Client Legacy system (mainframe) Existing application Legacy database Web server SOURCE: WIM GEVERS 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
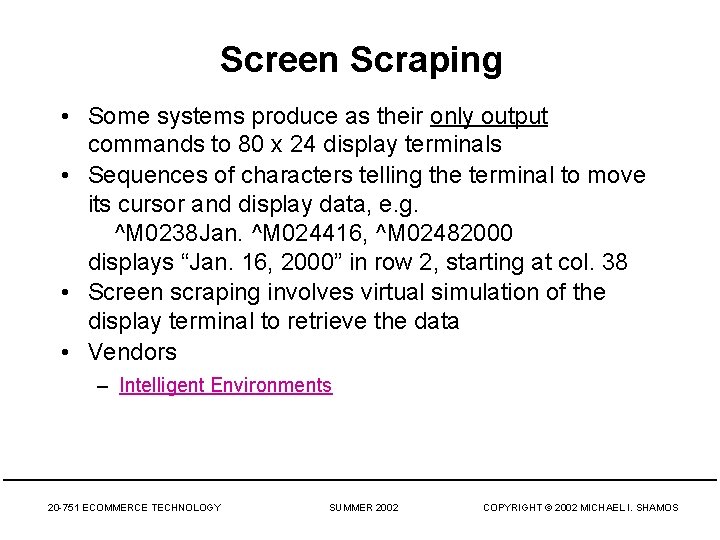
Screen Scraping • Some systems produce as their only output commands to 80 x 24 display terminals • Sequences of characters telling the terminal to move its cursor and display data, e. g. ^M 0238 Jan. ^M 024416, ^M 02482000 displays “Jan. 16, 2000” in row 2, starting at col. 38 • Screen scraping involves virtual simulation of the display terminal to retrieve the data • Vendors – Intelligent Environments 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
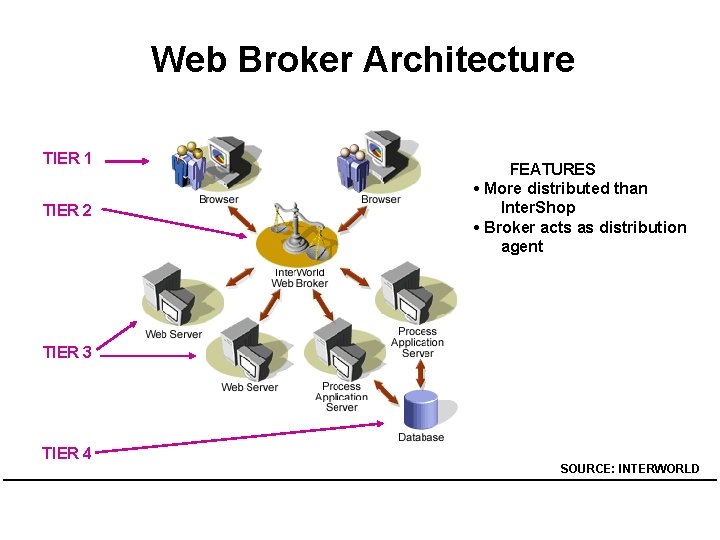
Web Broker Architecture TIER 1 TIER 2 FEATURES • More distributed than Inter. Shop • Broker acts as distribution agent TIER 3 TIER 4 SOURCE: INTERWORLD
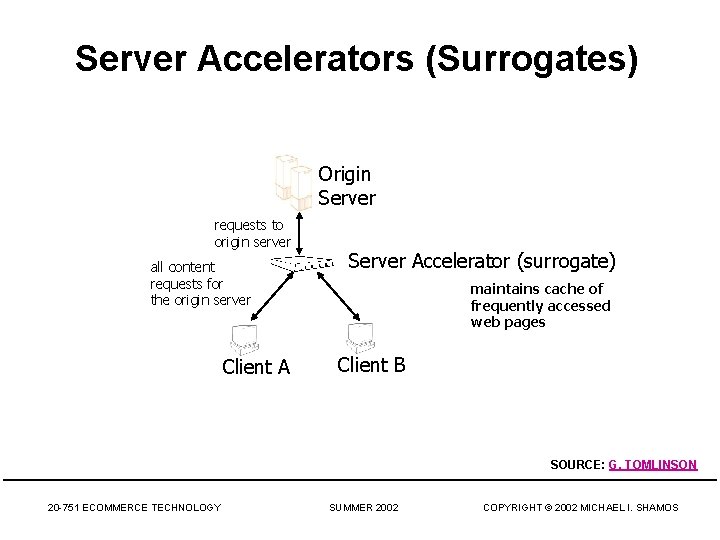
Server Accelerators (Surrogates) Origin Server requests to origin server all content requests for the origin server Client A Server Accelerator (surrogate) maintains cache of frequently accessed web pages Client B SOURCE: G. TOMLINSON 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
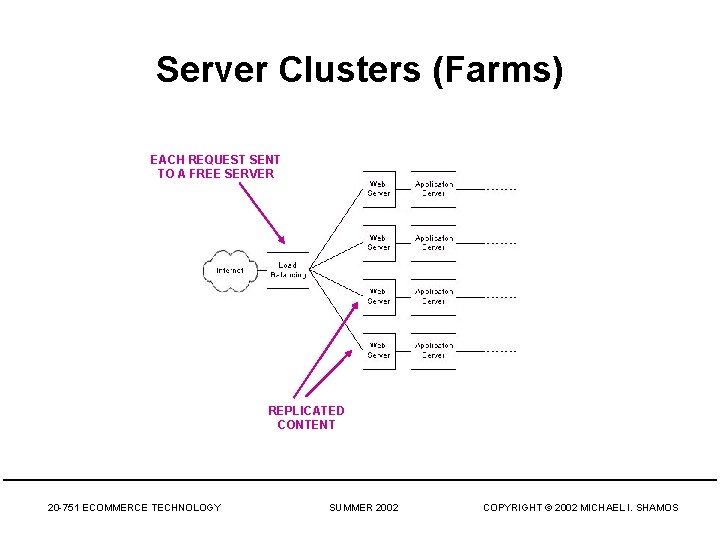
Server Clusters (Farms) EACH REQUEST SENT TO A FREE SERVER REPLICATED CONTENT 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
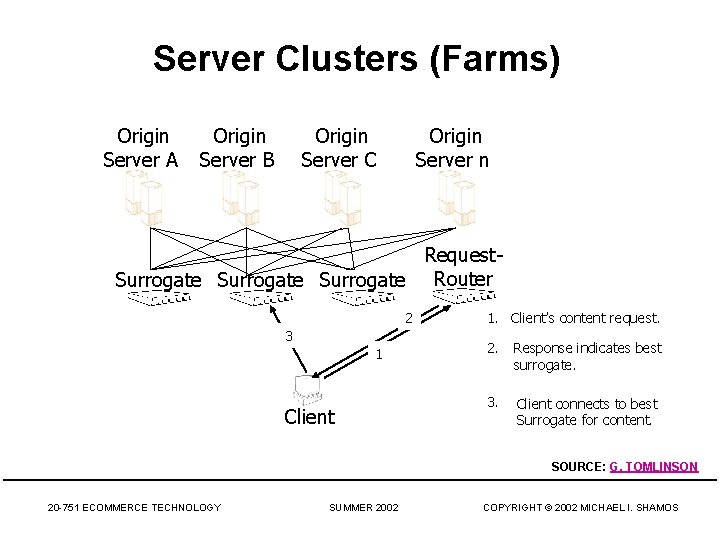
Server Clusters (Farms) Origin Server A Origin Server B Origin Server C Origin Server n Request. Surrogate Router 2 3 1 Client 1. Client’s content request. 2. Response indicates best surrogate. 3. Client connects to best Surrogate for content. SOURCE: G. TOMLINSON 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
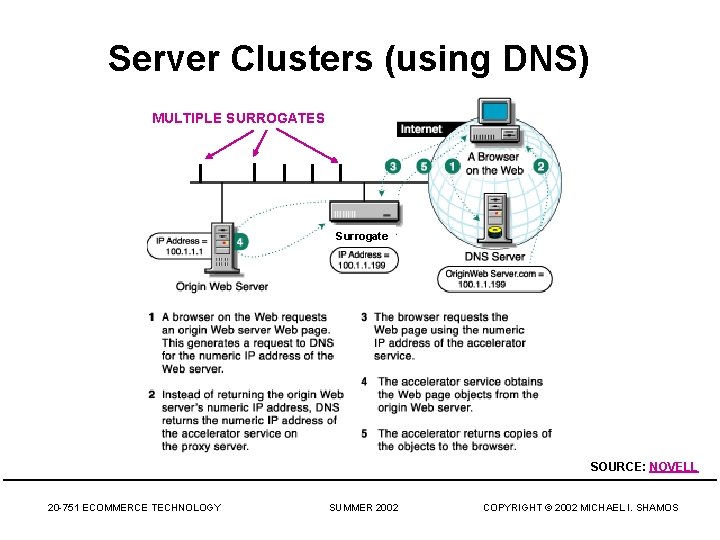
Server Clusters (using DNS) MULTIPLE SURROGATES Surrogate SOURCE: NOVELL 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
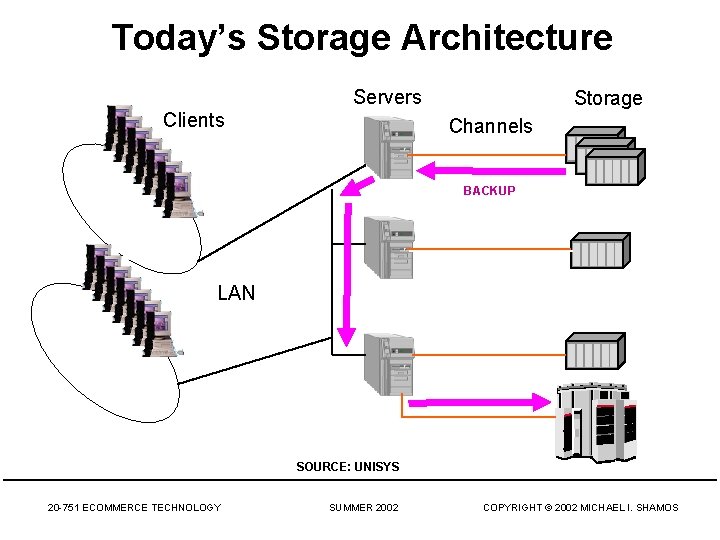
Today’s Storage Architecture Clients Servers Storage Channels BACKUP LAN SOURCE: UNISYS 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
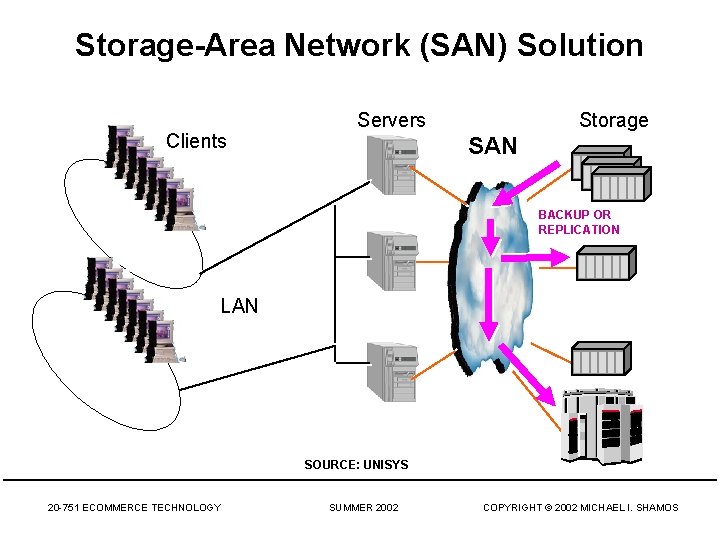
Storage-Area Network (SAN) Solution Clients Servers Storage SAN BACKUP OR REPLICATION LAN SOURCE: UNISYS 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
SAN Definition • • • Multiple paths to each resource Any-to-any connections Global Address view Open structure using industry standard protocol No node dependencies, (can function even if one or more nodes are inoperative) • Optimized for large block transfers • High bandwidth and high availability • Scales up with no performance loss SOURCE: UNISYS 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
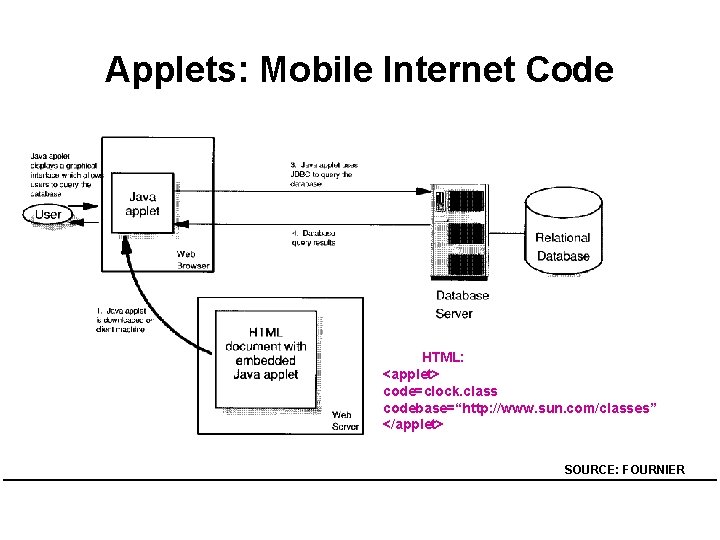
Applets: Mobile Internet Code HTML: <applet> code=clock. class codebase=“http: //www. sun. com/classes” </applet> SOURCE: FOURNIER
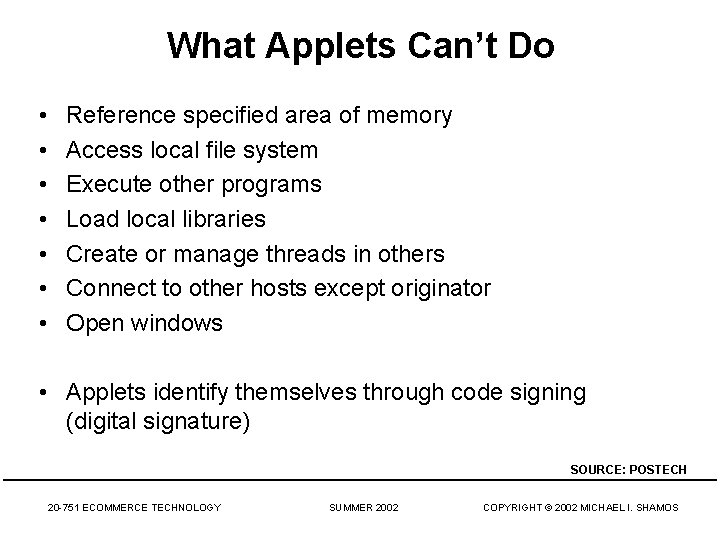
What Applets Can’t Do • • Reference specified area of memory Access local file system Execute other programs Load local libraries Create or manage threads in others Connect to other hosts except originator Open windows • Applets identify themselves through code signing (digital signature) SOURCE: POSTECH 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
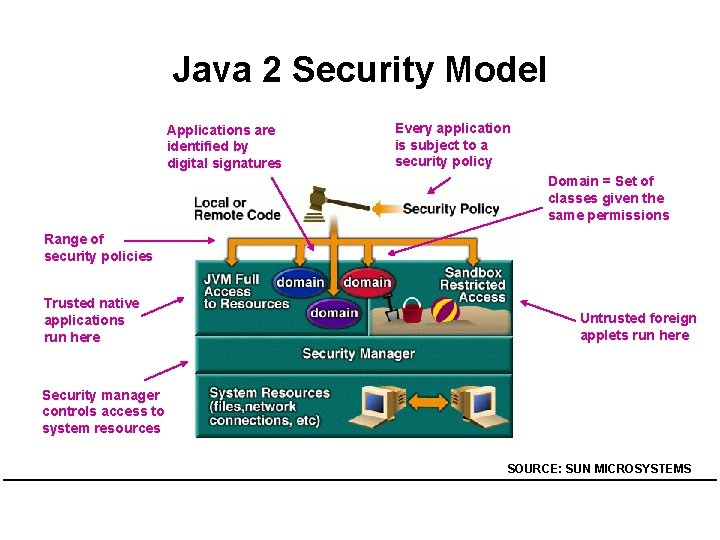
Java 2 Security Model Applications are identified by digital signatures Every application is subject to a security policy Domain = Set of classes given the same permissions Range of security policies Trusted native applications run here Untrusted foreign applets run here Security manager controls access to system resources SOURCE: SUN MICROSYSTEMS
Java Beans • Java Beans: reusable software components containing business logic for manipulation in a visual builder tool (e. g. Borland JBuilder, IBM Visual Age for Java) • Write once, run anywhere (WORA) • Properties of Beans: – Introspection: builder tool can analyze how a Bean works. get. Bean. Info(Bean. Class) – Customization: developer can use an app builder tool to customize the appearance and behavior of a Bean – Events: enables Beans to communicate and connect together – Properties: property editors to customize Beans – Persistence: developers can customize Beans, store and retrieve them, with customized features intact, for future use • Can buy and sell Beans. Visit Sun. 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
Enterprise Java Beans (EJB) • An interface specification for building scalable, distributed, component-based, multi-tier enterprisewide applications • Java Beans for server-side business applications • Platform and vendor-neutral • Java Beans extended with – transaction processing – state management – services not offered by the Java Virtual Machine • Idea: incorporate data and business logic into objects in one place in the enterprise • Employ reusable components 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
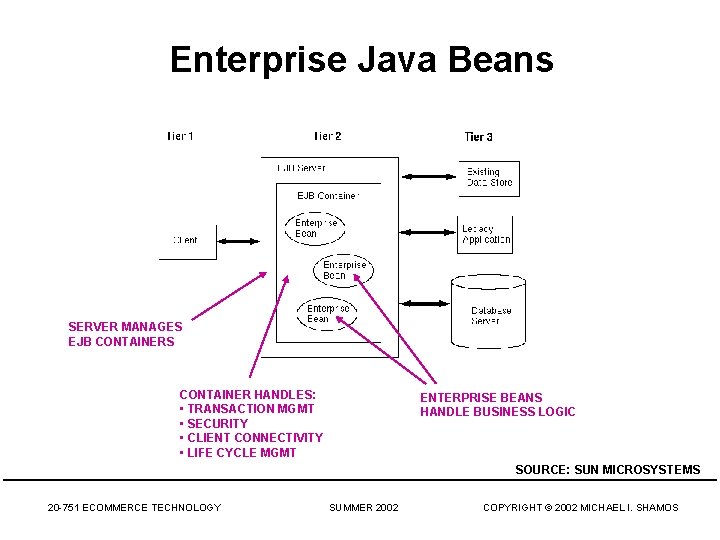
Enterprise Java Beans SERVER MANAGES EJB CONTAINERS CONTAINER HANDLES: • TRANSACTION MGMT • SECURITY • CLIENT CONNECTIVITY • LIFE CYCLE MGMT ENTERPRISE BEANS HANDLE BUSINESS LOGIC SOURCE: SUN MICROSYSTEMS 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
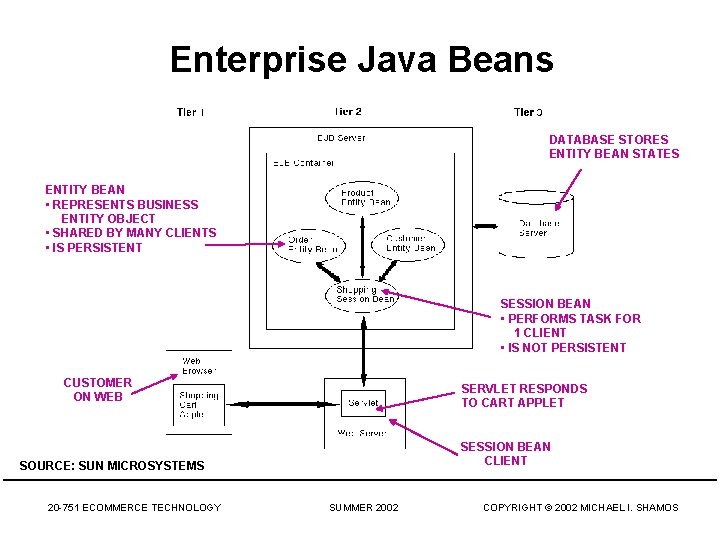
Enterprise Java Beans DATABASE STORES ENTITY BEAN STATES ENTITY BEAN • REPRESENTS BUSINESS ENTITY OBJECT • SHARED BY MANY CLIENTS • IS PERSISTENT SESSION BEAN • PERFORMS TASK FOR 1 CLIENT • IS NOT PERSISTENT CUSTOMER ON WEB SERVLET RESPONDS TO CART APPLET SESSION BEAN CLIENT SOURCE: SUN MICROSYSTEMS 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
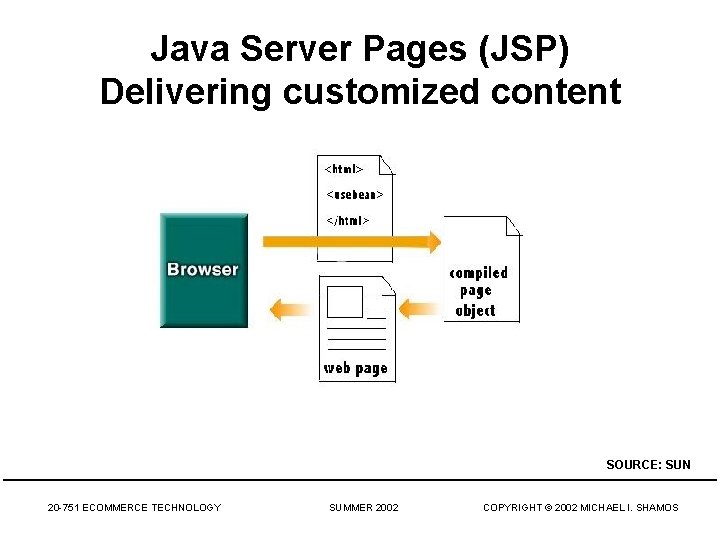
Java Server Pages (JSP) Delivering customized content SOURCE: SUN 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
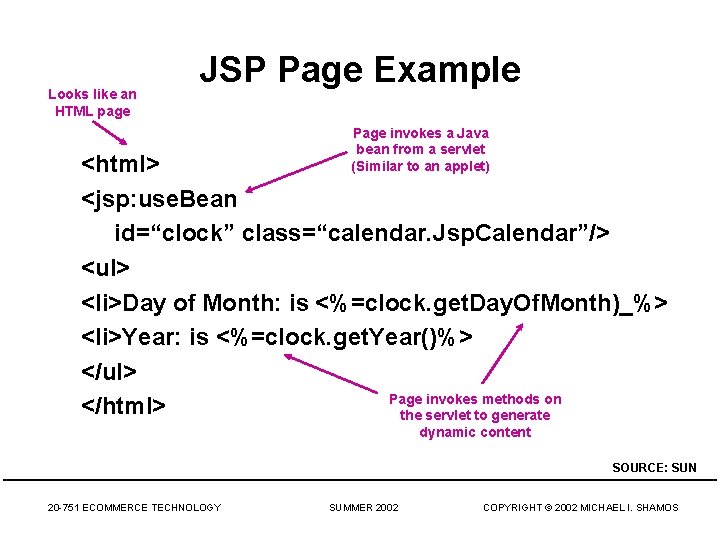
Looks like an HTML page JSP Page Example Page invokes a Java bean from a servlet (Similar to an applet) <html> <jsp: use. Bean id=“clock” class=“calendar. Jsp. Calendar”/> <ul> <li>Day of Month: is <%=clock. get. Day. Of. Month)_%> <li>Year: is <%=clock. get. Year()%> </ul> Page invokes methods on </html> the servlet to generate dynamic content SOURCE: SUN 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
Major Ideas • • Three-tiered (n-tiered) architecture Web development tools Storage Area Networks Enterprise Java Beans 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
Q&A 20 -751 ECOMMERCE TECHNOLOGY SUMMER 2002 COPYRIGHT © 2002 MICHAEL I. SHAMOS
- Slides: 27